Академический Документы
Профессиональный Документы
Культура Документы
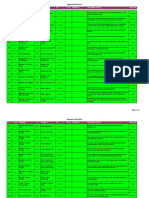
SOD Risk Summary - SAP With Mitigating Controls
Загружено:
Abhijit PodderОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
SOD Risk Summary - SAP With Mitigating Controls
Загружено:
Abhijit PodderАвторское право:
Доступные форматы
Segregation of Duty Risks
Risk ID FunctionID Function 1
FunctionID
Function 2
Mitigation ID
Function
Function 3
Description of Risk Finance
Create a fictitious GL account and generate journal activity or hide activity via posting entries. Alter a cost center without authorization and process unauthorized cost transfers to this center, possibly distorting CO reporting. Alter a cost center without authorization and process unauthorized revenue entries to this center, possibly distorting CO reporting.
Risk Level
F001
GL02
Maintain GL Master Data
GL01
Post Journal Entry Cost Transfer Processing Revenue Reposting
MIT-F001
Medium
F002
CC03
Maintain Cost Centers
CC06
MIT-F002
Medium
F003
CC03
Maintain Cost Centers Maintain CC or CE Groups Maintain Bank Master Data Maintain Asset Document Maintain Asset Document Cash Application
FI01
MIT-F003
Medium
F004
CC02
GL01
Post Journal Entry
MIT-F004
Manipulate cost center reports to hide inappropriate journal entry posting.
Medium
F005
FI04
AP01
AP Payments
MIT-F005
Create a non bona-fide bank account and create a check from it.
High
F006
FA01
AP02
Process Vendor Invoices
MIT-F006
Pay an invoice and hide it in an asset that would be depreciated over time.
High
F007
FA01
MM05
Goods Receipts to PO
MIT-F007
Create an invoice through ERS goods receipt and hide it in an asset that would be depreciated over time. Allows differences between cash deposited and cash collections posted to be covered up
High
F008
AR02
FI03
Bank Reconciliation
MIT-F008
High
F009
CC01
Maintain Cost Center Distributions Maintain Internal CO Order Maintain Activity Types
CC04
Execute Cost Center Distributions Internal Order Settlement Activity Allocation Maintain Asset Document Goods Receipts to PO
MIT-F009
Allocate costs to unauthorized cost centers thereby distorting financial reporting.
Low
F010
CC05
CC07
MIT-F010
Settle expenses from an unauthorized order and distort CO reporting.
Low
F011
FI07
FI02
MIT-F011
Alter an activity type used for cost allocation purposes with fictitious data, thereby distorting the cost allocation process. User responsible for asset masters records could process transactions that would allow the asset to be depreciated over time.
Low
F012
FA02
Maintain Asset Master
FA01
MIT-F012
Medium
F013
FA02
Maintain Asset Master Process Overhead Postings Maintain Projects and WBS Elements Maintain Projects and WBS Elements Maintain Bank Master Data Maintain Posting Periods
MM05
MIT-F013
Create the asset and manipulate the receipt of the associated asset.
High
F014
PS02
PS03
Settle Projects
MIT-F014
Post overhead expenses to the project and settle the project without going through the settlement approval process. Use a fictitious project to allocate overages of an actual project, and settle the project without going through the settlement approval process.
High
F015
PS01
PS03
Settle Projects
MIT-F015
High
F016
PS01
PS02
Process Overhead Postings
MIT-F016
Manipulate the work breakdown structure elements (profit centers, business areas, cost centers, plants) and post overhead expenses to the project
High
F017
FI04
AR02
Cash Application
MIT-F017
Maintain a non bona-fide bank account and divert incoming payments to it.
High
F018
FI06
GL01
Post Journal Entry
MIT-F018
Open previously closed accounting periods and inappropriately post entries after month end.
Medium Page 1 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 F019
FI06
FunctionID AP01
Function 2 AP Payments
Mitigation ID
MIT-F019
Function
Function 3
Description of Risk
Open previously closed accounting periods and inappropriately post payments after month end. User able to open accounting periods previously closed and enter incoming payments after month end reporting. Open previously closed accounting periods and inappropriately receive or issue goods after month end. Create a fictitious GL account and generate miscellaneous general ledger activity or hide fraudulent activity via posting entries. Manipulate cost center reports to hide inappropriate miscellaneous journal entry postings. Open previously closed accounting periods and inappropriately post tax and currency journal entries after month end.
Risk Level
Medium
Maintain Posting Periods
F020
FI06
Maintain Posting Periods
AR02
Cash Application
MIT-F020
Medium
F021
FI06
Maintain Posting Periods
MM04
Goods Movements Post Journal Entry (misc Tax/Currency) Post Journal Entry (misc Tax/Currency) Post Journal Entry (misc Tax/Currency) Manual Check Processing Manual Check Processing Confirm a Treasury Trade Process Vendor Invoices
MIT-F021
Medium
F022
GL02
Maintain GL Master Data Maintain CC or CE Groups Maintain Posting Periods Maintain Bank Master Data Maintain Posting Periods Create / Change Treasury Item Post Journal Entry
GL03
MIT-F022
Medium
F023
CC02
GL03
MIT-F023
Medium
F024
FI06
GL03
MIT-F024
Medium
F025
FI04
AP04
MIT-F025
Create a non bona-fide bank account and create manual checks from it
High
F026
FI06
AP04
MIT-F026
Open previously closed accounting periods and inappropriately post manual payments Users can create a fictitious trade and fraudulently confirm or exercise the trade Adjust the subsidiary balance using the vendor invoice entry and then cover it up using journal entries Adjust the subsidiary balance using the AR payment transaction and then cover it up using journal entries Adjust the subsidiary balance using the AR payment transaction and then cover it up using journal entries Adjust the subsidiary balance using the AR payment transaction and then cover it up using journal entries
Medium
F027
FI08
FI09
MIT-F027
High
F028
GL01
AP02
MIT-F028
Medium
F029
GL01
Post Journal Entry
AR01
AR Payments
MIT-F029
Medium
F030
GL01
Post Journal Entry
AR02
Cash Application
MIT-F030
Medium
F031
GL01
Post Journal Entry
AR05
AR Payments
MIT-F031
Medium
Materials Management / Quality Management / Production Planning M001
PP02
Production Order Processing Production Order Processing Confirm Production Order Quality Results Reporting Quality Results Reporting
FI05
Product Costing Confirm Production Order Product Costing
MIT-M001
Increase Production to reduce cost variances
Low
M002
PP02
PP01
MIT-M002
Production order processing and confirming production orders
Low
M003
PP01
FI05
MIT-M003
Increase Production to reduce cost variances due to productivity
Low
M004
QM01
SD02
Delivery Processing
MIT-M004
Transfer stock to general release to meet delivery schedules
Low
M005
QM01
MM07
Enter Counts - WM
MIT-M005
MM08
Clear Differences - WM Remove inferior materials by adjusting out via WM inventory
Medium
Page 2 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 M006
MM04
FunctionID
Function 2 Enter Counts - WM
Mitigation ID
MIT-M006
Function
Function 3 Clear Differences - WM
Description of Risk
Accept goods via goods receipts and perform a WM physical inventory adjustment afterwards.
