Академический Документы
Профессиональный Документы
Культура Документы
Eauction Report
Загружено:
Maneesh BradiyilОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Eauction Report
Загружено:
Maneesh BradiyilАвторское право:
Доступные форматы
ONLINE AUCTION 084991223
INTRODUCTION
we are developing a software for online-Auction .online-Auction is known by
several names, including electronic reverse bid Auctions, reverse auctions or
simply e-Auctions. Online auction is a group which is based for auction. If you
want to something sell by auction then you post that on website. It just a selling of
products. This project user can do a bid on particular Products. The main objective
of the e-Auction process must be to obtain best value and the highest price. It
cannot be possible to achieve best value outcomes whilst the focus remains on
price. There are two categories of persons one is customers and second one is
vendor. Vendor can sell his products on this website and customer will purchase it.
Product will be given to those customer who put a high bid price on product to
purchase. One user can do a more than one bid on products. There are two
categories of persons one is customers and second one is vendor. Both have their
own registration form .There is a common login page for vendors and for users but
when both login in, it would be easily find out that ether it is a vendor or a user
because of their registration details because their registration forms are different.
There are two home page i.e. one page behave different if vendor login then show
the vendors menu or if customer will login then customer menu will
show.Coustomers should have an appropriate knowledge of the e- Auction subject
1
ONLINE AUCTION 084991223
its market, its market price.. In this website anyone wants to sell products will have
to register first then a unique id is given to the registered users. After registered
user have to give details of their products like (price of product ,at what price
he/she wants to start the bid, image of the product) if he/she wants to sell his/her
product .
Product will be given to that customer who put a high bid price on product to
purchase. One user can do a more than one bid on products. After completion of
bidding process all the bids are check and the product will give to that customer for
purchase who has a high bid price. The bidding exercise will have a specified
opening and closing time. The E-Auction will close when no new bids are received
and the closing time has expired. If however, a new (lower) bid is received just
before the Scheduled closing time, the allocated bidding time will be extended.
User can also give their feedbacks about on this project. There would be Three
type of feedback which user can give they would be negative, positive. And
average experience of this project.
If user have problem related and wanted to know that what is e-auction they can
chat with the experts through live chat.
ONLINE AUCTION 084991223
Online Auction is loaded with features and functionality that allows you to create
an auction that is powerful and useful for buyers and sellers.
1. User (customer, vendor)
In our project there are two types of users one is customer who wants to buy
products by auctions and another is vendor who wants to sell his products.
At the time of registration user can select that he want to be a vendor, customer or
both. If he select vendor he can login with his vendor id and password vendor can
add his product details, edit existing product detail and he can delete product also.
But he cant participate on auctions to bid on a product.
If he registers as a customer then he will login with his customer id and password
he can choose any product which is available for auction from the menus then he
can bid on that product. But he cant set any product for auction to sell.
If he selects both at the time of registration he can buy and sell products he can
perform all the functions of customer and vendor.
2. Auction management
In auction management module there are many sub modules
ONLINE AUCTION 084991223
For vendor
Add a product
Edit product information
And delete existing product.
When a user clicks on ADD A PRODUCT dropdown will open in which user
enters details about their products like (price of product, at what price he/she wants
to start the bid, image of the product).Help is also available for users how to add a
product for auction.
Edit product info:
If user enter wrong information about product and he/she want to edit the info then
user will click on EDIT PRODUCT INFORMATION another dropdown will open
and user will edit full details of the product.
For customer
If a user login as a customer then he/she can bid on any product which is available
for auction on the website. On his main page he has a menu from which he can
choose the product for bidding. There is a categories menu from which he can
select a product by their types like he want to bid on a car he will choose
automobiles from the menu then he select car then all the list of cars will display
on the page. He can select car on which he want to participate on auction. After
4
ONLINE AUCTION 084991223
adding his first bid on that item his name will appear on the bidder list of that item.
After his first bid he will continue receive auction updates of that product. On his
page. He can also quit his participation for that product any time. If he quit his
name will remove from the bidder list and and the updates will also stops.
3. Auction closing
At the end of auction date of the product if he puts the highest price for that
product at the end of auction he got a mail that he won the auction and he can
purchase that product.
Payment gateway
Mode of payment is done by credit card of debit card if a customer puts highest bid
at the end of auction time then he can buy the product, to buy the product he has
two options he can buy from the credit card or debit card. He has to enter his
details then the product then the product is delivers to his home.
OBJECTIVE OF THE PROJECT
The main objective of this project is as follows
1. This portal gives selling/purchasing of product online.
5
ONLINE AUCTION 084991223
2. Any user have both type i.e. vendor and customer. If he/she sells the product
then he/she is vendor and if he/she purchases the product then he/she is the
customer.
3. This website has bid history.
4. The user can see the bid history.
In this, there is a feedback from. If the user wants to give some feedback, he/she
fill this form.
ONLINE AUCTION 084991223
TOOLS , PLATFORM , HARDWARE AND SOFTWARE
REQUIREMENTS SPECIFICATION
HARDWARE REQUIREMENTS
CORE 2 DUO PROCESSOR (3.0GHZ)
1 GB RAM
320 GB HDD
LCD MONITOR
PRINTER
SOFTWARE REQUIREMENTS
OPERATING SYSTEM WINDOWS 7
DATABASE SQL SERVER 2008
FRONT END - C # AND .NET FRAMEWORK
TOOL VISUAL STUDIO 2010
ONLINE AUCTION 084991223
SYSTEM ANALYSIS
System Analysis by definition is a process of systematic investigation for the
purpose of gathering data, interpreting the facts, diagnosing the problem and using
this information to either build a completely new system or to recommend the
improvements to the existing system.
A satisfactory system analysis involves the process of examining a business
situation with the intent of improving it through better methods and procedures. In
its core sense, the analysis phase defines the requirements of the system and the
problems which user is trying to solve irrespective of how the requirements would
be accomplished
There are 2 methods to perform System Requirement Analysis:
(i)
Structured Analysis
Structured Analysis is an analysis method that provides a basis for developing a
model of software to be developed. The objective of structured analysis is to
identify the customer requirements and establish a basis to create a software
model
ONLINE AUCTION 084991223
.
The components of a Structured Analysis are
Data Dictionary
Entity Relationship Diagram
Data Flow Diagram
Process Specification
Control Specification
ONLINE AUCTION 084991223
(ii)
Object Oriented Analysis
It refers to a detailed study of the various objects involved in a system and the
relationship of these objects with each other. While performing an object oriented
analysis, the focus of the system analyst is on the availability of the objects that are
relevant to software development.
10
ONLINE AUCTION 084991223
Identification of Need
In current competitive scenario every business establishment needs
quality
processes to increase their efficiency as well as improve their productivity. It is of
vital importance that manual, time consuming & monotonous operations be
automated so as to streamline the working of an organization. In the current
business environment, there were lot of person who are searching for jobs. But
the main thing is the proper match for a job opportunity. So the main objective of
this project is to provide right type of job to right person. Since, the existing
system (manual work) takes more time and manpower for processing. Our
system will deal with all the aspects of jobsites starting from jobseeker
registration, providing him right type of jobs. Employer will send its requirement
and consultant search proper match for the job as per the employer requirement
and inform both the jobseeker and employer. So the main objective is to provide
right job to right person.
Preliminary Investigation
11
ONLINE AUCTION 084991223
The basic purpose behind Preliminary Investigation is to first clarify, understand
and evaluate the Project Request.
Preliminary Investigation basically refers to the collection of information that
guides the management of an organization to evaluate the merits and demerits of
the project request and make an informed judgment about the feasibility of the
proposed system. This sort of investigation provides us with a through picture of
the kind of software and hardware requirements which are most feasible for the
system, plus the environment in which the entire project has to be installed and
made operational.
1) Reviewing the Documents provided by the Organization
They were quite effective in guiding us towards visualizing the
features that were needed to be put together in the system and the
required output which had to be generated once the system became
functional.
These specifications provided to us by the organization showed how the new
system should look like; it helped us in understanding the basic structure of the
application which we were supposed to develop.
2) On site Observation:
12
ONLINE AUCTION 084991223
Another technique utilized by us to gain information about the project was to
visit the client site where the system had to be installed. Here a detailed system
study was carried out, checking the existing system to replicate it with our
system. We also observed the activities of the system directly. During the on-site
observation, we saw the office environment, work load of the system and users,
method of work, and the facilities provided by the organization. This information
helped us to understand how the system should operate. But after interviewing
the persons, who is affected by the system, we got more details that further
explain the project and shown whether assistance is merited economically,
operationally and technically.
3)
Conducting Interviews:
This method of investigation conducted by us involved questioning
the concerned personnel to get the users (client) view about the
system and the features they desired it to have. Some of the Questions
put forward by our team were:
a) The amount of data needed to be stored.
b) The number of customers using the system and number of
which the application needed to be installed.
c) The issue of our application with existing system was widely
discussed.
13
ONLINE AUCTION 084991223
d) The level of access given to the customer would depend on his
department.
14
ONLINE AUCTION 084991223
FEASIBILITY STUDY
Feasibility study is the process of determination of whether or not a project is
worth doing. Feasibility studies are undertaken within tight time constraints and
normally culminate in a written and oral feasibility report. The contents and
recommendations of this feasibility study helped us as a sound basis for deciding
how to precede the project. It helped in taking decisions such as which software to
use, hardware combinations, etc.
The following is the process diagram for feasibility analysis. In the diagram, the
feasibility analysis starts with the user set of requirements. With this, the existing
system is also observed. The next step is to check for the deficiencies in the
existing system. By evaluating the above points a fresh idea is conceived to define
and quantify the required goals. The user consent is very important for the new
plan. Along with, for implementing the new system, the ability of the organization
is also checked. Besides that, a set of alternatives and their feasibility is also
considered in case of any failure in the proposed system. Thus, feasibility study is
an important part in software development.
15
ONLINE AUCTION 084991223
WORKING CURRENT SYSTEM
USERS CONSESUS
DEFICIENCES IN
CURRENT SYSTEM
USER
STATED
REQUIREMENTS
ANALYZE TO FIND
DEFICIENCES
DEFINE AND
QUANTIFY GOALS
REVISION BASED ON FEASIBILITY
CONSTRAINTS ON RESOURCES
EVALUATE
FEASIBILITY OF
ALTERNATES
PROPOSED FEASIBILITY
ALTERNATIVES
FIND BROAD
ALTERNATIVE
SOLUTION
ALTERNATIVES
(PROCESS DIAGRAM FOR FEASIBILITY ANALYSIS)
In the SDLC (Systems Development Life Cycle) of our project we maintained a
number of feasibility checkpoints between the two phases of the SDLC.
These checkpoints indicate that the management decision to be made after a
phase is complete.
The feasibility checkpoints in our project were as follows:
(i)
Survey phase checkpoint
(ii)
Study phase checkpoint
16
ONLINE AUCTION 084991223
(iii)
Selection phase checkpoint
(iv)
Acquisition phase checkpoint
(v)
Design phase checkpoint
We conducted three tests for Project feasibility namely, Technical,
Economical, and Operational feasibilities
Technical Feasibility
Technical feasibility determines whether the work for the project can be done with
the existing equipment, software technology and available personnel. Technical
feasibility is concerned with specifying equipment and software that will satisfy
the user requirement.
This project is feasible on technical remarks also, as the proposed system is more
beneficiary in terms of having a sound proof system with new technical
components installed on the system. The proposed system can run on any
machines supporting Windows and Internet services and works on the best
software and hardware that had been used while designing the system so it would
be feasible in all technical terms of feasibility.
Technical Feasibility addresses three major issues:
(a) Is the proposed Technology or Solution Practical?
17
ONLINE AUCTION 084991223
The technologies used are matured enough so that they can be applied to our
problems. The practicality of the solution we have developed is proved with the
use of the technologies we have chosen. The technologies
such as ASP, IIS,
VBscript and the compatible H/Ws are so familiar with the todays knowledge
based industry that anyone can easily be compatible to the proposed
environment.
(b)Do we currently posses the necessary technology?
We first make sure that whether the required technologies are available to us or
nor. If they are available then we must ask if we have the capacity. For instance,
Will our current Printer be able to handle the new reports and forms required
of a new system?
(c) Do we possess the necessary Technical Expertise and is the schedule
reasonable?
This consideration of technical feasibility is often forgotten during feasibility
analysis. We may have the technology, but that doesnt mean we have the skills
required to properly apply that technology.
As far as our project is concerned we have the necessary expertise so that the
proposed solution can be made feasible.
Some projects are initiated with specific deadlines. In our case first we have
given three months time but due to some problems regarding time and the
constraints of expertise it has been extended to six months. Now there are some
18
ONLINE AUCTION 084991223
organizational constraints that have not yet given us the opportunity to install
the system.
Economical Feasibility
Economical feasibility determines whether there are sufficient benefits in sufficient
benefits in creating to make the cost acceptable, or is the cost of the system too
high. As this signifies cost-benefit analysis and savings. On the behalf of the costbenefit analysis, the proposed system is feasible and is economical regarding its
pre-assumed cost for making a system.
Economical feasibility has great importance as it can outweigh other feasibilities
because costs affect organization decisions. The concept of Economic Feasibility
deals with the fact that a system that can be developed and will be used on
installation must be profitable for the Organization. The cost to conduct a full
system investigation, the cost of hardware and software, the benefits in the form of
reduced expenditure are all discussed during the economic feasibility.
During the economical feasibility test we maintained the balance between the
Operational and Economical feasibilities, as the two were the conflicting. For
example the solution that provides the best operational impact for the end-users
may also be the most expensive and, therefore, the least economically feasible.
19
ONLINE AUCTION 084991223
We classified the costs of ONLINE AUCTION according to the phase in which
they occur. As we know that the system development costs are usually one-time
costs that will not recur after the project has been completed. For calculating the
Development costs we evaluated certain cost categories viz.
(i)
Personnel costs
(ii)
Computer usage
(iii)
Training
(iv)
Supply and equipments costs
(v)
Cost of any new computer equipments and software.
In order to test whether the Proposed System is cost-effective
or not we evaluated it through three techniques viz.
Payback analysis
Return on Investment:
Net Present value
Operational Feasibility
Operation feasibility is a measure of how people feel about the system. Operational
Feasibility criteria measure the urgency of the problem or the acceptability of a
20
ONLINE AUCTION 084991223
solution. Operational Feasibility is dependent upon determining human resources
for the project. It refers to projecting whether the system will operate and be used
once it is installed.
1. If the ultimate users are comfortable with the present system and they see no
problem with its continuance, then resistance to its operation will be zero.
Behaviorally also the proposed system is feasible. A particular application may be
technically and but may fail to produce the forecasted benefits, because the
company is not able to get it to work. For the system, it is not necessary that the
user must be a computer expert, but any computer operator given a little bit of
knowledge and training can easily operate.
