Академический Документы
Профессиональный Документы
Культура Документы
10 Driscoll
Загружено:
johnroberts320 оценок0% нашли этот документ полезным (0 голосов)
26 просмотров12 страницbeepbeep real-time encryption - Driscoll presentation
Авторское право
© Attribution Non-Commercial (BY-NC)
Доступные форматы
PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документbeepbeep real-time encryption - Driscoll presentation
Авторское право:
Attribution Non-Commercial (BY-NC)
Доступные форматы
Скачайте в формате PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
26 просмотров12 страниц10 Driscoll
Загружено:
johnroberts32beepbeep real-time encryption - Driscoll presentation
Авторское право:
Attribution Non-Commercial (BY-NC)
Доступные форматы
Скачайте в формате PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 12
Real Time Cryptography
The application area
Cryptography optimized Ior
embedded, real-time, control systems
The development
A new algorithm, called BeepBeep, overcomes the problems
with using existing cryptography Ior real time systems
Contact: Kevin Driscoll Kevin.DriscollHoneywell.com
612-951-7263 (phone) 612-951-7438 (FAX)
Grid Security
'need at least 1 Gbps encryption
BeepBeep can do that ...
. in on a 1 GHz Pentium
No encryption hardware
Cheaper
More Ilexible and easier to manage
Allows ad hoc grids (i.e., SETIhome model)
II no physical security at nodes
Must assume some nodes will be compromised
Portion oI data and algorithm will exposed
Node`s keys will be exposed
Need unique key(s) Ior each node
Need crypto algorithm with good key agility
Encryption Basics
Encrypt Decrypt
Key
e
(K
e
)
Plaintext (P) Plaintext (P)
Key
d
(K
d
)
Ciphertext (C)
Key (K)
Plaintext (P) Plaintext (P) Ciphertext (C)
+
-
Pseudo Random
Number Generator
nitialization
Vector (V)
Key (K)
Pseudo Random
Number Generator
nitialization
Vector (V)
Optional
Autokey
Optional
Autokey
Problems with Using Existing SoItware
Cryptography Ior Embedded Real-Time Systems
Is relatively slow, particularly on start-up
Messages (and sessions) are small, less text to amortize start-up cost
Latency (lag) is more important than throughput
Only worst case timing counts, average is unimportant
One missed deadline is not helped by Iinishing early at all other times
Systems typically use repeating execution time slots oI Iixed size
Central control changes key Ior each message (high key agility)
Uses too much data memory (cache thrashing)
Real time systems are multitasking with many context switches / sec
Must assume cache is Ilushed, S-box accesses are mostly misses
Consumes additional communication bandwidth
Ciphertext must be no bigger than plaintext
Uses separate secrecy and integrity algorithms (or modes)
Makes execution even slower
Prevents 'lump in the cable retroIits
Most real-time cryptography will be retrofits,
which exacerbates the above problems
About 2 times faster for very large messages
About 40 times faster for small messages
About half the memory size
25 to 200 times faster than 3DES
Includes integrity with secrecy (increases the above ratios)
Allows 'lump in the cable (or 'dongle) implementations
(with possible sub-bit-time latency)
Several thousand times faster and smaller than public key
1:1 byte replacement (to fit existing message sizes)
Can eliminate need Ior the addition oI an explicit IV
Can incorporate existing CRC or checksum into integrity
Optimized for CPUs typically found in embedded, real
time, control, and communication systems
BeneIits (vs AES, on Pentium)
Achieving Speed
Use an efficient stream cipher
State stays in CPU registers (no RAM used)