Risk Level
High
Goods Movements
MM07
MM08
M007
QM01
Quality Results Reporting Post Journal Entry
PP01
Confirm Production Order Enter Counts - WM
MIT-M007
Release produced materials to GR stock to maintain production quotas
Medium
M008
GL01
MM07
MIT-M008
MM08
Clear Differences - WM Hide WM inventory adjustments via ledger entries
Medium
M009
QM01
Quality Results Reporting
MM02
Enter Counts - IM
MIT-M009
MM01
Clear Differences Inventory Management
Remove inferior materials by adjusting out via IM inventories
Medium
M010
QM01
Quality Results Reporting
MM03
Enter Counts & Clear Diff - IM
MIT-M010
Remove inferior materials by adjusting out via IM inventories
Medium
M011
MM04
Goods Movements
MM02
Enter Counts - IM Enter Counts & Clear Diff - IM Enter Counts & Clear Diff - IM Enter Counts - IM
MIT-M011
MM01
Clear Differences Inventory Management
Accept goods via goods receipts and perform an IM physical inventory adjustment afterwards. Accept goods via goods receipts and perform an IM physical inventory adjustment afterwards.
High
M012
MM04
Goods Movements
MM03
MIT-M012
High
M013
GL01
Post Journal Entry
MM03
MIT-M013
Hide IM inventory adjustments via ledger entries
Medium
M014
GL01
Post Journal Entry
MM02
MIT-M014
MM01
Clear Differences Inventory Management
Hide IM inventory adjustments via ledger entries
Medium
Procure to Pay P001
PR01
Vendor Master Maintenance AP Payments
AP02
Process Vendor Invoices Vendor Master Maintenance AP Payments
Maintain a fictitious vendor and enter a Vendor invoice for automatic payment
High
P002
AP01
PR01
Maintain a fictitious vendor and create a payment to that vendor
High
P003
AP02
Process Vendor Invoices
AP01
Enter fictitious vendor invoices and then render payment to the vendor
High
P004
PR02
Maintain Purchase Order
AP02
Process Vendor Invoices
Purchase unauthorized items and initiate payment by invoicing
High
P005
PR02
Maintain Purchase Order
MM05
Goods Receipts to PO
Enter fictitious purchase orders for personal use and accept the goods through goods receipt
High
P006
AP02
Process Vendor Invoices
MM05
Goods Receipts to PO
Enter fictitious vendor invoices and accept the goods via goods receipt
High
P007
PR02
Maintain Purchase Order Vendor Master Maintenance
AP01
AP Payments
Enter a fictitious purchase order and enter the covering payment
High
P008
PR01
PR02
Maintain Purchase Order
Create a fictitious vendor and initiate purchases to that vendor
High
Page 3 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 P009
AP03
FunctionID PR08
Function 2 Service Acceptance
Mitigation ID
Function
Function 3
Description of Risk
Receive or accept services and release a previously blocked Invoice to offset the receipt Enter unauthorized purchase order and release a previously blocked Invoice to offset the purchase order Inappropriately procure an item and manipulating the IM physical inventory counts to hide.
Risk Level
Medium
Release Blocked Invoices Release Blocked Invoices Maintain Purchase Order
P010
AP03
PR02
Maintain Purchase Order Enter Counts & Clear Diff - IM
Medium
P011
PR02
MM03
High
P012
PR03
Service Master Maintenance Maintain Material Master Data Bank Reconciliation Release Blocked Invoices Service Acceptance
PR07
Requisitioning
Risk of modifying or adding to service master data (to add item that normally is not ordered by the company) and then create / change a requisition.
Medium
P013
MM06
PR02
Maintain Purchase Order
Add items to the material master or service master file and create fraudulent purchase orders for those items
Medium
P014
FI03
AP02
Process Vendor Invoices
Can hide differences between bank payments & posted AP records
High
P015
AP03
MM05
Goods Receipts to PO
Receive goods against a purchase order and release a previously blocked Invoice to offset the receipt
Medium
P016
PR08
AP01
AP Payments
Receive or accept services and enter the covering payments
High
P017
PR02
Maintain Purchase Order Maintain Material Master Data PO Approval
PR08
Service Acceptance
Enter fictitious purchase orders for personal use and accept the services through service acceptance Add an item to the material master or service master file and then fraudulently adding those items to purchasing agreements Approve the purchase of unauthorized goods and hide the misuse of inventory by not fully receiving the order Commit the company to fraudulent purchase contracts and initiate payment for unauthorized goods and services. Release a non bona-fide purchase order and initiate payment for the order by entering invoices
Medium
P018
MM06
PR05
Purchasing Agreements
Medium
P019
PR04
MM05
Goods Receipts to PO
High
P020
PR04
PO Approval
AP01
AP Payments
High
P021
PR04
PO Approval
AP02
Process Vendor Invoices Clear Differences Inventory Management
High
P022
PR04
PO Approval
MM02
Enter Counts - IM Vendor Master Maintenance Maintain Material Master Data Purchasing Agreements
MM01
Release a non bona-fide purchase order and the action remain undetected by manipulating the IM physical inventory counts Create a fictitious vendor or change existing vendor master data and approve purchases to this vendor
High
P023
PR04
PO Approval
PR01
High
P024
PR04
PO Approval Release Blocked Invoices AP Payments
MM06
Add or modify material master data and release an order for personal use
Medium
P025
AP03
PR05
Modify a purchasing agreement and release a previously blocked invoice to offset the vendor account.
Medium
P026
AP01
PR05
Purchasing Agreements
Enter fictitious purchasing agreements and then render payment
High
Page 4 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 P027
PR01
FunctionID
Function 2 Purchasing Agreements
Mitigation ID
Function
Function 3
Description of Risk
Risk of entry of fictitious Purchasing Agreements and the entry of fictitious Vendor or modification of existing Vendor especially account data.
Risk Level
High
Vendor Master Maintenance
PR05
P028
PR05
Purchasing Agreements
MM05
Goods Receipts to PO
Modify purchasing agreements and then receive goods for fraudulent purposes. Enter unauthorized items to a purchasing agreement and create an invoice to obtain those items for personal use Risk of modifying service master data (to add a service that is normally not ordered by the company) and the entry of covering payments Risk of addition of services to the Service Master File (services not related to business purpose) and the ability to create a Requisition for those services. Risk of entering or maintaining a purchasing agreement and authorizing the related requisition through its release.
