Академический Документы
Профессиональный Документы
Культура Документы
Balanceo de Carga ECMP
Загружено:
Cesar CoelloАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Balanceo de Carga ECMP
Загружено:
Cesar CoelloАвторское право:
Доступные форматы
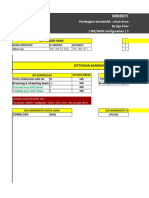
ECMP load balancing with masquerade
ECMP load balancing with masquerade
Introduction
This example is improved (different) version of round-robin load balancing example. It adds persistent user sessions,
i.e. a particular user would use the same source IP address for all outgoing connections. Consider the following
network layout:
Quick Start for Impatient
Configuration export from the gateway router:
/ ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local
add address=10.111.0.2/24 network=10.111.0.0 broadcast=10.111.0.255 interface=wlan2
add address=10.112.0.2/24 network=10.112.0.0 broadcast=10.112.0.255 interface=wlan1
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1,10.112.0.1 check-gateway=ping
/ ip firewall nat
add chain=srcnat out-interface=wlan1 action=masquerade
add chain=srcnat out-interface=wlan2 action=masquerade
/ ip firewall mangle
add chain=input in-interface=wlan1 action=mark-connection new-connection-mark=wlan1_conn
add chain=input in-interface=wlan2 action=mark-connection new-connection-mark=wlan2_conn
ECMP load balancing with masquerade
add chain=output connection-mark=wlan1_conn action=mark-routing new-routing-mark=to_wla1
add chain=output connection-mark=wlan1_conn action=mark-routing new-routing-mark=to_wla2
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1 routing-mark=to_wla1
add dst-address=0.0.0.0/0 gateway=10.111.0.2 routing-mark=to_wla2
Explanation
First we give a code snippet and then explain what it actually does.
IP Addresses
/ ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local
add address=10.111.0.2/24 network=10.111.0.0 broadcast=10.111.0.255 interface=wlan2
add address=10.112.0.2/24 network=10.112.0.0 broadcast=10.112.0.255 interface=wlan1
The router has two upstream (WAN) interfaces with the addresses of 10.111.0.2/24 and 10.112.0.2/24. The LAN
interface has the name "Local" and IP address of 192.168.0.1/24.
NAT
/ ip firewall nat
add chain=srcnat out-interface=wlan1 action=masquerade
add chain=srcnat out-interface=wlan2 action=masquerade
As routing decision is already made we just need rules that will fix src-addresses for all outgoing packets. if this
packet will leave via wlan1 it will be NATed to 10.112.0.2/24, if via wlan2 then NATed to 10.111.0.2/24
Routing
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1,10.112.0.1 check-gateway=ping
This is typical ECMP (Equal Cost Multi-Path) gateway with check-gateway. ECMP is "persistent per-connection
load balancing" or "per-src-dst-address combination load balancing". As soon as one of the gateway will not be
reachable, check-gateway will remove it from gateway list. And you will have a "failover" effect.
You can use asymmetric bandwidth links also - for example one link is 2Mbps other 10Mbps. Just use this command
to make load balancing 1:5
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1,10.112.0.1,10.112.0.1,10.112.0.1,10.112.0.1,10.112.0.1 check-gateway=ping
Connections to the router itself
/ ip firewall mangle
add chain=input in-interface=wlan1 action=mark-connection new-connection-mark=wlan1_conn
add chain=input in-interface=wlan2 action=mark-connection new-connection-mark=wlan2_conn
add chain=output connection-mark=wlan1_conn action=mark-routing new-routing-mark=to_wlan1
add chain=output connection-mark=wlan1_conn action=mark-routing new-routing-mark=to_wlan2
ECMP load balancing with masquerade
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1 routing-mark=to_wlan1
add dst-address=0.0.0.0/0 gateway=10.111.0.2 routing-mark=to_wlan2
With all multi-gateway situations there is a usual problem to reach router from public network via one, other or both
gateways. Explanations is very simple - Outgoing packets uses same routing decision as packets that are going
trough the router. So reply to a packet that was received via wlan1 might be send out and masqueraded via wlan2.
To avoid that we need to policy routing those connections.
Known Issues
DNS issues
ISP specific DNS servers might have custom configuration that treats specific requests from ISP's network
differently than requests from other network. So in case connection is made via other gateway those sites will not be
accessible.
To avoid that we suggest to use 3rd-party (public) DNS servers, and in case you need ISP specific recourse, create
static DNS entry and policy route that traffic to specific gateway.
