Академический Документы
Профессиональный Документы
Культура Документы
BAIN BRIEF Why Cybersecurity Is A Strategic Issue
Загружено:
najod310 оценок0% нашли этот документ полезным (0 голосов)
81 просмотров8 страницBAIN BRIEF Why Cybersecurity is a Strategic Issue from BAIN
Оригинальное название
BAIN BRIEF Why Cybersecurity is a Strategic Issue
Авторское право
© © All Rights Reserved
Доступные форматы
PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документBAIN BRIEF Why Cybersecurity is a Strategic Issue from BAIN
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
81 просмотров8 страницBAIN BRIEF Why Cybersecurity Is A Strategic Issue
Загружено:
najod31BAIN BRIEF Why Cybersecurity is a Strategic Issue from BAIN
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 8
Why cybersecurity is a strategic issue
Is your business one hack away from disaster?
By Syed Ali, Vishy Padmanabhan and Jim Dixon
Syed Ali is a principal with Bain & Company in Chicago. Vishy Padmanabhan
is a partner with Bain & Company in Dallas. Jim Dixon is a partner in Bains
Palo Alto ofce. All three work with Bains Global Information Technology practice.
Copyright 2014 Bain & Company, Inc. All rights reserved.
Why cybersecurity is a strategic issue
1
When you think of the billions of dollars organizations
spend to protect their digital assets, its amazing that
hardly a week goes by without news of a major security
breach. We see not only more attacks, but larger, more
complex and targeted incursions on organizations for
nancial gain (se Figure 1). Some enterprises face
advanced persistent threats (APTs), a highly sophisticated
form of malware that permeates the organization, mutates
into variants, remains innocuous and undetected for a
long time, and stealthily accesses and transmits corporate
assets. The sought-after digital assets include intel-
lectual property (IP), trade secrets, and customer and
nancial data (se Figure 2).
Organizations are having a tougher time mitigating
security breaches, and the average nancial impact of
each breach on an organization is increasing (see
Figure 3). Whats more, its becoming harder to keep
these attacks out of the news. Often, clients or regulatory
agencies require companies to disclose breaches; in
other cases, attackers themselves distribute the pilfered
information online. In many cases, the consequences for
organizations can be devastating in terms of lost revenue,
impugned reputations and nancial repercussions.
For example, an October 2013 attack on Adobe resulted
in the theft of customer data from 38 million accounts
and of valuable source code behind some of Adobes
most widely used products, including Reader, Photo-
Shop and ColdFusion.
Only two months later, in December 2013, Target Corpo-
ration confirmed that it suffered a massive security
breach resulting in the loss of credit and debit card data
on 40 million customers over a 19-day period. The data
may have been harvested by malware affecting physical
point-of-sale systems at nearly 2,000 Target stores.
