Академический Документы
Профессиональный Документы
Культура Документы
What is network management and its key benefits
Загружено:
kingsarat0 оценок0% нашли этот документ полезным (0 голосов)
21 просмотров3 страницыNetwork management involves maintaining all network resources in good working order and making them available to users as expected. The network administrator is responsible for network management, which includes ensuring visibility and accountability of devices, reducing troubleshooting time through configuration backups, providing timely alerts of configuration changes to minimize downtime, improving the process of configuration changes for better productivity, and ensuring compliance of device configurations, software versions, and hardware.
Исходное описание:
sdkjnjs
Оригинальное название
fdkskjnl
Авторское право
© © All Rights Reserved
Доступные форматы
DOCX, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документNetwork management involves maintaining all network resources in good working order and making them available to users as expected. The network administrator is responsible for network management, which includes ensuring visibility and accountability of devices, reducing troubleshooting time through configuration backups, providing timely alerts of configuration changes to minimize downtime, improving the process of configuration changes for better productivity, and ensuring compliance of device configurations, software versions, and hardware.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
21 просмотров3 страницыWhat is network management and its key benefits
Загружено:
kingsaratNetwork management involves maintaining all network resources in good working order and making them available to users as expected. The network administrator is responsible for network management, which includes ensuring visibility and accountability of devices, reducing troubleshooting time through configuration backups, providing timely alerts of configuration changes to minimize downtime, improving the process of configuration changes for better productivity, and ensuring compliance of device configurations, software versions, and hardware.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 3
HOMEWORK-1
2. What is network management?
Network management is the set of actions that ensures that all network resources
are put to productive use as best as possible. It consists of maintaining all network
resources in good shape and making them available to users in accordance with the
users' expectations.
The person who performs network management is called a network administrator or
a network manager.
2.
Better visibility and accountability for devices in the network: Device
configuration management includes the ability to conduct an accurate and up
to date network device inventory. This will help ensure that the IT department
and the business group in the organization are aligned with each other. By
maintaining accurate and up to date information of devices, substantiation
for incidents, troubleshooting configuration issues, managing configuration
changes and also budget planning for devices, it provides a comprehensive
platform for inventory/device management.
Less troubleshooting time in the case of downtime caused by configuration
issues: Network downtime can be caused due to device hardware malfunction
or erroneous changes in the configuration of the device. In either case,
having an up-to-date network configuration backup plan in place enables you
to reduce downtime by restoring the configuration from a backup. Therefore,
to protect critical devices in your network, its best to have the ability to set
automated network configuration backups.
Timely alerts and identification of configuration changes to reduce network
downtime: With the rapid increase in the number of devices in the network,
management tends to become more and more difficult. As the business
grows and infrastructure changes occur, it becomes mandatory to have alert
systems and mechanisms in place to be notified in real-time on issues and
changes in the network.
Improved process of configuration changes for better network
productivity: Unapproved configurations changes often lead to bad changes
and cause network downtime. By having a change request approval
process in place, youll better be able to track and tackle sensitive
configuration changes made in the network.
Ensure compliance for device configuration, software versions, and
hardware: With effective configuration management in place along with
appropriate processes, compliance becomes less of a challenge. This will also
improve the capability to support network operations.
3. Fault Management addresses the generation of error specific notifications
(alarms), the logging of error notifications at source and the testing of network
resources in order to trace and identify faults. Fault management systems should
undertake alarm surveillance activities (analysis, filtering and correlation), perform
resource testing and provide fault localisation and correction functions. The key
requirements are event-based operation, a well-defined generic set of alarms and a
testing framework. The relevant SMFs are event reporting [X734], logging [X735],
alarm reporting [X733] and testing [X737][X745].
Configuration Management deals with initialization, installation and provisioning
activities. It allows the collection of configuration and status information on
demand, provides inventory facilities and supports the announcement of
configuration changes through relevant notifications. The key requirements are
event-based operation, control of change, generic resource state and relationship
representation, scheduling, time management, software distribution and system
discovery facilities. The relevant SMFs are event reporting [X734], logging [X735],
object [X730], state [X731] and relationship [X.732] management, scheduling
[X746], time management [X743], software distribution [X744] and shared
management knowledge [X750].
