Академический Документы
Профессиональный Документы
Культура Документы
Risk Management Roles and Responsibilities
Загружено:
Omnia HassanИсходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Risk Management Roles and Responsibilities
Загружено:
Omnia HassanАвторское право:
Доступные форматы
Risk Management Roles and Responsibilities
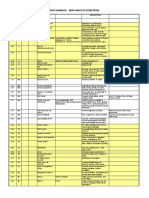
Roles Senior Management. Responsibilities Senior management, under the standard of due care and ultimate responsibility for mission accomplishment, must ensure that the necessary resources are effectively applied to develop the capabilities needed to accomplish the mission. They must also assess and incorporate results of the risk assessment activity into the decision making process. An effective risk management program that assesses and mitigates IT-related mission risks requires the support and involvement of senior management. The CIO is responsible for the agencys IT planning, budgeting, and performance including its information security components. Decisions made in these areas should be based on an effective risk management program. The system and information owners are responsible for ensuring that proper controls are in place to address integrity, confidentiality, and availability of the IT systems and data they own. Typically the system and information owners are responsible for changes to their IT systems. Thus, they usually have to approve and sign off on changes to their IT systems (e.g., system enhancement, major changes to the software and hardware). The system and information owners must therefore understand their role in the risk management process and fully support this process. The managers responsible for business operations and IT procurement process must take an active role in the risk management process. These managers are the individuals with the authority and responsibility for making the trade-off decisions essential to mission accomplishment. Their involvement in the risk management process enables the achievement of proper security for the IT systems, which, if managed properly, will provide mission effectiveness with a minimal expenditure of resources. IT security program managers and computer security officers are responsible for their organizations security programs, including risk management. Therefore, they play a leading role in introducing an appropriate, structured methodology to help identify, evaluate, and minimize risks to the IT systems that support their organizations missions. ISSOs also act as major consultants in support of senior management to ensure that this activity takes place on an ongoing basis. IT security practitioners (e.g., network, system, application, and database administrators; computer specialists; security analysts; security consultants) are responsible for proper implementation of security requirements in their IT systems. As changes occur in the existing IT system environment (e.g., expansion in network connectivity, changes to the existing infrastructure and organizational policies, introduction of new technologies), the IT security practitioners must support or use the risk management process to identify and assess new potential risks and implement new security controls as needed to safeguard their IT systems. Status Notes
Chief Information Officer (CIO).
System and Information Owners.
Business and Functional Managers.
ISSO.
IT Security Practitioners.
Security Awareness The organizations personnel are the users of the IT Trainers (Security/Subject systems. Use of the IT systems and data according to Matter Professionals). an organizations policies, guidelines, and rules of behavior is critical to mitigating risk and protecting the organizations IT resources. To minimize risk to the IT systems, it is essential that system and application users be provided with security awareness training. Therefore, the IT security trainers or security/subject matter professionals must understand the risk management process so that they can develop appropriate training materials and incorporate risk assessment into training programs to educate the end users.