Our Project is operationally feasible since there is no need for special training of
staff member and whatever little instructing on this system is required can be done
so quite easily and quickly as it is essentially This project is being developed
keeping in mind the general people who one have very little knowledge of
computer operation, but can easily access their required database and other
related information. The redundancies can be decreased to a large extent as the
system will be fully automated.
Project planning
A software project development is a highly labour-intensive activity. Large
software may involve hundreds of people and span of time. A project in it is
dimension can easily turn into chaos if proper management is not done. Proper
21
ONLINE AUCTION 084991223
management controls and checkpoints are required for effective project
monitoring. Controlling the development, ensuring quality, satisfying the
constraints of the selective process model are require careful management of the
project.
The major issue the project plan addresses are:
Cost estimation
Schedule and milestone
Personal plan
Software quality assurance
Configuration management plan
Project monitoring plans
Risk management
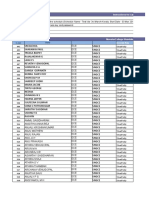
COST ESTIMATION
22
ONLINE AUCTION 084991223
Development costs
Personnel cost:
1
System analysts (80 hrs) Rs. 35.00/hr
Rs. 3000
Programmer (130 hrs) Rs. 100.00/hr
Rs. 12000
Data base specialist (20 hrs) Rs.
Rs. 2000
40.00/hr
New hardware and software:
4
Development S/W (Visual Studio.Net)
Rs. 1300
Operating system windows 7
Rs. 2000
Training staff (10 classes) Rs.150/class
Rs. 1500
Training
6
Planning Tools
23
ONLINE AUCTION 084991223
Without planning it is difficult to measure progress. As phases are crystallized,
crises should begin to disappear. A project manager must plan the life cycle to the
project and delegate authority for its implementation.
Project planning involves plotting project activities against a time frame. One of
the first steps in planning is developing a road map structure or a network based on
analysis of the tasks that must be performed to complete the project. In the early
1900s, formal planning used a Gantt chart or a milestone chart. By plotting
activities on the Y-axis and time on the X-axis, the analyst laid out on overall
network specifying interrelationships among actions. Later on, formal planning
techniques such as the program evaluation and review technique (PERT) was
introduces. Other operations research techniques such as linear programming and
queuing theory have also been introduced in allocating resources. In the early
1980s software packages became available for project planning.
Gantt chart:
Basic planning uses bar charts that show project activities and the amount of time
they will take. This activity scheduling method was first introduced in 1914 by
Henry L. Gantt as a rudimentary aid to plot individual tasks against time. The
Gantt chart uses horizontal bars to show the durations of actions or tasks. The left
end marks the beginning of the tasks; the right end its finish. Earlier tasks appear
in the upper left and later ones in the lower right.
In planning this project, several steps are undertaken:
1.
Identify the activities and tasks in the stage. Each
activity must be identified to plan the completion date and allocate
24
ONLINE AUCTION 084991223
responsibilities among members of the project team. In our project, there are
seven activities :
i.
Understanding Project Requirement
ii.
Designing Tables
iii.
Designing Forms
iv.
Coding
v.
Report Designing
vi.
Testing
vii.
Implementation
2.
Determine the tasks for each activity and the
estimated completion times. Each activity is broken down into several tasks.
3.
Determine the total estimated time for each activity
and obtain an agreement to proceed.
4.
Plot activities on a Gantt chart. All activities, tasks,
and milestones are drawn on the Gantt chart, with emphasis on simplicity and
accuracy.
5.
Review and record progress periodically. The actual
amount of time spent on each activity is recorded and compared with the
budgeted times
25
ONLINE AUCTION 084991223
26
ONLINE AUCTION 084991223
Program Evaluation and Review Technique (PERT)
Like the Gantt chart, PERT makes use of tasks. Like milestone charts, it shows
achievements. These achievements however are not task achievements. They are
terminal achievement, called events. Arrows are used to represent tasks and circles
represent the beginning or completion of a task. The PERT chart uses these paths
and events to show the interrelationships of project activities.
The events in my project can be categorised as:
1. Meeting to the Employees of company to understand the project.
2. Table Designing
3. Form Designing
4. Writing Codes
5. Designing Reports
6. Testing the project
7. Implementation of project
Each task is limited by an identifiable event. An event has no duration; it simply
tells you that the activity has ended or begun. Each task must have a beginning and
an ending event. A task can start only after the tasks depends on have been
completed. PERT does not allow looping back because a routing that goes back
to a task does not end.
A PERT chart is valuable when a project is being planned. When the network is
finished, the next step is to determine the critical path. It is the longest path
through the network. No task on the critical path can be held up without delaying
the start of the next tasks and, ultimately, the completion of the project. So the
critical path determines the project completion date.
27
ONLINE AUCTION 084991223
A = Order Computing Platform
B = Prepare Site
C = Review Specification
D = Install Equipment
E = Test Hardware
F = Training
28
ONLINE AUCTION 084991223
G = Write Programs
H = Test Programs
I = Test Software
J = Convert System
K = Implementation Follow-up
L=Accept
In addition to showing the interrelationships among project activities, PERT
chart shows the following:
1. The activities that must be completed before initiating a specific activity.
2. Interdependencies of the tasks.
3. Other activities that can be completed while a given activity is in progress.
4. The activities that cannot be initiated until after other specific activities are
completed. This is called a precedence relationship.
Quality Assurance Plan:
To ensure that the final product is of high quality, some quality control activities
must be performed throughout the development. As we saw earlier, if this is not
done, correcting errors in the final stages can be vary expansive, especially if they
originated in the early phases. The purpose of the software quality assurance plans
29
ONLINE AUCTION 084991223
(SQAP) is to specify all the work products that need to be produced during the
project, activities that need to be methods that may be used for the SQA activities.
Note that SQAP takes a board view quality. It is interested in the quality of not
only the final product, but also of the intermediate products, even through in a
project we are ultimately interested in the quality of the delivered product. This is
due to the fact that in a project it is very unlikely that the intermediate work
products are of poor quality, but the final product is of high quality. So, to ensure
that the delivered software is of good quality it is essential to make sure that the
requirements and design are also of good quality.
Project Scheduling
It is important, right at the start of the design process, for the designer or design
team, to set clear objective. The primary objectives will always be to design a
system that delivers the functions required by the client to support the business
objective of their organization. For example the system may be required to speed
up the production of accurate invoices, or to provide up to date, detailed
management information to improve the managing directors control over the
business; or to help senior managers to make strategic decisions. In the other
words, to be a quality product the system must conform to the customers
requirements and be delivered in a way, which meets their expectations in terms of
service. There are many ways in which these requirements might be mat by a
30
ONLINE AUCTION 084991223
physical design solution, but there are a number of other objectives that must be
considered if a god design is to be produced. The design objective is:
Flexible:
The design should enable future requirements of the business to be incorporated
with out too much difficulty. Often during the analysis phase, users may not be
clear about exactly what they will require from the new system, for example which
reports will be most useful to them. However during the evaluation period after the
new system becomes operational, the real needs often emerge and flexible design
will be able to accommodate these new requirements .In addition, business change
over time and a good design enable the system to reflect these changes.
Maintainable:
This is closely linked to the previous objective because it is about change. A good
design is easy to maintain ands this reduces the clients maintenance costs, which
usually represent a high proportion of the total lifetime cost of the system.
Portable:
Still on the subject of change, a client who has bought a software system may wish
to change the hardware on which the system runs .A good design is portable-in
31
ONLINE AUCTION 084991223
other words it is capable of being transferred from one machine environment to
another with the minimum amount of effort to convert it.
Easy to use:
With the increasing exposure of people to computer applications in the home as
well as in the office, expectations of computer systems in terms of their ease of use
are also increasing. A good design will result in a system which is user friendly
easy to understand, not difficult to learn how to use and straightforward to operate.
Reliable:
This objective is about designing systems which are secure against human error,
deliberate misuse of machine failure, and in which data will be stored without
corruption. While this is desirable in any computer system, for certain systems in
the areas of defence, process control or banking, it will be a key design objective.
Secure:
Security is nether objective that must be considered by the designer .In order to
protect the confidentiality of the data, particularly if it is commercially sensitive, it
may be important to build in methods to restrict access to authorized users only, for
example by introducing passwords.
32
ONLINE AUCTION 084991223
Programmer-friendly:
While the other objective are mainly about delivering benefits to the client, the
designer must also consider how easy it will be for the programmers to produce the
code from the program specifications. By producing a programmer- friendly
design, both the costs of production and the risk of building in errors are reduced.
Cost-effective:
his includes a number of the other objectives, and is about designing a system that
delivers the required functionally, ease (simplicity) of use, reliability, security, etc.
to the client in the most cost-objective way.
33
ONLINE AUCTION 084991223
SOFTWARE REQUIREMENT ANALYSIS AND
SPECIFICATION
The quality of a software product is only as good as the process that creates it.
Requirements engineering one of the most crucial steps in this creation process.
Without well-written requirements specification, developers do not know what to
build, customers do not know what to expect, and there is no way to validate that
the built system satisfies the requirements. Requirements engineering includes all
activities related to the following:
Identification and documentation of customer and users needs
Creation of a document that describes the external behaviour and the
associated constraints hat will satisfies those needs
Analysis and validation of the requirements documents to ensure
consistency, and feasibility
Evolution of needs
The primary output of requirements engineering is requirements specification. If it
describes both hardware and software, it is a system requirement specification. If it
describes only software, it is a software requirement specification. Requirement
stage end with creating a document called the Software Requirement Specification
(SRS), which contain s a complete description of the external behaviour of the
software system.
34
ONLINE AUCTION 084991223
Nature of the SRS:
The basic issues that SRS writers shall address are the following:
1. Functionality: What the software is supposed to do?
2. External interfaces: How does the software interact with people, the
systems hardware, other hardware, and other software?
3. Performance: What is the speed, availability, response time, recovery time,
etc of various software functions?
4. Attributes: What is the consideration for portability, correctness,
maintainability, security, reliability etc.?
5. Design constraints imposed on an implementation: Are there any
required standards on effect, implementation language, policies for database
integrity etc.?
Since the SRS has specific role to play in the software development process, SRS
writers should be careful not o go beyond the bounds of that role. This means the
SRS
1. Should correctly define all the software requirements. A software
requirement may exit because of the nature or the task to be solved or
because of a special characteristic of the project.
35
ONLINE AUCTION 084991223
2. Should not describe any design or implementation details. These should be
described in the design stage of the project.
3.
Should not impose additional constraints on the software. These are
properly specified in other documents such as a software quality assurance
plan.
Therefore, a properly written SRS limits the range of valid designs, but does not
specify any particular design.
CHARACTERISTICS OF A GOOD SRS:
1. Correct: An SRS is correct if; every requirement stated therein one that the
software shall meet. There is no tool or procedure that assures correctness.
2. Unambiguous: An SRS is unambiguous if, and only if; every requirement
stated therein has only one interpretation
SOFTWARE ENGINEERING PARADIGM APPLIED
The development strategy that encompasses the process, methods, and tools and
the generic phases is called Software Engineering Paradigm. The s/w paradigm for
software is chosen based on the nature of the project and application, the method
and tools to be used, and the controls and deliverables that are required. All
software development can be characterized as a problem-solving loops (fig. 2) in
36
ONLINE AUCTION 084991223
which four distinct stages are encountered: status quo, problem definition,
technical development, and solution integration.
Problem
Solving
Technical
Status
Development
Quo
Solution
Integration
37
ONLINE AUCTION 084991223
Online Auction SRS
Introduction
we are developing a software for online-Auction .online-Auction is known by
several names, including electronic reverse bid Auctions, reverse auctions or
simply e-Auctions. Online auction is a group which is based for auction. If you
want to something sell by auction then you post that on website. It just a selling of
products. This project user can do a bid on particular Products. The main objective
of the e-Auction process must be to obtain best value and the highest price. It
cannot be possible to achieve best value outcomes whilst the focus remains on
price. There are two categoriesof persons one is customers and second one is
vendor. Vendor can sell his products on this website and customerwill purchase
it.Product will be given to those customer who put a high bid price on product to
purchase. One user can do a more than one bid on products.
Information description
There are two categoriesof persons one is customers and second one is vendor.
Both have their own registration form .There is a common login page for vendors
and for users but when both login in, it would be easily find out that ether it is a
vendor or a user because of their registration details because their registration
forms are different. There are two home page i.e. one page behave different if
vendor login then show the vendors menu or if customer will login then customer
menu will show.Coustomers should have an appropriate knowledge of the eAuction subject its market, its market price.. In this website anyone wants to sell
products will have to register first then a unique id is given to the registered users.
After registered user have to give details of their products like (price of product
38
ONLINE AUCTION 084991223
,at what price he/she wants to start the bid, image of the product) if he/she wants
to sell his/her product .
Product will be given to that customer who put a high bid price on product to
purchase. One user can do a more than one bid on products. After completion of
bidding process all the bids are check and the product will give to that customer for
purchase who has a high bid price. The bidding exercise will have a specified
opening and closing time. The E-Auction will close when no new bids are received
and the closing time has expired. If however, a new (lower) bid is received just
before the Scheduled closing time, the allocated bidding time will be extended.
User can also give their feedbacks about on this project. There would be
Three type of feedback which user can give they would be negative, positive. And
average experience of this project.
If user have problem related and wanted to know that what is e-auction they can
chat with the experts through live chat.
Functional description
4. User (customer, vendor)
In our project there are two types of users one is customer who wants to buy
products by auctions and another is vendor who wants to sell his products.
At the time of registration user can select that he want to be a vendor, customer or
both. If he select vendor he can login with his vendor id and password vendor can
add his product details, edit existing product detail and he can delete product also.
But he cant participate on auctions to bid on a product.
39
ONLINE AUCTION 084991223
If he registers as a customer then he will login with his customer id and password
he can choose any product which is available for auction from the menus then he
can bid on that product. But he cant set any product for auction to sell.
If he selects both at the time of registration he can buy and sell products he can
perform all the functions of customer and vendor.
5. Auction management
In auction management module there are many sub modules
For vendor
Add a product
Edit product information
When a user clicks on ADD A PRODUCT dropdown will open in which user
enters details about their products like (price of product, at what price he/she wants
to start the bid, image of the product).Help is also available for users how to add a
product for auction.
Edit product info:
If user enter wrong information about product and he/she want to edit the info then
user will click on EDIT PRODUCT INFORMATION another dropdown will open
and user will edit full details of the product.
40
ONLINE AUCTION 084991223
For customer
If a user login as a customer then he/she can bid on any product which is available
for auction on the website. On his main page he has a menu from which he can
choose the product for bidding. There is a categories menu from which he can
select a product by their types like he want to bid on a car he will choose
automobiles from the menu then he select car then all the list of cars will display
on the page. He can select car on which he want to participate on auction. After
adding his first bid on that item his name will appear on the bidder list of that item.
