Академический Документы
Профессиональный Документы
Культура Документы
CSE316
Загружено:
anon_262108279Исходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
CSE316
Загружено:
anon_262108279Авторское право:
Доступные форматы
Lovely Professional University, Punjab
Course Code CSE316 Course Category Course Title OPERATING SYSTEMS Courses with conceptual focus Course Planner 14623::Pushpendra Kumar Petriya Lectures 4.0 Tutorials Practicals Credits 0.0 0.0 4.0
TextBooks Sr No T-1 Title Operating System Concepts Reference Books Sr No R-1 R-2 R-3 Other Reading Sr No OR-1 OR-2 OR-3 OR-4 OR-5 OR-6 OR-7 OR-8 OR-9 Journals articles as Compulsary reading (specific articles, complete reference) http://codex.cs.yale.edu/avi/os-book/OS8/os8c/practice-exer-dir/22-web.pdf , http://codex.cs.yale.edu/avi/os-book/OS8/os8c/practice-exer-dir/21-web.pdf , http://codex.cs.yale.edu/avi/os-book/os7/slidedir/ index.html , www.softlookup.com/tutorial/os.asp , http://ocw.mit.edu/courses/electrical-engineering-and-computer-science/6-828-operating-system-engineering-fall-2006/lecture-notes/ , http://www.academicearth.org/courses/operating-systems-and-system-programming , http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating%20Systems/New_index1.html , http://academic.research.microsoft.com/Journal/190/sigops-operating-systems-review , http://static.usenix.org/events/osdi10/tech/full_papers/Boyd-Wickizer.pdf , Title Operating Systems Internals and Design Principles Operating Systems Modern Operating System Author WilliamStallings D.M.Dhardhere Andrew S. Tanenbaum Edition 5th 2nd 2nd Year 2000 2006 1992 Publisher Name Prentice Hall Tata McGraw Hill Prentice Hall Author Silberschatz and Galvin, Edition 7th Year 2000 Publisher Name Wiley
Relevant Websites Sr No RW-1 RW-2 RW-3 RW-4 (Web address) (only if relevant to the course) http://academic.research.microsoft.com/Keyword/44295/virtual-memory http://static.usenix.org/events/hotos11/tech/final_files/Bhattacharya.pdf http://static.usenix.org/events/hotos11/tech/final_files/Kooburat.pdf http://static.usenix.org/events/hotos11/tech/final_files/Kuz.pdf Salient Features Discussed Virtual Memory Virtually Cool Ternary Content Addressable Memory The Best of Both Worlds with On-Demand Virtualization Multicore OS benchmarks
Software/Equipments/Databases Sr No SW-1 SW-2 SW-3 SW-4 SW-5 SW-6 SW-7 SW-8 (S/E/D) (only if relevant to the course) http://ocw.mit.edu/courses/electrical-engineering-and-computer-science/6-828operating-system-engineering-fall-2006/lecture-notes/l1.pdf http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating %20Systems/pdf/Lecture_Notes/Mod%201_LN.pdf http://ocw.mit.edu/courses/electrical-engineering-and-computer-science/6-828operating-system-engineering-fall-2006/lecture-notes/l3.pdf http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating %20Systems/pdf/Lecture_Notes/Mod%202_LN.pdf http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating %20Systems/pdf/Lecture_Notes/Mod%203_LN.pdf http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating %20Systems/pdf/Lecture_Notes/Mod%204_LN.pdf http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating %20Systems/pdf/Lecture_Notes/Mod%205_LN.pdf http://nptel.iitm.ac.in/courses/Webcourse-contents/IISc-BANG/Operating %20Systems/pdf/Lecture_Notes/Mod%208_LN.pdf Salient Features OS overview Introduction to Operating System OS Organization File Systems and Management Processes and Process management Memory Management Input Output (IO) Management Real-time Operating Systems and Microkernels
LTP week distribution: (LTP Weeks) Weeks before MTE Weeks After MTE Spill Over 7 6 2
Detailed Plan For Lectures
Week Number Lecture Number Broad Topic(Sub Topic) Chapters/Sections of Text/reference books Other Readings, Lecture Description Relevant Websites, Audio Visual Aids, software and Virtual Labs It will be about Introduction of Operating Systems About Modes of Operating System About Operations and Functions of Operating Systems Learning Outcomes Pedagogical Tool Demonstration/ Case Study / Images / animation / ppt etc. Planned Slide show
Week 1
Lecture 1
Introduction to Operating System (Operating System Meaning) Introduction to Operating System (Supervisor & User Mode)
T-1:1.1
