Академический Документы
Профессиональный Документы
Культура Документы
5.config Passw and Privileges
Загружено:
SteggosИсходное описание:
Оригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
5.config Passw and Privileges
Загружено:
SteggosАвторское право:
Доступные форматы
Configuring Passwords and Privileges
Using passwords and assigning privilege levels is a simple way of providing terminal access control
in your network.
This chapter describes the following topics and tasks:
• Protect Access to Privilege EXEC Commands
• Encrypt Passwords
• Configure Multiple Privilege Levels
• Recover a Lost Enable Password
• Recover a Lost Line Password
• Configure Identification Support
For a complete description of the commands used in this chapter, refer to the “Password and
Privileges Commands” chapter in the Security Command Reference. To locate documentation of
other commands that appear in this chapter, use the command reference master index or search
online. For configuration examples using the commands in this chapter, refer to the “Passwords and
Privileges Configuration Examples” section located at the end of the this chapter.
Protect Access to Privilege EXEC Commands
The following tasks provide a way to control access to the system configuration file and privilege
EXEC (enable) commands:
• Set or Change a Static Enable Password
• Protect Passwords with Enable Password and Enable Secret
• Set or Change a Line Password
• Set TACACS Password Protection for Privilege EXEC Mode
Set or Change a Static Enable Password
To set or change a static password that controls access to privileged EXEC (enable) mode, perform
the following task in global configuration mode:
Task Command
Establish a new password or change an existing enable password password
password for the privileged command level.
Configuring Passwords and Privileges SC-213
Protect Access to Privilege EXEC Commands
For examples of how to define enable passwords for different privilege levels, see the “Multiple
Levels of Privileges Examples” section at the end of this chapter.
Protect Passwords with Enable Password and Enable Secret
To provide an additional layer of security, particularly for passwords that cross the network or are
stored on a TFTP server, you can use either the enable password or enable secret commands. Both
commands accomplish the same thing; that is, they allow you to establish an encrypted password
that users must enter to access enable mode (the default), or any privilege level you specify.
We recommend that you use the enable secret command because it uses an improved encryption
algorithm. Use the enable password command only if you boot an older image of the Cisco IOS
software, or if you boot older boot ROMs that do not recognize the enable secret command.
If you configure the enable secret command, it takes precedence over the enable password
command; the two commands cannot be in effect simultaneously.
To configure the router to require an enable password, perform one of the following tasks in global
configuration mode:
Task Command
Establish a password for a privilege command enable password [level level] {password |
mode. encryption-type encrypted-password}
Specify a secret password, saved using a enable secret [level level] {password |
non-reversible encryption method. (When enable encryption-type encrypted-password}
password and enable secret are both set, users must
enter the enable secret password.)
Use either of these commands with the level option to define a password for a specific privilege level.
After you specify the level and set a password, give the password only to users who need to have
access at this level. Use the privilege level configuration command to specify commands accessible
at various levels.
If you have the service password-encryption command enabled, the password you enter is
encrypted. When you display it with the show running-config command, it is displayed in
encrypted form.
If you specify an encryption type, you must provide an encrypted password—an encrypted password
you copy from another router configuration.
Note You cannot recover a lost encrypted password. You must clear NVRAM and set a new
password. See the sections “Recover a Lost Enable Password” or “Recover a Lost Line Password”
in this chapter if you have lost or forgotten your password.
Set or Change a Line Password
To set or change a password on a line, perform the following task in global configuration mode:
Task Command
Establish a new password or change an existing password password
password for the privileged command level.
SC-214 Security Configuration Guide
Encrypt Passwords
Set TACACS Password Protection for Privilege EXEC Mode
You can set the TACACS protocol to determine whether a user can access privileged EXEC (enable)
mode. To do so, perform the following task in global configuration mode:
Task Command
Set the TACACS-style user ID and enable use-tacacs
password-checking mechanism at the privileged
EXEC level.
When you set TACACS password protection at the privilege EXEC mode, the enable EXEC
command prompts for both a new username and a password. This information is then passed to the
TACACS server for authentication. If you are using the extended TACACS, it also passes any
existing UNIX user identification code to the TACACS server.
Caution If you use the enable use-tacacs command, you must also specify tacacs-server
authenticate enable, or you will be locked out of the privilege EXEC (enable) mode.
