Академический Документы
Профессиональный Документы
Культура Документы
InfoSec Definitions
Загружено:
Anonymous Fhs3ufkC0 оценок0% нашли этот документ полезным (0 голосов)
14 просмотров1 страницаInfosec definitions
Авторское право
© © All Rights Reserved
Доступные форматы
TXT, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документInfosec definitions
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате TXT, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
14 просмотров1 страницаInfoSec Definitions
Загружено:
Anonymous Fhs3ufkCInfosec definitions
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате TXT, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 1
Definitions[edit]
Information Security Attributes: or qualities, i.e., Confidentiality, Integrity
and Availability (CIA). Information Systems are composed in three main portions,
hardware, software and communications with the purpose to help identify and app
ly information security industry standards, as mechanisms of protection and prev
ention, at three levels or layers: physical, personal and organizational. Essent
ially, procedures or policies are implemented to tell people (administrators, us
ers and operators) how to use products to ensure information security within the
organizations.
The definitions of InfoSec suggested in different sources are summarized below (
adopted from).[3]
1. "Preservation of confidentiality, integrity and availability of information.
Note: In addition, other properties, such as authenticity, accountability, non-r
epudiation and reliability can also be involved." (ISO/IEC 27000:2009)[4]
2. "The protection of information and information systems from unauthorized acce
ss, use, disclosure, disruption, modification, or destruction in order to provid
e confidentiality, integrity, and availability." (CNSS, 2010)[5]
3. "Ensures that only authorized users (confidentiality) have access to accurate
and complete information (integrity) when required (availability)." (ISACA, 200
8)[6]
4. "Information Security is the process of protecting the intellectual property
of an organisation." (Pipkin, 2000)[7]
5. "...information security is a risk management discipline, whose job is to man
age the cost of information risk to the business." (McDermott and Geer, 2001)[8]
6. "A well-informed sense of assurance that information risks and controls are i
n balance." (Anderson, J., 2003)[9]
7. "Information security is the protection of information and minimises the risk
of exposing information to unauthorised parties." (Venter and Eloff, 2003)[10]
8. "Information Security is a multidisciplinary area of study and professional a
ctivity which is concerned with the development and implementation of security m
echanisms of all available types (technical, organisational, human-oriented and
legal) in order to keep information in all its locations (within and outside the
organisation's perimeter) and, consequently, information systems, where informa
tion is created, processed, stored, transmitted and destroyed, free from threats
.
Threats to information and information systems may be categorised and a correspo
nding security goal may be defined for each category of threats. A set of securi
ty goals, identified as a result of a threat analysis, should be revised periodi
cally to ensure its adequacy and conformance with the evolving environment. The
currently relevant set of security goals may include: confidentiality, integrity
, availability, privacy, authenticity & trustworthiness, non-repudiation, accoun
tability and auditability." (Cherdantseva and Hilton, 2013)[3]
Вам также может понравиться
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- COD RealityДокумент3 страницыCOD RealityAnonymous Fhs3ufkCОценок пока нет
