Академический Документы
Профессиональный Документы
Культура Документы
Separable Encrypted Colour Image Watermarking Using VLSI
Загружено:
ijcctsАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Separable Encrypted Colour Image Watermarking Using VLSI
Загружено:
ijcctsАвторское право:
Доступные форматы
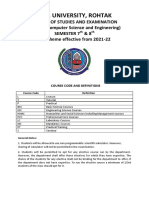
International Journal of Communication and Computer Technologies
Volume 02 No.01 Issue: 02 Feb 2014
ISSN NUMBER : 2278-9723
Volume 01 No.2, Issue: 01 Page 7
International Journal of Communication and Computer Technologies www.ijccts.org
SEPARABLE ENCRYPTED COLOUR IMAGE
WATERMARKING USING VLSI
Deepa.M
1
, Senthilkumar.M
2
1
PG scholar, Department of EEE, K.S.R College of Engineering, Tiruchengode,
2
Assistant Professor, Department of EEE, K.S.R college of Engineering, Tiruchengode,
ABSTRACT
Due to rapid development in the network and
communication field, it has become necessary to
protect the unauthorized duplication of a confidential
image. Conventional methods having information loss
during recovery, it will be easily hacked, lower
embedding capacity, requires more memory and
power consumption. The proposed scheme offers an
effective protection, data embedding along with high
security. Curvelet transform used to overlay visible
watermark on colour image. For transferring
confidential data, content owner encrypts the original
uncompressed colour image using an encryption key.
Then image-hider compress the LSB of all three
planes of encrypted colour image using a image-hiding
key. With an encrypted image containing secret image,
if a receiver has the image-hiding key will extract the
secret images and the receiver has the encryption key
will decrypt the received data to obtain an original
image. In order to extract secret image and to recover
the original content simultaneously both image hiding
key and encryption key are necessary. Randomization
in encryption key generation is improved by parallel
RC4 algorithm. Hidden image security will be
increased by odd and even shuffling of secret image
bits within compressed encrypted colour image. It has
good embedding capacity and better quality recovered
image.
Keywords- Curvelet transform, RC4, private keys, Stream
cipher, encryption, cryptography, watermarking.
1. Introduction
There are also a number of works on data hiding
differs on method used for data embedding. Cover
image and secret images are converted to vector form,
then entire decimal signal are convert to binary signals
which means bit form. Secret image in form of bits are
embed in the LSB of cover image bits [1]. The group
of bits stored in a file and using the simulink block
sets read an image in bit by bit format. The Elliptic
Curve Cryptography method presented in [2]
authenticates the information by generating signature
and signed messages. In [3], scrambled watermark is
embedded in middle frequency sub band and Arnold
Transform is used to scramble the image. When
wavelet transform [4] is used for decomposition of
image due to compression and decompression, it may
introduce loss during recovery. The embedding
method is multiplicative and done at second level of
DWT decomposition [5], [6] by most favorable choice
of the embedding strength. In [7] data embedding is
done on LSB modification of cover image, embed the
watermark bits in the blocks located at the even
columns in the HL region and the blocks located at the
odd columns in the LH subband. In [8] multiple binary
watermarks are embedded into digital medical images
based on the concept of Visual Cryptography.
Reversible data hiding method presented in [9], [10],
[11] uses data hiding key and encryption key if any
one of key is lost both original image and secret data
will lost. In separable reversible data hiding method
presented in [12] though receiver has lost encryption
key will able to extract hidden data and if data hiding
key has lost it is not possible to extract secret data but
using encryption key alone original image will be
recovered. In presence of both data hiding key and
encryption key, receiver will decrypt image and
recover original data simultaneously. Here grayscale
image is used as cover image and invisible
watermarking has done.
Figure 1: process involved in watermarking and
information hiding
Proposed method uses image as media for
watermarking, both visible and invisible watermarking
is used. Logo is inserted on image by curvelet
transform which results in visible watermarking. Three
binary images are embedded on encrypted LSB of
RGB planes of colour image for secret transmission of
International Journal of Communication and Computer Technologies
Volume 02 No.01 Issue: 02 Feb 2014
ISSN NUMBER : 2278-9723
Volume 01 No.2, Issue: 01 Page 8
International Journal of Communication and Computer Technologies www.ijccts.org
image. Entire process is carried out in spatial domain
it uses LSB of the image for embedding. Encryption
[13] is done on the image prior to secret image
embedding. Encryption/ decryption use symmetrical
keys generated by parallel RC4 stream cipher. It uses
private key method for secret image extraction.
