Академический Документы
Профессиональный Документы
Культура Документы
JCC 2
Загружено:
Nishigandha VanarseИсходное описание:
Оригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
JCC 2
Загружено:
Nishigandha VanarseАвторское право:
Доступные форматы
Secure and Practical Outsourcing of Linear Programming in Cloud Computing
Abstract: Cloud Computing has great potential of providing robust computational power to the society at reduced cost. It enables customers with limited computational resources to outsource their large computation workloads to the cloud, and economically enjoy the massive computational power, bandwidth, storage, and even appropriate software that can be shared in a pay-per-use manner. Despite the tremendous benefits, security is the primary obstacle that prevents the wide adoption of this promising computing model, especially for customers when their confidential data are consumed and produced during the computation. On the one hand, the outsourced computation workloads often contain sensitive information, such as the business financial records, proprietary research data, or personally identifiable health information etc. To combat against unauthorized information leakage, sensitive data have to be encrypted before outsourcing so as to provide end to- end data confidentiality assurance in the cloud and beyond. However, ordinary data encryption techniques in essence prevent cloud from performing any meaningful operation of the underlying plaintext data, making the computation over encrypted data a very hard problem. On the other hand, the operational details inside the cloud are not transparent enough to customers. As a result, there do exist various motivations for cloud server to behave unfaithfully and to return incorrect results, i.e., they may behave beyond the classical semi honest model.
Existing System: Despite the tremendous benefits, outsourcing computation to the commercial public cloud is also depriving customers direct control over the systems that consume and produce their data during the computation, which inevitably brings in new security concerns and challenges towards this promising computing model. On the one hand, the outsourced computation workloads often contain sensitive information, such as the business financial records, proprietary research data, or personally identifiable health information etc. To combat against unauthorized information leakage, sensitive data have to be encrypted before outsourcing. so as to provide end to- end data confidentiality assurance in the cloud and beyond. However, ordinary data encryption techniques in essence prevent cloud from performing any meaningful operation of the underlying plaintext data, making the computation over encrypted data a very hard problem. On the other hand, the operational details inside the cloud are not transparent enough to customers. As a result, there do exist various motivations for cloud server to behave unfaithfully and to return incorrect results, i.e., they may behave beyond the classical semi hones model. For example, for the computations that require a large amount of computing resources, there are huge financial incentives for the cloud to be lazy if the customers cannot tell the correctness of the output. Besides, possible software bugs, hardware failures, or even outsider attacks might also affect the quality of the computed results. Thus, we argue that the cloud is intrinsically not secure from the viewpoint of customers. Without providing a mechanism for secure computation outsourcing, i.e., to protect the sensitive input and output information of the workloads and to validate the integrity of the computation result, it would be hard to expect cloud customers to turn over control of their workloads from local machines to cloud solely based on its economic savings and resource flexibility. For practical consideration, such a design should further ensure that customers perform less amount of operations following the mechanism than completing the computations
by themselves directly. Otherwise, there is no point for customers to seek help from cloud. Recent researches in both the cryptography and the theoretical computer science communities have made steady advances in secure outsourcing expensive computations
Proposed System: On the one hand, the outsourced computation workloads often contain sensitive information, such as the business financial records, proprietary research data, or personally identifiable health information etc. To combat against unauthorized information leakage, sensitive data have to be encrypted before outsourcing so as to provide end to- end data confidentiality assurance in the cloud and beyond. However, ordinary data encryption techniques in essence prevent cloud from performing any meaningful operation of the underlying plaintext data, making the computation over encrypted data a very hard problem. On the other hand, the operational details inside the cloud are not transparent enough to customers. As a result, there do exist various motivations for cloud server to behave unfaithfully and to return incorrect results, i.e., they may behave beyond the classical semi honest model. Fully homomorphic encryption (FHE) scheme, a general result of secure
computation outsourcing has been shown viable in theory, where the computation is represented by an encrypted combinational Boolean circuit that allows to be evaluated with encrypted private inputs.
System Architecture:
Algorithm Used:
KeyGen(1k) {K}.
This is a randomized key generation algorithm which takes a system security parameter k, and returns a secret key K that is used later by customer to encrypt the target LP problem.
ProbEnc(K,_) {_K}.
This algorithm encrypts the input tuple _ into _K with the secret key K. According to problem transformation, the encrypted input _K has the same form as _, and thus defines the problem to be solved in the cloud.
ProofGen(_K) {(y, )}.
This algorithm augments a generic solver that solves the problem _K to produce both the output y and a proof . The output y later decrypts to x, and is used later by the customer to verify the correctness of y or x.
ResultDec(K,_, y, ) {x, }.
This algorithm may choose to verify either y or x via the proof . In any case, a correct output x is produced by decrypting y using the secret K. The algorithm outputs when the validation fails, indicating the cloud server was not performing the computation faithfully.
