Академический Документы
Профессиональный Документы
Культура Документы
Consti
Загружено:
Mar Sayos DalesИсходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Consti
Загружено:
Mar Sayos DalesАвторское право:
Доступные форматы
1
THE 1987 PHILIPPINE CONSTITUTION PROVISION OF
ARTICLE XVI SECTION 10 AND ITS RELATION TO THE
CYBERCRIME PREVENTION ACT OF 2012
A Term Paper
Presented to
Prof. Segundo E. Sim
Social Science Department
College of Liberal Arts
De La Salle University-Dasmarias
In Partial Fulfillment of the Requirements
in Philippine Constitution
Presented by:
Marielle Diane S. Dales
Psychology 1-1
February, 2013
TABLE OF CONTENTS
Page
I. Preliminaries
Title Page
Table of Contents
ii
Introduction
iii
Study of Related Literature/Studies
Methodology
xxi
Presentation, Analysis, Interpretation of Data
xxii
Summarization, Conclusion, Recommendation, Application
xxvii
II.
III.
References
xxix
Chapter 1
INTRODUCTION
The State shall provide the policy environment for the full development of
Filipino capability and the emergence of communication structures suitable to the
needs and aspirations of the nation and the balanced flow of information into, out
of, and across the country, in accordance with a policy that respects the freedom
of speech and of the press.
-Article 16 Section 10 1987 Philippine Constitution
The Philippines is now in the age of globalization and information
technology. With the internet as the fastest growing medium of communication
and a tool of the mass media to provide news and information, there are
instances that this technology is used to commit deception. In the year 2000, the
I Love You Virus in the computers of the United States and other countries
brought damage which a Filipino named Reomel Ramores and Onel de Guzman.
During that time, the Philippines have no Information Technology Law yet that
became the reason for the Philippine Government to drop the case. With this
situation, Philippine Congress enacted a law E-Commerce Act of 2000 or
Republic Act 8792. The objective of the law aims to facilitate domestic and
international dealings, transactions, arrangements agreements, contracts and
exchanges and storage of information through the utilization of electronic, optical
and similar medium, mode, instrumentality and technology to recognize the
authenticity and reliability of electronic documents related to such activities and
to promote the universal use of electronic transaction in the government and
general
public.
Other
laws
regarding
Information
and
Communication
Technology are the provisions in Intellectual Property Code of the Philippines or
R.A. 8293 and Optical Media Act of 2003 or RA 9239.
We must emphasize that even though the Philippines has already laws on
this aspect, the laws and government policies must be responsive to the
changing times. Thus, the Philippine Congress created the so-called Cybercrime
Prevention Act of 2012 or Republic Act 10175 which was signed into law by
President Noynoy Aquino on September 2012. Section 4 of the law states the
Cybercrime Offenses such as Illegal Access, Illegal Interception, Misuse of
Devices, Cyber-Squatting, Cybersex, Computer related fraud, Computer related
Identity Theft and others which the Declaration of State Policy Section 2 in the
law states that The State also recognizes the importance of providing an
environment conducive to the development, acceleration, and rational application
and exploitation of information and communications technology (ICT) to attain
free, easy, and intelligible access to exchange and / or delivery of information,
and the need to protect and safeguard the integrity of computer, computer and
communications systems, networks, and databases, and the confidentiality,
integrity, and availability of information, and data stored therein, from all forms of
misuse, abuse, and illegal access by making punishable under the law such
conduct or conducts. In this light, the State shall adopt sufficient powers to
effectively prevent and combat such offenses by facilitating their detection,
investigation, and prosecution at both the domestic and international levels, and
by providing arrangements for fast and reliable international cooperation. But
there are some provisions in the law which is detrimental to the right of privacy
and communication, freedom of speech and other civil liberties enshrined in the
1987 Philippine Constitution Article 3 Bill of Rights. The controversial provision of
Internet Libel in Section 4 and 6 and Section 19 of the Takedown Clause of
Department of Justice without any warrant from the Court are the contentious to
the individual rights of the Filipinos. Recently, the Supreme Court had the oral
arguments on the constitutionality of the Cybercrime Law. This debatable issue
of State Power to protect the General Welfare of the People and the Individual
Freedom of the Filipinos stated in the Bill of Rights are the main focal point to
amend or repeal this law.
Is the 1987 Philippine Constitution Article 16 Section 10 Balanced Flow of
Information into, out of and across the country, in accordance with a policy that
respects the freedom of speech and of the press can be achieved with
Cybercrime Prevention Act of 2012.
Chapter 2
STUDY OF RELATED LITERATURE
This research part of the study contained information gathered from
books, journals, magazines, other periodicals, researches and online-sources
that provided the researcher with comprehensive review of the topic and the
necessary background knowledge to perform this study.
1987 Philippine Constitution: Police Power and Bill of Rights
According to Cruz(2007) in the book Constitutional Law, Constitutional
Law is the study of the maintenance of the proper balance between authority as
represented by the three inherent powers of the State and liberty as guaranteed
by the Bill of Rights. The true role of Constitutional Law is to effect an equilibrium
between authority and liberty so that rights are exercised within the framework of
the law and the laws are enacted with due deference to rights. The 1987
Philippine Constitution enshrined the three inherent powers of the State namely:
Police Power, the Power of Eminent Domain and the Power of Taxation. In the
three fundamental powers of the State, the Police Power is the most strongest
and powerful among the three. It is the power of the State to regulate liberty and
property for the promotion of the general welfare of the people. The exercise of
the police power is with the Congress acting as a law-making body. There is also
valid delegation of legislative powers to the following: the President,
Administrative Bodies and. Local Government Legislative Bodies. The test to
determine the validity of the police measures are the following: The interest of the
public generally as distinguished from those of a particular class, require the
exercise of the police power or the Lawful Subject and The means employed are
reasonably necessary for the accomplishment of the purpose and not unduly
oppressive or the Lawful Means. According to Cruz(2007) in the book
Constitutional Law, The Lawful Subject means that the subject of the measure is
within the scope of the police power, that is , that the activity or property sought
to be regulated affects the public welfare while Lawful Means must be pursued
through a lawful method; that is, both the end and the means must be legitimate.
