Академический Документы
Профессиональный Документы
Культура Документы
Security Management For ZTE Core Nodes
Загружено:
Anees PeerzadaОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Security Management For ZTE Core Nodes
Загружено:
Anees PeerzadaАвторское право:
Доступные форматы
Chapter 2
Security Management
Function
The security management provides the following functions: l
Ensuring the legal use of the system.
l Managing users, command sets, and roles.
l Preventing illegal users from accessing the system through the login authentication. l
Providing security control for various security management operations through the
operation authorization.
The security management function is implemented by the Operation & Maintenance
Module (OMM) server and clients.
l The OMM clients process data in the login window and the command tree of security
management and display the processing result.
l The OMM server implements login authentication and operation authorization.
Basic Components
Users, roles, command sets, and operation commands are basic components of the
security management.Figure 2-1 shows the inclusion relationships (referred to as affiliated
relationships) between users, roles, command sets, and operation commands.
2-1
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Figure 2-1 Relationships Between Users, Roles, Command Sets and Operation
Commands
Users
Users are operators who log in to the OMM client and perform related operations.
The administrator restricts the users permissions by defining their roles.
Roles
Roles are the permissions provided to the corresponding users, which in essence
assign the operation permissions to a group of users by defining the operation
command sets.
Table 2-1 lists the default roles in the ZXUN iCX(MSCS).
Table 2-1 Default Roles
ID
Role
Highest Permission
Valid or Not
Administrator
All
Yes
Operator
Configuration
Yes
Maintenance
System maintenance
Yes
Data query
Yes
personnel
4
Supervisor
Command Sets
2-2
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
A command set is a set of commands and represents a set of operation permissions.
Multiple command sets can be assigned to the same role.
Table 2-2 lists the command sets for the administrator.
Table 2-2 Command Sets for the Administrator
Role
Highest Permission
Command Set
Command Set
ID
Administrator
All
Command sets of operation
management permission.
Command sets of
configuration permission.
Command sets of system
maintenance permission.
Command sets of data
query permission.
Table 2-3 lists the command sets for operators.
Table 2-3 Command Sets for Operators
Role
Highest Permission
Command Set
Command Set
ID
Operator
Configuration
Command sets of
configuration permission.
Command sets of system
maintenance permission.
Command sets of data
query permission.
Table 2-4 lists the command sets for maintenance personnel.
Table 2-4 Command Sets for Maintenance Personnel
Role
Highest Permission
Command Set
Command Set
ID
Maintenance
System maintenance
Command sets of system
personnel
maintenance permission.
4
Command sets of data
query permission.
Table 2-5 lists the command sets for supervisors.
2-3
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Table 2-5 Command Sets for Supervisors
Role
Highest Permission
Command Set
Command Set
ID
Supervisor
Data query
Command sets of data
query permission.
You can run the SHOW CMDSET MEMBER command to check the specific command
corresponding to the command set.
For example, to check the commands related to the operation management
permission, run the following command:
SHOW CMDSET MEMBER:IID=1;
SHOW CMDSET MEMBER:NAME="Command sets of operation management permissio
n";
l Operation Commands
Operation commands are used to perform operations after users log in to the OMM
client.
Table of Contents
Adding a Command Set ................................................................................................ 2-4
Adding a Role ................................................................................................................ 2-7
Adding a User .............................................................................................................. 2-10
Modifying Own Password ............................................................................................ 2-15
Adding a Login IP Range............................................................................................. 2-16
Disconnecting A Login User Forcibly .......................................................................... 2-18
Modifying the Password Policy of OAM User.............................................................. 2-19
Modifying the Account Policy of OAM User ................................................................ 2-22
Unlocking a User Manually .......................................................................................... 2-24
Inner Control Management .......................................................................................... 2-25
2.1 Adding a Command Set
This procedure describes how to add a command set and add operation command
members to the command set.
Steps
1. To add a command set, perform the following operations:
a. In the command box of the Terminal window, enter the ADD CMDSET command.
The ADD CMDSET configuration area is displayed, see Figure 2-2.
2-4
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Figure 2-2 ADD CMDSET Configuration Area
b. Enter Command Set Name, which cannot be identical with the name used by an
existing command set. For example: test.
c. Click
. Figure 2-3 shows the execution result.
Figure 2-3 Result of Adding a Command Set
Note:
Command Set ID is assigned by the system automatically.
2. To add command set members, perform the following steps:
a. In the command box of the Terminal window, enter the ADD CMDSET MEMBER
command. The ADD CMDSET MEMBER configuration area is displayed, see
Figure 2-4.
Figure 2-4 ADD CMDSET MEMBER Configuration Area
2-5
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-6.
Table 2-6 ADD CMDSET MEMBER Parameter Description
Parameter
Description
Command Set ID
The internal ID of a command Enter either one of the two
set, which is automatically
Setting
parameters. You can query the
allocated by the system when command set ID and the command
this command set is added.
Command Set Name
The name set when a
set name to be set with the SHOW
CMDSET command.
command set is added.