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- JSDFLANДокумент4 страницыJSDFLANAnonymous Fhs3ufkCОценок пока нет
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- PNALOTДокумент4 страницыPNALOTAnonymous Fhs3ufkCОценок пока нет
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- Olska PoemДокумент2 страницыOlska PoemAnonymous Fhs3ufkCОценок пока нет
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- ApsoДокумент2 страницыApsoAnonymous Fhs3ufkCОценок пока нет
- QUORAQДокумент1 страницаQUORAQAnonymous Fhs3ufkCОценок пока нет
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- OECD SummaryДокумент3 страницыOECD SummaryAnonymous Fhs3ufkCОценок пока нет
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- EDCRFVДокумент5 страницEDCRFVAnonymous Fhs3ufkCОценок пока нет
- JKL PoemДокумент2 страницыJKL PoemAnonymous Fhs3ufkCОценок пока нет
- New Text DocumentДокумент2 страницыNew Text DocumentAnonymous Fhs3ufkCОценок пока нет
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- You & Tube PoemДокумент3 страницыYou & Tube PoemAnonymous Fhs3ufkCОценок пока нет
- Tube PoemДокумент3 страницыTube PoemAnonymous Fhs3ufkCОценок пока нет
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Sapt JJMДокумент2 страницыSapt JJMAnonymous Fhs3ufkCОценок пока нет
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- KPLC PoemДокумент2 страницыKPLC PoemAnonymous Fhs3ufkCОценок пока нет
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Dates and TimesДокумент9 страницDates and TimesAnonymous Fhs3ufkCОценок пока нет
- OPQWEДокумент5 страницOPQWEAnonymous Fhs3ufkCОценок пока нет
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- Cov FeefДокумент5 страницCov FeefAnonymous Fhs3ufkCОценок пока нет
- CVB PoemДокумент2 страницыCVB PoemAnonymous Fhs3ufkCОценок пока нет
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- FFMMRRДокумент5 страницFFMMRRAnonymous Fhs3ufkCОценок пока нет
- GWZ PoemДокумент2 страницыGWZ PoemAnonymous Fhs3ufkCОценок пока нет
- BNM PoemДокумент2 страницыBNM PoemAnonymous Fhs3ufkCОценок пока нет
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- AbbaДокумент4 страницыAbbaAnonymous Fhs3ufkCОценок пока нет
- MBH PoemДокумент2 страницыMBH PoemAnonymous Fhs3ufkCОценок пока нет
- Articel 4 Defs 2Документ1 страницаArticel 4 Defs 2Anonymous Fhs3ufkCОценок пока нет
- Articel 4 DefsДокумент1 страницаArticel 4 DefsAnonymous Fhs3ufkCОценок пока нет
- RTFM Read AllДокумент1 страницаRTFM Read AllAnonymous Fhs3ufkCОценок пока нет
- HP 2016 Threat ReportДокумент2 страницыHP 2016 Threat ReportAnonymous Fhs3ufkCОценок пока нет
- Special Yoga JaiminiДокумент1 страницаSpecial Yoga JaiminiAnonymous Fhs3ufkC100% (1)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Articel 5 DefsДокумент1 страницаArticel 5 DefsAnonymous Fhs3ufkCОценок пока нет
- Body Organs - BhaavasДокумент2 страницыBody Organs - BhaavasAnonymous Fhs3ufkCОценок пока нет
- TBW Ad-Pki Guide Us MJДокумент51 страницаTBW Ad-Pki Guide Us MJgchaniОценок пока нет
- Brkucc 3732 PDFДокумент116 страницBrkucc 3732 PDFVG KarthikeyanОценок пока нет
- Mcafee Total Protection Product KeyДокумент2 страницыMcafee Total Protection Product KeyGeek Squad Plus TechnologyОценок пока нет
- Computer SecurityДокумент9 страницComputer SecuritynarimeneОценок пока нет
- Threat and Vulnerability Management PolicyДокумент12 страницThreat and Vulnerability Management PolicymadhwarajganguliОценок пока нет
- Unit 1 - Cyber CrimeДокумент25 страницUnit 1 - Cyber CrimeKanika LakheraОценок пока нет
- Packet Tracer - Configure SSH: Addressing TableДокумент2 страницыPacket Tracer - Configure SSH: Addressing TableRanghel SotoОценок пока нет
- Kali Linux Hacking Tutorials Hack WPA WPA2 WPS Reaver Kali Linux PDFДокумент17 страницKali Linux Hacking Tutorials Hack WPA WPA2 WPS Reaver Kali Linux PDFC.vijayОценок пока нет
- 32pdf PDFДокумент10 страниц32pdf PDFfaisal saghirОценок пока нет