The two test are the safeguard of the people to determine if a law in pursuit of
Police power of the State are within its powers and not detrimental to the civil
liberties of the people.
The Bill of Rights is enshrined in Article 3 of the 1987 Philippine
Constitution. The Right against unreasonable searches and seizure and to the
privacy of communication and correspondence and the Freedom of Speech and
Expression are the civil liberties of an individual against the State if it created a
law or government action that curtails its individual rights. Article 3 Section 2
1987 Philippine Constitution states that The right of the people to be secure in
their persons, houses, papers, and effects against unreasonable searches and
seizures of whatever nature and for any purpose shall be inviolable, and no
search warrant or warrant of arrest shall issue except upon probable cause to be
determined personally by the judge after examination under oath or affirmation of
the complainant and the witnesses he may produce, and particularly describing
the place to be searched and the persons or things to be seized. The privacy of
communication and correspondence shall be inviolable except upon lawful order
of the court, or when public safety or order requires otherwise, as prescribed by
law. Any evidence obtained in violation of this or the preceding section shall be
inadmissible for any purpose in any proceeding. (Article 3 Section 3 1987
Philippine Constitution). No law shall be passed abridging the freedom of speech,
of expression, or of the press, or the right of the people peaceably to assemble
and petition the government for redress of grievances. (Article 3 Section 4 1987
Philippine Constitution). According to Cruz(2007), The importance of freedom of
expression is easily appreciated. Notably, this is the first right that is always
curtailed when a free society falls under a repressive regime. Our Constitution
provides that Sovereignty resides in the people who manifest it regularly
through their suffrages and more frequently and generally, by the assertion of
their freedom of expression.
Cybercrime Prevention Act of 2012
The Cybercrime Law was signed into law by President Benigno S. Aquino
III on September 12, 2012. It is a law that penalizes the criminal acts in the
Internet.
Here
is
the
timeline
of
the
enactment
of
the
law:
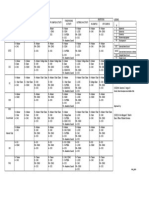
Here is the summary of the Cybercrime Prevention Act of 2012 by Janette
Toral who is the site owner of DigitallyFilipino.com website:
1. Penalizes (section 8) seventeen types of cybercrime (Section 4). They are:
Types of Cybercrime
Penalty
Prision mayor (imprisonment of six
years and 1 day up to 12 years) or
a fine of at least Two hundred
thousand pesos (P200,000) up to a
maximum amount commensurate to
the damage incurred or BOTH.
1. Illegal access
If committed
Unauthorized access (without right) to a
against critical
computer system or application.
infrastructure:Reclusion temporal
(imprisonment for twelve years and
one day up to twenty years)ora fine
of at least Five hundred thousand
pesos (P500,000) up to a maximum
amount commensurate to the
damage incurredor BOTH
2. Illegal interception
Unauthorized interception of any non-public
transmission of computer data to, from, or
- same as above
within a computer system.
3. Data Interference
Unauthorized alteration, damaging, deletion
or deterioration of computer data, electronic
document, or electronic data message, and
including the introduction or transmission of
viruses.Authorized action can also be
covered by this provision if the action of the
- same as above
10
person went beyond agreed scope resulting
to damages stated in this provision.
4. System Interference
- same as above
Unauthorized hindering or interference with
the functioning of a computer or computer
network by inputting, transmitting,
damaging, deleting, deteriorating, altering or
suppressing computer data or program,
electronic document, or electronic data
messages, and including the introduction or
transmission of viruses.Authorized action
can also be covered by this provision if the
action of the person went beyond agreed
scope resulting to damages stated in this
provision.
5. Misuse of devices
The unauthorized use, possession,
production, sale, procurement, importation,
distribution, or otherwise making available,
of devices, computer program designed or
adapted for the purpose of committing any
of the offenses stated in Republic Act
10175.Unauthorized use of computer
password, access code, or similar data by
- same as above except fine should
be no more than Five hundred
thousand pesos (P500,000).
which the whole or any part of a computer
system is capable of being accessed with
intent that it be used for the purpose of
committing any of the offenses under
Republic Act 10175.
6. Cyber-squatting
Acquisition of domain name over the
- same as above
11
Internet in bad faith to profit, mislead,
destroy reputation, and deprive others from
the registering the same. This includes
those existing trademark at the time of
registration; names of persons other than
the registrant; and acquired with intellectual
property interests in it.Those who get
domain names of prominent brands and
individuals which in turn is used to damage
their reputation can be sued under this
provision.Note that freedom of expression
and infringement on trademarks or names of
person are usually treated separately. A
party can exercise freedom of expression
without necessarily violating the trademarks
of a brand or names of persons.
7. Computer-related Forgery
Unauthorized input, alteration, or deletion of
computer data resulting to inauthentic data
with the intent that it be considered or acted Prision mayor (imprisonment of six
upon for legal purposes as if it were
years and 1 day up to 12 years) or a
authentic, regardless whether or not the
fine of at least Two hundred
data is directly readable and intelligible;
thousand pesos (P200,000) up to a
orThe act of knowingly using computer data maximum amount commensurate to
which is the product of computer-related
the damage incurred or BOTH.
forgery as defined here, for the purpose of
perpetuating a fraudulent or dishonest
design.
8. Computer-related Fraud
- same as aboveProvided, That if no
Unauthorized input, alteration, or deletion of damage has yet been caused, the
computer data or program or interference in penalty imposed shall be one (1)
12
the functioning of a computer system,
causing damage thereby with fraudulent
degree lower.
intent.
9. Computer-related Identity Theft
Unauthorized acquisition, use, misuse,
transfer, possession, alteration or deletion of - same as above
identifying information belonging to another,
whether natural or juridical.