Note When used without extended TACACS, the enable use-tacacs command allows anyone with
a valid username and password to access the privileged EXEC mode, creating a potential security
problem. This occurs because the TACACS query resulting from entering the enable command is
indistinguishable from an attempt to log in without extended TACACS.
Encrypt Passwords
Because protocol analyzers can examine packets (and read passwords), you can increase access
security by configuring the Cisco IOS software to encrypt passwords. Encryption prevents the
password from being readable in the configuration file.
Configure the Cisco IOS software to encrypt passwords by performing the following task in global
configuration mode:
Task Command
Encrypt a password. service password-encryption
The actual encryption process occurs when the current configuration is written or when a password
is configured. Password encryption is applied to all passwords, including authentication key
passwords, the privileged command password, console and virtual terminal line access passwords,
and BGP neighbor passwords. The service password-encryption command is primarily useful for
keeping unauthorized individuals from viewing your password in your configuration file.
Caution The service password-encryption command does not provide a high level of network
security. If you use this command, you should also take additional network security measures.
Although you cannot recover a lost encrypted password (that is, you cannot get the original password
back), you can recover from a lost encrypted password. See the sections “Recover a Lost Enable
Password” or “Recover a Lost Line Password” in this chapter if you have lost or forgotten your
password.
Configuring Passwords and Privileges SC-215
Configure Multiple Privilege Levels
Configure Multiple Privilege Levels
By default, the Cisco IOS software has two modes of password security: user mode (EXEC) and
privilege mode (enable). You can configure up to 16 hierarchical levels of commands for each mode.
By configuring multiple passwords, you can allow different sets of users to have access to specified
commands.
For example, if you want the configure command to be available to a more restricted set of users
than the clear line command, you can assign level 2 security to the clear line command and
distribute the level 2 password fairly widely, and assign level 3 security to the configure command
and distribute the password to level 3 commands to fewer users.
The following tasks describe how to configure additional levels of security:
• Set the Privilege Level for a Command
• Change the Default Privilege Level for Lines
• Display Current Privilege Levels
• Log In to a Privilege Level
Set the Privilege Level for a Command
To set the privilege level for a command, perform the following tasks in global configuration mode:
Task Command
Set the privilege level for a command. privilege mode level level command
Specify the enable password for a privilege level. enable password level level [encryption-type]
password
Change the Default Privilege Level for Lines
To change the default privilege level for a given line or a group of lines, perform the following task
in line configuration mode:
Task Command
Specify a default privilege level for a line. privilege level level
Display Current Privilege Levels
To display the current privilege level you can access based on the password you used, perform the
following task in EXEC mode:
Task Command
Display your current privilege level. show privilege
Log In to a Privilege Level
To log in to a router at a specified privilege level, perform the following task in EXEC mode:
Task Command
Log in to a specified privilege level. enable level
SC-216 Security Configuration Guide
Recover a Lost Enable Password
To exit to a specified privilege level, perform the following task in EXEC mode:
Task Command
Exit to a specified privilege level. disable level
Recover a Lost Enable Password
You can restore access to enable mode on a router when the password is lost using one of the three
procedures described in this section. The procedure you use depends on your router platform.
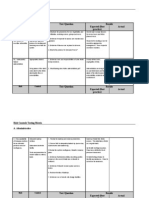
Table 15 shows which password recovery procedure to use with each router platform.
You can perform password recovery on most of the platforms without changing hardware jumpers,
but all platforms require the configuration to be reloaded. Password recovery can be done only from
the console port on the router.
Table 15 Platform-Specific Password Recovery Procedures
Password Recovery Procedure Router Platform
Password Recovery Procedure 1 Cisco 2000 series
Cisco 2500 series
Cisco 3000 series
Cisco 4000 series with 680x0 Motorola CPU
Cisco 7000 series running Cisco IOS Release 10.0 or later in
ROMs installed on the RP card
IGS series running Cisco Release IOS 9.1 or later in ROMs
Password Recovery Procedure 2 Cisco 1003
Cisco 1600 series
Cisco 3600 series
Cisco 4500 series
Cisco 7200 series
Cisco 7500 series
IDT Orion-based routers
AS5200 and AS5300 platforms
Password Recovery Process
Both password recovery procedures involve the following basic steps:
Step 1 Configure the router to boot up without reading the configuration memory (NVRAM).
