Академический Документы
Профессиональный Документы
Культура Документы
Open Source Tools & Components
Загружено:
Prabhat KumarАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Open Source Tools & Components
Загружено:
Prabhat KumarАвторское право:
Доступные форматы
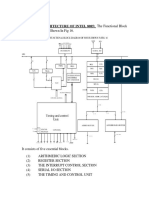
OPEN SOURCE TOOLS & COMPONENTS
SNS COLLEGE OF TECHNOLOGY
COIMBATORE - 35
DEPARTMENT OF COMPUTER SCIENCE AND ENGINEERING (UG & PG) Final Year Computer Science and Engineering, 8th Semester Subject Code & Name: OPEN SOURCE TOOLS & COMPONENTS Prepared by: Prof.T.KALAIKUMARN, Prof/CSE, Mrs.S.DHANALAKSHMI , AP/CSE,
Mr.D.PRABAKAR AP/CSE
UNIT I Part -A 1. What is Open source software? Open Source Software is software for which the underlying programming code is available to the users so that they may read it, make changes to it, and build new versions of the software incorporating their changes. There are many types of Open Source Software, mainly differing in the licensing term under which (altered) copies of the source code may (or must be) redistributed. 2. What is the Need of Open Source Systems? No initial cost No licensing issues Openness and Transparency Speed of Access Freedom of movement Portable Reliable Stable Security
3. What are the four important factors that led to the development of open source software? The following are the four important factors that lead to the development of Open Source Software: To diminish the high monopoly value of the Proprietary Software To avoid discrimination among persons like developers of the product and users of the product To enable the user finding and fixing the bugs themselves To allow customers to have control over the products they use and to redistribute the same with or without modifications. Page 1
SNSCT Department of Computer Science & Engineering (UG&PG)
OPEN SOURCE TOOLS & COMPONENTS
4. What are the advantages of open source system? Lesser hardware costs High-quality software No vendor lock-in Integrated management Simple license management Lower software costs Abundant support Scaling and consolidating.
5. Mention some Applications of Open Source Systems? Finance Educational Data Storage and Management Games Media Networking and Internet Graphics
6. What are the two phases in the evolution of Linux? A Development Phase: Here the Kernel is not reliable and the Process is to add functionality to it, Optimize it and to try new ideas. This Phase gives rise to odd-numbered version numbers, such as 1.1,1.3 etc., This is the time when the maximum amount of work is done on the kernel A Stabilization Phase: Where the aim is to produce as stable a kernel as possible. Only minor adjustments and modifications are made. The version numbers of so called Stable Kernels are even, such as 1.0,1.2 etc., 7. What are the advantages of Linux? Low-Cost Runs on old Hardware Choice Installation and GUI Security Open source 8. List the disadvantages of Linux Learning Lack of equivalent programs More technical ability needed Not all hardware compatible
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 2
OPEN SOURCE TOOLS & COMPONENTS
9. What are the types of system? Operating system is a generic term which in fact describes several families of systems Single task system: Only one program may be run at a time, and therefore only one person may work on a machine at one time. However, the process may make use of the whole of the resources and power of the machine Multi task system: Several Processes can be executed in parallel. Operating time is cut up into small intervals and each process is executed during these short periods. 10. What are the roles of an operating system? Virtual Machine: Sharing the Processor: Memory Management: Resource management: Communication hub of the machine 11. Define Kernel mode and user mode The kernel is a privileged mode, in which no restriction is imposed on the kernel of the system. The kernel may use all the instructions of the processor, manipulate the whole of the memory, and talk directly to the peripheral controllers. The user mode is the normal execution mode for a process. In this mode, the process has no privilege. 12. Define Scheduler The scheduler is the kernel function which decides which process should be executed by the processor: the scheduler scans the list of processes in the ready state, and uses several criteria to choose which process to execute. 13. What are the different scheduling policies in Linux? The Linux scheduler has three different scheduling policies: one for normal Processes, and two for real time processes SCHED_FIFO, for a unalterable real time process. SCHED_RR, for an alterable real time process, SCHED_OTHER, for a classical process. 14. List some of the GNU tools Gcc Debugger Strace Make 15. What are the formats supported in Linux for executable programs Linux supports two formats for executable programs A.out-binary format ELF dynamic libraries SNSCT Department of Computer Science & Engineering (UG&PG) Page 3
OPEN SOURCE TOOLS & COMPONENTS
16. Define FOSS? Free/Open Source Software, or FOSS, is software that is liberally licensed to Grant users the right to study, change and improve its design since its source code is Made available. The definition of free software, as enunciated by the Free Software Foundation, states that four essential freedoms should be contained within its license 17. List the Features of FOSS. The freedom to run the program for any purpose. The freedom to study and modify the program. The freedom to copy the program so you can help your neighbor, and The freedom to improve the program and release your improvements to the public, so that the whole community benefits. 18. Why we need the FOSS? Free Redistribution Source Code Derived Works Integrity of the Author's Source Code No Discrimination against Persons or Groups No Discrimination against Fields of Endeavor Distribution of License License Must Not Be Specific to a Product License Must Not Contaminate Other Software 19. Give An Advantage of Foss & Gnu/Linux. the reduction of overhead for software licenses increased efficiency Productivity for use of a more stable and secure system. quick and light Live CD distribution provide an easily maintained 20. Can you discuss about brief history of GNU/Linux. 1970s: UNIX operating system developed at Bell Labs and by a diverse group of contributors outside of Bell Labs; later AT&T enforces intellectual property rights and closes the code 1983: Richard Stallman founds the Free Software Foundation 1993: Linus Torvalds releases first version of Linux built 1997: Debian Free Software Guidelines released 1998: Netscape releases Navigator in source 21. List the Recent trends in Foss. Opportunity to build the next computing platform Disruptive Innovations for the next users Low-Cost Computers Server-centric Computing Linux and Open-Source Software Localisation (Language Support) Remote Server Management SNSCT Department of Computer Science & Engineering (UG&PG) Page 4
OPEN SOURCE TOOLS & COMPONENTS
22. Why partition is essential for OS? One of the goals of having different partitions is to achieve higher data security in case of disaster. By dividing the hard disk in partitions, data can be grouped and separated. When an accident occurs, only the data in the partition that got the hit will be damaged, while the data on the other partitions will most likely survive. 23. What are the two kinds of major partitions on a Linux system? Data partition: normal Linux system data, including the root partition containing all the data to start up and run the system; Swap partition: expansion of the computer's physical memory, extra memory on hard disk. 24. Define Mount Points. All partitions are attached to the system via a mount point. The mount point defines the place of a particular data set in the file system. Usually, all partitions are connected through the root partition. On this partition, which is indicated with the slash (/), directories are created. These empty directories will be the starting point of the partitions that are attached to them. 25. List the properties of LINUX Linux is free: Linux is portable to any hardware platform: Linux was made to keep on running: Linux is secure and versatile: Linux is scalable 26. What is GPL? The license commonly used is the GNU Public License (GPL). The license says That anybody who may want to do so, has the right to change Linux and eventually to redistribute a changed version, on the one condition that the code is still available after redistribution. In practice, you are free to grab a kernel image, for instance to add support for tele transportation machines or time travel and sell your new code, as long as your customers can still have a copy of that code. 27. Write the 4 independent management groups of PAM? Account Management Authentication Management Password Management Session Management 28. List various standards in FOSS. Free and Open Source Software (FOSS) Greece/UNU/Europe/Africa. Open Source (OS) Africa, Europe, USA, Canada, Japan Libre Software (LS) Spain, France, South American Free/Libre/Open Source Software (FLOSS) Europe, other parts of the world Free Software (FS) Free Software GNU Foundation USA, Africa Open Source Software (OSS) Open Source Initiative-USA, Asia, etc. SNSCT Department of Computer Science & Engineering (UG&PG) Page 5
OPEN SOURCE TOOLS & COMPONENTS
29. Distinguish propriety software and FOSS.
Proprietary software 1. Closed source commercial software 2. Proprietary ware (demos) 3. Shareware 4. Freeware 5. Abandon ware
Non-proprietary software 1. 2. 3. 4. 5. 6. Public domain Free Software (FS) Open Source (OSS) Commercial software Software licensed for a fee Both proprietary and nonproprietary.