10. Cybersex
Willful engagement, maintenance, control, or
operation, directly or indirectly, of any
lascivious exhibition of sexual organs or
sexual activity, with the aid of a computer
Prision mayor (imprisonment of six
system, for favor or consideration.There is a years and 1 day up to 12 years) or a
discussion on this matter if it involves
fine of at least Two hundred
couples or people in relationship who
thousand pesos (P200,000) but not
engage in cybersex. For as long it is not
exceeding One million pesos
done for favor or consideration, I dont think (P1,000,000) or BOTH.
it will be covered. However, if one party (in a
couple or relationship) sues claiming to be
forced to do cybersex, then it can be
covered.
11. Child Pornography
Penalty to be imposed shall be one
Unlawful or prohibited acts defined and
(1) degree higher than that provided
punishable byRepublic Act No. 9775 or the
for in Republic Act 9775, if
Anti-Child Pornography Act of 2009,
committed through a computer
committed through a computer system.
system.
12. Unsolicited Commercial
Imprisonment of arresto mayor (1
Communications (SPAMMING)
month and one day to 6 months)
The transmission of commercial
or a fine of at least Fifty thousand
communication with the use of computer
pesos (P50,000) but not exceeding
13
system which seek to advertise sell, or offer
for sale products and services are prohibited
unless:
(a) There is prior affirmative consent from
the recipient; or(b) The primary intent of the
communication is for service and / or
administrative announcements from the
sender to its existing users, subscribers or
customers; or(c) The following conditions
are present:(aa) The commercial electronic
communication contains a simple, valid, and
reliable way for the recipient to reject receipt
Two hundred fifty thousand pesos
(P250,000) or both.
of further commercial electronic messages
(opt-out) from the same source;(bb) The
commercial electronic communication does
not purposely disguise the source of the
electronic message; and(cc) The
commercial electronic communication does
not purposely include misleading information
in any part of the message in order to induce
the recipients to read the message.
13. Libel
Penalty to be imposed shall be one
Unlawful or prohibited acts of libel as
(1) degree higher than that provided
defined in Article 355 of the Revised Penal
for by the Revised Penal Code, as
Code, as amended committed through a
amended, and special laws, as the
computer system or any other similar means case may be.
which may be devised in the future.Revised
Penal Code Art. 355 states Libel means by
writings or similar means. A libel
committed by means of writing, printing,
lithography, engraving, radio, phonograph,
14
painting, theatrical exhibition,
cinematographic exhibition, or any similar
means, shall be punished by prision
correccional in its minimum and medium
periods or a fine ranging from 200 to 6,000
pesos, or both, in addition to the civil action
which may be brought by the offended
party.The Cybercrime Prevention Act
strengthened libel in terms of penalty
provisions.The electronic counterpart of libel
has been recognized since the year 2000
when the E-Commerce Law was passed.
The E-Commerce Law empowered all
existing laws to recognize its electronic
counterpart whether commercial or not in
nature.
Imprisonment of one (1) degree
14. Aiding or Abetting in the commission lower than that of the prescribed
of cybercrime Any person who willfully
penalty for the offense or a fine of at
abets or aids in the commission of any of the least One hundred thousand pesos
offenses enumerated in this Act shall be
(P100,000) but not exceeding Five
held liable.
hundred thousand pesos
(P500,000) or both.
15. Attempt in the commission of
cybercrime Any person who willfully
attempts to commit any of the offenses
- same as above
enumerated in this Act shall be held liable.
16. All crimes defined and penalized by
Penalty to be imposed shall be one
the Revised Penal Code, as amended, and (1) degree higher than that provided
special laws, if committed by, through and
for by the Revised Penal Code, as
with the use of information and
amended, and special laws, as the
15
communications technologies shall be
covered by the relevant provisions of this
case may be.
Act.
Although not exactly a cybercrime, I am
including this here as penalties are also
imposed by the law.
17. Corporate Liability. (Section 9)
When any of the punishable acts herein
defined are knowingly committed on behalf
of or for the benefit of a juridical person, by a
natural person acting either individually or as
part of an organ of the juridical person, who
has a leading position within, based on:(a) a
power of representation of the juridical
person provided the act committed falls
within the scope of such authority;(b) an
authority to take decisions on behalf of the
juridical person. Provided, That the act
committed falls within the scope of such
authority; or(c) an authority to exercise
control within the juridical person,It also
includes commission of any of the
For sanctioned actions, Juridical
person shall be held liable for a fine
equivalent to at least double the
fines imposable in Section 7 up to a
maximum of Ten million pesos
(P10,000,000).For neglect such as
misuse of computer resources that
resulted to cybercrime committed in
organization physical or virtual
premises or resources, juridical
person shall be held liable for a fine
equivalent to at least double the
fines imposable in Section 7 up to a
maximum of Five million pesos
(P5,000,000).Criminal liability may
still apply to the natural person.
punishable acts made possible due to the
lack of supervision or control.
If you are going to include all provisions in the Revised Penal Code, there can
even be more than 17 types of cybercrime as a result.
2. Liability on other laws
Section 7 has been subject to interpretation such as double-jeopardy. Lets take
the case of cybersex. For example, there is a cybersex den that forced a person
to do an act equivalent to rape and later on shown online. Rape is an offense
16
covered under Article 335 of the Revised Penal Code. The party therefore can be
sued for the crime of Cybersex under this law, Rape under Revised Penal Code,
and Crimes Against Women law. Is that considered double-jeopardy? I dont
think so.
The insertion of Libel in this law is the one that is causing a lot of confusion as it
is interpreted as a crime under this act and may be seen as separate under the
Revised Penal Code therefore giving room to double-jeopardy. From what I
gathered lately, electronic libel is the only case to be filed. The only time the case
of traditional libel will be filed under the Revised Penal Code concurrently is if the
act of libel also gets committed in traditional form simultaneously. Although they
are both separate offenses, it can also be seen as double jeopardy as traditional
libel is supposed to have recognized electronic forms with existing penalties
applying to it..