Students will understand what is an Operating System
T-1:1.5.1
Student will understand Slide show the modes of Operating Syste Students will learn, How operating system operates Slide show
Lecture 2
Introduction to Operating System (Operating System Operations and Functions) Introduction to Operating System (Types of Operating System : Simple Batch Systems)
T-1:1.5 1.6 1.7
Lecture 3
T-1:1.3
About Different Types of Student will learn the Operating Systems basic characteristics of different types of OS
Slide show
Week 1
Lecture 4
Introduction to Operating System (Multiprogramming and Multiprocessing System) Introduction to Operating System (Multitasking,Parallel ,Distributed and RTOS etc)
T-1:1.4
About Multiprogramming and Multiprocessing About Multitasking, Parallel or Distributed processing and RTOS
Students will be able to Slide show understand the differences between these two Students will get to know basic characteristics of Multitasking,Parallel, Distributed and RTOS etc Slide show
Week 2
Lecture 5
T-1:1.10 1.11
Lecture 6
Operating System Structure (Operating System Services) Operating System Structure (System Calls) Operating System Structure (System Programs) Process Management(Process Concept , Life Cycle) Process Management(PCB, Operations on Processes) Process Management(Co-operating and Independent Processes) Operating System Structure(Kernel structures : Monolithic) Operating System Structure (Layered Structure)
T-1:2.1
About Operating System students will learn Slide show Services AboutOperating System Services About System Calls about System Programs Learn about System Calls Learn about System Programs Slide show Slide show Slide show
Lecture 7 Lecture 8 Week 3 Lecture 10 Lecture 11
T-1:2.3 2.4 T-1:2.5 T-1:3.1 3.2 T-1:3.3
About Process Concept , Learn About Process Life Cycle Concept , Life Cycle About PCB, Operations on Processes Term Paper Allotment
students will learn Slide show about PCB, Operations on Processes Learn about Cooperating and Independent Processes Slide show
Lecture 12
T-1:3.4
Lecture 9
T-1:2.7
About Monolithic Kernel Students will learn structures about Monolithic Kernel structures About Layered Structure Learn about Layered Structure about InterProcess Communication About Thread Concept Kernel Level and User Level Threads About Multithreding,Thread Libraries and Thread Issues Homewok1 Allotment About Semaphores ,Mutex and Monitors About Dining Philosopher Problem,Readerwriter Problem Learn InterProcess Communication Learn Thread Concept Kernel Level and User Level Threads Learn about Multithreding,Thread Libraries and Thread Issues Learn about Critical Section Problem
Slide show
T-1:2.7 T-1:3.4 T-1:4.1
Slide show Slide show Slide show
Week 4
Lecture 13 Lecture 14
Process Management(Inter-Process Communication) Process Management(Thread Concept : Kernel Level and User Level Threads) Process Management (Multithreding,Thread Libraries and Thread Issues) Process Synchronization(Critical Section Problem) Process Synchronization (Semaphores ,Mutex and Monitors) Process Synchronization(Dining Philosopher Problem,Reader-writer Problem etc)
Lecture 15
T-1:4.2 4.3 4.4
Slide show
Lecture 16 Week 5 Lecture 17
T-1:6.2 6.3 T-1:6.5 6.7
Slide show
Learn about Slide show Semaphores ,Mutex and Monitors Learn about Dining Philosopher Problem,Readerwriter Problem Slide show
Lecture 18
T-1:6.6
Week 5
Lecture 19
Process Synchronization(Dining Philosopher Problem,Reader-writer Problem etc) CPU Scheduling(Types of Scheduling) CPU Scheduling(Scheduling Algorithms) CPU Scheduling(Scheduling Algorithms) CPU Scheduling(Multi-Processor Scheduling Algorithm)
T-1:6.6
About Dining Philosopher Problem,Readerwriter Problem About Types of Scheduling About Scheduling Algorithms About Scheduling Algorithms About MultiProcessor Scheduling Algorithm About Deadlock Characterization
Learn about Dining Philosopher Problem,Readerwriter Problem Learn about Types of Scheduling
Slide show
Lecture 20 Week 6 Lecture 21 Lecture 22
T-1:5.1 5.2 T-1:5.3 T-1:5.3 T-1:5.4
Slide show
Learn about Scheduling Slide show Algorithms Learn about Scheduling Slide show Algorithms Learn about MultiProcessor Scheduling Algorithm Learn about Deadlock Characterization Slide show
Lecture 23 Lecture 24
