Академический Документы
Профессиональный Документы
Культура Документы
105902-9393 Ijet-Ijens
Загружено:
KhairulОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
105902-9393 Ijet-Ijens
Загружено:
KhairulАвторское право:
Доступные форматы
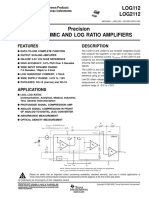
International Journal of Engineering & Technology IJET-IJENS Vol:10 No:02
55
A Proposed Model for Optimizing the Flow of
Pilgrims between Holy Sites During Hajj Using
Traffic Congestion Control
Omar Tayan
{otayan@tai bahu.edu.sa}
College of Computer Science and Engineering,
Department of Computer Science, Taibah University, K.S.A.
Abstract The use of computer simulations for modeling the
behavior of pre-existing/inaccessible products/real-life scenarios
is increasing in academia and industry. The advantages of
computer modeling and simulation are numerous, and include;
controlled experimentation on a pre-existing/in-accessible reallife scenario without disturbing the real -life system, time- and
space-compression of a real-life system and sensitivity analysis of
selected key parameters. The need for such advanced
computational techniques for behavioral analysis is increasing in
the domain of traffic congestion and control, which has
particular significance in an attempt to optimize the
movement/flow of traffic in various applications. This study is
particularly concerned with optimizing the flow of pilgrims
between Holy sites during the Hajj period, which remains a
relatively unexplored optimization problem of key significance
for the well-being of approximately three-million people each
year. The aim of this study is to introduce a new model for
optimizing the flow/transportation of pilgrims between the
various Holy sites through the deployment of existing techniques
in a new application-domain. Mature computer-science literature
are considered here for modeling the Makkah road network
using the widely applicable concept of queuing and polling
systems from computer science and engineering. A further
contribution of this paper is that key benefits are obtained by
employing a distributed approach to traffic management,
including increased efficiency of the available road network,
thereby resulting with a decrease in the delays encountered and
pollution emitted as a consequence of the inefficient flow of
traffic.
Index Term-- congestion-awareness algorithm, congestion
control, modeling, wireless sensor network application.
I.
INTRODUCTION
Significant progress in computer modeling and
simulation techniques are paving the way for the widespread
use of highly efficient computational techniques for modeling
inaccessible artifacts/real-life scenarios and determine whether
a planned change to the artifact/scenario can be implemented
while producing the desired results. For instance, the use of
computer simulations for modeling the behavior of p reexisting/inaccessible products/real-life scenarios is expected to
increase in academia and industry. Numerous advantages
emerge through the use of modeling and simulation, including,
controlled experimentation on an pre-existing/in-accessible
real-life scenario without disturbing the real-life system, timeand space-compression of a real-life system and sensitivity
analysis of selected key parameters.
Hence, computer modeling and simulation is an
attractive option and is particularly well-suited for numerous
applications that include: banks, hospitals, airports,
manufacturing systems, and computer and communication
systems. The importance of computer modeling and
simulation is that they can be used to optimize management
decisions made prior to implementing any change in a real-life
scenario/artifact, thereby resulting in cost, time and resource
optimization. The need for such advanced computational
techniques for behavioral analysis is increasing in the domain
of traffic congestion and control, which has particular
significance in the attempt to optimize the movement/flow of
pilgrims between Holy sites on the Makkah road network
during the Hajj period. The following sections provide an
overview description of the problem domain, the applied
methodology and a proposed model for the design and
implementation of a fair congestion-aware access protocol for
potential deployment onto key sites during the annual Hajj.
II. M OTIVATION AND OVERVIEW
A key aim of this study is to introduce models that
optimize the flow/transportation of pilgrims between the
various Holy sites through the use of sophisticated computer
modeling and simulation techniques. Modeling techniques are
considered here in order to simulate the Makkah road network
using the widely applicable concept of queuing and polling
systems from computer science and engineering. The use of
such modeling techniques in this study is imperative, thereby
allowing much of the relevant computer networking literature,
including standard and adapted/optimized protocols, to be
applied with great effect in this study. Makkahs road network
can then be modeled with the application of
standard/optimized and novel medium access (fairness)
protocols, in which multiple access points onto the road
network1 are modeled as nodes/queues in the queuing system
that compete for access to some shared resource (modeled as
servers). For example, an example of this scenario is observed
(Fig. 1) when several branch roads converge into a single
road/fewer roads.