Command ID List
Command ID
You can add several operation
commands to a customized
command set. If these commands
have been assigned, you cannot
repeat the operation.
You can find the command ID to
be configured with the SHOW
CMD command.
c. Click
to add one or more command set members.
Example: The Command Set Name is test, the Command ID is 1402000.
Figure 2-5 shows the execution result.
Figure 2-5 Result of Adding Command Set Members
- End of Steps -
Related Operation
For related operation commands, refer to the following table.
Operation
Command
Command Function
Delete Cmdset
DEL CMDSET
Deletes a command set.
2-6
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Operation
Command
Command Function
Copy Cmdset
COPY CMDSET
Copies an existing command set to create a command
set including the same operation commands.
Delete Cmdset
DEL CMDSET
Member
MEMBER
Show Cmdset
SHOW CMDSET
Member
MEMBER
Show Role by
SHOW CMDSET
Cmdset
ROLE
Deletes an existing command set member.
Queries the command set ID and name.
Queries roles corresponding to a command set.
2.2 Adding a Role
This procedure describes how to add a role and add a command set for the role, to assign
the operation permissions of the command set to the role.
Steps
1. To add a role, perform the following steps:
a. In the command box of the Terminal window, enter the ADD ROLE command.
The ADD ROLE configuration area is displayed, see Figure 2-6.
Figure 2-6 ADD ROLE Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-7.
Table 2-7 ADD ROLE Parameter Description
Parameter
Description
Setting
Role Name
Name of the customized role. Enter a role name different from any
existing name for easy recognition.
You can specify a maximum of 50
characters.
2-7
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Parameter
Description
Role Description
User-defined role description Enter the information about the
information.
Setting
role so that users can get familiar
with the role. You can specify a
maximum of 128 characters.
Valid Role (Yes or No) Validates the role or not.
Including:
l Yes indicates that this role is
effective.
l No indicates that this role is not
effective.
The default value is Yes.
c. Click
to add the role.
Example: Add and validate role TEST. Figure 2-7 shows the execution result.
Figure 2-7 Result of Adding a Role
Note:
The Role ID is assigned by the system automatically.
2. To add a role command set, perform the following steps:
a. In the command box of the Terminal window, enter the ADD ROLE CMDSET
command. The ADD ROLE CMDSET configuration area is displayed, see Figure
2-8.
2-8
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Figure 2-8 ADD ROLE CMDSET Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-8.
Table 2-8 ADD ROLE CMDSET Parameter Description
Parameter
Description
Setting
Role ID
Internal ID of a role,
Enter either one of the two
automatically assigned by
parameters.
the system when the role
You can find the parameters to be
is added.
configured with the SHOW ROLE
Role Name
The name set when a role
command.
is added.
Command Set ID List Command set ID
You can add several operation
command sets to a customized role.
If these command sets have been
assigned, you cannot repeat the
operation.
You can find the parameters to be
configured with the SHOW CMDSET
command.
c. Click
to add a role command set.
Example: The role name is TEST, the command set ID is 5. Figure 2-9 shows
the execution result.
Figure 2-9 Result of Adding a Command Set for a Role
- End of Steps 2-9
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Related Operation
For related operation commands, refer to the following table.
Operation
Command
Command Function
Delete Role
DEL ROLE
Deletes a role.
Modify Role
SET ROLE
Modifies parameters of a role.
Copy Role
COPY ROLE
Copies an existing role to create a role quickly.
Delete Role Cmdset
DEL ROLE CMDSET
Deletes one or more command sets of a
customized role.
Show Role Cmdset
SHOW ROLE CMDSET
Show User by Role
SHOW ROLE USER
Queries command sets of a role.
Queries users of a role.
2.3 Adding a User
This procedure describes how to add a user and assign roles to the user, so that the user has
the operation permissions of the roles.
Steps
1. To add a user, perform the following steps:
a. In the command box of the Terminal window, enter the ADD USER command,
and then select the More... check box. The ADD USER configuration area is
displayed, see Figure 2-10.
Figure 2-10 ADD USER Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-9.
2-10
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Table 2-9 ADD USER Parameter Description
Parameter
Description
Setting
User Name
Name of the new user.
A user name is allowed to include
English letters (case sensitive), digits,
and some special characters ( - ! @ %
& () - + ). This name cannot be identical
with the name of another existing user.
Description
Description of a user.
Description of a user.
Valid User(Yes or
Set whether the user
Default: Yes.
No)
status is effective.
Mobile
Mobile phone number of
Enter the mobile phone number of the
the user.
user.
E-mail address of the
Enter the E-mail address of the user.
user.
Maximum Login
The maximum number
Default: 10.
Count
of concurrently login
If this parameter is set to 0, it means that
users with the same user the system the number of concurrently
account.
login users with the same user account
is not restricted.
Restrict Password
If the Restrict Password
Default: No. This means that the
Validity
Validity is set to Yes, the
password
is
always
effective.
user has to modify the
expired password before
logging in to the system.
