Академический Документы
Профессиональный Документы
Культура Документы
Labs
Загружено:
murtaza5060 оценок0% нашли этот документ полезным (0 голосов)
75 просмотров12 страницlabs
Авторское право
© © All Rights Reserved
Доступные форматы
DOCX, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документlabs
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
75 просмотров12 страницLabs
Загружено:
murtaza506labs
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 12
The Islamia University of Bahawalpur
University College of Engineering & Technology
Computer Networking
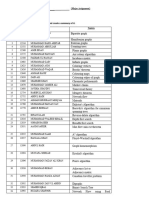
Name:------------------------- Roll No. --------------------------
Lab Instructor Signature: ---------------------- Date: -------------------------
Lab Experiment # 02
The Basic HTTP GET/response interaction:
Lets begin our exploration of HTTP by downloading a very simple HTML file - one that
is very short, and contains no embedded objects. Do the following:
1. Start up your web browser.
2. Start up the Wireshark packet sniffer, as described in the Introductory lab (but
dont yet begin packet capture). Enter http (just the letters, not the quotation
marks) in the display-filter-specification window, so that only captured HTTP
messages will be displayed later in the packet-listing window. (Were only
interested in the HTTP protocol here, and dont want to see the clutter of all
captured packets).
3. Wait a bit more than one minute (well see why shortly), and then begin
Wireshark packet capture.
4. Enter the following to your browser
http://gaia.cs.umass.edu/wireshark-labs/HTTP-wireshark-file1.html
Your browser should display the very simple, one-line HTML file.
5. Stop Wireshark packet capture.
Questions:
1. Is your browser running HTTP version 1.0 or 1.1? What version of HTTP is the
server running?
Ans:
Browser HTTP version is 1.1 and server running HTTP version is 1.0
2. What languages (if any) does your browser indicate that it can accept to the
server?
Ans:
en-US languages can accept the browser.
3. What is the IP address of your computer? Of the gaia.cs.umass.edu server?
Ans:
172.20.5.232 is the IP address of my computer and 239.255.255.250 is the IP address of server
.
4. What is the status code returned from the server to your browser?
Ans:
Status code is 200 returned from server to browser.
5. When was the HTML file that you are retrieving last modified at the server?
Ans:
Tue , 03 dec 2013, 17:42:01 GMT
6. How many bytes of content are being returned to your browser?
Ans:
Content length is 131 bytes.
7. By inspecting the raw data in the packet content window, do you see any headers
within the data that are not displayed in the packet-listing window? If so, name
one.
Ans: No, I dont see any in the HTTP Message below
The HTTP CONDITIONAL GET/response interaction:
Recall from Section 2.2.6 of the text, that most web browsers perform object caching and thus
perform a conditional GET when retrieving an HTTP object. Before performing the
steps below, make sure your browsers cache is empty. (To do this under Firefox, select
Tools->Clear Recent History and check the Cache box, or for Internet Explorer, select
Tools->Internet Options->Delete File; these actions will remove cached files from your
browsers cache.) Now do the following:
1. Start up your web browser, and make sure your browsers cache is cleared, as
discussed above.
2. Start up the Wireshark packet sniffer
3.Enter the following URL into your browser
http://gaia.cs.umass.edu/wireshark-labs/HTTP-wireshark-file2.html
Your browser should display a very simple five-line HTML file.
4.Quickly enter the same URL into your browser again (or simply select the refresh
button on your browser)
5. Stop Wireshark packet capture, and enter http in the display-filter-specification
window, so that only captured HTTP messages will be displayed later in the
packet-listing window.
(Note: If you are unable to run Wireshark on a live network connection, you can
use the http-ethereal-trace-2 packet trace to answer the questions below; see
footnote 1. This trace file was gathered while performing the steps above on one
of the authors computers.)
Answer the following questions:
8. Inspect the contents of the first HTTP GET request from your browser to the
server. Do you see an IF-MODIFIED-SINCE line in the HTTP GET?
Ans:
No I have not seen IF-MODIFIED-SINCE line in HTTP GET.
9. Inspect the contents of the server response. Did the server explicitly return the
contents of the file? How can you tell?