3. Jurisdiction
(a) The Regional Trial Court designated special cybercrime courts shall have
jurisdiction over any violation of the provisions of this Act including any violation
committed by a Filipino national regardless of the place of commission.
Jurisdiction shall lie if any of the elements was committed within the Philippines
or committed with the use of any computer system wholly or partly situation in the
country, or when by such commission any damage is caused to a natural or
juridical person who, at the time the offense was committed, was in the
Philippines. (section 21)
(b) For international and trans-national cybercrime investigation and prosecution,
all relevant international instruments on international cooperation in criminal
maters, arrangements agreed on the basis of uniform or reciprocal legislation,
and domestic laws, to the widest extent possible for the purposes of
investigations or proceedings concerning criminal offenses related to computer
systems and data, or for the collection of evidence in electronic form of a criminal
offense shall be given full force and effect. (section 21)
17
This gives the Philippines the ability to participate in treaties and of mutual
cooperation with countries that have counterpart legislation effectively
especially on cybercrime cases that have team members or victims residing in
the Philippines.
4. Responsibilities of the Philippine National Police (PNP) and National
Bureau of Investigation (NBI)
The law gave police authorities the mandate it needs to initiate investigation to
process the various complaints / report it gets from citizens. There are instances
of online attacks, done anonymously, where victims approach police authorities
for help. They often find themselves lost in getting investigation assistance as
police authorities cant effectively initiate an investigation (only do special
request) as their legal authority to request for logs or data does not exist at all
unless a case is already filed. (which in case of anonymously done will be hard
to initiate) I truly believe in giving citizen victims, regardless of stature, the
necessary investigation assistance they deserve. This law gave our police
authorities just that.
The PNP and NBI shall be responsible for the enforcement of this law. This
includes:
(a) The PNP and NBI are mandated to organize a cybercrime unit or center
manned by special investigators to exclusively handle cases involving violations
of this Act. (Section 10).
(b) The PNP and NBI are required to submit timely and regular reports including
pre-operation, post operation, and investigation results and such other
documents as may be required to the Department of Justice for review and
monitoring. (Section 11)
(b) Authorized to collect or record by technical or electronic means traffic data in
real time associated with specified communications transmitted by means of a
computer system. (Section 12)
18
(i) Traffic data refer only to the communications origin, destination, route, time,
date, size, duration, or type of underlying service, but not content, nor identities.
(ii) All other data to be collected or seized or disclosed will require a court
warrant. The court warrant shall only be issued or granted upon written
application and the examination under oath or affirmation of the applicant and the
witnesses he may produce and the showing: (1) that there are reasonable
grounds to believe that any of the crimes enumerated herein above has been
committed, or is being committed, is about to be committed; (2) that there are
reasonable grounds to believe that evidence that will be obtained is essential to
the conviction of any person for, or to the solution or, or to the prevention of any
such crimes, and (3) that there are no other means readily available for obtaining
such evidence.
(c) May order a one-time extension of another six (6) months on computer data
requested for preservation. Provided, That once computer data preserved,
transmitted or stored by service provider is used as evidence in a case, the mere
furnishing to such service provider of the transmittal document to the Office of the
Prosecutor shall be deemed a notification to preserve the computer data until the
termination of the case. (Section 13)
(d) Carry out search and seizure warrants on computer data. (section 15) Once
done, turn-over custody in a sealed manner to courts within 48 hours (section 16)
unless extension for no more than 30 days was given by the courts (section 15).
(e) Upon expiration of time required to preserve data, police authorities shall
immediately and completely destroy the computer data subject of a preservation
and examination. (section 17)
5. Responsibility of service providers (SP)
Service provider refers any public or private entity that provides to users of its
service the ability to communicate by means of a computer system,
and processes or stores computer data on behalf of such communication service
or users of such service. (Section 3(n).
(a) SPs are required to cooperate and assist law enforcement authorities in the
collection or recording of the above-stated information. (section 12)
19
(b) SP upon receipt of a court warrant from police authorities to disclose or
submit subscribers information, traffic data or relevant data in its possession or
control shall comply within seventy-two (72) hours from receipt of the order in
relation to a valid complaint officially docketed and assigned for investigation and
the disclosure is necessary and relevant for the purpose of investigation. (section
14)
(b) The integrity of traffic data and subscriber information relating to
communication services provided by a service provider shall be preserved for a
minimum of six (6) months period from the date of the transaction. Content data
shall be similarly preserved for six (6) months from the date of receipt of the
order from law enforcement authorities requiring its preservation.(Section 13)
(c) Once computer data preserved, transmitted or stored by service provider is
used as evidence in a case, the mere furnishing to such service provider of the
transmittal document to the Office of the Prosecutor shall be deemed a
notification to preserve the computer data until the termination of the case.
(Section 13)
(d) Upon expiration of time required to preserve data, SP shall immediately and
completely destroy the computer data subject of a preservation and examination.
(section 17)
(e) Failure to comply with the provisions of Chapter IV specifically the orders from
law enforcement authorities shall be punished as a violation of Presidential
Decree No. 1829 with imprisonment of prision correccional in its maximum period
or a fine of One hundred thousand pesos (P100,000) or both for each and every
non-compliance with an order issued by law enforcement authorities.
I think service providers participation in the implementing rules and regulation
creation will be important. They need to agree with the process on how data will
be requested and the response time needed for law enforcement to take action
especially when performing a surveillance crackdown where real-time traffic data
(communications origin, destination, route, time, date, size, duration, or type of
underlying service, but not content, nor identities) is important.
20
This is especially true for scammers targeting victims through mobile phones all
happening in a span of hours only or attacks online. Law enforcement needs to
act fast on that and service providers should be proactive in resolving it rather
than just be contented in issuing warnings reminding consumers to spot and
ignore scams, asking people to file request or complaint to block numbers at
NTC, and how to protect personal online account.
