Академический Документы
Профессиональный Документы
Культура Документы
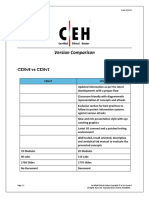
Ceh v7 and v8 Comparison
Загружено:
Ricardo J. Bendita LaricoАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Ceh v7 and v8 Comparison
Загружено:
Ricardo J. Bendita LaricoАвторское право:
Доступные форматы
Certified Ethical Hacker Version Comparison
Exam 312-50
Version Comparison
CEHv8 vs CEHv7
CEHv7 CEHv8 Updated information as per the latest developments with a proper flow Classroom friendly with diagrammatic representation of concepts and attacks Exclusive section for best practices to follow to protect information systems against various attacks New and rich presentation style with eye catching graphics Latest OS covered and a patched testing environment Well tested, result oriented, descriptive and analytical lab manual to evaluate the presented concepts 19 Modules 90 Labs 1700 Slides No Document 20 Modules 110 Labs 1770 Slides Document
Page | 1
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Module Comparison of CEHv8 with CEHv7
Introduction to Ethical Hacking
Hacking refers to exploiting system vulnerabilities and compromising security controls to gain unauthorized or inappropriate access to the system resources. The topics highlighted in red under CEHv8 Module 01: Introduction to Ethical Hacking are the new additions. CEHv7 Module 01: Introduction to Ethical Hacking Data Breach Investigations Report Essential Terminologies Elements of Information Security Effects of Hacking on Business Who Is a Hacker? Hacking Phases Types of Attacks on a System Why Ethical Hacking is Necessary Skills of an Ethical Hacker Vulnerability Research What Is Penetration Testing? CEHv8 Module 01: Introduction to Ethical Hacking Data Breach Investigations Report Essential Terminologies Elements of Information Security Top Information Security Attack Vectors Motives, Goals, and Objectives of Information Security Attacks Information Security Threats Information Warfare IPv6 Security Threats Hacking vs. Ethical Hacking Effects of Hacking on Business Who Is a Hacker? Hacking Phases Types of Attacks on a System Why Ethical Hacking is Necessary Skills of an Ethical Hacker Incident Management Process Types of Security Policies
Page | 2
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Vulnerability Research What Is Penetration Testing?
Footprinting and Reconnaissance
Footprinting refers to uncovering and collecting as much information as possible about a target network, for identifying various ways to intrude into an organizations network system. The topics highlighted in red under CEHv8 Module 02: Footprinting and Reconnaissance are the new additions. CEHv7 Module 02: Footprinting and Reconnaissance Footprinting Terminologies What Is Footprinting? Objectives of Footprinting Footprinting Threats Footprinting through Search Engines Website Footprinting Email Footprinting Competitive Intelligence Footprinting Using Google WHOIS Footprinting DNS Footprinting Network Footprinting Footprinting Tools Footprinting Countermeasures CEHv8 Module 02: Footprinting and Reconnaissance Footprinting Terminologies What Is Footprinting? Objectives of Footprinting Footprinting Threats Footprinting through Search Engines Website Footprinting Email Footprinting Competitive Intelligence Footprinting Using Google WHOIS Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting through Social Networking Sites
Page | 3
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Footprinting Pen Testing
Footprinting Tools Footprinting Countermeasures Footprinting Pen Testing Footprinting Terminologies What Is Footprinting?