1
In reality, wireless sensor networks (WSNs) would be employed to
measure the traffic levels at traffic points - illustrated using red circles in
Fig.2.
10 59 02 -9393 IJET-IJENS April 2010 IJENS
IJEN S
International Journal of Engineering & Technology IJET-IJENS Vol:10 No:02
Fig. 1. A map-view of the Makkah road network highlighting competing
access to a shared resource (map-image obtained from [11]).
The study compares a number of potential transport
protocols suitable for the Hajj environment, before justifying
the most appropriate/efficient protocol that optimizes the flow
of pilgrims between the various Holy sites. Hence, it is
evident that this study is highly significant in any effort to
manage the traffic flow of pilgrims and therefore provides
much potential for application. Key benefits would be
obtained by employing a distributed scheme to traffic
management, including increased efficiency of the available
road network, thereby resulting with a decrease in the delays
encountered and pollution emitted as a consequence of the
inefficient flow of traffic.
A number of related research-approaches have been
considered for the problem of traffic management, with the
most notable being the use of traffic lights with sensor devices
that open the gate for incoming traffic based on some
parameter value [1]. Such an approach is comparable to
intermediate routing in a queuing system. On the contrary, the
model presented here applies the concept of queuing systems
in order to evaluate a novel distributed approach that provides
a medium access (fairness) mechanism for traffic at key entry
points in addition to intermediate points within the road
network. This study aims to investigate the performance of
various protocols in terms of achieving the most
efficient/optimal road access/utilization mechanism, in which
performance is considered as the average waiting times of
pilgrims within each queue and within the system as a whole
from the point of entry to the point of exit on the road
network. Hence, this study focuses on congestion awareness
algorithms for Hajj traffic on the Makkah road network.
III. M ETHODOLOGY AND DESIGN
This study considers the use of queuing and polling
systems in order to construct an abstract model of the traffic
flow between Holy-sites in Makkah during the Hajj season.
The following discussion examines the significance of
queuing and polling systems in this study.
Polling systems have been studied extensively since
56
several decades ago, and consequently, a rich source of
knowledge has emerged in the use of polling models for a
variety of applications. Polling is a process whereby a
token/query is issued and broadcast to all networked nodes in
order to receive status information of each node [2] and
thereby determine which node is most eligible for access to a
shared-medium based on some medium-access control
scheme. Essentially, all polling systems consist of a single
source that is shared between multiple access queues [3, 4].
Fig. 2 shows a similar scenario in the study of Hajj traffic
flow and congestion control, whereby many frequently used
sections in the road network involve numerous roads merging
into a single road as a point-of-entry into a particular site.
A large number of studies can be found on the use of
polling systems to model a variety of applications in many
disciplines. Much literature exists on the use of polling
systems for modeling token-passing communication networks
with various polling schemes [2, 14], and is also found in the
modeling of more general applications involving the 'multipleaccess' problem for a shared resource [13]. In all the relevant
literature surveyed, polling systems were broadly classified
according to following characteristics that include [4, 8, 9];
continuous- or discrete-time systems, queuing buffer capacity,
queue service discipline, switch-over times, symmetric or
asymmetric properties, cyclic/non-cyclic service order
discipline, exact or approximate analysis. The characteristics
of the polling system used to model the Hajj traffic scenario is
considered in more detail.
First, the polling system comprises a number of source
generation processes to represent the incoming arrival traffic
Fig. 2. Overview of a simplified recurring scenario in the Hajj T raffic
Congestion
/pattern from numerous roads as in a multi-queue system,
leading to a single/or fewer roads, considered as the shared
medium that provides access to a Holy site. Fig. 2 shows a
server attending each of the queues as they compete for
access to a shared road/medium. Pilgrim vehicles, including
buses, cars/vans etc, are modeled as variable-length
container objects in the model, as opposed to modeling the
movement of masses of individuals, and thereby avoiding
ambiguities in statistical data requirements and essential
modeling assumptions. Hence, incoming traffic can be
10 59 02 -9393 IJET-IJENS April 2010 IJENS
IJEN S
International Journal of Engineering & Technology IJET-IJENS Vol:10 No:02
classified as discrete-event arrivals.