Вам также может понравиться
- Afn 1 PDFДокумент5 страницAfn 1 PDFLovely Ann ReyesОценок пока нет
- ERM PresentationДокумент13 страницERM PresentationBhargav Rishabh BaruahОценок пока нет
- Risk Management Report: A. OverviewДокумент4 страницыRisk Management Report: A. OverviewAmit JainОценок пока нет
- Undertaking The Risk Management Process: AudienceДокумент11 страницUndertaking The Risk Management Process: Audiencearfian yuddyОценок пока нет
- Safety Talk - Leading and Lagging IndicatorsДокумент2 страницыSafety Talk - Leading and Lagging IndicatorsmineprincessОценок пока нет
- It Audit Risk MatrixДокумент16 страницIt Audit Risk MatrixChinh Lê ĐìnhОценок пока нет
- The Biggest Internal Audit Challenges in The Next Five YearsДокумент3 страницыThe Biggest Internal Audit Challenges in The Next Five YearsBagusОценок пока нет
- Audit Flowchart 3Документ3 страницыAudit Flowchart 3naniappoОценок пока нет
- Risk Exposure CalculatorДокумент2 страницыRisk Exposure Calculatorharmandian100% (1)
- Ch.2-Evaluating Operational PerformanceДокумент21 страницаCh.2-Evaluating Operational PerformanceTiwi PangestiОценок пока нет
- Enterprise Risk Management (Erm) By: Joy Ann R. GonzalesДокумент6 страницEnterprise Risk Management (Erm) By: Joy Ann R. GonzalesBea MallariОценок пока нет
- Preventing Manual Handling Injuries To Catering Staff: HSE Information SheetДокумент6 страницPreventing Manual Handling Injuries To Catering Staff: HSE Information SheetAnzil NОценок пока нет
- Who Owns Fraud GreatДокумент7 страницWho Owns Fraud GreatgigitoОценок пока нет
- Audit Universe and Risk Assessment ToolДокумент10 страницAudit Universe and Risk Assessment ToolAsis KoiralaОценок пока нет
- Case Study Risk ManagementДокумент2 страницыCase Study Risk ManagementJonathanA.RamirezОценок пока нет
- WhistleblowerДокумент31 страницаWhistleblowerapi-156240047Оценок пока нет
- High Performance Work SystemsДокумент26 страницHigh Performance Work SystemsChristina DcostaОценок пока нет
- ID Risk Assessment TemplateДокумент51 страницаID Risk Assessment TemplateCORAL ALONSOОценок пока нет
- In Depth Guide To Public Company AuditingДокумент20 страницIn Depth Guide To Public Company AuditingAhmed Rasool BaigОценок пока нет
- Alcatraz Analysis (With Explanations)Документ16 страницAlcatraz Analysis (With Explanations)Raul Dolo Quinones100% (1)
- Question Excerpt From SAP Business One Practice Exam - EspañolДокумент25 страницQuestion Excerpt From SAP Business One Practice Exam - EspañolAndrea OsorioОценок пока нет
- Risk MatrixДокумент3 страницыRisk MatrixMourad HosniОценок пока нет
- Best Practice SOX ComplinceДокумент8 страницBest Practice SOX ComplinceSundar KumarОценок пока нет
- Planning and Strategy:: Bringing The Vision ToДокумент40 страницPlanning and Strategy:: Bringing The Vision ToPrem KumarОценок пока нет
- Process Consultation by ScheinДокумент16 страницProcess Consultation by ScheinZenia VОценок пока нет
- Risk Management PlanДокумент11 страницRisk Management Planmpriceatccusa100% (1)
- A Practical Approach To Creating A Risk Management PlanДокумент4 страницыA Practical Approach To Creating A Risk Management PlanNicoleAbdon0% (1)
- 40 Outsourcing RisksДокумент4 страницы40 Outsourcing RisksMadalina GrecescuОценок пока нет
- Session 17 Pillar 02 Strategic Management Part 1 PDFДокумент18 страницSession 17 Pillar 02 Strategic Management Part 1 PDFWijayasekara BuddhikaОценок пока нет
- Module Title Risk Incident and LeadershiДокумент11 страницModule Title Risk Incident and LeadershishaneОценок пока нет
