Академический Документы
Профессиональный Документы
Культура Документы
SQL Server Hacking Jeremy Druin Webpwnized
Загружено:
Pankaj KumarИсходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
SQL Server Hacking Jeremy Druin Webpwnized
Загружено:
Pankaj KumarАвторское право:
Доступные форматы
Notes: Database Exploitation/Post Exploitation SQL Server How does SQL Server handle connections? Server vs.
Instance vs. Port vs. Database Where are remote connections configured? SQL Server Connection Manager How does the client know where instances are listening? SQL Browser Service Configuration services.msc SQL Server Connection Manager Recon: Detecting SQL Server (Passive) DNS Hostnames Remediation Scanning: Detecting SQL Server (Active) SQL Server Browser Service (nmap, sqlscan) Metasploit mssql_ping Scapy MS SQL Browser Inquiry (Advanced Workshop) Remediation Browsing SQL Server Microsoft SQL Server Management Studio Microsoft osql.exe (Advanced Workshop) [Remote]: osql -U brokerage_qa -S JEREMY -8GNO9J7F\SQLEXPRESS -P brokerage_qa [Localhost]:osql -U brokerage_qa -S loca lhost\SQLEXPRESS -P brokerage_qa SQL Injection Remediation least-privilege schema-containment application accounts Bruteforcing passwords Metasploit mssql_login username = password silly passwords remediation smart cards active directory integration password policy Audit: SSMS -> Management -> Policy Mana gement -> Policies Locating Passwords SQL Injection VB Scripts Applications Service Accounts Windows Shares Developer Workstations DTS and DTSX files (Data Transformation Services ) Remediation
Stop treating development environment li ke a development environment Capturing Passwords Metasploit auxiliary/server/capture/mssql Post Exploitation Metasploit Microsoft SQL Server Configuration En umerator auxiliary/admin/mssql/mssql_enum Metasploit XP Command Shell auxiliary/admin/mssql/mssql_exec Listing Databases (use browser service) Listing Tables/Columns (SSMS) Listing Tables/Columns (Information Schema) (Adv anced Workshop) Dump Hashes Metasploit auxiliary/scanner/mssql/mssql _hashdump Query master..syslogins LOGINPROPERTY(na me, 'PasswordHash' ) (Advanced Workshop) SELECT name, LOGINPROPERTY(name, 'PasswordHash' ) hash FROM master.sys.syslogins john mssql05 hashcrack john --format=mssql05 /tmp/mssql-pwhash. txt Format <username>:<0Xhex_format_password _hash> Linked Servers Logins (AD vs. Windows vs. SQL Server logins vs. Users) Listing Logins ([master].[sys].[server_principal s]) (Advanced Workshop) Listing Credentials (SSMS) Listing Credentials ([master].[sys].[credentials ]) (Advanced Workshop) Listing backup device properties Running Commands Metasploit auxiliary/admin/mssql/mssql_e xec Microsoft osql.exe (Advanced Workshop) [Remote]: osql -U brokerage_qa S JEREMY-8GNO9J7F\SQLEXPRESS -P brokerage_qa [Localhost]:osql -U brokerage_qa -S localhost\SQLEXPRESS -P brokerage_qa SSMS How do these tools work? (Advanced Workshop) tcpdump code reviews
Вам также может понравиться
- Transport Superadmin: Admin Login Id Name Website UsernameДокумент4 страницыTransport Superadmin: Admin Login Id Name Website Usernamesadim22Оценок пока нет
- Payload For SunДокумент3 страницыPayload For Sunyashch2007100% (1)
- Output ReasecrДокумент356 страницOutput ReasecrJack WillОценок пока нет
- A 157Документ4 страницыA 157sunnyliuОценок пока нет
- Passwords and AccountsДокумент1 страницаPasswords and Accountsapi-291040047Оценок пока нет
- Passwords FilesДокумент2 страницыPasswords FilesAnsu NjieОценок пока нет
- SN EssДокумент1 страницаSN EssCnopsize AzaОценок пока нет
- Link Full (SFILE - MOBI) - 1Документ15 страницLink Full (SFILE - MOBI) - 1Chandra Eka Kurniawan50% (2)