The exhaustive (followed by the gated scheme) is the most
efficient service discipline when finite queue-lengths are
used (as required in this study). Polling systems are
associated with server switch-over times that correspond to
the time interval between the service completion time at a
queue, and the cons equent arrival time of the free token at
the next transmitting queue. In this study, the arrival rates,
service time distributions, and switch-over time distributions
are non-uniform between queues as in an asymmetric
system.
Cyclic service-order disciplines are used by the
server to allow data-gathering/request packets to rotate
between the competing stations in order to collate current
queue occupancy values, rate-of-arrivals, rate-of-departures
etc statistics from each station. Cyclic polling systems
employ a round-robin algorithm and a single server that
serves multiple container objects (gated or exhaustive
disciplines) on each queue visit. On the other hand, a non cyclic service-order discipline is required to serve queues
randomly, based on station requests for instance. Hence, the
dynamic service-order of queues can be classified as a
probabilistic polling scheme employing distributed and
stochastic algorithms, depending on the system state. For
instance, a service policy of particular interest in this study
is to observe the contents of each queue with the decision of
service allocation determined based on the highest queue
occupancy. An advantage of dynamic service orders is that
they are sensitive to the actual system state.
An alternative approach to dynamic service orders
would be to employ queue priority schemes. Queue service
mechanisms permit the prioritization of queues according to
key design parameters, thereby achieving improved system
performance. Important design parameters in such systems
include; visit order used, the frequency and duration of visits
at queues and the order of packet/message service within each
queue.
The operation of the proposed polling system is as
follows. Initially, the study aims to focus on modeling the
convergence of the road network from Mina to Arafat,
followed by Arafat to Muzdalifah, pending on the availability
of statistical data. However, it is noted that the convergence
scenario could be modeled more generally by observing that
any number of converging roads (modeled as queues or
stations/nodes) compete for access to a single/fewer point(s)
of entry, as in a cyclic interconnection of nodes towards a
single/fewer server(s). Thereafter, a request packet circulates
through the network of stations/nodes in a cyclic discipline in
order to obtain the necessary statistical data representing the
state of each node. The data collected describing the state of
the system is then used to serve a particular queue based on
queue-occupancy. Evidently, the engineering characteristics/
design of Makkahs roads between particular sites -of-interest
have a significant effect on the design of the model. For
instance, as the width of any convergent road increases (as in
10 59 02 -9393
57
the left of Fig. 2), the queue lengths decrease before attaining
the same queue-occupancy threshold. This scenario
effectively demonstrates the case where each road may
possess multiple lanes of traffic. Hence, for purposes of
medium access fairness, this study considers the queueoccupancy values/threshold without regard to the queuelengths in order to account for the varying dimensions of road
designs. As the circulating packet updates the state
information, the system determines the most eligible queue or
service on the next switch-over. Notably, the stochastic
service discipline employed resembles the random polling
schemes used in many stochastic data-traffic computernetwork models [8].
IV. DESIGN AND IM PLEM ENTATION
In the proposed protocol, access fairness to the road
resources is achieved by regulating traffic flow using a
distributed view of the queue loadings, whereby all affected
nodes are able to support/oppose required queue-flow services
[5, 8, 9]. Hence, the queuing model implementation must
allow intermediate nodes to decide whether they support or
oppose/reject each proposed queue-flow. The protocol would
then accept or reject, the proposed queue-flow by considering
its own local perception of the loading at the queue and the
stance taken by each affected node. Advantageously,
distributed protocols can be employed to establish queue-flow
request services, thereby removing the need for a central
management node. In this approach, the packet request
structure consists of M partitions, each corresponding to one
node, with the request packet circulating between the road
Fig. 3.
