Академический Документы
Профессиональный Документы
Культура Документы
Embedded
Загружено:
samsath10Оригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Embedded
Загружено:
samsath10Авторское право:
Доступные форматы
International Journal of Ethics in Engineering & Management Education
Website: www.ijeee.in (ISSN: 2348-4748, Volume 1, Issue 4, April 2014)
EMBEDDED BASED DOCUMENT LEAKAGE
PROTECTION SYSTEM
Akash1,Jaibheem2,Prakash3
Sharangowda S. Patil4
Student, Dept. of E&CE,
VNEC, Shorapur
Jaibheembg88@gmail.com
Asst.prof Dept,ECE
VNEC Shorapur
Authorized person in University board acts as the Base station.
To open the question paper box, RFID is needed to be swiped
with a valid RFID tag and then RFID will compare with data
such as RFID address. If the comparison is failure , then
controller sends WRONG ACCESS message to the Base
station through GSM modem and If anybody tries to open the
box before the pre-defined time with a valid RFID tag also,
then controller sends RULES VIOLATED message to the
Base station through GSM modem. The password is sent from
the Base station to the college at the time of opening the BOX.
If the person enters the wrong password, then
controller sends PASSWORD MISMATCH message to the
Base station through GSM modem. If the person enters the
correct password, then BOX is opened with the help of the DC
motor.
Abstract The main document leakage protection system is to
design and develop to the stop the corruption by putting a stop to
leakage of the documents with the help of technology i.e.,
Document Leakage Protection System. This document leakage
protection mechanism there will be a box which will have a
transceiver unit, a locking and unlocing mechanism. The box
will be locked administrator, if the box is tampered before the
time. It will generate the alaram. A signal will be generate from
base station which deactivate the lock.
1. INTRODUCTION
The main aim to the document leakage protection
system to implement a system which will help to stop the
malpractice of leaking the important and confidential
documents.
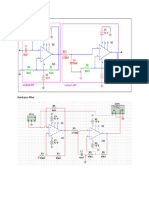
3. IMPLEMENTATION
Data leakage protection system requires series of
preparation work, including data classification, risk
assessment and privacy requirement.
GSM Modem
GSM stands for Global system for Mobile
Communication. This is the structural set developed by the
Europian Telecommunication standard institute (ETSI) to
describe the technology for second generation. The GSM
architecture which involve the (ms) mobile station directly
interacts with a base station controller (BSC) BTS and BSC
combined together forms the (BSS). More than one BTS are
connected with one BSC, the BSC further interacts with
mobile station controller (MSC) which is the heart of GSM
network (MSC) gives connectivity to the PSTN and other
PLMNS and (MSC) also responsible to interact with HLR and
VLR.
To achieve the document leakage protection system
using micro-controller now easily implemented within
embedded software of micro-controller and document leakage
protection system aims at putting together a robust
microcontroller based power supply unit access LCD screen
0.30 output range (upto 80w), computer connectivity and
control and over load protection all implemented.
2. BLOCK DIAGRAM & WORKING
RFID Reader
The document leakage protection system based on
RFID security system, and its stands for Radio Frequency
identification. Generally a RFID System consists of (2) parts
A reader and one or more transponders, also known as Tags.
RFID System evolved from bar code means automatically
identity and track product and people.
The RFID System can be seen in
1. Access control
2. Control Less payment system
3. Product tracking and inventory control.
GSM modem is connected to the box containing
question papers along with the microcontroller. Mobile of
382
International Journal of Ethics in Engineering & Management Education
Website: www.ijeee.in (ISSN: 2348-4748, Volume 1, Issue 4, April 2014)
RFID TAG:
The amount of data storage on a tag can vary, ranging
from 16 bits on the low end to as much as several thousand
bits on the high end. Of course, the greater the storage
capacity, the higher the price per tag.
The tag and antenna structure can come in a variety of
physical form factors and can either be self-contained or
embedded as part of a traditional label structure (i.e., the tag is
inside what looks like a regular bar code labelthis is termed
a 'Smart Label') companies must choose the appropriate form
factors for the tag very carefully and should expect to use
multiple form factors to suit the tagging needs of different
physical products and units of measure. For example, a pallet
may have an RFID tag fitted only to an area of protected
placement on the pallet itself. On the other hand, cartons on
the pallet have RFID tags inside bar code labels that also
provide operators human-readable information and a back-up
should the tag fail or pass through non RFID-capable supply
chain links.
