Академический Документы
Профессиональный Документы
Культура Документы
IT Summary Chapter 7
Загружено:
simcityfreak0 оценок0% нашли этот документ полезным (0 голосов)
14 просмотров3 страницыSummary of IT chapter 7. Legal work.
Авторское право
© © All Rights Reserved
Доступные форматы
DOC, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документSummary of IT chapter 7. Legal work.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOC, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
14 просмотров3 страницыIT Summary Chapter 7
Загружено:
simcityfreakSummary of IT chapter 7. Legal work.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOC, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 3
Chapter 7 Summaries
Storage, communication and disposal of data and information
Organisational goals and information systems
Mission statement defines organisation's purpose or what it is trying to achieve
Organisational goals explain how an organisation intends to go about achieving its
mission
System goal explains the specific role of the information system in achieving the
organisational goal and ultimately the companies mission
Legal obligations of organisations and individuals
Privacy Act 1998
Deals with 3 Main Areas:
Safeguards relating to the collection and use of TFN by federal government agencies
Protection of individuals private information stored by federal government departments
Information about peoples credit-worthiness held by credit reporting agencies and credit
providers
Privacy Amendment (Private Sector) Act 2000
11 National Privacy Principles
0. Manner and purpose of collection of personal information
1. Solicitation of personal information from the individual concerned
2. Solicitation of personal information generally
3. Storage and security of personal information
4. Information relating to records kept by the record keeper
5. Access to records containing personal information
6. Alteration of records containing personal information
7. Record keeper to check accuracy etc of personal information before use
8. Personal information to be used only for relevant purposes
9. Limits on the use of personal information
10. Limits on the disclosure of personal information
Information Privacy Act 2000
Victorian government policy outlining the privacy obligations of state government agencies
and contractors working for the state government.
Health Records Act 2001
Aim to protect patients medical information. Created separately to IPA as to cover both the
public and private hospital sectors. Protects patients information to be used only for their
primary purpose for which it was gathered.
Copyright Act 1968
Intellectual property might be defined as any product of human thought that us unique and
not self evident. The copyright act protects this property.
There are allowances made for formats such as audio music where you are allowed to
burn tracks to another cd for personal use and transfer them to mp3 players.
Other formats are much more heavily restricted such as games and computer software
where there may be multiple complex copyright issues with the design of a game.
Penalties
Most copyright infringements are dealt with as civil matters. When there has been
commercial distribution of pirated material the case will be tried as a criminal matter.
Civil matters will vary in the remedy awarded to the defendant.
In criminal cases, fines may be imposed up to $60500 and or up to 5 years imprisonment.
Ethics and information systems
Ethics refers to behaving ways based on our morals.
Key areas that affect employees, employers and clients or customers:
The responsibilities of employers and employees to each other and clients
Codes of conduct
Company computer use policies
Employee monitoring
Free speech on the internet
Steps to solving ethical dilemmas
11. Identify the problem
12. Identify the stakeholders
13. Identify possible alternatives
14. Identify ethical standards
15. Evaluate options
16. Make a decision
Workplace responsibilities
Between one another and customers or clients. Employer must pay staff for the work
carried out and provide a suitable environment that work can take place.
Organisation is expected to provide good quality products or high level service to
customers.
Codes of conduct and computer use polices
Code of conduct is a set of conventional principles and expectations considered binding on
any member of a particular group.
Computer use policy should be in place by an organisation. This explains clearly to those
using the equipment what management believes should and should not be done on the
computers or peripherals.
Employee Monitoring
Managers often use monitoring systems to check what their employees are doing. This
includes email checks for obscene language or attachments such as .exe or .jpg.
Mangers also monitor the use of the Internet as many employees "misuse" the net for
personal purposes.
Netiquette
Not posting to inappropriate groups
Refraining from commercial advertising
Personal messages to one or two individuals should not be posted to newsgroups
When responding to posting, the minimum necessary context should be quoted
Lines should be less than 70 characters long
Before asking a question a user should read existing questions and the groups FAQ
Threats to data and information
What is security?
Any measures that an organisation can take to minimise the potential loss of data by
intentional or accidental threats.
