Академический Документы
Профессиональный Документы
Культура Документы
Mca Degree Subjects
Загружено:
Varun UpadhyayОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Mca Degree Subjects
Загружено:
Varun UpadhyayАвторское право:
Доступные форматы
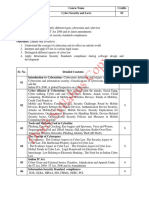
Cyber Security
Objectives Securing vital resources and information in the network is the most challenging
feat for system enterprise. Develop an understanding of information assurance as practiced in
computer operating systems, distributed systems, networks and representative
applications.Gain familiarity with prevalent network and distributed system attacks,
defenses against them.Develop a basic understanding of cryptography, how it has evolved,
and some key encryption techniques used today.Develop an understanding of security
policies (such as authentication, integrity and confidentiality), as well as protocols to
implement such policies in the form of message exchanges.
Outcomes Knowledge about the technical andlegal terms relating to thecybersecurity , cyber
offences and crimes. Gain an insight to the Indian Act 2000 and the organizational
implications of cyber Security
Unit No.
Unit I
Contents
No. Of
Hrs.
Introduction to Cybercrime
Cybercrime definition and origins of the world, Cybercrime and
information security, Classifications of cybercrime,
4 hrs
Unit II
ITA 2000 : Cybercrime and the Indian ITA 2000, A global Perspective on
cybercrimes
4 hrs
Unit III
Cyberoffenses& Cybercrime: Issues and challenges
How criminal plan the attacks, Social Engg, Cyber stalking, Cybercafe and
Cybercrimes, Botnets, Attack vector, Cloud computing,Proliferation of Mobile
and
Wireless Devices, Trends in Mobility, Credit Card Frauds in Mobile and
Wireless
Computing Era, Security Challenges Posed by Mobile Devices, Registry
Settings for
Mobile Devices, Authentication Service Security, Attacks on Mobile/Cell
Phones,
12 hrs
Mobile Devices:Security Implications for Organizations, Organizational
Measures for
Handling Mobile, Devices-Related Security Issues, Organizational Security
Policies
and Measures in Mobile Computing Era, Laptops
Internet Filtering Encryption issues, Internet Gambling, Spam - Unsolicited
Junk Email,
Digital Signatures, Anti-Spam Laws, Anti-Spam Suits, What is Cyber
squatting?
Ant cyber squatting, Software Piracy, Domain Name Disputes, File Sharing ,
Unit IV
Tools and Methods Used in Cyberline :
Proxy Servers and Anonymizers, Phishing, Password Cracking, Keyloggers
and
Spywares, Virus and Worms, Steganography, DoSDDoS Attacks, SQL
6 hrs
Injection,
Buffer Over Flow, Attacks on Wireless Networks, Phishing, Identity Theft (ID
Theft)
Unit V
Cybercrimes and Cybersecurity: The Legal Perspectives
Why do we need Cyberlaw: The Indian Context, The Indian IT Act, Digital
Signature
and the Indian IT Act, Amendments to the Indian IT Act, Cybercrime and
Punishment, Cyberlaw, Technology and Students: Indian Scenario
6 hrs
Cybersecurity: Organizational Implications
Cost of Cybercrimes and IPR Issues:Lesson for Organizations, Web Treats for
Organizations: The Evils and Perils, Security and Privacy Implications from
Cloud
Computing, Social Media Marketing:Security Risk and Perils for
Organization, Social
Computing and the Associated Challenges for Organizations, Protecting
Peoples
Privacy in the Organization,Organizational Guidelines for Internet Usage,
Safe
Computing Guidelines and Computer Usage Policy, Incident Handling: An
Essential
Component,Intellectual Property in the Cyberspace of Cybersecurity,
Importance of
Endpoint Security in Organizations
8 hrs
Unit VI
Unit VII Cyber Acts and related issues
Children's Online Privacy Protection Act (COPPA), The Childrens Internet
Protection Act (CIPA Sexual Predator Laws), The Child Online Protection Act
5 Hrs
(COPA) , The Communications Decency Act (CDA), Electronic Signatures in
Global & National Commerce Act (E-Sign),
Instructions forAssignments and Tutorials:
The Term Work Should consist of two tests, One Presentation/Case Study and six assignments
based on the recommended syllabus
References::
1. Nina Godbole, SunitBelapure, Cyber Security: Understanding Cyber Crimes, Computer
Forensics and Legal Perspectives, Wiley India, New Delhi
2. KAHATE ,Cryptography and Network Security, TMH
3. Information Systems Security, Nina Godbole, Wiley India, New Delhi
4. Cybersecurity: The Essential Body of Knowledge, Dan Shoemaker, William Arthur
Conklin, Wm Arthur Conklin, Cengage Learning.