Process involved in watermarking and information
hiding as shown in Fig. 1.
2. Proposed system
The proposed scheme uses colour image as the cover
image and three gray scale images as secret image.
Curvelet transform is used for embedding visible logo
on colour image. Then three secret images are
embedded in three planes of colour image namely
RGB planes. During image hiding three processes has
to be carried out namely image encryption, secret
image embedding and image-extraction. The content
owner encrypts the original uncompressed colour
image using an encryption key to produce an
encrypted image. Then, the image hider compresses
the least significant bits (LSB) of the encrypted colour
image using a image-hiding key to create a sparse
space to accommodate the secret binary image.
Figure 2: Block diagram of transmitter
At the Receiver side, the secrete image embedded in
the created space will be easily retrieved from the
encrypted image containing secret image according to
the image hiding key. Since the image embedding
affects the LSB not MSB of cover image, a decryption
with the encryption key will result in an image similar
to the original version. When using both of the
encryption and image-hiding keys, the embedded
additional secret image will be successfully extracted
and the original image is perfectly recovered by
exploiting the spatial correlation in natural image. The
Fig,3 shows proposed separable scheme at the
receiver.
Figure 3: Proposed separable scheme at the
receiver
2.1 Image encryption
Colour image of size P1 P2 is taken; logo is overlay
on the colour image by Curvelet transform results in
visible watermarking which uses Matlab tool. Then
the image is encrypted by simply XOR the pixel value
of image with keys generated by parallel RC4 stream
cipher using Modelsim tool.
B
i,j,u
=b
i.j,u
r
i,j,u
(1)
Where b
i.j,u
are pixels value of the of original image,
r
i,j,u
are the random keys generated by parallel RC4
[14], [15]. B
i,j,u
are pixels value of encrypted image.
Same keys are used for encryption as well as
decryption since it follows a private mode of
encryption.
2.2 Secret image embedding
For embedding secret image, select Pn encrypted
pixels of P encrypted pixels from R plane of encrypted
colour image. Repeat this procedure for G and B
planes of encrypted colour image, results in three
groups of Pn encrypted pixels are used to carry the
parameters for image hiding. The LSB of (P-Pn)
encrypted pixels of RGB planes are compressed and
divided into a number of groups, each of which
contains M pixels. For each pixel-group, collect the D
least significant bits of the M pixels, and denote them
as B (k, 1),B(k,2),...,B(k, M.D) where k is a group
index within [1, (P-Pn)/M] and D is a positive integer
less than 5. The image-hider generates a matrix G [16]
sized (D.M-V) D.M) for three planes of colour image
individually, So three G sized matrix are generated
which is composed of two parts
G=[I
D.M-V
Q] (2)
In equation (2) the left part is an (D.M-V) (D.M-V)
identity matrix, the right part Q sized (D.M-V)V is a
pseudo-random binary matrix derived from the image-
hiding key. Then, embed the values of the parameters
D, M and V into the LSB of Pn selected encrypted
pixels corresponding to RGB planes. Finally, total of
International Journal of Communication and Computer Technologies
Volume 02 No.01 Issue: 02 Feb 2014
ISSN NUMBER : 2278-9723
Volume 01 No.2, Issue: 01 Page 9
International Journal of Communication and Computer Technologies www.ijccts.org
(P-Pn).V/M bits made up of Pn original LSB of
selected encrypted pixels and (P-Pn).V/M-Pn
additional bits will be embedded into the pixel groups.
For each group of RGB plane, Calculate [16]
'( ,1) ( ,1)
'( , 2) ( , 2)
. . .
. .
'( , D M ) ( , D.M)
B k B k
B k B k
G
B k V B k
| | | |
| |
| |
| | =
| |
| |
| |
\ . \ .
