Академический Документы
Профессиональный Документы
Культура Документы
IP Multicast Technical Overview
Загружено:
Motasim_mАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
IP Multicast Technical Overview
Загружено:
Motasim_mАвторское право:
Доступные форматы
White Paper
IP Multicast Technical Overview
Last Updated: August, 2007
This paper provides an introductory overview of IP Multicast. It is assumed that the reader
is familiar with TCP/IP and networking in general. Please refer to Beau Williamson's book,
Developing IP Multicast Networks, Volume 1 (Cisco Press), for additional information
relating to the topics discussed in this overview.
Introduction
Traditional IP communications allow a host to send packets to another host (unicast
transmissions) or to all hosts (broadcast transmissions). IP Multicast provides a third
communication alternative: allowing a host to send packets to a group that is made up of a subset
of the hosts on the network. IP Multicast is a bandwidth-conserving technology specifically
designed to reduce traffic by simultaneously delivering a single stream of information to potentially
thousands of corporate recipients or homes. By replacing copies for all recipients with the delivery
of a single stream of information, IP Multicast is able to minimize the burden on both sending and
receiving hosts and reduce overall network traffic. Within a multicast network, routers are
responsible for replicating and distributing multicast content to all hosts that are listening to a
particular multicast group (see Figure 1). Cisco routers employ Protocol Independent Multicast
(PIM) to build distribution trees for transmitting multicast content, resulting in the most efficient
delivery of data to multiple receivers.
Alternatives to IP Multicast require the source to send more than one copy of the data. Traditional
application-level unicast, for example, requires the source to transmit one copy for each individual
receiver in the group.
Figure 1.
Multicast Transmission to Many Receivers
Mutlicast Applications and Environments
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 1 of 9
White Paper
IP Multicast solutions offer benefits relating to the conservation of network bandwidth. In the
case of a high-bandwidth application, such as MPEG video, IP Multicast can benefit situations
with only a few receivers because a few video streams would otherwise consume a large portion
of the available network bandwidth. Even for low-bandwidth applications, IP Multicast conserves
resources when transmissions involve thousands of receivers. Additionally, IP Multicast is the only
nonbroadcasting alternative for situations that require simultaneously sending information to more
than one receiver.
For low-bandwidth applications, an alternative to IP Multicast could involve replicating data at the
source. This solution, however, can deteriorate application performance, introduce latencies and
variable delays that impact users and applications, and require expensive servers to manage the
replications and data distribution. Such solutions also result in multiple transmissions of the same
content, consuming an enormous amount of network bandwidth. For most high-bandwidth
applications, these same issues make IP Multicast the only viable option.
Today, many applications commonly take advantage of multicast, as shown in Figure 2.
Figure 2.
Different Types of IP Multicast Applications
Other applications that take advantage of IP Multicast include:
Corporate communications
Consumer television and music channel delivery
Distance learning (for example, e-learning) and white-boarding solutions
IP surveillance systems
Interactive gaming
IP Multicast is supported in:
IPv4 networks
IPv6 networks
Multiprotocol Label Switching (MPLS) VPNs
Mobile and wireless networks
IP Multicast capabilities can be deployed using a variety of different protocols, conventions,
and considerations suited to the different network environments just mentioned. Multicast services
can also be deployed across multiple protocol platforms and domains within the same network.
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 2 of 9
White Paper
By implementing native IP Multicast functionality inside MPLS VPN networks, service providers
can more efficiently deliver bandwidth-intensive streaming services such as telecommuting,
videoconferencing, e-learning, and a host of other business applications. Cisco Multicast VPN
technology eliminates the packet replication and performance issues associated with the traffic
relating to these applications. Multicast MPLS VPNs further benefit service providers by:
Minimizing configuration time and complexity, configuration is required only at edge routers
Ensuring transparency of the service provider network
Providing the ability to easily build advanced enterprise-friendly services such as
Virtual Multicast Networks
Increasing network scalability
IP Multicast can work with Cisco Mobile Networks. An IP Mobility platform extends the network
with traditional fixed-line access to an environment that supports mobile wireless access. Multicast,
from the point of IP Mobility, is a network service or application. Within an IP Mobility environment,
IP Multicast can be employed to deliver content to users with wireless devices. An example is
the Cisco Mobile Networks Tunnel Template feature. Using this feature, service providers can
configure multicast on statically created tunnels to be applied to dynamic tunnels brought up on
the home agent and mobile router. A tunnel template is defined and applied to the tunnels
between the home agent and mobile router. The mobile router can now roam and the tunnel
template enables multicast sessions to be carried through to mobile users.