Routing table flushing
Every time when something triggers flush of the routing table and ECMP cache is flushed. Connections will be
assigned to gateways once again and may or may not be on the same gateway.(in case of 2 gateways there are 50%
chance that traffic will start to flow via other gateway).
If you have fully routed network (clients address can be routed via all available gateway), change of the gateway will
have no ill effect, but in case you use masquerade, change of the gateway will result in change of the packet's source
address and connection will be dropped.
Routing table flush can be caused by 2 things:
1) routing table change (dynamic routing protocol update, user manual changes)
2) every 10 minutes routing table is flushed for security reasons (to avoid possible DoS attacks)
So even if you do not have any changes of routing table, connections may jump to other gateway every 10
minutes
Article Sources and Contributors
Article Sources and Contributors
ECMP load balancing with masquerade Source: http://wiki.mikrotik.com/index.php?oldid=11939 Contributors: AegKim, Atis, Caci99, Eugene, GWISA, Haider74, Maximan, Megis, Normis,
ZoemDoef
Image Sources, Licenses and Contributors
Image:LoadBalancing.jpg Source: http://wiki.mikrotik.com/index.php?title=File:LoadBalancing.jpg License: unknown Contributors: Eugene
Вам также может понравиться
- IiooДокумент157 страницIiooGTA 5100% (1)
- Scripts Mikrotik de DaratoДокумент10 страницScripts Mikrotik de DaratoWalther Ortiz SuasnabarОценок пока нет
- Step To Remove Ads by PanCafe Pro Permanently and SafelyДокумент3 страницыStep To Remove Ads by PanCafe Pro Permanently and SafelyWin Rap0% (1)
- Scrip Mikrotik - Manajemen BanwidthДокумент15 страницScrip Mikrotik - Manajemen Banwidthinternet rumahОценок пока нет
- Bloquear PublicidadДокумент2 страницыBloquear PublicidadTeresita PicasoОценок пока нет
- Vpnpubg MikrotikДокумент2 страницыVpnpubg MikrotikLara ZainОценок пока нет
- Script 1wan Modified by Naufal FinalДокумент35 страницScript 1wan Modified by Naufal FinalSundary Rsbt100% (1)
- AOS 6.3.3.R01 OS6400 CLI Reference Guide PDFДокумент2 886 страницAOS 6.3.3.R01 OS6400 CLI Reference Guide PDFnixmicrosoftОценок пока нет
- Script Configuracion rB2011Документ5 страницScript Configuracion rB2011SoldierОценок пока нет
- Balanceo GorkaДокумент4 страницыBalanceo Gorkatelecomunicacionesos100% (1)
- ADS4020Документ2 страницыADS4020diegoh_silva0% (1)
- RING RING QTK-GE504GW-DX-XPON Pppoe ConfigurationДокумент5 страницRING RING QTK-GE504GW-DX-XPON Pppoe ConfigurationJuan AlexisОценок пока нет
- Port GameДокумент2 страницыPort GameAnonymous oV47buBoОценок пока нет
- Setting MikrotikДокумент10 страницSetting MikrotikLambace KecciОценок пока нет
- Mikrotik Static IP WAN - LAN PPPoE Server ConfigДокумент4 страницыMikrotik Static IP WAN - LAN PPPoE Server ConfigDenisa PriftiОценок пока нет
- Script RawДокумент2 страницыScript RawAshari JensakayОценок пока нет
- Copia RB 2011 Rita ... MikrotikДокумент9 страницCopia RB 2011 Rita ... MikrotikWireless Networks Empresa de telecomunicacionesОценок пока нет
- 3 Lineas Balanceo Mixto Microtik (Jhon)Документ3 страницы3 Lineas Balanceo Mixto Microtik (Jhon)jhonОценок пока нет
- ScriptДокумент17 страницScriptdhedoy kardiman100% (1)
- List ! - List - List ! - ListДокумент12 страницList ! - List - List ! - ListJames BoldОценок пока нет
- PPPoE Client SetupДокумент3 страницыPPPoE Client SetupJose Luis Rodriguez BarrazaОценок пока нет
- Configurar QoS en Mikrotik (1-2) - MangleДокумент4 страницыConfigurar QoS en Mikrotik (1-2) - MangleMax Fredi Quispe AguilarОценок пока нет
- Qos IndirectoДокумент3 страницыQos Indirectogustavo perezОценок пока нет