System Specification: Hardware System Requirement Processor Speed RAM Hard Disk Floppy Drive Key Board Mouse Monitor Pentium III 1.1 Ghz 256 MB(min) 20 GB 1.44 MB Standard Windows Keyboard Two or Three Button Mouse SVGA
S/W System Requirement
Operating System Application Server
: :
Windows 95/98/2000/NT4.0. Tomcat6.0
Front End Scripts Server side Script Database
: : : :
HTML, Java. JavaScript. Java Server Pages. Mysql. JDBC.
Database Connectivity :
Вам также может понравиться
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5795)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- Exotic DVM 11 3 CompleteДокумент12 страницExotic DVM 11 3 CompleteLuc CardОценок пока нет
- Beyond "The Arc of Freedom and Prosperity": Debating Universal Values in Japanese Grand StrategyДокумент9 страницBeyond "The Arc of Freedom and Prosperity": Debating Universal Values in Japanese Grand StrategyGerman Marshall Fund of the United StatesОценок пока нет
- ENT 300 Individual Assessment-Personal Entrepreneurial CompetenciesДокумент8 страницENT 300 Individual Assessment-Personal Entrepreneurial CompetenciesAbu Ammar Al-hakimОценок пока нет
- Retail Banking Black BookДокумент95 страницRetail Banking Black Bookomprakash shindeОценок пока нет
- FE CH 5 AnswerДокумент12 страницFE CH 5 AnswerAntony ChanОценок пока нет
- Low Budget Music Promotion and PublicityДокумент41 страницаLow Budget Music Promotion and PublicityFola Folayan100% (3)
- To Find Fatty Material of Different Soap SamplesДокумент17 страницTo Find Fatty Material of Different Soap SamplesRohan Singh0% (2)
- Analytical Chem Lab #3Документ4 страницыAnalytical Chem Lab #3kent galangОценок пока нет
- Modern School For SaxophoneДокумент23 страницыModern School For SaxophoneAllen Demiter65% (23)
- Resume 1Документ2 страницыResume 1Aidie HerreraОценок пока нет
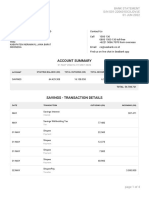
- Seabank Statement 20220726Документ4 страницыSeabank Statement 20220726Alesa WahabappОценок пока нет
- 레벨 테스트Документ2 страницы레벨 테스트BОценок пока нет
- Focus Edition From GC: Phosphate Bonded Investments For C&B TechniquesДокумент35 страницFocus Edition From GC: Phosphate Bonded Investments For C&B TechniquesAlexis De Jesus FernandezОценок пока нет
- Owners Manual Air Bike Unlimited Mag 402013Документ28 страницOwners Manual Air Bike Unlimited Mag 402013David ChanОценок пока нет
- Case Study - Kelompok 2Документ5 страницCase Study - Kelompok 2elida wenОценок пока нет
- Who Trs 993 Web FinalДокумент284 страницыWho Trs 993 Web FinalAnonymous 6OPLC9UОценок пока нет
- Bad Memories Walkthrough 0.52Документ10 страницBad Memories Walkthrough 0.52Micael AkumaОценок пока нет
- CiscoДокумент6 страницCiscoNatalia Kogan0% (2)
- I I I I: Peroxid.Q!Документ2 страницыI I I I: Peroxid.Q!Diego PradelОценок пока нет
- PE MELCs Grade 3Документ4 страницыPE MELCs Grade 3MARISSA BERNALDOОценок пока нет
- Business-Communication Solved MCQs (Set-3)Документ8 страницBusiness-Communication Solved MCQs (Set-3)Pavan Sai Krishna KottiОценок пока нет
- Fundamentals of Signal and Power Integrity PDFДокумент46 страницFundamentals of Signal and Power Integrity PDFjaltitiОценок пока нет
- Union Test Prep Nclex Study GuideДокумент115 страницUnion Test Prep Nclex Study GuideBradburn Nursing100% (2)
- Dec JanДокумент6 страницDec Janmadhujayan100% (1)
- Manual For Tacho Universal Edition 2006: Legal DisclaimerДокумент9 страницManual For Tacho Universal Edition 2006: Legal DisclaimerboirxОценок пока нет
- CS8CHP EletricalДокумент52 страницыCS8CHP EletricalCristian ricardo russoОценок пока нет
- Bajaj Vs Hero HondaДокумент63 страницыBajaj Vs Hero HondaHansini Premi100% (1)
- Instant Download Ebook PDF Ecology Concepts and Applications 8th Edition PDF ScribdДокумент41 страницаInstant Download Ebook PDF Ecology Concepts and Applications 8th Edition PDF Scribdsteven.cross256100% (45)
- Contoh Discussion Text Tentang HomeworkДокумент8 страницContoh Discussion Text Tentang Homeworkg3p35rs6100% (1)
- Adjective & VerbsДокумент3 страницыAdjective & VerbsDennis BerkОценок пока нет