5. Cyber Security, Edward Amoroso, Silicon Press, First Edition
6. Cyber Security &Global Information Assurance,Kennetch J. Knapp, Information Science
Publishing.
7. William Stallings, Cryptography and Network Security, Pearson Publication
Вам также может понравиться
- Cyber Security 1Документ17 страницCyber Security 1bhupesh yadavОценок пока нет
- Cyber Security (Open Elective) ObjectivesДокумент2 страницыCyber Security (Open Elective) Objectivessriramganesh8107Оценок пока нет
- CSL SyllabusДокумент2 страницыCSL SyllabusTanmay DoshiОценок пока нет
- CSL SyllabusДокумент2 страницыCSL SyllabusKrupesh PatilОценок пока нет
- Syllabus of Cyber Security - Topics List V1.0Документ6 страницSyllabus of Cyber Security - Topics List V1.0751kps100% (1)
- Safeguarding the Digital Fortress: A Guide to Cyber Security: The IT CollectionОт EverandSafeguarding the Digital Fortress: A Guide to Cyber Security: The IT CollectionОценок пока нет
- Study Material SMДокумент57 страницStudy Material SMDIVY UPADHYAYОценок пока нет
- Cyber Security NotesДокумент51 страницаCyber Security NotesBhure VedikaОценок пока нет
- ManagementДокумент16 страницManagementAbhishek KhandekarОценок пока нет
- Cyber SecurityДокумент29 страницCyber SecurityKanik GuptaОценок пока нет
- Cyber Security: Trends, Issues and ChallengesДокумент16 страницCyber Security: Trends, Issues and ChallengesIsaac NwekeОценок пока нет
- Cyber Security Notes 4-1Документ81 страницаCyber Security Notes 4-1Sripriya BellaryОценок пока нет
- Cyber Security - I.ravi KumarДокумент38 страницCyber Security - I.ravi KumarMr. RAVI KUMAR IОценок пока нет
- Internet SafeДокумент3 страницыInternet SafeMarta CapuchoОценок пока нет
- Digital Notes ON Cyber Security (R18A0521) : B.Tech Iii Year - Ii Sem (R18)Документ38 страницDigital Notes ON Cyber Security (R18A0521) : B.Tech Iii Year - Ii Sem (R18)Shyam Sulbhewar100% (1)
- Cyber SecurityДокумент9 страницCyber SecuritydiljitgippyОценок пока нет
- Role of Cyber Law in Cyber Security in IndiaДокумент4 страницыRole of Cyber Law in Cyber Security in IndiaHJ ManviОценок пока нет
- Organizations Prevent Network Attacks: Staying Safe in CyberspaceДокумент3 страницыOrganizations Prevent Network Attacks: Staying Safe in CyberspaceGitanjaliОценок пока нет
- Cyber SecurityДокумент53 страницыCyber SecurityAnvesha SharmaОценок пока нет
- Global Perspective Cyberlaw, Regulations and ComplianceДокумент4 страницыGlobal Perspective Cyberlaw, Regulations and ComplianceEditor IJTSRDОценок пока нет
- Cyber Crime: Name:-Jaivik Akbari Enroll No: - 20SS02IT002Документ19 страницCyber Crime: Name:-Jaivik Akbari Enroll No: - 20SS02IT002alakh patelОценок пока нет
- Cyber SecurityДокумент39 страницCyber SecurityprateekguptadelОценок пока нет
- Reserach Paper On Cyber SecurityДокумент8 страницReserach Paper On Cyber SecurityAnjali VashishthaОценок пока нет
- Building Cyber Security Warriors in 30 DaysДокумент191 страницаBuilding Cyber Security Warriors in 30 DaysForyanto J. Wiguna100% (4)
- Egovernance Case StudyДокумент10 страницEgovernance Case StudyHemant KhatiwadaОценок пока нет
- Cyber SecurityДокумент21 страницаCyber SecurityNaz SamОценок пока нет
- Cybersecurity and Machine LearningДокумент15 страницCybersecurity and Machine LearningRikky AbdulОценок пока нет
- Elective: Iv BEIT804T1 Cyber Security: B.E. Eighth SemesterДокумент2 страницыElective: Iv BEIT804T1 Cyber Security: B.E. Eighth SemesterSrinivas KanakalaОценок пока нет
- The Role of Artificial Intelligence in Cyber Security: Harsh ShrivastavaДокумент4 страницыThe Role of Artificial Intelligence in Cyber Security: Harsh ShrivastavaSandeep SutradharОценок пока нет
- Cyber Security (R18A0521) Lecture Notes: Department of CseДокумент37 страницCyber Security (R18A0521) Lecture Notes: Department of CseSRAVANTHI SALLARAM100% (2)
