Академический Документы
Профессиональный Документы
Культура Документы
Cyberoam Wireless LAN Implementation Guide
Загружено:
Peter AyimАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Cyberoam Wireless LAN Implementation Guide
Загружено:
Peter AyimАвторское право:
Доступные форматы
Cyberoam Wireless LAN Implementation Guide
Version 10
Document version 1.0 10.6.3.260 - 29/05/2015
Cyberoam Wireless LAN Configuration Guide
Important Notice
Cyberoam Technologies Pvt. Ltd. has supplied this Information believing it to be accurate and reliable at the time of printing, but
is presented without warranty of any kind, expressed or implied. Users must take full responsibility for their application of any
products. Cyberoam Technologies Pvt. Ltd. assumes no responsibility for any errors that may appear in this document.
Cyberoam Technologies Pvt. Ltd. reserves the right, without notice to make changes in product design or specifications.
Information is subject to change without notice.
USERS LICENSE
P
a
g
e
Use of this product and document is subject to acceptance of the terms and conditions
of Cyberoam End User License
|
Agreement (EULA) and Warranty Policy for Cyberoam UTM Appliances.
2
You will find the copy of the EULA at http://www.cyberoam.com/documents/EULA.html
and the Warranty Policy for
Cyberoam UTM Appliances at http://kb.cyberoam.com.
RESTRICTED RIGHTS
Copyright 1999 - 2015 Cyberoam Technologies Pvt. Ltd. All rights reserved. Cyberoam, Cyberoam logo are trademark of
Cyberoam Technologies Pvt. Ltd.
Corporate Headquarters
Cyberoam House,
Saigulshan Complex, Opp. Sanskruti,
Beside White House, Panchwati Cross Road,
Ahmedabad - 380006, GUJARAT, INDIA.
Tel: +91-79-66216666
Fax: +91-79-26407640 Web site: www.cyberoam.com
C
y
b
e
r
o
a
m
C
e
n
t
r
a
l
Page 2 of 31
C
o
n
s
o
l
e
Cyberoam Wireless LAN Configuration Guide
Technical Support
You may direct all questions, comments, or requests concerning the software you purchased, your
registration status, or similar issues to Customer care/service department
at the following address:
P
Corporate Office
Cyberoam Technologies Pvt. Ltd.
901, Silicon Tower
Off C.G. Road
Ahmedabad 380006
Gujarat, India.
Phone: +91-79-66065606
Fax: +91-79-26407640
Web site: www.cyberoam.com
a
g
e
|
3
Cyberoam contact:
Technical support (Corporate Office): +91-79-66065777
Email: support@cyberoam.com
Web site: www.cyberoam.com
Visit www.cyberoam.com for the regional and latest contact information.
Page 3 of 31
Cyberoam Wireless LAN Configuration Guide
Contents
Introduction....................................................................................................................... 5
Appliance Administrative Interfaces ............................................................................... 6
Web Admin Console ........................................................................................................................
6
P
Command Line Interface (CLI) Console ..........................................................................................
7
a
Cyberoam Central Console (CCC) ..................................................................................................
7
g
Web Admin Console ..........................................................................................................................
8
e
Web Admin Language ..................................................................................................................... 8
Supported Browsers ........................................................................................................................
9
|
Login procedure ............................................................................................................................. 10
Log out procedure ..........................................................................................................................
11
4
Menus and Pages .......................................................................................................................... 12
Page ............................................................................................................................................... 14
Icon bar .......................................................................................................................................... 15
List Navigation Controls ................................................................................................................. 16
Tool Tips ........................................................................................................................................ 16
Status Bar ...................................................................................................................................... 16
Common Operations ...................................................................................................................... 17
Cyberoam WLAN ............................................................................................................ 19
Connected Client ............................................................................................................................. 20
View Connection Status ................................................................................................................. 20
Settings............................................................................................................................................. 21
WLAN General Settings ................................................................................................................. 21
Access Point .................................................................................................................................... 23
View the list of Access Points ........................................................................................................ 23
Access Point Parameters .............................................................................................................. 25
Rogue Access Point....................................................................................................................... 28
Discover Access Points ................................................................................................................. 29
Mark Access Point as Rogue ......................................................................................................... 31
Page 4 of 31
Cyberoam Wireless LAN Configuration Guide
Introduction
The Appliances use Layer 8 technology to help organizations maintain a state of readiness against
today's blended threats and offer real-time protection.
P
a
g
Unified Threat Management Appliances offer identity-based
comprehensive security to
e
organizations against blended threats - worms, viruses, malware,
data loss, identity theft; threats
over applications viz. Instant Messengers; threats over secure protocols viz. HTTPS; and more.
|
They also offer wireless security (WLAN) and 3G wireless broadband.
Analog modem support can
be used as either Active or Backup WAN connection for business continuity.