30. Differentiate advantages & disadvantages of FOSS.
Advantages
Disadvantages
1. Ability to tailor to fit local needs 2. No restriction on use 3. Low cost
1. Unanticipated Efforts 2. Lack of coordination 3. Inadequate technical support : Customization :
31. Give different types of Library in LINUX. MicroLCS, Emilda Evergreen FireFly GNUTeca Avanti Koha OpenBiblio phpMyLibrary PMB PYTHEAS WEBLIS 32. Mention the some of SHELL Commands. /bin/csh - Executed after .cshrc when logging in with C shell as the login shell. Edit [file:] function - Edit helps in finding the line of program where execution was stopped. List: List command types the text of program in the vicinity where it is presently stopped. Function is name of function and file is name of file. SNSCT Department of Computer Science & Engineering (UG&PG) Page 6
OPEN SOURCE TOOLS & COMPONENTS
chmod command -With the help of chmod command we can change permissions of a file or a directory. chown username filename - With the help of chown command, we can change owner ship of a file or directory. Only real owner (exception for the super user) of the file or directory can change owner ship of a file or directory. Once it is changed,he/she will not have any authority revert it back.
33. What are the 2 stages in boot Process of Linux? The boot process in Linux has two stages: The boot loader stage The kernel stage. 34. What is PAM? Pluggable authentication modules (PAM) are a mechanism to integrate multiple low-level authentication schemes into a high-level application programming interface (API). It allows programs that rely on authentication to be written independent of the underlying authentication scheme. . 35. What are the functions of the TCP/IP? TCP/IP (Transport Control Protocol/Internet Protocol) is a protocol suite that is implemented in theOS you are using and is running on OSI-layer 3 and 4 the network and transport layer. TCP/IP is responsible for you having an IP-address and delivers the possibility to the computer to communicate with other systems using IP-addresses, a subnetmask, portnumbers and a default gateway. 36. Discuss about some of the Subdirectories. /root directory, starting point of the directory tree /home (private) directories of users /devDevice files that represent hardware components /etc Important files for system configuration /etc/init.d Boot scripts/usr/binGenerally accessible programs 37. What is the use of LINUX Directory Structure? Store drives Accessing data using folders Root directory: beginning of file system 38. What are strength and weakness of FOSS? Strength: Ability to fit local needs No restrictions on use Low cost & Innovation User-driven Collaboration &Transfer of Technical Know-How Weakness: Unanticipated Efforts Lack of Coordination Inadequate Technical Support & Risk of discontinuation SNSCT Department of Computer Science & Engineering (UG&PG) Page 7
OPEN SOURCE TOOLS & COMPONENTS
39. Give an Operating System responsibility. Device management using device drivers Process management using processes and threads Inter-process communication Memory management File systems 40. Differences between DOS and Unix1 UNIX is multi user and multi tasking operating system. Where as DOS is single user,single tasking system. All the commands in UNIX should be given in lower case. Where as in DOS Commands can be entered in any case. Processor will be in protected mode in Unix unlike DOS which uses unprotected o Mode. Unix supports both character user interface and graphical interface (X windows) Unlike DOS which supports only character user interface. User requires legal username and password to use Unix machines. DOS systems o Can be used by any one without any username and password. 41. What is POTS? POTS stand for Plain Old Telephone Service. This was the most popular method of Connecting to the Internet from ones home or when on the road. It: Uses the standard phone line User dials up the ISP to make a connection Speeds said to be 56K but always slower Requires minimal hardware and setup Costs about $14 to $20 / month for unlimited use 42. Give the POTS Advantages Available from anyplace. Just find a phone line and dial in. Easy set up. Most every computer purchased today includes all the necessary hardware and makes it easy to get connected to any one of several major ISPs. Easy to switch ISPs. If one provides poor service or raises their prices, you can switch to a new provider. Useful when traveling. Many ISPs will have local numbers in different cities so that you are able to access the Internet and your e-mail without having to dial long distance 43. Give the POTS Disadvantages Slow. Though advertised as 56K, the connection is always slower. In some communities where there has been recent growth, local phone companies will use their own compression technologies that can cut the speed of your modem in half or more. Dialing-up and connecting is slow. The time it takes to dial up an ISP and have the modem negotiate a connection with the other end can take about a minute Ties up the phone line. A modem cannot use the line at the same time as another device.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 8
OPEN SOURCE TOOLS & COMPONENTS
Intermittent connections. If you are not actively retrieving mail or browsing web pages, the ISP will break the connection. And, since it ties up the phone line, most individuals will wish to disconnect when not in use.
44. Define ISDN ISDN stands for Integrated Services Digital Network. This is a standard for digital communication that was established in the early 90s. It was to revolutionize Internet access when most of us were using 28K modems but it was difficult for the end user to get and slow to be adopted for a multitude of reasons. It is: Digital version of dial-up telephone Installed by local phone company Requires an ISDN card in the PC or an external modem A digital call is made at the time of need Reliable speeds of 64-128K Internet access (ISP) a separate cost Monthly fee: $45 base fee for metered use, $120 for unlimited use 45. Give the advantage of ISDN Fast dialing (~1.5 sec). The time it takes to make your initial connection is almost imperceptable. Easy to switch ISPs. All you have to do is call a different number. ISP can connect to you (extra cost) Available in some locations where alternatives are not 46. Give the disadvantage of ISDN Expensive Intermittent connections Requires additional hardware Requires new wiring Metered by phone company and sometimes the ISP Difficult to get installed Works only at the site of installation Limited availability 47. Define DSL DSL stands for Digital Subscriber Line. It is essentially a fixed digital connection between you and your ISP. Runs over ordinary telephone wires Digital signals use high frequencies not used by analog phones Installed by local phone company Reliable speeds of 144K to 7M Always on Internet access (ISP) a separate cost Costs from $22 for 256K to $275 for 7M 48. Give the DSL Advantages Always on Flat fee & Reliable Requires no new wiring. Will run over the standard phone wiring in your house. SNSCT Department of Computer Science & Engineering (UG&PG) Page 9
OPEN SOURCE TOOLS & COMPONENTS
Does not tie up phone line. A telephone and the computer can share the same physical wire and be used simultaneously. Fixed IP available so you can use it to host your own domain for your practice Can be used to host a web site. Dial-up access when traveling often included
49. Give the DSL Disadvantages Can be tough to switch providers Requires additional hardware (DSL Router) Can be difficult to get installed but this has improved significantly in the past 2 years Works only at the site of installation Limited availability Fast upload speeds are available at an extra cost 50. What is Cable? Cable access to the Internet is provided by many cable TV companies and is the preferred method for high-speed access to the Internet from home. Runs over cable TV wiring Installed by cable company Download speeds of 768K to 3M and higher Upload speeds slower. These can vary from 256K up to 384K Always on Shared bandwidth. Just like the freeway, the more people who are trying to get somewhere, the slower it is. Unlimited use with Internet access (ISP) included in cost Costs about $50 per month 51. Give the Advantage of Cable Usually quite fast Always on in most installations Flat fee Somewhat reliable but this varies considerably Broader availability Does not interfere with TV 52. Give the Disadvantage of Cable Shared bandwidth. The more people that are using it, the slower it is but even at its worst it is much faster than a modem. Requires additional hardware (cable box) Works only at the site of installation Upload slower than download No choice in cable company or ISP when selecting service Dial-up access when traveling usually not included 53. Define Satellite Available from remote locations Available from two companies Direcway (www.direcway.com) (Windows only) and Starband (www.starband.com) Downloads up to 1M. Upload via up-link. Uplink speeds 100K SNSCT Department of Computer Science & Engineering (UG&PG) Page 10
OPEN SOURCE TOOLS & COMPONENTS
Unlimited service $70/month. Hardware $500 for single Windows 98SE or newer machine, installation extra. Networked computers (Macm Win, Linux, Unix) unlimited service $150/month. Hardware $600