This is sometimes called the test system mode.
Step 2 Reboot the system.
Step 3 Access enable mode (which can be done without a password if you are in test system
mode).
Step 4 View or change the password, or erase the configuration.
Step 5 Reconfigure the router to boot up and read the NVRAM as it normally does.
Step 6 Reboot the system.
Configuring Passwords and Privileges SC-217
Recover a Lost Enable Password
Note Some password recovery requires that a terminal issue a Break signal; you must be familiar
with how your terminal or PC terminal emulator issues this signal. For example, in ProComm, the
keys Alt-B by default generates the Break signal, and in a Windows terminal you press Break or
CTRL-Break. A Windows terminal also allows you to define a function key as a BREAK signal. To
do so, select function keys from the Terminal window and define one as Break by entering the
characters ^$B (Shift 6, Shift 4, and uppercase B).
Password Recovery Procedure 1
Use this procedure to recover lost passwords on the following Cisco routers:
• Cisco 2000 series
• Cisco 2500 series
• Cisco 3000 series
• Cisco 4000 series with 680x0 Motorola CPU
• Cisco 7000 series running Cisco IOS Release 10.0 or later in ROMs installed on the RP card.
The router can be booting Cisco IOS Release 10.0 software in Flash memory, but it needs the
actual ROMs on the processor card too.
• IGS Series running Cisco IOS Release 9.1 or later in ROMs
To recover a password using Procedure 1, perform the following steps:
Step 1 Attach a terminal or PC with terminal emulation software to the console port of the router.
Step 2 Enter the show version command and record the setting of the configuration register. It
is usually 0x2102 or 0x102.
The configuration register value is on the last line of the display. Note whether the
configuration register is set to enable Break or disable Break.
The factory-default configuration register value is 0x2102. Notice that the third digit from
the left in this value is 1, which disables Break. If the third digit is not 1, Break is enabled.
Step 3 Turn off the router, then turn it on.
Step 4 Press the Break key on the terminal within 60 seconds of turning on the router.
The rommon> prompt with no router name appears. If it does not appear, the terminal is
not sending the correct Break signal. In that case, check the terminal or terminal
emulation setup.
Step 5 Enter o/r0x42 at the rommon> prompt to boot from Flash memory or o/r0x41 to boot
from the boot ROMs.
Note that the first character is the letter o, not the numeral zero. If you have Flash memory
and it is intact, 0x42 is the best setting. Use 0x41 only if the Flash memory is erased or
not installed. If you use 0x41, you can only view or erase the configuration. You cannot
change the password.
Step 6 At the rommon> prompt, enter the initialize command to initialize the router.
This causes the router to reboot but ignore its saved configuration and use the image in
Flash memory instead.
The system configuration display appears.
SC-218 Security Configuration Guide
Recover a Lost Enable Password
Step 7 Enter no in response to the System Configuration Dialog prompts until the following
message appears:
Press RETURN to get started!
Step 8 Press Return.
The Router> prompt appears.
Step 9 Enter the enable command.
The Router# prompt appears.
Step 10 Choose one of the following options:
• To view the password, if it is not encrypted, enter the more nvram:startup-config
command.
• To change the password (if it is encrypted, for example), enter the following
commands:
Router # configure memory
Router # configure terminal
Router(config)# enable secret 1234abcd
Router(config)# ctrl-z
Router # write memory
Note The enable secret command provides increased security by storing the enable secret
password using a non-reversible cryptographic function; however, you cannot recover a lost
password that has been encrypted.
Step 11 Enter the configure terminal command at the EXEC prompt to enter configuration
mode.
Step 12 Enter the config-register command and whatever value you recorded in step 2.
Step 13 Press Ctrl-Z to quit from the configuration editor.
Step 14 Enter the reload command at the privileged EXEC prompt and issue the write memory
command to save the configuration.