- Script Prioritas Game Online Labkom - Co.idДокумент11 страницScript Prioritas Game Online Labkom - Co.idAris SetyawanОценок пока нет
- Firewall MikrotikДокумент4 страницыFirewall Mikrotiktec_danielsotoОценок пока нет
- VPN Mikrotik Cliente - Servidor L2TP IPsec Extensiones Remotas IOS AndroidДокумент32 страницыVPN Mikrotik Cliente - Servidor L2TP IPsec Extensiones Remotas IOS AndroidJose ArturoОценок пока нет
- Load PCC+NTHДокумент1 страницаLoad PCC+NTHIskandar MustofaОценок пока нет
- PBR Wan DinamicasДокумент1 страницаPBR Wan DinamicasKelvin Rafael Del Rosario Martinez100% (1)
- Limit Bandwith Using Layer 7-Protocol PDFДокумент5 страницLimit Bandwith Using Layer 7-Protocol PDFwawa_sygОценок пока нет
- ECMP Load Balancing With MasqueradeДокумент6 страницECMP Load Balancing With Masqueradenadit88Оценок пока нет
- Load Balancer Metodo PCCДокумент5 страницLoad Balancer Metodo PCCJavier Toro MendozaОценок пока нет
- Load Balancing Persistent: From Mikrotik WikiДокумент5 страницLoad Balancing Persistent: From Mikrotik Wikiapi-19807007Оценок пока нет
- Manual PCCДокумент5 страницManual PCCAlejandro DariczОценок пока нет
- Mikrotik DUAL WAN Load Balancing Using PCC MethodДокумент46 страницMikrotik DUAL WAN Load Balancing Using PCC Methoddamian3003100% (3)
- Manual Mikrotik: Balanceo de Carga de Dos LineasДокумент6 страницManual Mikrotik: Balanceo de Carga de Dos LineasFranco Zuñiga ZavalaОценок пока нет
- MIKROTIK - FIREWALL - Firewall MarkingДокумент4 страницыMIKROTIK - FIREWALL - Firewall Markingmauro lipisОценок пока нет
- Mikrotik DUAL WAN Load Balancing Using PCC MethodДокумент2 страницыMikrotik DUAL WAN Load Balancing Using PCC Methodjuan_guzmán_144100% (1)
- Squid Load Between Two ServersДокумент5 страницSquid Load Between Two ServersMiriel Martin MesaОценок пока нет
- Networks Basic CommandsДокумент6 страницNetworks Basic CommandsSrija KondruОценок пока нет
- Cisco ActualTests 300-101 v2016-06-22 by Mangary 127qДокумент149 страницCisco ActualTests 300-101 v2016-06-22 by Mangary 127qGabriela PopescuОценок пока нет
- CCNA 1 v7 Examin FinaalДокумент62 страницыCCNA 1 v7 Examin FinaalRiadh SalhiОценок пока нет
- Hillstone All Series Device Troubleshooting and Debug GuideДокумент134 страницыHillstone All Series Device Troubleshooting and Debug GuideWAMS FILE100% (1)
- 350 001 V4Документ231 страница350 001 V4ryanshin10Оценок пока нет
- TSHOOT CH 7Документ9 страницTSHOOT CH 7liketotallyОценок пока нет
- CCNA3 ExamДокумент152 страницыCCNA3 ExamIgor CvijovicОценок пока нет
- 300 101Документ119 страниц300 101chetan666123Оценок пока нет
- Load Balancing 2 ISPДокумент7 страницLoad Balancing 2 ISPAr RasidОценок пока нет
- NTH Load Balancing With MasqueradeДокумент6 страницNTH Load Balancing With MasqueradeAan AansoriОценок пока нет
- MikRoTik VPN ConfigurationДокумент5 страницMikRoTik VPN ConfigurationShah ParanОценок пока нет
- 1) Not Able To Connect Database? (Ping Is Working Fine and Database Is Up and Running) What Would Be Reasons?Документ3 страницы1) Not Able To Connect Database? (Ping Is Working Fine and Database Is Up and Running) What Would Be Reasons?Sudhesh PnairОценок пока нет
- Mikrotik Transparent Traffic ShaperДокумент9 страницMikrotik Transparent Traffic Shaperoffline71Оценок пока нет
- Mariadb Maxscale HAДокумент12 страницMariadb Maxscale HADang Huu AnhОценок пока нет
- Cisco Examcollection Premium 300-101 v2015-11-18 Kaltzone 116q PDFДокумент192 страницыCisco Examcollection Premium 300-101 v2015-11-18 Kaltzone 116q PDFleotrimОценок пока нет
- Lab 1 5 3 PDFДокумент4 страницыLab 1 5 3 PDFSan SokvisalОценок пока нет
- Manual - PCC - MikroTik WikiДокумент5 страницManual - PCC - MikroTik WikiachainyaОценок пока нет