Scanning Networks
Network scanning refers to a set of procedures for identifying hosts, ports, and services in a network. The topics highlighted in red under CEHv8 Module 03: Scanning Networks are the new additions CEHv7 Module 03: Scanning Networks Overview of Network Scanning CEH Scanning Methodology Checking for Live Systems Scanning Techniques IDS Evasion Techniques Banner Grabbing Vulnerability Scanning Drawing Network Diagrams Proxy Chaining HTTP Tunneling Techniques SSH Tunneling Anonymizers IP Spoofing Detection Techniques Scanning Countermeasures Scanning Pen Testing CEHv8 Module 03: Scanning Networks Overview of Network Scanning CEH Scanning Methodology Checking for Live Systems Scanning IPv6 Network Scanning Techniques IDS Evasion Techniques Banner Grabbing Vulnerability Scanning Drawing Network Diagrams Proxy Chaining HTTP Tunneling Techniques SSH Tunneling Anonymizers IP Spoofing Detection Techniques Scanning Countermeasures Scanning Pen Testing Latest Network Scanning Tools Added
Page | 4 Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
6 more Labs Added
Enumeration
In the enumeration phase, attacker creates active connections to system and performs directed queries to gain more information about the target. The topics highlighted in red under CEHv8 Module 04: Enumeration are the new additions. CEHv7 Module 04: Enumeration What Is Enumeration? Techniques for Enumeration NetBIOS Enumeration CEHv8 Module 04: Enumeration What Is Enumeration? Techniques for Enumeration Services and Ports to Enumerate
Enumerate Systems Using Default Passwords NetBIOS Enumeration SNMP Enumeration UNIX/Linux Enumeration LDAP Enumeration NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing Enumerate Systems Using Default Passwords SNMP Enumeration Working of SNMP UNIX/Linux Enumeration LDAP Enumeration NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing Latest Enumeration Tools Added 1 more Lab Added
Page | 5
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
System Hacking
Password cracking techniques are used to recover passwords from computer systems. The topics highlighted in red under CEHv8 Module 05 System Hacking are the new additions. CEHv7 Module 05 System Hacking System Hacking: Goals CEH Hacking Methodology (CHM) Password Cracking Microsoft Authentication How to Defend against Password Cracking Privilege Escalation Types of Privilege Escalation Executing Applications Types of Keystroke Loggers and Spywares Anti-Keylogger and Anti-Spywares Detecting Rootkits NTFS Stream Manipulation Classification of Steganography Steganalysis Methods/Attacks on Steganography Covering Tracks Penetration Testing CEHv8 Module 05 System Hacking System Hacking: Goals CEH Hacking Methodology (CHM) Password Cracking Stealing Passwords Using Keyloggers Microsoft Authentication How to Defend against Password Cracking Privilege Escalation Types of Privilege Escalation Executing Applications Methodology of Attacker in using Remote Keylogger Types of Keystroke Loggers and Spywares Anti-Keylogger and Anti-Spywares Various methods to place a rootkit Detecting Rootkits NTFS Stream Manipulation Application of steganography Classification of Steganography Audio Steganography Methods Issues in Information hiding Steganalysis Methods/Attacks on Steganography Detecting Text, Image, Audio, and Video Steganography Covering Tracks Penetration Testing
Page | 6 Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Trojans and Backdoors
It is a program in which the malicious or harmful code is contained inside apparently harmless programming or data in such a way that it can get control and cause damage, such as ruining the file allocation table on your hard disk. The topics highlighted in red under CEHv8 Module 06: Trojans and Backdoors are the new additions. CEHv7 Module 06: Trojans and Backdoors What Is a Trojan? What Do Trojan Creators Look For Indications of a Trojan Attack Common Ports used by Trojans How to Infect Systems Using a Trojan Different Ways a Trojan can Get into a System How to Deploy a Trojan Types of Trojans How to Detect Trojans Trojan Countermeasures Trojan Horse Construction Kit Anti-Trojan Software Pen Testing for Trojans and Backdoors CEHv8 Module 06: Trojans and Backdoors What Is a Trojan? What Do Trojan Creators Look For Indications of a Trojan Attack Common Ports used by Trojans How to Infect Systems Using a Trojan Different Ways a Trojan can Get into a System How to Deploy a Trojan Types of Trojans Trojan Analysis How to Detect Trojans Trojan Countermeasures Trojan Horse Construction Kit Anti-Trojan Software Pen Testing for Trojans and Backdoors Latest Trojan Detection Tools Added 2 more Labs Added
Page | 7
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Viruses and Worms
A virus is a self-replicating program that produces its own code by attaching copies of itself into other executable codes. The topics highlighted in red under CEHv8 Module 07: Viruses and Worms are the new additions. CEHv7 Module 07: Viruses and Worms Introduction to Viruses Stages of Virus Life Working of Viruses Indications of Virus Attack How does a Computer Get Infected by Viruses Types of Viruses Virus Maker Computer Worms Worm Analysis Worm Maker Malware Analysis Procedure Online Malware Analysis Services Virus and Worms Countermeasures Antivirus Tools Penetration Testing for Virus CEHv8 Module 07: Viruses and Worms Introduction to Viruses Stages of Virus Life Working of Viruses Common Techniques Used to Distribute Malware on the Web Indications of Virus Attack How does a Computer Get Infected by Viruses Virus Analysis Types of Viruses Virus Maker Computer Worms Worm Analysis Worm Maker Malware Analysis Procedure Online Malware Analysis Services Virus Detection Methods Virus and Worms Countermeasures Antivirus Tools Penetration Testing for Virus
Page | 8
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Sniffers
Packet sniffing is a process of monitoring and capturing all data packets passing through a given network using software (application) or hardware device. The topics highlighted in red under CEHv8 Module 08: Sniffing are the new additions.