T oken-format that circulates between converging road accesspoints
access points as in a logical interconnection of ring nodes
(Fig. 3). Each partition is an N-bit binary counter that counts
the number of opposition-nodes encountered by each
(queue/station) flow request. N is the bit-length of each
request in the request field of the packet, relative to the
queuing-network size, 2N 1 . Hence, an N-bit counter is
required for each node in a 2( N 1)-node circular-road access
network, where each subfield is initialized to the reset state
(e.g. 000 for an interconnection of 4-nodes), indicating no
requests waiting. Fig. 3 illustrates the request-token/packet
format that circulates between converging roads/no des,
designated for use with inter-connected communicating
wireless sensor nodes and base stations. In practice, the
proposed congestion-awareness protocol would then be
applied as the medium access sub-layer that uses statistical
data obtained from the wireless sensor nodes for intelligently
IJET-IJENS April 2010 IJENS
IJEN S
International Journal of Engineering & Technology IJET-IJENS Vol:10 No:02
controlling traffic light signals between the competing access
points. Therefore, the main hardware requirements incurred
here would involve the costs for the wireless sensor network,
comprising wireless sensor nodes and base/field stations,
connected to an end-user/server for data-processing and datastorage/retrieval. A similar concept of employing wireless
sensor networks for data-monitoring applications has
previously emerged in the literature and include; vehicle
monitoring
applications
[15],
industrial-monitoring
applications [16] and wild-land cultural heritage sites
monitoring [17].
When a node transmits a connection request, it sets its
subfield to a binary 100. A reset value (000) at the request
field is only obtained at initialization or when no request was
sent; the reset value (000) cannot otherwise be obtained
regardless of the number of rejections made. Each rejectrequest on a request subtracts from the correct value of the
field associated with the request. Hence, the maximum
number of rejections made on any request would only reduce
the request subfield to 001. A clear benefit of this approach is
that the cell collects more management information regarding
the state of the network nodes as it circulates through the ring.
Furthermore, by counting the number of rejections on each
request, it has become possible to consider other factors for
deciding upon flow-request acceptance or rejection at each
source-node/queue-access-point. For example, in a network
whose access nodes are prioritized, it may be necessary that
high priority nodes/access -points are able to proceed with a
flow-request acceptance even after a majority of nodes have
rejected the request. Hence, this approach provides a
distributed-view of the state of competing roads/stations
through control/management information from the sensor
nodes deployed at access-points to a shared road. Thereafter, a
decision can be made on an order of service of the competing
access-stations/queues (either manually or using automation)
according to some selected parameter(s) such as instantaneous
and average queue-lengths or average queuing-delays for
instance.
This section also proposes an enhanced extension of the
above congestion-awareness protocol which conveys precise
details of nodes with opposing signals for each flow-request in
the system. Advantageously, such a system enables precise
data-gathering statistics regarding the state of each node at
any point in time. However, the resultant complex requestpacket structure associated with this protocol entails the
drawbacks of significantly extra logic (electronic) circuitry for
processing, loss of simplicity and increased-costs, rendering
this enhanced protocol less -efficient overall for the target
application-domain.
V. DISCUSSION AND CONCLUSION
The previous section has described a new approach that
provides a traffic-congestion awareness protocol, in which the
number of rejections on each queue-flow request is monitored
to yield a greater insight of the state of each node. Initial work
on the congestion-awareness protocol considers the effect of
varying the number of proposed node-rejections for each
58
queue-flow request before blocking the request, the effect of
varying queue-thresholds (maximum permitted number of
container objects before requesting to release traffic - queueflow), and the effect of varying the number of container
objects to release following a queue-flow request acceptance.
It is expected that as the queue-loadings and queue arrivalrates increase, more nodes shall propose to reject other queueflow requests in order to prevent their queues exceeding the
queue-threshold. Furthermore, it is expected that if the
rejection-threshold was increased (such that more proposed
rejections are required for each queue-flow in order to block
the request), traffic throughput would also increase with a
slight increase of the mean delay at each node/queue. An
increase in the queue-length threshold was expected to yield
an increase in the mean queuing delays encountered, whilst
reducing the number of proposed rejections for each queueflow request.