54. Give the Satellite Advantages Available from anyplace that has a view of the southern sky Always on Unlimited access 55. Give the Satellite Disadvantages Hardware and installation costs Monthly service fee Shared bandwidth. Speeds get slower as more users install the system Can be slow when using a Virtual Private Network (VPN) 56. What is Dedicated Leased Line A fixed digital connection with the phone company Bidirectional Internet access at guaranteed speeds Speeds range from 56K to T1 (1.5M) on up Always on, unmetered ISP separate charge Fees 56K $80/month + ISP $300/m. 1.5M T1 $250/m + ISP $1500/m 57. Give the Leased Line Advantages The most reliable connection to the Internet Guaranteed bandwidth and service levels Great for hosting a web site or for managing your own security and firewalls 56K lines available anyplace there is a telephone 58. Give the Leased Line Disadvantages Expensive T1 and higher access confined to metro. Extremely expensive in rural areas Difficult to get installed Not easy to switch ISPs Requires dedicated hardware 59. What are the ways to Sharing an Internet Connection? There are many ways to share an Internet connection among several machines. This technique has been around for years but has only recently become accessible to the average user. With the proper tools, one can have any number of machines share the same dial-up, DSL or Cable connection. 60. What way to Sharing a Dial-up connection and give the advantage & disadvantage Sharing a telephone line with any style of computer can easily be done with any number of products. The Apple Airport Base Station was the first to make this available to the consumer while other products such as the Lucent Orinoco RG-1000 are designed to work with any platform. Computers connect to the dial-up Internet via a local wired ethernet or wireless Wi-Fi network. SNSCT Department of Computer Science & Engineering (UG&PG) Page 11
OPEN SOURCE TOOLS & COMPONENTS
61. List the Sharing a Dial-up Connection Advantages and disadvanges. Advantages Cheap Uses only one phone line for all the machines on the LAN (Local Area Network) Any number of computers can be on the Internet at the same time Machines on the LAN are invisible to the Internet at large Disadvantages Slow. Same problems as POTS: connecting is slow and downloading is slow Speed slows as more attempt to use the line at the same time 62. Define Sharing a DSL or Cable Line and give the advantage & disadvantage Sharing a DSL or cable connection can be done with any number of products called Cable-DSL routers. Two manufacturers are Linksys and Asante. These products, which start at about $80, connect to your cable or DSL box supplied by your broadband provider and establish a connection with the ISP as if it were a computer. They then create an internal network (Local Area Network or LAN) that allows your machines to share that one Internet connection and to connect with each other. Machines on the LAN are behind a firewall. A specific machine on the LAN can be assigned as a web server, a secure mail server, an FTP server, or some other service and any requests from the Internet will be passed through the firewall to that machine. 63. Discuss about Sharing a DSL or Cable Line Advantages & Disadvantages. Advantages Always on Uses only one DSL or cable connection Any number of computers can access the Internet simultaneously Machines on your LAN (Local Area Network) are invisible to the Internet at large One of the machines on your LAN can be assigned to function as a web server for both your LAN and the Internet Disadvantages Requires extra hardware Requires a network
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 12
OPEN SOURCE TOOLS & COMPONENTS
Part-B 1. Explain the overview of Free/Open Source Software. 2. Explain History of GNU/Linux and the Free Software Movement. 3. Explain the advantages of Free Software and GNU/Linux, FOSS usage. 4. Explain GNU/Linux OS installation-- detect hardware, configure disk partitions & file systems and install a GNU/Linux distribution? 5. Basic shell commands - logging in, listing files, editing files, copying/moving files, viewing file contents, changing file modes and permissions 6. Explain about process management 7. Explain in detail i. ii. iii. User and group management File ownerships and permissions PAM authentication
8. Explain some common system configuration files & log files. 9. Explain about Configuring networking, basics of TCP/IP networking and routing? 10. Explain about connecting to the Internet through i. ii. iii. iv. Dialup DSL Ethernet Leased line.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 13
OPEN SOURCE TOOLS & COMPONENTS
UNIT II Part A 1. Mention some distributions of Linux. Corel Linux Debian GNU/Linux OpenLinux (Caldera) Red Hat Slackware SuSE TurboLinux
2. What is the hardware requirements need for installing the LINUX? CPU Main memory Optical Drive Graphic card Hard Drive Sound Card 3. Give steps for Configuring Linux System. Selecting a language Choosing automatic or manual partitioning Type of software to install Choosing which drive to boot from Adjusting the time settings Configuring the hardware aspect of the system Creating the root password (for the Administrator), and user accounts Hardware configuration 4. Define IMAP? IMAP is an Internet Message Access Protocol. It is a method of accessing electronic mail messages that are kept on a possibly shared mail server. In other words, it permits a "client" email program to access remote message stores as if they were local. For example, email stored on an IMAP server can be manipulated from a desktop computer at home, a workstation at the office, and a notebook computer while travelling, without the need to transfer messages or files back and forth between these computers. IMAP uses TCP/IP port 143. 5. Define POP Short for Post Office Protocol, a protocol used to retrieve e-mail from a mail server. Most e-mail applications (sometimes called an e-mail client) use the POP protocol, although some can use the newer IMAP (Internet Message Access Protocol). There are two versions of POP. The first, called POP2, became a standard in the mid-80's and requires SMTP to send messages. The newer version, POP3, can be used with or without SMTP. POP3 uses TCP/IP port 110. SNSCT Department of Computer Science & Engineering (UG&PG) Page 14
OPEN SOURCE TOOLS & COMPONENTS
6. Differentiate POP3 VS IMAP With IMAP, all your mail stays on the server in multiple folders, some of which you have created. This enables you to connect to any computer and see all your mail and mail folders. In general, IMAP is great if you have a dedicated connection to the Internet or you like to check your mail from various locations. With POP3 you only have one folder, the Inbox folder. When you open your mailbox, new mail is moved from the host server and saved on your computer. If you want to be able to see your old mail messages, you have to go back to the computer where you last opened your mail. With POP3 "leave mail on server" only your email messages are on the server, but with IMAP your email folders are also on the server. 7. What are the two things used in Secure Socket Layer The leading security protocol on the Internet. Developed by Netscape, SSL is Widely used to do two things: 1. To validate the identity of a Web site 2. To create an encrypted connection for sending credit card and other Personal d 8. Define Maildir Maildir is a widely-used format for storing e-mail that does not require applicationlevel file locking to maintain message integrity as messages are added, moved and deleted. Each message is kept in a separate file with a unique name. All changes are made using atomic filesystem operations so that the filesystem handles file locking concurrency issues. A Maildir is a directory (often named Maildir) with three subdirectories named tmp, new, and cur. 9. What are the common files in User Management? /etc/passwd /etc/group /etc/shadow /etc/samba/smbusers 10. What is SMTP? Simple Mail Transfer Protocol (SMTP) is used to transfer mail between Mail Servers over Internet The de facto standard for e-mail transmissions across the Internet It is defined in RFC 821 It is a relatively simple, text-based protocol Not entirely secure thus vulnerable to SPAM 11. What Status Codes responds with SMTP? The Server responds with a 3 digit code that may be followed by text info, o 2## - Success o 3## - Command can be accepted with more information o 4## - Command was rejected, but error condition is temporary o 5## - Command rejected, Bad User!
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 15
OPEN SOURCE TOOLS & COMPONENTS
12. What Problems occur with SMTP SERVER? No inherent security o Authentication o Encryption Only uses NVT (Network Virtual Terminal) 7-bit ASCII format 13. What is Samba?? Samba is an Open Source Suite that provides seamless file and print services to SMB/CIFS clients. Samba is freely available. With Samba, you can share a Linux file system with Windows 95, 98, 2000 and NT and vice versa. You can also share printers connected to either Linux or a system with Windows 95, 98, 2000 or NT. Samba enables a Linux or Unix server to function as a file server for client PCs running Windows software. 14. What is SMB? SMB stands for Server Message Block. It is a protocol by which a lot of PC-related machines share files and printers and other information such as lists of available files and printers. Operating systems that support this natively include Windows NT, OS/2, and Linux. 15. What is CIFS? CIFS Common Internet File System is a protocol that is basically an updated SMB.