CEHv7 Module 08: Sniffers Packet Sniffing Sniffing Threats Types of Sniffing Attacks Hardware Protocol Analyzers MAC Flooding How DHCP Works Rogue DHCP Server Attack ARP Spoofing Techniques ARP Poisoning Tools How to Defend Against ARP Poisoning Spoofing Attack Threats How to Defend Against MAC Spoofing DNS Poisoning Techniques How to Defend Against DNS Spoofing Sniffing Tools Sniffing Pen Testing
CEHv8 Module 08: Sniffing Packet Sniffing Sniffing Threats Types of Sniffing Attacks Hardware Protocol Analyzers IPv6 Addresses MAC Flooding How DHCP Works Rogue DHCP Server Attack ARP Spoofing Techniques ARP Poisoning Tools How to Defend Against ARP Poisoning Spoofing Attack Threats MAC Spoofing Technique IRDP Spoofing How to Defend Against MAC Spoofing DNS Poisoning Techniques How to Defend Against DNS Spoofing Sniffing Tools Sniffer Detection Technique Sniffing Pen Testing
Page | 9
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Social Engineering
Social engineering is the art of convincing people to reveal confidential information. Social engineers depend on the fact that people are unaware of their valuable information and are careless about protecting it. The topics highlighted in red under CEHv8 Module 09: Social Engineering are the new additions. CEHv7 Module 09: Social Engineering What Is Social Engineering? Factors that Make Companies Vulnerable to Attacks Warning Signs of an Attack Phases in a Social Engineering Attack Common Targets of Social Engineering Human-based Social Engineering Computer-based Social Engineering Social Engineering Through Impersonation on Social Networking Sites Identify Theft Social Engineering Countermeasures How to Detect Phishing Emails Identity Theft Countermeasures Social Engineering Pen Testing CEHv8 Module 09: Social Engineering What Is Social Engineering? Factors that Make Companies Vulnerable to Attacks Warning Signs of an Attack Phases in a Social Engineering Attack Common Targets of Social Engineering Human-based Social Engineering Computer-based Social Engineering Mobile-based Social Engineering Mobile-based Social Engineering Using SMS Social Engineering Through Impersonation on Social Networking Sites Identify Theft Social Engineering Countermeasures How to Detect Phishing Emails Identity Theft Countermeasures Social Engineering Pen Testing Social Engineering Toolkit
Page | 10
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Denial of Service
Denial of Service (DoS) is an attack on a computer or network that prevents legitimate use of its resources. The topics highlighted in red under CEHv8 Module 10: Denial-of-Service are the new additions. CEHv7 Module 10: Denial of Service What Is a Denial of Service Attack? What Are Distributed Denial of Service Attacks? Symptoms of a DoS Attack DoS Attack Techniques Botnet Botnet Ecosystem DDoS Attack Tools DoS Attack Tools Detection Techniques DoS/DDoS Countermeasure Techniques to Defend against Botnets Advanced DDoS Protection Appliances Denial of Service (DoS) Attack Penetration Testing CEHv8 Module 10: Denial-of-Service What Is a Denial of Service Attack? What Are Distributed Denial of Service Attacks? Symptoms of a DoS Attack DoS Attack Techniques Botnet Botnet Ecosystem Botnet Trojans DDoS Attack Tools DoS Attack Tools Detection Techniques DoS/DDoS Countermeasure Techniques to Defend against Botnets Advanced DDoS Protection Appliances Denial of Service (DoS) Attack Penetration Testing Latest DDoS and DoS attack tools added Latest DoS/DDoS Protection Tools added
Page | 11
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Session Hijacking
Session Hijacking refers to the exploitation of a valid computer session where an attacker takes over a session between two computers. The topics highlighted in red under CEHv8 Module 11: Session Hijacking are the new additions. CEHv7 Module 11: Session Hijacking What Is Session Hijacking? Why Session Hijacking Is Successful? Key Session Hijacking Techniques Brute Forcing Attack Session Hijacking Process Types of Session Hijacking Application Level Session Hijacking Session Sniffing Man-in-the-Middle Attack Network Level Session Hijacking TCP/IP Hijacking Session Hijacking Tools Protecting against Session Hijacking IPsec Architecture Session Hijacking Pen Testing CEHv8 Module 11: Session Hijacking
What Is Session Hijacking? Why Session Hijacking Is Successful? Key Session Hijacking Techniques Brute Forcing Attack Session Hijacking Process Types of Session Hijacking Application Level Session Hijacking Session Sniffing Man-in-the-Middle Attack Network Level Session Hijacking TCP/IP Hijacking Session Hijacking Tools Protecting against Session Hijacking IPsec Architecture Session Hijacking Pen Testing Latest Session Hijacking Tools Added
Page | 12
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Hacking Webservers