Increasing Demand For IP Multicast
Over the past decade, enterprise and public sector adoption of IP Multicast-enabled applications
has skyrocketed (see Figure 3), and service providers have responded by increasingly adding
multicast VPNs to service portfolios. Today, any service provider with enterprise customers must
support IP Multicast to remain competitive. The deployment of video services provides further
incentives for the strengthening of a service providers multicast platform, because it offers the
most efficient, cost-effective means of supporting triple-play traffic (data, voice, and video).
Figure 3.
Multicast Deployments
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 3 of 9
White Paper
Technical Overview
Multicast Groups
Networks using IP Multicast deliver source content to multiple users (hosts or receivers) that are
interested in the data stream. A multicast channel refers to the combination of a content source
IP address and the IP Multicast group address to which the content is being broadcasted. Unlike
unicast/broadcast addresses, multicast groups do not have any physical or geographic
boundaries, and receivers interested in joining can be located anywhere on a network or the
Internet as long as a multicast-enabled path has been established.
To receive a particular multicast data stream, hosts must join a multicast group by sending an
Internet Group Management Protocol (IGMP) message to their local multicast router. Almost all
networks and applications use either IGMP Version 2 or 3. IGMPv2/3 allows individual receivers
to independently join or leave a group.
Content is identified by (S,G) where G is the multicast group and S is the sending source
IP address. The multicast group address lies in the Class D IP address space. The content
provider/owner and service providers select the multicast address based on the local multicast
addressing policy (whether multicast applications are local or global in scope).
Multicast Forwarding and Distribution Trees
In a multicast network, routers are responsible for replicating source content and forwarding it to
multiple recipients. Routers use the PIM protocol to build distribution trees for multicast routing in
the network. Routers replicate source content at any point where the network paths diverge, and
use Reverse Path Forwarding (RPF) techniques to ensure content is forwarded to the appropriate
downstream paths without routing loops.
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 4 of 9
White Paper
Multicast-capable routers dynamically create distribution trees that control the path the content
travels through the network. PIM uses two types of multicast distribution trees: shared trees and
source trees. Services and applications can exclusively use shared trees (Bidirectional [Bi-Dir]),
exclusively use source trees (Source Specific Multicast [SSM]), or use a combination of the two
(Any-Source Multicast [ASM]).
Routers may create shared trees so that a single distribution tree can be shared by all sources.
Alternatively, a separate source tree can be built for each source. Source trees offer the most
optimal paths (and least latency) for multicast traffic, whereas shared trees consume much lower
router memory resources.
Because members of multicast groups can join or leave at any time, distribution trees must be
updated constantly. When all the active receivers on a particular branch stop requesting traffic for
a particular multicast group, routers along the path will prune that branch from the distribution
tree and stop forwarding traffic down that branch. If one receiver on that branch becomes active
and requests the multicast traffic, the router will dynamically modify the distribution tree and
resume forwarding traffic over that branch.
Security Requirements
To protect multicast content and multicast service networks, network administrators should
address the following security considerations:
Service-level security: Networks using IP Multicast can use filtering mechanisms to
ensure that data streams are sent (and new distribution tree branches created) only for
legitimate receivers and requesting routers. Service providers may use SSM along with
Extended ACL support for SSM, which requires that the source address be supplied by any
host requesting to join a multicast group. Using this combination of SSM and Extended ACL
for SSM protects the network from rogue senders that might try to inundate the network
with unauthorized traffic.
Access and admission control: IP Multicast networks should use access control
mechanisms such as access control lists (ACLs) and IGMP access groups to control
access to multicast-capable routers. Quality of service (QoS) policing and queuing
mechanisms, as well as multicast route-limiting mechanisms, provide additional access
control for multicast networks. Multicast authentication, authorization, and accounting (AAA)
integration can also be used for user authentication purposes within a multicast context.