- SystemДокумент3 страницыSystemAndrew ShevchenkoОценок пока нет
- TCS ApplicationДокумент6 страницTCS ApplicationRohan Rustagi100% (1)
- Bianca Fax Confirmation Combined SSA - RedactedДокумент14 страницBianca Fax Confirmation Combined SSA - RedactedNeg Blanche Boukman LouvertureОценок пока нет
- ScrweibdДокумент15 страницScrweibdSridhar TamilОценок пока нет
- Thincast WorkstationДокумент9 страницThincast WorkstationSebastian Perez lugoОценок пока нет
- Non UseДокумент20 страницNon UseChris AnokwuruОценок пока нет
- SSH 26 JulДокумент2 страницыSSH 26 JulabcdefgqweasdОценок пока нет
- Zeus Web AttacksДокумент50 страницZeus Web AttacksHarsha Vardhan ReddyОценок пока нет
- PasswordДокумент1 страницаPasswordmantineexОценок пока нет
- User-Agents 1000Документ48 страницUser-Agents 1000dunglee160810Оценок пока нет
- Username Password Sheet 1Документ6 страницUsername Password Sheet 1sadim22Оценок пока нет
- Raboplus Account Opening ChecklistДокумент3 страницыRaboplus Account Opening Checklistkbot@Оценок пока нет
- All NT PasswordsДокумент12 страницAll NT PasswordsFatima NayabОценок пока нет
- SSN Project Report PDFДокумент27 страницSSN Project Report PDFErlanggaAdinegoroОценок пока нет
- On Work Life Balance - Google SearchДокумент2 страницыOn Work Life Balance - Google Searchjassi782002Оценок пока нет
- ADDRESДокумент1 страницаADDREScowdery_guitarОценок пока нет
- Avas PasswordsДокумент2 страницыAvas PasswordsSol Ruiz CarbajalОценок пока нет
- LogДокумент135 страницLogДаня БорковскийОценок пока нет
- (Info) Check For MoreДокумент1 страница(Info) Check For MoreFred WilpenОценок пока нет
- License Key HMA ProVPNДокумент2 страницыLicense Key HMA ProVPNAkshay SinghОценок пока нет
- SerialДокумент3 страницыSerialBhusan KhoodyОценок пока нет
- Security Bank Online PDFДокумент1 страницаSecurity Bank Online PDFJesebelle Cuya ToraldeОценок пока нет
- Connected PasswordsДокумент2 страницыConnected Passwordsapi-433882389Оценок пока нет
- SSSHДокумент3 страницыSSSHJaganath ParthasarathyОценок пока нет
- Goetz Library Database PasswordsДокумент1 страницаGoetz Library Database Passwordsalan benedettaОценок пока нет
- michaelGoldenTechDocДокумент2 страницыmichaelGoldenTechDocandi gunawanОценок пока нет
- LOGINДокумент13 страницLOGINLesley ShiriОценок пока нет
- CookiesДокумент2 страницыCookiesHussein KHОценок пока нет
- Interview Questions - Clinical Worker: Provide An Example of An Ethical Dilemma You Have Dealt With in Your PracticeДокумент2 страницыInterview Questions - Clinical Worker: Provide An Example of An Ethical Dilemma You Have Dealt With in Your PracticeSam BushОценок пока нет
- Netflix BumberДокумент6 страницNetflix BumberAdel BejОценок пока нет
- Miami-Dade County Pre-Qualified Firms As of Friday, September 10, 2021 1:09 PMДокумент55 страницMiami-Dade County Pre-Qualified Firms As of Friday, September 10, 2021 1:09 PMGabriel AlvesОценок пока нет
- +rep Pls - PastebinДокумент1 страница+rep Pls - PastebinFelipeОценок пока нет
- Data Resources - Logins & Passwords - Revised 09-26-13Документ21 страницаData Resources - Logins & Passwords - Revised 09-26-13sadim22Оценок пока нет
- UAAS LoginsДокумент1 страницаUAAS Loginsksrinivas9999Оценок пока нет
- 1 Axis Bank 2 Sbi Priyanka7333 3 Federal Bank PRIYANKA7333: Sr. No. Bank Name Account Number Username PasswordДокумент2 страницы1 Axis Bank 2 Sbi Priyanka7333 3 Federal Bank PRIYANKA7333: Sr. No. Bank Name Account Number Username PasswordDeep GhateОценок пока нет
- FacebookPasswordListДокумент3 страницыFacebookPasswordListAshlee Renee100% (1)
- LoginДокумент3 страницыLoginVishwas NayakОценок пока нет