Web server pen testing is used to identify, analyze, and report vulnerabilities such as authentication weaknesses, configuration errors, protocol related vulnerabilities, etc. in a web server. The topics highlighted in red under CEHv8 Module 12: Hacking Webservers are the new additions. CEHv7 Module 11: Session Hijacking IIS Webserver Architecture Why Web Servers are Compromised? Impact of Webserver Attacks Webserver Attacks Webserver Attack Methodology Webserver Attack Tools Metasploit Architecture Web Password Cracking Tool Countermeasures How to Defend Against Web Server Attacks Patch Management Patch Management Tools Webserver Pen Testing CEHv8 Module 11: Session Hijacking IIS Webserver Architecture Why Web Servers are Compromised? Impact of Webserver Attacks Webserver Attacks Webserver Attack Methodology Webserver Attack Tools Metasploit Architecture Web Password Cracking Tool Countermeasures How to Defend Against Web Server Attacks How to Defend against HTTP Response Splitting and Web Cache Poisoning Patch Management Patch Management Tools Latest Webserver Security Tools Added Latest Webserver Pen Testing Tools Added Webserver Pen Testing
Page | 13
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Hacking Web Applications
Web applications provide an interface between end users and web servers through a set of web pages that are generated at the server end or contain script code to be executed dynamically within the client web browser. The topics highlighted in red under CEHv8 Module 13: Hacking Web Applications are the new additions. CEHv7 Module 13: Hacking Web Applications
How Web Applications Work Web Attack Vectors Web Application Threats Web App Hacking Methodology Footprint Web Infrastructure Hacking Web Servers Analyze Web Applications Attack Authentication Mechanism Attack Authorization Schemes Session Management Attack Attack Data Connectivity Attack Web App Client Attack Web Services Web Application Hacking Tools Countermeasures Web Application Security Tools Web Application Firewall Web Application Pen Testing
CEHv8 Module 13: Hacking Web Applications
How Web Applications Work Web Attack Vectors Web Application Threats Web App Hacking Methodology Footprint Web Infrastructure Hacking Web Servers Analyze Web Applications Attack Authentication Mechanism Attack Authorization Schemes Session Management Attack Attack Data Connectivity Attack Web App Client Attack Web Services Latest Web Application Hacking Tools Countermeasures Latest Web Application Security Tools Added Web Application Firewall Web Application Pen Testing
Page | 14
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
SQL Injection
SQL Injection is the most common website vulnerability on the Internet. It is a flaw in Web Applications and not a database or web server issue. The topics highlighted in red under CEHv8 Module 14: SQL Injection are the new additions. CEHv7 Module 14: SQL Injection
SQL Injection SQL Injection Attacks SQL Injection Detection SQL Injection Attack Characters Testing for SQL Injection Types of SQL Injection Blind SQL Injection SQL Injection Methodology Advanced SQL Injection Password Grabbing Network Reconnaissance Using SQL Injection SQL Injection Tools Evasion Technique How to Defend Against SQL Injection Attacks SQL Injection Detection Tools
CEHv8 Module 14: SQL Injection
SQL Injection SQL Injection Attacks SQL Injection Detection SQL Injection Attack Characters Testing for SQL Injection Types of SQL Injection Blind SQL Injection SQL Injection Methodology Advanced SQL Injection Bypass Website Logins Using SQL Injection Password Grabbing Network Reconnaissance Using SQL Injection Latest SQL Injection Tools Added Evasion Technique How to Defend Against SQL Injection Attacks Latest SQL Injection Detection Tools Added 2 more Labs Added
Page | 15
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Hacking Wireless Networks
Wi-Fi is developed on IEEE 802.11 standards, and it is widely used in wireless communication. It provides wireless access to applications and data across a radio network. The topics highlighted in red under CEHv8 Module 15: Hacking Wireless Networks are the new additions. CEHv7 Module 15: Hacking Wireless Networks Types of Wireless Networks Wireless Terminologies Types of Wireless Encryption How to Break WEP Encryption Wireless Threats Footprint the Wireless Network GPS Mapping Wireless Traffic Analysis What Is Spectrum Analysis? How to Reveal Hidden SSIDs Crack Wi-Fi Encryption Wireless Hacking Tools Bluetooth Hacking How to BlueJack a Victim How to Defend Against Wireless Attacks Wireless Security Tools Wireless Penetration Testing CEHv8 Module 15: Hacking Wireless Networks Types of Wireless Networks Wireless Terminologies Types of Wireless Encryption How to Break WEP Encryption Wireless Threats Footprint the Wireless Network Mobile-based Wi-Fi Discovery Tools GPS Mapping Wireless Traffic Analysis What Is Spectrum Analysis? How to Reveal Hidden SSIDs Crack Wi-Fi Encryption Latest Wireless Hacking Tools Added Bluetooth Hacking How to BlueJack a Victim How to Defend Against Wireless Attacks Latest Wireless Security Tools Added Wireless Penetration Testing 1 more Lab Added
Page | 16
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Hacking Mobile Platforms
CEHv8 Module 16 Hacking Mobile Platforms is a new module which covers the following topics: CEHv8 Module 16 Hacking Mobile Platforms Mobile Attack Vectors Mobile Platform Vulnerabilities and Risks Android OS Architecture Android Vulnerabilities Android Trojans Securing Android Devices Jailbreaking iOS Guidelines for Securing iOS Devices Windows Phone 8 Architecture Guidelines for Securing BlackBerry Devices Mobile Device Management (MDM) General Guidelines for Mobile Platform Security Mobile Protection Tools Mobile Pen Testing Guidelines for Securing Windows OS Devices Blackberry Attack Vectors