Deadlock(Deadlock Characterization) Deadlock(Handling of deadlocksDeadlock Prevention) Deadlock(Handling of deadlocksDeadlock Prevention) Deadlock(Deadlock Avoidance & Detection) Deadlock(Deadlock Avoidance & Detection) Deadlock(Deadlock Recovery)
T-1:7.2 T-1:7.3 7.4
Slide show
HomeWork1 Submission Learn about Handling Slide show of deadlocks Deadlock Prevention HomeWork1 Submission Learn about Handling Slide show of deadlocks Deadlock Prevention About Deadlock Avoidance Detection About Deadlock Avoidance Detection About Deadlock Recovery Learn about Deadlock Avoidance Detection Learn about Deadlock Avoidance Detection Learn about Deadlock Recovery Slide show Slide show Slide show
Week 7
Lecture 25
T-1:7.3 7.4
Lecture 26 Lecture 27 Lecture 28
T-1:7.5 7.6 T-1:7.5 7.6 T-1:7.7
MID-TERM
Week 8 Lecture 29 Lecture 30 Lecture 31 Memory Management(Logical & Physical Address Space) Memory Management(Swapping) Memory Management(Contiguous Memory allocation) Memory Management(Paging) Memory Management (Segmentation) Memory Management(Virtual Memory and Demand Paging) Memory Management(Virtual Memory and Demand Paging) T-1:8.1 T-1:8.2 T-1:8.3 About Logical Physical Learn about Logical Slide show Address Space Physical Address Space About About Contiguous Memory allocation About Paging About segmentation About Virtual Memory and Demand Paging About Virtual Memory and Demand Paging Students will learn about Swapping Students will learn about Contiguous Memory allocation Learn about Paging Learn about segmentation Students will learn about Virtual Memory and Demand Paging Students will learn about Virtual Memory and Demand Paging Slide show Slide show
Lecture 32 Week 9 Lecture 33 Lecture 34
T-1:8.4 T-1:8.6 T-1:9.1 9.2 9.4 9.6
Slide show Slide show Slide show
Lecture 35
T-1:9.1 9.2 9.4 9.6
Slide show
Week 9
Lecture 36
File Management(File Concepts) File Management(Access methods)
T-1:10.1 T-1:10.2 T-1:10.3 T-1:10.4 10.5
About File Concepts About Access methods About Directory Structure About File System Mounting and Sharing About Protection About Allocation methods About FreeSpace Management About Directory Implementation About Directory Implementation About Application IO Interface About Kernel IO subsystem Homework,Term Paper,Test 3
Learn about File Concepts Learn about Access methods Learn about Directory Structure Students will learn about File System Mounting and Sharing
Slide show Slide show Slide show Slide show
Week 10
Lecture 37 Lecture 38
File Management(Directory Structure) File Management(File System Mounting and Sharing) File Management(Protection) File Management(Allocation methods) File Management(Free-Space Management) File Management(Directory Implementation) I/O and Secondary Storage Structure(Directory Implementation)
Lecture 39 Lecture 40
T-1:10.6 T-1:10.4
Learn about Protection Slide show students will learn about Allocation methods Slide show
Week 11
Lecture 41 Lecture 42
T-1:11.5 T-1:11.3 T-1:11.3
Learn about FreeSpace Slide show Management Learn about Directory Implementation Learn about Directory Implementation Learn about Application IO Interface Students will learn About Kernel IO subsystem Slide show Slide show
Lecture 43
I/O and Secondary Storage Structure(Application I/O Interface) I/O and Secondary Storage Structure(Kernel I/O subsystem)
T-1:Chapter 13.3
Slide show
T-1:Chapter 13.4
Slide show
Lecture 44 Week 12 Lecture 45 I/O and Secondary Storage Structure(Disk Scheduling) I/O and Secondary Storage Structure(Disk Management) Lecture 46 I/O and Secondary Storage Structure(Swap-Space Management) I/O and Secondary Storage Structure(RAID Structure) Lecture 47 Protection and Security(Need for Security) Protection and Security(Secure Software Systems) Lecture 48 Protection and Security(Different Security Environments) T-1:Chapter 12.4 T-1:Chapter 12.5 T-1:Chapter 12.6
About Disk Scheduling
Learn about Disk Scheduling
Slide show Slide show Slide show
About Disk Management Learn about Disk Management about SwapSpace Management About RAID Structure System security introduction Term Paper Final Submission Learn SwapSpace Management Learn about RAID Structure Learn about system security Learn about Secure Software Systems
T-1:Chapter 12.7 T-1:17.1 17.2 17.3 T-1:18.1 T-1:18.2