Policing multicast networks: Multicast networks require mechanisms not only to
recognize illegitimate multicast groups, but to disable unauthorized groups, group ranges,
and, if necessary, network routers.
Firewall protection: New Cisco PIX security platforms (such as the Cisco ASA 5500
Series Adaptive Security Appliances running Cisco PIX Firewall Software Version 7.0)
provide PIM support. This feature eliminates the need to tunnel multicast traffic through
the firewall, which would otherwise circumvent security policies.
Native IP Multicast data encryption: New Cisco IOS Secure Multicast provides a set of
hardware and software features necessary to secure IP Multicast group traffic originating
on or flowing through a Cisco IOS device. It combines the keying protocol Group Domain
of Interpretation (GDOI) with IP Security (IPsec) encryption to provide users an efficient
method to secure IP Multicast group traffic. With Cisco IOS Secure Multicast, a router
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 5 of 9
White Paper
can apply encryption to IP Multicast traffic without having to configure generic routing
encapsulation (GRE) tunnels.
High-Availability Considerations
To ensure that critical multicast applications are reliable and highly available, network
administrators delivering IP Multicast services should:
Eliminate any single point of failure: Multicast networks should be architected to protect
the entire path, from the source all the way to every receiver. The loss of any single router
should not result in a disruption to the multicast stream at any point in the network.
Design networks that can dynamically respond to problems: Network architects should
use multicast protocols and strategies, such as anycast techniques for source
redundancy, network topologies that provide path redundancies, and route processor
redundancy in each node. These features ensure that the multicast network can
immediately and automatically respond to the loss of any single source or network
segment, and rapidly rebuild multicast trees as needed.
Build scalability into the network: IP Multicast networks should be able to absorb growth
dynamically, to ensure that usage spikes do not overwhelm the system.
Employ high-availability techniques: Network architects should use mechanisms such as
stateful switchover (SSO) and Cisco In-Service Software Upgrade (ISSU) support to help
ensure availability in multicast IPv4, IPv6, and VPN environments.
Managing Multicast Networks
To effectively manage multicast environments, network administrators can use the following
technologies:
Multicast MIBs, which can be used with Simple Network Management Protocol (SNMP)
tools to assess multicast network performance, identify issues and potential issues, and
plan for network growth
Multicast traps that can notify SNMP tools of multicast problems and errors such as invalid
PIM messages and group changes
Multicast heartbeat mechanisms, which confirm traffic stream activity and help prevent
critical sections of a multicast group from being cut off from the data stream
Multicast Syslog and NetFlow mechanisms, which provide Syslog and NetFlow
information for large-scale network management tools and network event correlation
engines
Cisco Multicast Manager software, which provides a Web-based network management
interface for multicast monitoring, diagnostics, health checks, and reporting
Cisco IP Multicast Technology Leadership
Cisco Systems was an early innovator of IP Multicast, and has provided IP Multicast technology
for more than a decade. The table in Figure 4 highlights important Cisco contributions to multicast
technology between 1994 and 2004.
Figure 4.
Cisco Multicast Industry Contributions
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 6 of 9
White Paper
More recent Cisco IOS Software multicast innovations include:
SSM Mapping for IPv4 and IPv6 Multicast (DNS-based)
Multicast High Availability: Triggered PIM Join
Multicast High Availability: IGMP High Availability
Multicast Subsecond Convergence
Multicast Fast Join/Leave for Faster Channel Change
Multicast Source Redundancy
Multicast AAA Integration
NetFlow Data Export (NDE) v9 for Multicast
IGMP Static-Group Range support
Extended ACL support for IGMP to support SSM
Per-Interface Mroute State Limits
SSM (S,G) filtering support on multicast boundary
Multicast Source Discovery Protocol (MSDP) Message Digest Algorithm 5 (MD5) password
authentication
Multicast Source Discovery Protocol (MSDP) compliance with RFC 3618
No Dense Mode Fallback after Rendezvous Point (RP) information loss
IGMP/MLD Limit Command(s)
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 7 of 9
White Paper
Delivering Multicast Services Within A Cisco IP Next-Generation Network
To effectively respond to changing market and changing customer demands, service providers
require an innovative, converged infrastructure that can accommodate multicast capabilities.