- Cyber Law and Information SecurityДокумент47 страницCyber Law and Information Securityswaroop666Оценок пока нет
- Cyber Law Cyber Crime & IPR NotesДокумент33 страницыCyber Law Cyber Crime & IPR NotesPRAVEEN M RОценок пока нет
- Essentials of Cyber SecurityДокумент1 страницаEssentials of Cyber Securityravikumar rayala100% (1)
- JITA Special Issue on CybersecurityДокумент4 страницыJITA Special Issue on CybersecurityZoran AvramovicОценок пока нет
- Cyber Crime and Cyber SecurityДокумент9 страницCyber Crime and Cyber SecurityEditor IJTSRDОценок пока нет
- Cyber SecurityДокумент5 страницCyber SecuritynaganathОценок пока нет
- Cyber Insurance PolicyДокумент4 страницыCyber Insurance Policyraj478885Оценок пока нет
- Towards the Impact of Hacking on Cyber SecurityДокумент18 страницTowards the Impact of Hacking on Cyber SecurityfarhanahОценок пока нет
- Cyber Security AbstractДокумент6 страницCyber Security AbstractB Pallavi ReddyОценок пока нет
- Sociology Resarch Paper 2Документ10 страницSociology Resarch Paper 2munОценок пока нет
- IEEE DL Survey ExactДокумент82 страницыIEEE DL Survey ExactArthee PandiОценок пока нет
- Cyber Security ResearchДокумент9 страницCyber Security Researchdagy36444Оценок пока нет
- Cybersecurity For Beginners: Learn How To Defend Against Online ThreatsОт EverandCybersecurity For Beginners: Learn How To Defend Against Online ThreatsОценок пока нет
- Chapter One For MieteДокумент7 страницChapter One For MieteoluwaseunОценок пока нет
- Thesis On Cybercrime in IndiaДокумент8 страницThesis On Cybercrime in Indiakarinathomasdenver100% (2)
- Digital AwarenessДокумент8 страницDigital Awarenessdj.newsense7Оценок пока нет
- Ethical Hacking and Counter Measures Course OutlineДокумент7 страницEthical Hacking and Counter Measures Course Outlineresearch.aiОценок пока нет
- Cybersecurity in The Digital AgeДокумент1 страницаCybersecurity in The Digital AgeCristiana FelicianoОценок пока нет
- Cyber Security Digital Forensics WorkДокумент6 страницCyber Security Digital Forensics Workokware brianОценок пока нет
- 47-Case Study (CS) - 101-1-10-20191001Документ3 страницы47-Case Study (CS) - 101-1-10-20191001gayathri vОценок пока нет
- Study of Measures To Be Taken For Ensuring Cyber SecurityДокумент17 страницStudy of Measures To Be Taken For Ensuring Cyber SecurityRahul JHA100% (2)
- Unit 1Документ107 страницUnit 1Rithik Barsal0% (1)
- Running Head: CYBERSECURITY 1Документ11 страницRunning Head: CYBERSECURITY 1Tonnie KiamaОценок пока нет
- Cyber Security and Its ImportanceДокумент5 страницCyber Security and Its ImportanceMarvin ArregladoОценок пока нет
- A Comparative Analysis of Cyber Attacks and Crimes in Cyber SecurityДокумент6 страницA Comparative Analysis of Cyber Attacks and Crimes in Cyber Securityprathameshsahastrabuddhe2003Оценок пока нет
- Dissertation Cyber CrimeДокумент7 страницDissertation Cyber CrimeDoMyPaperForMoneySingapore100% (2)
- CHAPTER 1& 2 - Cybersecurity - A World of Experts and Criminals and The Cybersecurity CubeДокумент13 страницCHAPTER 1& 2 - Cybersecurity - A World of Experts and Criminals and The Cybersecurity CubeBangtriggaОценок пока нет
- Need For Reforms in Cyber LawsДокумент16 страницNeed For Reforms in Cyber LawsVeerОценок пока нет
- Systems SecurityДокумент257 страницSystems SecurityMuriithi MurageОценок пока нет
- Introduction To BIAДокумент18 страницIntroduction To BIAVarun UpadhyayОценок пока нет
- Disaster Recovery Plans: Keep Business RunningДокумент19 страницDisaster Recovery Plans: Keep Business RunningVarun UpadhyayОценок пока нет
- Basics of Information SecurityДокумент16 страницBasics of Information SecurityVarun UpadhyayОценок пока нет
- Batch ProgrammingДокумент9 страницBatch ProgrammingVarun UpadhyayОценок пока нет