Slide show Slide show Slide show
about Different Security Learn about Different Slide show Environments Security Environments
Week 12
Lecture 48
Protection and Security(Security Vulnerability like Buffer overflow) Protection and Security(Trapdoors, Backdoors, cache poisoning etc) Protection and Security(Access Control based Security SystemsAccess Control Models)
T-1:18.1
about Security Learn about Security Vulnerability like Buffer Vulnerability like overflow Buffer overflow About ssecurity threats About Access Control based Security Systems Access Control Models Learn about security threats
Slide show
Week 13
Lecture 49
T-1:Chapter 18.2 T-1:Chapter 17.4
Slide show
Learn about Access Slide show Control based Security Systems Access Control Models Slide show
Lecture 50
Protection and Security (Implementing the Access Control Matrix) Protection and Security (Authentication-Password based Authentication) Protection and Security(Password Maintenance & Secure Communication)
T-1:Chapter 17.5
About Implementing the Learn about Access Control Matrix Implementing the Access Control Matrix About Password based Authentication About Password Maintenance Secure Communication Learn about Password based Authentication
T-1:Chapter 18.5
Slide show
T-1:Chapter 18.5
Learn About Password Slide show Maintenance Secure Communication
Lecture 51
Protection and Security (Application Security - Virus, Program Threats) Case studies(Case Studies of Linux) Case studies(Case Studies of Windows.)
T-1:Chapter 18.1 18.2 18.3 T-1:Chapter 21 T-1:Chapter 22
About Application Learn about Slide show Security Virus, Program Application Security Threats Virus, Program Threats About Case Studies of Linux About Case Studies of Windows Learn about Case Studies of Linux Learn about Case Studies of Windows Slide show Slide show
Lecture 52
SPILL OVER
Week 14 Lecture 53 T-1:23.6 23.8 Influential operating systems IBM OS360,CTSS Multimedia systems network management, CPU scheduling Students will learn Slide show about Influential operating systems IBM OS360,CTSS Students will learn about Multimedia systems network management, CPU scheduling slide show
Lecture 54
T-1:20.1 20.6
Scheme for CA:
Component Homework,Term Paper,Test Frequency 2 Total :Out Of 3 Each Marks Total Marks 10 10 20 20
Details of Academic Task(s)
AT No.
Objective
Topic of the Academic Task
Nature of Academic Task (group/individuals/field work Individual
Evaluation Mode
Allottment / submission Week 4/6
Homework 1
To reinforce and Introduction to Operating System, Operating System Structure, extend learning Process Management initiated in class and develop abilities for studying independently. To enrich learning and encourage individual initiatives.
On the basis of answers attempted by students
Term Paper 1
1 Compare the MemoryManagement of Windows with Linux Group 2 Case Study: According to you which one among UNIX, LINUX and Windows, is best. 3 What should be done for proper working of your computer system? Give general guidelines 4 How windows operating system handles viruses? Write down various viruses that can cause serious damage to the computer system. 5 Compare CPU Scheduling of LINUX and UNIX. 6 Compare the MemoryManagement of UNIX with Linux 7 Compare Features of Windows 2000 with windows Vista 8 Compare Features of Windows 2000 with windows XP 9 Compare Features of Windows 2000 with windows 98 10 Which operating system is used in Nokia Mobile Phones and how it works? 11 Differentiate FAT, FAT32 and NTFS 12 Which operating system is used to handle computer networks, how it works on LAN 13 Compare File Security mechanism of windows 98 with windows XP 14 Compare File Security mechanism of windows ME with windows XP 15 Compare File Security mechanism of windows 2000 with windows XP 16 How registry is helpful in managing security. 17 How operating system manages disk drives? How can we prevent disk damage?What is the process of disk sharing Individual
The term paper should be pedagogical in nature, explaining or illustrating a certain aspect of topic assigned.
3 / 12
Homework,Term Paper,Test 1
To assess student Memory Management, File Management, I/O and secondary performance in class management storage structure.
On the basis of answers attempted by students.