An RFID tag is comprised of a microchip containing
identifying information and an antenna that transmits this data
wirelessly to a reader. At its most basic, the chip will contain a
serialized identifier, or license plate number, that uniquely
identifies that item, similar to the way many bar codes are
used today. A key difference, however is that RFID tags have
a higher data capacity than their bar code counterparts. This
increases the options for the type of information that can be
encoded on the tag, including the manufacturer, batch or lot
number, weight, ownership, destination and history (such as
the temperature range to which an item has been exposed). In
fact, an unlimited list of other types of information can be
stored on RFID tags, depending on application needs. An
RFID tag can be placed on individual items, cases or pallets
for identification purposes, as well as on fixed assets such as
trailers, containers, totes, etc.
Tags come in a variety of types, with a variety of
capabilities "Read-only" versus "read-write"
There are three options in terms of how data can be
encoded on tags: (1) Read-only tags contain data such as a
serialized tracking number, which is pre-written onto them by
the tag manufacturer or distributor. These are generally the
least expensive tags because they cannot have any additional
information included as they move throughout the supply
chain. Any updates to that information would have to be
maintained in the application software that tracks SKU
movement and activity. (2) "Write once" tags enable a user to
write data to the tag one time in production or distribution
processes. Again, this may include a serial number, but
perhaps other data such as a lot or batch number. (3) Full
"read-write" tags allow new data to be written to the tag as
neededand even written over the original data. Examples for
the latter capability might include the time and date of
ownership transfer or updating the repair history of a fixed
asset. While these are the most costly of the three tag types
and are not practical for tracking inexpensive items, future
standards for electronic product codes (EPC) appear to be
headed in this direction.
Like all wireless communications, there are a variety of
frequencies or spectra through which RFID tags can
communicate with readers. Again, there are trade-offs among
cost, performance and application requirements. For instance,
low-frequency tags are cheaper than ultra high-frequency
(UHF) tags, use less power and are better able to penetrate
non-metallic substances. They are ideal for scanning objects
with high water content, such as fruit, at close range. UHF
frequencies typically offer better range and can transfer data
faster. But they use more power and are less likely to pass
through some materials. UHF tags are typically best suited for
use with or near wood, paper, cardboard or clothing products.
Compared to low-frequency tags, UHF tags might be better
for scanning boxes of goods as they pass through a bay door
into a warehouse. While the tag requirements for compliance
mandates may be narrowly defined, it is likely that a variety of
tag types will be required to solve specific operational issues.
You will want to work with a company that is very
knowledgeable in tag and reader technology to appropriately
identify the right mix of RFID technology for your
environment and applications.
The RF transceiver is the source of the RF energy used to
activate and power the passive RFID tags. The RF transceiver
383
International Journal of Ethics in Engineering & Management Education
Website: www.ijeee.in (ISSN: 2348-4748, Volume 1, Issue 4, April 2014)
may be enclosed in the same cabinet as the reader or it may be
a separate piece of equipment. When provided as a separate
piece of equipment, the transceiver is commonly referred to as
an RF module. The RF transceiver controls and modulates the
radio frequencies that the antenna transmits and receives. The
transceiver filters and amplifies the backscatter signal from a
passive RFID tag.
Buzzer
LCD (Liquid Crystal Display)
A liquid crystal display (LCD) is a thin, flat display
device made up of any number of color or monochrome pixels
arrayed in front of a light source or reflector. Each pixel
consists of a column of liquid crystal molecules suspended
between two transparent electrodes, and two polarizing filters,
the axes of polarity of which are perpendicular to each other.
Without the liquid crystals between them, light passing
through one would be blocked by the other. The liquid crystal
twists the polarization of light entering one filter to allow it to
pass through the other.
A buzzer or beeper is a signaling device, usually
electronic, typically used in automobiles, household
appliances such as a microwave oven.