Password Recovery Procedure 2
Use this procedure to recover lost passwords on the following Cisco routers:
• Cisco 1003
• Cisco 1600 series
• Cisco 3600 series
• Cisco 4500 series
• Cisco 7200 series
• Cisco 7500 series
• IDT Orion-Based Routers
• AS5200 and AS5300 platforms
Configuring Passwords and Privileges SC-219
Recover a Lost Enable Password
To recover a password using Procedure 2, perform the following steps:
Step 1 Attach a terminal or PC with terminal emulation software to the console port of the router.
Step 2 Enter the show version command and record the setting of the configuration register. It
is usually 0x2102 or 0x102.
The configuration register value is on the last line of the display. Note whether the
configuration register is set to enable Break or disable Break.
The factory-default configuration register value is 0x2102. Notice that the third digit from
the left in this value is 1, which disables Break. If the third digit is not 1, Break is enabled.
Step 3 Turn off the router, then turn it on.
Step 4 Press the Break key on the terminal within 60 seconds of turning on the router.
The rommon> prompt appears. If it doesn’t appear, the terminal is not sending the correct
Break signal. In that case, check the terminal or terminal emulation setup.
Step 5 Enter the confreg command at the rommon> prompt.
The following prompt appears:
Do you wish to change configuration[y/n]?
Step 6 Enter yes and press Return.
Step 7 Enter no to subsequent questions until the following prompt appears:
ignore system config info[y/n]?
Step 8 Enter yes.
Step 9 Enter no to subsequent questions until the following prompt appears:
change boot characteristics[y/n]?
Step 10 Enter yes.
The following prompt appears:
enter to boot:
Step 11 At this prompt, either enter 2 and press Return if Flash memory or, if Flash memory is
erased, enter 1. If Flash memory is erased, the Cisco 4500 must be returned to Cisco for
service. If you enter 1, you can only view or erase the configuration. You cannot change
the password.
A configuration summary is displayed and the following prompt appears:
Do you wish to change configuration[y/n]?
Step 12 Answer no and press Return.
The following prompt appears:
rommon>
Step 13 Enter the reload command at the privileged EXEC prompt or, for Cisco 4500 series and
Cisco 7500 series routers, power cycle the router.
Step 14 As the router boots, enter no to all the setup questions until the following prompt appears:
Router>
SC-220 Security Configuration Guide
Recover a Lost Line Password
Step 15 Enter the enable command to enter enable mode.
The Router# prompt appears.
Step 16 Choose one of the following options:
• To view the password, if it is not encrypted, enter the more nvram:startup-config
command.
• To change the password (if it is encrypted, for example), enter the following
commands:
Router # configure memory
Router # configure terminal
Router(config)# enable secret 1234abcd
Router(config)# ctrl-z
Router # write memory
Note The enable secret command provides increased security by storing the enable secret
password using a non-reversible cryptographic function; however, you cannot recover a lost
password that has been encrypted.
Step 17 Enter the configure terminal command at the prompt.
Step 18 Enter the config-register command and whatever value you recorded in step 2.
Step 19 Press Ctrl-Z to quit from the configuration editor.
Step 20 Enter the reload command at the prompt and issue the write memory command to save
the configuration.
Recover a Lost Line Password
If your router has the nonvolatile memory option, you can accidentally lock yourself out of enable
mode if you enable password checking on the console terminal line and then forget the line
password. To recover a lost line password, perform the following steps:
Step 1 Force the router into factory diagnostic mode.
See the hardware installation and maintenance publication for your product for specific
information about setting the processor configuration register to factory diagnostic mode.
Table 16 summarizes the hardware or software settings required by various products to
set factory diagnostic mode.
Step 2 Enter Yes when asked if you want to set the manufacturers’ addresses.
The following prompt appears:
TEST-SYSTEM >
Step 3 Issue the enable command to enter enable mode:
TEST-SYSTEM > enable
Step 4 Enter the show startup-config command to review the system configuration and find the
password. Do not change anything in the factory diagnostic mode.
TEST-SYSTEM # show startup-config
Step 5 To resume normal operation, restart the router or reset the configuration register.
Configuring Passwords and Privileges SC-221
Configure Identification Support
Step 6 Log in to the router with the password that was shown in the configuration file.
Note All debugging capabilities are turned on during diagnostic mode.
See the hardware installation and maintenance publication for your product for specific information
about configuring the processor configuration register for factory diagnostic mode. Table 16
summarizes the hardware or software settings required by the various products to set factory
diagnostic mode.