Accounting Management deals with the collection of accounting information and
its processing for charging and billing purposes. It should enable accounting limits
to be set and costs to be combined when multiple resources are used in the context
of a service. The key requirements are event based operation, in particular logging,
and a generic usage metering framework. The relevant SMFs are event reporting
[X734], logging [X735] and accounting metering [X742].
Performance Management addresses the availability of information in order to
determine network and system load under both natural and artificial conditions. It
also supports the collection of performance information periodically in order to
provide statistics and allow for capacity planning activities. Performance
management needs access to a large quantity of network information and an
important issue is to provide the latter with a minimum impact on the managed
network. Key requirements are the ability to convert raw traffic information to traffic
rates with thresholds and tidemarks applied to them; the periodic summarization of
a variety of performance information for trend identification and capacity planning;
the periodic scheduling of information collection; and the ability to determine the
response time between network nodes. The relevant SMFs are event reporting
[X734], logging [X735], metric monitoring [X739], summarization [X738],
scheduling [X746] and response time monitoring [X748].
Security Management is concerned with two aspects of systems security. The
management of security, which requires the ability to monitor and control the
availability of security facilities and to report security threats or breaches. And the
security of management, which requires the ability to authenticate management
users and applications, to guarantee the confidentiality and integrity of
management exchanges and to prevent unauthorised access to management
information. Authentication, integrity and confidentiality services are common to all
OSI applications and are addressed for the whole of the OSI framework in [X800]
[GULS]. The key requirements in OSI management are support for security alarms,
facilities for security audit trail and the provision of access control. The relevant
SMFs are event reporting [X734], logging [X735], security alarm reporting [X736],
security audit trail [X737] and access control [X741]
Вам также может понравиться
- Project Synopsis NMSДокумент8 страницProject Synopsis NMSAbhishek Narang100% (1)
- FinActivity2 - Lumanglas, Razel R.Документ9 страницFinActivity2 - Lumanglas, Razel R.Razel Rivera LumanglasОценок пока нет
- Network Design and ManagementДокумент16 страницNetwork Design and ManagementTrevor TheMask KapusaОценок пока нет
- Network Management: Presented by Asst. Prof. Hamidullah RiazДокумент15 страницNetwork Management: Presented by Asst. Prof. Hamidullah RiazMohammad Yasin QuraishiОценок пока нет
- Introduction To Network ManagementДокумент17 страницIntroduction To Network ManagementsaihunterОценок пока нет
- Central Issues in Network Management: Sarah Lowman April 2010Документ8 страницCentral Issues in Network Management: Sarah Lowman April 2010Arefin HasibОценок пока нет
- Planning Maintenance For Network: Elizalde L. Piol, LPT, MsitДокумент25 страницPlanning Maintenance For Network: Elizalde L. Piol, LPT, MsitElizalde Lopez PiolОценок пока нет
- Selecting Control Objectives and Controls, Part IIДокумент3 страницыSelecting Control Objectives and Controls, Part IIKwadwo OwusuОценок пока нет
- Network Administration and ManagementДокумент4 страницыNetwork Administration and Managementanthonylrush4Оценок пока нет
- SAДокумент10 страницSAAsna AbdulОценок пока нет
- ETGRMДокумент38 страницETGRMThe Bearded Guy (TheBeardedGuy)Оценок пока нет
- NMS NotesДокумент5 страницNMS NotesLutfil HadiОценок пока нет