It most commonly consists of a number of switches
or sensors connected to a control unit that determines if and
which button was pushed or a preset time has lapsed, and
usually illuminates a light on the appropriate button or control
panel, and sounds a warning in the form of a continuous or
intermittent buzzing or beeping sound. Initially this device
was based on an electromechanical system which was
identical to an electric bell without the metal gong . Often
these units were anchored to a wall or ceiling and used the
ceiling or wall as a sounding board. Another implementation
with some AC-connected devices was to implement a circuit
to make the AC current into a noise loud enough to drive a
loudspeaker and hook this circuit up to a cheap 8-ohm
speaker. Nowadays, it is more popular to use a ceramic-based
piezoelectric sounder like a Son alert which makes a highpitched tone. Usually these were hooked up to "driver" circuits
which varied the pitch of the sound or pulsed the sound on and
off.
Features :
Interface with either 4-bit or 8-bit
microprocessor.
Display data RAM
80x8 bits (80 characters).
Character generator ROM
160 different 5 .7 dot-matrix character
Character generator RAM
8 different user programmed 5.7
dot-matrix.
Numerous instructions: Clear Display, Cursor
Home, Display ON/OFF, Blink Character,
Cursor Shift, Display Shift.
Shapes and sizes :
The word "buzzer" comes from the rasping noise that
buzzers made when they were electromechanical devices,
operated from stepped-down AC line voltage at 50 or 60
cycles. Other sounds commonly used to indicate that a button
has been pressed are a ring or a beep.
4. DC MOTOR
A DC motor is a mechanically commutated electric
motor powered from direct current (DC). The stator is
stationary in space by definition and therefore its current. The
current in the rotor is switched by the comutator to also be
stationary in space. This is how the relative angle between the
stator and rotor magnetic flux is maintained near 90 degrees,
which generates the maximum torque.
DC motors have a rotating armature winding
(winding in which a voltage is induced) but non-rotating
armature magnetic field and a static field winding (winding
that produce the main magnetic flux) or permanent magnet.
Different connections of the field and armature winding
provide
different
inherent
speed/torque
regulation
384
International Journal of Ethics in Engineering & Management Education
Website: www.ijeee.in (ISSN: 2348-4748, Volume 1, Issue 4, April 2014)
characteristics. The speed of a DC motor can be controlled by
changing the voltage applied to the armature or by changing
the field current. The introduction of variable resistance in the
armature circuit or field circuit allowed speed control. Modern
DC motors are often controlled by power electronics systems
called DC drives.
The introduction of DC motors to run machinery
eliminated the need for local steam or internal combustion
engines, and line shaft drive systems. DC motors can operate
directly from rechargeable batteries, providing the motive
power for the first electric vehicles. Today DC motors are still
found in applications as small as toys and disk drives, or in
large sizes to operate steel rolling mills and paper machines.
[6].
[7].
[8].
[9].
[10].
5. POWER SUPPLY
To achieve document leakage protection system by
using power supply. To achieve this, using microcontrollers
seems to be the utmost solution. What can be done with
discrete electronic circuits inside the devices can now easily
be implemented within the embedded software of the
controller (i.e. a short circuit protection can be implemented
with a bulky crowbar circuit or simply with a fast loop in the
C). As a result, this projects aims at putting together a robust
microcontroller based power supply unit with easy access
LCD screen, 0-30V output range (up to 80W), computer
connectivity and control.
6. RESULT
The document leakage protection system to
implement with the help of RFID system to stop the
malpractice of leaking the important and confidential
documents.
7. CONCLUSION
After implementation of embedded based document
leakage protection system we conclude that security various
important and confidential documents. RFID based document
leakage protection system use of various hardware properties
like the RFID reader and Tag buzzer. Microcontroller, LCD,
GSM and Power Supply. The swapping of tag, validity of the
user and the reply of code provide the working of the motor
document leakage protection system and display in the LCD.
REFERENCES
[1].
[2].
[3].
[4].
[5].
K. Ray and K. M. Bhurchandi, Advanced microprocessors and
peripherals: architecture, programming and interfacing. New Delhi:
Teta McGraw-Hill Pub.Co, 2000. Call No. TK7895 Mic.Ra
A. P. Chandrakasan, W. Bowhill and F. Fox, Eds. Design of highperformance microprocessor circuits. New York: IEEE Press, 2001.