Password Validity(d)
Validity of the password.
If the Restrict Password Validity is set
to Yes, this parameter is required.
User Password
Password for logging in
User password must match the password
to the system.
policy of the current system (you can
view the password policy in Supper
Management).
User Confirm
User Confirm Password
Password
The confirm password must be
consistent with the user password.
Restrict Operable
Set whether to restrict
If this parameter is set to Yes, the
Date
the user to perform
Operable Start Date and Operable End
any operation on the
Date are required.
OMM system during the
specified days.
2-11
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Parameter
Description
Setting
Operable Start Date
Start date of restricting
If the Restrict Operable Date is set to
the user to perform any
Yes, this parameter is required.
operation on the OMM
system.
Operable End Date
End date of restricting
If the Restrict Operable Date is set to
the user to perform any
Yes, this parameter is required.
operation on the OMM
system.
Restrict Operable
Set whether to restrict
If this parameter is set to Yes, the
Time
the user to perform
Operable Start Time and Operable
any operation on the
End
Time
are
required.
OMM system during the
specified period.
Operable Start Time
Start time of restricting
If the Restrict Operable Time is set to
the user to perform any
Yes, this parameter is required.
operation on the OMM
system.
Operable End Time
End time of restricting
If the Restrict Operable Time is set to
the user to perform any
Yes, this parameter is required.
operation on the OMM
system.
Restrict Operable
Set whether to restrict
If this parameter is set to Yes, the
Day of Week
the user to perform any
Operable Day of Week is required.
operation on the OMM
system on specified days
of a week.
Operable Day of
Days in a week of
Click the Operable Day of Week text
Week
restricting the user to
box, and select days from the Operable
perform any operation
Day of Week dialog box.
on the OMM system.
c. Click
to add the user.
Example: Add user test with other parameters using their default values. Figure
2-11 shows the execution result.
2-12
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Figure 2-11 Result of Adding a User
Note:
The User ID is generated by the system automatically.
2. To add a user role, perform the following steps:
a. In the command box of the Terminal window, enter the ADD USER ROLE
command. The ADD USER ROLE configuration area is displayed, see Figure
2-12.
Figure 2-12 ADD USER ROLE Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-10.
Table 2-10 ADD USER ROLE Parameter Description
Parameter
Description
Setting
User ID
Internal ID of a
Enter either one of the two parameters.
user, automatically
You can find the parameters to be
generated by the
configured with the SHOW USER
system when the user
command.
is added.
User Name
The name set when the
user is added.
2-13
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Parameter
Description
Setting
Role ID List
Role ID
You can add several roles to a customized
user. If some roles have been assigned,
you cannot assign them again.
You can find the parameters to be
configured with the SHOW ROLE
command.
c. Click
to add user roles.
Example: The user name is test, the role ID is 5. Figure 2-13 shows the
execution result.
Figure 2-13 Result of Adding User Roles
- End of Steps -
Related Operation
For related operation commands, refer to the following table.
Operation
Command
Command Function
Delete User
DEL USER
Deletes a user.
Modify User
SET USER
Modifies information of a user.
Show User
SHOW USER
Queries information of a user, including user ID, name,
validity, mobile phone number, E-mail address, whether
the user is restricted to perform any operation during
specified days, the maximum number of concurrently
login users with the same user account, and whether to
restrict the password validity.
Copy User
COPY USER
Copies an existing user to create a new user quickly.
Delete User Role
DEL USER ROLE
Deletes roles of a customized user.
Show User Role
SHOW USER ROLE
Queries roles of a user.
2-14
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
2.4 Modifying Own Password
Once a user account is created, the user can modify its own password. This procedure
describes how to modify the password.
Steps
1. In the command box of the Terminal window, enter the SET PASSWORD command.
The SET PASSWORD configuration area is displayed, see Figure 2-14.
Figure 2-14 SET PASSWORD Configuration Area
2. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-11.
Table 2-11 SET PASSWORD Parameter Description
Parameter
Description
Setting
Old Password
The old password you want to
You must type the correct old
modify
password. Leaving this parameter
blank means that the old password
is empty.
New Password
New password of the user
Leaving this parameter blank
means that the new password is
empty.
Confirm Password
The confirm password has to be
Leaving this parameter blank
the same with the new password. means that the confirm password
is empty.
3. Click
to modify the password.
- End of Steps -
Related Operation
For related operation commands, refer to the following table.
2-15
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Operation
Command
Command Function
Set All Common Users SET ALLUSERSTATUS
Only the administrator can set all common
to be Effective or Not
users to be effective or not. Be cautious to
run this command.
Set All Common Users
SET ALLUSERPASSWD
Password
Only the administrator can modify the
password of all users. Be cautious to run this
command.
2.5 Adding a Login IP Range
This procedure describes how to add a login IP range for a user.
Steps
1. In the command box of the Terminal window, enter the ADD USER IPSEC command.
The ADD USER IPSEC configuration area is displayed, see Figure 2-15.