(3)
In equation (3), B(k,1), B(k, 2),...,B(k, DM) are
compressed as B(k,1), B(k,2),...,B(k, DM-V) and a
sparse space is therefore available for secret image
accommodation.
Let B(k,D.M-V+1), B(k,D.M-V+2),...,B(k,D.M) of
each group be the original LSB of selected encrypted
pixels and the additional data to be embedded. Then,
replace the B (k, 1), B(k,2),...,B(k, D.M) with the new
B(k, 1), B(k,2),...,B(k, M.L), and put them into their
original positions by an inverse permutation. At the
same time, the (8-D) most significant bits (MSB) of
encrypted pixels are kept unchanged. Since V bits are
embedded into each pixel-group, the total (P-Pn)V/M
bits will be accommodated in all groups of colour
image. While embedding secret image bits, odd bits
are embedded in one group and even bits are
embedded in another group. By this way security is
increased. The embedding capacity (EC) is
3
V
EC
M
=
(4)
In equation (4), M is number of pixel in each group, V
is the number of bits embedded in each group.
2.3 Secret image extraction and image recovery
During image recovery and secret image extraction
three cases are possible, that the receiver has only the
image hiding key, only the encryption key, and both
the image hiding and encryption keys. With an
encrypted image containing embedded secret image, if
the receiver has only the image-hiding key will obtain
the values of the parameters D, M and V from the LSB
of the Pn selected encrypted pixels. The receiver
permutes and divides the other (P-Pn) pixels into (P-
Pn)/M groups and extracts the V embedded bits from
the D LSB-planes of each group. When having the
total (P-Pn)V/M extracted bits, the receiver will
divide them into (P-Pn) original LSB of selected
encrypted pixels and (P-Pn)V/M-Pn additional bits.
Suppose the receiver has encryption key means only
original image content along with Logo will be
recovered. Denoting the bits of pixels in the encrypted
image containing embedded image as B
i,j.0
,
B
i,j,1
,...B
i,j,7
(1 i P1 and 1 j P2) the receiver will
decrypt the received data[16]
b
i,j,u
=B
i.j,u
r
i,j,u
(5)
In equation (5) r
i,j,u
are derived from the encryption
key generated by parallel RC4 stream cipher which
generates two keys per clock cycle. The average
energy (AE) of distortion [16] is
AE=
2 1 2 1
2 2
0 0
(2 1)
2 ( )
2
D D
V
D
V
o |
o |
= =
(6)
So, the value of peak signal to noise ratio (PSNR) in
the directly decrypted image is
PSNR=
10
10log ( ) AE
(7)
If the receiver has both the image-hiding and the
encryption keys will extract the embedded image and
recover the original image. According to the image-
hiding key, the values of D, M and V, the original
LSB of the Pn selected encrypted pixels, and the (P-
Pn)V/M-Pn additional bits are extracted from the
encrypted image containing embedded image. By
putting the Pn LSB into their original positions, the
encrypted image of the Pn selected pixels are retrieved
three planes of colour image and their original
intensity values are correctly decrypted using the
encryption keys. To recover the original intensity
values of the other (P-Pn) pixels. Considering a pixel-
group, because B(k,1), B(k,2),...B(k,D.M-V) in (3)
are given, [B(k,1), B(k,2), ..B(k,M)]
T
must be one of
the vectors meeting [16]
S=[B(k,1),B(k,2),....B(k,ML-S)00..0]
T
+a.H (8)
In equation (8), a is an arbitrary binary vector sized
1V and H is an V DM matrix made up of the
transpose of Q and an VV identity matrix
H=[Q
T
I
V
] (9)
Equation (10) denoting the decrypted pixel-group as
Gk and the intensity values in it as t
i,j
, then calculate
the total difference between the decrypted and
estimated intensity values [16] in the all group of RGB
planes
, ,
( , )
di
i j i j
i j Gk
t p
e
=
(10)
where the estimated intensity values is generated from
the neighbors in the directly decrypted image.