Evading IDS, Firewalls, and Honeypots
An intrusion detection system (IDS) gathers and analyzes information from within a computer or a network, to identify the possible violations of security policy, including unauthorized access, as well as misuse. The topics highlighted in red under CEHv8 Module 17: Evading IDS, Firewalls, and Honeypots are the new additions. CEHv7 Module 16: Evading IDS, Firewalls, and Honeypots Ways to Detect an Intrusion Types of Intrusion Detection Systems General Indications of Intrusions Firewall Architecture Types of Firewall Firewall Identification
Page | 17
CEHv8 Module 17: Evading IDS, Firewalls, and Honeypots Ways to Detect an Intrusion Types of Intrusion Detection Systems General Indications of Intrusions Firewall Architecture Types of Firewall Firewall Identification
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
How to Set Up a Honeypot Intrusion Detection Tools How Snort Works Firewalls Honeypot Tools Evading IDS Evading Firewalls Detecting Honeypots Firewall Evasion Tools Packet Fragment Generators Countermeasures Firewall/IDS Penetration Testing
How to Set Up a Honeypot Latest Intrusion Detection Tools Added How Snort Works Firewalls Latest Honeypot Tools Added Evading IDS Evading Firewalls Detecting Honeypots Latest Firewall Evasion Tools Added Packet Fragment Generators Countermeasures Firewall/IDS Penetration Testing 1 more Lab Added
Page | 18
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Buffer Overflow
A generic buffer overflow occurs when a program tries to store more data in a buffer than it was intended to hold. The topics highlighted in red under CEHv8 Module 18: Buffer Overflow are the new additions. CEHv7 Module 17: Buffer Overflow Heap-Based Buffer Overflow Knowledge Required to Program Buffer Overflow Exploits Buffer Overflow Steps Overflow Using Format String Buffer Overflow Examples How to Mutate a Buffer Overflow Exploit Identifying Buffer Overflows How to Detect Buffer Overflows in a Program BoF Detection Tools Defense Against Buffer Overflows Buffer Overflow Security Tools Buffer Overflow Penetration Testing CEHv8 Module 18: Buffer Overflow Heap-Based Buffer Overflow Why Are Programs and Applications Vulnerable to Buffer Overflows? Knowledge Required to Program Buffer Overflow Exploits Buffer Overflow Steps Overflow Using Format String Buffer Overflow Examples How to Mutate a Buffer Overflow Exploit Identifying Buffer Overflows How to Detect Buffer Overflows in a Program Latest BoF Detection Tools Added Defense Against Buffer Overflows Programming Countermeasures Latest Buffer Overflow Security Tools Added Buffer Overflow Penetration Testing
Page | 19
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Cryptography
Cryptography is the conversion of data into a scrambled code that is decrypted and sent across a private or public network. The topics highlighted in red under CEHv8 Module 19: Cryptography are the new additions. CEHv7 Module 18: Cryptography Cryptography Encryption Algorithms Ciphers What Is SSH (Secure Shell)? Cryptography Tools Public Key Infrastructure (PKI) Certification Authorities Digital Signature Disk Encryption Disk Encryption Tool Cryptography Attacks Code Breaking Methodologies Cryptanalysis Tools Online MD5 Decryption Tools CEHv8 Module 19: Cryptography Cryptography Encryption Algorithms Ciphers What Is SSH (Secure Shell)? Latest Cryptography Tools Added Public Key Infrastructure (PKI) Certification Authorities Digital Signature Disk Encryption Disk Encryption Tool Cryptography Attacks Code Breaking Methodologies Latest Cryptanalysis Tools Added Online MD5 Decryption Tools 2 more Labs Added
Page | 20
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Certified Ethical Hacker Version Comparison
Exam 312-50
Penetration Testing
Penetration testing assesses the security model of the organization as a whole. It reveals potential consequences of a real attacker breaking into the network. The topics highlighted in red under CEHv8 Module 20: Penetration Testing are the new additions. CEHv7 Module 19: Penetration Testing Security Assessments Vulnerability Assessment What Should be Tested? ROI on Penetration Testing Types of Penetration Testing Common Penetration Testing Techniques Pre-Attack Phase Attack Phase Post-Attack Phase Penetration Testing Deliverable Templates Pen Testing Roadmap Web Application Testing Outsourcing Penetration Testing Services CEHv8 Module 20: Penetration Testing Security Assessments Vulnerability Assessment Introduction to Penetration Testing Comparing Security Audit, Vulnerability Assessment, and Penetration Testing What Should be Tested? ROI on Penetration Testing Types of Penetration Testing Common Penetration Testing Techniques Pre-Attack Phase Attack Phase Post-Attack Phase Penetration Testing Deliverable Templates Pen Testing Roadmap Web Application Testing Outsourcing Penetration Testing Services
Page | 21
Certified Ethical Hacker Copyright by EC-Council All Rights Reserved. Reproduction Is Strictly Prohibited.