Ignore or circumvent conventional wisdom fears
Feedback shiIt registers are slow in soItware
Invention to improve speed by almost 100 times
Multiply is slow
Becoming Iaster (Irom 42 clocks to 1//4 clocks)
Invention to use multiply in a powerIul new way
Conditional jumps are slow on pipelined CPUs
Use multiplexor logic instead oI conditional jump
Instead oI: if C then Z = A else Z = B
Use this: Z = ((A xor B) and C) xor B
Use unrolled loop to eliminate other jumps
Speed on Pentium is better than 1 bit per clock
Actual speed is 1.19 vs theoretical 1.83 bits per clock
Simple and Small
BeepBeep`s executable code
One page oI C code
(halI oI which is declarations and comments)
Pentium* without explicit IV 419 bytes
Pentium* with explicit IV 484 bytes
Pentium* main loop 185 bytes
BeepBeep`s data memory
Pentium* MMX (data stays in registers) 0 bytes
* with MMX registers
Minimizing Message Size
No block padding (BeepBeep isn`t a block cipher)
Minimize or eliminate Initialization Vector (IV)
Use existing data Ior IV (e.g. unencrypted header Iields)
Use explicit or implicit message IDs (e.g. time / sequence)
(most real time systems use such IDs)
Use Block IV Mode to eliminate IVs (see next slide)
Eliminate some IVs by chaining messages together
Can be used with reliable message delivery
Crypto-state is carried over between messages
Use existing CRC or other check data for integrity
(may need to add bits iI existing check bits aren`t enough)
Security
Basis: 127 bit Linear Feedback ShiIt Register (LFSR)
Benefits: Good statistics, period that won`t repeat
Old Attack: Berlekamp-Massey
Old Fixes: clock control, nonlinear Iilter, nonlinear
combination oI multiple LFSRs
Newer Attacks: embedding, probabilistic correlation,
linear consistency, best aIIine approximation, ...
Fixes: use both clock control and nonlinear Iilter with
state, two-stage combiner, and 5 diIIerent algebras
Security (continued)
Non-linear filter
32-bit ones complement addition and 32-bit multiply
provide 128th order non-linearity
Integrity provided by two mechanisms
Two-stage combiner`s non-associative operations
Ciphertext (Plaintext Key
1
) XOR Key
2
Ciphertext Plaintext (Key
1
XOR Key
2
)
Ciphertext Plaintext (Key
x
) |Ior any possible key|
Can`t directly recover running key, even with known plaintext
Plaintext-based autokey Ieeds back into the non-linear
Iilter`s state and into the clock control`s state
Propagates any text changes through to the end oI message
Real-time control system messages usually end with check data
that can be used to detect tampering
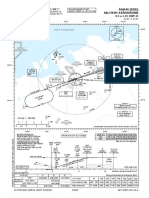
Aviation
Encryption oI ACARS radio traIIic
Constraints: bandwidth, real-time multitasking
Also memory and execution time Ior retro-Iit applications
This application has been cleared Ior export by BXA
Home automation and security (see Oct 2001 IEEE Computer)
Secrecy, integrity, authentication, and key management
Between central site and residences
Constraints: memory, bandwidth, small (8/16 bit) CPU
No other algorithm could meet memory constraints
when all Iour security services were included
Limit: 1638 bytes Flash ROM, 50 bytes RAM
Used: 1628 28
This application has been cleared Ior export by BXA
Commercial buildings and industrial controls
Postulated Uses
Вам также может понравиться
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- Beepbeep-3a2093546 148Документ34 страницыBeepbeep-3a2093546 148johnroberts32Оценок пока нет
- BeepBeep Embedded Real Time EncryptionДокумент15 страницBeepBeep Embedded Real Time Encryptionjohnroberts32Оценок пока нет