After his first bid he will continue receive auction updates of that product. On his
page. He can also quit his participation for that product any time. If he quit his
name will remove from the bidder list and and the updates will also stops.
6. Auction closing
At the end of auction date of the product if he puts the highest price for that
product at the end of auction he got a mail that he won the auction and he can
purchase that product.
41
ONLINE AUCTION 084991223
DATA FLOW DIAGRAM
A Data flow diagram (DFD) is used to express system requirements in a
graphical form. It is also known as a bubble chart. A DFD depicts
information flow and transform that are applied as data moves from input.
Use of DFD helps to clarify the system requirements. DFD are drawn
surging analysis and are the starting point for the design phase. A DFD could
be used represent a physical system, at the beginning of analysis, or a logical
system at alter point in the system development life cycle. Being graphical,
it is easy to understand.
A DFD is used to describe what data flows rather how if flows. The concern
is understanding the transforms that are required that are required to convert
the input to output. It is independent of hardware, software, data structure
and file organization.
42
ONLINE AUCTION 084991223
CONTEXT FREE DIAGRAM
Bid Management
User
Online
Auction
Auction Management
43
ONLINE AUCTION 084991223
LEVEL --1 DFD
Vendor
User
Managem
ent
Username master
User details
User
Auction master
Auction master
Auction
Auction Details
Managem
ent
Auction Type
Bid master
Bid Master
Bid
Managem
ent
paymentmaster
payment_details
Payment
gateway
Bid Details
Chat
44Managemen
t
ONLINE AUCTION 084991223
LEVEL --2 DFD
Username master
Accept
Checks
User Details
Checks Access
User
Managemen
t
Check New
User
Existence
Is It Vendor
or Customer
Vendor
User
New User
Sign up
Page
Store
Username Master & User Details
45
Customer
ONLINE AUCTION 084991223
User
Visible
Show
Auction
Auction Master
Access
Interact
Auction Type
Retrieve
Auction
Manageme
nt
Auction
Type
Create
Auction
Save
Auction
Auction Master & Auction Details
46
ONLINE AUCTION 084991223
Bid Master
Customer
VISIBLE
INTERACT
Show Bid
Bid
Managemen
t
Create Bid
Put
Bid Master & Details
47
ONLINE AUCTION 084991223
Payment
Gateway
Check
Validation
Is valid
is not valid
Payment
Is direct
Pay
Registration
is not direact
Party Pay
Thanks
Payment details
48
ONLINE AUCTION 084991223
ENTITY RELATIONSHIP - DIGRAM
An E R diagram is a model that identifies the concept or entities that exist in a
system and the relationships between those entities. An ERD is often used as a way
to visualize a relational database: each entity represents a database table and the
relationship lines represents the key in one table that point to specific records in
related tables.
Advantages of ER diagram
Professional and faster Development.
Productivity Improvement.
Fewer Faults in Development.
Maintenance becomes easy.
auction_catagor
yy
Create date
I_auto id
Interact
49
Auction Type
Interact
I_uid
i_bid
price
C_uid
id
C_pwd
Bid
User
management
management I_net
have
Interact
have
detail
i_uid
i_created by
Auction
Closing
management
History
i_bid id
ONLINE AUCTION 084991223
I_auto
id
Inter
act
1
1
1
D_effect_to
D_create
date
M
d_creat
e date
I_
auto_id
D_effect_fro
m
1
m
1
Have
detai
ls
1
1
i_auto
id
auto_id
I_auctio
n id
Class Digram
50
ONLINE AUCTION 084991223
51
ONLINE AUCTION 084991223
SURVEY OF TECHNOLOGY
ABOUT ACTIVE SERVER PAGE (ASP):
Introduction: Active Server Pages are Microsofts solution to creating dynamic
web pages. An ASP file can contain text, HTML tags and scripts. Scripts in an asp
file are executed on the server
What is ASP?
ASP is a program that runs at server Windows 2000/XP IIS plays the role of server.
IIS comes as a free component with Windows 2000/XP.
An ASP file is just the same as an HTML file; it can contain text, HTML, XML,
and scripts. Scripts in an ASP file are executed on the server and it has an
extension .asp.
In ASP Client-Server Model is implemented. A client computer requests some
needed information from Server computer. The Server returns this information and
the client acts on it. The client is a web browser on internet. With the internet the
server is a particular web server. A server is a computer that contains all the web
pages for a particular web site and has special software installed to send these web
pages to web browsers that request them.
52
ONLINE AUCTION 084991223
The client cant tell difference between an ASP page and a static page because it
receives just HTML text in both cases. When the web server processes an ASP
page, all the programmatic code is interpreted on the server-none of it is sent to the
client. The web plays a more active role when an ASP page is requested by the
client.
.NET FRAMEWORK
When .NET first appeared, it introduced a small avalanche of new technologies.
There was a whole new way to write web applications (ASP.NET), a whole new
way to connect to databases (ADO.NET), new type safe languages (C# and VB
.NET), and a managed runtime (the CLR). Not least among these new technologies
was Windows Forms, a library of classes for building Windows applications.
ASP.NET is Microsofts next-generation technology for creating server side web
applications. Its built on the Microsoft .NET Framework, which is a cluster of
closely related technologies that revolutionize everything from database access to
distributed applications. ASP.NET is one of the most important components of
the .NET Framework its the part that enables you to develop high-performance
web applications.
53
ONLINE AUCTION 084991223
Its not hard to get developers interested in ASP.NET. Without exaggeration,
ASP.NET is the most complete platform for web development thats ever been put
together. It far out classes its predecessor, ASP, which was designed as a quickand-dirty set of tools for inserting dynamic content into ordinary web pages. By
contrast, ASP.NET is a full-blown platform for developing comprehensive,
blisteringly fast applications.
ASP.NET
When the first version of the .NET Framework was released nearly a decade ago, it
was the start of a radical new direction in software design. Inspired by the best of
Java, COM, and the Web, and informed by the mistakes and limitations of previous
technologies, Microsoft set out to hit the reset button on their development
platform. The result was a set of surprisingly mature technologies that developers
could use to do everything from building a Windows application to executing a
database query, and a web-site-building tool known as ASP.NET.
Today, ASP.NET is as popular as ever, but its no longer quite as revolutionary.
And, although the basic functionality that sits at the heart of ASP.NET is
surprisingly virtually the same as it was ten years ago, Microsoft has added layers
of new features and higher-level coding abstractions. It has also introduced at least
54
ONLINE AUCTION 084991223
one new direction that competes with traditional ASP.NET programming, which is
Called ASP.NET MVC.
The Evolution of ASP.NET
When Microsoft released ASP.NET 1.0, even it didnt anticipate how
enthusiastically the technology would be adopted. ASP.NET quickly became the
standard for developing web applications with Microsoft technologies and a
heavy-hitting competitor against all other web development platforms. Since that
time, ASP.NET has had several updates. The following sections explain how
ASP.NET has evolved over the years.
ASP.NET 4
Parallel Extensions to improve support for parallel computing, which target multicore or distributed systems. To this end, they included technologies like PLINQ
(Parallel LINQ), a parallel implementation of the LINQ engine, and Task Parallel
Library, which exposes parallel constructs via method calls. New Visual Basic
.NET and C# language features, such as statement lambdas, implicit line
continuations, dynamic dispatch, named parameters, and optional parameters.
Support for Code Contracts.
55
ONLINE AUCTION 084991223
FEATURES OF ASP.NET
#1: ASP.NET is integrated with the .NET Framework.
#2: ASP.NET Is Compiled, Not Interpreted.
#3: ASP.NET Is Multilanguage.
#4: ASP.NET Is Hosted by the Common Language Runtime.
#5: ASP.NET Is Object-Oriented.
#6: ASP.NET supports all Browsers.
#7: ASP.NET Is Easy to Deploy and Configure.
ABOUT HTML
HTML is a computer language devised to allow website creation. These websites
can then be viewed by anyone else connected to the Internet. It is relatively easy to
learn, with the basics being accessible to most people in one sitting; and quite
powerful in HTML it allows you to create. It is constantly undergoing revision and
evolution to meet the demands and requirements of the growing Internet audience
under the direction of the W3C, the organization charged with designing and
maintaining the language.
56
ONLINE AUCTION 084991223
The definition of HTML is HyperText Markup Language.
HyperText is the method by which you move around on the web by clicking on
special text called hyperlinks which bring you to the next page. The fact that it
ishyper just means it is not linear i.e. you can go to any place on the Internet
whenever you want by clicking on links there is no set order to do things in.
Markup is what html tags do to the text inside them. They mark it as a certain type
of text (italicised text, for example). html is a Language, as it has code-words and
syntax like any other language.
How does it work?
consists of a series of short codes typed into a text-file by the site author these
are the tags. The text is then saved as a html file, and viewed through a browser,
like Internet Explorer or Netscape Navigator. This browser reads the file and
translates the text into a visible form, hopefully rendering the page as the author
had intended. Writing your own html entails using tags correctly to create your
vision.
57
ONLINE AUCTION 084991223
C#
Microsoft C# (pronounced C sharp) is a new programming language designed for
building a wide range of enterprise applications that run on the .NET Framework.
An evolution of Microsoft C and Microsoft C++, C# is simple, modern, type safe,
and object oriented. C# code is compiled as managed code, which means it
benefits from the services of the common language runtime. These services include
language interoperability, garbage collection, enhanced security, and improved
versioning support.
C# is introduced as Visual C# in the Visual Studio .NET suite. Support for Visual
C# includes project templates, designers, property pages, code wizards, an object
model, and other features of the development environment. The library for Visual
C# programming is the .NET Framework.
58
ONLINE AUCTION 084991223
About Internet Information Services (IIS):
Internet Information Services (IIS) is the Windows component that makes it easy
to publish information and bring business applications to the Web. IIS makes it
easy for you to create a strong platform for network applications and
communications
Internet Information Services 5.1 has many features to help Web administrators to
create scalable, flexible Web applications.
Security
Administration
Programmability
Internet Standards
Microsoft Internet Information Services 5.0 and 5.1 comply with the HTTP 1.1
standard, including features such as PUT and DELETE, the ability to customize
HTTP error messages, and support for custom HTTP headers.
IIS 5.1 offers greater protection and increased reliability for your Web applications.
By default, IIS runs all of your applications in a common or pooled process that is
separate from core IIS processes.
59
ONLINE AUCTION 084991223
In IIS 5.1, administrators and application developers have the ability to add custom
objects, properties, and methods to the existing ADSI provider, giving
administrators even more flexibility in configuring their sites
Internet Information Services (IIS) makes it easy for you to publish information on
the Internet or your intranet. IIS includes a broad range of administrative features
for managing Web sites and your Web Server. With programmatic features like
Active Server Pages (ASP), you can create and deploy scalable, flexible Web
applications.
60
ONLINE AUCTION 084991223
INTRODUCTION SQL
More than 10 years ago, the biggest factor in the performance of a business
application is the speed of the SQL it runs. It took me longer to realize just how
much room for improvement typically lies in that SQL. The SQL that most affects
the load on a system and the productivity of its end users can usually be improved
by a large factor. In the 1970s, IBM developed a product called SEQUEL, or
Structured English Query Language, which ultimately became SQL, the Structured
Query Language.
IBM, along with other relational database vendors, wanted a standardized method
for accessing and manipulating data in a relational database. Over the decades,
many competing languages have allowed programmers and developers to access
and manipulate data. However, few have been as easy to learn and as universally
accepted as SQL. Programmers and developers now have the benefit of learning a
language that, with minor adjustments, is applicable to a wide variety of database
applications and products. SQL in a Nutshell describes four implementations of the
current SQL standard, SQL99 (also known as SQL3): Microsofts SQL Server,
MySQL, Oracle, and SQL. For those migrating from implementations of the
earlier SQL standard,
The Relational Database Model Relational Database Management Systems
(RDBMSs), such as SQL Server and Oracle, are the primary engines of
61
ONLINE AUCTION 084991223
information systems worldwide, particularly Internet/Intranet applications and
distributed client/server computing systems.
An RDBMS is defined as a system whose users view data as a collection of tables
related to each other through common data values. Data is stored in tables, and
tables are composed of rows and columns. Tables of independent data can be
linked (or related) to one another if they each have columns of data (called keys)
that represent the same data value. This concept is so common as to seem trivial;
however, it was not so long ago that achieving and programming a system capable
of sustaining the relational model was considered a long shot that would have
limited usefulness.
SYSTEM DESIGN
62
ONLINE AUCTION 084991223
The objective of the system design is to deliver the requirements as specified in the
feasibility report. System design involves first logical design (logical design) and then
physical construction (detailed design) of the system. The logical design describes the
structure and characteristics of features, such as the outputs, inputs, files, databases, and
procedures. The physical construction produces actual program software, files, and a
working system.
A two part -design process:
The two design documents describe the same system, bit in different ways because
of the different audiences for the documents. The conceptual design answers the
following questions.
Where will the data come from?
What will happen to the data in the system?
How will the system look to users?
What choices will be offered to users?
What is the timing of events?
How will the reports and screens look like?
The conceptual design describes the system in language understandable to the
customer. It does not contain any technical jargons and is independent of
implementation.
63
ONLINE AUCTION 084991223
By contrast, the technical design describes the hardware configuration, the
software needs, the communication interfaces, the input and output of the system,
the network architecture, and any thing else that translates the requirement into the
solution to the customer problem.
Sometimes customers are very sophisticated and they can understand the what
and how together. This can happen when customers are themselves software
developers and may not require conceptual design. In such a cases comprehensive
design document may be produced.
OBJECTIVES OF DESIGN:
Since the simplification (i.e. the outside view) of a program should be as free as
possible aspects imposed by how the program will work (i.e. the inside view),
it is seldom a document from which coding can directly be done.
So design the gap between specifications and coding; taking the specifications,
deciding how the program will be organized, and the method it will used, in
sufficient detail as to be direct code able.
If the specifications call for a large or complex program (or both) then the design is
quite likely to work down through a no of levels. At each level, breaking the
implementation problem into a combination of smaller and simpler problems.
64
ONLINE AUCTION 084991223
Filling a large gap will involve a no of steeping stone! The wider the gap, the
larger the no of steeping stones. The design needs to be
Correct and complete
Understandable
At the right level
Maintainable and to facilitate maintenance of the product code software
designer do not arrive at a finished designed document immediately but
developed a design iteratively through a no of different phases. The design
process involves adding details as the designed developed with constant
backtracking to correct earlier, less formal, design. The starting point is an
informal design which is refined by adding information to make it consistent
and make it consistent and complete.
65
ONLINE AUCTION 084991223
MODULARIZATION DETAILS
1. MODULAR DESIGN CONCEPTS
(i) Functional Independence: The concept of functional independence is a direct
outgrowth of modularity and the concepts of abstraction and information hiding.