16. Give the Components of SMB smbd daemon: This provides the file and print services to SMB clients such as Windows NT or other Linux or Unix clients. smb.conf: This is the configuration file for smbd. nmbd daemon: This daemon provides NetBIOS nameserving and browsing support. smbclient: This is an smb client program that implement a simple FTP-like client on a Linux or Unix box. smbmount: This mounting program enables mounting of server directories on a Linux or Unix box. testparm: This utility is used to test the smb.conf configuration file. smbstatus: This programs lists the current Samba connections. SWAT: Swat allows a Samba administrator to configure the smb.conf file via a Web browser. smbpasswd: This allows the user to change the password used for their SMB sessions
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 16
OPEN SOURCE TOOLS & COMPONENTS
17. Give the most popular e-mail server The most popular is Send mail. Send mail supports POP3, IMAP4, and SMTP. Send mail is configured by editing sendmail.cf. It has a reputation as being very difficult to fine tune. Another popular mail server is Postfix. Postfix was designed to be a simpler to administer alternative to send mail. 18. What way to share the Linux files? NFS is primarily used to share files with other Linux clients. Linux clients can mount an NFS share as a directory within their local file system. SAMBA is primarily used to share files and printers with Windows clients.
19. Define DHCP? DHCP (Dynamic Host Configuration Protocol) is a network service that enables clients to obtain network settings (IP Address, Subnet Mask, Default Gateway, DNS Server, Hostname and Domain) automatically from a central server The DHCP client sends a broadcast request to find the DHCP server and the DHCP server in the subnet responds with an IP address (and other common network parameters) from a pool of IP addresses The IP address can be bound to the MAC address of the client
20. What is process in LINUX? Processes are created in a hierarchical structure whose depth is limited only by the virtual memory available to the virtual machine A process may control the execution of any of its descendants by suspending or resuming it, altering its relative priority, or even terminating it Termination of a process by default causes termination of all its descendants; termination of the root process causes termination of the session Linux assigns a process ID (PID) to the process
21. Define Daemons. Background processes for system administration are referred to as daemons These processes are usually started during the boot process The processes are not assigned any terminals 22. Why is IP Masquerading HOT? Demand to share a single Internet address across multiple machines. Demand to save Internet IPv4 address space. Demand for better internal network security.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 17
OPEN SOURCE TOOLS & COMPONENTS
23. Can you distinguish on PID & PPID? PID 1. A process ID is a unique identifier assigned to a process while it runs 2. Each time you run a process, it has a different PID (it takes a long time for a PID to be reused by the system) 3. You can use the PID to track the status of a process with the ps command or the jobs command, or to end a process with the kill command PPID 1. A process that creates a new process is called a parent process; the new process is called a child process 2. The parent process (PPID) becomes associated with the new child process when it is created
3. The PPID is not used for job control
24. What is a main objective of file sharing? File sharing lets you share files on your machine with others on the Network File sharing also lets you access files that are shared by others File services enable organizations to create and maintain central data stores File servers also allow complex access control to be applied to the data Stored on the server - so that only those who should have access to the data Can access it A file server could be used to share data with a Windows network or a Linux / UNIX network - Linux contains software to do both these things 25. Give two File sharing services on Linux. 1. Linux-with-Linux files sharing 2. Linux-with-Windows file sharing 26. Why we need SAMBA? Samba can be used with Linux to provide transparent access between Machines running Linux and machines running Windows. The basic architecture of Samba is that Samba itself runs on a Linux machine and makes shared files and printers available to Windows' machinesthe Windows machines see the shares on the Linux machine in the same way Windows machines see shares on other Windows machines or Windows servers. 27. List any 3 practical applications of SAMBA. Using a Linux server as a simple peer-to-peer server Using a Linux server as a member server on an existing Windows NT o Domain that has an existing domain controller Using a Linux server as a primary domain controller
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 18
OPEN SOURCE TOOLS & COMPONENTS
28. How to Test the Samba from Windows? Log into the machine as a local user Open up Network Neighbourhood and browse the complete network Locate the Workgroup that youve setup on your Linux machine and Click on it Inside this, select the machine that you want to use and test out It will prompt you for a password and then show you the shares that you Have defined in the Samba server Try doing some operations on the share to validate whether the access Control is happening correctly or not 29. How to manage the SAMBA users? Samba can only authenticate users against passwords stored in its own Database; it can not authenticate users again the Linux passwd file.However, it is necessary to have a mapping between Linux system users and Samba users - for each Samba user, a valid system user with the same name should also exist; otherwise Samba will not be able to lookup the user. 30. What is NFS? NFS is a file sharing protocol primarily used on the Linux/Windows world. It is completely transparent for a user or application - there is no change in the way a user or application would access a file on disk or over NFS. NFS is commonly implemented over UDP; it depends on RPC to perform most of its functions. On Debian, the NFS server package is called: nfskernel- server. Installing this package will install NFS on your Linux system. 31. What are things needs during sending the E-mail? Mail-Boxes User Agents Transfer-Agents Delivery agents Mailing lists and Aliases 32. List the features of SMTP. SMTP which stands for Simple Mail Transfer Protocol is the de facto standard for email receipt and delivery. SMTP used TCP/IP protocol to exchange email messages between two MTAs via intermediate MTAs using store and forward principle. Many SMTP servers are available for Linux such as Sendmail, Postfix, qmail, Exim. Today SMTP servers not only accept, relay and deliver email, but also perform other functions like Authentication, SPAM filtering and Access Control 33. What is the Role of DNS in Mail Delivery? DNS plays a very important role in delivering email Mail eXchanger (MX) records are Maintained by domain name servers (DNS) to tell MTAs where to send mail messages.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 19
OPEN SOURCE TOOLS & COMPONENTS
34. How mail is delivered? Mail client connects to the SMTP server saying that it has an email to send SMTP server authenticates the client to ensure that it is allowed to relay Through it SMTP server accepts the message and gives a success code to the mail Client as well as a message ID SMTP server checks the recipient(s) of the message and does a local Delivery if the recipient(s) are local; if the recipient(s) are not local, then the SMTP server initiates a remote mail delivery SMTP server connects to the remote mail server and tries to deliver the email Remote mail server authenticates the delivery and accepts the email if it is Authorized to receive email for the recipient(s) The remote mail server delivers the email to the recipient(s) mailbox Recipient(s) open the mailbox (using protocol like IMAP or POP3 or Locally on the shell) and read the email. 35. What are the Features of LINUX Printers? All printing systems on Linux make use of the excellent PostScript system called GhostScript (www.ghostscript.org). Ghostscript is a PostScript interpreter that is most commonly used on Linux Implements an excellent PostScript engine that can take as inputs formats like JPEG, TIFF, PS & Text and output data in formats like X Windows output, Raster formats and PDF Also handles conversion of PS output for non-PS printers; can also be used a basic, Spooler less printing system Most printing systems today use a combination of multiple tools (postscript I nterpreters, filters, rasterisers etc) to process and print documents The printing system converts PostScript into a raster format and then converts that into a printer specific language to send commands to the printer 36. Define CUPS. CUPS (Common Unix Printing System) uses IPP/1.1 to provide a complete, modern printing system for UNIX that can be extended to support new printers, devices, and protocols while providing compatibility with existing UNIX applications. CUPS is free software provided under the terms of the GNU General Public License and GNU Library General Public License 37. List the Features of CUPS. IPP/1.1 Support Supports banner pages, authentication, print accounting and quota Supports parallel, serial, usb, IPP and JetDirect-based printers as also printers shared Through other printing systems such as CUPS, lpd and Windows TLS (encryption) support Portable command set compatible with LPRng and LPD Excellent web-based interface for printer administration, configuration And management PPD-based drivers, rich API and imaging libraries Foomatic Printer database (from linuxprinting.org) has good support for CUPS SNSCT Department of Computer Science & Engineering (UG&PG) Page 20
OPEN SOURCE TOOLS & COMPONENTS
38. What is the use of Sharing Printers? Sharing printers is very easy with CUPS As long as network browsing support is enabled correctly in the configuration files, the Printers on other machines will be detected automatically This simplifies the mapping of printers in a network you just have to configure the Printer in one machine and as long as all other machines support and enable the CUPS Browse protocol, the configured printer will automatically show-up in the n/w nodes. On the server where the printer is configured, you may wish to introduce a separate section to allow only specific machines to print to the attached printer 39. Define Proxy Server. A web proxy server is a useful service to have on your network, or between your network and the Internet, as it provides an extra security layer that insulates your users from the Internet. A proxy server can also act as a cache, allowing users to share downloads transparently and speeding up Internet access, especially for frequently used files. 40. Define Squid? Squid is a high performance and relatively secure web proxy server that includes good Caching facilities. It is one of the most commonly used proxy servers on the Internet. 41. List the salient features of Squid . It is the leading caching proxy server performance, reliability, versatility and scalability. 42. What is Caching Proxy? A caching proxy is a server, which sits between web browsers, such as Netscape or Internet Explorer and remote web sites. The proxy stores local copies of files as they are downloaded, and if a file is requested that has already been downloaded the local copy is supplied, rather than repeating the download. This save money (sometimes) and bandwidth (always). 43. Can you discuss the Squid supports? o proxying and caching of HTTP, FTP, and other URLs o proxying for SSL o Cache hierarchies o ICP, HTCP, CARP, Cache Digests o Transparent caching o WCCP (Squid v2.3 and above) o Extensive access controls o HTTP server acceleration o SNMP o caching of DNS lookups