The immediate consequences for a company dealing
with a customer data breach are severe and may include
negative press, sales and stock price decline (at least
immediately after the breach), the threat of lawsuits
from customers and partners, and long legal investiga-
tions. When attackers gain access to the source code
Figure 1: Deeper and broader security vulnerabilities seem to correlate with more attacks and malware
Sources: MITRE CVE; Symantec; Trend Micro; Bain analysis
New vulnerabilities across all platforms Daily Web attacks blocked
Increasing rate of newly reported vulnerabilities,
especially in mobile platforms
seems to be correlated with a higher rate of attacks
and exponential growth in malware
2011
44%
50%
6%
4.2K
2012
33%
57%
10%
5.3K
+27%
High severity
Medium
severity
Low severity
2011 2012
190.4K
247.4K
+30%
2011
19%
29%
52%
315
2012
45%
41%
14%
415
+32%
Android
iOS
Other
New vulnerabilities in mobile platforms Cumulative volume of Android malware
2011 2012
1.2K
350.0K
+30,335%
2
Why cybersecurity is a strategic issue
Figure 3: Security breaches are becoming more difcult and expensive to detect and mitigate
Sources: Trustwave; Ponemon Institute; Bain analysis
Organizations are having a harder time detecting
and resolving security breaches
and the average financial impact of each breach
on an organization is increasing
2011 2012
174
18
192
210
24
234
+22%
Average days
to detect
Average days
to resolve
2011 2012
$8M
$9M
+6%
Figure 2: Most attacks come from outsiders looking for nancial gain
Sources: Symantec; Verizon 2011 investigations; Trustwave; Bain analysis
An increasing number of organizations
are being targeted directly
resulting in the loss of sensitive data
that can easily be monetized
with financial gain as
the primary motivation
2011 2012
82
116
+51%
Targeted assets
6%
94%
3%
2%
Customer
records
Corporate
trade
secrets
and IP
Protected
health
information
(PHI)
Other
corporate
information
Motivation
3%
94%
2%
1%
Financial
gain
Hactivism
Curiosity or
pride
Personal
grudge
Why cybersecurity is a strategic issue
3
of software products, they can find and exploit new
vulnerabilities (so-called zero-day attacks) that could
affect corporate and customer systems, data and devices.
With stakes so high, CEOs and boards must begin to
think about security in a new way. IT securitya task
that could once be delegated to the IT staffhas become
a top-level strategic issue because the consequences of
failure can ruin a business. Any organization may be
only a few hacks away from disaster.
And yet, every organization that found itself on the wrong
end of a security breach already had some form of cyber-
security in place. The names in recent headlines include
banks, technology and media companies, retailers,
research universities as well as security agenciesnone
of which are new to the game of protecting information.
So how is it that they found themselves ill-equipped to
deal with the rising tide of threats?
In our experience working with many leading enter-
prises on this important and sensitive issue, we see too
many organizations that fail to align their IT security
capabilities with their larger goals and appetite for risk.
At some companies, business and IT dont discuss
emerging threats or the relative importance of different
classes of digital assets. Not surprisingly, we frequently see
disconnects between an organizations risk-management
efforts and the development of necessary cybersecurity
capabilities. And too often, we see fits and starts, as
teams take an inconsistent approach to security planning,
operations and funding. Taken together, these mistakes
create gaps in strategy and operations that leave the
organization vulnerable.
New challenges for cybersecurity
Cybersecurity has never been more essential, for at
least four major reasons. First, companies have more
digital assets than they did 10 years ago, and these assets
are worth more than they were before. They include cus-
tomers personal, nancial and transaction information;
proprietary assets, including source code for products;
automated business processes; sensitive communications
with suppliers and partners; and other data. The security
around these assets varies greatly depending upon the
perceived (as opposed to the actual) nancial and strategic
value to the business, as well as the effectiveness of the
security technologies and processes in place.
Whats more, organizations are shifting to hybrid cloud
architectures as they continue to adopt software, security
and other solutions as services (SaaS, SECaaS and so on).
Historically, digital assets were protected within the
companys data center, where it was easier to guard the
perimeter and manage user access, authorization and
authentication from known locations and devices. Today,
corporate and customer data resides in the organizations
own data centers as well as public and private clouds,
distributed across remote locations. While hybrid cloud
architectures offer signicant economic benets, their
adoption requires a more sophisticated approach to
cybersecurity, including security management at the
level of individual digital assets and integrated moni-
toring and management capabilities across the hybrid
cloud environment.
Further complicating the challenge is the pervasive use
of mobile devices by staff and executives. Corporate IT
now has to manage the security of many more platforms
and devices, some owned by the company and others
that belong to employees who use them under bring-
your-own-device (BYOD) plans. A recent survey by ISACA
1
found that up to 66% of organizations will soon adopt
BYOD policies, yet half of IT staff members remain
concerned about the inherent security risks. To manage
these policies effectively, IT organizations will need to
provide ubiquitous security across many devices and
comprehensively manage user identity and access to
sensitive corporate data.