Вам также может понравиться
- Version Comparison: Cehv8 Vs Cehv7Документ21 страницаVersion Comparison: Cehv8 Vs Cehv7Tuấn NguyễnОценок пока нет
- EC-Council CEH v.7: Course Number: Course OverviewДокумент38 страницEC-Council CEH v.7: Course Number: Course Overviewprince_srivastava_2Оценок пока нет
- Ceh V6Документ19 страницCeh V6Tolu OlusakinОценок пока нет
- ECC CEHv8Документ35 страницECC CEHv8sjmpakОценок пока нет
- CEHv8 Course OutlineДокумент51 страницаCEHv8 Course OutlineSatya LakshmiОценок пока нет
- CEHday 1Документ121 страницаCEHday 1Yo YoОценок пока нет
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)От EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Рейтинг: 3 из 5 звезд3/5 (9)
- Certified Ethical Hacker (CEH) Preparation Guide: Lesson-Based Review of Ethical Hacking and Penetration TestingОт EverandCertified Ethical Hacker (CEH) Preparation Guide: Lesson-Based Review of Ethical Hacking and Penetration TestingРейтинг: 5 из 5 звезд5/5 (4)
- Certified Ethical Hacker Cehv12 Course ContentДокумент23 страницыCertified Ethical Hacker Cehv12 Course ContentM3iatОценок пока нет
- Ultimate Ethical Hacking From Zero To HeroДокумент2 страницыUltimate Ethical Hacking From Zero To Heroandres leonardo gomez murilloОценок пока нет
- CEH Version 7: WWW - Anninhmang.edu - VNДокумент4 страницыCEH Version 7: WWW - Anninhmang.edu - VNSilver SilverphoenixОценок пока нет
- English Preparation Guide Ehf 201505Документ12 страницEnglish Preparation Guide Ehf 201505jesus_yustasОценок пока нет
- CEHv8 Module 04 Enumeration PDFДокумент83 страницыCEHv8 Module 04 Enumeration PDFMehrdad100% (2)
- ETHICAL HACKING GUIDE-Part 1: Comprehensive Guide to Ethical Hacking worldОт EverandETHICAL HACKING GUIDE-Part 1: Comprehensive Guide to Ethical Hacking worldОценок пока нет
- ECSA Course OutlineДокумент27 страницECSA Course Outlinejeroc84879Оценок пока нет
- Ethical Hacking1Документ45 страницEthical Hacking1metheans_791455933Оценок пока нет
- EC Council Certified Ethical Hacker CEH v9.0Документ5 страницEC Council Certified Ethical Hacker CEH v9.0Juan Ignacio Concha AguirreОценок пока нет
- Certified Ethical Hacker Course ContentДокумент36 страницCertified Ethical Hacker Course ContentTamer DobalОценок пока нет
- Top 30+ Ethical Hacking Tools and Software For 2022Документ20 страницTop 30+ Ethical Hacking Tools and Software For 2022popzy malikОценок пока нет
- AlienvaultusesДокумент14 страницAlienvaultusessaieesha2010Оценок пока нет
- Ian 160q PDFДокумент48 страницIan 160q PDFDidier Choque AbayoОценок пока нет
- STДокумент5 страницSTJinto Thomas KidangattilОценок пока нет
- Portals 0 Images CEH-brochureДокумент12 страницPortals 0 Images CEH-brochureAnOop KaUshalОценок пока нет
- ECSS v3 BrochureДокумент39 страницECSS v3 BrochureMahesh BhatОценок пока нет
- Python for Cybersecurity: Using Python for Cyber Offense and DefenseОт EverandPython for Cybersecurity: Using Python for Cyber Offense and DefenseОценок пока нет
- Certified Ethical Hacker ProgramsДокумент18 страницCertified Ethical Hacker ProgramsJacques BeaubrunОценок пока нет
- Penetration Test Process and Types FactsДокумент5 страницPenetration Test Process and Types FactsKimberly PinedaОценок пока нет
- CISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024От EverandCISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024Оценок пока нет
- A Seminar Report On: Ethical HackingДокумент27 страницA Seminar Report On: Ethical HackingvijayОценок пока нет