5
The Appliance integrates features like stateful inspection firewall, VPN, Gateway Anti-Virus and
Anti- Spyware, Gateway Anti-Spam, Intrusion Prevention System, Content & Application Filtering,
Data Leakage Prevention, IM Management and Control, Layer 7 visibility, Web Application
Firewall, Bandwidth Management, Multiple Link Management and Comprehensive Reporting over
a single platform.
The Appliance has enhanced security by adding an 8th layer (User Identity) to the protocol stack.
Advanced inspection provides L8 user-identity and L7 application detail in classifying traffic,
enabling Administrators to apply access and bandwidth policies far beyond the controls that
traditional UTMs support. It thus offers security to organizations across layer 2 - layer 8, without
compromising productivity and connectivity.
The Appliance accelerates unified security by enabling single-point control of all its security
features through a Web 2.0-based GUI. An extensible architecture and an IPv6 Ready Gold logo
provide Appliance the readiness to deliver on future security requirements.
The Appliances provides increased LAN security by providing separate port for connecting to the
publicly accessible servers like Web server, Mail server, FTP server etc. hosted in DMZ which are
visible the external world and still have firewall protection.
Layer 8 Security:
The Appliances features are built around its patent pending Layer 8 technology. The Layer 8
technology implements the human layer of networking by allowing organizations control
traffic based on users instead of mere IP Addresses. Layer 8 technology keeps organizations a
step ahead of conventional security solutions by providing full business flexibility and security in
any environment including WI-FI and DHCP.
Note
All the screen shots in this Guide are taken from NG series of Appliances. The feature and functionalities
however remains unchanged across all Cyberoam Appliances.
Page 5 of 31
Cyberoam Wireless LAN Configuration Guide
Appliance Administrative
Interfaces
Appliance can be accessed and administered through:
1. Web Admin Console
2. Command Line Interface Console
3. Cyberoam Central Console
P
a
g
e
|
6
Administrative Access An administrator can connect and access the Appliance through HTTP,
HTTPS, telnet, or SSH services. Depending on the Administrator login account profile used for
access, an administrator can access number of Administrative Interfaces and Web Admin Console
configuration pages.
Appliance is shipped with two administrator accounts and four administrator profiles.
Administrator
Type
Login Credentials
Console Access
Privileges
Super
Administrator
admin/admin
Web
Admin
Console
CLI console
Full privileges for both the
consoles. It provides readwrite permission for all the
configuration
performed
through either of the
consoles.
Default
cyberoam/cyber
Web
Admin
console only
Full privileges. It provides
read-write permission for
all the configuration pages
of Web Admin console.
Note
We recommend that you change the password of both the users immediately on deployment.
Web Admin Console
Web Admin Console is a web-based application that an Administrator can use to configure,
monitor, and manage the Appliance.
You can connect to and access Web Admin Console of the Appliance using HTTP or a HTTPS
connection from any management computer using web browser:
1. HTTP login: http://<LAN IP Address of the Appliance>
2. HTTPS login: https://<LAN IP Address of the Appliance>
For more details, refer section Web Admin Console.
Page 6 of 31
Cyberoam Wireless LAN Configuration Guide
Command Line Interface (CLI) Console
Appliance CLI console provides a collection of tools to administer, monitor and control certain
Appliance component. The Appliance can be accessed remotely using the following connections:
P
a
1. Remote login Utility TELNET login
g
To access Appliance from command prompt using remote e
login utility Telnet, use command
TELNET <LAN IP Address of the Appliance>. Use default password admin.
|
2. SSH Client (Serial Console)
7
SSH client securely connects to the Appliance and performs command-line operations. CLI
console of the Appliance can be accessed via any of the SSH client using LAN IP Address of the
Appliance and providing Administrator credentials for authentication.
Note
Start SSH client and create new Connection with the following parameters:
Host <LAN IP Address of the Appliance>
Username admin
Password admin
Use CLI console for troubleshooting and diagnose network problems in details. For more details,
refer version specific Console Guide available on http://docs.cyberoam.com/.
Cyberoam Central Console (CCC)
Distributed Cyberoam Appliances can be centrally managed using a single Cyberoam Central
Console (CCC) Appliance, enabling high levels of security for Managed Security Service Provider
(MSSPs) and large enterprises. To monitor and manage Cyberoam using CCC Appliance you
must:
1. Configure CCC Appliance in Cyberoam
2. Integrate Cyberoam Appliance with CCC using: Auto Discovery or Manually
Once you have added the Appliances and organized them into groups, you can configure single
Appliance or groups of Appliances.
For more information, please refer CCC Administrator Guide.
Page 7 of 31
Cyberoam Wireless LAN Configuration Guide
Web Admin Console
CyberoamOS uses a Web 2.0 based easy-to-use graphical interface termed as Web Admin
Console to configure and manage the Appliance.