- Good AuditorДокумент20 страницGood AuditorBertu NatanaОценок пока нет
- CPD Action Plan (No More Than 4 Pages) : Strengths (+) Weaknesses (-)Документ6 страницCPD Action Plan (No More Than 4 Pages) : Strengths (+) Weaknesses (-)Lydia GriffithsОценок пока нет
- CH 1 Auditing and Internal ControlДокумент20 страницCH 1 Auditing and Internal Controlangelica valenzuelaОценок пока нет
- The Business Risk Audit - A Longitudinal Case Study of An Audit EngagementДокумент23 страницыThe Business Risk Audit - A Longitudinal Case Study of An Audit Engagementaudria_mh_110967519Оценок пока нет
- Case Study - ABCДокумент25 страницCase Study - ABClizasaari100% (3)
- 0enterprise Risk Management Policy and ProceduresДокумент25 страниц0enterprise Risk Management Policy and ProceduresHosam GomaaОценок пока нет
- Risk Assessment MatrixДокумент19 страницRisk Assessment MatrixChinh Lê ĐìnhОценок пока нет
- Balanced Scorecard ExamplesДокумент5 страницBalanced Scorecard Examplesapi-3825626100% (1)
- Internal Risks ChecklistДокумент3 страницыInternal Risks ChecklistOladimeji TaiwoОценок пока нет
- Section D Internal Controls P1Документ63 страницыSection D Internal Controls P1Hanif AftabОценок пока нет
- COSO and COSO ERMДокумент6 страницCOSO and COSO ERMAzkaОценок пока нет
- Selecting ERP Consulting PartnerДокумент7 страницSelecting ERP Consulting PartnerAyushmn SikkaОценок пока нет
- Indirect Cost PolicyДокумент6 страницIndirect Cost PolicyMuhammad Zaheer UdDin BabarОценок пока нет
- Operations Risk Paper - Dec 2011Документ24 страницыOperations Risk Paper - Dec 2011Lis SuryaniОценок пока нет
- Bright&Ded Solution To The ProblemДокумент3 страницыBright&Ded Solution To The Problemtalha munirОценок пока нет
- Protiviti Risk ModelДокумент20 страницProtiviti Risk ModelHaris AhmedОценок пока нет
- Gole ProjectДокумент73 страницыGole ProjectAaditya GoleОценок пока нет
- Functions of Marketing DepartmentДокумент10 страницFunctions of Marketing Departmentdani9203Оценок пока нет
- The Roles of MissionДокумент5 страницThe Roles of MissionMelissaCHDОценок пока нет
- Profit Loss StatementДокумент1 страницаProfit Loss StatementhmarcalОценок пока нет
- Risk ManagementДокумент9 страницRisk ManagementHassan_Syed_9406Оценок пока нет
- USG Donors and Reg OverviewДокумент20 страницUSG Donors and Reg OverviewEricka Yvette Paredes Matta100% (1)
- What Is A Marketing Audit?: External Environment Consists of Economic, Political and Legal Factors and ConcentratesДокумент5 страницWhat Is A Marketing Audit?: External Environment Consists of Economic, Political and Legal Factors and ConcentratesMohit MehraОценок пока нет
- Corporate Risk ControlДокумент31 страницаCorporate Risk ControlRyan AdamsОценок пока нет
- Safety AuditsДокумент3 страницыSafety AuditsAdeel Ahmed100% (1)
- Attachment e Requirements Traceability Matrix 2Документ123 страницыAttachment e Requirements Traceability Matrix 2Nevets NonnacОценок пока нет
- Managing Work Environment and Facilities2Документ38 страницManaging Work Environment and Facilities2jОценок пока нет
- Audit Sampling Prepared by Omnia HassanДокумент5 страницAudit Sampling Prepared by Omnia HassanOmnia HassanОценок пока нет
- Audit Ethics and Regulations Prepared by Omnia HassanДокумент22 страницыAudit Ethics and Regulations Prepared by Omnia HassanOmnia HassanОценок пока нет
- Nazlawi Business College: Project Cost ManagementДокумент72 страницыNazlawi Business College: Project Cost ManagementOmnia HassanОценок пока нет