- Penetration Testing: An Art of Securing The System (Using Kali Linux)Документ8 страницPenetration Testing: An Art of Securing The System (Using Kali Linux)Carolus GazaОценок пока нет
- Cybersecuritypedia - Ethical Hacking Questions and AnswersДокумент33 страницыCybersecuritypedia - Ethical Hacking Questions and Answersmayurigupta007Оценок пока нет
- Certified Penetration TesterДокумент14 страницCertified Penetration TesterEvangal jeksonОценок пока нет
- CEHv10 Course OutlineДокумент46 страницCEHv10 Course OutlineNaitik Haiking0% (1)
- Certified Penetration TesterДокумент14 страницCertified Penetration TesterEvangal jeksonОценок пока нет
- Pen Testing BasicsДокумент153 страницыPen Testing BasicsChristopher C. Cheng100% (2)
- UntitledДокумент139 страницUntitledJuancaОценок пока нет
- Certified Ethical Hacking: Ron Woerner, CISSP, CEHДокумент35 страницCertified Ethical Hacking: Ron Woerner, CISSP, CEHranjithc24Оценок пока нет
- EC-Council - Certified Security Analyst: Course Introduction Student IntroductionДокумент30 страницEC-Council - Certified Security Analyst: Course Introduction Student IntroductionSalman AslamОценок пока нет
- Syllabus-Certified Pentester & Bug Hunter (CPTBH) - PremiumДокумент22 страницыSyllabus-Certified Pentester & Bug Hunter (CPTBH) - Premiumbug bountyОценок пока нет
- SSL VPN : Understanding, evaluating and planning secure, web-based remote accessОт EverandSSL VPN : Understanding, evaluating and planning secure, web-based remote accessОценок пока нет
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021От EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021Оценок пока нет
- Penetration Testing Fundamentals -1: Penetration Testing Study Guide To Breaking Into SystemsОт EverandPenetration Testing Fundamentals -1: Penetration Testing Study Guide To Breaking Into SystemsОценок пока нет
- CEH and Security+ Course OutlineДокумент17 страницCEH and Security+ Course Outlineahaque08Оценок пока нет
- CompTia CH7 Host, Data, and Application SecurityДокумент5 страницCompTia CH7 Host, Data, and Application SecurityVVetoОценок пока нет
- Certified Ethical Hacker v9Документ9 страницCertified Ethical Hacker v9JJ Asonyer100% (1)
- Siberseguridad Todo Copiado Aqui 2020Документ29 страницSiberseguridad Todo Copiado Aqui 2020vladi reyОценок пока нет
- CEH v7 and CEH v6.1 Exam Objectives Comparison-1Документ18 страницCEH v7 and CEH v6.1 Exam Objectives Comparison-1zecedegeteОценок пока нет
- Examen - CEHv10-1Документ24 страницыExamen - CEHv10-1Benyhi Deyvi Mantilla FloresОценок пока нет
- Security TestingДокумент7 страницSecurity TestingGedi Chandra Mohan ReddyОценок пока нет
- Cyber Security MumbaiДокумент18 страницCyber Security Mumbairony raiОценок пока нет
- Ethical HackerДокумент196 страницEthical HackerMarco Antonio Martinez AndradeОценок пока нет
- Exam CEHv10Документ30 страницExam CEHv10Benyhi Deyvi Mantilla FloresОценок пока нет
- CEH v6.1 PISДокумент103 страницыCEH v6.1 PIStawhide_islamicОценок пока нет
- ReportДокумент12 страницReportpkpscОценок пока нет
- Ethical Hacking: Keith Brooks CIO and Director of Services Vanessa Brooks, Inc. Twitter/Skype: LotusevangelistДокумент34 страницыEthical Hacking: Keith Brooks CIO and Director of Services Vanessa Brooks, Inc. Twitter/Skype: Lotusevangelistjindalyash1234Оценок пока нет
- Ethical HackingДокумент109 страницEthical HackingRameswar ReddyОценок пока нет