Table 16 Factory Diagnostic Mode Settings for the Configuration Register
Platform Setting
Modular products Set jumper in bit 15 of the processor configuration register, then
restart; remove the jumper when finished.
Cisco AS5100 Use the config-register command to set the processor
Cisco AS5200 configuration register to 0x8000, then initialize and boot the
system. Use the reload command to restart and set the processor
Cisco AS5300 configuration register to 0x2102 when finished.
Cisco 1600 series
Cisco 2500 series
Cisco 3000 series
Cisco 3600 series
Cisco 4000 series
Cisco 4500 series
Cisco 7000 series
Cisco 7200 series
Cisco 7500 series
Configure Identification Support
Identification support allows you to query a Transmission Control Protocol (TCP) port for
identification. This feature enables an unsecure protocol, described in RFC 1413, to report the
identity of a client initiating a TCP connection and a host responding to the connection. With
identification support, you can connect a TCP port on a host, issue a simple text string to request
information, and receive a simple text-string reply.
To configure identification support, perform the following task in global configuration mode:
Task Command
Enable identification support. ip identd
SC-222 Security Configuration Guide
Passwords and Privileges Configuration Examples
Passwords and Privileges Configuration Examples
This section describes multiple privilege level and username authentication examples and contains
the following sections:
• Multiple Levels of Privileges Examples
• Username Examples
Multiple Levels of Privileges Examples
This section provides examples of using multiple privilege levels to specify who can access different
sets of commands.
Allow Users to Clear Lines Examples
If you want to allow users to clear lines, you can do either of the following:
• Change the privilege level for the clear and clear line commands to 1 or “ordinary user level,”
as follows. This allows any user to clear lines.
privilege exec level 1 clear line
• Change the privilege level for the clear and clear line commands to level 2. To do so, use the
privilege level global configuration command to specify privilege level 2. Then define an enable
password for privilege level 2 and tell only those users who need to know what the password is.
enable password level 2 pswd2
privilege exec level 2 clear line
Define an Enable Password for System Operators Examples
In the following example, you define an enable password for privilege level 10 for system operators
and make clear and debug commands available to anyone with that privilege level enabled.
enable password level 10 pswd10
privilege exec level 10 clear line
privilege exec level 10 debug ppp chap
privilege exec level 10 debug ppp error
privilege exec level 10 debug ppp negotiation
The following example lowers the privilege level of the show running-config command and most
configuration commands to operator level so that the configuration can be viewed by an operator. It
leaves the privilege level of the configure command at 15. Individual configuration commands are
displayed in the show running-config output only if the privilege level for a command has been
lowered to 10. Users are allowed to see only those commands that have a privilege level less than or
equal to their current privilege level.
enable password level 15 pswd15
privilege exec level 15 configure
enable password level 10 pswd10
privilege exec level 10 show running-config
Configuring Passwords and Privileges SC-223
Passwords and Privileges Configuration Examples
Disable a Privilege Level Example
In the following example, the show ip route command is set to privilege level 15. To keep all
show ip and show commands from also being set to privilege level 15, these commands are specified
to be privilege level 1.
privilege exec level 15 show ip route
privilege exec level 1 show ip
privilege exec level 1 show
Username Examples
The following sample configuration sets up secret passwords on Routers A, B, and C, to enable the
three routers to connect to each other.
To authenticate connections between Routers A and B, enter the following commands:
On Router A:
username B password a-b_secret
On Router B:
username A password a-b_secret
To authenticate connections between Routers A and C, enter the following commands:
On Router A:
username C password a-c_secret
On Router C:
username A password a-c_secret
To authenticate connections between Routers B and C, enter the following commands:
On Router B:
username C password b-c_secret
On Router C:
username B password b-c_secret
For example, suppose you enter the following command:
username bill password westward
The system displays this command as follows:
username bill password 7 21398211
The encrypted version of the password is 21398211. The password was encrypted by the
Cisco-defined encryption algorithm, as indicated by the “7.”