Call No. TK7895 Mic.Ch
A. V. Deshmukh, Microcontrollers: theory and applications. New
Delhi: Tata McGraw-Hill, 2005. Call No. TJ223 Pro.De
A. Williams, Microcontroller projects with Basic Stamps.
Lawrence, Kan.: R&D, 2000. Call No. TJ223 Pro.Wi
B. B. Brey, The Intel microprocessors: 8086/8088, 80186/80188,
80286, 80386, 80486, Pentium, Pentium Pro processor, Pentium II,
385
Pentium III, and Pentium 4: architecture, programming, and
interfacing, 6th ed., Upper Saddle River, N. J.: Prentice Hall, 2003. Call
No. QA76.8 Int.Br
C. Hellebuyck, Programming PIC microcontrollers using PicBasic.
Amsterdam: Newnes, 2003. Call No. TJ223 Pro.He
C. J. Bergquist, Guide to PICMICRO microcontrollers.
Indianapolis, Ind.: Prompt Publications, 2001. Call No. TJ223 Pro.Be
C. Kuhnel and K. Zahnert, BASIC stamp. Boston: Newnes, 2000.
Call No. TJ223 Pro.Ku
C. Nagy, Embedded systems design using the TI MSP430 series.
Amsterdam; Boston: Newnes, 2003. Call No. TK7895 Emb.Na
D. A. Geller, Programmable controllers using the Allen-Bradley
SLC-500 family. Upper Saddle River, N.J.: Prentice Hall, 2000. Call
No. TJ223 Pro.Ge
Вам также может понравиться
- Channel Coding: Theory, Algorithms, and Applications: Academic Press Library in Mobile and Wireless CommunicationsОт EverandChannel Coding: Theory, Algorithms, and Applications: Academic Press Library in Mobile and Wireless CommunicationsОценок пока нет
- RFID Based Employee Attendance System Complete ReportДокумент174 страницыRFID Based Employee Attendance System Complete Reportvivek singh96% (27)
- Vehicle Tracking and Ticketing System Using RFID Muy Bueno Pero en Ingles ImagenesДокумент32 страницыVehicle Tracking and Ticketing System Using RFID Muy Bueno Pero en Ingles ImagenesFé GabrielaОценок пока нет
- Rfid Project ReportДокумент65 страницRfid Project Reportgsrawat123Оценок пока нет
- E Chem Analyst Software ManualДокумент45 страницE Chem Analyst Software ManualPrima RizkiОценок пока нет
- RFID Based Chalan SystemДокумент7 страницRFID Based Chalan Systemفہد رضاОценок пока нет
- RFID Project ReportДокумент53 страницыRFID Project Reportchhavigupta168933% (3)
- Automatic Car Parking System-1Документ75 страницAutomatic Car Parking System-1Hai DoanОценок пока нет
- RFID Based Attendance and Security SystemДокумент12 страницRFID Based Attendance and Security SystemAmit ChauhanОценок пока нет
- Animal IdentificationДокумент19 страницAnimal IdentificationMaryam QuadriОценок пока нет
- Rfid Based Telemedicine SystemДокумент18 страницRfid Based Telemedicine SystemTilottama DeoreОценок пока нет
- Rfid Based Vehicle Tracking SystemДокумент8 страницRfid Based Vehicle Tracking SystemprakashbkОценок пока нет
- True Cost of RfidДокумент16 страницTrue Cost of RfidJaldeep KarasaliyaОценок пока нет
- RFID Based Automatic Vehicle Parking SystemДокумент6 страницRFID Based Automatic Vehicle Parking SystemSanjay VjОценок пока нет
- PPTДокумент69 страницPPTAjit MishraОценок пока нет
- Automatic Car Parking System-1Документ16 страницAutomatic Car Parking System-1Vishvesh BaliОценок пока нет
- Chipless RFID Reader Design for Ultra-Wideband Technology: Design, Realization and CharacterizationОт EverandChipless RFID Reader Design for Ultra-Wideband Technology: Design, Realization and CharacterizationОценок пока нет
- Chipless RFID based on RF Encoding Particle: Realization, Coding and Reading SystemОт EverandChipless RFID based on RF Encoding Particle: Realization, Coding and Reading SystemОценок пока нет