Ans:
Yes, the server explicity return the contents of file
10. Now inspect the contents of the second HTTP GET request from your browser to
the server. Do you see an IF-MODIFIED-SINCE: line in the HTTP GET? If
so, what information follows the IF-MODIFIED-SINCE: header?
Ans:
11. What is the HTTP status code and phrase returned from the server in response to
this second HTTP GET? Did the server explicitly return the contents of the file?
Explain.
Ans:
No, the server not explicity return the contents of the file. Status code and phrase of second
HTTP GET is given in fig.
The Islamia University of Bahawalpur
University College of Engineering & Technology
Computing Network
Name:------------------------- Roll No. --------------------------
Lab Instructor Signature: ---------------------- Date: -------------------
LAB EXPERIMENT NO.03
Retrieving Long Documents
In our examples thus far, the documents retrieved have been simple and short HTML
files. Lets next see what happens when we download a long HTML file. Do the
following:
1. Start up your web browser, and make sure your browsers cache is cleared, as
discussed above.
2. Start up the Wireshark packet sniffer
3. Enter the following URL into your browser
http://gaia.cs.umass.edu/wireshark-labs/HTTP-wireshark-file3.html
Your browser should display the rather lengthy US Bill of Rights.
4. Stop Wireshark packet capture, and enter http in the display-filter-specification
window, so that only captured HTTP messages will be displayed.
(Note: If you are unable to run Wireshark on a live network connection, you can
use the http-ethereal-trace-3 packet trace to answer the questions below; see
footnote 1. This trace file was gathered while performing the steps above on one
of the authors computers.)
In the packet-listing window, you should see your HTTP GET message, followed by a
multiple-packet TCP response to your HTTP GET request. This multiple-packet
response deserves a bit of explanation. Recall from Section 2.2 (see Figure 2.9 in the
text) that the HTTP response message consists of a status line, followed by header lines,
followed by a blank line, followed by the entity body. In the case of our HTTP GET, the
entity body in the response is the entire requested HTML file. In our case here, the
HTML file is rather long, and at 4500 bytes is too large to fit in one TCP packet. The
single HTTP response message is thus broken into several pieces by TCP, with each
piece being contained within a separate TCP segment (see Figure 1.24 in the text). In
recent versions of Wireshark, Wireshark indicates each TCP segment as a separate
packet, and the fact that the single HTTP response was fragmented across multiple TCP
packets is indicated by the TCP segment of a reassembled PDU in the Info column of
the Wireshark display. Earlier versions of Wireshark used the Continuation phrase to
indicated that the entire content of an HTTP message was broken across multiple TCP
segments.. We stress here that there is no Continuation message in HTTP!
Answer the following questions:
12. How many HTTP GET request messages did your browser send? Which packet
number in the trace contains the GET message for the Bill or Rights?
Ans:
One HTTP GET request massege send the browser. And packet number is 72 in trace.
13. Which packet number in the trace contains the status code and phrase associated
with the response to the HTTP GET request?
Ans:
Packet number in the trace contains the status code phrase with the response to the HTTP GET
request is 91.
14. What is the status code and phrase in the response?
Ans:
Status code is 200 and phrase is ok in the response.
15. How many data-containing TCP segments were needed to carry the single HTTP
response and the text of the Bill of Rights?
Ans:
4 data-containing TCP segments were needed to carry the single HTTP response.
HTML Documents with Embedded Objects
Now that weve seen how Wireshark displays the captured packet traffic for large HTML
files, we can look at what happens when your browser downloads a file with embedded
objects, i.e., a file that includes other objects (in the example below, image files) that are
stored on another server(s).
Do the following:
1. Start up your web browser, and make sure your browsers cache is cleared, as
discussed above.
2. Start up the Wireshark packet sniffer
3. Enter the following URL into your browser
http://gaia.cs.umass.edu/wireshark-labs/HTTP-wireshark-file4.html
Your browser should display a short HTML file with two images. These two
images are referenced in the base HTML file. That is, the images themselves are
not contained in the HTML; instead the URLs for the images are contained in the
downloaded HTML file. As discussed in the textbook, your browser will have to
retrieve these logos from the indicated web sites. Our publishers logo is
retrieved from the www.aw-bc.com web site. The image of the cover for our 5th
edition (one of our favorite covers) is stored at the manic.cs.umass.edu server.