The principle of information hiding suggests that modules be characterized by
design decisions that (each) hides from all others. In other words modules should
be specified and designed so that information (procedure and data) contained
within a module is inaccessible to other modules that have no need for such
information. Hiding implies that effective modularity can be achieved by defining
a set of independent modules that communicate with one another only that
information necessary to achieve software function. Abstraction helps to define the
procedure entities that make up the software. As data and procedure are hidden
from other parts of the software inadvertent errors introduced during modification
are less likely to propagate to other locations within the software.Functional
independence is achieved by developing modules with single-minded function
and an aversion to excessive interaction with other modules.
Advantages: Independent modules are easier to maintain (and test) because
secondary effects caused by design or code modification are limited, error
66
ONLINE AUCTION 084991223
propagation is reduced, and reusable modules are possible.Thus with taking utmost
care of this concept we have maintained functional independence in our project
ONLINE AUCTION at some extent that required interaction among different
modules is maintained.
(ii) Cohesion: Cohesion of a module represents how tightly bound the internal
elements of the module are to one another. Cohesion of a module gives the
designer an idea about whether the different elements of a module belong together
in the same module.
(iii) Coupling: Coupling is a measure of interconnection among modules in a
software structure. Coupling depends on the interface complexity between
modules, the point at which entry or reference is made to a module, and what data
pass across the interface. In software design, we strive for lowest possible
coupling. Simple connectivity among modules results in software that is easier to
understand and less prone to a ripple effect when errors occur at one location and
propagate through a system.
Data coupling: Data coupling means simple argument list (data) is passed and a
one to one correspondence exists. A variation of data coupling is found when a
portion of a data structure rather than simple arguments is passed via a module
interface.
67
ONLINE AUCTION 084991223
Control coupling: When a control flag (a variable that controls decisions in a
subordinate or super ordinate module) is passed between modules.
External coupling: It is a relatively high level of coupling occurs when modules
are tied to an environment external to software.
Common coupling: When a number of modules reference a global data area. In
ONLINE AUCTION we have maintained the use of global data but restricted
ourselves against the common consequences of this coupling.
Content coupling: The highest degree of coupling, content coupling occurs when
one module makes use of data or control information maintained within the
boundary of another module. Secondarily, content coupling occurs when branches
are made into the middle of a module. As this type of coupling makes software
complex so in ONLINE AUCTION we have tried our best to avoid such coupling.
As the cohesion and coupling are clearly related. Usually the greater the cohesion
of each module in a system, the lower the coupling between modules is. So we
have maintained a balance between these two engineering concepts.
68
ONLINE AUCTION 084991223
SPECIFICATION OF MODULES:
Module specification is the major part of system design specification. All modules
in the system should be identified when the system design is complete, and these
modules should be specified in the document. To specify a module, the design
document must specify,
(i) The abstract behavior of the module: specifying the modules functionality or
its input/output.
(ii) The interface of the module: All data items, their types, and whether they are
for input and /or output.
(iii) All other modules used by the module being specified: This information is
quiet useful in maintaining and understanding the digram.
Client Review:
Client involvement is important in all aspects of design and development of every
successful project. To this end, client is encouraged to understand and input his
reviews throughout the project. Upon completion of each phase, a client review is
conducted. Reviews serve to verify that the program is instructionally sound, meets
established milestones and budget and reflects the expectations and goals of the
69
ONLINE AUCTION 084991223
client.
Control design:
The control design indicates necessary procedures which will ensure correctness of
processing, accuracy of data, timely output etc. This will ensure that the system is
functioning as per plan. One of the controls the access control is achieved by
UserID and password.
All the steps of system design are fully implemented in the project.
70
ONLINE AUCTION 084991223
DATA INTIGRITY AND CONTRAINTS
Security constraints guard against accidental or malicious tampering with data,
whereas integrity constraints ensure that any properly authorized access, alteration,
deletion, or insertion of the data in the database does not change the consistency
and validity of the data. This requires that there is a need for guarding against
invalid database operations. An operation here is used to indicate any action
performed on behalf of a user or application program that modifies the state of the
database. Such operations are the result of actions such as update, insert, or delete.
In short, invalid changes have to be guarded against by the security subsystem.
Database integrity involves the correctness of data; this correctness has to be
preserved in the presence of concurrent operations, errors in the users operations
and application programs, and failures in hardware and software. Two facets of
maintaining the integrity of data in the presence of concurrent operations and
failures of various types. For example, the concurrency control mechanism ensures
that two concurrent transactions are serialized. However, the integrity constraints
must be applied to both these concurrent operations and these constraints ensures
that each of these transactions, when run to completion, concurrently or in
isolation, will not cause the database to become invalid. The recovery subsystem
ensures that failures of various types, which may cause the loss of some of the
actions of one or more transactions, will not cause the database to become
inconsistent. We consider some type of constraints that the database has to enforce
to maintain the consistency and validity of data. One aspect that has to be dealt
with by the integrity subsystem is to ensure that only valid values can be assigned
to each data-item. This is referred to as domain integrity. Another set of integrity
71
ONLINE AUCTION 084991223
constraints are the so-called structural and semantic constraints. Some of these
types of constraints are addressed by the data models used and others are addressed
in the design of the database by combining appropriate functional dependencies
indifferent records. Some if not most of the functional dependencies can be
expressed if the DBMS allows each record type or relation to have an associated
primary key.
In traditional system, application programs were responsible for the validation of
data and maintaining the consistency of the data used by the programs. However,
depending on data application programs to perform these checks has the following
drawback.
Each application program must have correct validation and consistency
check routines; a failure in one program could lead to database
inconsistencies.
Each application program must be aware of the semantic of the complete
database to enforce the correct consistency checks; this is not always the
case and unnecessarily burdens the application program writers.
There will be considerable duplication of efforts.
Integrity constraints are hard to understand when they are buried in the code
of application programs.
No consistency or validity checks are possible for direct database
manipulation using a query language.
Centralizing the integrity checks directly under the DBMS reduces
duplication and ensures the consistency and validity of the database.
The centralized integrity constraints can be maintained in a system
catalog and
72
ONLINE AUCTION 084991223
can be accessible to the database users via the query language. This
does not rule out an application program performing some specific
checking, including input validation.
Component level design (Procedural design):
Component level Design establishes the algorithmic detail required to
manipulate
data
structures,
effect
communication
between
software
components via their interface, and implement the processing algorithms
allocated to each component.
Design representations of data, architecture, and interfaces form the foundation
for component-level design.
73
ONLINE AUCTION 084991223
DATABASE DESIGN AND TABLE STRUCTURE
Admin Master
Attributes
i_autoid
Username
Password
Createdate
Datatype
int
Varchar(50)
Varchar(50)
datetime
Size
Datatype
Int
Int
Int
Int
Date
date
Varchar(100)
datetime
Size
Auction master
Attributes
i_autoid
Userid
starting_amount
Itemid
Startingdate
Endingdate
Description
CreateDate
Bid details
74
ONLINE AUCTION 084991223
Attributes
i_autoid
i_refid
i_userid
i_bidprice
Createdate
Datatype
int
int
int
int
datetime
Size
Datatype
int
int
datetime
Size
Datatype
int
Varchar(50)
Varchar(50)
Varchar(50)
Varchar(50)
datetime
Size
Bid master
Attributes
i_autoid
i_auctionid
Createdate
Contacts Details
Attributes
i_autoid
Name
Mobileno
Msg
Email
Createdate
75
ONLINE AUCTION 084991223
Feedback details
Attributes
i_autoid
Name
Emailed
Subject
Feedback
Createdate
Datatype
int
Varchar(50)
Varchar(50)
Varchar(50)
Varchar(100)
datetime
Size
Datatype
Int
Int
Varchar(50)
Varchar(50)
datetime
Size
Item Details Master
Attributes
i_autoid
i_refid
Itemname
Itemimage
Createdate
76
ONLINE AUCTION 084991223
Type Master
Attributes
i_autoid
Typename
Typeimage
Createdate
Datatype
Int
Varchar(50)
Varchar(50)
datetime
Size
Datatype
Int
Int
Varchar(50)
Varchar(100)
bigint
Varchar(50)
Varchar(50)
Varchar(50)
datetime
Size
Datatype
int
Varchar(50)
Varchar(50)
Varchar(50)
Varchar(50)
datetime
Size
Type User Details
Attributes
i_autoid
ref_id
user_type
address
mobile_no
Email_id
account_no
bankname
createdate
User Master
Attributes
i_autoid
username
password
Question
ans
Createdate
77
ONLINE AUCTION 084991223
User Interface
Index
This page have many options like it shows the list of products in which a user can
bid or set auction , user can login from this page with the username and password
given to him by registration. If a new user wants to do a auction or bid he can sign
up from the sign up link.
78
ONLINE AUCTION 084991223
Registration
From this page user can register himself to bid and to do a auction on the site. He
has to enter his full details like his bank account no and mobile no and other
important details he can select option of vendor customer or both at the time of
registration.
79
ONLINE AUCTION 084991223
Password Recovery
If a user forgot his password he/she can retrieve his password from this page.
He has to answer his security question and enter his username both information
should be correct if he/she wants to retrieve his/her password after clicking on
submits.
80
ONLINE AUCTION 084991223
About Us
This page shows about the project all details summary of the project.
81
ONLINE AUCTION 084991223
Contact us
If a user wants to contact to the admin of the website he/she can fill the form his all
details like email id mobile no and description about himself.
82
ONLINE AUCTION 084991223
Feedback Form
If users wants to give a feedback about the site . his/her problems suggestions and
other type of feedback he/she can fill the feedback form and this information will
send to the admin of the site.
83
ONLINE AUCTION 084991223
Vendor Account
This is vendor account page after vendor login this page will show this page have
all details of user his mobile no bank account details address etc. he can edit his
details and he can start auction from the given categories by clicking on it. All
auctions by current user will also shows in this page.
84
ONLINE AUCTION 084991223
Credit Card
85
ONLINE AUCTION 084991223
Debit Card
86
ONLINE AUCTION 084991223
Add Auction page
When a user click on categories of product all products will show in this page in
that categories .like a user clicks on electronics then all related products to
electronics will shows in this page user can click on these items and then start
auction.
87
ONLINE AUCTION 084991223
Add Auction Details
After selecting the item for bidding user will add details of auction from this page
like starting date ending date of the auction and starting price for bidding and
description of his product.
88
ONLINE AUCTION 084991223
Admin
Admin Login
From this page admin of the site can login with his username and password. To
manage the site admin will use this page to login.
89
ONLINE AUCTION 084991223
Admin Page
This page opens after admins login from this page side menus have all the options
for the admin , admin can add items delete existing items and updates items.
90
ONLINE AUCTION 084991223
Add Items
From this page admin can add categories and add items on added categories in
which a vendor can add auctions to the site and bidder can bid on the site.
91
ONLINE AUCTION 084991223
Feedback details
This page shows admin all details of feedback which users and visitors sends to
admin by feedback form. Admin can manage all the feedback details .
92
ONLINE AUCTION 084991223
Contact Details
When admin clicks on contact details from the side menus this page will open this
page shows all the details send by user then admin can manage it and contact to the
users and visitors of the website from this details.
93
ONLINE AUCTION 084991223
Auction Details
This page shows all the running auctions on the site all details of auction last
bidder starting date ending date and price of bidding and maximum bid and bid
user etc. all the details will shows to admin from this page.