1 1 , 1 , 1 1
,
' / 2 ' / 2 ' / 2 ' / 2
2 2
4
D D D D
i i i j i j D D
i j
p p p p
p
+ +
( ( ( ( + + +
= +
(11)
By (11), the estimated pixel values [16] are only
dependent on the MSB of neighbour pixels. Mean
square error (MSE) is calculated using following
formula (12)
512
2
1
2
( )
(512)
512
i
error
MSE
=
=
(12)
International Journal of Communication and Computer Technologies
Volume 02 No.01 Issue: 02 Feb 2014
ISSN NUMBER : 2278-9723
Volume 01 No.2, Issue: 01 Page 10
International Journal of Communication and Computer Technologies www.ijccts.org
Similarity ratio (SR) is calculated using following
equation (13)
SR =
Maximum similar data
Total data
(13)
3. EXPERIMENTAL RESULTS
The test colour image Lena of size 512512 as shown in
Fig.4 (A) is used as the original cover image in the
experiment. Logo of size 128128 was embedded in the
cover image using Curvelet transform results in visible
watermarking and then inverse Curvelet transform is
performed. Then the watermarked image containing Logo
is encrypted using encryption key. For information
hiding, information in form of binary image (camera
man) of size 185185 is written as bits in LSB of the
Encrypted image using image hiding key. So to decrypt
the image and to recover the hidden binary image two
keys are necessary as shown in Fig..4 (G). If receiver has
image hiding key will recover binary image but
decryption of image is not possible. If the receiver has
encryption key will decrypt the watermarked image but
not possible to extract hidden binary image as shown in
Fig.4 (F). TABLE 1 shows Experimental results of
proposed scheme applied for different colour images.
Separable method is applied to various colour image and
results of directly decrypted(image hiding key) images
are compared with recovered images (both image hiding
key and encryption key).
(A) (B) (C) (D)
(E) (F) (G)
Figure 4: (A)Cover image of size 512512, (B) Logo of size 128128, (C)Secret binary image of size 185185
(D)Watermarked image (E) Encrypted watermarked image containing secret binary image with embedding capacity of
(F) Directly decrypted image (only encryption key) with PSNR 36.7dB (G) Recovered image (encryption key image
hiding key) with PSNR 45.06 dB
Table 1.Experimental results of proposed scheme applied for different colour images
International Journal of Communication and Computer Technologies
Volume 02 No.01 Issue: 02 Feb 2014
ISSN NUMBER : 2278-9723
Volume 01 No.2, Issue: 01 Page 11
International Journal of Communication and Computer Technologies www.ijccts.org
4. Conclusion
The proposed scheme offers an effective protection,
data embedding along with high security. It offers
authentication by curvelet transform based visible
watermarking and allows secret transmission of image
within cover image. For transferring confidential
image, a content owner encrypts the original
uncompressed colour image using an encryption key.
Then image hider may compress the LSB of all three
planes of encrypted colour image using image-hiding
key for embedding secret image. Though the receiver
has lost any of the two keys it is either possible to
extract secret image or to decrypt image. Lower
memory requirements, speed of the encryption process
and randomized encryption key generation are
improved by parallel RC4 algorithm. Hidden image
security has increased by odd and even shuffling of
secret image.
4.1 Future scopes
In future the processed image will be implemented in
FPGA to calculate power, memory requirements etc
and extend to apply this concept from image to video.
4.2 Applications
With the conception of separable encrypted
watermarking on colour image, the identification and
copyright ownership protection are carried out. Digital
content embedded with watermarks depicting
metadata identifies the copyright owners. It plays a
vital role in military application where the secret
transmission of confidential data is significant.
REFERENCES
[1] T. J. Anumol, V. A. Binson and S. Rasheed,
FPGA Implementation of Low Power, High
Speed, Area Efficient Invisible Image
Watermarking Algorithm for Images,
International Journal of scientific and
engineering research, 4(8), 2013.
[2] A. Chitla and M. C. Mohan, Authentication
of images through lossless watermarking
International Journal of Communication and Computer Technologies
Volume 02 No.01 Issue: 02 Feb 2014
ISSN NUMBER : 2278-9723
Volume 01 No.2, Issue: 01 Page 12
International Journal of Communication and Computer Technologies www.ijccts.org
technique with the aid of elliptic curve
cryptography (ECC), International Journal
of computer applications, 57(6), 2012, pp. 17-
25.