- Human Resources Department:: Item # Position Salary Fringe Subtotal Type: FT, PT, HourlyДокумент10 страницHuman Resources Department:: Item # Position Salary Fringe Subtotal Type: FT, PT, Hourlysadim22Оценок пока нет
- O o o o O: ReceivedДокумент10 страницO o o o O: ReceivedCalWonkОценок пока нет
- Fresh Logs From RussiaДокумент6 страницFresh Logs From RussiaJorge LionОценок пока нет
- Roadrunner Password RecoveryДокумент7 страницRoadrunner Password RecoverySteve SmithОценок пока нет
- Login InformationДокумент1 страницаLogin InformationmohamestОценок пока нет
- Circ 02Документ4 страницыCirc 02Kausthub KrishnamurthyОценок пока нет
- Nerde HistoryДокумент449 страницNerde Historypsx duperОценок пока нет
- 0004456675Документ11 страниц0004456675DylanОценок пока нет
- Admin LoginДокумент5 страницAdmin LoginNeha solutions full project availableОценок пока нет
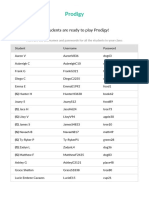
- Prodigy Login Info 86119024 1513013796Документ27 страницProdigy Login Info 86119024 1513013796Joseph HillОценок пока нет
- Password List: Site Username Password NotesДокумент1 страницаPassword List: Site Username Password Notessadim22Оценок пока нет
- Attacking Modern Environments With MSSQL Server SPsДокумент67 страницAttacking Modern Environments With MSSQL Server SPsmajeedsterОценок пока нет
- Attacking Modern Environments With MSДокумент45 страницAttacking Modern Environments With MSkashif majeed janjuaОценок пока нет
- SQLДокумент4 страницыSQLAshok kumarОценок пока нет
- My Measurement LogДокумент3 страницыMy Measurement LogPankaj KumarОценок пока нет
- MealsДокумент2 страницыMealsPankaj KumarОценок пока нет
- DB Bent Over RowДокумент1 страницаDB Bent Over RowPankaj KumarОценок пока нет
- DB SquatДокумент1 страницаDB SquatPankaj KumarОценок пока нет
- DB Incline Bench PressДокумент1 страницаDB Incline Bench PressPankaj KumarОценок пока нет
- DB LungeДокумент1 страницаDB LungeRAM NAIDU CHOPPAОценок пока нет
- Barbell Front Squat: Instructions MusclesДокумент1 страницаBarbell Front Squat: Instructions MusclesPankaj KumarОценок пока нет
- What Happens Within The Muscles in Response To Different Rep RangesДокумент3 страницыWhat Happens Within The Muscles in Response To Different Rep Rangessanchit_dalviОценок пока нет
- Charles Poliquin - The Five Percent SolutionДокумент4 страницыCharles Poliquin - The Five Percent SolutionAlen_D100% (8)
- By William DДокумент2 страницыBy William Dluchici123Оценок пока нет
- BB Bent Over RowДокумент1 страницаBB Bent Over RowGlenn JohnstonОценок пока нет
- Markdown Tip Sheet Quick ReferenceДокумент1 страницаMarkdown Tip Sheet Quick ReferenceNimisha SinghОценок пока нет
- BB SquatДокумент1 страницаBB SquatPankaj KumarОценок пока нет
- DB Bench PressДокумент1 страницаDB Bench PressPankaj KumarОценок пока нет
- Hughes: Company ProfileДокумент6 страницHughes: Company ProfilePankaj KumarОценок пока нет
- The Taste of SuccessДокумент9 страницThe Taste of SuccessMatei StănescuОценок пока нет
- BB Dead LiftДокумент1 страницаBB Dead Liftmaverick_navigateur89Оценок пока нет
- NhyДокумент1 страницаNhyPankaj KumarОценок пока нет
- Document 0Документ5 страницDocument 0Pankaj KumarОценок пока нет
- BB Dead LiftДокумент1 страницаBB Dead Liftmaverick_navigateur89Оценок пока нет
- C & C++Документ11 страницC & C++AbhiОценок пока нет
- Readme - Running BurpДокумент1 страницаReadme - Running Burpzxc123zxczxcОценок пока нет
- ISIS ProtocolДокумент2 страницыISIS ProtocolMuhammad Usman SarwarОценок пока нет
- Unified Theory of NutritionДокумент4 страницыUnified Theory of NutritionPankaj KumarОценок пока нет
- India Financial Sector Reform TalkДокумент16 страницIndia Financial Sector Reform TalkRonit RoyОценок пока нет
- Cisco Access List Commands Cheat SheetДокумент1 страницаCisco Access List Commands Cheat SheetBrad ThompsonОценок пока нет