In all other details beyond traffic logs, a court order is already required. (Section
12 of Cybercrime Prevention Act of 2012)
I think at the end of the day, it is either the Service Provider offers a cooperative
win-win solution so that law enforcement can be effective in dealing with
cybercrime or be told to give its full cooperation.
Service Provider protection insofar as liability is concern is already covered under
the E-Commerce Law.
6. Responsibility of individuals
(a) Individuals upon receipt of a court warrant being required to disclose or
submit subscribers information, traffic data or relevant data in his possession or
control shall comply within seventy-two (72) hours from receipt of the order in
relation to a valid complaint officially docketed and assigned for investigation and
the disclosure is necessary and relevant for the purpose of investigation.
(b) Failure to comply with the provisions of Chapter IV specifically the orders from
law enforcement authorities shall be punished as a violation of Presidential
Decree No. 1829 with imprisonment of prision correccional in its maximum period
or a fine of One hundred thousand pesos (P100,000) or both for each and every
non-compliance with an order issued by law enforcement authorities.
7. Inadmissible evidence
(a) Any evidence procured without a valid warrant or beyond the authority of the
same shall be inadmissible for any proceeding before any court or tribunal.
(section 18)
8. Access limitation
21
(b) When a computer data is prima facie found to be in violation of the provisions
of the Cybercrime Prevention Act, the DOJ shall issue an order to restrict or
block access to such computer data. (section 19)
Note that prima facie is a higher form of evidence as it meets burden of proof
requirement at the first sight. This can include a sex scandal being shown online
where violation against our pornography laws are clear.
Prima facie is different from probable cause as this refers to suspicion requiring
further investigation.
9. Cybercrime new authorities
(a) Office of Cybercrime within the DOJ designated as the central authority in all
matters relating to international mutual assistance and extradition. (section 23)
(b) Cybercrime Investigation and Coordinating Center (CICC) an inter-agency
body to be created under the administrative supervision of the Office of the
President, for policy coordination among concerned agencies and for the
formulation and enforcement of the national cybersecurity plan. (section 24)
CICC will be headed by the Executive Director of the Information and
Communications Technology Office under the Department of Science and
Technology as Chairperson with the Director of the NBI as Vice Chairperson; the
Chief of the PNP, Head of the DOJ Office of Cybercrime; and one (1)
representative from the private sector and academe, as members. (section 25)
The CICC is the cybercrime czar tasked to ensure this law is effectively
implemented. (section 26). Although the law specifically stated a fifty million
pesos (P50,000,000) annual budget, the determination as where it would go or
allotted to, I assume shall be to the CICC.
22
Chapter 3
RESEARCH METHODOLOGY
This chapter presents the research procedures that will be employing in
the conduct of the study. These will be presented in the following sections:
1.) Research Method 2.) Subject of the Study 3.) Data Gathering 4.) Materials
used
Research Method
The descriptive method of research, employing a documentary
analysis is utilized. It will describe the nature of a situation and the gathering of
information by examining documents (Sevilla,1992).The researcher used this
method to further analyze and review the 1987 Philippine Constitution particularly
Article 16 Section 10 and its relation to Cybercrime Prevention Act of 2012..
Documentary analysis gave the researcher a glance on the Cybercrime
Prevention Act of 2012 that is seen in the necessary documents which is
detrimental on the conduct of the study.
Subject/Respondent of the Study
The focus of the study is the Cybercrime Prevention Act of 2012
and its relation to the 1987 Philippine Constitution particularly Article 16 Section
10.
Data Gathering
The researcher first secure basic information about the subject on
the newspaper items, magazine items, related books and internet sources. After
which, the researcher used some books, articles and other references that came
from the Aklatang Emilio Aguinaldo(De La Salle University-Dasmarias Library),
to further intensify the research particularly the Review of Related Literature and
Presentation of Data.
Materials Used
The researcher used the 1987 Philippine Constitution and the
Cybercrime Prevention Act of 2012 as primary source. Furthermore, the
researcher used different newspaper articles, magazines, books and the internet
as source of information to intensify this study.
23
Chapter 4
Presentation, Analysis and Interpretation of Data
In this chapter, the researcher presents pertinent facts: the data including
the interpretation and analysis to answer the relationship of the 1987 Philippine
Constitution and Cybercrime Prevention Act of 2012:
The Cybercrime Prevention Act of 2012, officially recorded
as Republic Act No. 10175, is a law in the Philippines approved on 12
September 2012. It aims to address legal issues concerning online interactions
and the Internet in the Philippines. Among the cybercrime offenses included in
the bill are cybersquatting, cybersex, child pornography, identity theft, illegal
access to data and libel. While hailed for penalizing illegal acts done via the
internet that were not covered by old laws, the act has been criticized for its
provision on criminalizing libel, which is perceived to be a curtailment in freedom
of expression. On 5 February 2013, The Supreme Court extended the temporary
restraining order on the law, "until further orders from the court.
Article 16 Section 10 1987 Philippine Constitution
The State shall provide the policy environment for the full development of
Filipino capability and the emergence of communication structures suitable to the
needs and aspirations of the nation and the balanced flow of information into, out
of, and across the country, in accordance with a policy that respects the freedom
of speech and of the press.
According to De Leon (2011), Section 10 provides the cornerstone for the
formulation of a national policy on mass media, touching on such aspects as the
right of the individual to communicate, the role of the private sector in mass
media, the involvement of the government in mass media; the use of media in
education, etc. Today, in the Philippines and the whole world internet is
considered as a data bank of news, information and communication. This
provision of the 1987 Philippine Constitution emergence of communication
structures suitable to the needs and aspirations of the nation is not only
concentrated to the traditional mass media namely: Television, Radio and
24
Newspaper. Now, Social Media in the Internet is seen as potential tool for New
Communication. Furthermore, Article 2 Section 24 of the 1987 Philippine
Constitution provides that The State recognizes the vital role of communication
and information in nation-building. The Philippines must keep abreast of
communication innovations but at the same time be selective and discriminating
to ensure that only those suitable to the needs and aspirations of the nation are
adapted. Utilized and managed wisely and efficiently, communication and
information are very useful tools for the economic, social, cultural and political
development of society.(De Leon, 2011)
SEC. 19 of R.A 10175. Restricting or Blocking Access to Computer
Data. When a computer data is prima facie found to be in violation of the
provisions of this Act, the DOJ shall issue an order to restrict or block access to
such computer data.