- Mcga-Shs Capt Guide Chap13Документ6 страницMcga-Shs Capt Guide Chap13johnroberts32Оценок пока нет
- Study MethodДокумент1 страницаStudy Methodjohnroberts32Оценок пока нет
- Tardis 40 CH 1Документ7 страницTardis 40 CH 1johnroberts32Оценок пока нет
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (120)
- Passat No. 13/1: Comfort System, With Alarm SystemДокумент16 страницPassat No. 13/1: Comfort System, With Alarm SystemLuix TiradoОценок пока нет
- I/G/O I/G/O A/M/I: Instrument Approach Chart - IcaoДокумент1 страницаI/G/O I/G/O A/M/I: Instrument Approach Chart - IcaoMIkołaj MorzeОценок пока нет
- 320d WiringДокумент2 страницы320d WiringMohamed Harb100% (5)
- The Effects of Dissolved Sodium Chloride (Nacl) On Well Injectivity During Co2 Storage Into Saline AquifersДокумент20 страницThe Effects of Dissolved Sodium Chloride (Nacl) On Well Injectivity During Co2 Storage Into Saline AquifersMuhammad FatchurroziОценок пока нет
- UV-5R MenusДокумент4 страницыUV-5R MenusRikardoviskiОценок пока нет
- 122Документ10 страниц122Bayangan HatiОценок пока нет
- Relationship of EN 954-1 and IEC 61508 Standards PDFДокумент2 страницыRelationship of EN 954-1 and IEC 61508 Standards PDFfitasmounirОценок пока нет
- FP CLOCK - csproj.FileListAbsoluteДокумент14 страницFP CLOCK - csproj.FileListAbsolutePhi Huỳnh NgôОценок пока нет
- PayrollBatchLoader v4Документ158 страницPayrollBatchLoader v4MaheshОценок пока нет
- Centrifugal PumpsДокумент6 страницCentrifugal Pumpsjerome fajardoОценок пока нет
- ReleaseNotes MimicsMedical 21.0Документ24 страницыReleaseNotes MimicsMedical 21.0陳司瀚Оценок пока нет
- HPSIM Command Line InterfaceДокумент107 страницHPSIM Command Line Interfacegverma80Оценок пока нет
- Honda Gx200 Engine ManualДокумент2 страницыHonda Gx200 Engine Manualgomes_marina930% (1)
- Dax Patel CVДокумент1 страницаDax Patel CVPriyanshОценок пока нет
- HSE FRM 32 Final Incident ReportДокумент6 страницHSE FRM 32 Final Incident ReportDilshad aliОценок пока нет
- Butterworth Filter Design With A Low Pass ButterworthДокумент8 страницButterworth Filter Design With A Low Pass ButterworthashishkkrОценок пока нет
- Iso 5294 1989Документ9 страницIso 5294 1989a.mursadinОценок пока нет
- DC Rectifier - OrionДокумент12 страницDC Rectifier - OrionLimbagaОценок пока нет
- E5263 - M4A87TD EVO PDFДокумент76 страницE5263 - M4A87TD EVO PDFLeandro Henrique AgostinhoОценок пока нет
- Pre Accion PDFДокумент8 страницPre Accion PDFjhoger2012Оценок пока нет
- Working of Steam Turbine Learn EngineeringДокумент4 страницыWorking of Steam Turbine Learn EngineeringWahid HusainОценок пока нет
- 2021 Product Catalogue DTH - English - LOWДокумент42 страницы2021 Product Catalogue DTH - English - LOWEmrah MertyürekОценок пока нет
- Company ProfileДокумент6 страницCompany ProfileFaidzil ChabibОценок пока нет
- 10 Famous Shipping Canals of The WorldДокумент7 страниц10 Famous Shipping Canals of The Worldparth_upadhyay_1Оценок пока нет
- Simulasi Pengendalian Level Steam DrumДокумент15 страницSimulasi Pengendalian Level Steam DrumSatria dinusaОценок пока нет
- Ormin ElementaryДокумент19 страницOrmin ElementaryPRC Board100% (1)
- Pacom S72724+PDR32-RMT-HYB+ManualДокумент130 страницPacom S72724+PDR32-RMT-HYB+ManualDavidChisholmОценок пока нет
- Craftsman 73754 ManualДокумент24 страницыCraftsman 73754 Manualjkchromy945Оценок пока нет
- Notificatio N (Rese Rvation) Gove Rnment: A Cu) UTДокумент1 страницаNotificatio N (Rese Rvation) Gove Rnment: A Cu) UT122-Ayush Kumar ParganihaОценок пока нет
- Makalah Program PDFДокумент10 страницMakalah Program PDFIvanFolkОценок пока нет