- IT Infrastructure Management and Maintenance System - A Positive Climate Architecture (Itimms)Документ4 страницыIT Infrastructure Management and Maintenance System - A Positive Climate Architecture (Itimms)NaveenJainОценок пока нет
- Lecture 2Документ33 страницыLecture 2makangara22Оценок пока нет
- Physical Infrastructure Management SolutionsДокумент10 страницPhysical Infrastructure Management SolutionsnguyenmanhОценок пока нет
- Secure Network Infrastructure Best PracticesДокумент19 страницSecure Network Infrastructure Best PracticesManuel A. Barros JrОценок пока нет
- Role of IT Operations in E2E AssuranceДокумент5 страницRole of IT Operations in E2E Assuranceconversant.puneetОценок пока нет
- HITRUST Policies - Network Security Management ProcedureДокумент8 страницHITRUST Policies - Network Security Management ProcedureMebrat WorkuОценок пока нет
- Network MonitoringWAДокумент9 страницNetwork MonitoringWAwasirifieОценок пока нет
- Asset Tracking and ManagementДокумент7 страницAsset Tracking and ManagementMukoya OdedeОценок пока нет
- IT Security Management Checklist: 9 Key Recommendations To Keep Your Network SafeДокумент11 страницIT Security Management Checklist: 9 Key Recommendations To Keep Your Network SafeshabuzmushfiqueОценок пока нет
- Circuit Breakers by SoftwareДокумент21 страницаCircuit Breakers by SoftwareKushalgym888 gym888Оценок пока нет
- NOC and SOCДокумент19 страницNOC and SOCshivpreetsandhuОценок пока нет
- Evolution in Network ManagementДокумент5 страницEvolution in Network ManagementJan Nikko MillareОценок пока нет
- ONGC's Information Security Management System and IT Infrastructure MaintenanceДокумент4 страницыONGC's Information Security Management System and IT Infrastructure MaintenanceMinal AggarwalОценок пока нет
- Csi Zero Trust Network Environment PillarДокумент12 страницCsi Zero Trust Network Environment PillarAzaelCarionОценок пока нет
- NETWORK MANAGEMENT & ADMINISTRATION - OverviewДокумент12 страницNETWORK MANAGEMENT & ADMINISTRATION - OverviewRobinson JoshuaОценок пока нет
- Operational procedures and responsibilities documentationДокумент19 страницOperational procedures and responsibilities documentationIRIEОценок пока нет
- CPPPMUSABДокумент74 страницыCPPPMUSABMusabОценок пока нет
- 2 NagiosДокумент48 страниц2 NagiosPrabala Siva KrishnaОценок пока нет
- Design Configuraton and Documentation of IT SecurityДокумент9 страницDesign Configuraton and Documentation of IT SecurityRajanItjJa RAjyaОценок пока нет
- Network Management Processes and ChallengesДокумент5 страницNetwork Management Processes and ChallengesMiraculous MiracleОценок пока нет
- Network Management Definition of Network ManagementДокумент4 страницыNetwork Management Definition of Network ManagementHajiram BeeviОценок пока нет
- Information Security Program Guide Company Policies, Departmental Procedures, IT Standards GuidelinesДокумент66 страницInformation Security Program Guide Company Policies, Departmental Procedures, IT Standards Guidelinesamit balodhi100% (1)
- What is Network ManagementДокумент6 страницWhat is Network ManagementZaheer MohamedОценок пока нет
- Netscreen Security Manager DatasheetДокумент2 страницыNetscreen Security Manager DatasheetDaveОценок пока нет
- Distributed ComputingДокумент13 страницDistributed ComputingEdgar OsoroОценок пока нет
- Network Management Basics ExplainedДокумент6 страницNetwork Management Basics ExplainedMarjorie BustamanteОценок пока нет
- FCAPSДокумент37 страницFCAPSPrashant PanseОценок пока нет
- Circuit Breaker Maintenance by Mobile Agent Software TechnologyДокумент22 страницыCircuit Breaker Maintenance by Mobile Agent Software Technologydinesh414875% (4)
- Nms 2nd UnitДокумент30 страницNms 2nd UnitjilikajithendarОценок пока нет
- Chapter 5: Network ManagementДокумент25 страницChapter 5: Network ManagementANGELIN SHINYОценок пока нет