In short, this study has investigated access control and
fairness protocol for Makkahs road network between Holy
sites during the significant annual event of Hajj. A fair
mechanism of controlling road access and preventing node
starvation, whilst limiting the delay in the network could be
achieved using the proposed traffic congestion -awareness
protocol.
REFERENCES
[1] Intelligent system for the management of traffic lights in Medina , K.
AlAwfi, Proceedings of the Second Scientific Research Forum on
Madinah Al-Munawwarrah, Madinah Al-Munawwarrah, 2008.
[2] Optimal Polling in Communication networks, A.A. Rescigno, IEEE
T ransactions on Parallel and Distributed Systems, Vol. 8, Issue 5, 1997.
[3] Teletraffic Theory and Applications , H. Akimaru, K. Kawashima,
Published by Springer 1999.
[4] Queuing Analysis of Polling Models, H. T akagi, Proceedings of ACM
Computing Surveys, Vol. 20, No. 1, March 1988.
[5] Traffic Regulation and Control in the Manhattan Street Network , O.
T ayan, D. Harle, Proceedings of Networking 2004, T hird International
IFIP-T C6 Networking Conference, Athens, May 2004.
[6] Electronic Tracking of Pilgrims, Proceedings of the Second Scientific
Re-search Forum on Madinah Al-Munawwarrah, Madinah AlMunawwarrah, 2008.
[7] Traffic Engineering Analysis , chapter 6, in Kutz, M., Handbook of
T ransportation Engineers, Abdulhai, B., Kattan, L., McGraw Hill
Publishing, ISBN: 0071391223, November, 2003.
[8] Waiting Time Estimates in Symmetric ATM- Oriented Rings with the
Destination Release of Used Slots, M. Zafir-Vukotic, IEEE/ACM
T ransactions on Networking, Volume 7, Number 2, April 1999, pp251 261.
[9] Exemplar High-Speed Network Architectures: A Modern Approach to
Networking, O. T ayan, Lambert Academic Publishers, Published
December 2009.
[10] Polling Systems: Modeling and Optimization, H. Levy and M. Sidi,
IEEE T ransactions on Communications, Vol. 38, No. 10, October 1990.
[11] Makkah Map-View Image, http://www.hajis.co.uk/images/popups/maps/makkahmap.gif, <last accessed 5/4/10>.
[12] Ubiquitious Computing for Safe and Efficient Pilgrimage Operations, E.
Abuelela, Proceedings of the Second Scientific Research Forum o n AlMadinah Al-Munawwarrah, Madinah Al-Munawwarrah, 2008.
[13] On the performance of protocols for collecting responses over a
multiple-access channel, M.H. Ammar, G.N. Rouskas, IEEE
T ransactions on Communications, Vol. 43, Issue 234, 1995.
[14] Polling systems with server timeouts and their application to token
passing networks, E. De Souza e Silva, H.R. Gail, R.R. Muntz, IEEE
T ransactions on Networking, Vol. 3, Issue 5, 1995.
[15] A Vehicular Monitoring System with Power-Efficient Wireless Sensor
Networks, Jatuporn Chinrungrueng, Udomporn Sununtachaikul, Satien
10 59 02 -9393 IJET-IJENS April 2010 IJENS
IJEN S
International Journal of Engineering & Technology IJET-IJENS Vol:10 No:02
59
T riamlumlerd, Proceedings of the 6 th International Conference on IT S
T elecommunications, 2006.
[16] Performance Measurements of CSMA/CA-Based Wireless Sensor
Networks for Industrial Applications, M. Bertocco, G. Gamba, A. Sona,
S. Vitturi, Proceedings of the Instrumentation and Measurement
T echnology Conference, 2007.
[17] A Wireless Sensor System for Long-Term Microclimate Monitoring in
Wildland Cultural Heritage Sites, Xia Ming, Dong Yabo, Lu Dongming,
Xue Ping, Liu Gang, Proceedings of the International Symposium on
Parallel and Distributed Processing with Applications, 2008.