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 21
OPEN SOURCE TOOLS & COMPONENTS
Part - B 1. Explain configuring additional hardware such as i. ii. iii. iv. v. vi. Sound cards Displays & display cards Network cards modems USB drives CD writers
2. Explain about Understanding the OS boot up process? 3. Explain performing every day tasks using gnu/Linux i. Accessing the Internet ii. Playing music iii. Editing documents and spreadsheets iv. Sending and receiving email v. Copy files from disks and over the network vi. Playing games vii. Writing CDs 4. Explain: X Window system configuration and utilities i. Configure X windows ii. Detect display devices 5. Installing software from source code as well as using binary packages. 6. Explain: Setting up email servers i. using postfix (SMTP services) ii. courier (IMAP & POP3 services) iii. squirrel mail ( web mail services) 7. Explain: Setting up web servers using apache (HTTP services) 8. Explain and give an example program for php (server-side scripting)? 9. What is perl (CGI support)? 10. Explain about Setting up file services -- using samba and NFS? 11. Setting up proxy services -- using squid? 12. Setting up printer services - using CUPS and foomatic?
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 22
OPEN SOURCE TOOLS & COMPONENTS
UNIT III Part A 1. List the types of FIREWALLS. packet-filtering firewall, application gateway (screened-host firewall) Proxy firewall (application level circuit gateway). 2. Define Networks Firewalls. A network firewall protects your computer from attacks or intrusions from malicious crackers in the network. 3. List three levels of network firewall security. Highly secure firewall Medium grade secure firewall: No firewall 4. What are Rules we need remember while install in Linux? IP Address of Source (Allow from Trusted Sources) IP Address of Destination (Allow to trusted Destinations) Application Port Number (Allow Mail but restrict Telnet) Direction of Traffic (Allow outgoing traffic but restrict incoming traffic) 5. HOW to test the Network Connections? To test the network connection, use the ping command If no lines appear, networking is not configured or activated on your system To test your network adapter card configuration, use the ping command followed by an IP address You can run the net utility in Red Hat Linux to configure your networking card 6. What is a Desktop Manager? The roll of the Desktop Manager is to provide you with the ability to manage all of the details of your system that would otherwise require you to type in a bunch of commands in a terminal window. These details include managing your files, launching programs, configuring various aspects of your system, etc. 7. What is GNU DEBUGGER? o How gdb debugs? o GDB commands o Getting Started o Stepping through code o Breakpoints and Watchpoints o Setting variables o Backtrace and Changing Frames o Handling Signals o Debugging Programs SNSCT Department of Computer Science & Engineering (UG&PG) Page 23
OPEN SOURCE TOOLS & COMPONENTS
8. Define Debugger a program that helps in locating and correcting o programming errors. A tool used by a programmer to identify and fix bugs in a program A debugger is a program which runs other programs in such a way as to let you see every step of program execution. A debugger will let you stop the program while it is running, change the program or program variables, and start the program running again. is the most popular debugger for unix systems to debug C and C++ programs. helps you to find out o Statement or expression which causes crash o Values of program variables at a particular point during execution of program o Result of particular expression 9. How GDB Debugs? Run the program up to certain point and stop Print the values of variables at that point Step through the program one line at a time Printout the values of each variable after executing each line.
10. Define Fire Wall
Firewall is a system designed to prevent unauthorized access to or from a private Network. A firewall is a system or router that sits between an external network (i.e. the Internet) and an internal network. A firewall has two network connections, one for the external network and one for the internal network. Firewalls can be implemented in both hardware and software, or a combination of both. All messages entering or leaving the intranet pass through the firewall, which examines each message and blocks those to meet the specified security criteria. A firewall protects your network from unwanted Internet traffic. The primary functions of a firewall are to let good traffic pass through while bad traffic gets blocked. 11. Define hardware and software firewall? A hardware firewall is the most secure version and would be used by large companies to protect their networks from outside attack from the internet. A software firewall is more suited to a personal computer or SME (small to medium sized enterprise) and is much cheaper. (Free in the example below). 12. What task perform both h/w & s/w firewall? Positive Effects User authentication Auditing and logging Security SNSCT Department of Computer Science & Engineering (UG&PG) Page 24
OPEN SOURCE TOOLS & COMPONENTS
Negative Effects Traffic bottlenecks Single point of failure
13. What are the Types of Firewall?
Packet filter Stateful packet inspection Application gateway/proxy
14. Define Packet filter
Each packet passes is examined and information contained in the header is compared to a pre-configured set of rules or filters. An allow or deny decision is made based on the results of the comparison. A packet filtering firewall is often called a network layer firewall because the filtering is primarily done at the network layer (layer three) or the transport layer (layer four) of the OSI reference model.
15. Write the packet filtering rules Packet filtering rules or filters can be configured to allow or deny traffic based on one or more of the following variables Source IP address,Destination IP address Protocol type (TCP/UDP) Source port, Destination port 16. List the Strengths & weakness of packet filter Strength Faster than other packet screening methods have very little impact on overall network performance Packet filtering firewalls less expensive can be implemented transparently Weakness There are three common exploits to which packet filtering firewalls are susceptible. IP spoofing, Buffer overruns, ICMP tunneling. It allows a direct connection to be made between the two endpoints. 17. Define Stateful Packet Inspection Stateful packet inspection uses the same fundamental packet screening technique that packet filtering does. In addition, it examines the packet header information from the network layer of the OSI model to the application layer to verify that the packet is part of a legitimate connection and the protocols are behaving as expected. This method can make decisions based on one or more of the following: Source IP address, Destination IP address Protocol type (TCP/UDP) Source port, Destination port & Connection state
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 25
OPEN SOURCE TOOLS & COMPONENTS
18. Give the strengths and weakness of Stateful Packet Inspection Strengths More secure than basic packet filtering Have logging capabilities Weakness Rules and filters in this packet screening method can become complex, hard to manage, prone to error and difficult to test. It allows a direct connection to be made between the two endpoints. 19. Write Application gateway/proxy This type of firewall operates at the application level of the OSI model. For source and destination endpoints to be able to communicate with each other, a proxy service must be implemented for each application protocol. The gateways/proxies are carefully designed to be reliable and secure because they are the only connection point between the two networks. When a client issues a request from the untrusted network, a connection is established with the application gateway/proxy. The proxy determines if the request is valid (by comparing it to any rules or filters) and then sends a new request on behalf of the client to the destination. By using this method, a direct connection is never made from the trusted network to the untrusted network and the request appears to have originated from the application gateway/proxy. The request is answered in the same manner. The response is sent back to the application gateway/proxy, which determines if it is valid and then sends it on to the client. By breaking the client/server model, this type of firewall can effectively hide the trusted network from the untrusted network. 20. List the Strengths & weakness of Application gateway/proxy Strengths Do not allow a direct connection to be made between endpoints Do not route between networks keeps the internal network separate from the external one More control over traffic passing through the firewall Offer robust user authentication It has extensive logging capabilities Weakness Slower than packet filtering methods Each protocol (HTTP, SMTP, etc.) requires its own gateway/proxy application Require additional client configuration Performance typically degrades when the number of clients increases 21. What is netfilter/iptables Netfilter and iptables are building blocks of a framework inside the Linux 2.4.x and 2.6.x kernel. This framework enables packet filtering, network address and other packet mangling. Improved successor of the previous ipchains and Linux 2.0.x ipfwadm systems. Netfilter is a set of hooks inside the Linux kernel that allows kernel modules to register SNSCT Department of Computer Science & Engineering (UG&PG) Page 26
OPEN SOURCE TOOLS & COMPONENTS
Callback functions with the network stack. A registered callback function is then called back for every packet that traverses the respective hook within the network stack. Iptables is a generic table structure for the definition of rule sets. Each rule within an IP table consists of a number of classifiers (iptables matches) and one connected action (iptables target). Netfilter, iptables and the connection tracking as well as the NAT subsystem together build the whole framework.