A Cisco IP Next-Generation Network (NGN) provides the:
Mobility of a cellular network, allowing extensive roaming of all its services
Bandwidth of an optical network, transparently supporting any type of service
Flexibility of Ethernet, so that it can be deployed quickly and used easily
Security of a private network, protecting traffic even when a service traverses a
public network
A Cisco IP NGN also allows service providers to achieve:
Levels of service awareness: Recognizing the type, priority, and needs of a service
Service richness: The ability to manage many different and distinct services
simultaneously, with the ability to add more as needed
Service flexibility: The ability to deploy and offer the service in different ways to match the
needs of the customer
For customers, a Cisco IP NGN can deliver a better experience by providing a much broader range
of on-demand services, tailored to their unique needs. At the same time, it simplifies the service
providers operational responsibilities while providing them the means to earn more revenue and
increase brand awareness and customer loyalty.
By providing a highly efficient, cost-effective, and secure means of delivering innovative enterprise
applications and consumer triple-play services, Cisco IP Multicast technologies represent a critical
component of the Cisco IP NGN vision. By employing innovative Cisco IP Multicast strategies,
service providers can immediately enhance service delivery while laying a robust foundation for
future services and applications.
Further Reading
Developing IP Multicast Networks, Cisco Press: http://www.ciscopress.com/title/1578700779
Multicast Introduction: http://www.cisco.com/en/US/tech/tk828/tk363/tsd_technology_support_subprotocol_home.html
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 8 of 9
White Paper
Printed in USA
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
C11-355686-02 8/07
Page 9 of 9
Вам также может понравиться
- Multicast Services For IP Triple-Play Networks: White PaperДокумент14 страницMulticast Services For IP Triple-Play Networks: White PaperDistracted AmesОценок пока нет
- Multicasting: 1. BroadcastДокумент5 страницMulticasting: 1. BroadcastfortuananhОценок пока нет
- Instructions For Seminar-Computer EngineeringДокумент44 страницыInstructions For Seminar-Computer EngineeringAvinash BajajОценок пока нет
- IPV4 Address Classes (32-Bit) : Class Range First BIT Usage Subnet Mask Network Bits Host Bits Private AddressДокумент14 страницIPV4 Address Classes (32-Bit) : Class Range First BIT Usage Subnet Mask Network Bits Host Bits Private Addressjibrangill100% (1)
- What is a WebLogic Server ClusterДокумент16 страницWhat is a WebLogic Server ClusterVeeru SreОценок пока нет
- IPV4 Address Classes (32-Bit) : Class Range First BIT Usage Subnet Mask Network Bits Host Bits Private AddressДокумент16 страницIPV4 Address Classes (32-Bit) : Class Range First BIT Usage Subnet Mask Network Bits Host Bits Private AddressKushal GuptaОценок пока нет
- University University: MulticastingДокумент18 страницUniversity University: MulticastingsaqibОценок пока нет
- Multicast UploadДокумент8 страницMulticast UploadaОценок пока нет
- Key Protocols and Features Supported in The Cisco IOS XR Software Multicast Routing ImplementationДокумент3 страницыKey Protocols and Features Supported in The Cisco IOS XR Software Multicast Routing ImplementationSu ThandaОценок пока нет
- How To Do High-Speed Multicast Right!Документ12 страницHow To Do High-Speed Multicast Right!maindoor1981Оценок пока нет
- Multicasting in WSNs: Benefits and Design Approaches < 40Документ11 страницMulticasting in WSNs: Benefits and Design Approaches < 40Ayonabha ChandraОценок пока нет
- Core RouterДокумент3 страницыCore RouterSu ThandaОценок пока нет