P
You can access the Appliance for HTTP and HTTPS web browser-based
administration from any
a
of the interfaces. Appliance when connected and powered gup for the first time, it will have a
following default Web Admin Console Access configuration foreHTTP and HTTPS services.
Services
Interface/Zones
HTTP
LAN, WAN
HTTPS
WAN
|
8
Default Port
TCP Port 80
TCP Port 443
The administrator can update the default ports for HTTP and HTTPS services from System >
Administration > Settings.
Web Admin Language
The Web Admin Console supports multiple languages, but by default appears in English. To cater
to its non-English customers, apart from English, Chinese-Simplified, Chinese-Traditional, Hindi,
Japanese and French languages are also supported. Administrator can choose the preferred GUI
language at the time of logging on.
Listed elements of Web Admin Console will be displayed in the configured language:
Dashboard Doclet contents
Navigation menu
Screen elements including field & button labels and tips
Error messages
Page 8 of 31
Cyberoam Wireless LAN Configuration Guide
Supported Browsers
You can connect to the Web Admin Console of the Appliance using HTTP or a secure HTTPS
connection from any management computer using one of the following web browsers:
P is 1024 X 768 and 32-bit true xxThe minimum screen resolution for the management computer
a
color.
g
Browser
Supported
e Version
Microsoft Internet Explorer
|
Version 8+
Mozilla Firefox
9
Version 3+
Google Chrome
Safari
Opera
All versions
5.1.2(7534.52.7)+
15.0.1147.141+
The Administrator can also specify the description for firewall rule, various policies, services and
various custom categories in any of the supported languages.
All the configuration done using Web Admin Console takes effect immediately. To assist you in
configuring the Appliance, the Appliance includes a detailed context-sensitive online help.
Page 9 of 31
Cyberoam Wireless LAN Configuration Guide
Login procedure
The log on procedure authenticates the user and creates a session with the Appliance until the
user logs-off.
P
To get to the login window, open the browser and type the LAN
IP Address of Cyberoam in the
a username and password.
browsers URL box. A dialog box appears prompting you to enter
g
e
|
1
0
Screen Login Screen
Screen Element
Description
Enter user login name.
Username
If you are logging on for the first time after installation,
use the default username.
Specify user account password.
Password
Dots are the placeholders in the password field.
If you are logging on for the first time after installation
with the default username, use the default password.
Language
Select the language. The available options are ChineseSimplified, Chinese-Traditional, English, French, and
Hindi.
Default English
To administer Cyberoam, select Web Admin Console
Log on to
To view logs and reports, select Reports.
To login into your account, select My Account.
Login button
Click to log on the Web Admin Console.
Table Login Screen
The Dashboard appears as soon as you log on to the Web Admin Console. It provides a quick and
fast overview of all the important parameters of your Appliance.
Page 10 of 31
Cyberoam Wireless LAN Configuration Guide
Log out procedure
To avoid un-authorized users from accessing Cyberoam, log off after you have finished working.
This will end the session and exit from Cyberoam.
To log off from the Appliance, click the
Admin Console pages.
button located
P at the top right of any of the Web
a
g
e
|
1
1
Page 11 of 31
Cyberoam Wireless LAN Configuration Guide
Menus and Pages
The Navigation bar on the leftmost side provides access to various configuration pages. This menu
consists of sub-menus and tabs. On clicking the menu item in the navigation bar, related
management functions are displayed as submenu items in the navigation bar itself. On clicking
submenu item, all the associated tabs are displayed as the horizontal menu bar on the top of the
P tab.
page. To view a page associated with the tab, click the required
a
g
e clicked on without navigating to a
The left navigation bar expands and contracts dynamically when
submenu. When you click on a top-level heading in the left navigation bar, it automatically expands
|
that heading and contracts the heading for the page you are currently
on, but it does not navigate
away from the current page. To navigate to a new page, first click on the heading, and then click
1
on the submenu you want navigate to. On hovering the cursor upon the up-scroll icon
or the
2
down-scroll icon
, automatically scrolls the navigation bar up or down respectively.
The navigation menu includes following modules:
System System administration and configuration, firmware maintenance, backup - restore
Objects Configuration of various policies for hosts, services, schedules and file type
Networks Network specific configuration viz., Interface speed, MTU and MSS settings,
Gateway, DDNS
Page 12 of 31
Cyberoam Wireless LAN Configuration Guide
Identity Configuration and management of User and user groups
Firewall Firewall Rule Management
VPN VPN and SSL VPN access configuration
IPS IPS policies and signature
Web Filter Web filtering categories and policies configuration
P configuration
Application Filter Application filtering categories and policies
WAF Web Application Filtering policies configuration. aAvailable in all the models except
g
CR15iNG and CR15wiNG.
e
IM IM controls
QoS Policy management viz., surfing quota, QoS, access| time, data transfer
Anti Virus Antivirus filtering policies configuration
Anti Spam Anti Spam filtering policies configuration
Traffic Discovery Traffic monitoring
1
3
Logs & Reports Logs and reports configuration
Note
Use F1 key for page-specific help.