High
P029
AP02
Process Vendor Invoices
PR05
Purchasing Agreements Service Master Maintenance Release Requisitions
High
P030
AP01
AP Payments Service Master Maintenance
PR03
High
P031
PR03
PR06
Medium
P032
PR06
Release Requisitions
PR05
Purchasing Agreements
Medium
P033
PR07
Requisitioning
PR02
Maintain Purchase Order Service Master Maintenance Enter Counts & Clear Diff - IM Requisitioning
Risk of the same person requisitioning an item and creating a purchase order from that requisition. Add items to the service master file and create fraudulent purchase orders for those items Risk of the same person entering a Purchasing Agreement for materials and then adjusting the IM inventory for those materials. Risk of modifying or adding to material master data (to add material that normally is not ordered by the company) and then the release of a material requisition. Risk of the same person requisitioning an item and then releasing a requisition for purchase, bypassing the authorization process.
Medium
P034
PR02
Maintain Purchase Order
PR03
Medium
P035
PR05
Purchasing Agreements Maintain Material Master Data Requisitioning
MM03
Medium
P036
MM06
PR07
Medium
P037
PR07
PR06
Release Requisitions
Medium
P038
AP01
AP Payments
FI03
Bank Reconciliation
Risk of entering unauthorized payments and reconcile with the bank through the same person.
High
P039
AP02
Process Vendor Invoices
PR08
Service Acceptance
Risk of entering Vendor invoices and the ability to accept those services in the Service Receipts Entry. Risk of the same person releasing a requisitioning and generating the accompanying purchase order.
Medium
P040
PR06
Release Requisitions
PR02
Maintain Purchase Order
Medium
P041
PR03
Service Master Maintenance
PR05
Purchasing Agreements
Add an item to the material master or service master file and then fraudulently adding those items to purchasing agreements
Medium
P042
PR04
PO Approval Release Blocked Invoices
PR03
Service Master Maintenance PO Approval
Add or modify service master data and release an order for personal use
Medium
P043
AP03
PR04
Release a purchase order and release a previously blocked invoice to offset the vendor account.
Medium
Page 5 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 P044
PR04
FunctionID PR08
Function 2 Service Acceptance
Mitigation ID
Function
Function 3
Description of Risk
Release a fictitious purchase order for personal use and accept the services through service acceptance
Risk Level
Medium
PO Approval
P045
PR02
Maintain Purchase Order
MM02
Enter Counts - IM
MM01
Clear Differences Inventory Management Clear Differences - WM
Inappropriately procure an item and manipulating the IM physical inventory counts to hide. Inappropriately procure an item and manipulating the WM physical inventory counts to hide. Release a non bona-fide purchase order and the action remain undetected by manipulating the IM physical inventory counts Release a non bona-fide purchase order and the action remain undetected by manipulating the WM physical inventory counts Risk of the same person entering a Purchasing Agreement for materials and then adjusting the IM inventory for those materials. Risk of the same person entering a Purchasing Agreement for materials and then adjusting the WM inventory for those materials.
High
P046
PR02
Maintain Purchase Order
MM07
Enter Counts - WM Enter Counts & Clear Diff - IM Enter Counts - WM
MM08
High
P047
PR04
PO Approval
MM03
High
P048
PR04
PO Approval
MM07
MM08
Clear Differences - WM Clear Differences Inventory Management Clear Differences - WM
High
P049
PR05
Purchasing Agreements
MM02
Enter Counts - IM
MM01
Medium
P050
PR05
Purchasing Agreements Manual Check Processing Process Vendor Invoices
MM07
Enter Counts - WM Vendor Master Maintenance Manual Check Processing Manual Check Processing Manual Check Processing Manual Check Processing
MM08
Medium
P051
AP04
PR01
Maintain a fictitious vendor and create a payment to that vendor
High
P052
AP02
AP04
Enter fictitious vendor invoices and then render payment to the vendor
High
P053
PR02
Maintain Purchase Order
AP04
Enter a fictitious purchase order and enter the covering payment
High
P054
PR08
Service Acceptance
AP04
Receive or accept services and manually enter the covering check payments Commit the company to fraudulent purchases and initiate manual check payments for unauthorized goods and services.
High
P055
PR04
PO Approval
AP04
High
P056
AP04
Manual Check Processing Manual Check Processing Manual Check Processing Maintain Purchase Order
PR05
Purchasing Agreements
Enter fictitious purchasing agreements and then render manual checks for payment
High
P057
AP04
PR03
Service Master Maintenance Bank Reconciliation
Risk of modifying service master data (to add a service that is normally not ordered by the company) and the entry of covering payments Risk of entering unauthorized manual payments and reconcile with the bank through the same person. Where release strategies are utilized, the same user should not maintain the purchase order and release or approve it. The automated controls for invoicing can be circumvented. Invoices are usually blocked due to price or quantity differences.
High
P058
AP04
FI03
High
P059
PR02
PR04
PO Approval Release Blocked Invoices AP Payments
High
P060
AP02
Process Vendor Invoices Maintain Vendor Pricing Conditions
AP03
Medium
P061
PR11
AP01
Transactional processing should be segregated from pricing master data.
Medium
Page 6 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 P062
PR11
FunctionID AP02
Function 2 Process Vendor Invoices Release Blocked Invoices Manual Check Processing
Mitigation ID
Function
Function 3
Description of Risk
Transactional processing should be segregated from pricing master data.
Risk Level
Medium
Maintain Vendor Pricing Conditions Maintain Vendor Pricing Conditions Maintain Vendor Pricing Conditions Maintain Vendor Pricing Conditions Maintain Vendor Pricing Conditions Maintain Vendor Pricing Conditions
P063
PR11
AP03
Transactional processing should be segregated from pricing master data.
Medium
P064
PR11
AP04
Transactional processing should be segregated from pricing master data.
Medium
P065
PR11
PR04
PO Approval
Transactional processing should be segregated from pricing master data.
Medium
P066
PR11
PR06
Release Requisitions
Transactional processing should be segregated from pricing master data.
Medium
P067
PR11
PR07
Requisitioning
Transactional processing should be segregated from pricing master data.
Medium
Order to Cash S001
AR04
Credit Management
SD05
Sales Order Processing
Enter or modify sales documents and approve customer credit limits
High
S002
SD05
Sales Order Processing
AR03
Clear Customer Balance
Create sales documents and immediately clear customer's obligation
High
S003
SD05
Sales Order Processing
SD01
Maintain Customer Master Data Process Customer Invoices
Create a fictitious customer and initiate fraudulent sales document
High
S004
SD01
Maintain Customer Master Data Maintain Customer Master Data
AR07
Make an unauthorized change to the master record (payment terms, tolerance level) in favor of the customer and enter an inappropriate invoice. Inappropriately create or change rebate agreements and manage a customer's master record in the favor of the customer. Could also change a customer's master record to direct payment to an inappropriate location. Potentially clear a customer's balance before and create or make the same change to the billing document for the same customer, clearing them of their obligation. Inappropriately create or change a sales documents and generate a corresponding billing document for it. Manipulate the user's credit limit and assign generous rebates to execute a marginal customer's order.