Finally, compliance remains the most important cyber-
security driver, especially for companies in regulated
industries or with contractual obligations. In a recent
Bain survey, more than 75% of CIOs identied com-
pliance requirements as the main determinant of invest-
ment in IT security. Another recent survey of IT staff
by ISACA found that outside of compliance obligations,
4
Why cybersecurity is a strategic issue
Identify the security risks and gaps. Assess current
security capabilities and determine the likelihood of
experiencing known and emerging risks. Business
and IT leaders should then align on the gaps and
the estimated mitigation costs.
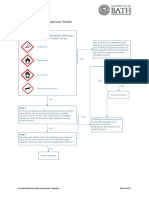
Dene the cybersecurity strategy. Based on a thorough
understanding of the organizations security prior-
ities and gaps, IT should create comprehensive
technology, process and organizational designs and
blueprints with strategic and operational elements
that protect digital assets (se Figure 4).
Emphasize gaps, priorities and strategy to the CEO and
board. Leadership should know about the security-
related risks and gaps they face, so they can understand
the importance of the investments required.
Engage recognized security specialists. As the threat
landscape expands and attacks become more sophis-
ticated, organizations should work closely with
rms that can provide ongoing services to diagnose,
redesign and monitor their cybersecurity.
IT has insufficient resources and limited business
engagement for effective risk management.
2
These nd-
ings highlight the operational approach to cybersecurity
taken by many organizations. Compliance should
dene the lower bound for security capabilities while
the upper bound should aspire to meet the organiza-
tions strategic priorities, including IP protection, con-
tinuous operations and a secure corporate reputation.
Protecting your data, reputation and business
Leading organizations take a more strategic rather than
an operational approach to security to respond to the
new challenges.
Understand the organizations key assets and appetite
for risk. Align business and IT leaders on the prior-
itization of digital assets based on value and risk
to the organization to ensure the proper design of
technology, processes and supporting resources.
For example, customer data, point-of-sale and order
management systems are a higher priority while
marketing and promotion systems may be lower.
Figure 4: Bains approach to cybersecurity aligns strategic imperatives with the necessary operational capabilities
Business alignment
Does IT understand the organizations security needs and its appetite for risk?
Are senior leaders involved?
O
p
e
r
a
t
i
o
n
a
l
S
t
r
a
t
e
g
i
c
IT risk management
How is risk proactively gauged and managed?
Who aligns risk mitigation with IT policies?
Administration
Does IT have an accountable and empowered chief information security officer and team?
Does IT have funding for the necessary security capabilities?
Architecture and engineering
Does the strategic security plan and solution design reflect standards and
best practices for dealing with current and emerging threats?
Is security applied at the digital asset level?
Monitoring and operations
Is security equipped to identify and make a coordinated response to threats?
Is there ongoing user training on security practices and threat awareness?
Are there integrated monitoring capabilities across the hybrid cloud environment?
Physical security
Are data centers and other facilities as secure as virtual assets?
Are user devices encrypted and enabled for remote security management?
Source: Bain & Company
1 ISACA: 2013 IT Risk/Reward Barometer Global Results
2 ISACA: 2012 Study on Application Security
Shared Ambiion, Tru Rsults
Bain & Company is the management consulting rm that the worlds business leaders come
to when they want results.
Bain advises clients on strategy, operations, technology, organization, private equity and mergers and acquisitions.
We develop practical, customized insights that clients act on and transfer skills that make change stick. Founded
in 1973, Bain has 50 ofces in 32 countries, and our deep expertise and client roster cross every industry and
economic sector. Our clients have outperformed the stock market 4 to 1.
What sets us apart
We believe a consulting rm should be more than an adviser. So we put ourselves in our clients shoes, selling
outcomes, not projects. We align our incentives with our clients by linking our fees to their results and collaborate
to unlock the full potential of their business. Our Results Delivery
process builds our clients capabilities, and
our True North values mean we do the right thing for our clients, people and communitiesalways.