Section 19 is under the enforcement and implementation chapter of the
Cybercrime Law. It is violative of the constitutional prohibition against unlawful
searches and seizure and the due process clause of the Constitution. According
to Atty. Sta. Maria (resident legal analyst of News5) Section 19 of the Cybercrime
law is also a sleeping provision seriously endangering the freedom of
expression and the right to privacy of Filipinos. Section 19 is dangerous because
you are an ordinary citizen enjoying the interactive power of your computer and
the social media. You share an article in Facebook posted by somebody strongly
criticizing a high public official. You share it every day for one week so that, in
case, some of your contacts miss it, there will always be an opportunity to
immediately find and read it. The article included some unpleasant remarks
directed toward the criticized public official. Then the criticized-public official
reads the article in your Facebook page. He then approaches the Secretary of
Justice. He shows the messages to the Secretary who agrees that there appears
to be prima facie evidence (not even proof beyond reasonable doubt) of a
libellous statement in the article which is punishable under Section 4 (4) of the
new Cybercrime Law. The Secretary, using his or her Section 19-power under
25
the Cybercrime Law, issues an ORDER blocking access to your computer data.
Immediately, without any warning, your right to communicate was abated and the
opportunity to access and see your stored-information snuffed.
SEC. 6 of RA 10175. All crimes defined and penalized by the Revised
Penal Code, as amended, and special laws, if committed by, through and with
the use of information and communications technologies shall be covered by the
relevant provisions of this Act: Provided, That the penalty to be imposed shall be
one (1) degree higher than that provided for by the Revised Penal Code, as
amended, and special laws, as the case may be.
Section 6 is under the punishable acts chapter of the Cybercrime Law. It
violates the constitutional guarantees on equal protection and due process of law
It can be punishable under the Act if they are committed with, using, and through
a computer system. Among the countrys special laws, the Intellectual Property
Code penalizes, among others, illegal distribution and consumption of
copyrighted content.
The Revised Penal Code contains the general penal laws of the Philippines.
First enacted in 1930, it remains in effect today, despite several amendments
thereto. It does not comprise a comprehensive compendium of all Philippine
penal laws. The Revised Penal Code itself was enacted as Act No. 3815, and
some Philippine criminal laws have been enacted outside of the Revised Penal
Code as separate Republic Acts. The Revised Penal Code criminalizes a whole
class of acts that are generally accepted as criminal, such as the taking of a life
whether through murder or homicide, rape, robbery and theft, and treason. The
Code also penalizes other acts which are considered criminal in the Philippines,
such as adultery, concubinage, and abortion. The Code expressly defines the
elements that each crime comprises, and the existence of all these elements
have to be proven beyond reasonable doubt in order to secure conviction.
According to University of the Philippines College of Law Professor Atty. JJ
Disini, meanwhile, said that because of Section 6, the law essentially made all
crimes a form of cybercrime when committed through a computer or Internet
26
system. Other provisions in the law, Disini said, are actually ingredients to a
perfect recipe for law-enforcement agencies to crack down and monitor illegal
downloading and sharing of copyrighted content over the Internet.
Sections 19 and 6 of Cybercrime Law are violating Article 16 Section 10 of
1987 Philippine Constitution because they are both inimical and affecting
peoples freedom of speech, of expression or of the press. These sections are
incompatible with Filipinos freedom of speech. In just one click, your act can be
libellous and your own freedom of speech will be gone. According to an abscbnnews.com article, Guingona, who was the lone senator who opposed the
Senate bill on cybercrime, said the new law denies equal protection for people.
"Equal protection means all people of the same class should be treated equally.
What happens here in this law: if you violate this law using the computer,
committing libel, you are penalized one degree higher," he said. "Ordinary libel
under the revised penal code is punishable with 4 years and 2 months.
Cybercrime law says that you are punishable 6-12 years. The only difference is
that one used a pen and paper, the other used a computer," he added. "Hindi
pantay-pantay ang trato ng batas. Basically what the law is saying: anybody who
uses computers should be punished more. But [the question is] why?" he asked.
Guingona also expressed alarm at the vast powers given to the Secretary of
Justice by the law's Section 19. "When a computer data is found to be in violation
of the act, the DOJ will give an order to restrict or block access to such computer
data. This is in effect, seizure. You cannot look at it, you cannot have access to
this information," he said. Under the law, websites can be blocked even without a
court order, the senator reiterated. "It is based just upon their discretion on when
to seize. Not a judge will decide. The secretary of DOJ will decide." These two
sections are dangerous. It wont play fair. In an InterAksyon.com article, Atty.
Mel Sta. Maria pointed out: Section 1 of Article III of the Bill of Rights of the 1987
Constitution provides that no person shall be deprived of life, liberty or property
without due process of law, nor shall any person be denied the equal protection
of the laws. However, under Section 19 of the Cybercrime Prevention Act, when
27
a computer data is prima facie found to be in violation of the provisions of this
Act, the Department of Justice (DOJ) shall issue an order to restrict or block
access to such computer. No court intervention is needed; the DOJ can go right
ahead and compel you to stop publishing your posts. According to a blog
(tumblr.com) it only wants to hear nice things. If youre a law-abiding citizen
who happens to use blogs, Facebook, and Twitter to let the world know about
your beef against, say, certain elected officials who are far from being geniuses
then youve been living a lie. Under the Cybercrime Prevention Act, youre just
like any other cybercriminal. Your tweet about the barangay captain who loves
San Miguel more than his job? That could be classified as libel, which is defined
in the Revised Penal Code as the public and malicious imputation of a crime, or
of a vice or defect, real or imaginary, or any act, omission, condition, status, or
circumstance tending to cause the dishonor, discredit, or contempt of a natural or
juridical person Take note of the part where it says real or imaginary. Youre
damned if youre lying and youre damned if youre telling the truth.
