Академический Документы
Профессиональный Документы
Культура Документы
Open Proxies
Загружено:
Kunal Singh Choudhary0 оценок0% нашли этот документ полезным (0 голосов)
32 просмотров1 страницаOpen Proxies
Авторское право
© © All Rights Reserved
Доступные форматы
TXT, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документOpen Proxies
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате TXT, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
32 просмотров1 страницаOpen Proxies
Загружено:
Kunal Singh ChoudharyOpen Proxies
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате TXT, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 1
Open proxies[edit]
Diagram of proxy server connected to the Internet.
An open proxy forwarding requests from and to anywhere on the Internet.
Main article: Open proxy
An open proxy is a forwarding proxy server that is accessible by any Internet us
er. Gordon Lyon estimates there are "hundreds of thousands" of open proxies on t
he Internet.[3] An anonymous open proxy allows users to conceal their IP address
while browsing the Web or using other Internet services. There are varying degr
ees of anonymity however, as well as a number of methods of 'tricking' the clien
t into revealing itself regardless of the proxy being used.
Reverse proxies[edit]
A proxy server connecting the Internet to an internal network.
A reverse proxy taking requests from the Internet and forwarding them to servers
in an internal network. Those making requests connect to the proxy and may not
be aware of the internal network.
Main article: Reverse proxy
A reverse proxy (or surrogate) is a proxy server that appears to clients to be a
n ordinary server. Requests are forwarded to one or more proxy servers which han
dle the request. The response from the proxy server is returned as if it came di
rectly from the original server, leaving the client no knowledge of the origin s
ervers.[4] Reverse proxies are installed in the neighborhood of one or more web
servers. All traffic coming from the Internet and with a destination of one of t
he neighborhood's web servers goes through the proxy server. The use of "reverse
" originates in its counterpart "forward proxy" since the reverse proxy sits clo
ser to the web server and serves only a restricted set of websites. There are se
veral reasons for installing reverse proxy servers:
Encryption / SSL acceleration: when secure web sites are created, the Secure Soc
kets Layer (SSL) encryption is often not done by the web server itself, but by a
reverse proxy that is equipped with SSL acceleration hardware. Furthermore, a h
ost can provide a single "SSL proxy" to provide SSL encryption for an arbitrary
number of hosts; removing the need for a separate SSL Server Certificate for eac
h host, with the downside that all hosts behind the SSL proxy have to share a co
mmon DNS name or IP address for SSL connections. This problem can partly be over
come by using the SubjectAltName feature of X.509 certificates.
Load balancing: the reverse proxy can distribute the load to several web servers
, each web server serving its own application area. In such a case, the reverse
proxy may need to rewrite the URLs in each web page (translation from externally
known URLs to the internal locations).
Serve/cache static content: A reverse proxy can offload the web servers by cachi
ng static content like pictures and other static graphical content.
Compression: the proxy server can optimize and compress the content to speed up
the load time.
Spoon feeding: reduces resource usage caused by slow clients on the web servers
by caching the content the web server sent and slowly "spoon feeding" it to the
client. This especially benefits dynamically generated pages.
Security: the proxy server is an additional layer of defense and can protect aga
inst some OS and Web Server specific attacks. However, it does not provide any p
rotection from attacks against the web application or service itself, which is g
enerally considered the larger threat.
Extranet Publishing: a reverse proxy server facing the Internet can be used to c
ommunicate to a firewall server internal to an organization, providing extranet
access to some functions while keeping the servers behind the firewalls. If used
in this way, security measures should be considered to protect the rest of your
infrastructure in case this server is compromised, as its web application is ex
posed to attack from the Internet.