For more information, visit www.bain.com
Key contacts in Bains Global Information Technology practice:
Americas: Syed Ali in Chicago (syed.ali@bain.com)
Steve Berez in Boston (steve.berez@bain.com)
Vishy Padmanabhan in Dallas (vishy.padmanabhan@bain.com)
Rudy Puryear in Chicago (rudy.puryear@bain.com)
Jean-Claude Ramirez in So Paulo (jean-claude.ramirez@bain.com)
Jonathan Stern in San Francisco (jonathan.stern@bain.com)
Rasmus Wegener in Atlanta (rasmus.wegener@bain.com)
Asia-Pacic: Arpan Sheth in Mumbai (arpan.sheth@bain.com)
Peter Stumbles in Sydney (peter.stumbles@bain.com)
Europe, Middle East Thomas Gumsheimer in Frankfurt (thomas.gumsheimer@bain.com)
and Africa: Marc Lino in Amsterdam (marc.lino@bain.com)
Stephen Phillips in London (stephen.phillips@bain.com)
Sachin Shah in London (sachin.shah@bain.com)
Вам также может понравиться
- Data ProtectionДокумент3 страницыData ProtectionppallavseoОценок пока нет
- Ebook CyberSecurityДокумент14 страницEbook CyberSecurityharvinder singhОценок пока нет
- Cyber Risk Appetite WP - 2Документ4 страницыCyber Risk Appetite WP - 2Muhamad Fadzel AbdullahОценок пока нет
- Cyber Risk Appetite WPДокумент4 страницыCyber Risk Appetite WPMuhamad Fadzel AbdullahОценок пока нет
- The Data Centric Security ParadigmДокумент10 страницThe Data Centric Security ParadigmLuke O'ConnorОценок пока нет
- Lesson 3 PDFДокумент8 страницLesson 3 PDFJacob Satorious ExcaliburОценок пока нет
- CISSE - Organization Security Controls For Effective Cyber Defense - ProceedingsДокумент25 страницCISSE - Organization Security Controls For Effective Cyber Defense - Proceedingsmichellee12Оценок пока нет
- Security Through Information Risk ManagementДокумент13 страницSecurity Through Information Risk ManagementPat NОценок пока нет
- CYB401Документ14 страницCYB401yormie2019Оценок пока нет
- 3736 GUI Cybersecurity TrendsДокумент14 страниц3736 GUI Cybersecurity TrendsNatnael TafesseОценок пока нет
- IT Security and Risk ManagementДокумент10 страницIT Security and Risk ManagementNikhil GangwarОценок пока нет
- The Business Owner's Guide to Cybersecurity: Protecting Your Company from Online ThreatsОт EverandThe Business Owner's Guide to Cybersecurity: Protecting Your Company from Online ThreatsОценок пока нет
- Expanding The Strategic Security Conversation: Impact of AIДокумент9 страницExpanding The Strategic Security Conversation: Impact of AIblack MirrorОценок пока нет
- Cyber Trends 2020 ReportДокумент10 страницCyber Trends 2020 ReportDogan AkcayОценок пока нет
- Building A Cybersecurity Audit Risk Assessment EbookДокумент16 страницBuilding A Cybersecurity Audit Risk Assessment EbookDavi DE SouzaОценок пока нет
- IT and Cyber Risks Ebook Hartman Executive AdvisorsДокумент13 страницIT and Cyber Risks Ebook Hartman Executive AdvisorsArin DaSilvaОценок пока нет
- Elevating the Discussion on the Data Centric Security ModelДокумент10 страницElevating the Discussion on the Data Centric Security ModelNinis UnoОценок пока нет
- Garrett Saiki - Blog WritingДокумент7 страницGarrett Saiki - Blog WritingG SОценок пока нет
- Enterprise IT Security: The Ultimate GuideДокумент44 страницыEnterprise IT Security: The Ultimate GuideVlad VikernesОценок пока нет