Figure 2-15 ADD USER IPSEC Configuration Area
2. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-12.
Table 2-12 ADD USER IPSEC Parameter Description
Parameter
Description
Setting
User ID
ID of the user.
You must and can only set
User Name
Name of the user.
one of User ID and User
Name.
To query the user ID and
name, run the SHOW USER
command.
Description
Description of the login IP address Range: 0 to 50 characters.
range.
2-16
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Parameter
Description
Setting
IP Section
The IP address range.
Required.
i.
Click this text box. The
IP Section dialog box is
displayed.
ii.
In the IP Section dialog
box, set the Start IP and
End IP.
A maximum of 50 IP
address segments can be
configured for a user.
3. Click
to add a login IP address range for a user.
Example: The user name is test, the start IP address is 10.40.53.45, and the end IP
address is 10.40.53.47. Figure 2-16 shows the execution result.
Figure 2-16 Result of Adding a Login IP Range for a User
- End of Steps -
Related Operation
For related operation commands, refer to the following table.
Operation
Command
Command Function
Delete User IP Range
DEL USER IPSEC
Deletes an IP range of a user.
Show User IP Range
SHOW USER IPSEC
Queries the IP ranges of a
user.
Delete User All IP Range
DEL USER ALLIPSEC
Deletes all IP ranges of a user.
2-17
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
2.6 Disconnecting A Login User Forcibly
When performing system maintenance or detecting that a department user tries to perform
illegal operations, an administrator can disconnect the user compulsorily.
Prerequisite
You have logged in to the Local Maintenance Terminal page as the system administrator
admin.
Steps
1. To query information of a login user, including user name, IP address, login time and
login type, perform the following steps:
a. In the command box of the Terminal window, enter the SHOW LOGINUSER
command. The SHOW LOGINUSER configuration area is displayed, see Figure
2-17.
Figure 2-17 SHOW LOGINUSER Configuration Area
b. Enter the name of the user (If you leave it blank, you queries all users logging in
to the LMT).
c. Click
to query information of a login user.
Example: Query all users logging in to the LMT. Figure 2-18 shows the execution
result.
Figure 2-18 Result of Querying All Login Users
2-18
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
2. To disconnect a login user forcibly, perform the following steps:
a. In the command box of the Terminal window, enter the RMV USERLINK
command. The RMV USERLINK configuration area is displayed, see Figure
2-19.
Figure 2-19 RMV USERLINK Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-13.
Table 2-13 RMV USERLINK Parameter Description
Parameter
Description
Setting
User Name
Name of the user to be
You can specify a maximum of
disconnected
30 characters.
IP address of the terminal where
IP address format
IP Address
this login user is located.
Login Time
Type
c. Click
Time when this login user logged
Time format: YYYY-MM-DD
in to the OMM system.
HH:MM:SS
Type of the terminal through which
Terminal types are OMM
this user logs in to the OMM
Client, TELNET Client, NDF
system.
Client and SSH Client.
to disconnect the login user compulsorily.
End of Steps -
2.7 Modifying the Password Policy of OAM User
This procedure describes how to modify the password policy of the security management
system.
Prerequisite
You have logged in to the Local Maintenance Terminal page as the system administrator
admin.
2-19
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Steps
1. To query current password policy, perform the following steps:
a. In the command box of the Terminal window, enter the SHOW PASSWORDTAC
TIC command. The SHOW PASSWORDTACTIC configuration area is displayed.
Parameter setting is not required.
b. Click
to query current password policy.
2. To modify the password policy of OAM user, perform the following steps:
a. In the command box of the Terminal window, enter the SET PASSWORDTACTIC
command. The SET PASSWORDTACTIC configuration area is displayed, see
Figure 2-20.
Figure 2-20 SET PASSWORDTACTICConfiguration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-14.
Table 2-14 SET PASSWORDTACTIC Parameter Description
Parameter
Description
Setting
Mininum Length of Minimal length of a password
Integer from 0 to 20, with a
Password
default of 0. It is recommended
to change it to 6.
2-20
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Parameter
Description
Setting
Enable Password
The password complexity policy
Including:
Complexity
means:
l Yes: the password
Requirement
l A password must contain
complexity policy is enabled.
characters from three of the
following
four
l No: the password
categories:
complexity policy is disabled.
English uppercase
characters, English
lowercase characters, base
10 digits and non-alphabetic
characters.
l A password cannot be
identical with the user name.
l A password cannot be the
reverse of the user name
string.
Reminding Days
Warns a user before N days ago
Before Password
when the password is overdue.
Integer from 0 to 90.
Expired
Must Modify
Specifies whether it is required to
Including:
Expired Password
modify an expired password.
Yes: The expired password
must be modified.
No: The expired password
needs not to be modified.
Count of Latest
The new password cannot any
Passwords Cannot
latest password that has been
Integer from 0 to 90.
Be Reused
entered for N times.
Day of Latest
The new password cannot be any
Passwords Cannot
latest password that has been
Be Reused
entered within N days.