4. Stop Wireshark packet capture, and enter http in the display-filter-specification
window, so that only captured HTTP messages will be displayed.
(Note: If you are unable to run Wireshark on a live network connection, you can
use the http-ethereal-trace-4 packet trace to answer the questions below; see
footnote 1. This trace file was gathered while performing the steps above on one
of the authors computers.)
Answer the following questions:
16. How many HTTP GET request messages did your browser send? To which
Internet addresses were these GET requests sent?
Ans:
Browser send three HTTP GET requests messages. And internet addresses(IP) are
128.119.245.12 and 165.193.140.14 and 128.119.240.90 respectively.
17. Can you tell whether your browser downloaded the two images serially, or
whether they were downloaded from the two web sites in parallel? Explain.
Ans:
Browser downloaded two images in parallel TCP conections because the destination addresses
are not same.
HTTP Authentication:
Finally, lets try visiting a web site that is password-protected and examine the sequence
of HTTP message exchanged for such a site. The URL
http://gaia.cs.umass.edu/wireshark-labs/protected_pages/HTTP-wireshark-file5.html is
password protected. The username is wireshark-students (without the quotes), and the
password is network (again, without the quotes). So lets access this secure
password-protected site. Do the following:
1. Make sure your browsers cache is cleared, as discussed above, and close down
your browser. Then, start up your browser
2. Start up the Wireshark packet sniffer
3. Enter the following URL into your browser
http://gaia.cs.umass.edu/wireshark-labs/protected_pages/HTTP-wiresharkfile5.
html
Type the requested user name and password into the pop up box.
4. Stop Wireshark packet capture, and enter http in the display-filter-specification
window, so that only captured HTTP messages will be displayed later in the
packet-listing window.
(Note: If you are unable to run Wireshark on a live network connection, you can
use the http-ethereal-trace-5 packet trace to answer the questions below; see
footnote 2. This trace file was gathered while performing the steps above on one
of the authors computers.)
Now lets examine the Wireshark output. You might want to first read up on HTTP
authentication by reviewing the easy-to-read material on HTTP Access Authentication
Framework at http://frontier.userland.com/stories/storyReader$2159
Answer the following questions:
18. What is the servers response (status code and phrase) in response to the initial
HTTP GET message from your browser?
Ans:
19. When your browsers sends the HTTP GET message for the second time, what
new field is included in the HTTP GET message?
Ans:
Вам также может понравиться
- TQ Log BookДокумент1 страницаTQ Log Bookmurtaza506Оценок пока нет
- Saep 127Документ9 страницSaep 127murtaza506Оценок пока нет
- Algebric Formulas PDFДокумент5 страницAlgebric Formulas PDFmurtaza506Оценок пока нет
- Coating by Mechanical AlloyingДокумент5 страницCoating by Mechanical Alloyingmurtaza506Оценок пока нет
- Monthly QC ReportДокумент4 страницыMonthly QC Reportmurtaza506Оценок пока нет
- Request For Inspection: Engineering & Project Management Site Projects DepartmentДокумент2 страницыRequest For Inspection: Engineering & Project Management Site Projects Departmentmurtaza506Оценок пока нет
- Questions in InterviewДокумент1 страницаQuestions in Interviewmurtaza506Оценок пока нет
- PQI FormatДокумент6 страницPQI Formatmurtaza506100% (2)
- Pqi Trend ChartДокумент4 страницыPqi Trend Chartmurtaza506Оценок пока нет
- 123Документ2 страницы123murtaza506Оценок пока нет
- RFI Log SheetДокумент2 страницыRFI Log Sheetmurtaza506Оценок пока нет
- Hardfacing GuideДокумент52 страницыHardfacing GuideGm Murtaza100% (2)
- Dns LabsДокумент15 страницDns Labsmurtaza506Оценок пока нет