High
S005
SD01
SD03
Sales Rebates
High
S006
AR03
Clear Customer Balance
AR05
Maintain Billing Documents Maintain Billing Documents Sales Rebates
High
S007
SD05
Sales Order Processing
AR05
High
S008
AR04
Credit Management
SD03
High
S009
SD05
Sales Order Processing
AR02
Cash Application Maintain Billing Documents AR Payments
Enter a fictitious sales document and then render fictitious payments.
Medium
S010
AR02
Cash Application Maintain Customer Master Data
AR05
Create a billing document for a customer and inappropriately post a payment from the same customer to conceal non-payment. Create a fictitious customer and initiate payment to the unauthorized customer.
High
S011
SD01
AR01
High
Page 7 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 S012
AR06
FunctionID AR01
Function 2 AR Payments Sales Document Release Delivery Processing
Mitigation ID
Function
Function 3
Description of Risk
Initiate an unauthorized payment to the customer by entering fictitious credit memos. Change the accounts receivable records to cover differences with customer statements.
Risk Level
High
Process Customer Credit Memos Cash Application
S013
AR02
SD04
High
S014
SD05
Sales Order Processing Process Customer Invoices Sales Order Processing
SD02
Cover up unauthorized shipment by creating a fictitious sales documents
High
S015
AR07
SD06
Sales Pricing Condition
Sales price modifications for sales invoicing.
High
S016
SD05
SD06
Sales Pricing Condition
Enter sales documents and lower prices for fraudulent gain
High
S017
AR04
Credit Management
AR02
Cash Application
Perform credit approval function and modify cash received for fraudulent purposes.
High
S018
AR02
Cash Application
SD03
Sales Rebates Maintain Customer Master Data Sales Document Release Sales Rebates
Enter a fictitious sales rebates and then render fictitious payments.
High
S019
AR02
Cash Application
SD01
Risk of the same person entering changes to the Customer Master file and modifying the Cash Received for the customer.
High
S020
SD05
Sales Order Processing
SD04
Risk of entering and releasing sales documents by the same person
Medium
S021
SD05
Sales Order Processing Process Customer Invoices Maintain Billing Documents Maintain Customer Master Data Maintain Customer Master Data Cash Application
SD03
Risk of entering sales documents and giving sales rebates by the same person, effectively granting an indirect price discount. Risk of modifying and entering Sales Invoices and approving Credit Limits by the same person.
Medium
S022
AR07
AR04
Credit Management
High
S023
AR05
SD06
Sales Pricing Condition
Risk of Sales Price modifications for Sales invoicing.
High
S024
SD01
AR03
Clear Customer Balance Maintain Billing Documents Process Customer Invoices Cash Application Process Customer Invoices Process Customer Credit Memos
Maintain a customer master record and post a fraudulent payment against it
High
S025
SD01
AR05
User can create a fictitious customer and then issue invoices to the customer. User can create/change an invoice and enter/change payments against the invoice. User can create fictitious/incorrect delivery and enter payments against these, potentially misappropriating goods. User able to create a fraudulent sales contract to include additional goods and enter an incorrect customer invoice to hide the deception.
High
S026
AR02
AR07
High
S027
SD02
Delivery Processing
AR02
High
S028
SD05
Sales Order Processing
AR07
High
S029
AR03
Clear Customer Balance
AR06
Create a credit memo then clear the customer to prompt a payment.
High
HR and Payroll
Page 8 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 H001
HR03
FunctionID
Function 2 Process Payroll
Mitigation ID
Function
Function 3
Description of Risk
Modify payroll master data and then process payroll. Potential for fraudulent activity.
Risk Level
High
Maintain Employee (PA) Master Data - 0008 0009 ( HR Benefits
PY04
H002
HR01
PY04
Process Payroll
Change employee HR Benefits then process payroll without authorization. Potential for fraudulent activity. Change to master data and creating the remittance could result in fraudulent payments. Change payroll master data and enter time data applied to incorrect settings.
High
H003
PY07
3rd Party Remittance
HR02
HR Vendor Data
High
H004
HR04
Maintain Time Data
PY01
Approve Time
High
H005
HR04
Maintain Time Data Maintain Payroll Configuration Maintain Employee (PA) Master Data - 0008 0009 (
PY04
Process Payroll
Modify time data and process payroll resulting in fraudulent payments
High
H006
PY02
PY04
Process Payroll
Change configuration of payroll then process payroll resulting in fraudulent payments
High
H007
HR03
PY02
Maintain Payroll Configuration Maintain Employee (PA) Master Data - 0008 0009 ( Payroll Maintenance
Change configuration of payroll then modify payroll master data resulting in fraudulent payments
High
H008
HR05
Modify PD Structure
HR03
Change payroll master data and modify PD Structure
High
H009
HR04
Maintain Time Data
PY03
Enter false time data and perform payroll maintenance.
High
H010
PY03
Payroll Maintenance Maintain Payroll Configuration Maintain Time Data
PY04
Process Payroll
Change payroll and process payroll without proper authorization.
High
H011
PY02
PY03
Payroll Maintenance Maintain Payroll Configuration Modify PD Structure
Change payroll configuration and perform maintenance on payroll settings.
High
H012
HR04
PY02
Modify payroll configuration and enter false time data.
High
H013
HR04
Maintain Time Data Maintain Employee (PA) Master Data - 0008 0009 ( Maintain Employee (PA) Master Data - 0008 0009 ( Payroll Schemas
HR05
Enter false time data and maintain PD structure
High
H014
HR03
HR04
Maintain Time Data
Users may enter false time data and process payroll resulting in fraudulent payments.