Intentional Damage
Viruses
Hacking/Cracking
Tampering with files
Information theft
Vandalism of hardware
Theft of hardware
Accidental Damage
User error
Failure to follow file management procedures
Equipment failure/damage
Consequences of violating security and privacy measures
Consequences include but are not limited to:
Breaches of privacy
Loss of intellectual property
Loss of income due to unavailability of information or services
Вам также может понравиться
- May 5 - 6 Phillip Island CAMS National RoundДокумент1 страницаMay 5 - 6 Phillip Island CAMS National RoundsimcityfreakОценок пока нет
- WOW AddonsДокумент1 страницаWOW AddonssimcityfreakОценок пока нет
- Aircraft: Importing Into FSXДокумент5 страницAircraft: Importing Into FSXsimcityfreakОценок пока нет
- Time ConnectivesДокумент1 страницаTime ConnectivessimcityfreakОценок пока нет
- Practical Investigation: Ticker-Timer ExperimentДокумент2 страницыPractical Investigation: Ticker-Timer ExperimentsimcityfreakОценок пока нет
- Fill in The Gaps in The Sentences With A Joining Word From The BalloonsДокумент1 страницаFill in The Gaps in The Sentences With A Joining Word From The BalloonssimcityfreakОценок пока нет
- Thank You For Downloading My Decimal BINGO!Документ11 страницThank You For Downloading My Decimal BINGO!simcityfreakОценок пока нет
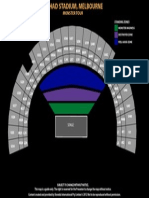
- MonsterTour Etihad MelbourneДокумент1 страницаMonsterTour Etihad MelbournesimcityfreakОценок пока нет
- Unit Planner-Three SessionsДокумент5 страницUnit Planner-Three SessionssimcityfreakОценок пока нет
- Android IntroДокумент2 страницыAndroid IntrosimcityfreakОценок пока нет
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5795)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1091)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Smart City Cyber Security, Privacy: Rama Vedashree Ceo, DsciДокумент7 страницSmart City Cyber Security, Privacy: Rama Vedashree Ceo, DsciAtul SaikumarОценок пока нет
- 9AKK101130D1384 - PGPdisplayBuilder ManualДокумент271 страница9AKK101130D1384 - PGPdisplayBuilder ManualanbarasanОценок пока нет
- CF CRДокумент1 244 страницыCF CRapi-235354823Оценок пока нет
- SeminarДокумент16 страницSeminarAjay RajОценок пока нет
- SECURING ProjectДокумент23 страницыSECURING Projectsaadsidd22Оценок пока нет
- CCNA3-G11 CertificadoДокумент1 страницаCCNA3-G11 CertificadoJorge Félix González AcostaОценок пока нет
- Boobalan V: Graphic DesignerДокумент1 страницаBoobalan V: Graphic DesignerSelvakumar DОценок пока нет
- Final Project CpeДокумент15 страницFinal Project CpeKael Aaron GallanoОценок пока нет
- SRSДокумент21 страницаSRSAkshay100% (1)
- Cse308 - Operating Systems: G.Manikandan Sap / Ict / Soc SastraДокумент15 страницCse308 - Operating Systems: G.Manikandan Sap / Ict / Soc SastraPuttu PuneetОценок пока нет
- Release Notes GLD Editor V1.51 2Документ3 страницыRelease Notes GLD Editor V1.51 2Papa ConfiОценок пока нет
- File Storage Performance GuideДокумент7 страницFile Storage Performance GuideCarlos Alexandre MansurОценок пока нет
- Welcome To The World of Iot!: Seamless, Simple Yet Sophisticated!Документ8 страницWelcome To The World of Iot!: Seamless, Simple Yet Sophisticated!Franco BarezziОценок пока нет
- C-Programming TutДокумент56 страницC-Programming Tutapi-657085471Оценок пока нет
- Calculator in Go and FyneДокумент18 страницCalculator in Go and Fynemamta yadavОценок пока нет
- Oracle Linux 8: Installing Oracle LinuxДокумент58 страницOracle Linux 8: Installing Oracle Linuxcoky doank100% (1)
- 2018 - Avaya Call Reporting Installation Guide - Final V2Документ18 страниц2018 - Avaya Call Reporting Installation Guide - Final V2ursus006Оценок пока нет
- E4990A Help PDFДокумент685 страницE4990A Help PDFMarisol VenegasОценок пока нет
- Ruijie RG-RSR77-XA Series Routers Datasheet (1) - 1Документ10 страницRuijie RG-RSR77-XA Series Routers Datasheet (1) - 1harry chan PutraОценок пока нет
- Data Modeling Part 3 - PracticalДокумент19 страницData Modeling Part 3 - PracticalBOCIL GAMINGОценок пока нет
- Tiksha Kakade's ResumeДокумент2 страницыTiksha Kakade's Resumeomkar dhumaleОценок пока нет
- At The End of This Topic, Students Will Be Able To:: Learning ObjectivesДокумент5 страницAt The End of This Topic, Students Will Be Able To:: Learning ObjectivesRuby Alintana PantiОценок пока нет
- Spartan Controls Ltd. Field Trouble Shooting GuideДокумент48 страницSpartan Controls Ltd. Field Trouble Shooting GuideBill Kerwin Nava Jimenez100% (1)
- Work With Maxbox InsiderДокумент12 страницWork With Maxbox InsiderMax KleinerОценок пока нет
- HCIE-R&S Huawei Certified Internetwork Expert-Routing and Switching Material V1.1Документ1 212 страницHCIE-R&S Huawei Certified Internetwork Expert-Routing and Switching Material V1.1stanleyОценок пока нет
- Tree and Its TerminologiesДокумент36 страницTree and Its TerminologiesKHAWAJA MANNANОценок пока нет
- Apple Laptop PricesДокумент9 страницApple Laptop PricesAdriana SharmaineОценок пока нет
- Scala and Spark For Big Data AnalyticsДокумент874 страницыScala and Spark For Big Data AnalyticsSneha SteevanОценок пока нет
- Software Requirement Specification On: Prison Management SystemДокумент37 страницSoftware Requirement Specification On: Prison Management SystemSEENU MANGALОценок пока нет
- 1998-09 The Computer Paper - Ontario EditionДокумент165 страниц1998-09 The Computer Paper - Ontario EditionthecomputerpaperОценок пока нет