Use F10 key to return to Dashboard.
Each section in this guide shows the menu path to the configuration page. For example, to reach
the Zone page, choose the Network menu, then choose Interface sub-menu from the navigation
bar, and then choose Zone tab. Guide mentions this path as Network > Interface > Zone.
Page 13 of 31
Cyberoam Wireless LAN Configuration Guide
Page
A typical page looks as shown in the below given image:
P
a
g
e
|
1
4
Screen Page
Page 14 of 31
Cyberoam Wireless LAN Configuration Guide
Icon bar
P
a
g
e
|
1
5
The Icon bar on the upper rightmost corner of every page provides access to several commonly
used functions like:
1. Dashboard Click to view the Dashboard
2. Wizard Opens a Network Configuration Wizard for a step-by-step configuration of the
network parameters like IP Address, subnet mask and default gateway for your Appliance.
3. Report Opens a Reports page for viewing various usage reports. Integrated Logging and
Reporting solution - iView, to offer wide spectrum of 1000+ unique user identity-based
reporting across applications and protocols and provide in-depth network visibility to help
organizations take corrective and preventive measures.
This feature is not available for CR15xxxx series of Appliances.
4. Console Provides immediate access to CLI by initiating a telnet connection with CLI without
closing Web Admin console.
5. Logout Click to log off from the Web Admin Console.
6. More Options
follows:
Provides options for further assistance. The available options are as
Support Opens the customer login page for creating a Technical Support Ticket. It is
fast, easy and puts your case right into the Technical Support queue.
About Product Opens the Appliance registration information page.
Help Opens the context sensitive help page.
Reset Dashboard Resets the Dashboard to factory default settings.
Lock Locks the Web Admin Console. Web Admin Console is automatically locked if the
Appliance is in inactive state for more than 3 minutes. To unlock the Web Admin Console
you need to re-login. By default, Lock functionality is disabled. Enable Admin Session Lock
from System > Administration > Settings.
Reboot Appliance Reboots the Appliance.
Shutdown Appliance Shut downs the Appliance .
Page 15 of 31
Cyberoam Wireless LAN Configuration Guide
List Navigation Controls
The Web Admin Console pages display information in the form of lists that are spread across the
multiple pages. Page Navigation Control Bar on the upper right top corner of the list provides
navigation buttons for moving through the list of pages with a large number of entries. It also
includes an option to specify the number entries/records displayed per page.
P
a
g
e
|
1
6
Tool Tips
To view the additional configuration information use tool tip. Tool tip is provided for many
configurable fields. Move the pointer over the icon
to view the brief configuration summary.
Status Bar
The Status bar at the bottom of the page displays the action status.
Page 16 of 31
Cyberoam Wireless LAN Configuration Guide
Common Operations
Adding an Entity
You can add a new entity like policy, group, user, rule, ir host by clicking the Add button available
on most of the configuration pages. Clicking this button either opens a new page or a pop-up
P
window.
a
g
e
|
1
7
Editing an Entity
All the editable entities are hyperlinked. You can edit any entity by clicking either the hyperlink or
the Edit icon
under the Manage column.
Deleting an Entity
You can delete an entity by selecting the checkbox and clicking the Delete button or Delete icon.
To delete multiple entities, select
To delete all the entities, select
individual entity and click the Delete button.
in the heading column and click the Delete button.
Page 17 of 31
Cyberoam Wireless LAN Configuration Guide
P
a
g
e
Sorting Lists
To organize a list spread over multiple pages, sort the list in 1ascending or descending order of a
column attribute. You can sort a list by clicking a column heading.
8
Ascending Order icon
in a column heading indicates that the list is sorted in ascending
order of the column attribute.
Descending Order icon
in a column heading indicates that the list is sorted descending
order of the column attribute.
Filtering Lists
To search specific information within the long list spread over multiple pages, filter the lists.
Filtering criteria vary depending on a column data and can be a number or an IP address or part of
an address, or any text string combination.
To create filter, click the Filter
the Filter icon changes to
icon in a column heading. When a filter is applied to a column,
Configuring Column Settings
By default on every page all columnar information is displayed but on certain pages where a large
number of columnar information is available, all the columns cannot be displayed. It is also
possible that some content may not be of use to everyone. Using column settings, you can
configure to display only those numbers of columns which are important to you.
To configure column settings, click Select Column Settings and select the checkbox against the
columns you want to display and clear the checkbox against the columns which you do not want to
display. All the default columns are greyed and not selectable.
Page 18 of 31
Cyberoam Wireless LAN Configuration Guide
Cyberoam WLAN
Note
P
a
g
e
Wireless Local Area Network (WLAN) is used to associate devices through wireless distribution
|
method and connection to the internet is provided through an access
point.