- RFID Inventory TrackingДокумент20 страницRFID Inventory TrackingGaurav KumarОценок пока нет
- RFID Handbook: Fundamentals and Applications in Contactless Smart Cards, Radio Frequency Identification and Near-Field CommunicationОт EverandRFID Handbook: Fundamentals and Applications in Contactless Smart Cards, Radio Frequency Identification and Near-Field CommunicationОценок пока нет
- Abcs of RfidДокумент6 страницAbcs of RfidGeny KucherОценок пока нет
- RFID Based Prepaid Energy MeterДокумент38 страницRFID Based Prepaid Energy MeterSaad Ali100% (1)
- RFID Based Women Security SystemДокумент39 страницRFID Based Women Security SystemDebashishParidaОценок пока нет
- RFID Explained - What is RFID and How Does it WorkДокумент7 страницRFID Explained - What is RFID and How Does it WorkBharat KhanejaОценок пока нет
- RFID Based Prepaid Energy MeterДокумент7 страницRFID Based Prepaid Energy MeterBilal KhanОценок пока нет
- Rfid - An Attempt To Make: Everything AutomaticДокумент10 страницRfid - An Attempt To Make: Everything AutomaticRichard LoboОценок пока нет
- Low Cost RFID Library ManagementДокумент5 страницLow Cost RFID Library ManagementKrunal PadmaniОценок пока нет
- MCA RFID Report PDFДокумент16 страницMCA RFID Report PDFDIVYA RОценок пока нет
- RFID Toll Tax SystemДокумент12 страницRFID Toll Tax SystemDevender Singh PahlawatОценок пока нет
- WMC Seminar ReportДокумент11 страницWMC Seminar ReportVijit SinghОценок пока нет
- RFID Modules & Guideline For Selecting Appropriate RFID Module For IndustriesДокумент4 страницыRFID Modules & Guideline For Selecting Appropriate RFID Module For IndustriesInternational Journal of Application or Innovation in Engineering & ManagementОценок пока нет
- C C C C CCC !"#"#$% !Документ9 страницC C C C CCC !"#"#$% !Milin PatelОценок пока нет
- JKMДокумент78 страницJKMShaanu ShaanОценок пока нет
- SBA-RFID Feasibility StudyДокумент13 страницSBA-RFID Feasibility StudyMobileLeadersОценок пока нет
- Privacy and security issues of low-cost RFID tagsДокумент8 страницPrivacy and security issues of low-cost RFID tagssidhubrarОценок пока нет
- Electromagnetic Fields: Radio-Frequency Identification (RFID) Is The Wireless Non-Contact Use of RadioДокумент2 страницыElectromagnetic Fields: Radio-Frequency Identification (RFID) Is The Wireless Non-Contact Use of RadioVinnu KumarОценок пока нет
- Kwame Nkrumah University of Science and TechnologyДокумент18 страницKwame Nkrumah University of Science and TechnologyGilbert DansoОценок пока нет
- Authentication and Lightweight Cryptography in Low Cost RfidДокумент7 страницAuthentication and Lightweight Cryptography in Low Cost RfidGautam KunalОценок пока нет
- Seminar Report: Nini P SureshДокумент31 страницаSeminar Report: Nini P SureshNini P SureshОценок пока нет
- RFID Based Attendance System: Chapter SummariesДокумент35 страницRFID Based Attendance System: Chapter SummariespriyaОценок пока нет
- Research Paper On Radio Frequency IdentificationДокумент5 страницResearch Paper On Radio Frequency Identificationfemeowplg100% (1)
- Rfid Reader:: Access ControlДокумент10 страницRfid Reader:: Access ControlSridevi KesanakurthiОценок пока нет
- RFID Applications: An Introductory and Exploratory StudyДокумент7 страницRFID Applications: An Introductory and Exploratory StudyDorothy BrewerОценок пока нет
- IntroductionДокумент17 страницIntroductionrtpatil76Оценок пока нет
- Security Framework For RFID-based Applications in Smart Home EnvironmentДокумент10 страницSecurity Framework For RFID-based Applications in Smart Home EnvironmentAlwaleed AlssamaniОценок пока нет