- Multicast-VPN - IP Multicast Support For MPLS VPNsДокумент166 страницMulticast-VPN - IP Multicast Support For MPLS VPNsVũ Hải QuânОценок пока нет
- Multicast in Mpls Environment: P.F.I.E.VДокумент13 страницMulticast in Mpls Environment: P.F.I.E.Vhem777Оценок пока нет
- Cisco - IP Multicast CourseДокумент1 065 страницCisco - IP Multicast Coursepininaes2Оценок пока нет
- A_New_Approach_in_Radio_and_Television_BДокумент19 страницA_New_Approach_in_Radio_and_Television_BOtun OlusholaОценок пока нет
- Difference Between Unicast, Broadcast and MulticastДокумент4 страницыDifference Between Unicast, Broadcast and Multicastme1111Оценок пока нет
- Multicast Traffic Aggregation in BGP MPLS Based VPNДокумент9 страницMulticast Traffic Aggregation in BGP MPLS Based VPNnguyentienduy1512Оценок пока нет
- Multicast in WirelessДокумент88 страницMulticast in WirelessAbhishek PuranamОценок пока нет
- Ars-Msr 1 Mcast 2014Документ44 страницыArs-Msr 1 Mcast 2014Sorina ElenaОценок пока нет
- Reliable Multicast Protocols and Applications CiscoДокумент18 страницReliable Multicast Protocols and Applications CiscoVijay UkaniОценок пока нет
- Ip Multicast Bes Practices For Enterprise Coustomers - c11-474791Документ15 страницIp Multicast Bes Practices For Enterprise Coustomers - c11-474791krana26Оценок пока нет
- Ipx (Ip Exchange) Is AДокумент4 страницыIpx (Ip Exchange) Is AelmagnouОценок пока нет
- MPLS Virtual Private Networks: About This DocumentДокумент50 страницMPLS Virtual Private Networks: About This DocumentzenruzzОценок пока нет
- Triple Play Multicast: in This ChapterДокумент70 страницTriple Play Multicast: in This ChaptermuthulakshmiОценок пока нет
- Unit 4 Multicast and Multicast RoutingДокумент20 страницUnit 4 Multicast and Multicast RoutingDudzayi KasiyoОценок пока нет
- Arcticle Iptv PDFДокумент14 страницArcticle Iptv PDFfapewo4007Оценок пока нет
- A 9 2633 FFF PDFДокумент14 страницA 9 2633 FFF PDFfapewo4007Оценок пока нет
- IP Multicasting Simulation Technology Based On eNSPДокумент5 страницIP Multicasting Simulation Technology Based On eNSPAnthony IpanaquéОценок пока нет
- IP Multicast Tutorial PDFДокумент175 страницIP Multicast Tutorial PDFmcclaink06100% (1)
- Triple Play Multicast GuideДокумент64 страницыTriple Play Multicast GuideSidney Lopes CoutoОценок пока нет
- A Framework of Multicast Transmission On MPLS Network Using PIM-SMДокумент6 страницA Framework of Multicast Transmission On MPLS Network Using PIM-SMjackson8002Оценок пока нет
- Metro Ethernet MulticastДокумент18 страницMetro Ethernet MulticastĐỗ TháiОценок пока нет
- Product Data Sheet0900aecd80582067Документ8 страницProduct Data Sheet0900aecd80582067Rafael FerreiraОценок пока нет
- Converged IP MPLS Backbone NetworkДокумент10 страницConverged IP MPLS Backbone Networkmark_siotingОценок пока нет
- A Service-Centric Multicast Architecture and Routing ProtocolДокумент17 страницA Service-Centric Multicast Architecture and Routing Protocolإمحمد السنوسي القزيريОценок пока нет
- Location Based Internet - Broadcasting (Phase-I)Документ12 страницLocation Based Internet - Broadcasting (Phase-I)watshakerОценок пока нет
- McBride Iptv N44 PDFДокумент117 страницMcBride Iptv N44 PDFimamrockОценок пока нет
- Internet and Intranet Past Questions SolutionДокумент110 страницInternet and Intranet Past Questions SolutionAngel DahalОценок пока нет
- Assignment CCNP1Документ9 страницAssignment CCNP1Zulhilmi RosliОценок пока нет
- Using Ip Multicast With Vmware® Esx 3.5: Technical NoteДокумент9 страницUsing Ip Multicast With Vmware® Esx 3.5: Technical Notemmonce8916Оценок пока нет
- Trev 312-Kernen QoEДокумент11 страницTrev 312-Kernen QoEStarLink1Оценок пока нет
- DLRP Dynamic Layered Routing Protocol For IP MulticastДокумент6 страницDLRP Dynamic Layered Routing Protocol For IP MulticastHarikrishnan ShunmugamОценок пока нет
- WorksДокумент562 страницыWorkslavidolacoОценок пока нет