This section is applicable to Wi-Fi models only.
1
Wi-Fi appliances support three wireless protocols called IEEE9802.11n, 802.11b and 802.11g, and
send data via radio transmissions. By functioning as an Access point, secure wireless gateway
and firewall, it provides real-time network protection and high-speed wireless connectivity.
Apart from the access point for wireless LAN, by integrating with firewall, Wi-Fi delivers
comprehensive protection to small, remote and branch office users from threats like malware,
virus, spam, phishing, and pharming attacks.
Note
All the screen shots in the Cyberoam User Guides are taken from NG series of appliances. The feature
and functionalities however remains unchanged across all Cyberoam appliances.
As WLAN interface is a member of LAN zone:
All the services enabled for the LAN zone from the Appliance Access page are automatically
applicable on WLAN1 and other access points too.
All the firewall rules applied on LAN zone will be applied on WLAN access points too.
Wi-Fi models, by default include one wireless interface called WLAN1.
Limitations
Only one access point can be configured when appliance is deployed in Bridge mode
Alias and VLAN sub-interfaces are not supported for access point interfaces.
Wi-Fi appliances support the following wireless network standards:
802.11n (5 GHz Band)
802.11b (2.4-GHz Band)
802.11g (2.4-GHz Band)
WEP64 and WEP128 Wired Equivalent Privacy (WEP)
Wi-Fi Protected Access (WPA), WPA2 and WPA2 Auto using pre-shared keys
Page 19 of 31
Cyberoam Wireless LAN Configuration Guide
Connected Client
The page displays following details of all the connected Wireless LAN clients.
1. IP Address leased for Wireless connection
2. MAC Address of the device
P
3. Wireless Access Point from which the connection is established
a
g
The Administrator can filter connected clients by searching for
e IP Address, MAC Address or by
access points
|
View Connection Status
2
To view and manage connected WLAN clients, go to Network
> Wireless LAN >
0
Connected Client.
Screen View Connection Status
Screen Element
Description
Leased IP Address
IP Address leased for Wireless connection.
MAC Address
MAC Address of the device
Access Point
Wireless Access Point from which the connection is
established
Table View Connection Status screen elements
Page 20 of 31
Cyberoam Wireless LAN Configuration Guide
Settings
The page allows general configuration of Wireless LAN connection.
By default, Wi-Fi appliances include one wireless interface, P
called WLAN1 and additional seven
interfaces can be added. All wireless interfaces use the same
a wireless parameters and hence
there is no need to configure different settings for each interface.
g
e
WLAN General Settings
2 LAN > Settings.
To configure WLAN connection, go to Network > Wireless
1
Screen WLAN General Settings
Screen Element
Description
WLAN Radio
Click to enable WLAN
Wireless Protocol
Select the Wireless Protocol to be used.
802.11b/g/n
802.11g/n
802.11b/g
802.11n
802.11g
Geography
Channel
802.11b
Select your country or location. This determines which
channels will be available for your network
Select a channel for your wireless network.
Available channel options are based on the Geographical
location you selected.
Transmission Power
Default Auto
Select power level of the radio signal transmission, higher the
number, larger the area CR15wi will broadcast. For example,
Page 21 of 31
Cyberoam Wireless LAN Configuration Guide
if you want signal to go from building-to-building, select Full
Power and if you want to keep the wireless signal to a small
area, select minimum.
.
Available Options:
Full Power
Half (-3 dB)
Quarter (-6 dB)
Eighth (-9 dB)
Minimum
P
a
g
e
|
2
Default - Full Power
2 signal to the WLAN.
Full power sends the strongest
Beacon Interval
Specify the time interval between two beacon packets to be
sent.
Beacon Packets - Access Points broadcast Beacons to
synchronize wireless networks. For faster connectivity, select
lower time interval. However, lower time interval will increase
the number of beacons sent. While this will make it quicker to
find and connect to the wireless network, it requires more
overhead, slowing the throughput.
Default - 100 milliseconds
Acceptable Range: 100 1024 milliseconds
Specify the threshold time before the RTS frames are sent.
RTS Threshold
The RTS threshold is the maximum size, in bytes, of a packet
that the appliance will accept without sending RTS/CTS
packets to the sending wireless device.
If network throughput is slow or a large number of frame
retransmissions are occurring, decrease the RTS threshold to
enable RTS clearing.
Fragmentation Threshold
Default - 2347
Acceptable Range - 1 to 2347
It is the maximum size of a data packet before it is broken into
smaller packets, reducing the chance of packet collisions.
Appliance will allow specified number of bytes of fragmented
data in the network.
If the packet size is larger than the threshold, packets will be
fragmented before transmission.