10 59 02 -9393 IJET-IJENS April 2010 IJENS
IJEN S
Вам также может понравиться
- Week 4Документ8 страницWeek 4KhairulОценок пока нет
- Week 6Документ23 страницыWeek 6KhairulОценок пока нет
- Tradable News ReportsДокумент10 страницTradable News ReportsKhairulОценок пока нет
- 3.2.3 Newton's Divided Difference Interpolation: Lagrange Method Has The Following WeaknessesДокумент31 страница3.2.3 Newton's Divided Difference Interpolation: Lagrange Method Has The Following WeaknessesKhairulОценок пока нет
- 3.4 Numerical Solution of Differential EquationsДокумент21 страница3.4 Numerical Solution of Differential EquationsKhairulОценок пока нет
- Week 5Документ28 страницWeek 5KhairulОценок пока нет
- Unit Normal Vector Is Denoted byДокумент20 страницUnit Normal Vector Is Denoted byKhairulОценок пока нет
- Item Analysis Subjective With OptionДокумент18 страницItem Analysis Subjective With OptionKhairulОценок пока нет
- 3 Construction of MCQДокумент14 страниц3 Construction of MCQKhairulОценок пока нет
- 1 Assessment PrinciplesДокумент25 страниц1 Assessment PrinciplesKhairulОценок пока нет
- Assessment Methods: Vincent Pang Universiti Malaysia SabahДокумент10 страницAssessment Methods: Vincent Pang Universiti Malaysia SabahKhairulОценок пока нет
- 2 Bloom's Taxonomy and Test BlueprintДокумент25 страниц2 Bloom's Taxonomy and Test BlueprintKhairul100% (3)
- 4 Construction of Subjective ItemsДокумент15 страниц4 Construction of Subjective ItemsKhairul100% (1)
- Kernel RBF PaperДокумент7 страницKernel RBF PaperKhairulОценок пока нет
- Nuclear Instruments and Methods in Physics Research A: Irène BuvatДокумент7 страницNuclear Instruments and Methods in Physics Research A: Irène BuvatKhairulОценок пока нет
- 1 s2.0 S1877050914003676 MainДокумент11 страниц1 s2.0 S1877050914003676 MainKhairulОценок пока нет
- Eula Microsoft Visual StudioДокумент3 страницыEula Microsoft Visual StudioqwwerttyyОценок пока нет
- Computer Simulations To Maximise Fuel Efficiency and Work Performance of Agricultural Tractors in Rotovating and Ploughing OperationsДокумент11 страницComputer Simulations To Maximise Fuel Efficiency and Work Performance of Agricultural Tractors in Rotovating and Ploughing OperationsKhairulОценок пока нет
- 1 s2.0 S026069171500461X MainДокумент3 страницы1 s2.0 S026069171500461X MainKhairulОценок пока нет
- Journal LinkДокумент1 страницаJournal LinkKhairulОценок пока нет
- Scripta Materialia: S.V. Starikov, L.N. KolotovaДокумент4 страницыScripta Materialia: S.V. Starikov, L.N. KolotovaKhairulОценок пока нет
- 1 s2.0 S0376738815301186 MainДокумент14 страниц1 s2.0 S0376738815301186 MainKhairulОценок пока нет
- 1 s2.0 S0043135415303250 MainДокумент9 страниц1 s2.0 S0043135415303250 MainKhairulОценок пока нет
- 1 s2.0 S1552526015023687 MainДокумент1 страница1 s2.0 S1552526015023687 MainKhairulОценок пока нет
- 1 s2.0 S0927025615006230 MainДокумент8 страниц1 s2.0 S0927025615006230 MainKhairulОценок пока нет
- 1 s2.0 S1876139915000900 MainДокумент6 страниц1 s2.0 S1876139915000900 MainKhairulОценок пока нет
- 1 s2.0 S0010465515003483 MainДокумент8 страниц1 s2.0 S0010465515003483 MainKhairulОценок пока нет
- 1 s2.0 S0897189715002074 MainДокумент4 страницы1 s2.0 S0897189715002074 MainKhairulОценок пока нет
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Digital Logic Design Final ExamДокумент12 страницDigital Logic Design Final Examamanuel abrehaОценок пока нет