Вам также может понравиться
- Computer FundamentalДокумент19 страницComputer Fundamentalredcard53Оценок пока нет
- Ics e Helpline 101Документ1 страницаIcs e Helpline 101Kunal Singh ChoudharyОценок пока нет
- Computer Java Arrays Notes Compiled by Anmol Agarwal1 PDFДокумент12 страницComputer Java Arrays Notes Compiled by Anmol Agarwal1 PDFKunal Singh ChoudharyОценок пока нет
- Important BST NotesДокумент55 страницImportant BST NotesKunal Singh ChoudharyОценок пока нет
- Doc16 17Документ1 страницаDoc16 17Kunal Singh ChoudharyОценок пока нет
- Important Notes of EconomicsДокумент49 страницImportant Notes of EconomicsKunal Singh ChoudharyОценок пока нет
- Railway Recruitment Board, Malda, Govt. of India (Ministry of Railways)Документ20 страницRailway Recruitment Board, Malda, Govt. of India (Ministry of Railways)Kunal Singh ChoudharyОценок пока нет
- Learn Astrology The Easy Way by G.S Kapoor PDFДокумент245 страницLearn Astrology The Easy Way by G.S Kapoor PDFAbo Habib100% (29)
- Open VPNДокумент3 страницыOpen VPNKunal Singh ChoudharyОценок пока нет
- Kolkata RailwaysДокумент97 страницKolkata RailwaysKunal Singh ChoudharyОценок пока нет
- GrapheneДокумент3 страницыGrapheneKunal Singh ChoudharyОценок пока нет
- Cen 02 2015ntpc Ug SRDДокумент5 страницCen 02 2015ntpc Ug SRDKunal Singh ChoudharyОценок пока нет
- PanelCEN 2012Документ12 страницPanelCEN 2012Kunal Singh ChoudharyОценок пока нет
- Astronomy Relevant To Astrology by V.P. JainДокумент142 страницыAstronomy Relevant To Astrology by V.P. Jainsaluja_rajinder2031100% (1)
- Top 5 Grammar Books For IELTSДокумент2 страницыTop 5 Grammar Books For IELTSKunal Singh ChoudharyОценок пока нет
- 10 by Kult UM Kult Warranty CardДокумент31 страница10 by Kult UM Kult Warranty CardKunal Singh ChoudharyОценок пока нет
- Kult 10 Service CenterДокумент1 страницаKult 10 Service CenterKunal Singh ChoudharyОценок пока нет
- Transmission Control Protocol (TCP)Документ1 страницаTransmission Control Protocol (TCP)Kunal Singh ChoudharyОценок пока нет
- Trivial File Transfer ProtocolДокумент3 страницыTrivial File Transfer ProtocolKunal Singh ChoudharyОценок пока нет
- An Antarctic Mystery PDFДокумент388 страницAn Antarctic Mystery PDFKunal Singh ChoudharyОценок пока нет
- Transmission Control Protocol (TCP)Документ2 страницыTransmission Control Protocol (TCP)Kunal Singh ChoudharyОценок пока нет
- Reverse ProxyДокумент1 страницаReverse ProxyKunal Singh ChoudharyОценок пока нет
- Execute JavaДокумент1 страницаExecute JavaKunal Singh ChoudharyОценок пока нет
- Twenty Thousand Leagues Under The Sea PDFДокумент354 страницыTwenty Thousand Leagues Under The Sea PDFKunal Singh ChoudharyОценок пока нет
- The Usborne Illustrated Dictionary of Maths (gnv64) PDFДокумент131 страницаThe Usborne Illustrated Dictionary of Maths (gnv64) PDFAnonymous 6HADGUEXD88% (24)
- Q. 1 A) B) C) D) Q. 2 A) B) C) D) Q. 3 A) B) C) D) Q. 4 A) B) C) D) Q. 5Документ3 страницыQ. 1 A) B) C) D) Q. 2 A) B) C) D) Q. 3 A) B) C) D) Q. 4 A) B) C) D) Q. 5Kunal Singh ChoudharyОценок пока нет
- Q. 1 A) B) C) D) Q. 2 A) B) C) D) Q. 3 A) B) C) D) Q. 4 A) B) C) D) Q. 5Документ3 страницыQ. 1 A) B) C) D) Q. 2 A) B) C) D) Q. 3 A) B) C) D) Q. 4 A) B) C) D) Q. 5Kunal Singh ChoudharyОценок пока нет
- X ElectronДокумент1 страницаX ElectronKunal Singh ChoudharyОценок пока нет
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