Default - 2346
Acceptable Range: 256 2346
Table WLAN General Settings screen elements
Page 22 of 31
Cyberoam Wireless LAN Configuration Guide
Access Point
Wi-Fi models, by default include one wireless interface called WLAN1 and support up to seven
additional wireless interfaces to be configured as Access Points. All the configured access points
use the same wireless parameters.
P
a
Limitations
g
Only one access point can be configured when appliance ise deployed in Bridge mode.
|
View the list of Access Points
2
3
To manage access points, go to Network > Wireless LAN > Access Point.
Screen Manage Access Point
Screen Element
Description
Name
Displays the name of the Access Point.
Zone
Displays the Zone of Access point.
Access point can be the member of LAN zone only.
IP Address
Displays IP Address and netmask for the access point.
If appliance is deployed as Bridge, IP Address will not be
displayed.
SSID
Displays the unique Service Set Identifier (SSID) for
broadcast.
The access point is identified by its SSID. The access point
sends broadcast messages advertising its SSID for the
receiver to acknowledge and use the Internet through that
access point.
Security Mode
Security Mode selected.
Available Options:
None
WEP-Open
WEP-Shared
WEP-Auto
WPA PSK
WPA2-PSK
Page 23 of 31
Cyberoam Wireless LAN Configuration Guide
WPA-WPA2-PSK-Auto
WPA-Enterprise
WPA2-Enterprise
Table Manage Access Point screen elements
Note
Default Access Point cannot be deleted.
P
a
g
e
|
2
4
Page 24 of 31
Cyberoam Wireless LAN Configuration Guide
Access Point Parameters
To add or edit access points, go to Network > Wireless LAN > Access Point. Click Add
Button to add a new access point. To update the details, click on the access point or Edit icon
in the Manage column against the access point you want to modify.
P
a
g
e
|
2
5
Screen Add Access Point
Screen Element
Description
Zone
Select Zone for the Access Point.
Access Point can be the member of LAN zone only.
IP Address
Specify IP Address for the Access Point.
Netmask
Specify subnet mask.
SSID
Specify Service Set Identifier (SSID).
The access point is identified by its SSID. Users who want to
use the wireless network must configure their computers with
this SSID.
Broadcast SSID
Enable to broadcast the SSID.
Security Mode
Broadcasting the SSID enables clients to connect to your
wireless network without knowing the SSID. For security
purpose, do not broadcast the SSID as there will be less
chances of an unwanted user connecting to your wireless
network. If you choose not to broadcast the SSID, you need to
forward SSID to your users so that they can configure their
wireless devices.
Select the security mode for encrypting the wireless traffic.
Available Options:
None
Page 25 of 31
Cyberoam Wireless LAN Configuration Guide
WEP-Open
WEP-Shared
WEP-Auto
WPA PSK
WPA2-PSK
WPA-WPA2-PSK-Auto P
a
WPA-Enterprise
g
WPA2-Enterprise
e
|
WPA mode is better for security than WEP mode.
For WEP-Open, WEP-Shared and WEP-Auto only
Key Entry
Select Key entry mode
2
6
Available Options:
ASCII
Hexadecimal
Key Length
Select the length of security key. A longer key length ensures
better security.
Available Options:
64 bit
28 bit
Key
Specify security key for authentication.
Maximum Clients
Specify the maximum number of clients that are allowed to
connect across all the access points simultaneously.
Default 255
Maximum Clients allowed range: 1 - 255
For WPA PSK, WPA2-PSK and WPA-WPA2-PSK-Auto only
Encryption
Select the Encryption type.
Available Options:
TKIP Temporal Key Integrity Protocol
AES Advanced Encryption Standard
Auto
Pass Phrase
Specify the phase to be used as password
Pass Phrase range: 8 63 characters
Group Key update
Enable the Group Key Update checkbox to generate new
security key after the configured timeout interval.
Timeout Interval
Specify the timeout interval for generating security key.
Maximum Clients
Specify the maximum number of clients that are allowed to
connect across all the access points simultaneously.
Default 255
Maximum Clients allowed range: 1 - 255
For WPAEnterprise and WPA2-enterprise
Page 26 of 31
Cyberoam Wireless LAN Configuration Guide
Encryption
Select the Encryption type.
Available Options:
TKIP Temporal Key Integrity Protocol
Server IP & port
Shared Secret
Backup Server IP and
Port
Shared Secret
Maximum Clients
Intra SSID Traffic
AES Advanced Encryption Standard
P
Auto
a
IP Address and Port number gof the primary RADIUS server.
Password with which primaryeRADIUS server can be
accessed.
IP Address and Port number |of the backup RADIUS server.
2
Password with which backup RADIUS server can be
7
accessed.
Specify the maximum number of clients that are allowed to
connect across all the access points simultaneously.
Default 255
Maximum Clients allowed range: 1 - 255
Select to configure Wi-Fi Client isolation.
Available Options:
Allow Select to allow communication between Wi-Fi
clients.