- Enterprise Network ManagementДокумент5 страницEnterprise Network Managementalex10989Оценок пока нет
- Inter PreperationДокумент23 страницыInter PreperationAdarsha BhattaraiОценок пока нет
- The Effect of Information Technology On The Audit Function: Answers To Review QuestionsДокумент4 страницыThe Effect of Information Technology On The Audit Function: Answers To Review QuestionsroxanneОценок пока нет
- Cis - Lesson 4 Part 2Документ6 страницCis - Lesson 4 Part 2Terrence Grace EscobidoОценок пока нет
- IT Infrastructure Management Operations ProcessДокумент35 страницIT Infrastructure Management Operations ProcesssatriaОценок пока нет
- ITSU3008 Project 1 Assignment 3 Systems Analysis Report: Submitted byДокумент6 страницITSU3008 Project 1 Assignment 3 Systems Analysis Report: Submitted byFarhanAshrafОценок пока нет
- Auditing of Information Systems Case StudyДокумент130 страницAuditing of Information Systems Case StudyhjzaliОценок пока нет
- Introduction to Network Management Protocols SNMP & TR-069Документ22 страницыIntroduction to Network Management Protocols SNMP & TR-069Nguyen Anh DucОценок пока нет
- Unit 4 Assignment 1Документ2 страницыUnit 4 Assignment 1DKnott86Оценок пока нет
- CPPPMUSABДокумент75 страницCPPPMUSABMusabОценок пока нет
- Network Monitoring SystemДокумент23 страницыNetwork Monitoring Systemjack_16Оценок пока нет
- Trish StratusДокумент1 страницаTrish StratusJehanzeb KayaniОценок пока нет
- Guidelines On Maritime Cyber Risk ManagementДокумент15 страницGuidelines On Maritime Cyber Risk Managementseth4422Оценок пока нет
- Securing The NetworkWAДокумент9 страницSecuring The NetworkWAwasirifieОценок пока нет
- Chapter 10 Asset Management 2014 From Machine To Machine To The Internet of ThingsДокумент8 страницChapter 10 Asset Management 2014 From Machine To Machine To The Internet of ThingsDaviti GachechiladzeОценок пока нет
- Network Management Concepts and PrinciplesДокумент3 страницыNetwork Management Concepts and PrinciplesDistro MusicОценок пока нет
- Lesson 1Документ5 страницLesson 1Erika Mae MirandaОценок пока нет
- FlantherДокумент4 страницыFlantherkingsaratОценок пока нет
- DiДокумент7 страницDikingsaratОценок пока нет
- California tenants guide rights responsibilitiesДокумент122 страницыCalifornia tenants guide rights responsibilitieskingsaratОценок пока нет
- Certified School List 5-21-14Документ279 страницCertified School List 5-21-14kingsaratОценок пока нет
- ECE 231 Laboratory Manual 090112 (Word 10)Документ54 страницыECE 231 Laboratory Manual 090112 (Word 10)kingsaratОценок пока нет
- Mandatory Immigration Advisement Session For International StudentsДокумент73 страницыMandatory Immigration Advisement Session For International StudentskingsaratОценок пока нет
- Flight RevisitedДокумент14 страницFlight RevisitedRicardo JaimesОценок пока нет
- Digital Ic DesignДокумент20 страницDigital Ic DesignbindasrahilОценок пока нет
- 2014-2015 International Transfer Special InstructionsДокумент2 страницы2014-2015 International Transfer Special InstructionskingsaratОценок пока нет
- ECE571 Chapter 5Документ19 страницECE571 Chapter 5kingsaratОценок пока нет
- Matlab 13 Install GuideДокумент161 страницаMatlab 13 Install GuideBen Umobi JnrОценок пока нет
- Lumped Elements On The Smith Chart: N O O O N O O OДокумент11 страницLumped Elements On The Smith Chart: N O O O N O O OkingsaratОценок пока нет
- Lumped Elements On The Smith Chart: N O O O N O O OДокумент11 страницLumped Elements On The Smith Chart: N O O O N O O OkingsaratОценок пока нет
- Graduate Student Info BookletДокумент13 страницGraduate Student Info BookletkingsaratОценок пока нет
- GPA CalculationДокумент1 страницаGPA CalculationkingsaratОценок пока нет
- GPA CalculationДокумент1 страницаGPA CalculationkingsaratОценок пока нет
- Poh Medical MirrorДокумент1 страницаPoh Medical MirrorkingsaratОценок пока нет