The relevance of Article 16 Section 10 of 1987 Philippine Constitution to
Filipinos is to have and make a law for the development and improvement of
communication in our country without violating peoples freedom of speech, of
expression or of the press. The point is to have a law respecting and compatible
with Filipinos freedom of speech.
28
Chapter 5
Summarization, Conclusion, Recommendation, Application
This chapter presents the summary of the study, conclusion and
recommendation on the relationship of the Cybercrime Prevention Act of 2012
and the 1987 Philippine Constitution.
Summary
According to Dascil (2004), The 1987 Philippine Constitution is the
fundamental law of the land. The fundamental law acknowledged the importance
of communication and information through various provisions of it namely Article
2 Section 24 and Article 16 Section 10. In the course of new technology, our laws
should coincide with the 1987 Philippine Constitution interplay and interaction of
the Police Power and Bill of Rights. The Cybercrime Prevention Act of 2012 is a
law addressing the need to combat cybercrimes. But there are certain provisions
of the law which is now contested in the Supreme Court regarding its
constitutionality. As of now, the Supreme Court issued a Temporary Restraining
Order regarding the postponement of the implementation of the law until further
notice last February 5, 2013.
Conclusion
Indeed, the Cybercrime Prevention Act of 2012 is a pertinent law for
combating cybercrimes in our country. It is for the benefit of the Internet-users of
the Philippines. But there are certain provisions of the law that must be amended
because it is contrary to the provisions of the 1987 Philippine Constitution. In this
instance, the law will ensure that freedom of expression, speech and the press is
protected together with the general welfare of the people against cybercrimes.
Recommendation
The researcher offers the following recommendations:
1.
To Academicians and students that through this research, they may see
the importance of the Cybercrime Prevention Act of 2012 and the upholding of
the Constitutional Provision on the Bill of Rights as a vital tool for them to
understand the cyber world and its effects to the Philippine Society
29
2.
To Legislators especially the Senators and Congressmen that through this
research, they may be more productive in understanding the needed laws on
information technology for the Filipinos. They must consider the amendment of
the Cybercrime Prevention Act of 2012 especially Section 6 and Section 19
which are contrary to the provision of Article 16 Section 10 of the 1987 Philippine
Constitution and other related provisions.
3.
To the different sectors of the Philippine Society that uses the Social
Media and the Internet that through this research, they may see the importance
to fight criminality in the cyberspace. Also, it is the right time to guard the
implementation of the law after the Supreme Court decided on its constitutionality
to ensure its effectiveness and no Bill of Rights protected in the 1987 Philippine
Constitution that is violated.
4.
To the Supreme Court Justices that through this thesis, they may decide
according to the rule of law and public interest the constitutionality of the
Cybercrime Prevention Act of 2012.
5.
To Future Researchers that through this thesis, they may initiate
comprehensive researches with the implementation of the law and the impact of
it in the Philippine Society.
30
References
A. Books
Cruz, I. (2007). Constitutional Law. Quezon City: Central Law Books
Dascil, R. (2004). Threshold to the Legal Profession: An Introduction to Law.
Manila: Rex Book Store.
De Leon, H. (2011). Textbook on the Philippine Constitution Manila: Rex Book
Store.
Organista, A.F. (1995). Philippine Government and the 1987 Philippine
Constitution: Notes. Caloocan City: Philippine Graphic Arts.
Sevilla, C. et. al. (1992). Research Methods. Manila: Rex Bookstore
B. Internet Sources
Wikipedia On-Line Encyclopedia (www.wikipedia.org)
Chan Robles Virtual Law Library (www.chanrobles.com)
Rappler (www.rappler.com)
Interaksyon: The Online News Portal of News5 (www.interaksyon.com)
Digital Filipino (www.digitalfilipino.com )
Вам также может понравиться
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- 1 Sonia R. Lorenzo Award For Women in Leadership and Good GovernanceДокумент2 страницы1 Sonia R. Lorenzo Award For Women in Leadership and Good GovernanceMar Sayos DalesОценок пока нет
- Midterm - Current TrendsДокумент6 страницMidterm - Current TrendsMar Sayos DalesОценок пока нет
- Loan Agreement SampleДокумент2 страницыLoan Agreement SampleJameson Uy100% (1)
- Affidavit of Taxi OwnerДокумент3 страницыAffidavit of Taxi OwnerMar Sayos DalesОценок пока нет
- Romualdez-Marcos vs. ComelecДокумент1 страницаRomualdez-Marcos vs. ComelecMar Sayos DalesОценок пока нет
- Affidavit of Witness (BI)Документ3 страницыAffidavit of Witness (BI)Mar Sayos DalesОценок пока нет
- 1987 Constitution 1973 Constitution 1935 Constitution Preamble Preamble PreambleДокумент1 страница1987 Constitution 1973 Constitution 1935 Constitution Preamble Preamble PreambleMar Sayos DalesОценок пока нет