22. Write the Applications of Iptables Build internet firewalls based on stateless and stateful packet filtering Use NAT and masquerading for sharing internet access if you don't have enough public IP addresses. Use NAT to implement transparent proxies Aid the tc and iproute2 systems used to build sophisticated QoS and policy routers Do further packet manipulation (mangling) like altering the TOS/DSCP/ECN bits of the IP header 23. Write the IPTables command options There are three built-in tables in the Linux kernel's netfilter, and each has built-in chains. the iptables command is used to configure these tables. 1. Filter A table that is used for routing network packets. This is default table, and is assumed by iptables if the -t parameter is not specified. INPUT Network packets that are destined for the server. OUTPUT Network packets that originate on the server. FORWARD Network packets that are routed through the server. 2. Nat A table that is used for NAT. NAT is a method of translating internal IP address To external IP addresses. PREROUTING- network packets that can be altered when they arrive at the server. OUTPUT- Network packets that originate on the server POSTROUTING Network packets that can be altered right before they are sent out. 3. Mangle A table that is used for altering network packets. INPUT Network packets that are destined for the server. OUTPUT Network packets that originate on the server. FORWARD Network packets that are routed through the server. PREROUTING- network packets that can be altered when they arrive at the server. POSTROUTING Network packets that can be altered right before they are sent out. Commands tell IPTables to perform a specific action, and only one command is allowed per iptables command string. Except for the help command, all Commands are written in upper-case characters. 24. Define Proxy Server A web proxy server is a useful service to have on your network, or between your network and the Internet, as it provide an extra security layer that insulates your users from the Internet. A proxy server can also act as a cache, allowing users to share SNSCT Department of Computer Science & Engineering (UG&PG) Page 27
OPEN SOURCE TOOLS & COMPONENTS
downloads transparently and speeding up Internet access, especially for frequently used files. 23. Define GNU RCS (Revision control System). GNU RCS (Revision Control System) manages multiple revisions of files. RCS can store, retrieve, log, identify, and merge revisions. It is useful for files that are revised frequently, e.g. programs, documentation, graphics, and papers. It can handle text as well as binary files, although functionality is reduced for the latter. 24. What is NAT? NAT allows an Internet Protocol (IP) network to maintain public IP addresses separately from private IP addresses. NAT is a popular technology for Internet connection sharing. It is also sometimes used in server load balancing applications on corporate networks. 25. What is the use of Diff command? Diff - find differences between two files In the simplest case, diff compares the contents of the two files from-file and to-file. A file name of - stands for text read from the standard input. As a special case, diff - compares a copy of standard input to itself.
Part - B 1. Explain about Setting up a firewall - Using netfilter and ip tables.
2. Explain about using the GNU Compiler Collection GNU compiler tools i. The C preprocessor (cpp) ii. The C compiler (gcc) iii. The C++ compiler (g++) iv. Assembler (gas). 3. Explain about understanding build systems : i. Constructing make files and using make ii. Using autoconf and autogen.
4. Explain about using source code versioning and management tools - using CVS to manage source code revisions, patch & diff. 5. Discuss the CVS.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 28
OPEN SOURCE TOOLS & COMPONENTS
UNIT IV Part - A 1. What is Apache Web Server? The Apache Geronimo v3.0-beta-1 - Leading Open Source Application Server Now Certified Java EE 6 Full- and Web Profile Compatible. Flexible, modular, and easy to manage, Apache Geronimo is the ideal platform for lightweight server deployments to full-scale enterprise environments, with complete support for Java EE... 2. Define CGI. CGI refers to the Common Gateway Interface, and is the most common method of executing external programs or scripts on the server side to generate content. Even things like PHP make use of the concepts of CGI to perform their functions and features. CGI can also be your worst security nightmare, so use it carefully, and pay close attention to your server configuration. Probably the best instructions on enabling CGI in Apache ever written are the CGI HOWTO included with the Apache documentation. 3. What is SSI? SSI Server Side Includes (SSI) allows for an easy way to include right in the middle of a web page such things as file modification time, values of environment variables, current date and time, and even the output of programs and scripts. 4. What is MDA? Model Driven Architecture is a new way of writing specifications and developing applications, based on a platform independent model (PIM).[OMG] 5. What are the features of Model Driven Architecture? A New Way to Specify and Build Systems Based on modeling with UML Supports full lifecycle: analysis, design, implementation, deployment, maintenance, evolution & integration with later systems Builds in Interoperability and Portability Lowers initial cost and maximizes ROI 6. List the Goals of MDA Speeding up the development process Increasing the quality of software Central error correction Increasing the re-use Reducing complexity through abstraction
7. What are the models of MDA? Computation Independent Model (CIM) Platform Independent Model (PIM) Platform Specific Model (PSM)
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 29
OPEN SOURCE TOOLS & COMPONENTS
8. Distinguish the advantages and disadvantages of MDA advantages Reduces the complexity of a system Allows easy adaptation to new technologies Standardization allows integration between different tools Simple models allow easier communication with the customer Automatic code generation disadvantages Manual changes in code Manual changes in lower level models How optimized will the generated code be Still unresolved standard issues Increased complexity of the modeling languages
9. Give some of the tools in MDA. Open-source : AndroMDA, Kermeta, MOFScript, ModFact, OpenMDX, XDoclet, OOMEGA 10. What are the benefits of using MDA? o Portability o Cross-platform Interoperability, o Platform Independence, Productivity 11. List the four principles from the OMG's view of MDA. Models expressed in a well-defined notation are a cornerstone to understanding systems for enterprise-scale solutions. The building of systems can be organized around a set of models by imposing a series of transformations between models, organized into an architectural framework of layers and transformations. A formal underpinning for describing models in a set of metamodels facilitates meaningful integration and transformation among models, and is the basis for automation through tools. Acceptance and broad adoption of this model-based approach requires industry standards to provide openness to consumers, and foster competition among vendors. 12. Why should we use MDA? MDA allows you to model the functionality and behavior only once.Therefore saves a lot of time.E.g. Carphone Warehouse were using Uniface Software and now are switching to Java.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 30
OPEN SOURCE TOOLS & COMPONENTS
13. Differentiate between model and Meta model
Model
a description or analogy used to help visualize something that cannot be directly observed models are used for describing, visualizing, and observing models describe a system from different viewpoints, for different stakeholders, at different levels of abstraction
Meta model
Metamodels describe models (i.e., metamodel instances) allowed metaelements, their properties and relationships well-formedness rules for the instantiated models in essence, an abstract syntax for models!