[3] B. L. Gunjal, Wavelet based colour image
watermarking scheme giving high robustness
and exact correlation, International Journal
of Emerging Trends in Engineering and
Technology, 1(1), 2011, pp. 23-30.
[4] B. Evelyn, W. Michael and H. Robert, The
Effect of Wavelet Families on
Watermarking, Journal of computers, 4(6),
2009, pp 554-566.
[5] M. Devapriya and K. Ramar, Statistical
Image Watermarking In DWT with Capacity
Improvement, Global Journal of Computer
Science and Technology, 10(2), 2010, pp. 20-
24.
[6] S. Kumar and R. Bansal, Enhanced
Technique for Watermarking Using
MFHWT, International Journal of Advanced
Research in Computer Science and Software
Engineering, 3(5), 2013, pp. 1199-1202.
[7] P. Y. Jih, W. L.Che, J. L. Wei and H. W.
Hung, Watermarking technique based on
DWT associated with embedding rule,
International Journal of Circuits, Systems and
Signal Processing, 4(2), 2010, pp. 72-82.
[8] A. Umaamaheshvari and K. Thanushkodi, A
novel watermarking technique based on visual
cryptography, International Journal of
advanced research in computer engineering
and technology, 1(7), 2012, pp. 70-74.
[9] R. Manikandan, M. Uma and S. M.
MahalakshmiPreethi, Reversible Data Hiding
for Encrypted Image, Journal of Computer
Applications, 5(1), 2012, pp.104-110.
[10] Z. Ni, Y. Q. Shi, N. Ansari and W. Su,
Reversible data hiding, IEEE Transactions
Circuits System Video Technology, 16(3),
2006, pp. 354-362.
[11] X. Zhang, Reversible data hiding in
encrypted image, IEEE signal processing
letters, 18(4), 2011, pp. 255258.
[12] X. Zhang, Separable reversible data hiding in
encrypted image, IEEE transactions on
information forensics and security, 7(2),
2012, pp. 826-832.
[13] P. Gupta, Cryptography based digital image
watermarking algorithm to increase security
of watermark data, International Journal of
Scientific and Engineering Research, 3(9),
2012, pp 1-4.
[14] A. Mousa and A. Hamad, Evaluation of
the RC4 Algorithm for Data Encryption,
International Journal of Computer Science
and Applications, 3(2), 2006, pp. 44-56.
[15] J. Singh, K. Munjal, A New Robust
Enrichment Symmetric Stream Cipher
Approach for Confidentiality Based on RC4
Stream Cipher Algorithm, International
Journal of Engineering Research &
Technology, vol. 2, no.3, pp. 1-8, Mar. 2013.
Вам также может понравиться
- Harmonic Mitigation in Doubly Fed Induction Generator For Wind Conversion Systems by Using Integrated Active Filter CapabilitiesДокумент8 страницHarmonic Mitigation in Doubly Fed Induction Generator For Wind Conversion Systems by Using Integrated Active Filter CapabilitiesijcctsОценок пока нет
- Improvement of Power Quality Using PQ Theory Based Series Hybrid Active Power FilterДокумент5 страницImprovement of Power Quality Using PQ Theory Based Series Hybrid Active Power FilterijcctsОценок пока нет
- 6.VLSI Architecture Design For Analysis of Fast Locking ADPLL Via Feed Forward Compensation Algorithm (33-38)Документ6 страниц6.VLSI Architecture Design For Analysis of Fast Locking ADPLL Via Feed Forward Compensation Algorithm (33-38)ijcctsОценок пока нет
- 5.modeling of Three Phase Self Excited Induction Generator (26-32)Документ7 страниц5.modeling of Three Phase Self Excited Induction Generator (26-32)ijcctsОценок пока нет
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Steganography Project ReportДокумент40 страницSteganography Project ReportArunangshu Sen100% (1)
- Petrovic, Winograd, Jemili, Metois - Data Hiding Within Audio Signals PDFДокумент20 страницPetrovic, Winograd, Jemili, Metois - Data Hiding Within Audio Signals PDFInterfan_allinОценок пока нет