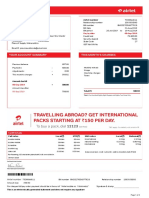
- July To August 19 Mobile BillДокумент15 страницJuly To August 19 Mobile BillPravin AwalkondeОценок пока нет
- Channel Unit E&M VF-P Op HandbookДокумент97 страницChannel Unit E&M VF-P Op HandbookzehantnОценок пока нет
- Azure Network BasicsДокумент11 страницAzure Network BasicsI'm RangaОценок пока нет
- JNCIE SEC v1.3 Workbook 2018Документ20 страницJNCIE SEC v1.3 Workbook 2018Chris Brown100% (1)
- How To Configure and Reset Alcatel-Lucent I-240G-D Router 2Документ1 страницаHow To Configure and Reset Alcatel-Lucent I-240G-D Router 2DylanОценок пока нет
- C01 IntroductionДокумент31 страницаC01 IntroductionpadmareddyjОценок пока нет
- SVA Data PlanningДокумент5 страницSVA Data PlanningFarrukhmohdОценок пока нет
- Sno. Input Required: Enter Value Enter ValueДокумент8 страницSno. Input Required: Enter Value Enter ValueBapun DayaОценок пока нет
- Midterm Assignment6 JarantillaДокумент2 страницыMidterm Assignment6 JarantillaLeague of RònОценок пока нет
- Cellular and Mobile CommunicationsДокумент6 страницCellular and Mobile CommunicationsSudeepSah100% (2)
- USART Vs UART Know The DifferenceДокумент2 страницыUSART Vs UART Know The DifferenceSandra Daniela RotaruОценок пока нет
- AMOS 4 EnglishДокумент8 страницAMOS 4 EnglishdugizulОценок пока нет
- Telegrame v90Документ18 страницTelegrame v90benachour ismailОценок пока нет
- CSIS 110 - Chapter 6Документ75 страницCSIS 110 - Chapter 6khattarОценок пока нет
- Cox SIP Trunking Configuration Guide v2.1 - Cisco UCM 8.6.2 With CUBE - Doc - Sip-config-guide-cisco-ucm862-CubeДокумент95 страницCox SIP Trunking Configuration Guide v2.1 - Cisco UCM 8.6.2 With CUBE - Doc - Sip-config-guide-cisco-ucm862-Cubekayudo80Оценок пока нет
- IT AssingmentДокумент20 страницIT AssingmentLeen NisОценок пока нет
- AU80 v17.5 To v18.0 XG Firewall Training UpdateДокумент109 страницAU80 v17.5 To v18.0 XG Firewall Training UpdateEudes MillánОценок пока нет
- CommunicationДокумент12 страницCommunicationabirami sОценок пока нет
- 43MR LCF12 C03Документ2 страницы43MR LCF12 C03Luciano Silvério LeiteОценок пока нет
- The ROADM ComponentsДокумент4 страницыThe ROADM ComponentsRaviОценок пока нет
- La1837 La1837Документ10 страницLa1837 La1837Nath MateoОценок пока нет
- Subnetting 1Документ10 страницSubnetting 1Amro GoneimОценок пока нет
- Network Security Engineer (PT. Sentra Paramitra)Документ1 страницаNetwork Security Engineer (PT. Sentra Paramitra)Yoga “HighFootball” KoswaraОценок пока нет
- Slide - 2 (Amplitude Modulation)Документ36 страницSlide - 2 (Amplitude Modulation)Shuvo DevОценок пока нет
- CTR V04-2 Fall 1974Документ153 страницыCTR V04-2 Fall 1974aldern_foxgloveОценок пока нет
- CCNPv6 SWITCH Lab7-3 Voice Security Case Study InstructorДокумент7 страницCCNPv6 SWITCH Lab7-3 Voice Security Case Study InstructorAarón Fonseca CandiaОценок пока нет
- Analysis RCA GuidelineДокумент19 страницAnalysis RCA GuidelineAnshul Gupta100% (1)
- Zebra Xi Series Maintenance Manual For 105s-140xiДокумент218 страницZebra Xi Series Maintenance Manual For 105s-140xiJosé PerezОценок пока нет
- SIAE AlfoPlus2 User ManualДокумент136 страницSIAE AlfoPlus2 User ManualConnor MilliganОценок пока нет
- Mikrotik Routeros™ V3.0: Reference ManualДокумент302 страницыMikrotik Routeros™ V3.0: Reference Manualvj-arifОценок пока нет