9 / 11
Вам также может понравиться
- Operating System Objectives and Functions d2Документ62 страницыOperating System Objectives and Functions d2Sruthi AKОценок пока нет
- Os EvolutionДокумент14 страницOs EvolutionLeena N ThomasОценок пока нет
- Hydrokinetic Energy Conversion Technology ResearchДокумент15 страницHydrokinetic Energy Conversion Technology ResearchGILBERTO OLANO BUSTAMANTEОценок пока нет
- Oil and Gas IndustryДокумент23 страницыOil and Gas IndustryJoshwin JacobОценок пока нет
- HW Fluido IIДокумент33 страницыHW Fluido IIRodrigo PerezОценок пока нет
- 2Документ1 страница2Gilang Lovianindra Cipta IIОценок пока нет
- NLNGДокумент11 страницNLNGAifuwa TundeОценок пока нет
- New Investor Overview March 20011Документ27 страницNew Investor Overview March 20011Amrinder6Оценок пока нет
- Site Location SelectionДокумент12 страницSite Location Selectionhos JohnsonОценок пока нет
- (Lecture Notes in Computer Science 4488) JeongHee Cha, GyeYoung Kim, HyungIl Choi (auth.), Yong Shi, Geert Dick van Albada, Jack Dongarra, Peter M. A. Sloot (eds.)-Computational Science – ICCS 2007_ 7.pdfДокумент1 284 страницы(Lecture Notes in Computer Science 4488) JeongHee Cha, GyeYoung Kim, HyungIl Choi (auth.), Yong Shi, Geert Dick van Albada, Jack Dongarra, Peter M. A. Sloot (eds.)-Computational Science – ICCS 2007_ 7.pdfGaboGagОценок пока нет
- MidaДокумент16 страницMidaSyed Zafirna W HОценок пока нет
- Instromet CatalogueДокумент4 страницыInstromet CatalogueGabriel A. ZorrillaОценок пока нет
- 002 016 1 PDFДокумент15 страниц002 016 1 PDFaepriyadiОценок пока нет
- PD ProjectДокумент70 страницPD ProjectUmer AizazОценок пока нет
- Seamless Precision Steel Tubes For Hydraulic Cylinders - TN 008-00Документ8 страницSeamless Precision Steel Tubes For Hydraulic Cylinders - TN 008-00refeiОценок пока нет
- Role of Engineering in Poverty ReductionДокумент8 страницRole of Engineering in Poverty ReductionVarma AmitОценок пока нет
- Real Time System (MCQS)Документ12 страницReal Time System (MCQS)Vibha100% (1)
- Bechtel Technology Journal: Major OfficesДокумент216 страницBechtel Technology Journal: Major Officesข้าวเม่า ทอดОценок пока нет
- Sagarmala ProjectДокумент22 страницыSagarmala ProjectAnkit Agarwal100% (1)
- Woodfibre LNG Information Sheets Seawater CoolingДокумент2 страницыWoodfibre LNG Information Sheets Seawater CoolingFeldon DsilvaОценок пока нет
- Skmm4513 Cad Project Sem 1 1516Документ4 страницыSkmm4513 Cad Project Sem 1 1516Puvendran Balakrishnan100% (2)
- Column Design PDFДокумент3 страницыColumn Design PDFVineet KhandelwalОценок пока нет
- HW 1 SolutionДокумент5 страницHW 1 SolutionNisargPatelОценок пока нет
- Major ProjectДокумент55 страницMajor ProjectpraveenpusaОценок пока нет
- Circular Pipe Loaded Laterally in Cohesive SoilДокумент4 страницыCircular Pipe Loaded Laterally in Cohesive SoilMaruda8382Оценок пока нет
- CFD For Offshore ApplicationsДокумент34 страницыCFD For Offshore ApplicationsDaniel GómezОценок пока нет
- Daewoo International: December 2010Документ38 страницDaewoo International: December 2010Angelica MeloОценок пока нет
- Sbtet Ap C-14 Syllabus Dmet C-14Документ211 страницSbtet Ap C-14 Syllabus Dmet C-14thirukumarОценок пока нет
- Label Scale User ManualДокумент27 страницLabel Scale User ManualmrrceliОценок пока нет
- Fyp SlideДокумент52 страницыFyp SlideZulhilmi ZalizanОценок пока нет
- Reliance Industries Limited: Hazira Manufacturing DivisionДокумент20 страницReliance Industries Limited: Hazira Manufacturing DivisionTracy WhiteОценок пока нет