- UTM 1 Edge DatasheetДокумент4 страницыUTM 1 Edge DatasheetSoporte TijuanaОценок пока нет
- CCS425 Encryption BasicsДокумент91 страницаCCS425 Encryption BasicsJeniela EmpleoОценок пока нет
- Ailox UsersДокумент9 страницAilox UsersKhasyta azОценок пока нет
- Matriks 9001 14001 45001 Checklist Rev 1Документ55 страницMatriks 9001 14001 45001 Checklist Rev 1mdeky20Оценок пока нет
- Address List FACEBOOKДокумент2 страницыAddress List FACEBOOKSina NeouОценок пока нет
- Bearing Witness Uncovering The Logic Behind Russian Military Cyber Operations 2020 PDFДокумент84 страницыBearing Witness Uncovering The Logic Behind Russian Military Cyber Operations 2020 PDFbob smithОценок пока нет
- 1 s2.0 S0306457320308505 MainДокумент12 страниц1 s2.0 S0306457320308505 Mainuzma nisarОценок пока нет
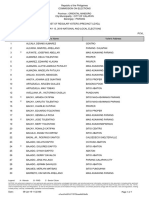
- Parang DecДокумент63 страницыParang DecAngelika CalingasanОценок пока нет
- T318 Applied Network Security: Dr. Mahmoud AttalahДокумент56 страницT318 Applied Network Security: Dr. Mahmoud Attalahباسل طفورОценок пока нет
- Stenography Using Image, Audio & Video AbstractДокумент4 страницыStenography Using Image, Audio & Video AbstractTelika Ramu0% (1)
- Cryptography Report of LIUCryptoДокумент7 страницCryptography Report of LIUCryptoBob Wazneh100% (1)
- Cryptography AND Information Security, Second Edition by Pachghare, V - KДокумент2 страницыCryptography AND Information Security, Second Edition by Pachghare, V - KamarОценок пока нет
- Palo Alto SyllabusДокумент1 страницаPalo Alto SyllabusVamsi ChowdaryОценок пока нет
- WWW - Manaresults.Co - In: Set No. 1Документ1 страницаWWW - Manaresults.Co - In: Set No. 1Priyanka vadapalliОценок пока нет
- Protecting Industrial Control Systems From Electronic ThreatsДокумент8 страницProtecting Industrial Control Systems From Electronic ThreatsMomentum Press0% (3)
- Tutorial 5Документ4 страницыTutorial 5shahrilyen89Оценок пока нет
- Ethical Challenge in Today's Age of Technology Data Protection 4Документ14 страницEthical Challenge in Today's Age of Technology Data Protection 4valerie abbygailОценок пока нет
- Final Report SAMPLEДокумент27 страницFinal Report SAMPLEtuancoiОценок пока нет
- DETAILED Lesson PLAN ICTДокумент9 страницDETAILED Lesson PLAN ICTJeanno Rhey Garces100% (3)
- Global Technology Audit Guide: Managing and Auditing IT VulnerabilitiesДокумент15 страницGlobal Technology Audit Guide: Managing and Auditing IT VulnerabilitiesSheena AbajarОценок пока нет
- Amlc Tsa Protocol PDFДокумент25 страницAmlc Tsa Protocol PDFMark Alexis MungcalОценок пока нет
- Python for Beginners: A Crash Course Guide to Learn Python in 1 WeekОт EverandPython for Beginners: A Crash Course Guide to Learn Python in 1 WeekРейтинг: 4.5 из 5 звезд4.5/5 (7)
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityОт EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityРейтинг: 5 из 5 звезд5/5 (1)
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessОт EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessОценок пока нет
- Excel 2023 for Beginners: A Complete Quick Reference Guide from Beginner to Advanced with Simple Tips and Tricks to Master All Essential Fundamentals, Formulas, Functions, Charts, Tools, & ShortcutsОт EverandExcel 2023 for Beginners: A Complete Quick Reference Guide from Beginner to Advanced with Simple Tips and Tricks to Master All Essential Fundamentals, Formulas, Functions, Charts, Tools, & ShortcutsОценок пока нет
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveОт EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveОценок пока нет
- Nine Algorithms That Changed the Future: The Ingenious Ideas That Drive Today's ComputersОт EverandNine Algorithms That Changed the Future: The Ingenious Ideas That Drive Today's ComputersРейтинг: 5 из 5 звезд5/5 (7)