- De La Salle University: DasmariñasДокумент1 страницаDe La Salle University: DasmariñasMar Sayos DalesОценок пока нет
- Sample ManifestoДокумент1 страницаSample ManifestoMar Sayos DalesОценок пока нет
- Affidavit of Security Guard CCTVДокумент3 страницыAffidavit of Security Guard CCTVMar Sayos DalesОценок пока нет
- Visita Iglesia 2014 Stations of The Cross 1. Immaculate Conception Parish (Bayan), Dasmariñas CityДокумент3 страницыVisita Iglesia 2014 Stations of The Cross 1. Immaculate Conception Parish (Bayan), Dasmariñas CityMar Sayos DalesОценок пока нет
- Leo Year 2008-2009 Proposed Upcoming Projects: Dasmariñas Leo ClubДокумент1 страницаLeo Year 2008-2009 Proposed Upcoming Projects: Dasmariñas Leo ClubMar Sayos DalesОценок пока нет
- Overview of The Filipino YouthДокумент10 страницOverview of The Filipino YouthMar Sayos DalesОценок пока нет
- 1989 IBP Elections 178 SCRA 398Документ18 страниц1989 IBP Elections 178 SCRA 398Mar Sayos DalesОценок пока нет
- About The Holy Name Society of The PhilippinesДокумент6 страницAbout The Holy Name Society of The PhilippinesMar Sayos DalesОценок пока нет
- Spiritual RationaleДокумент1 страницаSpiritual RationaleMar Sayos DalesОценок пока нет
- Guide Project Proposal-MATRIXДокумент1 страницаGuide Project Proposal-MATRIXMar Sayos DalesОценок пока нет
- Bishop ReyДокумент3 страницыBishop ReyMar Sayos DalesОценок пока нет
- The Vessel Dispute: Asukal vs. Titan The Mediation ProcessДокумент15 страницThe Vessel Dispute: Asukal vs. Titan The Mediation ProcessMar Sayos DalesОценок пока нет
- District Iv: Vicariate of Immaculate ConceptionДокумент2 страницыDistrict Iv: Vicariate of Immaculate ConceptionMar Sayos DalesОценок пока нет
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Paredes vs. Abad - Canonizado vs. AguirreДокумент2 страницыParedes vs. Abad - Canonizado vs. AguirrePAULAMIKHAELA ARIASОценок пока нет
- Deregistration/ Change of Address FormДокумент2 страницыDeregistration/ Change of Address Formpoetdb1594Оценок пока нет
- Jison Vs CA - 124853 - February 24, 1998 - J. Davide, Jr. - First DivisionДокумент21 страницаJison Vs CA - 124853 - February 24, 1998 - J. Davide, Jr. - First DivisionMarchini Sandro Cañizares KongОценок пока нет
- Vicar International Corp vs. Feb Leasing Case DigestДокумент3 страницыVicar International Corp vs. Feb Leasing Case Digestkikhay11Оценок пока нет
- Lopez V Orosa and Plaza Theater G.R. Nos. L-10817-18Документ3 страницыLopez V Orosa and Plaza Theater G.R. Nos. L-10817-18newin12Оценок пока нет
- Remedies Outline: Competitive, Smothering Competition. Contrarily, Brunswick'sДокумент4 страницыRemedies Outline: Competitive, Smothering Competition. Contrarily, Brunswick'sHannah ElizabethОценок пока нет
- LAM - AssignmentДокумент7 страницLAM - Assignmentmahesh sharmaОценок пока нет
- Old Standard ClippingsДокумент9 страницOld Standard Clippings9newsОценок пока нет
- PD 957 PDFДокумент4 страницыPD 957 PDFInnah MontalaОценок пока нет
- Senate Vs Ermita - G.R. 169777, April 20, 2006Документ2 страницыSenate Vs Ermita - G.R. 169777, April 20, 2006DyanОценок пока нет
- Good Faith Bad Faith.Документ4 страницыGood Faith Bad Faith.twenty19 law100% (1)
- Player-Agency AgreementДокумент4 страницыPlayer-Agency AgreementNour Mohamed100% (1)
- PFR Week 3 Case DigestsДокумент18 страницPFR Week 3 Case DigestsTrixie ArciagaОценок пока нет
- Commerce Clause FlowchartДокумент1 страницаCommerce Clause FlowchartMark Adamson100% (1)
- Dumlao Vs ComelecДокумент2 страницыDumlao Vs ComelecDave Jonathan MorenteОценок пока нет
- Original PDF Guiding Young Children 9th Edition by Patricia F Hearron PDFДокумент34 страницыOriginal PDF Guiding Young Children 9th Edition by Patricia F Hearron PDFjoseph.mikesell366100% (31)
- National Service CorporationДокумент13 страницNational Service Corporationalyza burdeosОценок пока нет
- NEBOSH ConstructionДокумент54 страницыNEBOSH ConstructionHarbir Singh33% (6)
- NDA STD Mutual (PI)Документ5 страницNDA STD Mutual (PI)Avi DahiyaОценок пока нет
- Distress Act 1951 (Revised 1981) - Act 255Документ18 страницDistress Act 1951 (Revised 1981) - Act 255peterparker100% (1)
- Anti Honour Killing Act 2016Документ5 страницAnti Honour Killing Act 2016Atif Khan AfridiОценок пока нет
- Hollier v. Rambler Motors AMC LTD (1972)Документ5 страницHollier v. Rambler Motors AMC LTD (1972)Saurabh MisalОценок пока нет
- Lecturer AESRB Admit CardДокумент2 страницыLecturer AESRB Admit CardAmenul HoqueОценок пока нет
- Pil 1 Barcelona Traction CaseДокумент1 страницаPil 1 Barcelona Traction CaseCayen Cervancia CabiguenОценок пока нет
- September 12, 2015Документ16 страницSeptember 12, 2015The Delphos HeraldОценок пока нет
- CONTRACT OF LEASE Ni TilloДокумент2 страницыCONTRACT OF LEASE Ni TilloDeil L. NaveaОценок пока нет
- Airbus A320Документ14 страницAirbus A320radi8100% (7)
- Manuel Rodriguez v. Sunny L. Schriver, Superintendent, Wallkill Correctional Facility, 392 F.3d 505, 2d Cir. (2004)Документ11 страницManuel Rodriguez v. Sunny L. Schriver, Superintendent, Wallkill Correctional Facility, 392 F.3d 505, 2d Cir. (2004)Scribd Government DocsОценок пока нет
- RM 1509e GB WW 1116-18Документ888 страницRM 1509e GB WW 1116-18Mr.K chОценок пока нет