14. List an Adopted technologies in Object Management Group (OMG). Model Driven Architecture (MDA) Meta-Object Facility (MOF) Unified Modeling Language (UML) XML Metadata Interchange (XMI) Common Warehouse Metamodel (CWM) Common Object Request Broker Architecture (CORBA) 15. Define MOF. MOF(The Meta-Object Facility) defines an abstract language and a framework for specifying, constructing, and managing technology neutral metamodels (e.g. UML, MOF itself) 16. What is MOF specification? A formal definition of MOF meta-metamodel Abstract language for specifying MOF metamodels A mapping from arbitrary MOF metamodels to CORBA IDL Produces IDL interfaces for managing metadata A set of reflective CORBA IDL interfaces For representing and managing MOF metamodels An XMI format for MOF metamodel interchange 17. Differences between MOF and UML. MOF Binary associations No AssociationClasses or Qualifiers Direct References Generalization and Dependency are Associations No support for templates Subset of CORBA primitive data types and constructors UML N -ary associations AssociationClass, Qualifier Navigation through Associations Generalization and Dependency are metaclasses Template metaclass No CORBA awareness
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 31
OPEN SOURCE TOOLS & COMPONENTS
18. List the features of MOF MOF offers metamodeling and a metadata architecture implementation an industry standard support for existing and upcoming technologies aligned with UML a single reference point throughout the enterprise 19. Define the services provided by Web server. Web server: A webserver is a computer system that delivers web pages. Every web server has an IP address and possibly a domain name. for example an URL: http://www.niceindia.com/index.html in our browser. This sends a request to the server whose domain name is niceindia.com. the server fetches the page named index.html and sends back to our browsers. 20. What is Distributed Computing Environment? The Distributed Computing Environment is a set of standard pioneered by the open software foundation (OSF), includes a standard for RPC. Although the DCE standard has been around for some time, and was probably a good idea, it has never gained wide acceptance and exists today as little more than an historical curiosity.
21. What is patch file? Linux and UNIX source software often comes with security and other patches. Patch takes a patch file patchfile containing a difference listing produced by the diff program and applies those differences to one or more original files, producing patched versions. Normally the patched versions are put in place of the originals.
Part - B 1. 2. 3. 4. 5. How to configure of Apache web server? Explain the Model Driven Architecture? Make a comparison with Apache web server and IIS server. List the Features of Meta Object facility. Discuss the concept of UML.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 32
OPEN SOURCE TOOLS & COMPONENTS
UNIT V Part - A 1. Discuss the Basics of the X Windows server architecture. X was designed with a client-server architecture. The applications themselves are the clients; they communicate with the server and issue requests, also receiving information from the server. The X server maintains exclusive control of the display and services requests from the clients. At this point, the advantages of using this model are pretty clear. Applications (clients) only need to know how to communicate with the server, and need not be concerned with the details of talking to the actual graphics display device. At the most basic level, a client tells the server stuff like "draw a line from here to here", or "render this string of text, using this font, at this position onscreen".
2. Define Window Managers Window managers: The metaphor of desktop is important for a user. By analogy, a user may choose to activate one of the tasks from many on his desk. The window managers are designed to provide this illusion. In other words, a window manager (WM in short) must provide facilities that can support such desk-oriented operation from the view on the screen. 3. List some X-Clients and its functionalities xclock: A clock display. It is possible to have a numerical or an analog display for the current time. xbiff: A Berkeley support program that displays mail status with a flag up, to Show the arrival of a new mail. xterm: It provides a user with a new terminal window. With -C option the window can receive and display console messages. 4. What Is Thin-Client/Server Computing? The thin-client/server computing model involves connecting thin-client software or a thin-client hardware device with the server side using a highly efficient network protocol such as Citrix's ICA. The thin-client/server architecture enables 100 percent server-based processing, management, deployment, and support for missioncritical,productivity, Web-based, or other custom applications across any type of connection to any type of client hardware, regardless of platform. The client hardware can include Windows-based terminals, PCs, NetPCs, network computers, Apple Macintosh computers, or UNIX devices. 5. Define Qt Programming. Qt is a library of C++ GUI application development software. Its purpose is to provide everything needed to develop the user interface portion of applications. It does this primarily in the form of a collection of C++ classes.
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 33
OPEN SOURCE TOOLS & COMPONENTS
6. Give silent features of Qt Programming. A Qt program is created by having the mainline of the program create a QApplication object and use it to control the windows. A KDE program is formed the same way, using a KApplication object. The main window of an application is a single widget. This widget normally Contains a collection of other widgets that display information and supply the user interface. An object can be written to broadcast one or more signals. An object can also contain one or more slots designed to receive broadcast signals. The implementation details of slots and signals are automated through the use of macros and the MOC compiler. 7. What is the purpose of Qt? Cross platform applications built from one source Builds native applications with native look and feel Easy to (re)use API, high developer productivity, openess, fun to use 8. What are the mechanisms in Qt? It contains many of the mechanisms that make up Qt events signals and slots properties memory management 9. What is GTK+, and how can I use it? GTK+, or the GIMP Toolkit, is a multi-platform toolkit for creating graphical user interfaces. Offering a complete set of widgets, GTK+ is suitable for projects ranging from small one-off tools to complete application suites. 10. Where can I use this GTK+? Everywhere! GTK+ is cross-platform and boasts an easy to use API, speeding up your development time. Take a look at thescreenshots to see a number of platforms GTK+ will run. 11. What languages are supported for GTK+ ? GTK+ is written in C but has been designed from the ground up to support a wide range of languages, not only C/C++. Using GTK+ from languages such as Perl and Python (especially in combination with the Glade GUI builder) provides an effective method of rapid application development. 12. Are there any licensing restrictions are for GTK+? GTK+ is free software and part of the GNU Project. However, the licensing terms for GTK+, the GNU LGPL, allow it to be used by all developers, including those developing proprietary software, without any license fees or royalties. Get on overview of GTK+. Understand who started it, the basic architecture and why we use the license we do. GTK+ has been involved in many projects and some big platforms. To get a glimpse of what people think of GTK+ and how it has been used in commercial projects, read the success stories... SNSCT Department of Computer Science & Engineering (UG&PG) Page 34
OPEN SOURCE TOOLS & COMPONENTS
13. List the GTK libraries. o Glib o Pango o ATK o GDK o GdkPixbuf o Cairo
14. Define Signal, Event and Callback. GTK+ library is an event driven system. All GUI applications are event driven. The applications start a main loop, which continuously checks for newly generated events. If there is no event, the application waits and does nothing. In GTK+ an event is a message from the X server. When the event reaches a widget, it may react to this event by emitting a signal. The GTK+ programmer can connect a specific callback to a signal. The callback is a handler function that reacts to a signal.
15. What is GTK+ dialogs? Dialog windows or dialogs are an indispensable part of most modern GUI applications. A dialog is defined as a conversation between two or more persons. In a computer application a dialog is a window which is used to "talk" to the application. A dialog is used to input data, modify data, change the application settings etc. Dialogs are important means of communication between a user and a computer program. 16. Define GTK+ Widgets. Widgets are basic building blocks of a GUI application. Over the years, several widgets became a standard in all toolkits on all OS platforms. For example a button, a check box or a scroll bars. The GTK+ toolkit's philosophy is to keep the number of widgets at a minimum level. More specialized widgets are created as custom GTK+ widgets. 17. Give ant 2 features of GKT+. GTK (GIMP Toolkit) is a library for creating graphical user interfaces. It is licensed using the LGPL license, so you can develop open software, free software, or even commercial non-free software using GTK without having to spend anything for licenses or royalties. GTK is essentially an object oriented application programmers interface (API). Although written completely in C, it is implemented using the idea of classes and callback functions (pointers to functions).