- NitridingДокумент6 страницNitridingmurtaza506Оценок пока нет
- Thermal SprayingДокумент91 страницаThermal Spraying12345marian100% (1)
- HW1 SolutionДокумент5 страницHW1 Solutionmurtaza506Оценок пока нет
- ItpДокумент3 страницыItpmurtaza506Оценок пока нет
- F (A) - WPS FormДокумент2 страницыF (A) - WPS FormSuhaina SulimanОценок пока нет
- AWI Heat Input CalculatorДокумент2 страницыAWI Heat Input CalculatorMohammad ElhedabyОценок пока нет
- Welders Hand BookДокумент23 страницыWelders Hand Booksamyqatar100% (2)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (120)
- Hibernate-Generic-Dao: GenericdaoexamplesДокумент1 страницаHibernate-Generic-Dao: GenericdaoexamplesorangotaОценок пока нет
- NBA AwarenessДокумент39 страницNBA AwarenessRaja SekarОценок пока нет
- Appendix F Sample Erosion and Sediment Control PlanДокумент11 страницAppendix F Sample Erosion and Sediment Control Planjhj01Оценок пока нет
- GPS Equipment CalibrationДокумент10 страницGPS Equipment CalibrationAishah Drahman100% (1)
- Power Meditation: by Mahaswami MedhiranandaДокумент7 страницPower Meditation: by Mahaswami Medhiranandaanhadbalbir7347Оценок пока нет
- 12.22.08 Dr. King Quotes BookletДокумент16 страниц12.22.08 Dr. King Quotes BookletlamchunyienОценок пока нет
- Neil Bryan N. Moninio: Professional GoalДокумент3 страницыNeil Bryan N. Moninio: Professional GoalNeil Bryan N. MoninioОценок пока нет
- 2 Gentlemen of VeronaДокумент12 страниц2 Gentlemen of VeronaAaravОценок пока нет
- Mcob OcДокумент19 страницMcob OcashisОценок пока нет
- Reflection and Refraction of LightДокумент34 страницыReflection and Refraction of Lightseunnuga93Оценок пока нет
- Forensic Dental TechniquesДокумент3 страницыForensic Dental Techniqueschrisr310Оценок пока нет
- Function, Roles, and Skills of A Manager: Lesson 3Документ12 страницFunction, Roles, and Skills of A Manager: Lesson 3Christine Joy ResponteОценок пока нет
- DistillationДокумент8 страницDistillationsahil khandelwalОценок пока нет
- 4as Lesson PlanДокумент3 страницы4as Lesson PlanLenette Alagon100% (3)
- Els2204 Sinsis 1718 CepДокумент7 страницEls2204 Sinsis 1718 CepChristian MarpaungОценок пока нет
- Data MiningДокумент14 страницData MiningRavi VermaОценок пока нет
- Oil SeparatorДокумент7 страницOil Separatorbookslover1Оценок пока нет
- Fast Ai PDFДокумент11 страницFast Ai PDFfolioxОценок пока нет
- Baird, A. Experimental and Numerical Study of U-Shape Flexural Plate.Документ9 страницBaird, A. Experimental and Numerical Study of U-Shape Flexural Plate.Susana Quevedo ReyОценок пока нет
- Decision Making Techniques: How To Make Good DecisionsДокумент10 страницDecision Making Techniques: How To Make Good DecisionsParanthaman RamanОценок пока нет
- 11 Technical Analysis & Dow TheoryДокумент9 страниц11 Technical Analysis & Dow TheoryGulzar AhmedОценок пока нет
- Smart Meter For The IoT PDFДокумент6 страницSmart Meter For The IoT PDFNaga Santhoshi SrimanthulaОценок пока нет
- EI in NegotiationsДокумент22 страницыEI in NegotiationspranajiОценок пока нет
- Spectrofotometru SpectroDirect (De La Lovibond)Документ360 страницSpectrofotometru SpectroDirect (De La Lovibond)FlaviusОценок пока нет
- Graph Theory (B)Документ2 страницыGraph Theory (B)Waqar RoyОценок пока нет
- The Scientific Method Is An Organized Way of Figuring Something OutДокумент1 страницаThe Scientific Method Is An Organized Way of Figuring Something OutRick A Middleton JrОценок пока нет
- Understanding Culture, Society, and Politics Quarter 2 - Module 1Документ21 страницаUnderstanding Culture, Society, and Politics Quarter 2 - Module 1Allaine's ChannelОценок пока нет
- PsiRun SheetsДокумент3 страницыPsiRun SheetsalemauОценок пока нет
- Q2 Week7g56Документ4 страницыQ2 Week7g56Judy Anne NepomucenoОценок пока нет
- Genogram and Eco GramДокумент5 страницGenogram and Eco GramGitichekimОценок пока нет