- Computer Auditing Prepared by Omnia HassanДокумент7 страницComputer Auditing Prepared by Omnia HassanOmnia HassanОценок пока нет
- Systems Assessment Prepared by Omnia HassanДокумент25 страницSystems Assessment Prepared by Omnia HassanOmnia HassanОценок пока нет
- Nazlawi Business School: (Project Procurement Management)Документ32 страницыNazlawi Business School: (Project Procurement Management)Omnia HassanОценок пока нет
- Nazlawi Business School: (Project Communication Management)Документ24 страницыNazlawi Business School: (Project Communication Management)Omnia HassanОценок пока нет
- Nazlawi Business College: Project Scope ManagementДокумент43 страницыNazlawi Business College: Project Scope ManagementOmnia HassanОценок пока нет
- Nazlawi Business College: Pmbok 13, Knowledge Areas Project Integration ManagementДокумент52 страницыNazlawi Business College: Pmbok 13, Knowledge Areas Project Integration ManagementOmnia HassanОценок пока нет
- Nazlawi Business College: (Project Schedule Management)Документ55 страницNazlawi Business College: (Project Schedule Management)Omnia HassanОценок пока нет
- Balance Sheet q2Документ6 страницBalance Sheet q2Omnia HassanОценок пока нет
- Nazlawi Business School: (Project Stakeholder Management)Документ25 страницNazlawi Business School: (Project Stakeholder Management)Omnia HassanОценок пока нет
- Nazlawi Business College: Chapter Seven Project Cost ManagementДокумент30 страницNazlawi Business College: Chapter Seven Project Cost ManagementOmnia HassanОценок пока нет
- Class Notes 6-8Документ11 страницClass Notes 6-8Omnia HassanОценок пока нет
- Nazlawi Business School: (Project Risk Management)Документ50 страницNazlawi Business School: (Project Risk Management)Omnia HassanОценок пока нет
- CMA2 P1 A Budgeting Alpha Tech P3694Q3Документ4 страницыCMA2 P1 A Budgeting Alpha Tech P3694Q3Omnia HassanОценок пока нет
- 03 Supply Chain StrategyДокумент21 страница03 Supply Chain StrategyOmnia HassanОценок пока нет
- Nazlawi Business School: Chapter Eight Project Quality ManagementДокумент32 страницыNazlawi Business School: Chapter Eight Project Quality ManagementOmnia HassanОценок пока нет
- Corporate Finance: Final Exam - Spring 2003Документ38 страницCorporate Finance: Final Exam - Spring 2003Omnia HassanОценок пока нет
- Common Stock q1Документ2 страницыCommon Stock q1Omnia HassanОценок пока нет
- Accounts Receivable q3Документ3 страницыAccounts Receivable q3Omnia HassanОценок пока нет
- Presentation of Expertise Training CourseДокумент74 страницыPresentation of Expertise Training CourseOmnia HassanОценок пока нет
- International Project AccountingДокумент168 страницInternational Project AccountingOmnia HassanОценок пока нет
- Accounts Receivable q2Документ4 страницыAccounts Receivable q2Omnia Hassan100% (1)
- Horngren Ima16 stppt08Документ38 страницHorngren Ima16 stppt08Omnia HassanОценок пока нет
- Language Competence ReflectionДокумент2 страницыLanguage Competence Reflectionapi-532062165Оценок пока нет
- Martin George Cooke 7th January 2011Документ2 страницыMartin George Cooke 7th January 2011Martin Cooke Cert EdОценок пока нет
- Optimizing Leadership AcumenДокумент111 страницOptimizing Leadership AcumenObakozuwa Edokpolo Oghogho PeterОценок пока нет
- The Electrical Worker August 2010Документ20 страницThe Electrical Worker August 2010Kathryn R. ThompsonОценок пока нет
- Aristotle's Political PhilosophyДокумент1 страницаAristotle's Political PhilosophyPatrick Matthew RabinoОценок пока нет