18. What is the Video LAN project? VideoLAN is a complete software solution for video streaming, developed by students of the Ecole Centrale Paris and developers from all over the world, under the GNU General Public License (GPL). VideoLAN is designed to stream MPEG videos on high bandwidth networks. SNSCT Department of Computer Science & Engineering (UG&PG) Page 35
OPEN SOURCE TOOLS & COMPONENTS
19. What are The VideoLAN solutions? VLS (VideoLAN Server), which can stream MPEG1, MPEG2 and MPEG4 files, DVDs, digital satellite channels, digital terrestial television channels and live videos on the network in unicast or multicast, VLC (initially VideoLAN Client), which can be used as a server to stream MPEG1, MPEG2 and MPEG4 files, DVDs and live videos on the network in unicast or multicast ; or used as a client to receive, decode and display MPEG streams under multiple operating systems. 20. What is multicast? Multicast is a norm implemented in all modern network hardware (switches, routers ...). It provides an intelligent manner to send a stream to a dynamic group of machines. If you want to use multicast, make sure that all your network hardware support it. 21. What is a codec? A codec is a compression algorithm, used to reduce the size of a stream. There are audio codecs and video codecs. MPEG1, MPEG2, MPEG4, Vorbis, DivX, ... are codecs A container format contains one or several streams already encoded by codecs. Very often, there is an audio stream and a video one. AVI, Ogg, MOV, ASF, ... are container formats. The streams contained can be encoded using different codecs. In a perfect world, you could put any codec in any container format. Unfortunately, there are some incompatibilities. You can find a matrix of ossible codecs and container formats on the features page 22. How to manipulate the Manipulating X Client Windows? Moving Windows: Moving a window. Resizing Windows: Resizing a window. Destroying Windows: When you don't want a window anymore. Minimizing Windows: Turning a window into an icon. Maximizing Windows: Restoring a window from an icon. 23. How to configure X windows? To Configuring X windows by using these modes Video Modes: Changing video modes and resolutions. Xsession: Running certain clients automatically. Root Window: Changing the root window parameters. Window Managers: The choice of window manager is yours! 24. What is ImageMagick? ImageMagick is a suite of programs that convert and manipulate graphics files from the command line. It is also well suited for batch conversions that is, converting many files at once. In addition, ImageMagick includes PerlMagick, a binding that lets you invoke the ImageMagick utilities from the Perl programming language. It comes with most Linux distributions;
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 36
OPEN SOURCE TOOLS & COMPONENTS
Part-B 1. Explain: X Windows server architecture 2. What is Qt Programming? Explain with example program. 3. Write simple a Qt program for simple window creation. 4. What is Gtk+ Programming? Explain with example program. 5. Write simple a Gtk+ program for simple window creation. 6. Explain Python Programming with examples? 7. Explain Glade: A Visual Designer Tool for GTK, GNOME? 8. Explain Programming GUI applications with localization support? 9. Explain GUI applications with localization support using Qt program? 10. Explain signals and slots?
Prepared By
Prof.T.KALAIKUMARN, Prof/CSE, Mrs.S.DHANALAKSHMI, AP/CSE, Mr.D.PRABAKAR AP/CSE
Verified by
Prof.T.KALAIKUMARN, Prof/CSE,
Reviewed by Dr.S.Karthik, Prof & Head/CSE
Approved By Dr.V.P.Arunachalam Principal
SNSCT Department of Computer Science & Engineering (UG&PG)
Page 37
Вам также может понравиться
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (890)
- The Seasons of Life by Jim RohnДокумент111 страницThe Seasons of Life by Jim RohnChristine Mwaura97% (29)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Aligning With New Digital Strategy A Dynamic CapabilitiesДокумент16 страницAligning With New Digital Strategy A Dynamic Capabilitiesyasit10Оценок пока нет
- Causes of The Renaissance: Silk RoadДокумент6 страницCauses of The Renaissance: Silk RoadCyryhl GutlayОценок пока нет
- Release emotions with simple questionsДокумент10 страницRelease emotions with simple questionsDubravko ThorОценок пока нет
- MATH 8 QUARTER 3 WEEK 1 & 2 MODULEДокумент10 страницMATH 8 QUARTER 3 WEEK 1 & 2 MODULECandy CastroОценок пока нет
- Industrial/Organi Zational Psychology: Alday, Angeli Camille M. - 2P2Документ51 страницаIndustrial/Organi Zational Psychology: Alday, Angeli Camille M. - 2P2SteffanyОценок пока нет
- ST Veronica Giuliani For OFS PresentationДокумент7 страницST Veronica Giuliani For OFS Presentationleo jОценок пока нет
- Bca 503Документ186 страницBca 503Prabhat KumarОценок пока нет
- Scan Conversion Algorithms-2Документ22 страницыScan Conversion Algorithms-2Kartik MakkarОценок пока нет
- Line Circle DrawДокумент63 страницыLine Circle DrawAvinash Kumar100% (1)
- Bca 3 P18 2011Документ6 страницBca 3 P18 2011Prabhat KumarОценок пока нет
- MicroprocessorДокумент7 страницMicroprocessorSulekh SharmaОценок пока нет
- Data Aggregation in Wireless Sensor Network 2010 NandaniДокумент6 страницData Aggregation in Wireless Sensor Network 2010 NandaniPrabhat KumarОценок пока нет
- 1959Документ6 страниц1959Prabhat KumarОценок пока нет
- BrochureДокумент2 страницыBrochurePrabhat KumarОценок пока нет
- Cs 4 BaДокумент6 страницCs 4 BaPrabhat KumarОценок пока нет
- Hope 03 21 22Документ3 страницыHope 03 21 22Shaina AgravanteОценок пока нет
- Liquid Air Energy Storage Systems A - 2021 - Renewable and Sustainable EnergyДокумент12 страницLiquid Air Energy Storage Systems A - 2021 - Renewable and Sustainable EnergyJosePPMolinaОценок пока нет
- ARTS 9 Q4 Week 1Документ3 страницыARTS 9 Q4 Week 1Elaissa MaglanqueОценок пока нет
- Day 2 TaskДокумент4 страницыDay 2 TaskYaathriganОценок пока нет
- Feyzin Oil Refinery DisasterДокумент8 страницFeyzin Oil Refinery DisasterDavid Alonso Cedano EchevarriaОценок пока нет
- Nodelman 1992Документ8 страницNodelman 1992Ana Luiza RochaОценок пока нет
- Vikash Kumar: 1. Aunico India May 2018Документ4 страницыVikash Kumar: 1. Aunico India May 2018Rama Krishna PandaОценок пока нет
- Implementing a JITD system to reduce bullwhip effect and inventory costsДокумент7 страницImplementing a JITD system to reduce bullwhip effect and inventory costsRaman GuptaОценок пока нет
- Manage a micro business with BSB30315Документ3 страницыManage a micro business with BSB30315Theo A W JacksonОценок пока нет
- VIACRYL VSC 6250w/65MP: Technical DatasheetДокумент2 страницыVIACRYL VSC 6250w/65MP: Technical DatasheetPratik MehtaОценок пока нет
- Case Study On Global Branding - DuluxДокумент18 страницCase Study On Global Branding - DuluxAakriti NegiОценок пока нет
- NVH PDFДокумент3 страницыNVH PDFSubhendu BarisalОценок пока нет
- Bronchogenic CarcinomaДокумент13 страницBronchogenic Carcinomaloresita_rebongОценок пока нет
- X TensoqaДокумент2 страницыX TensoqaLeo CabelosОценок пока нет
- Srimanta Shankardev: Early LifeДокумент3 страницыSrimanta Shankardev: Early LifeAnusuya BaruahОценок пока нет
- Goldenberg and Reddy (2017)Документ10 страницGoldenberg and Reddy (2017)Mariana ToniniОценок пока нет
- TG KPWKPДокумент8 страницTG KPWKPDanmar CamilotОценок пока нет
- Plant Processes: Lesson 3Документ3 страницыPlant Processes: Lesson 3Kayla Ta’jaeОценок пока нет
- Film set safety rules for COVIDДокумент12 страницFilm set safety rules for COVIDTanveer HossainОценок пока нет
- Silyzer 300 - Next Generation PEM ElectrolysisДокумент2 страницыSilyzer 300 - Next Generation PEM ElectrolysisSaul Villalba100% (1)
- 4439 Chap01Документ28 страниц4439 Chap01bouthaina otОценок пока нет
- Equivalent Record Form: Department of Education MIMAROPA RegionДокумент1 страницаEquivalent Record Form: Department of Education MIMAROPA RegionEnerita AllegoОценок пока нет
- Advisory Circular: Aircraft Maintenance Engineer Licence - Examination Subject 2 Aircraft Engineering KnowledgeДокумент44 страницыAdvisory Circular: Aircraft Maintenance Engineer Licence - Examination Subject 2 Aircraft Engineering KnowledgejashkahhОценок пока нет