Must Modify
Integer from 0 to 180.
l If this parameter is set to
Password When
Yes, the user must modify
User Login First
the password at the first
login.
l If this parameter is set to
No: the user do not need to
modify the password at the
first login.
2-21
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Parameter
Description
Setting
Must Modify
l If this parameter is set
Password When
to Yes, the user who
Alarmed User
successively enters the
Login
incorrect password for
three times but still remains
unlocked must modify the
password after the login. l If
this parameter is set
to No, the user who
successively enters the
incorrect password for
three times but still remains
unlocked do not need to
modify the password after
the login.
c. Click
to modify the password policy.
End of Steps -
2.8 Modifying the Account Policy of OAM User
This procedure describes how to query the account policy of the security management
system.
Prerequisite
You have logged in to the Local Maintenance Terminal as the system administrator
admin.
Steps
1. To query current account policy, perform the following steps:
a. In the command box of the Terminal window, enter the SHOW USERTACTIC
command. The SHOW USERTACTIC configuration area is displayed. Parameter
setting is not required.
b. Click
to query current account policy.
2. To modify the account policy, perform the following steps:
a. In the command box of the Terminal window, enter the SET USERTACTIC
command. The SET USERTACTIC configuration area is displayed, see Figure
2-21.
2-22
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Figure 2-21 SET USERTACTIC Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-15.
Table 2-15 SET USERTACTIC Parameter Description
Parameter
Description
Setting
Lock Status
Account lock policy
Including:
l Never Lock: indicates that the
system does not lock this user
even if the user types a wrong
password many times.
l Policy Lock: indicates that the
system does not lock this user
if the number of times that the
user successively enter a wrong
password exceeds the preset
number. The user is unlocked after
preset auto unblocking time.
l Lock Forever: indicates that the
system locks a user the number of
times that the user successively
types a wrong password exceeds
the preset number. The user can
only
Lock User by IP
be
manually
unlocked.
Whether to lock an
You need to set this parameter when
account in accordance
the lock status is Policy Lock or Lock
with the IP address of
Forever. Including:
the login client of the
l Yes: Lock an account in
account.
accordance with the IP address of
the login client that this account.
l No: Lock an account not in
accordance with the IP address of
the login client that this account.
2-23
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Parameter
Description
Setting
Max. Times of
The maximum number
You need to set this parameter when
Incorrect Password
of times that a user can
the lock status is Policy Lock or Lock
Enter
enter a wrong password.
Forever.
The account is locked if
the number exceeds the
preset value.
Auto Unlock Time
The time when the
You need to set this parameter when
(Hr)
system automatically
the lock status is Policy Lock or Lock
unlocks a user.
Forever. The range is from 1 to 72.
Lock-Check Period
Period of lock status
Set the period for a lock status
(d)
detection.
detection. Integer from 1 to 999.
Reminding Days
Number of days before
Integer from 0 to 90.
before Account
account expiration to
Expired
start reminding the user.
c. Click
to modify the account policy.
End of Steps -
2.9 Unlocking a User Manually
The user account rules define conditions for locking users, that is, the number of times a
wrong password is entered. If a user types a wrong password for up to the specified times, the
account is locked. The system administrator can manually unlock a user.
Prerequisite
You have logged in to the Local Maintenance Terminal page as the system administrator
admin.
Steps
1. To query locked user, perform the following steps:
a. In the command box of the Terminal window, enter the SHOW LOCKEDUSE
R command. The SHOW LOCKEDUSER configuration area is displayed, see
Figure 2-22.
2-24
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Figure 2-22 SHOW LOCKEDUSER Configuration Area
b. Enter the User Name. If no name is entered, the system queries all locked users.
c. Click
to query information of a locked user.
2. To unlock a user manually, perform the following steps:
a. In the command box of the Terminal window, enter the UNLOCK USER
command. The UNLOCK USER configuration area is displayed, see Figure 2-23.
Figure 2-23 UNLOCK USER Configuration Area
b. Enter the parameters in accordance with your actual situations. For the parameter
description, refer to Table 2-16.
Table 2-16 UNLOCK USER Command Parameter Description
Parameter
Description
Setting
User Name
Name of the user you
You can find the user name and IP
want to unlock
Address to be configured with the
IP Address
IP address of the client
SHOW LOCKEDUSER command.
through which the user
logs in to OMM system.
c. Click
to manually unlock the user.
End of Steps -
2.10 Inner Control Management
Inner control management supports the management of inner control accounts in the OMM
system, including data file accounts and file transfer service accounts. With this function,
maintenance engineers can perform operations, such as modifying the password of an
inner control account.
2-25
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Inner control management and inner control account are described as follows:
l An inner control account is created during installation. It is used for accessing data
files or other resources in the system. For the application of an inner control account,
see Figure 2-24.
l Inner control management adopts its own policy, which is different from the policy of
managing permission users.
l The user having the inner control management permission can query and set the inner
control management policy as required.