- David Mendes - An Imaginary Interview With DR Humberto MaturanaДокумент2 страницыDavid Mendes - An Imaginary Interview With DR Humberto MaturanadrleonunesОценок пока нет
- Obtain Authorisation Before Overriding or Disabling Safety ControlsДокумент9 страницObtain Authorisation Before Overriding or Disabling Safety ControlsKathleen Faith C. BrionesОценок пока нет
- Unit 1 Lesson 1Документ3 страницыUnit 1 Lesson 1Danica SilvaОценок пока нет
- Siop PPДокумент1 страницаSiop PPapi-565608712Оценок пока нет
- 02 Hart and His Critics Ver 3.0Документ23 страницы02 Hart and His Critics Ver 3.0Anshika AgarwalОценок пока нет
- Imo Last EditionsДокумент2 страницыImo Last EditionsjakkyntoОценок пока нет
- Va-Yasem Oto 'Al Nes: Standards in Limmudei Kodesh For Modern Orthodox Day SchoolsДокумент15 страницVa-Yasem Oto 'Al Nes: Standards in Limmudei Kodesh For Modern Orthodox Day Schoolsoutdash2Оценок пока нет
- (20201007) (Piloting With EBSI Learning Package Toolkit) (v1.00)Документ85 страниц(20201007) (Piloting With EBSI Learning Package Toolkit) (v1.00)Jean DanielОценок пока нет
- 3 Basic Economic Problems and Philippine Socioeconomic Development in The 21st CenturyДокумент16 страниц3 Basic Economic Problems and Philippine Socioeconomic Development in The 21st Centuryjonel tuazon81% (85)
- MM ConfigurationДокумент6 страницMM ConfigurationSAPОценок пока нет
- FBI Tracking Warrant For Baltimore Police Officer Catherine FilippouДокумент35 страницFBI Tracking Warrant For Baltimore Police Officer Catherine FilippouAmeliaMcDonell-ParryОценок пока нет
- Activity in Chapter 2 Lesson 2 (Group5)Документ2 страницыActivity in Chapter 2 Lesson 2 (Group5)elme rose siasolОценок пока нет
- Multiplying Binomials Lesson PlanДокумент3 страницыMultiplying Binomials Lesson PlanMolly Frantz100% (1)
- Experience Letter DeependraДокумент1 страницаExperience Letter DeependraanimshakyaОценок пока нет
- Arc FormДокумент2 страницыArc Formcraig_fultonОценок пока нет
- Module in P.E Grade 7: Fitness in Folk Dancing: Pre AsessmentДокумент5 страницModule in P.E Grade 7: Fitness in Folk Dancing: Pre AsessmentGlenn ParasОценок пока нет
- World of BiosimilarsДокумент20 страницWorld of BiosimilarsWasi AkhtarОценок пока нет
- NICE 2.0 and EC Council Cert Mapping PDFДокумент385 страницNICE 2.0 and EC Council Cert Mapping PDFAmit BshwsОценок пока нет
- Formal and Informal Register Part 2Документ3 страницыFormal and Informal Register Part 2Ignacio NoriaОценок пока нет
- IPR Workshop - Biotech and PharmaДокумент9 страницIPR Workshop - Biotech and PharmaCheshta SharmaОценок пока нет
- NullДокумент3 страницыNullapi-25623005Оценок пока нет
- 14 SQUARE OF A NUMBER Semi-Detailed LPДокумент2 страницы14 SQUARE OF A NUMBER Semi-Detailed LPDawn Razonable100% (1)
- 6 1 19 2 10 20181013Документ13 страниц6 1 19 2 10 20181013Ramsi A. HОценок пока нет
- 2 PDFДокумент1 страница2 PDFTomlin HazelОценок пока нет
- School of Law: The Rizal Memorial Colleges, IncДокумент2 страницыSchool of Law: The Rizal Memorial Colleges, IncConsuelo Narag GalagalaОценок пока нет
- The Internet Con: How to Seize the Means of ComputationОт EverandThe Internet Con: How to Seize the Means of ComputationРейтинг: 5 из 5 звезд5/5 (6)
- Coding Democracy: How a Growing Hacking Movement is Disrupting Concentrations of Power, Mass Surveillance, and Authoritarianism in the Digital AgeОт EverandCoding Democracy: How a Growing Hacking Movement is Disrupting Concentrations of Power, Mass Surveillance, and Authoritarianism in the Digital AgeРейтинг: 4.5 из 5 звезд4.5/5 (3)