- Defending Your Budget: How To Show ROI of Cybersecurity InvestmentsДокумент7 страницDefending Your Budget: How To Show ROI of Cybersecurity InvestmentsTanteОценок пока нет
- Cybersecurity Career Guide 2020Документ20 страницCybersecurity Career Guide 2020Pakeeza AwanОценок пока нет
- 2009 01 08 Barry Foer and Larry Clinton ISA Comprehensive Overview For Critical Infrastructure Partnership Advisory Council CIPAC PresentationДокумент43 страницы2009 01 08 Barry Foer and Larry Clinton ISA Comprehensive Overview For Critical Infrastructure Partnership Advisory Council CIPAC PresentationisallianceОценок пока нет
- Dataguise WP Why Add Masking PDFДокумент8 страницDataguise WP Why Add Masking PDFdubillasОценок пока нет
- SailPoint Horizons of Identity Security Report 2023 SP2336Документ39 страницSailPoint Horizons of Identity Security Report 2023 SP2336pnorbertoОценок пока нет
- Risk Assessment (Assessment 2)Документ13 страницRisk Assessment (Assessment 2)Mitali BiswasОценок пока нет
- Cyber SecurityДокумент19 страницCyber Securityjavaria_ashraf_5100% (2)
- The Importance of Cybersecurity Department of Justice, Yahoo and JP Morgan ChasДокумент3 страницыThe Importance of Cybersecurity Department of Justice, Yahoo and JP Morgan ChasVesa LokuОценок пока нет
- Csol 560-Final-Assignment 7-Enterprise Information Security Risk Assessment-Aris Nicholas-4-17-2023Документ29 страницCsol 560-Final-Assignment 7-Enterprise Information Security Risk Assessment-Aris Nicholas-4-17-2023api-654754384Оценок пока нет
- Compliance Concepts With Microsoft 365: Digital Estate, Have Grown Enormously in Recent Years and So Have TheДокумент51 страницаCompliance Concepts With Microsoft 365: Digital Estate, Have Grown Enormously in Recent Years and So Have TheYesika GonzalezОценок пока нет
- 2008 11 19 Larry Clinton ISA Overview and International Outreach To PortugalДокумент34 страницы2008 11 19 Larry Clinton ISA Overview and International Outreach To PortugalisallianceОценок пока нет
- ISNS Winter 2012Документ39 страницISNS Winter 2012PranavPksОценок пока нет
- Digital Resilience Seven Practices in Cybersecurity Digital McKinseyДокумент3 страницыDigital Resilience Seven Practices in Cybersecurity Digital McKinseyJohn evansОценок пока нет
- 1.2.1 Types of Organizational DataДокумент12 страниц1.2.1 Types of Organizational DataHunde gutemaОценок пока нет
- Ucc301 ProposalДокумент10 страницUcc301 ProposalNjeru DanielОценок пока нет
- Loss or Theft of Intellectual PropertyДокумент8 страницLoss or Theft of Intellectual PropertyWipuli Lochana DisanayakeОценок пока нет
- Becoming A Cybersecurity ExpertДокумент8 страницBecoming A Cybersecurity ExpertDimitrisMaketasОценок пока нет
- Top Causes of Security BreachesДокумент6 страницTop Causes of Security BreachesMarcelo Plada IntОценок пока нет
- Csol 580 Week 7Документ8 страницCsol 580 Week 7api-487513274Оценок пока нет
- The Business Case For A Next Generation SIEMДокумент11 страницThe Business Case For A Next Generation SIEMGheorghica AndreeaОценок пока нет
- Cyber-Ark (NASDAQ: CYBR)Документ5 страницCyber-Ark (NASDAQ: CYBR)The Focused Stock TraderОценок пока нет