High
H015
HR03
PY03
Payroll Maintenance
Users may maintain employee master data including pay rates and delete the payroll result
High
H016
PY06
HR04
Maintain Time Data
Users may enter false time data and perform work schedule evaluations
High
H017
PY05
Time Evaluations
HR04
Maintain Time Data
Users may enter false time data and perform time evaluations
Medium
Page 9 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 H018
PY05
FunctionID HR05
Function 2 Modify PD Structure
Mitigation ID
Function
Function 3
Description of Risk
Perform time evaluations and change the PD structure to mis route the data for approvals Perform time evaluations and delete payroll results which could disrupt the payroll process Users who perform both the time evaluation and process payroll could hide fraudulent actions. Users who can perform both the time evaluations and maintain payroll schemas to hide fraudulent actions
Risk Level
Medium
Time Evaluations
H019
PY05
Time Evaluations
PY03
Payroll Maintenance
Medium
H020
PY05
Time Evaluations
PY04
Process Payroll
Medium
H021
PY05
Time Evaluations
PY06
Payroll Schemas
Medium
Basis B001
BS02
Basis Development
BS11
System Administration
MIT-B001
A developer could modify an existing program in production, perform traces to the program, and configure the production environment to run the program. This may affect system performance, data integrity and inappropriate program modification. A developer could modify an existing program in production, perform traces to the program and configure the production environment to limit monitoring of the program run by increasing alarm thresholds and eliminating audit trails through external OS comma A developer could create or modify a program in production and replicate these changes to other clients. This bypasses the inherent controls in the transport process and could negatively impact the DV and QA clients. A developer could create or modify a program in production and force the transport of these changes after the fact to conceal irregular development practices. This also enables the reverting back to the program's original version without any trace of the changes made in production. A developer could modify program components (menus, screen layout, messages, queries) and configure the production environment to execute the program with these changes. This may affect system performance, data integrity and inappropriate program modification A developer could modify program components (menus, screen layout, messages, queries) and configure the production environment to limit monitoring of the program runs using the modified program components by increasing alarm thresholds and eliminating audit trail A developer could modify program components (menus, screen layout, messages, queries) and replicate these changes to other clients. This bypasses the inherent controls in the transport process and could negatively impact the DV and QA clients. A developer could modify program components (menus, screen layout, messages, queries) and force the transport of these changes after the fact to conceal irregular development practices. This also enables the reverting back to the program components origin An individual could modify data in tables or modify valid configuration values and setup the production environment to run transactions and programs using the inappropriately modified data. This could affect data integrity, system performance, and proper An individual could modify data in tables or change valid configuration and replicate these changes to other clients. This is particularly sensitive if client administration transactions come with client-independent authorization allowing the developer to An individual could inappropriately modify roles and assignments and reflect this change to the production's mirror copy eliminating the chance to revert to the appropriate setup.
Medium
B002
BS02
Basis Development
BS06
Configuration
MIT-B002
High
B003
BS02
Basis Development
BS05
Client Administration
MIT-B003
Medium
B004
BS02
Basis Development
BS12
Transport Administration
MIT-B004
High
B005
BS04
Basis Utilities
BS11
System Administration
MIT-B005
Medium
B006
BS04
Basis Utilities
BS06
Configuration
MIT-B006
High
B007
BS04
Basis Utilities
BS05
Client Administration
MIT-B007
Medium
B008
BS04
Basis Utilities
BS12
Transport Administration
MIT-B008
High
B009
BS03
Basis Table Maintenance Basis Table Maintenance
BS11
System Administration
MIT-B009
High
B010
BS03
BS05
Client Administration
MIT-B010
High
B011
BS10
Security Administration
BS05
Client Administration
MIT-B011
High
Page 10 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 B012
BS10
FunctionID BS12
Function 2 Transport Administration
Mitigation ID
MIT-B012
Function
Function 3
Description of Risk
A security administrator could make inappropriate changes to unauthorized security roles, transport them, and assign them to a fictitious user for execution. An administrator could execute archiving transactions during peak end-user usage and administer the production system to allow for maximum system resources to complete the archiving function, affecting system performance. A user could configure the production environment to limit monitoring of the inappropriate archiving runs by increasing alarm thresholds and eliminating audit trails through external OS commands. A user could inappropriately archive client-independent data and settings and use client administration functions to replicate such changes to other clients. Usually the individuals responsible for archiving are end-users who understand the business processes and data retention needs. Their job responsibilities do not require transport administration transactions. The reverse can be said for the users responsibilities Can create transports, add objects to the transport, and move the transport: Can put unauthorized object changes into production, bypassing the Change Control process. Can reset the number ranges (1) and delete your log/audit trail (2).
Risk Level
High
Security Administration
B013
BS01
Archiving
BS11
System Administration
MIT-B013
Medium
B014
BS01
Archiving
BS06
Configuration
MIT-B014
Medium
B015
BS01
Archiving
BS05
Client Administration
MIT-B015
Medium
B016
BS01
Archiving
BS12
Transport Administration
MIT-B016
Medium
B017
BS07
Create Transport Maintain Number Ranges Maintain User Master
BS09
Perform Transport
MIT-B017
High
B018
BS08
BS11
System Administration
MIT-B018
High
B019
BS13
BS14
Maintain Profiles / Roles
MIT-B019
One person controlling both the access in the profile/role and the user Ids increases the risk of inappropriate access
High
CRM D001
CR01
Generate & Process Leads Generate & Process Leads Maintain Business Partner Process CRM Sales Order Process CRM Sales Order Process CRM Sales Order Service Order Processing
CR02
Maintain Opportunity
Maintaining Opportunities (qualifying the lead) must be independent of generating leads. Sales or Production forecast could be based on the number of qualified leads. In some companies, commissions could be paid based on the number of qualified leads. The creation of key Business Partner data should be segregated from the Marketing groups Leads and Opportunity management. BPs should only be created after the appropriate review by the Master Data group. A user could create a fictitious business partner and initiate fraudulent sales orders for that partner. Master data such as business partners should not be maintained by the same users who process transactions using that master data. A user could create a fictitious sales order to cover up an unauthorized shipment. Inappropriately create or change sales documents and generate the corresponding billing document in CRM. Inappropriately create or change sales documents and generate the corresponding billing document in R3. Enter fictitious service orders for personal use and accept the services through service acceptance. The user could prompt fraudulent payments. In addition spare parts could be fraudulently issued from inventory as a result of the confirmation. User can create a fictitious business partner and then process billing in CRM for that partner. User can create a fictitious business partner and then process billing in R3 for that partner.
