Академический Документы
Профессиональный Документы
Культура Документы
Rule 41 Letter To DOJ From Congress October 2016
Загружено:
Michael Lowe, Attorney at Law0 оценок0% нашли этот документ полезным (0 голосов)
508 просмотров3 страницыOctober 2016 Letter from bipartisan members of Congress to Attorney General addressing concerns with privacy protections under amendment rule 41 of the Federal Rules of Criminal Procedure.
Оригинальное название
Rule 41 Letter to DOJ From Congress October 2016
Авторское право
© © All Rights Reserved
Доступные форматы
PDF или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документOctober 2016 Letter from bipartisan members of Congress to Attorney General addressing concerns with privacy protections under amendment rule 41 of the Federal Rules of Criminal Procedure.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PDF или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
508 просмотров3 страницыRule 41 Letter To DOJ From Congress October 2016
Загружено:
Michael Lowe, Attorney at LawOctober 2016 Letter from bipartisan members of Congress to Attorney General addressing concerns with privacy protections under amendment rule 41 of the Federal Rules of Criminal Procedure.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PDF или читайте онлайн в Scribd
Вы находитесь на странице: 1из 3
Congress of the United States
Washington, BC 20510
October 27, 2016
The Honorable Loretta Lynch
United States Attorney General
Department of Justice
950 Pennsylvania Avenue, N.W.
‘Washington, D.C. 20530
Dear Attorney General Lynch:
We write to request information regarding the Department of Justice’s proposed amendments to
Rule 41 of the Federal Rules of Criminal Procedure. These amendments were approved by the
Supreme Court and transmitted to Congress pursuant to the Rules Enabling Act on April 30,
2016. Absent congressional action the amendments will take effect on December 1, 2016.
‘The proposed amendments to Rule 41 have the potential to significantly expand the
Department's ability to obtain a warrant to engage in “remote access,” or hacking of computers
and other electronic devices, We are concerned about the full scope of the new authority that
‘would be provided to the Department of Justice. We believe that Congress -- and the American
public -- must better understand the Department's need for the proposed amendments, how the
‘Department intends to use its proposed new powers, and the potential consequences to our digital
security before these rules go into effect. In light of the limited time for congressional
consideration of the proposed amendments, we tequest that you provide us with the following
information two weeks after your receipt of this letter.
1. How would the goverment prevent “forum shopping” under the proposed
amendments? The proposed amendments would allow prosecutors to seek a warrant in
any district “where activities related to a crime may have occurred,” Will the Department
issue guidance to prosecutors on how this should be interpreted?
2, We are concemed that the deployment of software to search for and possibly disable a
botnet may have unintended consequences on intemet-connected devices, from
smartphones to medical devices. Please describe the testing that is conducted on the
viability of ‘network investigative techniques’ (“NITs”) to safely search devices such as
phones, tablets, hospital information systems, and internet-connected video monitoring
systems.
3. Will law enforcement use authority under the proposed amendments to disable o
otherwise render inoperable software that is damaging or has damaged a protected
device? In other words, will network investigative techniques be used to “clean” infected
devices, including devices that belong to innocent Americans? Has the Department ever
attempted to “clean” infected computers in the past? If so, under what legal authority?
|. What methods will the Department use to notify users and owners of devices that have
been searched, particularly in potential cases where tens of thousands of devices are
searched?
. How will the Department maintain proper chain of custody when analyzing or removing
evidence from a suspect’s device? Please describe how the Department intends to
address technical issues such as fluctuations of internet speed and limitations on the
ability to securely transfer data,
. Please describe any differences in legal requirements between obtaining a warrant for a
physical search versus obtaining a warrant for a remote electronic search. In particular,
and if applicable, please describe how the principle of probable cause may be used to
justify the remote search of tens of thousands of devices. Is it sufficient probable cause
for a search that a device merely be “damaged” and connected to a crime?
Ifthe Department were to search devices belonging to innocent Americans to combat a
complicated computer crime, please describe what procedures the Department would use
to protect the private information of victims and prevent further damage to accessed
devices.