- OSCP Offensive Security Certified Professional Practice Tests With Answers To Pass the OSCP Ethical Hacking Certification ExamОт EverandOSCP Offensive Security Certified Professional Practice Tests With Answers To Pass the OSCP Ethical Hacking Certification ExamОценок пока нет
- Facing Cyber Threats Head On: Protecting Yourself and Your BusinessОт EverandFacing Cyber Threats Head On: Protecting Yourself and Your BusinessРейтинг: 4.5 из 5 звезд4.5/5 (27)
- Tor Darknet Bundle (5 in 1): Master the Art of InvisibilityОт EverandTor Darknet Bundle (5 in 1): Master the Art of InvisibilityРейтинг: 4.5 из 5 звезд4.5/5 (5)
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNОт EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNРейтинг: 5 из 5 звезд5/5 (1)
- 200+ Ways to Protect Your Privacy: Simple Ways to Prevent Hacks and Protect Your Privacy--On and OfflineОт Everand200+ Ways to Protect Your Privacy: Simple Ways to Prevent Hacks and Protect Your Privacy--On and OfflineОценок пока нет
- Hands-On AWS Penetration Testing with Kali Linux: Set up a virtual lab and pentest major AWS services, including EC2, S3, Lambda, and CloudFormationОт EverandHands-On AWS Penetration Testing with Kali Linux: Set up a virtual lab and pentest major AWS services, including EC2, S3, Lambda, and CloudFormationОценок пока нет
- Hacking With Kali Linux : A Comprehensive, Step-By-Step Beginner's Guide to Learn Ethical Hacking With Practical Examples to Computer Hacking, Wireless Network, Cybersecurity and Penetration TestingОт EverandHacking With Kali Linux : A Comprehensive, Step-By-Step Beginner's Guide to Learn Ethical Hacking With Practical Examples to Computer Hacking, Wireless Network, Cybersecurity and Penetration TestingРейтинг: 4.5 из 5 звезд4.5/5 (9)
- Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTОт EverandPractical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTОценок пока нет
- Transformational Security Awareness: What Neuroscientists, Storytellers, and Marketers Can Teach Us About Driving Secure BehaviorsОт EverandTransformational Security Awareness: What Neuroscientists, Storytellers, and Marketers Can Teach Us About Driving Secure BehaviorsРейтинг: 5 из 5 звезд5/5 (2)
- Cyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyondОт EverandCyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyondРейтинг: 4.5 из 5 звезд4.5/5 (14)
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingОт EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingРейтинг: 5 из 5 звезд5/5 (3)
- Cybersecurity for Beginners : Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide: 1От EverandCybersecurity for Beginners : Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide: 1Оценок пока нет
- CYBERSECURITY FOR BEGINNERS: HOW TO DEFEND AGAINST HACKERS & MALWAREОт EverandCYBERSECURITY FOR BEGINNERS: HOW TO DEFEND AGAINST HACKERS & MALWAREРейтинг: 3.5 из 5 звезд3.5/5 (6)
- The Mediatrician's Guide: A Joyful Approach to Raising Healthy, Smart, Kind Kids in a Screen-Saturated WorldОт EverandThe Mediatrician's Guide: A Joyful Approach to Raising Healthy, Smart, Kind Kids in a Screen-Saturated WorldОценок пока нет
- CCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamОт EverandCCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamОценок пока нет
- Crypto: How the Code Rebels Beat the Government--Saving Privacy in the Digital AgeОт EverandCrypto: How the Code Rebels Beat the Government--Saving Privacy in the Digital AgeРейтинг: 4 из 5 звезд4/5 (1)