Medium
D002
CR01
CR03
Maintain Business Partner Process CRM Sales Order
Medium
D003
CR03
CR04
High
D004
CR04
SD02
Delivery Processing
High
D005
CR04
CR07
CRM Billing Maintain Billing Documents
High
D006
CR04
AR05
High
D007
CR05
CR06
Service Confirmation
High
D008
CR07
CRM Billing Maintain Billing Documents
CR03
Maintain Business Partner Maintain Business Partner
High
D009
AR05
CR03
High
Page 11 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 D010
CR06
FunctionID CR07
Function 2 CRM Billing Maintain Billing Documents Process Credit Memo
Mitigation ID
Function
Function 3
Description of Risk
Inappropriately accept or confirm a service order and generate a corresponding billing document in CRM for the order. Inappropriately accept or confirm a service order and generate a corresponding billing document in R3 for the order. Internal user can be in collusion with a customer, process a fictitious inbound delivery (based on complaint entered by the customer) and process a credit memo to the customer. User could create a fictitious credit memo and run billing due in CRM to prompt a payment to a customer. The customer could provide a kickback to the internal user. User could create a fictitious credit memo and run billing due in R3 to prompt a payment to a customer. The customer could provide a kickback to the internal user. Pricing conditions could be manipulated to provide inappropriate discounts or incentives to customers which will be realized in an incorrect invoice. A user could enter a sales order in CRM and lower prices via conditions for fraudulent gain Commission or Incentives may be paid based on the number of qualified leads. Inappropriately qualified leads could result in fraudulent commission payments. Commission or Incentives may be paid based on the number of service orders. Fraudulent orders could be entered to achieve higher sales for commissions. Commission or Incentives may be paid based on the number of sales orders. Fraudulent orders could be entered to achieve higher sales reporting for commissions. Add items to product catalogs and create fictitious sales orders for those items
Risk Level High
Service Confirmation
D011
CR06
Service Confirmation Inbound Delivery Processing Process Credit Memo
AR05
High
D012
SD07
CR08
Medium
D013
CR08
CR07
CRM Billing Maintain Billing Documents Maintain Conditions
High
D014
CR08
Process Credit Memo Process Customer Invoices Process CRM Sales Order Maintain Opportunity Service Order Processing Process CRM Sales Order Maintain Product Catalog
AR05
High
D015
AR07
CR09
High
D016
CR04
CR09
Maintain Conditions
High
D017
CR02
PY04
Process Payroll
High
D018
CR05
PY04
Process Payroll
High
D019
CR04
PY04
Process Payroll Process CRM Sales Order
High
D020
CR10
CR04
Medium
SRM E001
SR01
EBP / SRM Vendor Master EBP / SRM Purchasing
SR03
EBP / SRM Invoicing
Maintain a fictitious vendor and enter an invoice to be included in the automatic payment run
High
E002
SR02
SR03
EBP / SRM Invoicing EBP / SRM Goods Receipt/Service Acceptance EBP / SRM Goods Receipt/Service Acceptance EBP / SRM Purchasing
Purchase unauthorized items and prompt the payment by invoicing
High
E003
SR02
EBP / SRM Purchasing
SR04
Enter fictitious orders for personal use and accept the goods or services through goods receipt or service acceptance
High
E004
SR03
EBP / SRM Invoicing
SR04
Enter fictitious invoices and accept goods or services via goods receipt or service acceptance
High
E005
SR01
EBP / SRM Vendor Master EBP / SRM Purchasing
SR02
Maintain a fictitious vendor and initiate purchases to that vendor.
High
E006
SR02
MM07
Enter Counts - WM
MM08
Clear Differences - WM Clear Differences Inventory Management
Inappropriately procure items and manipulate the WM physical inventory counts to hide. Inappropriately procure items and manipulate the IM physical inventory counts to hide.
Medium
E007
SR02
EBP / SRM Purchasing
MM02
Enter Counts - IM
MM01
Medium
Page 12 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 E008
SR02
FunctionID MM03
Function 2 Enter Counts & Clear Diff - IM
Mitigation ID
Function
Function 3
Description of Risk
Inappropriately procure items and manipulate the IM physical inventory counts to hide.
Risk Level Medium
EBP / SRM Purchasing
E009
SR05
EBP / SRM Product Maintenance
SR02
EBP / SRM Purchasing
Add items to the catalog or master file and create fraudulent orders for those items.
Medium
E010
FI03
Bank Reconciliation EBP / SRM Goods Receipt/Service Acceptance EBP / SRM Goods Receipt/Service Acceptance EBP / SRM Goods Receipt/Service Acceptance EBP / SRM Purchasing
SR03
EBP / SRM Invoicing
A user can hide differences between bank payments and posted AP records.
High
E011
SR06
MM07
Enter Counts - WM
MM08
Clear Differences - WM
Accept goods via SRM goods receipts and perform a WM physical inventory adjustment afterwards.
High
E012
SR06
MM02
Enter Counts - IM
MM01
Clear Differences Inventory Management
Accept goods via SRM goods receipts and perform IM physical inventory adjustment afterwards.
High
E013
SR06
MM03
Enter Counts & Clear Diff - IM
Accept goods via SRM goods receipts and perform IM physical inventory adjustment afterwards using powerful IM transactions
High
E014
SR02
MM05
Goods Receipts to PO
Enter fictitious orders for personal use and access the goods or services through goods receipt Enter fictitious orders for personal use and access the goods or services through service acceptance
High
E015
SR02
EBP / SRM Purchasing
PR08
Service Acceptance
High
E016
SR08
EBP / SRM Maintain Shopping Cart
SR05
EBP / SRM Product Maintenance
Initiate purchases for fictitious goods by selecting those goods to be included in a shopping cart
Medium
E017
SR08
EBP / SRM Maintain Shopping Cart
SR01
EBP / SRM Vendor Master EBP / SRM Goods Receipt/Service Acceptance
Maintain a fictitious vendor and initiate purchases to that vendor by selecting goods to be included in a shopping cart
Medium
E018
SR07
EBP / SRM PO Approval
SR04
Approve the purchase of unauthorized goods and hide the misuse of inventory by not fully receiving the order in SRM
Medium
E019
SR07
EBP / SRM PO Approval
MM05
Goods Receipts to PO
Approve the purchase of unauthorized goods and hide the misuse of inventory by not fully receiving the order in R3
High
E020
SR02
EBP / SRM Purchasing
SR07
EBP / SRM PO Approval
Where release strategies are utilized, the same user should not maintain the purchase order and release or approve it.