- Radio Frequency Identification (Rfid) : BackgroundДокумент4 страницыRadio Frequency Identification (Rfid) : BackgroundAshutosh PatriОценок пока нет
- Rfid Technology: What Is RFID and How Will It Help You?Документ8 страницRfid Technology: What Is RFID and How Will It Help You?payal samantaОценок пока нет
- RFID Security and Privacy: A Research Survey: Ari JuelsДокумент14 страницRFID Security and Privacy: A Research Survey: Ari JuelsAhmedAzriОценок пока нет
- RFID InfrastructureДокумент18 страницRFID InfrastructureSubash Chandra VarmaОценок пока нет
- Use of RFID For Safety at School/Hospital Campus: Sushil I. Bakhtar and Prof. Ram S. DhekekarДокумент4 страницыUse of RFID For Safety at School/Hospital Campus: Sushil I. Bakhtar and Prof. Ram S. DhekekarSushil BakhtarОценок пока нет
- Human ID Implant Seminar ReportДокумент23 страницыHuman ID Implant Seminar Report20261A3232 LAKKIREDDY RUTHWIK REDDYОценок пока нет
- Rfid SeminarДокумент7 страницRfid Seminaranon_344748121Оценок пока нет
- Technology Radio Waves: Radio-Frequency Identification (RFID) Is AДокумент9 страницTechnology Radio Waves: Radio-Frequency Identification (RFID) Is ANeha GambhirОценок пока нет
- N Recent YearsДокумент10 страницN Recent YearsMukesh KumarОценок пока нет
- RFID Project Report SummaryДокумент38 страницRFID Project Report SummarySaloni JainОценок пока нет
- Integration of RFID and Wireless Sensor Networks: 1.2 Tags and Frequency RangesДокумент6 страницIntegration of RFID and Wireless Sensor Networks: 1.2 Tags and Frequency RangesMahmoud El-tabeyОценок пока нет
- Building the Internet of Things with IPv6 and MIPv6: The Evolving World of M2M CommunicationsОт EverandBuilding the Internet of Things with IPv6 and MIPv6: The Evolving World of M2M CommunicationsОценок пока нет
- EC6411 Circuits and Simulation Lab Experiments and RequirementsДокумент2 страницыEC6411 Circuits and Simulation Lab Experiments and Requirementssamsath10Оценок пока нет
- ECE Regulation 2017 Full SyllabusДокумент121 страницаECE Regulation 2017 Full SyllabusNandha KumarОценок пока нет
- EC2035 CANS Nov Dec 2014 QPДокумент3 страницыEC2035 CANS Nov Dec 2014 QPsamsath10Оценок пока нет
- Band Pass Filter MultisimДокумент2 страницыBand Pass Filter Multisimsamsath10Оценок пока нет
- Prog MicroprocessorДокумент9 страницProg Microprocessorbabji049Оценок пока нет
- EC6304 SyllabusДокумент2 страницыEC6304 Syllabussamsath10Оценок пока нет
- Question Bank: Unit I Part AДокумент4 страницыQuestion Bank: Unit I Part Asamsath10Оценок пока нет
- EC6503 TLW SyllabusДокумент1 страницаEC6503 TLW Syllabussamsath10Оценок пока нет
- Anna University Report FormatДокумент7 страницAnna University Report Formatdilip_66690% (10)
- Design and Implementation of Environment Sensing System Based On Gsm/Gprs Using Embedded Controlled Sensor NetworkДокумент4 страницыDesign and Implementation of Environment Sensing System Based On Gsm/Gprs Using Embedded Controlled Sensor Networksamsath10Оценок пока нет
- Low Complexity Implementation of LDPC Decoder UsingДокумент5 страницLow Complexity Implementation of LDPC Decoder Usingsamsath10Оценок пока нет
- SensorsДокумент22 страницыSensorssamsath10Оценок пока нет
- CSE - Sem 7 - WN SyllabusДокумент23 страницыCSE - Sem 7 - WN Syllabussamsath10Оценок пока нет
- WN April May 14Документ1 страницаWN April May 14samsath10Оценок пока нет
- WN April-May 2015Документ2 страницыWN April-May 2015samsath10Оценок пока нет