However, if you enter the following command, the system determines that the password is already
encrypted and performs no encryption. Instead, it displays the command exactly as you entered it:
username bill password 7 21398211
username bill password 7 21398211
SC-224 Security Configuration Guide
Вам также может понравиться
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- 6th Central Pay Commission Salary CalculatorДокумент15 страниц6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (894)
- Stew Smith Lean Down Meal Options PDFДокумент20 страницStew Smith Lean Down Meal Options PDFCorey Mays67% (3)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- How To Hack Facebook Password - Learn How To Hack - Ethical Hacking and SecuДокумент22 страницыHow To Hack Facebook Password - Learn How To Hack - Ethical Hacking and SecuDedy Sugiyanto60% (10)
- Half Marathon Training ProgramДокумент10 страницHalf Marathon Training ProgramSteggos100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Risk Controls Testing Matrix A. AdministrativeДокумент9 страницRisk Controls Testing Matrix A. AdministrativesilkycОценок пока нет
- 2 Gear LinkageGolf Mk1Документ46 страниц2 Gear LinkageGolf Mk1SteggosОценок пока нет
- Information Communication Technology (ICT) Infrastructure Specifications Manual (Local Area Networks and Data Cabling)Документ92 страницыInformation Communication Technology (ICT) Infrastructure Specifications Manual (Local Area Networks and Data Cabling)SteggosОценок пока нет
- RS232 Cable PinoutsДокумент5 страницRS232 Cable PinoutsSteggos100% (2)
- Cybrsecurity: EC-507 Internship ReportДокумент27 страницCybrsecurity: EC-507 Internship ReportRaj ShuklaОценок пока нет
- Model - Airplane.international - Issue.91 February.2013Документ84 страницыModel - Airplane.international - Issue.91 February.2013Steggos100% (4)
- Metasploit Pro v4.11Документ188 страницMetasploit Pro v4.11PatriziaОценок пока нет
- Network Address TranslationДокумент13 страницNetwork Address TranslationRoberd LeeОценок пока нет
- Local Quality of Service ConfigurationДокумент14 страницLocal Quality of Service ConfigurationSteggosОценок пока нет
- T25 BetaДокумент1 страницаT25 BetaSteggosОценок пока нет
- T25 Gamma HybridДокумент1 страницаT25 Gamma HybridPoly SgОценок пока нет
- Cisco IP Telephony Flash CardsДокумент48 страницCisco IP Telephony Flash CardsSteggosОценок пока нет
- T25 Alpha PDFДокумент1 страницаT25 Alpha PDFDavid Berisso100% (1)
- Basic Network ConfigurationДокумент13 страницBasic Network ConfigurationRoberd LeeОценок пока нет
- VLan ConfigurationДокумент15 страницVLan ConfigurationSteggosОценок пока нет
- 1a T25-Gamma PDFДокумент1 страница1a T25-Gamma PDFYesu Zea RОценок пока нет
- Mega 100WR MANUAL AZTME1 PDFДокумент55 страницMega 100WR MANUAL AZTME1 PDFSteggosОценок пока нет
- To Be Done 1-2 Times Per Day!Документ1 страницаTo Be Done 1-2 Times Per Day!SteggosОценок пока нет
- 3COM 4400 Management Interface Reference GuideДокумент151 страница3COM 4400 Management Interface Reference GuideСергей ЛобакевичОценок пока нет
- Bwidth ConsumeДокумент8 страницBwidth Consumemichael_mccabe_18Оценок пока нет
- Procurve and Siemens PhoneДокумент12 страницProcurve and Siemens PhoneSteggosОценок пока нет
- Ddavis QoS WorksheetДокумент5 страницDdavis QoS WorksheetSteggosОценок пока нет
- SSHДокумент11 страницSSHSteggosОценок пока нет
- 862-02701 HDR5 System Manual Issue 4Документ182 страницы862-02701 HDR5 System Manual Issue 4SteggosОценок пока нет
- Internet FirewallsДокумент8 страницInternet FirewallsSteggosОценок пока нет
- Police Vs ShapeДокумент8 страницPolice Vs ShapeSteggosОценок пока нет