- Ilovepdf MergedДокумент23 страницыIlovepdf Mergedvignesh558855Оценок пока нет
- Aoc Monitor I2475PXQUДокумент1 страницаAoc Monitor I2475PXQUdeki0007Оценок пока нет
- CFS VehicleHistoryReportДокумент8 страницCFS VehicleHistoryReportJAVIОценок пока нет
- Shneiderman's 8 Golden Rules of Interface Design: The Principles Questions To Consider Mark CompleteДокумент1 страницаShneiderman's 8 Golden Rules of Interface Design: The Principles Questions To Consider Mark CompletellОценок пока нет
- Indian Standards List As On Jan2009Документ216 страницIndian Standards List As On Jan2009Vasudeva Pavan VemuriОценок пока нет
- BSE SoSДокумент2 страницыBSE SoSALI AHMADОценок пока нет
- Mtech VlsiДокумент15 страницMtech VlsiMukesh MaheshwariОценок пока нет
- IBM Tivoli Storage Manager Version 6.4 Problem Determination GuideДокумент294 страницыIBM Tivoli Storage Manager Version 6.4 Problem Determination GuideBogdanОценок пока нет
- Implementing DR Demings Quality PhilosophyДокумент45 страницImplementing DR Demings Quality PhilosophyDavid del CampoОценок пока нет
- ATV320 Getting Started EN NVE21763 02Документ4 страницыATV320 Getting Started EN NVE21763 02Berkah Jaya PanelОценок пока нет
- Ryoks-1644896915710 STKДокумент2 страницыRyoks-1644896915710 STKRyoka SasakyОценок пока нет
- FAQ AWS AcademyДокумент3 страницыFAQ AWS AcademyMohamed Chiheb BEN CHAABANEОценок пока нет
- tc200 Installation Guide PDFДокумент8 страницtc200 Installation Guide PDFSK Salud - AsistenteОценок пока нет
- Bagting Marvin: Positions HeldДокумент2 страницыBagting Marvin: Positions HeldMarvin BagtingОценок пока нет
- Prosurge UL CertificateДокумент13 страницProsurge UL CertificateROMEL ENRIQUE LOLI SALCEDOОценок пока нет
- Chapter 8 - Project Planning - Project Resource ManagementДокумент6 страницChapter 8 - Project Planning - Project Resource ManagementSuada Bőw WéěžýОценок пока нет
- SEALДокумент6 страницSEALkishorsinghОценок пока нет
- Continental Finance FIT PDFДокумент1 страницаContinental Finance FIT PDFJoe AcevesОценок пока нет
- Radius: Remote Authentication Dial in User Service (RADIUS) Is A NetworkingДокумент6 страницRadius: Remote Authentication Dial in User Service (RADIUS) Is A NetworkingVandana SharmaОценок пока нет
- 6 Months / 6 Weeks Industrial / Institutional Training Daily DairyДокумент11 страниц6 Months / 6 Weeks Industrial / Institutional Training Daily DairyRahul ThakurОценок пока нет
- Next Generation Network Addressing SolutionsДокумент318 страницNext Generation Network Addressing SolutionspvsairamОценок пока нет
- 3D TRAFFIC v3 CatalogДокумент42 страницы3D TRAFFIC v3 CatalogAKASH SINGHОценок пока нет
- IRM IT Knowledge Topic - RPAДокумент9 страницIRM IT Knowledge Topic - RPAJoel Colquepisco EspinozaОценок пока нет
- LOG112Документ21 страницаLOG112Otto Lambertus0% (1)
- Presentation On: Travelling Wave Tube Course Code:EEE 3208 CourseДокумент12 страницPresentation On: Travelling Wave Tube Course Code:EEE 3208 Coursesanjida jahanОценок пока нет
- Hitz Work and PayДокумент2 страницыHitz Work and Paynajergodfred12Оценок пока нет
- Chapter 2. Information Seekers and Electronic EnvironmentsДокумент17 страницChapter 2. Information Seekers and Electronic EnvironmentsCatalina Echeverri GalloОценок пока нет
- History of Electronic SpreadsheetДокумент7 страницHistory of Electronic SpreadsheetJVОценок пока нет
- Häfele Appliance MRP ListДокумент10 страницHäfele Appliance MRP Listpriyanjit910Оценок пока нет