94
ONLINE AUCTION 084991223
Coding
Data Context Class
using System;
using System.Collections.Generic;
using System.Web;
using System.Data;
using System.Data.SqlClient;
public class DataContext
{
SqlConnection con = new SqlConnection();
SqlCommand cmd = new SqlCommand();
SqlDataAdapter da = new SqlDataAdapter();
//SqlDataReader dr = new SqlDataReader();
public void Openconnection()
{
if (con.State == ConnectionState.Closed)
{
try
{
95
ONLINE AUCTION 084991223
string constring = "Data Source=.; Initial Catalog=onlineauction; Integrated
Security=True";
con.ConnectionString = constring;
con.Open();
cmd.Connection = con;
}
catch (Exception ex)
{
ex.Message.ToString();
}
}
}
public void CloseConnection()
{
if (con.State == ConnectionState.Open)
{
con.Close();
}
}
public DataTable getdataTable(string Query)
96
ONLINE AUCTION 084991223
{
DataTable dt = new DataTable();
Openconnection();
cmd.CommandType = CommandType.Text;
cmd.CommandText = Query;
da.SelectCommand = cmd;
da.Fill(dt);
CloseConnection();
return dt;
}
public int executeNonquery(string Query)
{
Openconnection();
cmd.CommandType = CommandType.Text;
cmd.CommandText = Query;
int i = cmd.ExecuteNonQuery();
CloseConnection()
97
ONLINE AUCTION 084991223
Business Logic Class
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
/// <summary>
/// Summary description for BusinessLogic
/// </summary>
public class BusinessLogic
{
DataContext obj_datacontext = new DataContext();
public bool submitdetails(string username, string password, string name, string
Email, long mobile, string accountno, string bankname, string usertype,string
address,string ques,string ans)
{
98
ONLINE AUCTION 084991223
string query="insert into tbl_usermaster (Username,Password,question,ans)
values('"+username+"','"+password+"','"+ques+"','"+ans+"')";
int i = obj_datacontext.executeNonquery(query);
string query1 = "select max(i_autoid) as i_autoid from tbl_usermaster ";
DataTable dt = obj_datacontext.getdataTable(query1);
int refid = Convert.ToInt32(dt.Rows[0]["i_autoid"].ToString());
string query2 = "INSERT INTO tbl_userdetails (ref_id, user_type, address,
name, mobile_no, Email_id, Account_no, bankname) VALUES ('"+refid+"',
'"+usertype+"', '"+address+"', '"+name+"', '"+mobile+"', '"+Email+"',
'"+accountno+"', '"+bankname+"')";
int roweffected = obj_datacontext.executeNonquery(query2);
if (i > 0 && roweffected > 0)
{
return true;
}
else
{
99
ONLINE AUCTION 084991223
return false;
}
public DataTable getuserdetails(int userid)
{
string query = "SELECT ref_id, user_type, address, name, mobile_no,
Email_id, Account_no, bankname FROM tbl_userdetails where ref_id = '" +
userid + "'";
DataTable dt = obj_datacontext.getdataTable(query);
return dt;
}
public bool updateuserdetails(int uid, string accountno, string name, string
Email, long mobile, string bankname, string address)
{
100
ONLINE AUCTION 084991223
string query = "UPDATE tbl_userdetails SET address ='"+address+"', name
='"+name+"', mobile_no ='"+mobile+"', Email_id ='"+Email+"', Account_no
='"+accountno+"', bankname ='"+bankname+"' WHERE (ref_id = '"+uid+"')";
int i = obj_datacontext.executeNonquery(query);
if (i > 0)
{
return true;
}
else
{
return false;
}
}
public bool inserttypedata(string typeimagepath,string typename)
{
string query = "insert into tbl_typemaster (typeimage,typename)
values('"+typeimagepath+"','"+typename+"')";
101
ONLINE AUCTION 084991223
int roweffected = obj_datacontext.executeNonquery(query);
if (roweffected > 0)
{
return true;
}
else
{
return false;
}
}
public DataTable getitemtypes()
{
string query = "select * from tbl_typemaster";
DataTable dt = obj_datacontext.getdataTable(query);
return dt;
102
ONLINE AUCTION 084991223
public bool insertitemsdetails(int i_refid,string itemimagepath, string itemname)
{
string query = "insert into
tbl_itemsdetailsmaster(i_refid,itemname,itemimage)
values('"+i_refid+"','"+itemname+"','"+itemimagepath+"')";
int i = obj_datacontext.executeNonquery(query);
if (i > 0)
{
return true;
}
else
{
return false;
}
public DataTable getitemsdetails(int typeid)
103
ONLINE AUCTION 084991223
{
string query = "SELECT tbl_itemsdetailsmaster.itemname,
tbl_itemsdetailsmaster.itemimage, tbl_typemaster.i_autoid FROM
tbl_itemsdetailsmaster INNER JOIN tbl_typemaster ON
tbl_itemsdetailsmaster.i_refid = tbl_typemaster.i_autoid WHERE
(tbl_itemsdetailsmaster.i_refid = '" + typeid + "')";
DataTable dt = obj_datacontext.getdataTable(query);
return dt;
public bool addauctiondetails(DateTime effectedfrom, DateTime effectedto,
string description, int userid, int itemid, int starting_amount)
{
string query = "INSERT INTO tbl_auctionmaster (userid, itemid, startingdate,
endingdate, Description,starting_amount) VALUES ('" + userid + "','" + itemid +
"', '" + effectedfrom + "','" + effectedto + "', '" + description + "','" +
starting_amount + "')";
104
ONLINE AUCTION 084991223
int i = obj_datacontext.executeNonquery(query);
if (i > 0)
{
return true;
}
else
{
return false;
}
}
public DataTable getauctiondetails(int userid)
{
string query = "SELECT tbl_auctionmaster.itemid,
tbl_itemsdetailsmaster.itemname, tbl_itemsdetailsmaster.itemimage,
tbl_auctionmaster.starting_amount, tbl_auctionmaster.startingdate,
tbl_biddetails.i_bidprice FROM tbl_bidmaster INNER JOIN tbl_biddetails ON
tbl_bidmaster.i_autoid = tbl_biddetails.i_refid INNER JOIN tbl_auctionmaster ON
tbl_bidmaster.i_auctionid = tbl_auctionmaster.i_autoid INNER JOIN
105
ONLINE AUCTION 084991223
tbl_itemsdetailsmaster ON tbl_auctionmaster.itemid =
tbl_itemsdetailsmaster.itemname WHERE
(tbl_biddetails.i_bidprice =
MAX(tbl_biddetails.i_bidprice) AND (tbl_auctionmaster.userid = '"+userid+"'))";
DataTable dt = obj_datacontext.getdataTable(query);
return dt;
public bool submitContactForm(string name, string email, string description,
string mobileno)
{
string query = "INSERT INTO tbl_contactDetails (Name, Mobileno, Msg,
Email) VALUES ('" + name + "', '" + mobileno + "', '" + description + "', '" +
email + "')";
int roweffected = obj_datacontext.executeNonquery(query);
if (roweffected > 0)
{
return true;
}
106
ONLINE AUCTION 084991223
else
{
return false;
}
public DataTable getContactdetails()
{
string query = "select * from tbl_contactDetails";
DataTable dt = obj_datacontext.getdataTable(query);
if (dt.Rows.Count > 0)
{
return dt;
}
else
{
dt = null;
return dt;
107
ONLINE AUCTION 084991223
}
}
public DataTable getAllauctionDetails()
{
string query = "SELECT tbl_auctionmaster.itemid,
tbl_itemsdetailsmaster.itemname, tbl_itemsdetailsmaster.itemimage,
tbl_auctionmaster.startingdate, tbl_auctionmaster.endingdate,
tbl_auctionmaster.Description, tbl_auctionmaster.starting_amount,
tbl_auctionmaster.userid FROM
tbl_auctionmaster INNER JOIN
tbl_itemsdetailsmaster ON tbl_auctionmaster.itemid =
tbl_itemsdetailsmaster.i_autoid";
DataTable dt = obj_datacontext.getdataTable(query);
if (dt.Rows.Count > 0)
{
return dt;
}
else
108
ONLINE AUCTION 084991223
{
dt = null;
return dt;
}
public bool sendfeedback(string name, string emailid, string subject, string
feedback)
{
string query = "INSERT INTO tbl_feedbackdetails (name, emailid, subject,
feedback) VALUES ('"+name+"', '"+emailid+"', '"+subject+"', '"+feedback+"')";
int i = obj_datacontext.executeNonquery(query);
if (i > 0)
{
return true;
}
else
{
109
ONLINE AUCTION 084991223
return false;
}
}
public DataTable getFeedbackdetails()
{
string query = "select * from tbl_feedbackdetails";
DataTable dt = obj_datacontext.getdataTable(query);
return dt;
public DataTable recoverpassword(string username, string securityques, string
ans)
{
string query = "select * from tbl_usermaster where username =
'"+username+"'and Question='"+securityques+"'";
DataTable dt = obj_datacontext.getdataTable(query);
return dt;
}
110
ONLINE AUCTION 084991223
111
ONLINE AUCTION 084991223
Index page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Web.UI;
using System.Data;
using System.Web.UI.WebControls;
public partial class Index : System.Web.UI.Page
{
BusinessLogic obj_business = new BusinessLogic();
DataContext obj_datacontext = new DataContext();
protected void Page_Load(object sender, EventArgs e)
{
if (!IsPostBack)
{
112
ONLINE AUCTION 084991223
DataTable dt = obj_business.getitemtypes();
datalisttypes.DataSource = dt;
datalisttypes.DataBind();
}
}
protected void btnsubmit_Click(object sender, EventArgs e)
{
string query = "select* from tbl_usermaster where username =
'"+txtUsername.Text.ToString()+"'";
DataTable dt = obj_datacontext.getdataTable(query);
int refid = Convert.ToInt32(dt.Rows[0]["i_autoid"].ToString());
string query1 = "select * from tbl_userdetails where ref_id = '"+refid+"'";
DataTable dt1 = obj_datacontext.getdataTable(query1);
if (dt.Rows.Count > 0)
{
Session["username"] = dt.Rows[0]["username"].ToString();
Session["userid"] = Convert.ToInt32(dt.Rows[0]["i_autoid"].ToString());
113
ONLINE AUCTION 084991223
if(dt.Rows[0]["username"].ToString() == Session["username"].ToString()
&& dt.Rows[0]["password"].ToString()==txtpwd.Text.ToString())
{
if (dt1.Rows[0]["user_type"].ToString() == "vendor")
{
Response.Redirect("myaccountvendor.aspx?userid=" +
Session["userid"].ToString());
}
else if (dt1.Rows[0]["user_type"].ToString() == "both")
{
Response.Redirect("myaccountboth.aspx?userid=" +
Session["userid"].ToString());
}
else if (dt1.Rows[0]["user_type"].ToString() == "customer")
{
Response.Redirect("myaccountcustomer.aspx?userid=" +
Session["userid"].ToString());
}
}
114
ONLINE AUCTION 084991223
}
}
protected void btnsignup_Click(object sender, EventArgs e)
{
Response.Redirect("registration.aspx");
}
public string getSRC(object imgSRC)
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["typeimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/UserImage/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
115
ONLINE AUCTION 084991223
public string itemtype(object sURL)
{
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["typename"].ToString();
return heading;
}
protected void btnforgot_Click(object sender, EventArgs e)
{
Response.Redirect("PasswordRecovery.aspx");
}
}
116
ONLINE AUCTION 084991223
Registration Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class Registration : System.Web.UI.Page
{
string username = "";
string password = "";
string name = "";
string Email= "";
long mobile = 0;
string accountno = "";
string bankname = "";
string address = "";
117
ONLINE AUCTION 084991223
string usertype = "";
BusinessLogic obj_businesslogic = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
}
protected void btnSubmit_Click(object sender, EventArgs e)
{
username=txtUsernamereg.Text.ToString();
password=txtpasswordreg.Text.ToString();
name=txtname.Text.ToString();
Email=txtEmailid.Text.ToString();
mobile= Convert.ToInt64(txtMobileno.Text.ToString());
accountno=txtAcountno.Text.ToString();
bankname=txtBankname.Text.ToString();
address = txtAddress.Text.ToString();
if(rbtCustomer.Checked==true)
{
118
ONLINE AUCTION 084991223
usertype = "customer";
}
else if(rbtVendor.Checked==true)
{
usertype="vendor";
}
else if(rbtCustomer.Checked==true && rbtVendor.Checked==true)
{
usertype="both";
}
if(obj_businesslogic.submitdetails(username,
password,name,Email,mobile,accountno,bankname
,usertype,address,ddlSecurityques.Text.ToString(),txtSecurityans.Text.ToString()))
{
LblRegistration.Text = "Registration sucessful";
}
119
ONLINE AUCTION 084991223
}
protected void btnworks_Click(object sender, EventArgs e)
{
Response.Redirect("siteworking.aspx");
}
}
120
ONLINE AUCTION 084991223
Add Auction Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Data;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class addauction : System.Web.UI.Page
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
int typeid = Convert.ToInt32(Request.QueryString["typeid"]);
DataTable dt = obj_business.getitemsdetails(typeid);
dataitems.DataSource = dt;
dataitems.DataBind();
121
ONLINE AUCTION 084991223
}
public string getSRC(object imgSRC)
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["Itemimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/UserImage/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["itemname"].ToString();
122
ONLINE AUCTION 084991223
Add Auction Details Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class AddAuctionDetails : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
DateTime effectedfrom;
DateTime effectedto;
string description = "";
protected void Page_Load(object sender, EventArgs e)
{
if (Session["userid"]== null)
{
123
ONLINE AUCTION 084991223
Response.Redirect("Index.aspx");
}
}
protected void btnSubmit_Click(object sender, EventArgs e)
{
int userid = Convert.ToInt32(Session["userid"].ToString());
int itemid = Convert.ToInt32(Request.QueryString["itemid"].ToString());
effectedfrom = Convert.ToDateTime(txteffectfrom.Text.ToString());
effectedto = Convert.ToDateTime(txteffectto.Text.ToString());
int starting_amount = Convert.ToInt32(txtStartingprice.Text.ToString());
if (obj_businesslogic.addauctiondetails(effectedfrom, effectedto, description,
userid, itemid, starting_amount))
{
lblmessage.Text = "AUCTION ADDED";
}
}
}
124
ONLINE AUCTION 084991223
Contact Us Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class ContactUs : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
}
protected void btnSubmit_Click(object sender, EventArgs e)
{
string name = txtName.Text.ToString();
string email = txtEmailid.Text.ToString();
125
ONLINE AUCTION 084991223
string description = txtDescription.Text.ToString();
string mobileno = txtMobileno.Text.ToString();
if (obj_businesslogic.submitContactForm(name, email, description,
mobileno))
{
lblMessage.Text = "Contact Details Send We Will Contact You Shortly";
}
}
}
126
ONLINE AUCTION 084991223
Feedback Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class FeedbackForm : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
}
protected void btnSubmit_Click(object sender, EventArgs e)
{
string name = txtName.Text.ToString();
string emailid = txtEmailid.Text.ToString();
127
ONLINE AUCTION 084991223
string subject = txtsubject.Text.ToString();
string feedback = txtDescription.Text.ToString(); ;
if (obj_businesslogic.sendfeedback(name, emailid, subject, feedback))
{
txtName.Text = "";
txtsubject.Text = "";
txtEmailid.Text = "";
txtDescription.Text = "";
lblMessage.Text = "Your Feedback Sent";
}
else
{
lblMessage.Text = "Error";
}
}
}
128
ONLINE AUCTION 084991223
My Account Both
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class myaccountboth : System.Web.UI.Page
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable dt = obj_business.getitemtypes();