- Oph3W: Technical DataДокумент2 страницыOph3W: Technical DataArdhan BoyzzОценок пока нет
- Mark Java ResumeДокумент4 страницыMark Java ResumesravanpaulОценок пока нет
- Monitor Stakeholder EngagementДокумент19 страницMonitor Stakeholder EngagementAung Thein OoОценок пока нет
- How to update a crack using pattern search and hex editingДокумент17 страницHow to update a crack using pattern search and hex editingpeterОценок пока нет
- R0310WL007224Документ1 страницаR0310WL007224princesenapati59Оценок пока нет
- VX400s LED Display Controller User ManualДокумент33 страницыVX400s LED Display Controller User ManualAlam PereyraОценок пока нет
- BloodspireДокумент37 страницBloodspirediegoff77Оценок пока нет
- Denoising Chaotic Signals Using Ensemble Intrinsic Time-Scale Decomposition (2022)Документ9 страницDenoising Chaotic Signals Using Ensemble Intrinsic Time-Scale Decomposition (2022)Zsolt ArmaiОценок пока нет
- Chapter 5. Probability and Random Process - UpdatedДокумент151 страницаChapter 5. Probability and Random Process - UpdatedHariharan S RОценок пока нет
- MTTI successful bidders prequalification 2020/2021Документ10 страницMTTI successful bidders prequalification 2020/2021Lawrence KyaloОценок пока нет
- Merford Support StatementДокумент3 страницыMerford Support StatementEdison GonsalvesОценок пока нет
- Ultrasound Designed To Fit Your Application: Logiq C3 PremiumДокумент2 страницыUltrasound Designed To Fit Your Application: Logiq C3 PremiumRSUD SangkulirangОценок пока нет
- Comandos Ccna SecurityДокумент26 страницComandos Ccna SecurityMarcelo Nuñez100% (1)
- Strategic ManagmentДокумент15 страницStrategic ManagmentOzunitos ComunicaОценок пока нет
- SAP MM Interview QuestionsДокумент19 страницSAP MM Interview Questionsok tourОценок пока нет
- Account Management FormДокумент1 страницаAccount Management FormJhannel TupanОценок пока нет
- Computer Hardware Worksheet / Quiz: Make Sure That The Worksheet Is Saved Into The Network Drive Folder For CreditДокумент2 страницыComputer Hardware Worksheet / Quiz: Make Sure That The Worksheet Is Saved Into The Network Drive Folder For CreditRaimundo LimaОценок пока нет
- Holiday Homework for Class 10 Cbse 2015Документ7 страницHoliday Homework for Class 10 Cbse 2015afmtcbjca100% (1)
- Script For Video InterviewДокумент2 страницыScript For Video InterviewRojakBusukОценок пока нет
- Mounted Disc Plough Operator ManualДокумент14 страницMounted Disc Plough Operator ManualJunior KachikhoОценок пока нет
- Google Analytics Event Tracking GuideДокумент20 страницGoogle Analytics Event Tracking GuideagungbijaksanaОценок пока нет
- 30296 Details PDF - Find 30296 Price, Stock, DatasheetДокумент1 страница30296 Details PDF - Find 30296 Price, Stock, DatasheetMaikel Borges IglesiasОценок пока нет
- POLYCAB - MV Power Cable IEC 60502 2Документ32 страницыPOLYCAB - MV Power Cable IEC 60502 2AmitabhaОценок пока нет
- Crusher Cross-Section (Gyratory) PDFДокумент1 страницаCrusher Cross-Section (Gyratory) PDFJuan ArosОценок пока нет
- Chapter 2 Research - Shiela MaeДокумент6 страницChapter 2 Research - Shiela MaeKate Alyzza TubatoОценок пока нет
- TAO (Trace Architecture Office) Projects in Beijing, ChinaДокумент11 страницTAO (Trace Architecture Office) Projects in Beijing, ChinaAlina VoОценок пока нет
- Caja de Piso Ref 25249-FBAДокумент4 страницыCaja de Piso Ref 25249-FBACristianDuarteSandovalОценок пока нет
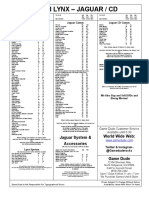
- Atari Lynx - Jaguar / CD: Jaguar System & Accessories World Wide WebДокумент1 страницаAtari Lynx - Jaguar / CD: Jaguar System & Accessories World Wide WebGame DudeОценок пока нет
- ConfigurationДокумент115 страницConfigurationTheo CastroОценок пока нет
- The New Photovoltaic Roof Tile: Made in ItalyДокумент2 страницыThe New Photovoltaic Roof Tile: Made in ItalyYorky Manuel GomezОценок пока нет