High
E021
SR01
EBP / SRM Vendor Master
SR07
EBP / SRM PO Approval
Create a fictitious vendor or change existing vendor master data and approve purchases to this vendor
High
E022
SR02
EBP / SRM Purchasing
SR09
EBP / SRM Maintain Org Structure
Enter fictitious orders for personal use and manipulate the organizational structure to bypass approvals
High
Page 13 of 15
Segregation of Duty Risks
Risk ID FunctionID Function 1 E023
SR01
FunctionID
Function 2 EBP / SRM Maintain Org Structure
Mitigation ID
Function
Function 3
Description of Risk
Create or maintain fictitious vendor and manipulate the organizational structure to bypass approvals or secondary checks
Risk Level High
EBP / SRM Vendor Master
SR09
E024
SR08
EBP / SRM Maintain Shopping Cart
SR07
EBP / SRM PO Approval
Initiate purchases to selecting goods to be included in a shopping cart then approving the purchase
High
EC-CS (Assumption - Data is uploaded to the Consolidation system. Additional risks may need to be defined for fully integrated systems) G001
EC01
Maintain Hierarchies
AP01
AP Payments
MIT-G001
AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output AP/AR/GL master data creation and posting functions in conjunction with payment processing, receipt of money, GL account access; and the ability to modify ECCS hierarchy and reporting output
High
G002
EC01
Maintain Hierarchies
AP02
Process Vendor Invoices Manual Check Processing Cash Application Process Customer Invoices Maintain Cost Centers Maintain Asset Document Maintain Asset Master
MIT-G002
High
G003
EC01
Maintain Hierarchies
AP04
MIT-G003
High
G004
EC01
Maintain Hierarchies
AR02
MIT-G004
High
G005
EC01
Maintain Hierarchies
AR07
MIT-G005
High
G006
EC01
Maintain Hierarchies
CC03
MIT-G006
High
G007
EC01
Maintain Hierarchies
FA01
MIT-G007
High
G008
EC01
Maintain Hierarchies
FA02
MIT-G008
High
G009
EC01
Maintain Hierarchies
FI01
Revenue Reposting
MIT-G009
High
G010
EC01
Maintain Hierarchies
GL01
Post Journal Entry
MIT-G010
High
G011
EC01
Maintain Hierarchies
GL02
Maintain GL Master Data Post Journal Entry (misc Tax/Currency) Vendor Master Maintenance Maintain Customer Master Data
MIT-G011
High
G012
EC01
Maintain Hierarchies
GL03
MIT-G012
High
G013
EC01
Maintain Hierarchies
PR01
MIT-G013
High
G014
EC01
Maintain Hierarchies
SD01
MIT-G014
High
Page 14 of 15
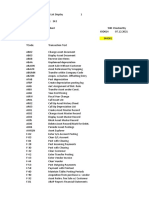
Functional Area Finance / Controlling Manufacturing Procure to Pay Order to Cash HR Basis CRM
Novus Monitor & Approver Davud Friedman Steve Bass
Email Address Davud.Friedman@novusint.com Stephen.Bass@novusint.com
Mark Meyer
Mark.Meyer@novusint.com
Вам также может понравиться
- SOD and Critical Action Ruleset Review - Feedback Received - Consolidatedv6-RACM ReviewДокумент1 страницаSOD and Critical Action Ruleset Review - Feedback Received - Consolidatedv6-RACM ReviewDenys Pavez VeraОценок пока нет
- GRC RulesetДокумент6 страницGRC RulesetDAVIDОценок пока нет
- SAP GRC SOD Conflicts High RiskДокумент12 страницSAP GRC SOD Conflicts High RiskRyan Pitts100% (6)
- List of SOD Conflicts - 1.29.18Документ16 страницList of SOD Conflicts - 1.29.18fanoustОценок пока нет
- Sod-Analyze Using MS ExcelДокумент9 страницSod-Analyze Using MS ExcelJeethender KummarikuntaОценок пока нет
- List of SOD Conflicts - 1.29.18Документ5 страницList of SOD Conflicts - 1.29.18YasserAl-mansourОценок пока нет
- SAP GRC SOD Conflicts High RiskДокумент32 страницыSAP GRC SOD Conflicts High RiskSridharan GovindarajОценок пока нет
- Segregation of DutiesДокумент1 страницаSegregation of DutiesjadfarranОценок пока нет
- SAP Technical AuditДокумент5 страницSAP Technical AuditSuryanarayana TataОценок пока нет
- Sox Compliance ChecklistДокумент6 страницSox Compliance Checklistsiddhesh8Оценок пока нет
- SAP - Audit FindingsДокумент22 страницыSAP - Audit FindingsCristina BancuОценок пока нет
- SOD MatrixДокумент1 страницаSOD MatrixAjai SrivastavaОценок пока нет
- Auditing SAP GRC PDFДокумент45 страницAuditing SAP GRC PDFAnywhere100% (1)
- GR C 10 TrainingДокумент76 страницGR C 10 TrainingChandresh BajpaiОценок пока нет
- Segregation of Duties OverviewДокумент1 страницаSegregation of Duties OverviewKarthik EgОценок пока нет
- SAP Security Audit Guidelinses - SAP Security Easy Way To Learn Sap Security!!Документ9 страницSAP Security Audit Guidelinses - SAP Security Easy Way To Learn Sap Security!!lcky141Оценок пока нет
- Top 20 GRC SoD List For SAP SystemДокумент1 страницаTop 20 GRC SoD List For SAP SystemIndiver RaichandОценок пока нет
- Segregation of Duties ReviewДокумент17 страницSegregation of Duties ReviewPabitraKumarОценок пока нет
- Security and Control For SAP R3Документ220 страницSecurity and Control For SAP R3jacquescork83% (6)
- Security: Tier I Audit GuideДокумент6 страницSecurity: Tier I Audit GuideLavinia GligaОценок пока нет
- Final SAP - Audit ChecklistДокумент15 страницFinal SAP - Audit ChecklistSambhaji Chawale100% (1)
- SOD Risk Summary SAP With Mitigating ControlsДокумент14 страницSOD Risk Summary SAP With Mitigating ControlsArun Racharla100% (1)
- Segregation of DutiesДокумент46 страницSegregation of DutiesYai Ibrahim100% (2)
- SAP Basis Security Audit Program PreviewДокумент10 страницSAP Basis Security Audit Program PreviewrajankthomasОценок пока нет
- Sod AnalyzeДокумент9 страницSod AnalyzeChim RaОценок пока нет
- Top 20 SOD Conflicts in SAPДокумент2 страницыTop 20 SOD Conflicts in SAPsarfarazukОценок пока нет
- Role Designer For SAPДокумент22 страницыRole Designer For SAPanh tho0% (1)
- Procurement and AP - SoD FinalДокумент4 страницыProcurement and AP - SoD FinalManishОценок пока нет
- SOD MatrixДокумент1 страницаSOD Matrixsakthy82Оценок пока нет
- GRC 12Документ52 страницыGRC 12bandila.samuel100% (1)
- Sap R 3 Accounts Payable MatrixДокумент19 страницSap R 3 Accounts Payable Matrixpaichowzz100% (1)
- Sod MatrixДокумент2 382 страницыSod Matrixbarber bob0% (2)
- Authorization MatrixДокумент2 страницыAuthorization MatrixArunKhemaniОценок пока нет
- Top 20 SAP ConflictsДокумент12 страницTop 20 SAP ConflictsAndrew MalcolmsonОценок пока нет
- Matriz Sod SapДокумент10 страницMatriz Sod SapEduardo EdОценок пока нет
- Apps Segregation of DutiesДокумент31 страницаApps Segregation of DutiesMahmoud Fawzy100% (1)
- SAP Security DesignДокумент28 страницSAP Security DesignJose Garcia50% (4)
- Sap GRC Risk Analysis and RemediationДокумент38 страницSap GRC Risk Analysis and RemediationShiva Kumar0% (1)