datalisttypes.DataSource = dt;
datalisttypes.DataBind();
}
public string getSRC(object imgSRC)
129
ONLINE AUCTION 084991223
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["typeimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/UserImage/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["typename"].ToString();
return heading;
130
ONLINE AUCTION 084991223
My account Vendor Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class myaccount : System.Web.UI.Page
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable dt = obj_business.getitemtypes();
datalisttypes.DataSource = dt;
datalisttypes.DataBind();
131
ONLINE AUCTION 084991223
public string getSRC(object imgSRC)
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["typeimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/UserImage/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
132
ONLINE AUCTION 084991223
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["typename"].ToString();
return heading;
}
133
ONLINE AUCTION 084991223
My account Customer
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class myaccount : System.Web.UI.Page
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable dt = obj_business.getitemtypes();
datalisttypes.DataSource = dt;
datalisttypes.DataBind();
134
ONLINE AUCTION 084991223
public string getSRC(object imgSRC)
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["typeimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/UserImage/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
DataRowView dRView = (DataRowView)sURL;
135
ONLINE AUCTION 084991223
string heading = dRView["typename"].ToString();
return heading;
}
136
ONLINE AUCTION 084991223
My Account Both
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class myaccountboth : System.Web.UI.Page
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable dt = obj_business.getitemtypes();
datalisttypes.DataSource = dt;
datalisttypes.DataBind();
}
public string getSRC(object imgSRC)
137
ONLINE AUCTION 084991223
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["typeimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/UserImage/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["typename"].ToString();
return heading;
138
ONLINE AUCTION 084991223
Password Recovery Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Web.UI;
using System.Data;
using System.Web.UI.WebControls;
public partial class PasswordRecovery : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
}
protected void btngetpass_Click(object sender, EventArgs e)
{
139
ONLINE AUCTION 084991223
DataTable dt =
obj_businesslogic.recoverpassword(txtusername.Text.ToString(),ddlSecurityques.T
ext.ToString(),txtans.Text.ToString());
if (dt.Rows[0]["ans"].ToString() == txtans.Text.ToString())
{
lblpassword.Text = dt.Rows[0]["password"].ToString();
}
else
{
lblpassword.Text = "Error";
}
}
}
140
ONLINE AUCTION 084991223
User Control Auction Details
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class Auctiondetails : System.Web.UI.UserControl
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
if (!IsPostBack)
{
int userid =Convert.ToInt32(Session["userid"].ToString());
DataTable auction_details = obj_business.getauctiondetails(userid);
gvMyauctions.DataSource = auction_details;
141
ONLINE AUCTION 084991223
gvMyauctions.DataBind();
}
}
public string getSRC(object imgSRC)
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["Itemimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/itemimages/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
142
ONLINE AUCTION 084991223
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["itemname"].ToString();
return heading;
}
User Control User Details
using System;
143
ONLINE AUCTION 084991223
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Data;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class UsersDetails : System.Web.UI.UserControl
{
BusinessLogic obj_business = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable dt =
obj_business.getuserdetails(Convert.ToInt32(Request.QueryString["userid"].ToStri
ng()));
txtAcountno.Text = dt.Rows[0]["account_no"].ToString();
txtAddress.Text = dt.Rows[0]["address"].ToString();
txtBankname.Text = dt.Rows[0]["bankname"].ToString();
txtEmailid.Text = dt.Rows[0]["email_id"].ToString();
144
ONLINE AUCTION 084991223
txtMobileno.Text = dt.Rows[0]["account_no"].ToString();
txtname.Text = dt.Rows[0]["name"].ToString();
lblUsertype.Text = dt.Rows[0]["user_type"].ToString();
}
protected void btnEdit_Click(object sender, EventArgs e)
{
txtAcountno.ReadOnly = false;
txtAddress.ReadOnly = false;
txtBankname.ReadOnly = false;
txtEmailid.ReadOnly = false;
txtMobileno.ReadOnly = false;
txtname.ReadOnly = false;
}
protected void btnUpdate_Click(object sender, EventArgs e)
{
string accountno = txtAcountno.Text.ToString();
string name = txtname.Text.ToString();
string Email = txtEmailid.Text.ToString();
long mobile = Convert.ToInt64(txtMobileno.Text.ToString());
145
ONLINE AUCTION 084991223
string bankname = txtBankname.Text.ToString();
string address = txtAddress.Text.ToString();
int uid = Convert.ToInt32(Request.QueryString["userid"].ToString());
if (obj_business.updateuserdetails(uid, accountno, name, Email, mobile,
bankname, address))
{
}
else
{
Response.Write("error");
}
}
}
Add Items Page
using System;
using System.Collections.Generic;
using System.Linq;
146
ONLINE AUCTION 084991223
using System.Web;
using System.Data;
using System.Web.UI;
using System.IO;
using System.Web.UI.WebControls;
public partial class admin_additems : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable dt = obj_businesslogic.getitemtypes();
ddltypes.DataSource = dt;
ddltypes.DataTextField = "typename";
ddltypes.DataValueField = "i_autoid";
ddltypes.DataBind();
147
ONLINE AUCTION 084991223
}
protected void btninsert_Click(object sender, EventArgs e)
{
if (uploadtypeimage.PostedFile != null)
{
//save the destination path of the image
string mymap = MapPath("~/");
// save the image name into ImageName
string ImageName = uploadtypeimage.FileName;
//save the full url of the image with folder name and image name
string ImageSaveURL = mymap + "Typeimages\\" + ImageName;
//upload image to the path of image
uploadtypeimage.PostedFile.SaveAs(ImageSaveURL);
uploadtypeimage.DataBind();
string typeimagepath = "~/" + "Typeimages\\" + ImageName;
148
ONLINE AUCTION 084991223
if (obj_businesslogic.inserttypedata(typeimagepath,
txttypename.Text.ToString()))
{
txtitemname.Text = "";
lblmsg0.Text = "Type Inserted";
}
}
protected void btnsubmit_Click(object sender, EventArgs e)
{
if (uploaditemimage.PostedFile != null)
{
//save the destination path of the image
string mymap = MapPath("~/");
// save the image name into ImageName
string ItemImageName = uploaditemimage.FileName;
//save the full url of the image with folder name and image name
149
ONLINE AUCTION 084991223
string ImageSave = mymap + "itemimages\\" + ItemImageName;
//upload image to the path of image
uploaditemimage.PostedFile.SaveAs(ImageSave);
uploaditemimage.DataBind();
string itemimagepath = "~/" + "itemimages\\" + ItemImageName;
string itemname = txtitemname.Text.ToString();
int i_refid = Convert.ToInt32(ddltypes.SelectedValue.ToString());
if (obj_businesslogic.insertitemsdetails(i_refid,itemimagepath,itemname))
{
txtitemname.Text = "";
lblmsg.Text = "Item Inserted";
150
ONLINE AUCTION 084991223
AdminLogin Page
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class admin_Adminlogin : System.Web.UI.Page
{
DataContext obj_datacontext = new DataContext();
protected void Page_Load(object sender, EventArgs e)
{
protected void BtnLogin_Click(object sender, EventArgs e)
151
ONLINE AUCTION 084991223
{
string query = "select* from tbl_adminmaster where username =
'"+txtUsername.Text.ToString()+"'";
DataTable dt = obj_datacontext.getdataTable(query);
if (dt.Rows.Count > 0)
{
if (txtUsername.Text.ToString() == dt.Rows[0]["username"].ToString() &&
txtPassword.Text.ToString() == dt.Rows[0]["password"].ToString())
{
Session["adminid"] = Convert.ToInt32(dt.Rows[0]["i_autoid"].ToString());
Response.Redirect("additems.aspx?id=" + Convert.ToInt32(dt.Rows[0]
["i_autoid"].ToString()))
}
152
ONLINE AUCTION 084991223
else
{
lblmessage.Text = "Invalid Username Password";
}
}
else
{
lblmessage.Text = "Username Not exist";
}
}
}
Auction Details
153
ONLINE AUCTION 084991223
using System;
using System.Collections.Generic;
using System.Linq;
using System.Data;
using System.Web;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class admin_AuctionDetails : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
protected void Page_Load(object sender, EventArgs e)
{
DataTable auctiondetails = obj_businesslogic.getAllauctionDetails();
gvauctions.DataSource = auctiondetails;
gvauctions.DataBind();
public string getSRC(object imgSRC)
154
ONLINE AUCTION 084991223
{
DataRowView dRView = (DataRowView)imgSRC;
string ImageName = dRView["Itemimage"].ToString();
if (ImageName == "NoImage")
{
return ResolveUrl(@"~/itemimages/missing.jpg");
}
else
{
return ResolveUrl(ImageName);
}
}
public string itemtype(object sURL)
{
DataRowView dRView = (DataRowView)sURL;
string heading = dRView["itemname"].ToString(); return heading;}}
Contact Details
using System;
155
ONLINE AUCTION 084991223
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Data;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class admin_Enquirydetails : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
DataTable dt = null;
protected void Page_Load(object sender, EventArgs e)
{
if (!Page.IsPostBack)
{
dt = obj_businesslogic.getContactdetails();
gvenquiry.DataSource = dt;
gvenquiry.DataBind();
156
ONLINE AUCTION 084991223
}
}
}
157
ONLINE AUCTION 084991223
Feedback Details
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Data;
using System.Web.UI;
using System.Web.UI.WebControls;
public partial class admin_FeedbackDetails : System.Web.UI.Page
{
BusinessLogic obj_businesslogic = new BusinessLogic();
DataTable dt = null;
protected void Page_Load(object sender, EventArgs e)
{
if (!Page.IsPostBack)
{
dt = obj_businesslogic.getFeedbackdetails();
158
ONLINE AUCTION 084991223
gvenquiry.DataSource = dt;
gvenquiry.DataBind();
}
}
}
159
ONLINE AUCTION 084991223
Coding for Desigining
Index
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="Index.aspx.cs" Inherits="Index" %>
<%@ Register src="Sidemenus.ascx" tagname="Sidemenus" tagprefix="uc1" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style15
{
width: 587px;
}
.style56
{
width: 132px;
}
.style57
{
width: 132px;
height: 146px;
}
.style59
{
font-size: 12px;
160
ONLINE AUCTION 084991223
font-size: 12px;
color: #847676;
font-weight: bold;
padding: 0px;
height: 32px;
}
.style60
{
height: 333px;
}
.style61
{
height: 443px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:103%; height: 267px;">
<tr>
<td class="style61" valign="top">
<uc1:Sidemenus ID="Sidemenus1" runat="server" />
</td>
<td class="style61">
<table style="width: 100%;">
<tr>
161
ONLINE AUCTION 084991223
<td class="style15" rowspan="3" valign="top">
<table style="width: 100%;">
<tr>
<td class="center_title_bar" colspan="3">
Categories</td>
</tr>
<tr>
<td colspan="3">
<asp:DataList ID="datalisttypes" runat="server"
CellPadding="2" CellSpacing="5"
Height="235px" RepeatColumns="4"
RepeatDirection="Horizontal" Width="564px">
<ItemTemplate>
<table style="border: thin solid #C0C0C0;
height: 197px; width: 119px;"><tr>
<td style="border: thin solid" class="style57"
valign="top">
<a href='addauction.aspx?typeid=<
%#Eval("i_autoid") %>'>
<asp:Image ID="Image1" runat="server"
BorderColor="#33CC33" Height="143px"
ImageUrl="<%#
getSRC(Container.DataItem) %>" Width="123px" />
</a>
</td></tr>
<tr>
162
ONLINE AUCTION 084991223
<td class="style56"
style="border: thin solid #C0C0C0;
background-image: url('images/typename_bg.gif'); background-repeat: norepeat;">
<a
href='addauction.aspx?typeid=<%#Eval("i_autoid") %>'
style="background-image:
url('images/menu_title_bg.gif'); background-repeat: no-repeat">
<asp:HyperLink ID="HyperLink1"
runat="server"
Text="<%#
itemtype(Container.DataItem) %>"></asp:HyperLink>
</a>
</td>
</tr>
</table>
</ItemTemplate>
</asp:DataList>
</td>
</tr>
<tr>
<td>
</td>
<td>
</td>
<td>
163
ONLINE AUCTION 084991223
</td>
</tr>
</table>
</td>
<td valign="top" class="style60">
<table style="width: 98%; height: 202px;">
<tr>
<td class="style59" colspan="2"
style="background-image: url('images/menu_title_bg.gif');
background-repeat: no-repeat"
valign="top">
&
nbsp;
<span class="title_box">Login </span></td>
</tr>
<tr>
<td valign="top">
Username</td>
<td valign="top">
<asp:TextBox ID="txtUsername" runat="server"
CssClass="contact_input"
Height="21px" Width="111px"></asp:TextBox>
</td>
</tr>
<tr>
164
ONLINE AUCTION 084991223
<td>
Password</td>
<td>
<asp:TextBox ID="txtpwd" runat="server"
CssClass="contact_input" Height="21px"
Width="111px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style12">
</td>
<td>
<asp:LinkButton ID="btnforgot" runat="server"
onclick="btnforgot_Click">Forgot Password</asp:LinkButton>
</td>
</tr>
<tr>
<td class="style12">
<asp:LinkButton ID="btnsignup" runat="server"
onclick="btnsignup_Click">SignUp</asp:LinkButton>
</td>
<td>
<asp:Button ID="btnsubmit" runat="server"
onclick="btnsubmit_Click"
Text="Submit" CssClass="en-send" Height="30px"
Width="77px" />
165
ONLINE AUCTION 084991223
</td>
</tr>
<tr>
<td class="title_box" colspan="2">
News</td>
</tr>
<tr>
<td colspan="2">
</td>
</tr>
<tr>
<td colspan="2">
</td>
</tr>
<tr>
<td colspan="2">
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td>
</td>
</tr>
<tr>
166
ONLINE AUCTION 084991223
<td>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td>
</td>
<td>
</td>
</tr>
</table>
</asp:Content>
167
ONLINE AUCTION 084991223
Registration
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="Registration.aspx.cs" Inherits="Registration"
%>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style49
{
width: 465px;
}
.style19
{
width: 463px;
}
.style46
{
height: 24px;
}
style51
{
width: 355px;
168
ONLINE AUCTION 084991223
}
.style52
{
width: 402px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:103%; height: 407px; background-color: #FFFFFF;">
<tr>
<td class="style49" valign="top">
<table style="width: 214%; height: 539px;">
<tr>
<td class="style52" valign="top">
<asp:Image ID="Image1" runat="server" Height="274px"
ImageUrl="~/images/Auctions hammer.jpg" Width="337px" />
<br />
<span class="Apple-style-span"