- Class Test 4 & 5 Cams - Gears - Assignment Questions KomДокумент10 страницClass Test 4 & 5 Cams - Gears - Assignment Questions KomVenkateswar Reddy MallepallyОценок пока нет
- Shubham SalunkheДокумент14 страницShubham Salunkheप्रथमेश क्षीरसागरОценок пока нет
- Summer Internship Project Work OnДокумент28 страницSummer Internship Project Work OnVikramОценок пока нет
- MetroДокумент24 страницыMetroMoin MughalОценок пока нет
- Red Hat Certified System Administrator I With RHCSAДокумент3 страницыRed Hat Certified System Administrator I With RHCSASyedОценок пока нет
- Design Exploration - Judd KaiserДокумент30 страницDesign Exploration - Judd KaiserSangbum KimОценок пока нет
- PAT Scheme in IndiaДокумент44 страницыPAT Scheme in IndiarvnesariОценок пока нет
- Introduction To Machine Learning For Chemists An Undergraduate Course Using Python Notebooks For Visualization Data Processing Data Analysis and Data ModelingДокумент14 страницIntroduction To Machine Learning For Chemists An Undergraduate Course Using Python Notebooks For Visualization Data Processing Data Analysis and Data Modelingjose castillaОценок пока нет
- Liferay Certified Professional Developer Exam BlueprintДокумент6 страницLiferay Certified Professional Developer Exam Blueprintnokia6230iОценок пока нет
- Cement OsДокумент28 страницCement OsLuis Romer Soliz AndiaОценок пока нет
- Concept Plan South Aspelund Industrial Park 2013-06-19Документ24 страницыConcept Plan South Aspelund Industrial Park 2013-06-19Edgar MugaruraОценок пока нет
- 1 Socket & Spigot Cotter JointДокумент37 страниц1 Socket & Spigot Cotter JointShubham BajpaiОценок пока нет
- FTA - Report - WPT 2014 PDFДокумент61 страницаFTA - Report - WPT 2014 PDFJustin SitohangОценок пока нет
- Week 3 - History - Introduction and Current Developments of Project Management (Student's Version 2.0)Документ67 страницWeek 3 - History - Introduction and Current Developments of Project Management (Student's Version 2.0)Fadhli Fegious100% (1)
- Pyxis SPT HepДокумент597 страницPyxis SPT HepanithaarumallaОценок пока нет
- Mech-Project Report of VwatДокумент50 страницMech-Project Report of VwatOscar Reyes RodríguezОценок пока нет
- NSS GPRSДокумент154 страницыNSS GPRSVenkatramana VundyalaОценок пока нет
- Newater Supply SingaporeДокумент41 страницаNewater Supply SingaporeBui Quynh NgaОценок пока нет
- Rajan Viva Voce PHDДокумент65 страницRajan Viva Voce PHDSatyanarayan Reddy KОценок пока нет
- Study of Quality Management in Construction Industry: I J I R S E TДокумент8 страницStudy of Quality Management in Construction Industry: I J I R S E Trizwan hassanОценок пока нет
- Fluid Mechanics & Machines - by LearnEngineering - inДокумент307 страницFluid Mechanics & Machines - by LearnEngineering - inVishva PatelОценок пока нет
- Preview Steffen Bangsow Auth. Tecnomatix Plant Simulation Modeling and Programming by Means of ExamplesДокумент20 страницPreview Steffen Bangsow Auth. Tecnomatix Plant Simulation Modeling and Programming by Means of Examplesaakhyar_2Оценок пока нет
- Project IOCДокумент28 страницProject IOCAyan SinghОценок пока нет
- 010 Subsea Hose PDFДокумент16 страниц010 Subsea Hose PDFJhonatan FerreiraОценок пока нет
- Assignment On Feasibility Study of A SunДокумент7 страницAssignment On Feasibility Study of A SunI Tech Services KamranОценок пока нет
- Using Python As Primary Language For Teaching ProgrammingДокумент9 страницUsing Python As Primary Language For Teaching ProgrammingHaisum Bhatti100% (1)
- Henkel Loctite AdesiveДокумент60 страницHenkel Loctite Adesive69x4Оценок пока нет
- Python Course in ChandigarhДокумент11 страницPython Course in ChandigarhManpreet SinghОценок пока нет