- Information Security PolicyДокумент19 страницInformation Security PolicyVarun UpadhyayОценок пока нет
- How To Cancel TicketsДокумент1 страницаHow To Cancel TicketsVarun UpadhyayОценок пока нет
- Finalsol f05Документ6 страницFinalsol f05sparkyboy1Оценок пока нет
- Fire Jumper Academy Essentials Assessments and POVsДокумент45 страницFire Jumper Academy Essentials Assessments and POVscrisandy310% (1)
- Cisco Secure Email: Ordering Guide For GPLДокумент39 страницCisco Secure Email: Ordering Guide For GPLDOUGLASS SANTAMARIA CASTA�EDAОценок пока нет
- Mail-Secure 2000-3000 For Midsized Businesses: Product OverviewДокумент3 страницыMail-Secure 2000-3000 For Midsized Businesses: Product OverviewYossefОценок пока нет
- Fortios Handbook 54 PDFДокумент3 124 страницыFortios Handbook 54 PDFNova JosephОценок пока нет
- PlanДокумент30 страницPlanBen Torkia JaweherОценок пока нет
- Ccba and Cbap Recertification HandbookДокумент13 страницCcba and Cbap Recertification HandbookRachit GandhiОценок пока нет
- SOPRANO TIM SMTP Interface Developers GuideДокумент43 страницыSOPRANO TIM SMTP Interface Developers GuidenettellectОценок пока нет
- Setting Up A High-Availability Load Balancer (With Failover and Session Support) With HAProxy - Heartbeat On Debian Lenny - PageДокумент12 страницSetting Up A High-Availability Load Balancer (With Failover and Session Support) With HAProxy - Heartbeat On Debian Lenny - PageIanas AndreeaОценок пока нет
- Release NotesДокумент147 страницRelease NotesSoumya RoutОценок пока нет
- Electronic MailДокумент18 страницElectronic MailAsifZharafОценок пока нет
- CVD EmailSecurityUsingCiscoESADesignGuide AUG14Документ36 страницCVD EmailSecurityUsingCiscoESADesignGuide AUG14zxkiwiОценок пока нет
- NetScaler 10.5 HTTP CalloutsДокумент45 страницNetScaler 10.5 HTTP CalloutssudharaghavanОценок пока нет
- ESA 8-0 User GuideДокумент1 124 страницыESA 8-0 User GuidersebbenОценок пока нет
- Mcafee Endpoint Security Suites Comparison Chart: Quick Reference CardДокумент2 страницыMcafee Endpoint Security Suites Comparison Chart: Quick Reference CardSven HedinОценок пока нет
- Cisco Email Security Customer PresentationДокумент38 страницCisco Email Security Customer Presentationravi199250% (2)
- Ddei 3.0 BPGДокумент82 страницыDdei 3.0 BPGNguyen AnhОценок пока нет
- Enhancing Mail Server Security Using MachineДокумент5 страницEnhancing Mail Server Security Using MachineInternational Journal of Innovative Science and Research TechnologyОценок пока нет
- Features and Advantages EPL Vs CE PDFДокумент15 страницFeatures and Advantages EPL Vs CE PDFEd Phénix le PrinceОценок пока нет
- BigPond User GuideДокумент18 страницBigPond User GuideAlbert KiralyОценок пока нет
- Spam Detection MLДокумент2 страницыSpam Detection MLWT OОценок пока нет
- Imsva 9.0 AgДокумент643 страницыImsva 9.0 Agafeesh0% (1)
- ICTNWK536 Assessment Instruction v1.0Документ15 страницICTNWK536 Assessment Instruction v1.0shafe SPОценок пока нет
- Ironport Training 1Документ28 страницIronport Training 1Puneet KumarОценок пока нет
- OSPEERS Notes For AuthorsДокумент3 страницыOSPEERS Notes For AuthorsBharath VОценок пока нет
- EMS - Administrators GuideДокумент419 страницEMS - Administrators GuideNelson MacedoОценок пока нет
- InterScan Messaging Security SuiteДокумент24 страницыInterScan Messaging Security SuiteIslam HelloОценок пока нет
- January 2023: Top 10 Cited Articles in Computer Science & Information TechnologyДокумент32 страницыJanuary 2023: Top 10 Cited Articles in Computer Science & Information TechnologyAnonymous Gl4IRRjzNОценок пока нет
- Email Success by Design PDFДокумент184 страницыEmail Success by Design PDFJuan IsaacОценок пока нет
- Fake Job Recruitment Detection Using Machine Learning ApproachДокумент7 страницFake Job Recruitment Detection Using Machine Learning ApproachPranoti DeshmukhОценок пока нет