style="border-collapse: separate; color: rgb(0, 0, 0); font-family:
'Times New Roman'; font-style: normal; font-variant: normal; font-weight: normal;
letter-spacing: normal; line-height: normal; orphans: 2; text-align: -webkit-auto;
text-indent: 0px; text-transform: none; white-space: normal; widows: 2; wordspacing: 0px; -webkit-border-horizontal-spacing: 0px; -webkit-border-verticalspacing: 0px; -webkit-text-decorations-in-effect: none; -webkit-text-size-adjust:
auto; -webkit-text-stroke-width: 0px; font-size: medium; ">
169
ONLINE AUCTION 084991223
<span class="Apple-style-span"
style="color: rgb(66, 66, 66); font-family: Arial, Helvetica, sansserif; font-size: 11px; ">
<div class="innerSec"
style="font-family: Arial, Helvetica, sans-serif; font-size: 11px;
color: rgb(66, 66, 66); outline-style: none; outline-width: initial; outline-color:
initial; width: 378px; float: left; height: 21px;">
<strong class="size14 blueText"
style="outline-style: none; outline-width: initial; outline-color:
initial; color: rgb(17, 74, 97) !important; font-size: 14px !important; ">
Create a profile today for free and receive...</strong></div>
<div class="innerSec"
style="font-family: Arial, Helvetica, sans-serif; font-size: 11px;
color: rgb(66, 66, 66); outline-style: none; outline-width: initial; outline-color:
initial; width: 382px; float: left; height: 85px;">
<ul class="dotBlack"
style="margin-top: 0px; margin-right: 0px; margin-bottom:
0px; margin-left: 0px; padding-top: 0px; padding-right: 0px; padding-bottom: 0px;
padding-left: 0px; list-style-type: none; list-style-position: initial; list-style-image:
initial; outline-style: none; outline-width: initial; outline-color: initial; width:
auto;">
<li class="blue"
style="margin-top: 0px; margin-right: 0px; margin-bottom:
0px; margin-left: 0px; padding-top: 0px; padding-right: 0px; padding-bottom: 0px;
padding-left: 15px; list-style-type: none; list-style-position: initial; list-style-image:
initial; outline-style: none; outline-width: initial; outline-color: initial; background170
ONLINE AUCTION 084991223
image: url(http://www.auction.com/images/dotBlue.gif); background-attachment:
initial; background-origin: initial; background-clip: initial; background-color:
transparent; font-size: 12px; color: rgb(110, 110, 110); line-height: 18px;
background-position: 0px 0px; background-repeat: no-repeat;">
Custom Alerts sent to your email or cell phone</li>
<li class="blue"
style="margin-top: 0px; margin-right: 0px; margin-bottom:
0px; margin-left: 0px; padding-top: 0px; padding-right: 0px; padding-bottom: 0px;
padding-left: 15px; list-style-type: none; list-style-position: initial; list-style-image:
initial; outline-style: none; outline-width: initial; outline-color: initial; backgroundimage: url(http://www.auction.com/images/dotBlue.gif); background-attachment:
initial; background-origin: initial; background-clip: initial; background-color:
transparent; font-size: 12px; color: rgb(110, 110, 110); line-height: 18px;
background-position: 0px 0px; background-repeat: no-repeat;">
Notification of Auctions relevant to you</li>
<li class="blue"
style="margin-top: 0px; margin-right: 0px; margin-bottom:
0px; margin-left: 0px; padding-top: 0px; padding-right: 0px; padding-bottom: 0px;
padding-left: 15px; list-style-type: none; list-style-position: initial; list-style-image:
initial; outline-style: none; outline-width: initial; outline-color: initial; backgroundimage: url(http://www.auction.com/images/dotBlue.gif); background-attachment:
initial; background-origin: initial; background-clip: initial; background-color:
transparent; font-size: 12px; color: rgb(110, 110, 110); line-height: 18px;
background-position: 0px 0px; background-repeat: no-repeat;">
Customized brochures</li>
<li class="blue"
171
ONLINE AUCTION 084991223
style="margin-top: 0px; margin-right: 0px; margin-bottom:
0px; margin-left: 0px; padding-top: 0px; padding-right: 0px; padding-bottom: 0px;
padding-left: 15px; list-style-type: none; list-style-position: initial; list-style-image:
initial; outline-style: none; outline-width: initial; outline-color: initial; backgroundimage: url(http://www.auction.com/images/dotBlue.gif); background-attachment:
initial; background-origin: initial; background-clip: initial; background-color:
transparent; font-size: 12px; color: rgb(110, 110, 110); line-height: 18px;
background-position: 0px 0px; background-repeat: no-repeat;">
Access to our online auctions 24/7</li>
</ul>
</div>
<br />
<br />
<br />
</span>
<asp:HyperLink ID="hyperworking" runat="server"
NavigateUrl="~/siteworking.aspx">How Does it Works ? Find
Now!</asp:HyperLink>
</span>
</td>
<td class="style51" valign="top">
<table class="style19"
style="border: 1px solid #000000; height: 374px; margin-left: 0px;">
<tr>
<td class="style46" style="border-style: double" colspan="2">
<span class="Apple-style-span"
172
ONLINE AUCTION 084991223
style="font-family: Arial, Helvetica, sans-serif; font-size:
22px; font-weight: bold; text-align: left; white-space: nowrap;">Join Now it's easy
!<br />
</span><br />if you Already Registered Sign In
<asp:HyperLink ID="hyprlogin" runat="server"
NavigateUrl="~/Index.aspx">Here!</asp:HyperLink>
</td>
</tr>
<tr>
<td class="style46" style="border-style: double">
Username</td>
<td class="style47">
<asp:TextBox ID="txtUsernamereg" runat="server"
Width="139px"></asp:TextBox>
<asp:RequiredFieldValidator ID="RequiredFieldValidator3"
runat="server"
ControlToValidate="txtUsernamereg"
ErrorMessage="UserName Reqired"></asp:RequiredFieldValidator>
</td>
</tr>
<tr>
<td class="style44" style="border-style: double">
Password</td>
<td class="style45">
173
ONLINE AUCTION 084991223
<asp:TextBox ID="txtpasswordreg" runat="server"
TextMode="Password"
Width="139px"></asp:TextBox>
<asp:RequiredFieldValidator ID="RequiredFieldValidator4"
runat="server"
ControlToValidate="txtpasswordreg"
ErrorMessage="Password Required"></asp:RequiredFieldValidator>
</td>
</tr>
<tr>
<td class="style29" style="border-style: double" valign="top">
Confirm Password</td>
<td class="style33" valign="top">
<asp:TextBox ID="txtcpwdreg" runat="server"
TextMode="Password" Width="139px"></asp:TextBox>
<asp:CompareValidator ID="CompareValidator1" runat="server"
ControlToCompare="txtpasswordreg"
ControlToValidate="txtcpwdreg"
ErrorMessage="Password Not
Match"></asp:CompareValidator>
</td>
</tr>
<tr>
<td class="style42" style="border-style: double">
Name</td>
<td class="style43">
174
ONLINE AUCTION 084991223
<asp:TextBox ID="txtname" runat="server"
Width="139px"></asp:TextBox>
<asp:RequiredFieldValidator ID="RequiredFieldValidator6"
runat="server"
ControlToValidate="txtname" ErrorMessage="Enter Full
Name"></asp:RequiredFieldValidator>
</td>
</tr>
<tr>
<td class="style40" style="border-style: double">
Email</td>
<td class="style41">
<asp:TextBox ID="txtEmailid" runat="server"
Width="139px"></asp:TextBox>
<asp:RequiredFieldValidator ID="RequiredFieldValidator12"
runat="server"
ControlToValidate="txtEmailid" ErrorMessage="Enter Full
Name"></asp:RequiredFieldValidator>
</td>
</tr>
<tr>
<td class="style38" style="border-style: double">
Mobile No</td>
<td class="style39">
<asp:TextBox ID="txtMobileno" runat="server"
Width="139px"></asp:TextBox>
175
ONLINE AUCTION 084991223
</td>
</tr>
<tr>
<td class="style38" style="border-style: double">
AccountNo</td>
<td class="style39">
<asp:TextBox ID="txtAcountno" runat="server"
Width="139px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style36" style="border-style: double">
BankName</td>
<td class="style37" valign="top">
<asp:TextBox ID="txtBankname" runat="server"
Width="139px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style31" style="border-style: double">
Usertype</td>
<td class="style34">
<asp:CheckBox ID="rbtVendor" runat="server" Text="Vendor" />
<asp:CheckBox ID="rbtCustomer" runat="server" Text="customer"
/>
</td>
176
ONLINE AUCTION 084991223
</tr>
<tr>
<td class="style31" style="border-style: double">
Security Question</td>
<td class="style34">
<asp:DropDownList ID="ddlSecurityques" runat="server"
Height="26px"
Width="142px">
<asp:ListItem>What Is your Name?</asp:ListItem>
</asp:DropDownList>
</td>
</tr>
<tr>
<td class="style31" style="border-style: double">
Ans</td>
<td class="style34">
<asp:TextBox ID="txtSecurityans" runat="server"
Width="139px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style30">
Address</td>
<td class="style32">
<br />
177
ONLINE AUCTION 084991223
<asp:TextBox ID="txtAddress" runat="server" Height="93px"
TextMode="MultiLine"
Width="216px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style30">
</td>
<td class="style32">
<asp:Button ID="btnSubmit" runat="server"
onclick="btnSubmit_Click"
Text="Submit" Width="83px" />
</td>
</tr>
<tr>
<td class="style30">
</td>
<td class="style32">
<asp:Label ID="LblRegistration" runat="server"></asp:Label>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td class="style52">
178
ONLINE AUCTION 084991223
</td>
<td class="style51">
</td>
</tr>
<tr>
<td class="style52">
</td>
<td class="style51">
</td>
</tr>
</table>
</td>
</tr>
</table>
</asp:Content>
179
ONLINE AUCTION 084991223
Password Recovery
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="PasswordRecovery.aspx.cs"
Inherits="PasswordRecovery" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
width: 158px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:100%;">
<tr>
<td class="style1">
Username</td>
<td>
<asp:TextBox ID="txtusername" runat="server"></asp:TextBox>
</td>
<td>
</td>
</tr>
<tr>
<td class="style1">
Security Question</td>
<td>
<asp:DropDownList ID="ddlSecurityques" runat="server"
Height="26px"
Width="182px">
<asp:ListItem>What Is your Name?</asp:ListItem>
</asp:DropDownList>
</td>
<td>
</td>
</tr>
180
ONLINE AUCTION 084991223
<tr>
<td class="style1">
ans</td>
<td>
<asp:TextBox ID="txtans" runat="server"></asp:TextBox>
</td>
<td>
</td>
</tr>
<tr>
<td class="style1">
</td>
<td>
<asp:Button ID="btngetpass" runat="server"
onclick="btngetpass_Click"
Text="Submit" />
</td>
<td>
</td>
</tr>
<tr>
<td class="style1">
Your Password Is</td>
<td>
<asp:Label ID="lblpassword" runat="server"></asp:Label>
</td>
<td>
</td>
</tr>
</table>
</asp:Content>
181
ONLINE AUCTION 084991223
My Account vendor
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="myaccountvendor.aspx.cs"
Inherits="myaccount" %>
<%@ Register src="UsersDetails.ascx" tagname="UsersDetails" tagprefix="uc1"
%>
<%@ Register src="Auctiondetails.ascx" tagname="Auctiondetails"
tagprefix="uc2" %>
<%@ Register src="Sidemenus.ascx" tagname="Sidemenus" tagprefix="uc3" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style50
{
width: 500px;
}
.style60
{
width: 164px;
}
182
ONLINE AUCTION 084991223
.style55
{
width: 401px;
}
.style57
{
width: 132px;
height: 146px;
}
.style56
{
width: 132px;
}
.style59
{
font-size: 12px;
color: #159dcc;
text-align: justify;
line-height: 15px;
width: 433px;
padding: 5px 0;
}
.style58
{
height: 33px;
}
183
ONLINE AUCTION 084991223
.style53
{
width: 433px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style=" height: auto; width: 978px;">
<tr>
<td style="width: 100%; height: auto;" valign="top">
<table style="width: 100%; height: 558px"><tr><td class="style50"
valign="top">
<table style="width: 98%; height: 88px;">
<tr>
<td class="style60" valign="top">
<uc3:Sidemenus ID="Sidemenus1" runat="server"
/>
</td>
<td rowspan="3" valign="top">
<table style="width:80%; height: 580px;">
<tr>
<td class="style52" valign="top">
<table style="width: 42%; height: 504px;">
<tr>
<td style="font-size: medium" valign="top">
184
ONLINE AUCTION 084991223
<strong>CATEGORIES</strong></td>
</tr>
<tr>
<td class="style55">
<asp:DataList ID="datalisttypes" runat="server"
CellPadding="2" CellSpacing="5"
Height="368px" RepeatColumns="3"
RepeatDirection="Horizontal">
<ItemTemplate>
<br />
<table style="border: thin solid #C0C0C0;
height: 197px; width: 119px;"><tr>
<td style="border: thin solid" class="style57"
valign="top">
<a href='addauction.aspx?typeid=<
%#Eval("i_autoid") %>'>
<asp:Image ID="Image1" runat="server"
BorderColor="#33CC33" Height="143px"
ImageUrl="<%#
getSRC(Container.DataItem) %>" Width="123px" />
</a>
</td></tr>
<tr>
<td class="style56"
185
ONLINE AUCTION 084991223
style="border: thin solid #C0C0C0;
background-image: url('images/typename_bg.gif'); background-repeat: norepeat;">
<a
href='addauction.aspx?typeid=<%#Eval("i_autoid") %>'
style="background-image:
url('images/menu_title_bg.gif'); background-repeat: no-repeat">
<asp:HyperLink ID="HyperLink1"
runat="server"
Text="<%#
itemtype(Container.DataItem) %>"></asp:HyperLink>
</a>
</td>
</tr>
</table>
</ItemTemplate>
</asp:DataList>
</td>
</tr>
</table>
</td>
<td class="style59" valign="top">
Users Detail<br />
<uc1:UsersDetails ID="UsersDetails1" runat="server" />
</td>
</tr>
186
ONLINE AUCTION 084991223
<tr>
<td class="style58" colspan="2"
style="background-image: url('images/bar_bg.gif');
background-repeat: no-repeat">
Auctions By You </td>
</tr>
<tr>
<td class="style52" colspan="2">
</td>
</tr>
<tr>
<td class="style52">
</td>
<td class="style53">
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td class="style60">
</td>
</tr>
<tr>
<td class="style60">
</td>
187
ONLINE AUCTION 084991223
</tr>
</table>
</td></tr></table></td>
</tr>
188
ONLINE AUCTION 084991223
My account Customer
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="myaccountcustomer.aspx.cs"
Inherits="myaccountcustomer" %>
<%@ Register src="UsersDetails.ascx" tagname="UsersDetails" tagprefix="uc1"
%>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style54
{
width: 720px;
}
.style55
{
}
.style56
{
height: 33px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
189
ONLINE AUCTION 084991223
<table style="width:100%;">
<tr>
<td class="style56" colspan="2"
style="background-image: url('images/bar_bg.gif');
background-repeat: no-repeat">
</td>
<td class="style56">
</td>
</tr>
<tr>
<td colspan="2" valign="top">
</td>
<td>
<uc1:UsersDetails ID="UsersDetails1" runat="server" />
</td>
</tr>
<tr>
<td class="style55">
</td>
<td class="style54">
</td>
<td>
</td>
</tr>
</table>
</asp:Content>
190
ONLINE AUCTION 084991223
My account Both
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="myaccountboth.aspx.cs"
Inherits="myaccountboth" %>
<%@ Register src="UsersDetails.ascx" tagname="UsersDetails" tagprefix="uc1"
%>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style48
{
}
.style52
{
width: 412px;
}
.style55
{
width: 401px;
}
.style57
{
width: 132px;
height: 146px;
}
.style56
{
width: 132px;
}
.style53
{
width: 483px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