- Next Generation Networks: Expectations and Goals: Compiled and Presented by - Aditya Mathur A1607110024Документ18 страницNext Generation Networks: Expectations and Goals: Compiled and Presented by - Aditya Mathur A1607110024Aditya MathurОценок пока нет
- An Ipv4-Ipv6 Translation Mechanism For Sip Overlay Network in Umts All-Ip EnvironmentДокумент10 страницAn Ipv4-Ipv6 Translation Mechanism For Sip Overlay Network in Umts All-Ip Environmentfelipitosorio89Оценок пока нет
- Wireless and Mobile ComputingДокумент6 страницWireless and Mobile ComputingIJRASETPublicationsОценок пока нет
- BICC Vs SIPДокумент8 страницBICC Vs SIPXuân Toàn100% (1)
- Effective Transmission of Data Through RBPH For Group Communication (Synopsis)Документ7 страницEffective Transmission of Data Through RBPH For Group Communication (Synopsis)sanjaykumarguptaa100% (1)
- Wired and Wireless IPTV Access Networks: A Comparison Study: October 2012Документ10 страницWired and Wireless IPTV Access Networks: A Comparison Study: October 2012juninho.sasigОценок пока нет
- Ims ArchitectureДокумент12 страницIms ArchitectureHemanth KattojuОценок пока нет
- Cisco - IP Multicast Course PDFДокумент1 065 страницCisco - IP Multicast Course PDFSedjali Ali-MustaphaОценок пока нет
- Cisco IP Over DWDM Solution For IP NGN: White PaperДокумент12 страницCisco IP Over DWDM Solution For IP NGN: White PaperkamrankhanОценок пока нет
- Sis Netinsight Digital TV Network Construction Nimbra PlatformДокумент8 страницSis Netinsight Digital TV Network Construction Nimbra PlatformchuckyhappyОценок пока нет
- Ip Multicast OverviewДокумент6 страницIp Multicast OverviewwoodksdОценок пока нет
- Island Multicast: Combining IP Multicast With Overlay Data DistributionДокумент13 страницIsland Multicast: Combining IP Multicast With Overlay Data DistributionskirubameОценок пока нет
- 03-Design of Traffic Engineered MPLS VPN For Protected Traffic Using GNS SimulatorДокумент5 страниц03-Design of Traffic Engineered MPLS VPN For Protected Traffic Using GNS SimulatorHerschel PomaliaОценок пока нет
- Multimedia Multicast on the InternetОт EverandMultimedia Multicast on the InternetAbderrahim BenslimaneОценок пока нет
- Deploying Next Generation Multicast-enabled Applications: Label Switched Multicast for MPLS VPNs, VPLS, and Wholesale EthernetОт EverandDeploying Next Generation Multicast-enabled Applications: Label Switched Multicast for MPLS VPNs, VPLS, and Wholesale EthernetОценок пока нет
- Chapter 26 Chemical Analysis Moisture Measurement 2010 Instrumentation Reference Book Fourth EditionДокумент8 страницChapter 26 Chemical Analysis Moisture Measurement 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Chapter 34 Advanced Control For The Plant Floor 2010 Instrumentation Reference Book Fourth EditionДокумент10 страницChapter 34 Advanced Control For The Plant Floor 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Chapter 35 Batch Process Control 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыChapter 35 Batch Process Control 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Prepare For IELTSДокумент169 страницPrepare For IELTSapi-3818413100% (2)
- Avatar Upgrade Program PDFДокумент33 страницыAvatar Upgrade Program PDFMotasim_mОценок пока нет
- Chapter 38 Instrument Installation and Commissioning 2010 Instrumentation Reference Book Fourth EditionДокумент6 страницChapter 38 Instrument Installation and Commissioning 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Introduction 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыIntroduction 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Programming With MatLabДокумент23 страницыProgramming With MatLabZia SilverОценок пока нет
- Copyright 2010 Instrumentation Reference Book Fourth EditionДокумент1 страницаCopyright 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Contributors 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыContributors 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Switches ExplainedДокумент3 страницыSwitches ExplainedMotasim_mОценок пока нет