- Metrorail Western Cape Train Schedule 2006Документ13 страницMetrorail Western Cape Train Schedule 2006SteggosОценок пока нет
- Checklist For Deploying An IDS: 2.1 Determining Policy, Junction of MaintenanceДокумент3 страницыChecklist For Deploying An IDS: 2.1 Determining Policy, Junction of MaintenanceSteggosОценок пока нет
- Cisco Interface CardsДокумент24 страницыCisco Interface CardsSteggosОценок пока нет
- Understanding FoodДокумент6 страницUnderstanding FoodSteggosОценок пока нет
- Operating System Security OverviewДокумент14 страницOperating System Security OverviewDesalegn Asefa100% (3)
- EMail Security Protocols ComparedДокумент20 страницEMail Security Protocols ComparedAayatKhanОценок пока нет
- Managing Firewall AAA RulesДокумент26 страницManaging Firewall AAA RulesJaved IqbalОценок пока нет
- Password Cracking Detection System With Honeyword: Florita Sylvester TuscanoДокумент4 страницыPassword Cracking Detection System With Honeyword: Florita Sylvester TuscanoEditor IJRITCCОценок пока нет
- FortipamДокумент6 страницFortipamDebarros MartinsОценок пока нет
- Attack and Defense in Wireless Networks: Presented by Aleksandr DoroninДокумент14 страницAttack and Defense in Wireless Networks: Presented by Aleksandr DoroninjrgtonyОценок пока нет
- Porta Cipher: CiphersДокумент1 страницаPorta Cipher: CiphersMarcos MarcosОценок пока нет
- Cisco Adaptive Wireless Intrusion Prevention System: Protecting Information in MotionДокумент8 страницCisco Adaptive Wireless Intrusion Prevention System: Protecting Information in Motionpopcorns1986Оценок пока нет
- Itron Security Manager (ISM) : Keep Your Data SafeДокумент4 страницыItron Security Manager (ISM) : Keep Your Data Safeagus wiyonoОценок пока нет
- s53fds65f DSFDSFDSFДокумент17 страницs53fds65f DSFDSFDSFBi MiloОценок пока нет
- Mapping Course Content To CompTIA CySA+ (Exam CS0-002)Документ15 страницMapping Course Content To CompTIA CySA+ (Exam CS0-002)GF TeamОценок пока нет
- Proxying Eduroam With freeRADIUSДокумент37 страницProxying Eduroam With freeRADIUSakun1994Оценок пока нет
- Solution Guide - InsightIDR Detection MethodologiesДокумент12 страницSolution Guide - InsightIDR Detection MethodologiesdviktorОценок пока нет
- Plagiarism Checker X Originality Report: Similarity Found: 18%Документ5 страницPlagiarism Checker X Originality Report: Similarity Found: 18%Saket Sukhwant SinghОценок пока нет
- Module 01: Foundations of Security: UnderstandДокумент64 страницыModule 01: Foundations of Security: UnderstandRian AfiliandiОценок пока нет
- TU170-Session 1Документ24 страницыTU170-Session 1Professor HОценок пока нет
- Cyber Safety: by Lakshay Aggarwal Class 10-B Maxfort SchoolДокумент10 страницCyber Safety: by Lakshay Aggarwal Class 10-B Maxfort Schoolᒺᗩᖇᖆᖻ ᘜᗋᖇᘜОценок пока нет
- Cicada 3301: DescriptionДокумент2 страницыCicada 3301: DescriptionJasom BourneОценок пока нет
- Lab 4Документ5 страницLab 4Nguyen Dinh Quan (K15 HCM)Оценок пока нет
- ECIH Review QuestionsДокумент24 страницыECIH Review QuestionsGopinath SОценок пока нет
- COMSEC MaterialДокумент24 страницыCOMSEC MaterialHoang PhucОценок пока нет
- Crypto Basics Exam AnswersДокумент2 страницыCrypto Basics Exam AnswersNizam DinОценок пока нет
- RFC 6749 - The Oauth 2Документ76 страницRFC 6749 - The Oauth 2Jaimy EmmanuelОценок пока нет
- HdfcLogs 20 June 23Документ35 страницHdfcLogs 20 June 23rajeshr0876Оценок пока нет
- IoT Data Sharing Challenges and SolutionsДокумент87 страницIoT Data Sharing Challenges and SolutionsNaveen RoashanОценок пока нет
- Zyxel Zywall Usg300 & GreenBow IPSec VPN Software ConfigurationДокумент16 страницZyxel Zywall Usg300 & GreenBow IPSec VPN Software Configurationgreenbow100% (4)