Inner control management covers modification of account password, inner control
password policy. The following table provides the description for related operation
commands.
Figure 2-24 Inner Control Account Application
2.10.1 Modifying the Information of Inner-Control Accounts
This procedure describes how to modify information of a specified inner control account,
including account description, password validity, and password of the account.
Prerequisite
You have logged in to the Local Maintenance Terminal page as the system administrator
admin.
Steps
1. To query information of inner control accounts, perform the following steps:
a. In the command box of the Terminal window, enter the SHOW ACCOUNTINF
O command. The SHOW ACCOUNTINFO configuration area is displayed, see
Figure 2-25.
2-26
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Figure 2-25 SHOW ACCOUNTINFO Configuration Area
b. Click
to query the information of all inner control accounts. If you want to query
information of an inner control account, select the type of the account from the
Account Type list or enter the name of the account in the Account Name text
box. For the parameter description, refer to Table 2-17.
2. To modify description or password validity of an inner control account, perform the
following steps:
a. In the command box of the Terminal window, enter the SET ACCOUNTINFO
command. The SET ACCOUNTINFO configuration area is displayed, see Figure
2-26.
Figure 2-26 SET ACCOUNTINFO Configuration Area
b. Enter the command parameters as needed. For parameter descriptions, refer to
Table 2-17.
Table 2-17 SET ACCOUNTINFO Parameter Descriptions
Parameter
Description
Account Type
Type of the inner control Options:
account
Setting
l Data File Account
l File Transfer Account
l OMP File Transfer Account
l OMP TELNET Account
Account Name
Name of the inner
Case-insensitive.
control account
Enter the name of an existing inner
control account in the text box.
To query the name of an existing inner
control account in the system, run the
SHOW ACCOUNTINFO command.
2-27
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
Parameter
Description
Account Description
Description of the inner Range: 0-128 characters.
control account
Setting
Enter the new description for the inner
control account.
Password Validity(d)
Validity of the inner
Range: 1-90 days.
control account
Enter the new password validity.
password
c. Click
to modify description of an inner control account.
Example: Modify description of the file transfer account 1_FTP to FTP, and set the
password validity to 60. Figure 2-27 shows the execution result.
Figure 2-27 Result of Modifying Description of an Inner Control Account
3. To modify the password of an inner control account, perform the following steps:
a. In the command box of the Terminal window, enter SET ACCOUNTPASSWD
command. The SET ACCOUNTPASSWD configuration area is displayed, see
Figure 2-28.
Figure 2-28 SET ACCOUNTPASSWD Configuration Area
b. Enter the command parameters as needed. For parameter descriptions, refer to
Table 2-18.
2-28
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Table 2-18 SET ACCOUNTPASSWD Parameter Descriptions
Parameter
Description
Setting
Account Type
Type of the inner
Options:
control account
l Data File Account
l File Transfer Account
l OMP File Transfer Account
l OMP TELNET Account
Account Name
Name of the inner
Case-insensitive.
control account
Enter the name of an existing inner control
whose password is
account in the text box.
to be modified
To query the name of an inner control
account, run the SHOW ACCOUNTINFO
command.
Old Password
Original password
You must enter the correct original number
of the inner control
before running the command.
account
New Password
New password of
The new password must comply with the
the inner control
inner control password policy.
account
Confirm Password
Confirm password
The confirm password must be the same
of the inner control
with the new password.
account
c. Click
. The Confirm dialog box is displayed.
d. Click Yes to modify the password of an inner control account.
- End of Steps -
2.10.2 Modifying the Password Policy of Inner-Control Accounts
This procedure describes how to modify the parameters of the password policy of
inner-control accounts, including Min Length of the Password, Max Length of the
Password, Weak Password Check, Password Repeat Count, Days Before the
Password Is Invalid, and Need to Send Alarm When Invalid.
Prerequisite
You have logged in to the Local Maintenance Terminal page as the system administrator
admin.
Steps
1. Query the password policy of inner-control accounts.
2-29
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
a. In the command box of the Terminal window, enter SHOW PASSWDTACTIC
command. The SHOW PASSWDTACTIC configuration area is displayed. The
parameter setting is not required.
b. Click
to query the current inner control password policy.
2. Modify the password policy of inner-control accounts.
a. In the command box of the Terminal window, enter SET PASSWDTACTIC
command. The SET PASSWDTACTIC configuration area is displayed, see
Figure 2-29.
Figure 2-29 SET PASSWDTACTIC Configuration Area
b. Enter the command parameters as needed. For the parameter description, refer
to Table 2-19.
Table 2-19 SET PASSWDTACTIC Parameter Description
Parameter
Description
Setting
Min Length of
Minimum length of a
Range: 1-32. The minimal length
Password
password
of a password must be not greater
than the maximum length of the
password.
Max Length of
Maximum length of a
Range: 1-32. The maximum
Password
password
length of a password must be not
less than the minimal length of the
password.