Drop Select to configure complete isolation. In complete
isolation, Wi-Fi Clients cannot communicate with each
other.
Firewall Select to customize isolation. Administrator can
allow/deny traffic of specific services between the wireless
clients through firewall rule.
Default - Allow
Table Add Access Point screen elements
Page 27 of 31
Cyberoam Wireless LAN Configuration Guide
Rogue Access Point
A Rogue Access Point (AP) is any Wi-Fi access point connected to your network without
authorization. It can be a setup used by an attacker for the purpose of sniffing wireless network
traffic i.e. to conduct a man-in-the-middle attack. It allows anyone with a Wi-Fi-equipped device to
connect to your corporate network, leaving your IT assets wide open for the casual snooper or
P
criminal hacker.
a
g
Appliance can alleviate this by recognizing rogue access points
potentially attempting to gain
e
access to your network.
|
To discover rogue access points and authorize access points, go to Network > Wireless
2
LAN > Rogue AP scan. You can:
8
Scan for nearby access points
Authorize AP
Mark AP as Rogue
Click "Schedule system-triggered scan" to enable a schedule for Rogue AP Scan. You can
select from the pre-defined schedules or create a custom schedule.
Screen General Settings
Screen Add Schedule
Page 28 of 31
Cyberoam Wireless LAN Configuration Guide
Discover Access Points
To increase the security capabilities and identify the unauthorized APs, Wireless appliances
provides scanning capability by which nearby APs can be discovered and administrator can take
countermeasures against the most common types of illicit wireless activity.
P
Go to Network > Wireless LAN > Rogue AP scan
to manually scan or schedule
a
scanning for the automatic discovery of APs. To schedule the
g scanning, enable schedule based
scanning and select the schedule. To manually scan, click Scan
e Now.
|
If you are scanning for the first time, after enabling Wireless LAN, all the discovered APs will be
listed in Unrecognized Access Points table. Scanning result is displayed in the form of 3 tables:
2
9
Unrecognized Access Points
Screen Unrecognized Access Points
Table lists all the discovered nearby APs and displays following information:
Channel - The radio channel used by the access point.
BSSID - The MAC Address of the radio interface of the detected access point.
SSID - The radio SSID of the access point.
Signal Strength - The strength of the detected radio signal
Security Mode - Mode for encrypting the wireless traffic
Wireless Mode Wireless protocol
Action Click the icon
Click the icon
to mark the AP as authorized AP and move in the Authorized AP table.
to mark the AP as Rogue AP and move to the Rogue AP table.
Rogue Access Points
Screen Rogue Access Points
Table lists all the APs marked as Rogue and displays following information:
Channel - The radio channel used by the access point.
BSSID - The MAC Address of the radio interface of the detected access point.
SSID - The radio SSID of the access point.
Signal Strength - The strength of the detected radio signal
Security Mode - Mode for encrypting the wireless traffic
Wireless Mode Wireless protocol
Page 29 of 31
Cyberoam Wireless LAN Configuration Guide
Action Click the icon
Click the icon
to mark the AP as authorized AP and move in the Authorized AP table.
to mark the AP as unrecognized AP and move to the Unrecognized AP table.
Authorized Access Points
P
a
g
e
Screen Authorized Access Points
|
3
Table lists all the APs marked as Rogue and displays following information:
0
Channel - The radio channel used by the access point.
BSSID - The MAC Address of the radio interface of the detected access point.
SSID - The radio SSID of the access point.
Signal Strength - The strength of the detected radio signal
Security Mode - Mode for encrypting the wireless traffic
Wireless Mode Wireless protocol
Action Click the icon
table. Click the icon
to mark the AP as unrecognized AP and move to the Unrecognized AP
to mark the AP as Rogue AP and move to the Rogue AP table.
Authorize Access Points
All the discovered Access Points detected are regarded as unrecognized until they are identified
as authorized for operation. To authorize an access point, click the icon
marked as authorized in the Unrecognized AP table.
against the AP to be
Page 30 of 31
Cyberoam Wireless LAN Configuration Guide
Mark Access Point as Rogue
All the discovered Access Points detected are regarded as unrecognized until they are identified
as authorized or rogue for operation. To mark an access point as rogue, click the icon
the AP to be marked as rogue in the Unrecognized AP table.