- 1001 Vocabulary and Spelling QuestionsДокумент160 страниц1001 Vocabulary and Spelling Questionssashi01092% (12)
- Appendix 4 Solutions To Self Test Questions 2001 Measurement and Instrumentation Principles Third EditionДокумент4 страницыAppendix 4 Solutions To Self Test Questions 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- ISO 9000 Quality Assurance AcknowledgementsДокумент1 страницаISO 9000 Quality Assurance AcknowledgementsMotasim_mОценок пока нет
- Simulation, Modeling, and Performance Analysis of IEEE 802.16e OFDMA Systems For Urban and Rural EnvironmentsДокумент4 страницыSimulation, Modeling, and Performance Analysis of IEEE 802.16e OFDMA Systems For Urban and Rural EnvironmentsMotasim_mОценок пока нет
- Chapter 5 Security For Industrial Automation1 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыChapter 5 Security For Industrial Automation1 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- 90 Days of ActionДокумент92 страницы90 Days of ActionPaula StanwyckОценок пока нет
- Appendix 1 Imperial Metric SI Conversion Tables 2001 Measurement and Instrumentation Principles Third EditionДокумент7 страницAppendix 1 Imperial Metric SI Conversion Tables 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- Hsu 4 Information and Control Systems AbДокумент43 страницыHsu 4 Information and Control Systems AbMotasim_mОценок пока нет
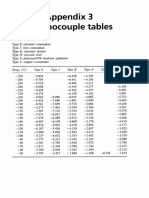
- Appendix 3 Thermocouple Tables 2001 Measurement and Instrumentation Principles Third EditionДокумент6 страницAppendix 3 Thermocouple Tables 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- Appendix 3 Thermocouple Tables 2001 Measurement and Instrumentation Principles Third EditionДокумент6 страницAppendix 3 Thermocouple Tables 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- Appendix 2 TH Venin S Theorem 2001 Measurement and Instrumentation Principles Third EditionДокумент6 страницAppendix 2 TH Venin S Theorem 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- Appendix 4 Solutions To Self Test Questions 2001 Measurement and Instrumentation Principles Third EditionДокумент4 страницыAppendix 4 Solutions To Self Test Questions 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- 1081app A 1 PDFДокумент11 страниц1081app A 1 PDFMotasim_mОценок пока нет
- Index 2001 Measurement and Instrumentation Principles Third EditionДокумент7 страницIndex 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- Chapter 3 Measurement Methods and Control Strategies 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыChapter 3 Measurement Methods and Control Strategies 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Preface 2001 Measurement and Instrumentation Principles Third EditionДокумент3 страницыPreface 2001 Measurement and Instrumentation Principles Third EditionMotasim_mОценок пока нет
- Appendix D International Society of Automation Formerly Instrument Society of America 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыAppendix D International Society of Automation Formerly Instrument Society of America 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Chapter 4 Simulation and Design Software1 2010 Instrumentation Reference Book Fourth EditionДокумент2 страницыChapter 4 Simulation and Design Software1 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- Appendix C The Institute of Measurement and Control 2010 Instrumentation Reference Book Fourth EditionДокумент4 страницыAppendix C The Institute of Measurement and Control 2010 Instrumentation Reference Book Fourth EditionMotasim_mОценок пока нет
- College Wise Form Fillup Approved Status 2019Документ4 страницыCollege Wise Form Fillup Approved Status 2019Dinesh PradhanОценок пока нет