- Chapter 7 Data Security - DONE DONE DONEДокумент41 страницаChapter 7 Data Security - DONE DONE DONERoche ChenОценок пока нет
- Information Assurance and Cybersecurity SolutionsДокумент18 страницInformation Assurance and Cybersecurity Solutionszahra zahidОценок пока нет
- Top Trends in Cybers 760806 NDXДокумент22 страницыTop Trends in Cybers 760806 NDXAmit CohenОценок пока нет
- Class Case Work # 1 (Group Work) Data Science: "Identifying The Most Suitable Network Security Software For Alpha 365"Документ12 страницClass Case Work # 1 (Group Work) Data Science: "Identifying The Most Suitable Network Security Software For Alpha 365"Alex AndersenОценок пока нет
- Order 2434907.editedДокумент8 страницOrder 2434907.editedPaul WahomeОценок пока нет
- Cyber Security Program: Student's Name Institution Affiliation Course Name Instructor's Name DateДокумент17 страницCyber Security Program: Student's Name Institution Affiliation Course Name Instructor's Name DateEPIC BRIEFSОценок пока нет
- Step 8: Policy Revisions Evaluation: Name of Student: Course: Institution: Date of SubmissionДокумент12 страницStep 8: Policy Revisions Evaluation: Name of Student: Course: Institution: Date of SubmissionsamwiseОценок пока нет
- Insider Threat Report May 2020 SecuronixДокумент13 страницInsider Threat Report May 2020 SecuronixDebarati GuptaОценок пока нет
- IDC Report 2019Документ7 страницIDC Report 2019Julie SmithОценок пока нет
- 03 Aacb 067083 D 5 FFДокумент11 страниц03 Aacb 067083 D 5 FFWolf RichardОценок пока нет
- Accenture Strategy Cybersecurity in Banking PDFДокумент9 страницAccenture Strategy Cybersecurity in Banking PDFTejas JadhavОценок пока нет
- Future-Proofing Your Authentication Infrastructure WPДокумент6 страницFuture-Proofing Your Authentication Infrastructure WPAlok TripathiОценок пока нет
- NCSC Cyber Security Risk Management ExecutiveДокумент8 страницNCSC Cyber Security Risk Management ExecutivereliableplacementОценок пока нет
- Privacy and Security Issues in The Age of Big Data - BusinessДокумент13 страницPrivacy and Security Issues in The Age of Big Data - BusinessSarah Jean TrajanoОценок пока нет
- GET PROACTIVE: BUILD A RESILIENT CYBERSECURITY PROGRAMДокумент19 страницGET PROACTIVE: BUILD A RESILIENT CYBERSECURITY PROGRAMVlad Vikernes100% (1)
- InfoSec Analysis and Audit: Security ChallengesДокумент9 страницInfoSec Analysis and Audit: Security ChallengesPIYUSH RAJ GUPTAОценок пока нет
- Leveraging Agile Project Management for Robust Cybersecurity: A Guide for Leaders & ManagersОт EverandLeveraging Agile Project Management for Robust Cybersecurity: A Guide for Leaders & ManagersОценок пока нет
- It SecurityДокумент15 страницIt SecurityamruthaОценок пока нет
- 4 Fallacies INFOSECДокумент2 страницы4 Fallacies INFOSECMac KОценок пока нет
- PM Course Code 10B11PD611Документ29 страницPM Course Code 10B11PD611Mukesh KumarОценок пока нет
- The Role of One Health in Wildlife Conservation: A Challenge and OpportunityДокумент9 страницThe Role of One Health in Wildlife Conservation: A Challenge and OpportunitySrikar KalidossОценок пока нет
- HSE Requirements Contractors High-Risk ProjectsДокумент33 страницыHSE Requirements Contractors High-Risk ProjectsTrần Nam Phong67% (3)