P
a
g
e
against
|
3
1
Page 31 of 31
Вам также может понравиться
- EMC Vnxe3200 Best Practices For Performance WPДокумент27 страницEMC Vnxe3200 Best Practices For Performance WPPeter AyimОценок пока нет
- Cacti On Windows Using Wamp A1Документ41 страницаCacti On Windows Using Wamp A1bagassafaОценок пока нет
- Cyberoam PresentationДокумент88 страницCyberoam PresentationPeter AyimОценок пока нет
- CCSM Assignment March 2012 FinalДокумент9 страницCCSM Assignment March 2012 FinalPeter Ayim100% (1)
- 10rules To Manage Your BossДокумент18 страниц10rules To Manage Your BossPeter AyimОценок пока нет
- Server GuideДокумент308 страницServer GuideRaja KumaravelОценок пока нет
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- Revision Control:: Cable Wireless Business Gateway - CGA2121Документ28 страницRevision Control:: Cable Wireless Business Gateway - CGA2121korajlicОценок пока нет
- Throughput Enhancement of IEEE 802.11 WLAN For Next Generation CommunicationsДокумент68 страницThroughput Enhancement of IEEE 802.11 WLAN For Next Generation Communicationsnurcoe1902100% (1)
- UT-9061 User ManualДокумент36 страницUT-9061 User ManualCamelot colindresОценок пока нет
- DS3 Admin Manua Version 15 - 2Документ55 страницDS3 Admin Manua Version 15 - 2AjmiОценок пока нет
- TL Wn620g PanduanДокумент29 страницTL Wn620g PanduanClams MostОценок пока нет
- (Step by Step) Dos Attack On Router (Wireless Network Wi)Документ9 страниц(Step by Step) Dos Attack On Router (Wireless Network Wi)László LОценок пока нет
- Wireless Technology Research PaperДокумент6 страницWireless Technology Research Paperp0zikiwyfyb2100% (1)
- UNM2000 Training PDFДокумент77 страницUNM2000 Training PDFcukjaya100% (1)
- Ambicom Wl11-Sd Wireless Lan SD CardДокумент28 страницAmbicom Wl11-Sd Wireless Lan SD Card林亮劼Оценок пока нет
- DS FitCon 100Документ3 страницыDS FitCon 100Terrel YehОценок пока нет
- Test Bank For Business Data Networks and Security 11th Edition 11th EditionДокумент25 страницTest Bank For Business Data Networks and Security 11th Edition 11th Editionthomasbrownmjtbonysgk100% (25)
- Juniper - Mist AP21 Access Point SeriesДокумент4 страницыJuniper - Mist AP21 Access Point SeriesBullzeye StrategyОценок пока нет
- B Cisco Business Wifi 6 Admin GuideДокумент182 страницыB Cisco Business Wifi 6 Admin GuideiziОценок пока нет
- Multicast Design Solutions - Multicast-Enabled Clinical Networks - Cisco Press Book ChapterДокумент37 страницMulticast Design Solutions - Multicast-Enabled Clinical Networks - Cisco Press Book ChapterwijitharОценок пока нет
- How To Configure Long Distance PTP Connection With OMR 32 and 11Документ15 страницHow To Configure Long Distance PTP Connection With OMR 32 and 11Cres AlvaradoОценок пока нет
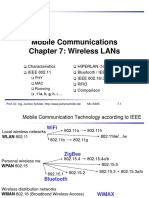
- Mobile Communications Chapter 7: Wireless LansДокумент47 страницMobile Communications Chapter 7: Wireless LansGrandhe HarshavardhanОценок пока нет
- Router AWAP608 ManualДокумент31 страницаRouter AWAP608 ManualMy doksОценок пока нет
- SL GuiДокумент946 страницSL GuirakawidОценок пока нет
- TR 5a v2.2Документ92 страницыTR 5a v2.2ulperezОценок пока нет
- Nebula - 150 User ManualДокумент94 страницыNebula - 150 User ManualSamuel MongeОценок пока нет
- Z7Z6NWG (En) 01Документ62 страницыZ7Z6NWG (En) 01Zlatko OžanićОценок пока нет
- Cheat Sheets NetworkingДокумент28 страницCheat Sheets NetworkingClaudio StroeОценок пока нет
- WLR 510 - 115x83 UkДокумент19 страницWLR 510 - 115x83 UkJuan Francisco Palomeque GonzálezОценок пока нет
- AgvДокумент75 страницAgvHarikrishna MuchalaОценок пока нет
- Troubleshooting Guide For Wireless ClientsДокумент22 страницыTroubleshooting Guide For Wireless ClientsLeonardo SuarezОценок пока нет
- IEEE 802.11: Mobility and Evolutions: 4Tc - ArmДокумент31 страницаIEEE 802.11: Mobility and Evolutions: 4Tc - ArmdocteurgynecoОценок пока нет
- Pwnie Express User Manual: PWN Plug R3 Fixed SensorДокумент32 страницыPwnie Express User Manual: PWN Plug R3 Fixed SensorSamir GasimovОценок пока нет
- EC6802 Wireless NetworksДокумент81 страницаEC6802 Wireless Networksg ezhilОценок пока нет
- LAB Manual Tech Support DSL BroadbandДокумент41 страницаLAB Manual Tech Support DSL BroadbandWaleed AhmadОценок пока нет
- APC Button AF 5.95 UG PDFДокумент77 страницAPC Button AF 5.95 UG PDFRemis TОценок пока нет