- HERBAL SHAMPOO PPT by SAILI RAJPUTДокумент24 страницыHERBAL SHAMPOO PPT by SAILI RAJPUTSaili Rajput100% (1)
- PIA Project Final PDFДокумент45 страницPIA Project Final PDFFahim UddinОценок пока нет
- The Effects of Cabergoline Compared To Dienogest in Women With Symptomatic EndometriomaДокумент6 страницThe Effects of Cabergoline Compared To Dienogest in Women With Symptomatic EndometriomaAnna ReznorОценок пока нет
- Ellen Gonzalvo - COMMENTS ON REVISIONДокумент3 страницыEllen Gonzalvo - COMMENTS ON REVISIONJhing GonzalvoОценок пока нет
- Unit I. Phraseology As A Science 1. Main Terms of Phraseology 1. Study The Information About The Main Terms of PhraseologyДокумент8 страницUnit I. Phraseology As A Science 1. Main Terms of Phraseology 1. Study The Information About The Main Terms of PhraseologyIuliana IgnatОценок пока нет
- 5 6107116501871886934Документ38 страниц5 6107116501871886934Harsha VardhanОценок пока нет
- IB Theatre: The Ilussion of InclusionДокумент15 страницIB Theatre: The Ilussion of InclusionLazar LukacОценок пока нет
- Addendum Dokpil Patimban 2Документ19 страницAddendum Dokpil Patimban 2HeriYantoОценок пока нет
- Irony in Language and ThoughtДокумент2 страницыIrony in Language and Thoughtsilviapoli2Оценок пока нет
- MiQ Programmatic Media Intern RoleДокумент4 страницыMiQ Programmatic Media Intern Role124 SHAIL SINGHОценок пока нет
- Note-Taking StrategiesДокумент16 страницNote-Taking Strategiesapi-548854218Оценок пока нет
- Canine Guided Occlusion and Group FuntionДокумент1 страницаCanine Guided Occlusion and Group Funtionlittlestar35100% (3)
- HRM in A Dynamic Environment: Decenzo and Robbins HRM 7Th Edition 1Документ33 страницыHRM in A Dynamic Environment: Decenzo and Robbins HRM 7Th Edition 1Amira HosnyОценок пока нет
- Labov-DIFUSÃO - Resolving The Neogrammarian ControversyДокумент43 страницыLabov-DIFUSÃO - Resolving The Neogrammarian ControversyGermana RodriguesОценок пока нет
- Jesus' Death on the Cross Explored Through Theological ModelsДокумент13 страницJesus' Death on the Cross Explored Through Theological ModelsKhristian Joshua G. JuradoОценок пока нет
- Transformation of Chinese ArchaeologyДокумент36 страницTransformation of Chinese ArchaeologyGilbert QuОценок пока нет
- Business Law Module No. 2Документ10 страницBusiness Law Module No. 2Yolly DiazОценок пока нет
- Organisation Study of KAMCOДокумент62 страницыOrganisation Study of KAMCORobin Thomas100% (11)
- Kedudukan Dan Fungsi Pembukaan Undang-Undang Dasar 1945: Pembelajaran Dari Tren GlobalДокумент20 страницKedudukan Dan Fungsi Pembukaan Undang-Undang Dasar 1945: Pembelajaran Dari Tren GlobalRaissa OwenaОценок пока нет
- Tax Invoice/Bill of Supply/Cash Memo: (Original For Recipient)Документ1 страницаTax Invoice/Bill of Supply/Cash Memo: (Original For Recipient)Pravin AwalkondeОценок пока нет
- Jaap Rousseau: Master ExtraodinaireДокумент4 страницыJaap Rousseau: Master ExtraodinaireKeithBeavonОценок пока нет
- Architectural PlateДокумент3 страницыArchitectural PlateRiza CorpuzОценок пока нет
- Product Packaging, Labelling and Shipping Plans: What's NextДокумент17 страницProduct Packaging, Labelling and Shipping Plans: What's NextShameer ShahОценок пока нет
- Housekeeping NC II ModuleДокумент77 страницHousekeeping NC II ModuleJoanne TolopiaОценок пока нет
- Megha Rakheja Project ReportДокумент40 страницMegha Rakheja Project ReportMehak SharmaОценок пока нет
- Excel Keyboard Shortcuts MasterclassДокумент18 страницExcel Keyboard Shortcuts MasterclassluinksОценок пока нет
- Brain Chip ReportДокумент30 страницBrain Chip Reportsrikanthkalemla100% (3)
- Italy VISA Annex 9 Application Form Gennaio 2016 FinaleДокумент11 страницItaly VISA Annex 9 Application Form Gennaio 2016 Finalesumit.raj.iiit5613Оценок пока нет
- The Insanity DefenseДокумент3 страницыThe Insanity DefenseDr. Celeste Fabrie100% (2)