- Configuring Multiple WAN Connection Failover in AOSДокумент12 страницConfiguring Multiple WAN Connection Failover in AOSDavid StowellОценок пока нет
- Configuracion de Red EthernetДокумент7 страницConfiguracion de Red EthernetCesar LeonОценок пока нет
- 300-101.examcollection - Premium.exam.149q: 300-101 Implementing Cisco IP RoutingДокумент41 страница300-101.examcollection - Premium.exam.149q: 300-101 Implementing Cisco IP RoutingGabriela PopescuОценок пока нет
- CCNP Route 300-101 Dump by Alozie CharlesДокумент101 страницаCCNP Route 300-101 Dump by Alozie CharlesKAy Cee100% (4)
- Cisco Security Troubleshooting: Part III - Intrusion Prevention SystemsДокумент14 страницCisco Security Troubleshooting: Part III - Intrusion Prevention SystemshoadiОценок пока нет
- EC Council Product Job Role SheetДокумент1 страницаEC Council Product Job Role Sheetak123456Оценок пока нет
- IOS Zone-Based FirewallДокумент1 страницаIOS Zone-Based FirewallWalter ValverdeОценок пока нет
- Ieee 802.11 Wlan PDFДокумент2 страницыIeee 802.11 Wlan PDFruletriplexОценок пока нет
- BGP Multi Homing HOWTO WhitepaperДокумент29 страницBGP Multi Homing HOWTO WhitepaperLaolu SijuwolaОценок пока нет
- BGP Casos PDFДокумент288 страницBGP Casos PDFnambiar123Оценок пока нет
- Internet ProtocolsДокумент14 страницInternet ProtocolsMARIO BUENAVENTEОценок пока нет
- 15 f08 Network Sockets1Документ12 страниц15 f08 Network Sockets1akirank1Оценок пока нет
- Loadbalance PCC +NTHДокумент1 страницаLoadbalance PCC +NTHIskandar Mustofa100% (1)
- Audiocodes Multi-Service Business Router Family: All-In-One Integrated Routers With Access, Data, Voice and SecurityДокумент3 страницыAudiocodes Multi-Service Business Router Family: All-In-One Integrated Routers With Access, Data, Voice and SecurityrcpinfoОценок пока нет
- 8.1.4.8 Lab - Identifying IPv4 Addresses PDFДокумент4 страницы8.1.4.8 Lab - Identifying IPv4 Addresses PDFErnestoPérezОценок пока нет
- Threat Assessment Last Week 2022-06-21T02 03 00ZДокумент19 страницThreat Assessment Last Week 2022-06-21T02 03 00ZDung Nguyen HoaiОценок пока нет
- Practical No. 4: Configure IP Routing Using RIPДокумент13 страницPractical No. 4: Configure IP Routing Using RIPkuldeep RajbharОценок пока нет
- CiscoKits CCNA Self LabДокумент2 страницыCiscoKits CCNA Self LablokelaniОценок пока нет
- Florante at LauraДокумент12 страницFlorante at LauraKuroo TetsuОценок пока нет
- Hcip H12-222Документ407 страницHcip H12-222M.fajar RabbaniОценок пока нет
- Ccnpv7 Route Lab3-2 Multi-Area-ospf StudentДокумент19 страницCcnpv7 Route Lab3-2 Multi-Area-ospf StudentCarlos Alberto Pedraza CruzОценок пока нет
- EchoLife HG510 Home Gateway User ManualДокумент69 страницEchoLife HG510 Home Gateway User ManualSteve BrootsОценок пока нет
- x900 Series Rev ZB PDFДокумент8 страницx900 Series Rev ZB PDFandra_kaneОценок пока нет
- Chart Title: US Census BureauДокумент7 страницChart Title: US Census BureauShubham AroraОценок пока нет
- Examen 11-13Документ9 страницExamen 11-13Jhon RojasОценок пока нет
- FTTHДокумент7 страницFTTHBSNL TRANSMISSION kathuaОценок пока нет
- Chapter 12Документ3 страницыChapter 12Anonymous QE45TVC9e3Оценок пока нет
- Ccie Routing SwitchingДокумент20 страницCcie Routing SwitchingMusaib SyedОценок пока нет
- Document Guide For Barracuda NG Firewall & Control CenterДокумент184 страницыDocument Guide For Barracuda NG Firewall & Control CenterForex HocОценок пока нет
- MPLS and Traffic Engineering in IP NetworksДокумент6 страницMPLS and Traffic Engineering in IP Networksجمال سينغОценок пока нет
- 04 Network Layer Protocols and IP AddressingДокумент45 страниц04 Network Layer Protocols and IP Addressingيوسف الدرسيОценок пока нет