- ISIS ProtocolДокумент2 страницыISIS ProtocolMuhammad Usman SarwarОценок пока нет
- Read MeДокумент1 страницаRead MePankaj KumarОценок пока нет
- 2008 Cse2Документ72 страницы2008 Cse2Pankaj KumarОценок пока нет
- KSy IPsecДокумент15 страницKSy IPseceditevilОценок пока нет
- Report MTAДокумент22 страницыReport MTAmeenachiОценок пока нет
- Configure An Opc Ua Server On A Compactlogix 5480 Controller Using Factorytalk Linx GatewayДокумент17 страницConfigure An Opc Ua Server On A Compactlogix 5480 Controller Using Factorytalk Linx Gatewayeng abctechОценок пока нет
- SC-200 - Microsoft Security Operations Analyst v2 0Документ37 страницSC-200 - Microsoft Security Operations Analyst v2 0Akash ChopraОценок пока нет
- How To Copy DLL From Global Assembly CacheДокумент6 страницHow To Copy DLL From Global Assembly CachejoydeeptapadarОценок пока нет
- CRM ActionsДокумент22 страницыCRM ActionsgvrnaiduОценок пока нет
- C++ Engineers and ScientistsДокумент54 страницыC++ Engineers and ScientistsTorres JeromeОценок пока нет
- Vision PlusДокумент12 страницVision PlusShashank Shukla67% (6)
- Network Fundamentals Chapter 11Документ28 страницNetwork Fundamentals Chapter 11Leyla BeatrizОценок пока нет
- EmdepДокумент4 страницыEmdepmeedОценок пока нет
- Ansys CAD Integration PDFДокумент86 страницAnsys CAD Integration PDFSamuel PintoОценок пока нет
- A Hybrid Cloud Approach For Secure Authorized ReduplicationsДокумент4 страницыA Hybrid Cloud Approach For Secure Authorized ReduplicationsLOGIC SYSTEMSОценок пока нет
- I FM360Документ11 страницI FM360AmarendraОценок пока нет
- TCX Sky Programmers GuideДокумент582 страницыTCX Sky Programmers GuideEdison San LucasОценок пока нет
- Raju OrdbmsДокумент36 страницRaju Ordbmssammy21791Оценок пока нет
- Introduction To Power BI Slide DeckДокумент265 страницIntroduction To Power BI Slide DeckAchamyeleh TamiruОценок пока нет
- SmarView 11 1 2 5 910 PDFДокумент783 страницыSmarView 11 1 2 5 910 PDFfayazusaОценок пока нет
- PXE Everywhere Installation GuideДокумент22 страницыPXE Everywhere Installation Guidelmlm007Оценок пока нет
- Microsoft 365 Enterprise On A Page - With F1Документ1 страницаMicrosoft 365 Enterprise On A Page - With F1AdrianОценок пока нет
- DRIVES-FT-CC-004 - Altivar Process ATV6x0 Update - 250116 - Rev 2Документ32 страницыDRIVES-FT-CC-004 - Altivar Process ATV6x0 Update - 250116 - Rev 2Edwin RamírezОценок пока нет
- Clipper NetworkДокумент7 страницClipper NetworkVladimir RađenovićОценок пока нет
- VXvue Service Manual.V86b27 - ENДокумент132 страницыVXvue Service Manual.V86b27 - ENspiris100% (2)
- Shravan Kumar DasariДокумент3 страницыShravan Kumar DasariDasari Shràván KümârОценок пока нет
- Outlook TipsДокумент15 страницOutlook TipsSampatmaneОценок пока нет
- Visibility Script For BasebandДокумент16 страницVisibility Script For BasebandWAQAS ASLAMОценок пока нет
- Symantec™ Data Center Security: Server, Monitoring Edition, and Server Advanced 6.7 Overview GuideДокумент25 страницSymantec™ Data Center Security: Server, Monitoring Edition, and Server Advanced 6.7 Overview GuideOstilio SystemsОценок пока нет
- Aura ComponentДокумент2 страницыAura ComponentChandra MohanОценок пока нет
- Java MCQ 3Документ14 страницJava MCQ 3sandeepaprОценок пока нет
- Server Process Redundancy and Race Conditions v1.0Документ25 страницServer Process Redundancy and Race Conditions v1.0Rudi Chandra IIОценок пока нет
- Selecting Development ApproachДокумент10 страницSelecting Development ApproachSoroosh RahimianОценок пока нет
- WWSystemPlatformCourse Part2 EntireManual 1Документ10 страницWWSystemPlatformCourse Part2 EntireManual 1RAHALОценок пока нет