- ECSS v3 BrochureДокумент39 страницECSS v3 Brochurekojo2kgОценок пока нет
- Uipe Graduate Membership FormДокумент7 страницUipe Graduate Membership FormJustin MugissaОценок пока нет
- Long Play Version of SM 911Документ6 страницLong Play Version of SM 911dОценок пока нет
- 01 Samss 039Документ14 страниц01 Samss 039azhar enggОценок пока нет
- MZ15313U Product OverViewДокумент4 страницыMZ15313U Product OverViewsp.marianОценок пока нет
- Learn R Programming in A DayДокумент229 страницLearn R Programming in A Daymigust100% (6)
- 0readme DPSFДокумент3 страницы0readme DPSFgforce_haterОценок пока нет
- Satel Price List October 2013Документ2 страницыSatel Price List October 2013spyroszafОценок пока нет
- ASQ Certified Quality Inspector Body of KowledgeДокумент7 страницASQ Certified Quality Inspector Body of Kowledgeblack bettyОценок пока нет
- Reliability: Supplement OutlineДокумент19 страницReliability: Supplement OutlineRamesh AlhatОценок пока нет
- Rule: Airports: General ElectricДокумент3 страницыRule: Airports: General ElectricJustia.comОценок пока нет
- The DES Algorithm Illustrated: by J. Orlin GrabbeДокумент14 страницThe DES Algorithm Illustrated: by J. Orlin GrabbeHaris ClovesОценок пока нет
- HPE ProLiant DL380 Gen10 Server UKDoC HSTNS-5200-a50005003enwДокумент3 страницыHPE ProLiant DL380 Gen10 Server UKDoC HSTNS-5200-a50005003enwhesmaileeОценок пока нет
- Ikoy's Computer Shop Timer and Monitoring SystemДокумент20 страницIkoy's Computer Shop Timer and Monitoring SystemPresley Lecaroz0% (1)
- c501 ManualДокумент15 страницc501 ManualjosueramirОценок пока нет
- Waleed Khattak CVДокумент2 страницыWaleed Khattak CVwaleed1212Оценок пока нет
- Jindal Panther PDFДокумент11 страницJindal Panther PDFzilangamba_s4535Оценок пока нет
- Norma A751Документ5 страницNorma A751Dionisio Hidalgo SanchezОценок пока нет
- Visual Inspection of Defects and DiscontinuitiesДокумент21 страницаVisual Inspection of Defects and Discontinuitiessanketpavi21Оценок пока нет
- SEJ BoardДокумент15 страницSEJ BoardTarun ChopraОценок пока нет
- Appendix 3 Bsc6900 Umts v900r014c00spc500 Alarm Changes (Vs v9r13c00spc500)Документ17 страницAppendix 3 Bsc6900 Umts v900r014c00spc500 Alarm Changes (Vs v9r13c00spc500)Ramiro GonzalezОценок пока нет
- Nokia E72 User Guide (En)Документ141 страницаNokia E72 User Guide (En)jeff slaterОценок пока нет
- Indique Law Journal GuidelinesДокумент12 страницIndique Law Journal GuidelinesAryan MewadaОценок пока нет
- SQL Error CodesДокумент160 страницSQL Error CodesdsbdayalОценок пока нет
- SAP® Disclosure Management 10.0, Starter Kit For U.S. GAAP: Configuration OverviewДокумент29 страницSAP® Disclosure Management 10.0, Starter Kit For U.S. GAAP: Configuration OverviewCátia Coelho SilvaОценок пока нет
- Functional Configuration AuditДокумент5 страницFunctional Configuration AuditSabahat Hussain100% (1)
- Volkswagen Scirocco R BrochureДокумент2 страницыVolkswagen Scirocco R BrochureUmar FaruqОценок пока нет
- Windows Management Framework 4 0 Release NotesДокумент22 страницыWindows Management Framework 4 0 Release NotesJohn RofinОценок пока нет
- 8002 Pacom Edge Controller DatasheetДокумент3 страницы8002 Pacom Edge Controller DatasheetJonathan Pérez Salazar50% (2)
- Motoped Pro AssemblyДокумент112 страницMotoped Pro AssemblyLuis Rivera100% (1)
- FMRC 6049 Flammable and Combustible Liquid Storage BuildingsДокумент19 страницFMRC 6049 Flammable and Combustible Liquid Storage Buildingsdyıldırım_4Оценок пока нет