- (At Command) Usr Tcp232 E2 at Command Set - v1.0.0Документ22 страницы(At Command) Usr Tcp232 E2 at Command Set - v1.0.0curzОценок пока нет
- CCNPv6 ROUTE On Line SkillДокумент2 страницыCCNPv6 ROUTE On Line SkillMithaq Abdulla100% (2)
- 3 Hours / 70 Marks: Seat NoДокумент4 страницы3 Hours / 70 Marks: Seat NobodevewОценок пока нет
- SGOSAdmin 73Документ1 584 страницыSGOSAdmin 73Erhan GündüzОценок пока нет
- Unit Iv-1Документ33 страницыUnit Iv-1InnocentОценок пока нет
- CCNA 2 v7.0 Final Exam Answers-21-40Документ20 страницCCNA 2 v7.0 Final Exam Answers-21-40kavindu AmeshОценок пока нет
- Q.no 1. How Many Versions Available of IP?Документ169 страницQ.no 1. How Many Versions Available of IP?Ash's HELLОценок пока нет
- Topic 2.4 Network ServicesДокумент13 страницTopic 2.4 Network ServicesمحمدجوزيايОценок пока нет
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityОт EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityРейтинг: 5 из 5 звезд5/5 (1)
- The Internet Con: How to Seize the Means of ComputationОт EverandThe Internet Con: How to Seize the Means of ComputationРейтинг: 5 из 5 звезд5/5 (6)
- The Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellОт EverandThe Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellРейтинг: 5 из 5 звезд5/5 (6)
- How to Do Nothing: Resisting the Attention EconomyОт EverandHow to Do Nothing: Resisting the Attention EconomyРейтинг: 4 из 5 звезд4/5 (421)
- More Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingОт EverandMore Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingРейтинг: 3.5 из 5 звезд3.5/5 (24)
- The Dark Net: Inside the Digital UnderworldОт EverandThe Dark Net: Inside the Digital UnderworldРейтинг: 3.5 из 5 звезд3.5/5 (104)
- Grokking Algorithms: An illustrated guide for programmers and other curious peopleОт EverandGrokking Algorithms: An illustrated guide for programmers and other curious peopleРейтинг: 4 из 5 звезд4/5 (16)
- Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTОт EverandPractical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTОценок пока нет
- Nine Algorithms That Changed the Future: The Ingenious Ideas That Drive Today's ComputersОт EverandNine Algorithms That Changed the Future: The Ingenious Ideas That Drive Today's ComputersРейтинг: 5 из 5 звезд5/5 (7)
- HTML5 and CSS3 Masterclass: In-depth Web Design Training with Geolocation, the HTML5 Canvas, 2D and 3D CSS Transformations, Flexbox, CSS Grid, and More (English Edition)От EverandHTML5 and CSS3 Masterclass: In-depth Web Design Training with Geolocation, the HTML5 Canvas, 2D and 3D CSS Transformations, Flexbox, CSS Grid, and More (English Edition)Оценок пока нет
- Python for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldОт EverandPython for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldОценок пока нет
- Ten Arguments for Deleting Your Social Media Accounts Right NowОт EverandTen Arguments for Deleting Your Social Media Accounts Right NowРейтинг: 4 из 5 звезд4/5 (388)
- React.js Design Patterns: Learn how to build scalable React apps with ease (English Edition)От EverandReact.js Design Patterns: Learn how to build scalable React apps with ease (English Edition)Оценок пока нет
- The Wires of War: Technology and the Global Struggle for PowerОт EverandThe Wires of War: Technology and the Global Struggle for PowerРейтинг: 4 из 5 звезд4/5 (34)
- Articulating Design Decisions: Communicate with Stakeholders, Keep Your Sanity, and Deliver the Best User ExperienceОт EverandArticulating Design Decisions: Communicate with Stakeholders, Keep Your Sanity, and Deliver the Best User ExperienceРейтинг: 4 из 5 звезд4/5 (19)