- Visvesvaraya Technological University: R L Jalappa Institute of TechnologyДокумент22 страницыVisvesvaraya Technological University: R L Jalappa Institute of TechnologyKarpareddy BharathmohanreddyОценок пока нет
- New Additive Watermark Detectors Based On AДокумент9 страницNew Additive Watermark Detectors Based On AJerald RoyОценок пока нет
- Steganography: Watermarking byДокумент38 страницSteganography: Watermarking byluong tranОценок пока нет
- Image Processing/Communications-MATLAB: Code TitleДокумент7 страницImage Processing/Communications-MATLAB: Code Titlebabu surendraОценок пока нет
- PPTДокумент25 страницPPTprabhjtОценок пока нет
- Wavelet Based WatermarkingДокумент43 страницыWavelet Based Watermarkingdj0808Оценок пока нет
- Literature Review On Visual CryptographyДокумент8 страницLiterature Review On Visual Cryptographyafmyervganedba100% (1)
- Copyright Protection of Web Applications Through Watermarking AbstractДокумент7 страницCopyright Protection of Web Applications Through Watermarking AbstractTelika RamuОценок пока нет
- 1 KKWIEER, Nashik Dv&DaДокумент15 страниц1 KKWIEER, Nashik Dv&Davikas ramesh jadhavОценок пока нет
- EMTM 553: E-Commerce Systems: Lecture 7a: Digital WatermarkingДокумент36 страницEMTM 553: E-Commerce Systems: Lecture 7a: Digital WatermarkingKusum KumariОценок пока нет
- Digital WatermarkingДокумент3 страницыDigital WatermarkingAmrita Saloni SinghОценок пока нет
- Review of Digital Image Forgery DetectionДокумент4 страницыReview of Digital Image Forgery DetectionEditor IJRITCCОценок пока нет
- Dummy Report Digital - Image - WatermarkingДокумент46 страницDummy Report Digital - Image - Watermarkingaman AgrawalОценок пока нет
- Copy Move Forgery Based On DWT-DCTДокумент4 страницыCopy Move Forgery Based On DWT-DCTShiva KeeОценок пока нет
- Dcia Whitepaper p2pДокумент10 страницDcia Whitepaper p2pVinay KumarОценок пока нет
- Spread SstenoДокумент37 страницSpread SstenokanchanОценок пока нет
- A Survey On Various Encryption Techniques: John Justin M, Manimurugan SДокумент4 страницыA Survey On Various Encryption Techniques: John Justin M, Manimurugan SUmmama khanОценок пока нет
- Real Time Watermarking For Professional PhotographyДокумент7 страницReal Time Watermarking For Professional PhotographyInternational Journal of Application or Innovation in Engineering & ManagementОценок пока нет
- Watermark Host10Документ6 страницWatermark Host10Bala ChandranОценок пока нет
- Data Man AДокумент462 страницыData Man Acarlosnporras1137Оценок пока нет
- Term Paper About Computer ScienceДокумент8 страницTerm Paper About Computer Sciencedelhwlwgf100% (1)
- Digital Image Watermarking For Protection Against Data DuplicationДокумент8 страницDigital Image Watermarking For Protection Against Data DuplicationKripa SindhuОценок пока нет
- Amax Security System Corp. Price List: Picture ModelДокумент57 страницAmax Security System Corp. Price List: Picture ModelJing AbionОценок пока нет
- Multimedia Data hiding-Image-VideoДокумент228 страницMultimedia Data hiding-Image-VideoRendy Dwi RendragrahaОценок пока нет
- M.Phil Computer Science Image Processing ProjectsДокумент27 страницM.Phil Computer Science Image Processing ProjectskasanproОценок пока нет
- Electronic Payment Systems Architecture Elements Challengesand Security Concepts An OverviewДокумент13 страницElectronic Payment Systems Architecture Elements Challengesand Security Concepts An OverviewDMT IPOОценок пока нет
- Techniquesin Detecting Forgeryin Identity DocumentsДокумент8 страницTechniquesin Detecting Forgeryin Identity Documentsmarm496Оценок пока нет
- 4 - 09-14-2021 - 14-46-32 - B.Tech CSE 4th YearДокумент53 страницы4 - 09-14-2021 - 14-46-32 - B.Tech CSE 4th YearGOURAB PANDITОценок пока нет