2-30
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Chapter 2 Security Management
Parameter
Description
Setting
Weak Password
The password complexity
Including:
Check
policy means:
Yes: The password complexity
policy is enabled.
A password must
l
contain characters
No: The password complexity
policy
from three of the
is
disabled.
following four categories:
English uppercase
characters,
lowercase
English
characters,
base 10 digits
and
non-alphabetic
characters.
l
A password should not
be the same as the user
name or the combination
of double user names.
l A password cannot be
the reverse of the user
name string.
Can Not Use Recently
Keeps password history for
Range: 1-50.
Used Password Times N passwords remembered.
Reminding Days
Specifies the number of days
You need to set this parameter
Before Password
you are prompted to change
when Send Alarm or Not When
Expired
the password before the
Password Expired is set to Yes.
password expires.
Range: 0-90. If this parameter is
set to 0, you are prompted when a
password expires.
Send Alarm or Not
Specifies whether the system Including:
When Password
prompts you of password
Expired
expiration.
l Yes: The system prompts the
user of password expiration.
l No: The system does not
prompt user of password
expiration either before or after
a password expires.
c. Click
to modify the password policy of inner-control accounts.
End of Steps -
2-31
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
ZXUN iCX(MSCS) General Operation Guide
This page intentionally left blank.
2-32
SJ-20120730093520-013|2012-10-31(R1.0)
ZTE Proprietary and Confidential
Вам также может понравиться
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- Volte ArchitectureДокумент34 страницыVolte ArchitecturedspwhizОценок пока нет
- APIДокумент7 страницAPIAnees PeerzadaОценок пока нет
- RNC Health Check DTДокумент1 страницаRNC Health Check DTAnees PeerzadaОценок пока нет
- Date Time Severity Specific Problem: C2 - Vodafone Idea InternalДокумент2 страницыDate Time Severity Specific Problem: C2 - Vodafone Idea InternalAnees PeerzadaОценок пока нет
- GSM, GPRS, UMTS, HSDPA and HSUPA Protocols and Call Flow OverviewДокумент103 страницыGSM, GPRS, UMTS, HSDPA and HSUPA Protocols and Call Flow Overview742952100% (3)
- Mobile Packet Backbone Network White Paper PDFДокумент8 страницMobile Packet Backbone Network White Paper PDFAnees Peerzada50% (2)
- Usefull APG43 CommandsДокумент8 страницUsefull APG43 Commandswertys90Оценок пока нет
- IMS StandardsДокумент74 страницыIMS StandardsAnees PeerzadaОценок пока нет
- 2g and 3g Kpi Improvement by Parameter Optimization NSN Ericsson Huawei Reck On Talk PDFДокумент2 страницы2g and 3g Kpi Improvement by Parameter Optimization NSN Ericsson Huawei Reck On Talk PDFFrancisco J LopezОценок пока нет
- HLR BasicsДокумент13 страницHLR BasicsAyan Chakraborty75% (4)
- WP SRVCC With LteДокумент14 страницWP SRVCC With LteMarcelo AranibarОценок пока нет
- Voice Drop Call Rate (VDCR) MeasurementДокумент21 страницаVoice Drop Call Rate (VDCR) MeasurementAnees PeerzadaОценок пока нет
- Mef Cecp TrainingДокумент5 страницMef Cecp TrainingShambhu KhanalОценок пока нет
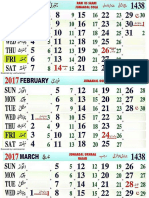
- Calendar Dec 2017Документ1 страницаCalendar Dec 2017Anees PeerzadaОценок пока нет
- BladeДокумент4 страницыBladeMonika RathoreОценок пока нет
- 6th Central Pay Commission Salary CalculatorДокумент15 страниц6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- HLR PROFILE OVERVIEWДокумент5 страницHLR PROFILE OVERVIEWAnees Peerzada100% (1)
- GSM Location Update Sequence DiagramДокумент4 страницыGSM Location Update Sequence DiagramYogesh BindwalОценок пока нет
- Ericsson Core Sts and KpiДокумент24 страницыEricsson Core Sts and KpiDarwin Noel Mataro100% (2)
- Usefull APG43 CommandsДокумент8 страницUsefull APG43 Commandswertys90Оценок пока нет
- GSM, GPRS, UMTS, HSDPA and HSUPA Protocols and Call Flow OverviewДокумент103 страницыGSM, GPRS, UMTS, HSDPA and HSUPA Protocols and Call Flow Overview742952100% (3)
- Islamic Calendar 2017Документ12 страницIslamic Calendar 2017Anees PeerzadaОценок пока нет
- Resolviing Subsciber Related Problem OSS PDFДокумент17 страницResolviing Subsciber Related Problem OSS PDFAnees PeerzadaОценок пока нет
- GSM BasicsДокумент57 страницGSM BasicsAnees PeerzadaОценок пока нет