- CS - Authorization Matrix V1.0Документ4 страницыCS - Authorization Matrix V1.0anupam0022Оценок пока нет
- Segregation of Duties Template2Документ5 страницSegregation of Duties Template2are2007Оценок пока нет
- SoD Analysis and Access GovernanceДокумент8 страницSoD Analysis and Access Governancevansh143Оценок пока нет
- SAP Audit and Control PointsДокумент9 страницSAP Audit and Control Pointsmani197Оценок пока нет
- SOD Risk Summary SAP With MitigatingДокумент16 страницSOD Risk Summary SAP With Mitigatingpreeti singhОценок пока нет
- Segregation of Duties MatrixДокумент13 страницSegregation of Duties MatrixForumnoj100% (1)
- C23 - Segregation of DutiesДокумент16 страницC23 - Segregation of Dutieskannie_bОценок пока нет
- Segregation of Duties QuestionnaireДокумент25 страницSegregation of Duties QuestionnaireManna MahadiОценок пока нет
- SAP Audit Guide ExpenditureДокумент8 страницSAP Audit Guide ExpenditurescribdjpdОценок пока нет
- SAP GRC (Basic) ,: Biju (Jays)Документ42 страницыSAP GRC (Basic) ,: Biju (Jays)Peter PanterОценок пока нет
- SAP Audit Guide BasisДокумент10 страницSAP Audit Guide BasispchoiОценок пока нет
- SAP Security Configuration and Deployment: The IT Administrator's Guide to Best PracticesОт EverandSAP Security Configuration and Deployment: The IT Administrator's Guide to Best PracticesОценок пока нет
- SAP Security Interview Questions, Answers, and ExplanationsОт EverandSAP Security Interview Questions, Answers, and ExplanationsРейтинг: 4 из 5 звезд4/5 (3)
- Mundosap - Risk - TXДокумент57 страницMundosap - Risk - TXCesar ArevaloОценок пока нет
- SAP FI Transaction Code List 1Документ9 страницSAP FI Transaction Code List 1Leonardo Barbosa SilvaОценок пока нет
- 21 Sap Fico TR CodesДокумент33 страницы21 Sap Fico TR CodesSaurabh ChaplotОценок пока нет
- SAP TCodeДокумент2 страницыSAP TCodeAman Singh KauravОценок пока нет
- CL-9 SAP AuthorizationДокумент13 страницCL-9 SAP AuthorizationEVAОценок пока нет
- SAP FICO - Accounting Transactions ListДокумент18 страницSAP FICO - Accounting Transactions ListSudhakar PotnuruОценок пока нет
- Accounting T Codes91011245389659Документ18 страницAccounting T Codes91011245389659Jayanth MaydipalleОценок пока нет
- MM SD Fico GL Sod RisksДокумент23 страницыMM SD Fico GL Sod RisksAbhijit PodderОценок пока нет
- What Is A System LandscapeTMSДокумент12 страницWhat Is A System LandscapeTMSAbhijit PodderОценок пока нет
- Workflow PR Release StrategyДокумент10 страницWorkflow PR Release StrategyAbhijit PodderОценок пока нет
- Sod MatrixДокумент9 страницSod MatrixAbhijit Podder100% (1)
- MM SD Fico GL Sod RisksДокумент23 страницыMM SD Fico GL Sod RisksAbhijit PodderОценок пока нет
- Lecture ISO9001Документ32 страницыLecture ISO9001Huseyn AgayevОценок пока нет
- Mindmap For Global Logistics Integration Ism EyefreightДокумент1 страницаMindmap For Global Logistics Integration Ism EyefreightEdison Reus SilveiraОценок пока нет
- Strategic Management Bookoff and The Book Retail Industry in JapanДокумент8 страницStrategic Management Bookoff and The Book Retail Industry in JapanNicko FabrianoОценок пока нет
- CHAPTER 1 - History of Kaizen & Lean ManagementДокумент8 страницCHAPTER 1 - History of Kaizen & Lean Managementsam100% (1)
- ZARAДокумент42 страницыZARATiên Nguyễn ThủyОценок пока нет
- Local Literature3Документ5 страницLocal Literature3Nica GuerreroОценок пока нет
- Munoz Villamizar2021Документ13 страницMunoz Villamizar2021Syahwa RamadhanОценок пока нет
- The Future of Talent Management: Four Stages of Evolution: An Oracle White Paper June 2012Документ19 страницThe Future of Talent Management: Four Stages of Evolution: An Oracle White Paper June 2012aini amanОценок пока нет
- 24 Inventories HWДокумент4 страницы24 Inventories HWSandeep JaiswalОценок пока нет
- Nikhil G Suresh: ProfileДокумент4 страницыNikhil G Suresh: ProfileNikhil SureshОценок пока нет
- Anshika+Chitranshi Digital+MarketingДокумент1 страницаAnshika+Chitranshi Digital+MarketingGaurav kushwahaОценок пока нет
- The Amazon FBA Business Model ExplainedДокумент9 страницThe Amazon FBA Business Model ExplainedShaheryar AhmedОценок пока нет
- Gkingdom Moonligt Enterprises LTD Export Acceleration Program 2021/2021Документ4 страницыGkingdom Moonligt Enterprises LTD Export Acceleration Program 2021/2021SCHAEFFER CAPITAL ADVISORSОценок пока нет
- Internal Audit Checklist StoresДокумент2 страницыInternal Audit Checklist Storesdhir.ankurОценок пока нет
- CB Case Study Submission - ReportДокумент7 страницCB Case Study Submission - ReportSURABHI SUSHREE NAYAKОценок пока нет
- Astha School of Management 2 Semester Sub: Fundamentals of It & Erp (18mba207) Module - LLL (MCQS)Документ12 страницAstha School of Management 2 Semester Sub: Fundamentals of It & Erp (18mba207) Module - LLL (MCQS)MD Rehan100% (1)
- 1633 Quan LuuДокумент15 страниц1633 Quan LuuNguyen Duc Manh (FGW HN)Оценок пока нет
- Jbptunikompp GDL Nureffendi 23781 3 Ch08Документ24 страницыJbptunikompp GDL Nureffendi 23781 3 Ch08May JangkumОценок пока нет
- Computer Information in The EnterpriseCh02 PDFДокумент30 страницComputer Information in The EnterpriseCh02 PDFภาณุพงศ์ วิจิตรทองเรืองОценок пока нет
- Marketing in Hospitality IndustryДокумент77 страницMarketing in Hospitality IndustrySheena HarrienОценок пока нет
- Total Quality Management and RewardДокумент4 страницыTotal Quality Management and RewardUdaykumar PhatakОценок пока нет
- SCMДокумент1 страницаSCMrajamovie0% (9)
- OTC-28118-MS Planned Shutdown Time Optimization Using Lean Six SigmaДокумент10 страницOTC-28118-MS Planned Shutdown Time Optimization Using Lean Six SigmaAymenОценок пока нет
- Understanding Service Operations StrategyДокумент35 страницUnderstanding Service Operations StrategyJOHN DAVID DELTOОценок пока нет
- Plastic WeldingДокумент9 страницPlastic WeldingTrecita BacoОценок пока нет
- Amazon Fulfillment ProcessДокумент1 страницаAmazon Fulfillment ProcessRAHUL RNAIRОценок пока нет
- Principles of Marketing Canadian 9th Edition Kotler Test BankДокумент25 страницPrinciples of Marketing Canadian 9th Edition Kotler Test BankKaylaSmithdbwf100% (37)
- Supply Chain DriversДокумент26 страницSupply Chain DriversHaris AlviОценок пока нет
- Workday Standard Reports - NivasДокумент294 страницыWorkday Standard Reports - NivasAnnam Raju Sai GopiОценок пока нет
- Accenture 10K 20101026Документ144 страницыAccenture 10K 20101026Rucha ShahОценок пока нет