- Kodak Pylon Application NoteДокумент13 страницKodak Pylon Application NoteBradОценок пока нет
- Operating Systems PDFДокумент11 страницOperating Systems PDFsidsurОценок пока нет
- Cse 508Документ11 страницCse 508ishanatmuzaffarpur7893Оценок пока нет
- Lovely Professional University, Punjab: Course No Cours Title Course Planner Lectures Tutorial Practical CreditsДокумент8 страницLovely Professional University, Punjab: Course No Cours Title Course Planner Lectures Tutorial Practical CreditsAnjan TanejaОценок пока нет
- Nc62-2016-E1 - CATALOGДокумент724 страницыNc62-2016-E1 - CATALOGpanaynte7693Оценок пока нет
- ESD 5 UnitsДокумент117 страницESD 5 UnitsgirishgandhiОценок пока нет
- Operating Systems Notes FINAL - Unit2Документ13 страницOperating Systems Notes FINAL - Unit2Arvind UpadhyayОценок пока нет
- BIT 2102 Computer Systems and OrganizationДокумент21 страницаBIT 2102 Computer Systems and Organizationwillyman3009Оценок пока нет
- Parallel Computing (Unit5)Документ25 страницParallel Computing (Unit5)Shriniwas YadavОценок пока нет
- Emb 1Документ14 страницEmb 1Shah VatsalОценок пока нет
- 10 ProgrammingParadigmsДокумент48 страниц10 ProgrammingParadigmsHải TrầnОценок пока нет
- MIT Assignment (19CS20)Документ34 страницыMIT Assignment (19CS20)Imran AliОценок пока нет
- Nicolas Pantano ReportДокумент23 страницыNicolas Pantano Reportdhruv111Оценок пока нет
- Os (2marks Only)Документ20 страницOs (2marks Only)John mugiОценок пока нет
- Lesson 1.2 (Evolution of Operating Systems)Документ7 страницLesson 1.2 (Evolution of Operating Systems)Elyzza Wye AlbaoОценок пока нет
- JHS CSS - PPE Grade 10 4th WeekДокумент23 страницыJHS CSS - PPE Grade 10 4th WeekJoeven Pantaleon100% (1)
- CR800 Controller - Detailed Explanations of Functions and Operations Bfp-A3478j PDFДокумент800 страницCR800 Controller - Detailed Explanations of Functions and Operations Bfp-A3478j PDFM LLОценок пока нет
- Multiple Choice QuestionsДокумент13 страницMultiple Choice QuestionsArpitGuptaОценок пока нет
- CRITICAL REVIEW of The Structure of The "THE"-Multiprogramming SystemДокумент2 страницыCRITICAL REVIEW of The Structure of The "THE"-Multiprogramming SystemUmme YahyaОценок пока нет
- ln1 Intro v2 PDFДокумент29 страницln1 Intro v2 PDFVeeresh PalledОценок пока нет
- Naresh It Interview Questions-1Документ13 страницNaresh It Interview Questions-1Aman JolheОценок пока нет
- Operating Systems: Ms. Uma.SДокумент73 страницыOperating Systems: Ms. Uma.SAmirtha VarshiniОценок пока нет
- I PUC Unit AДокумент44 страницыI PUC Unit AAman kekkarОценок пока нет
- Process Management, Threads, Process Scheduling - Operating SystemsДокумент21 страницаProcess Management, Threads, Process Scheduling - Operating SystemsMukesh50% (2)
- Question: Explain Context SwitchingДокумент10 страницQuestion: Explain Context SwitchingpathakpranavОценок пока нет
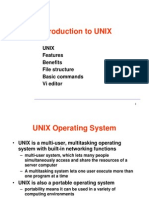
- Introduction To UNIX: Unix Features Benefits File Structure Basic Commands Vi EditorДокумент14 страницIntroduction To UNIX: Unix Features Benefits File Structure Basic Commands Vi EditorPankaj TripathiОценок пока нет
- OS NotesДокумент78 страницOS NotesGRIMHEART REAPERОценок пока нет
- Nso Science Olympiad Sample Question Paper 1 Class 10Документ22 страницыNso Science Olympiad Sample Question Paper 1 Class 10Technical AyushОценок пока нет
- Course ModulesДокумент322 страницыCourse ModulesJoseph Amor Colis SomeraОценок пока нет
- KicksДокумент137 страницKicksavdubeyОценок пока нет
- MCQ AllДокумент6 страницMCQ Allmukeshsharma86Оценок пока нет