- Root Cause Analysis Fishbone DiagramДокумент3 страницыRoot Cause Analysis Fishbone Diagramhalil ibrahim kizilayОценок пока нет
- GRAINS PRODUCTION NC II TRAINING REGULATIONSДокумент121 страницаGRAINS PRODUCTION NC II TRAINING REGULATIONSphil parkОценок пока нет
- Quality ManualДокумент36 страницQuality ManualDhananjay PatilОценок пока нет
- Here's A Horrifying Picture of What Sleep Loss Will Do To YoДокумент17 страницHere's A Horrifying Picture of What Sleep Loss Will Do To YoAnonymous 01pQbZUMMОценок пока нет
- #36 IG2-forms-electronic-submissionДокумент6 страниц#36 IG2-forms-electronic-submissionHassan Alawami100% (3)
- Vinzons Pilot High School DRRR AssessmentДокумент3 страницыVinzons Pilot High School DRRR AssessmentJaslor LavinaОценок пока нет
- deugro's Petrochemical Industry ExpertiseДокумент11 страницdeugro's Petrochemical Industry Expertiseegy pureОценок пока нет
- Operational Management in Construction CompanyДокумент20 страницOperational Management in Construction CompanyBipin LamaОценок пока нет
- Management of 21st CenturyДокумент8 страницManagement of 21st CenturyKhandaker Sakib Farhad100% (2)
- Case No: 1998 Folio 1588Документ6 страницCase No: 1998 Folio 1588Manoj VarrierОценок пока нет
- Capstone Template 2Документ44 страницыCapstone Template 2Kino RiveraОценок пока нет
- Designing Substantive Procedures: Prepared by DR Phil SajДокумент28 страницDesigning Substantive Procedures: Prepared by DR Phil SajMëŕĕ ĻöľõmãОценок пока нет
- 2nd Session - Chapter 6 - Risk, Return, and The Capital Asset Pricing ModelДокумент51 страница2nd Session - Chapter 6 - Risk, Return, and The Capital Asset Pricing Model'Osvaldo' RioОценок пока нет
- Risk Analysis in Sterilization ServicesДокумент9 страницRisk Analysis in Sterilization ServicesTianti Puadi100% (1)
- Identification of Fire and Explosion Hazards:: Step 1Документ5 страницIdentification of Fire and Explosion Hazards:: Step 1sabriОценок пока нет
- Framing and Decision MakingДокумент6 страницFraming and Decision Makingi KafkalasОценок пока нет
- Risk Appetite & Assurance: Do You Know Your Limits?Документ12 страницRisk Appetite & Assurance: Do You Know Your Limits?Nazmul HasanОценок пока нет
- Project Management Practice QuestionsДокумент29 страницProject Management Practice QuestionsabdahisahОценок пока нет
- Neelam Dissertation Final ProjectДокумент78 страницNeelam Dissertation Final ProjectNeelam SharmaОценок пока нет
- Click or Tap Here To Enter Text. Click or Tap Here To Enter TextДокумент17 страницClick or Tap Here To Enter Text. Click or Tap Here To Enter TextMAEZEL ASHLEY FREDELUCES0% (1)
- Suguna Poultry FarmДокумент11 страницSuguna Poultry Farmananthi RОценок пока нет
- 38 Stock Market Trading PsychologyДокумент14 страниц38 Stock Market Trading PsychologyAani RashОценок пока нет
- TRA Strainer Cleaning 01Документ7 страницTRA Strainer Cleaning 01Ijaz Hussain0% (1)
- Pob SbaДокумент12 страницPob Sbatimothy pahaladОценок пока нет
- Ventana Gold La BodegaДокумент6 страницVentana Gold La BodegaCarlos MarОценок пока нет
- Issai 400 EnglishДокумент18 страницIssai 400 EnglishSceptic GrannyОценок пока нет
- APC-HSE-HSMS-00527 - Lone WorkingДокумент5 страницAPC-HSE-HSMS-00527 - Lone WorkingRajesh gpОценок пока нет