Sincerely,
Ron Wyden
United States Senator
ahah Ke
Patrick Leahy
United States Senator
United States Senator
Ted Poe
Member of Congress
Member of Congress
mn Chaffetz
‘Member of Congress
Dhue. Dare
ye Daines Tad, u
United States Senat Mehber of
‘Al Franken sRccthen
United States Senator ‘Member of Congress
- ’
‘Mazie W/ Hirono Suzan TefBens
United States Senator Lo ‘Member of Congress
KCK. ,
Mike Lee LouieGohmet =
United States Senator ‘Memiber of Congress
fel Ahn aleflleinn
Inited States Senator Member of Congress
bbl W ice
Ted W. Liew
Usted States Senator ‘Member of Congress
Martin Heinrich Lofgre
United States Senator ber of Pongress
Jerrold Nadler —
Member of Congress
Вам также может понравиться
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- PPP FRAUD INDICTMENT Southern District of Texas (Houston)Документ18 страницPPP FRAUD INDICTMENT Southern District of Texas (Houston)Michael Lowe, Attorney at LawОценок пока нет
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- Texas Mexican Mafia ConstitutionДокумент9 страницTexas Mexican Mafia ConstitutionMichael Lowe, Attorney at LawОценок пока нет
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- State Bar of Texas Grievance Complaint Against John JacksonДокумент72 страницыState Bar of Texas Grievance Complaint Against John JacksonMichael Lowe, Attorney at LawОценок пока нет
- Good Time Table 2019Документ4 страницыGood Time Table 2019Michael Lowe, Attorney at LawОценок пока нет
- Top 10 Mistakes in Sexual Assault and Indecency With A Child CasesДокумент9 страницTop 10 Mistakes in Sexual Assault and Indecency With A Child CasesMichael Lowe, Attorney at LawОценок пока нет
- Texas Sex Offender Deregistration Synopsis: Overview and Steps For Name RemovalДокумент7 страницTexas Sex Offender Deregistration Synopsis: Overview and Steps For Name RemovalMichael Lowe, Attorney at LawОценок пока нет
- Motion For Release of Brendan Dassey Pending Appeal of Wrongful Conviction RulingДокумент48 страницMotion For Release of Brendan Dassey Pending Appeal of Wrongful Conviction RulingMichael Lowe, Attorney at Law100% (1)
- Ray Jackson Complaint AffidavitДокумент16 страницRay Jackson Complaint AffidavitMichael Lowe, Attorney at LawОценок пока нет
- 18 Uscs - 2252Документ3 страницы18 Uscs - 2252Michael Lowe, Attorney at LawОценок пока нет
- Sent Hearing Dec 8Документ6 страницSent Hearing Dec 8Michael Lowe, Attorney at LawОценок пока нет
- Transcript Jan. 8, 2018Документ23 страницыTranscript Jan. 8, 2018Julie Turkewitz100% (1)
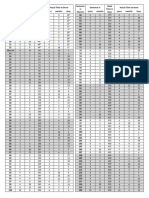
- 2016 U.S. Sentencing TableДокумент1 страница2016 U.S. Sentencing TableMichael Lowe, Attorney at Law100% (1)
- JDGMTDEC8Документ4 страницыJDGMTDEC8Michael Lowe, Attorney at LawОценок пока нет
- Jeff Sessions Memo Charging and Sentencing Policy, Dated 10 May 2017Документ2 страницыJeff Sessions Memo Charging and Sentencing Policy, Dated 10 May 2017KimLaCapriaОценок пока нет
- Forest Park Medical Center Kickback IndictmentДокумент44 страницыForest Park Medical Center Kickback IndictmentmedtechyОценок пока нет
- Federal Sentencing Guidelines 2G2.2Документ5 страницFederal Sentencing Guidelines 2G2.2Michael Lowe, Attorney at LawОценок пока нет
- 18 Uscs - 2252Документ3 страницы18 Uscs - 2252Michael Lowe, Attorney at LawОценок пока нет
- Dallas County Bond Schedule 2017Документ2 страницыDallas County Bond Schedule 2017Michael Lowe, Attorney at LawОценок пока нет
- Texas Commission of Judicial Conduct Public Sanctions For FY 2015 Including Public Admonition of Etta MullinДокумент80 страницTexas Commission of Judicial Conduct Public Sanctions For FY 2015 Including Public Admonition of Etta MullinMichael Lowe, Attorney at LawОценок пока нет
- State of Texas Task Force On Domestic Violence Report 2015Документ46 страницState of Texas Task Force On Domestic Violence Report 2015Michael Lowe, Attorney at LawОценок пока нет
- Special Court of Review in Re Etta MullinДокумент29 страницSpecial Court of Review in Re Etta MullinMichael Lowe, Attorney at LawОценок пока нет
- Court of Appeals Notice To CounselДокумент1 страницаCourt of Appeals Notice To CounselMichael Lowe, Attorney at LawОценок пока нет
- USAttyManual ReleaseandDetentionPendingJudclPrcdgsДокумент8 страницUSAttyManual ReleaseandDetentionPendingJudclPrcdgsMichael Lowe, Attorney at LawОценок пока нет
- Cortez WritДокумент2 страницыCortez WritMichael Lowe, Attorney at LawОценок пока нет
- John Wiley Price IndictmentДокумент109 страницJohn Wiley Price IndictmentRobert Wilonsky100% (1)
- Factual Resume in U.S. v. Brian J. PolitoДокумент4 страницыFactual Resume in U.S. v. Brian J. PolitoMichael Lowe, Attorney at LawОценок пока нет
- July 2014 Retroactivity Reduction in Federal Sentencing Guidelines (USSC)Документ9 страницJuly 2014 Retroactivity Reduction in Federal Sentencing Guidelines (USSC)Michael Lowe, Attorney at LawОценок пока нет