- Core Network Introduction PDFДокумент32 страницыCore Network Introduction PDFAnees Peerzada100% (2)
- HLR subscriber profile guideДокумент5 страницHLR subscriber profile guideAnees PeerzadaОценок пока нет
- 6th Central Pay Commission Salary CalculatorДокумент15 страниц6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- RNC Health Check DTДокумент1 страницаRNC Health Check DTAnees PeerzadaОценок пока нет
- Huawei CS Core OverviewДокумент46 страницHuawei CS Core OverviewAnees Peerzada100% (1)
- Disaster Recovery PreparednessДокумент1 страницаDisaster Recovery PreparednessAnees PeerzadaОценок пока нет
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- Carding Dell Orders in March 2013Документ2 страницыCarding Dell Orders in March 2013BADBOY BRETОценок пока нет
- IdeaДокумент34 страницыIdeasukla.banerjee6427Оценок пока нет
- Sai Arpan Patra - Internship ReportДокумент36 страницSai Arpan Patra - Internship Reporthimanshubehera73Оценок пока нет
- 32 Topic 4-ActiveДокумент3 страницы32 Topic 4-ActiveVladimir ApostolovОценок пока нет
- What is Data Protection and Why Do You Need ItДокумент4 страницыWhat is Data Protection and Why Do You Need Itmilind21006Оценок пока нет
- Modern Public-Key CryptosystemsДокумент57 страницModern Public-Key CryptosystemsShaurya KapoorОценок пока нет
- Understanding The Risks of Mobile AppsДокумент7 страницUnderstanding The Risks of Mobile AppsblussierttОценок пока нет
- User ID Password Step of LoginДокумент1 страницаUser ID Password Step of LoginVinod MevafarosОценок пока нет
- Cracking DES - Secrets Of2013-07-12 20-54-101377 PDFДокумент278 страницCracking DES - Secrets Of2013-07-12 20-54-101377 PDFbruno di matteiОценок пока нет
- Xerox Workcentre 5225 - NVRAM PDFДокумент1 страницаXerox Workcentre 5225 - NVRAM PDFkarl_frederick100% (1)
- Cert Exercises HandbookДокумент88 страницCert Exercises HandbookDaniel Checchia100% (1)
- CriptographyДокумент9 страницCriptographyapi-3746880Оценок пока нет
- TorGuard VPN Review: Cryptic Interface, Average SpeedsДокумент3 страницыTorGuard VPN Review: Cryptic Interface, Average SpeedsPappu KhanОценок пока нет
- A Guide To International Data Protection - EducationДокумент8 страницA Guide To International Data Protection - EducationDavid KefferОценок пока нет
- Study of RSA Public Key GenerationДокумент4 страницыStudy of RSA Public Key GenerationPahchan GargОценок пока нет
- What Is Business Email CompromiseДокумент3 страницыWhat Is Business Email Compromiseaariya goelОценок пока нет
- Cisco Global Threat Report 2q2011Документ15 страницCisco Global Threat Report 2q2011Peyman LotfiОценок пока нет
- TOEFL ReadingДокумент72 страницыTOEFL ReadingJihan MОценок пока нет
- CEH v8 PDFДокумент1 927 страницCEH v8 PDFgayatri kuekeringОценок пока нет
- Zhang2019 A Security Scheme For Intelligent Substation Communications Considering Real-Time PerformanceДокумент14 страницZhang2019 A Security Scheme For Intelligent Substation Communications Considering Real-Time Performanceedsonpaveli-1Оценок пока нет
- An Advanced AES Algorithm Using Swap and 400 Bit Data Block With Flexible S-Box in Cloud ComputingДокумент6 страницAn Advanced AES Algorithm Using Swap and 400 Bit Data Block With Flexible S-Box in Cloud ComputingusuimisakiОценок пока нет
- Image Encryption Using Chaos-Based Modified Blowfish AlgorithmДокумент5 страницImage Encryption Using Chaos-Based Modified Blowfish AlgorithmzakariaОценок пока нет
- Differential Cryptanalysis On FEAL 4Документ10 страницDifferential Cryptanalysis On FEAL 4Marcu Adrian BercaОценок пока нет
- Financial Times Europe - 17-06-2021Документ20 страницFinancial Times Europe - 17-06-2021HoangОценок пока нет
- BarracudaWebAppFirewall AG ManualДокумент252 страницыBarracudaWebAppFirewall AG ManualcrearnombreОценок пока нет
- Key Cyber Resiliency Terms and ConceptsДокумент3 страницыKey Cyber Resiliency Terms and ConceptsCharleston FernandesОценок пока нет
- ProxySG Training SlideДокумент18 страницProxySG Training SlideIrwan DasukiОценок пока нет
- 7 8 Css Week 8 9 Maintain Computer Equipment and SystemsДокумент8 страниц7 8 Css Week 8 9 Maintain Computer Equipment and SystemsHachiko CubangbangОценок пока нет
- ISFS exam questions and answersДокумент21 страницаISFS exam questions and answersthiagodiebОценок пока нет
- Script MikrotikДокумент3 страницыScript MikrotikwartechОценок пока нет