- HP Pavilion ZE2000 (AMD) - Pavilion dv1000 (AMD) - HP Compaq Presario M2000 (AMD) PDFДокумент41 страницаHP Pavilion ZE2000 (AMD) - Pavilion dv1000 (AMD) - HP Compaq Presario M2000 (AMD) PDFMarcos Alessandro Santana SantosОценок пока нет
- (11.2C.30 - Bahasa Inggris II) Tugas Pertemuan Ke-6Документ2 страницы(11.2C.30 - Bahasa Inggris II) Tugas Pertemuan Ke-6Argim Aegiza ArkanantaОценок пока нет
- Maxtor M3 Portable - User Manual-EN - E01 - 19 05 2016 PDFДокумент22 страницыMaxtor M3 Portable - User Manual-EN - E01 - 19 05 2016 PDFAhmad ElsheemyОценок пока нет
- MPMCДокумент7 страницMPMCSivaprasad ReddyОценок пока нет
- MIPS AssemblyInstruction FormatsДокумент5 страницMIPS AssemblyInstruction Formatsfeezy1100% (1)
- Serial Number Range GuideДокумент106 страницSerial Number Range GuideLeobardo Genaro Roque NájeraОценок пока нет
- Gamecloud Technologies PVT LTD - ARVR Game Testing CompanyДокумент6 страницGamecloud Technologies PVT LTD - ARVR Game Testing CompanyGC marketingОценок пока нет
- Aspirating Smoke Detector: Technical DescriptionДокумент115 страницAspirating Smoke Detector: Technical DescriptionSecuriton ArgentinaОценок пока нет
- 001 Bizgram Asia Pricelist December 23HДокумент15 страниц001 Bizgram Asia Pricelist December 23HBizgram AsiaОценок пока нет
- Aster Analytics Foundation 0510Документ611 страницAster Analytics Foundation 0510Emanuele ParenteОценок пока нет
- Alat SMK 2018Документ16 страницAlat SMK 2018Jae Tama Grand'sОценок пока нет
- E FlexДокумент124 страницыE FlexsawarОценок пока нет
- Service Fs c2026mfp c2126Документ365 страницService Fs c2026mfp c2126abm503181Оценок пока нет
- W 27 e 512Документ16 страницW 27 e 512MassimoОценок пока нет
- NtbtlogДокумент32 страницыNtbtlogVictor FernandezОценок пока нет
- Dse500 ManualДокумент18 страницDse500 ManualHuannt Huan0% (1)
- Techline La25 Actuator User Manual EngДокумент80 страницTechline La25 Actuator User Manual EngOPG serviceОценок пока нет
- Chapter8 SlidesДокумент36 страницChapter8 Slidesrandomname112Оценок пока нет
- Products3329CM284 S12Документ2 страницыProducts3329CM284 S12Imran ShaukatОценок пока нет
- How to Build a Twig Stove: An 11-Step GuideДокумент14 страницHow to Build a Twig Stove: An 11-Step GuideJohnnОценок пока нет
- Inventor 2014 Application OptionsДокумент21 страницаInventor 2014 Application OptionsDobrica PetrovicОценок пока нет
- BlackBerry 10 OS Version 10.3.2 10.3.1.2576-10.3.2.2474Документ23 страницыBlackBerry 10 OS Version 10.3.2 10.3.1.2576-10.3.2.2474MahmoudОценок пока нет
- Coding Decoding For IBPS ExamДокумент10 страницCoding Decoding For IBPS ExamlenovojiОценок пока нет
- Imode: An Introduction: Imode: Inception, Presence and ImpactДокумент30 страницImode: An Introduction: Imode: Inception, Presence and Impactapi-19937584100% (1)
- DX DiagДокумент31 страницаDX DiagJhon SaucedoОценок пока нет
- Installation Instructions: 18SP548-Install Exhaust Back Pressure Sensor Kit On Series 50 or Series 60 Diesel Coach EngineДокумент10 страницInstallation Instructions: 18SP548-Install Exhaust Back Pressure Sensor Kit On Series 50 or Series 60 Diesel Coach EngineHamilton MirandaОценок пока нет
- Linux UnhatchedДокумент24 страницыLinux UnhatchedGeorgiana SimaОценок пока нет
- Cisco Tvoice Tshoot Planning PDFДокумент495 страницCisco Tvoice Tshoot Planning PDFGoutham BaratamОценок пока нет
- Poweredge r740 - Users Guide3 - en UsДокумент57 страницPoweredge r740 - Users Guide3 - en UsSarut LapthaweechokОценок пока нет