191
ONLINE AUCTION 084991223
<table style="width:100%;">
<tr>
<td class="style48">
<table style="width:100%; height: auto;">
<tr>
<td class="style52" valign="top">
<table style="width: 42%; height: 504px;">
<tr>
<td class="oferta_text">
CATEGORIES</td>
</tr>
<tr>
<td class="style55">
<asp:DataList ID="datalisttypes" runat="server"
CellPadding="2" CellSpacing="5"
Height="368px" RepeatColumns="3"
RepeatDirection="Horizontal">
<ItemTemplate>
<br />
<table style="border: thin solid #C0C0C0;
height: 197px; width: 119px;"><tr>
<td style="border: thin solid" class="style57"
valign="top">
<a href='addauction.aspx?typeid=<
%#Eval("i_autoid") %>'>
<asp:Image ID="Image1" runat="server"
BorderColor="#33CC33" Height="143px"
ImageUrl="<%#
getSRC(Container.DataItem) %>" Width="123px" />
</a>
</td></tr>
<tr>
<td class="style56"
style="border: thin solid #C0C0C0;
background-image: url('images/typename_bg.gif'); background-repeat: norepeat;">
<a
href='addauction.aspx?typeid=<%#Eval("i_autoid") %>'
192
ONLINE AUCTION 084991223
style="background-image:
url('images/menu_title_bg.gif'); background-repeat: no-repeat">
<asp:HyperLink ID="HyperLink1"
runat="server"
Text="<%#
itemtype(Container.DataItem) %>"></asp:HyperLink>
</a>
</td>
</tr>
</table>
</ItemTemplate>
</asp:DataList>
</td>
</tr>
</table>
</td>
<td class="oferta_text" valign="top">
Users Detail<br />
<uc1:UsersDetails ID="UsersDetails1" runat="server" />
</td>
</tr>
<tr>
<td class="style52">
</td>
<td class="style53">
</td>
</tr>
<tr>
<td class="style52">
</td>
<td class="style53">
</td>
</tr>
</table>
</td>
</tr>
</table>
</asp:Content>
193
ONLINE AUCTION 084991223
Feedback Form
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="FeedbackForm.aspx.cs"
Inherits="FeedbackForm" %>
<%@ Register src="Sidemenus.ascx" tagname="Sidemenus" tagprefix="uc1" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
width: 175px;
}
.style2
{
width: 181px;
}
.style4
{
width: 723px;
height: 29px;
}
.style5
194
ONLINE AUCTION 084991223
{
width: 161px;
height: 29px;
}
.style6
{
width: 723px;
height: 11px;
}
.style7
{
width: 161px;
height: 11px;
}
.style8
{
width: 723px;
height: 14px;
}
.style9
{
width: 161px;
height: 14px;
}
.style10
{
195
ONLINE AUCTION 084991223
width: 723px;
height: 13px;
}
.style11
{
width: 161px;
height: 13px;
}
.style12
{
width: 723px;
height: 128px;
}
.style13
{
width: 161px;
height: 128px;
}
.style14
{
width: 723px;
height: 2px;
}
.style15
{
width: 161px;
196
ONLINE AUCTION 084991223
height: 2px;
}
.style17
{
width: 723px;
height: 202px;
}
.style16
{
width: 161px;
height: 59px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:100%;">
<tr>
<td class="style1" valign="top">
<uc1:Sidemenus ID="Sidemenus1" runat="server" />
</td>
<td rowspan="3" valign="top">
<table style="width:100%;">
<tr>
<td class="style2">
Send Us Your Feedback</td>
197
ONLINE AUCTION 084991223
<td>
</td>
</tr>
<tr>
<td class="style2">
<table style="width: 475px; height: 367px;">
<tr>
<td class="style4">
</td>
<td class="style5">
</td>
</tr>
<tr>
<td class="style6">
Name</td>
<td class="style7">
<asp:TextBox ID="txtName" runat="server"
Width="203px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style8">
Email id</td>
<td class="style9">
<asp:TextBox ID="txtEmailid" runat="server"
Width="203px"></asp:TextBox>
198
ONLINE AUCTION 084991223
</td>
</tr>
<tr>
<td class="style10">
Subject</td>
<td class="style11">
<asp:TextBox ID="txtsubject" runat="server"
Width="203px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style12" valign="top">
Your Feedback</td>
<td class="style13">
<asp:TextBox ID="txtDescription" runat="server"
Height="150px"
TextMode="MultiLine"
Width="303px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style14">
<asp:Label ID="lblMessage"
runat="server"></asp:Label>
</td>
<td class="style15">
199
ONLINE AUCTION 084991223
<asp:Button ID="btnSubmit" runat="server"
onclick="btnSubmit_Click"
Text="Submit" />
</td>
</tr>
<tr>
<td class="style17">
</td>
<td class="style16">
</td>
</tr>
</table>
</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
</td>
<td>
</td>
</tr>
</table>
</td>
</tr>
<tr>
200
ONLINE AUCTION 084991223
<td class="style1">
</td>
</tr>
<tr>
<td class="style1">
</td>
</tr>
</tab
201
ONLINE AUCTION 084991223
Contact Us
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="ContactUs.aspx.cs" Inherits="ContactUs"
%>
<%@ Register src="Sidemenus.ascx" tagname="Sidemenus" tagprefix="uc1" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
width: 175px;
}
.style2
{
width: 181px;
}
.style4
{
width: 723px;
height: 29px;
}
.style5
{
width: 161px;
height: 29px;
}
.style6
{
width: 723px;
height: 11px;
}
.style7
{
width: 161px;
height: 11px;
}
.style8
202
ONLINE AUCTION 084991223
{
width: 723px;
height: 14px;
}
.style9
{
width: 161px;
height: 14px;
}
.style10
{
width: 723px;
height: 13px;
}
.style11
{
width: 161px;
height: 13px;
}
.style12
{
width: 723px;
height: 128px;
}
.style13
{
width: 161px;
height: 128px;
}
.style14
{
width: 723px;
height: 2px;
}
.style15
{
width: 161px;
height: 2px;
}
203
ONLINE AUCTION 084991223
.style17
{
width: 723px;
height: 202px;
}
.style16
{
width: 161px;
height: 59px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:100%;">
<tr>
<td class="style1" valign="top">
<uc1:Sidemenus ID="Sidemenus1" runat="server" />
</td>
<td rowspan="3" valign="top">
<table style="width:100%;">
<tr>
<td class="style2">
Contact US</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
<table style="width: 475px; height: 367px;">
<tr>
<td class="style4">
</td>
<td class="style5">
</td>
</tr>
<tr>
<td class="style6">
Name</td>
204
ONLINE AUCTION 084991223
<td class="style7">
<asp:TextBox ID="txtName" runat="server"
Width="203px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style8">
Email id</td>
<td class="style9">
<asp:TextBox ID="txtEmailid" runat="server"
Width="203px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style10">
Mobile No</td>
<td class="style11">
<asp:TextBox ID="txtMobileno" runat="server"
Width="203px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style12" valign="top">
Description</td>
<td class="style13">
<asp:TextBox ID="txtDescription" runat="server"
Height="150px"
TextMode="MultiLine"
Width="303px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="style14">
<asp:Label ID="lblMessage"
runat="server"></asp:Label>
</td>
<td class="style15">
<asp:Button ID="btnSubmit" runat="server"
onclick="btnSubmit_Click"
205
ONLINE AUCTION 084991223
Text="Submit" />
</td>
</tr>
<tr>
<td class="style17">
</td>
<td class="style16">
</td>
</tr>
</table>
</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
</td>
<td>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td class="style1">
</td>
</tr>
<tr>
<td class="style1">
</td>
</tr>
</table>
</asp:Content>
206
ONLINE AUCTION 084991223
Add Auction Details
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="AddAuctionDetails.aspx.cs"
Inherits="AddAuctionDetails" %>
<%@ Register Assembly="AjaxControlToolkit"
Namespace="AjaxControlToolkit" TagPrefix="asp" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
}
.style2
{
width: 126px;
height: 23px;
}
.style3
{
height: 23px;
}
.style4
{
width: 121px;
207
ONLINE AUCTION 084991223
}
.style5
{
width: 121px;
height: 23px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width: 98%; height: 274px;">
<tr>
<td class="center_title_bar" colspan="3">
Add Details</td>
</tr>
<tr>
<td class="cart_title">
</td>
<td class="style4">
</td>
<td rowspan="4">
<asp:ScriptManager ID="ScriptManager1" runat="server">
</asp:ScriptManager>
<asp:CalendarExtender ID="exeffectedfrom" runat="server"
TargetControlID="txteffectfrom">
</asp:CalendarExtender>
208
ONLINE AUCTION 084991223
<asp:CalendarExtender ID="exeffectedto" runat="server"
TargetControlID="txteffectto">
</asp:CalendarExtender>
</td>
</tr>
<tr>
<td class="cart_title">
Effect From</td>
<td class="style4">
<asp:TextBox ID="txteffectfrom" runat="server" Height="22px"
Width="173px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="cart_title">
Effect To</td>
<td class="style5">
<asp:TextBox ID="txteffectto" runat="server" Height="22px"
Width="173px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="cart_title">
Starting Price</td>
<td class="style4">
209
ONLINE AUCTION 084991223
<asp:TextBox ID="txtStartingprice" runat="server" Height="22px"
Width="173px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="cart_title" valign="top">
Description</td>
<td class="style4">
<asp:TextBox ID="txtDescription" runat="server" Height="126px"
TextMode="MultiLine" Width="322px"></asp:TextBox>
</td>
</tr>
<tr>
<td class="cart_title">
<asp:Label ID="lblmessage" runat="server"></asp:Label>
</td>
<td class="style4">
<asp:Button ID="btnSubmit" runat="server" Height="26px"
onclick="btnSubmit_Click" Text="Submit" Width="80px" />
</td>
</tr>
</table>
</asp:Content>
210
ONLINE AUCTION 084991223
Admin Folder
Add Items
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="additems.aspx.cs"
Inherits="admin_additems" %>
<%@ Register src="AdminMenus.ascx" tagname="AdminMenus"
tagprefix="uc1" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
height: 22px;
}
.style2
{
width: 132px;
}
.style3
{
height: 22px;
width: 132px;
}
.style4
211
ONLINE AUCTION 084991223
{
width: 206px;
}
.style5
{
height: 22px;
width: 206px;
}
.style6
{
width: 132px;
height: 21px;
}
.style7
{
width: 206px;
height: 21px;
}
.style8
{
height: 21px;
}
.style9
{
width: 132px;
height: 18px;
212
ONLINE AUCTION 084991223
}
.style10
{
width: 206px;
height: 18px;
}
.style11
{
height: 18px;
}
.style12
{
width: 132px;
height: 26px;
}
.style13
{
width: 206px;
height: 26px;
}
.style14
{
height: 26px;
}
.style15
{
213
ONLINE AUCTION 084991223
width: 160px;
height: 283px;
}
.style16
{
height: 283px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:102%; height: 338px;">
<tr>
<td class="style15" valign="top">
<uc1:AdminMenus ID="AdminMenus1" runat="server" />
</td>
<td class="style16">
<table style="width:100%;">
<tr>
<td class="style2">
ADD ITEM TYPE</td>
<td class="style4">
</td>
<td>
</td>
</tr>
214
ONLINE AUCTION 084991223
<tr>
<td class="style3">
TYPE NAME</td>
<td class="style5">
<asp:TextBox ID="txttypename" runat="server" Height="21px"
Width="201px"></asp:TextBox>
</td>
<td class="style1">
</td>
</tr>
<tr>
<td class="style2">
TYPE IMAGE</td>
<td class="style4">
<asp:FileUpload ID="uploadtypeimage" runat="server" Height="21px"
/>
</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
<asp:Label ID="lblmsg0" runat="server"></asp:Label>
</td>
<td class="style4">
<asp:Button ID="btninsert" runat="server" Height="24px"
215
ONLINE AUCTION 084991223
onclick="btninsert_Click" Text="Insert" Width="81px" />
</td>
<td>
</td>
</tr>
<tr>
<td class="style9">
</td>
<td class="style10">
</td>
<td class="style11">
</td>
</tr>
<tr>
<td class="style2">
ADD ITEMS </td>
<td class="style4">
</td>
<td>
</td>
</tr>
<tr>
<td class="style12">
ITEM NAME</td>
<td class="style13">
216
ONLINE AUCTION 084991223
<asp:TextBox ID="txtitemname" runat="server" Height="21px"
Width="201px"></asp:TextBox>
</td>
<td class="style14">
</td>
</tr>
<tr>
<td class="style6">
ITEM TYPE</td>
<td class="style7">
<asp:DropDownList ID="ddltypes" runat="server" Height="21px"
Width="200px"
AutoPostBack="True">
</asp:DropDownList>
</td>
<td class="style8">
</td>
</tr>
<tr>
<td class="style2">
ITEM IMAGE</td>
<td class="style4">
<asp:FileUpload ID="uploaditemimage" runat="server" />
</td>
<td>
</td>
217
ONLINE AUCTION 084991223
</tr>
<tr>
<td class="style2">
<asp:Label ID="lblmsg" runat="server"></asp:Label>
</td>
<td class="style4">
<asp:Button ID="btnsubmit" runat="server" Height="25px"
Text="Submit"
onclick="btnsubmit_Click" />
</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
</td>
<td class="style4">
</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
</td>
<td class="style4">
</td>
218
ONLINE AUCTION 084991223
<td>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td colspan="2">
</td>
</tr>
</table>
</asp:Content>
219
ONLINE AUCTION 084991223
Admin Login
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="Adminlogin.aspx.cs"
Inherits="admin_Adminlogin" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style2
{
}
.style1
{
width: 121px;
}
.style3
{
width: 144px;
}
.style4
{
width: 258px;
}
.style5
{
font-size: large;
color: #66CCFF;
220
ONLINE AUCTION 084991223
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width: 100%;">
<tr>
<td class="style5" colspan="2">
<strong>Admin Login Page </strong>
</td>
<td>
</td>
</tr>
<tr>
<td class="style2">
</td>
<td class="style4">
</td>
<td>
<table style="width: 42%;">
<tr>
<td class="style1">
Username</td>
<td class="style3">
<asp:TextBox ID="txtUsername"
runat="server"></asp:TextBox>
221
ONLINE AUCTION 084991223
</td>
<td>
</td>
</tr>
<tr>
<td class="style1">
Password</td>
<td class="style3">
<asp:TextBox ID="txtPassword" runat="server"></asp:TextBox>
</td>
<td>
</td>
</tr>
<tr>
<td class="style1">
<asp:Label ID="lblmessage" runat="server"></asp:Label>
</td>
<td class="style3">
<asp:Button ID="BtnLogin" runat="server" Height="25px"
onclick="BtnLogin_Click"
Text="Login" Width="69px" />
</td>
<td>
</td>
</tr>
</table>
222
ONLINE AUCTION 084991223
</td>
</tr>
<tr>
<td class="style2">
</td>
<td class="style4">
</td>
<td>
</td>
</tr>
</table>
</asp:Content>
223
ONLINE AUCTION 084991223
Admin Menus
Admin Page
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="adminpage.aspx.cs" Inherits="adminpage"
%>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
width: 119px;
}
.style2
{
height: 99px;
}
.style3
{
font-size: xx-large;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
224
ONLINE AUCTION 084991223
<table style="width: 100%;">
<tr>
<td class="style1" rowspan="3" valign="top">
<asp:Menu ID="Menu1" runat="server" BackColor="#F7F6F3"
DynamicHorizontalOffset="2" Font-Names="Verdana" FontSize="Small"
ForeColor="Black" Height="166px" StaticSubMenuIndent="10px"
style="margin-right: 3px; margin-bottom: 4px" Width="151px">
<DynamicHoverStyle BackColor="#7C6F57" ForeColor="White" />
<DynamicMenuItemStyle HorizontalPadding="5px"
VerticalPadding="2px" />
<DynamicMenuStyle BackColor="#F7F6F3" />
<DynamicSelectedStyle BackColor="#5D7B9D" />
<Items>
<asp:MenuItem NavigateUrl="~/admin/additems.aspx" Text="Add
Items"
Value="Add Items"></asp:MenuItem>
<asp:MenuItem Text="Delete Items" Value="Delete
Items"></asp:MenuItem>
<asp:MenuItem Text="Update Items" Value="Update
Items"></asp:MenuItem>
<asp:MenuItem Text="Logout" Value="Logout"></asp:MenuItem>
</Items>
<StaticHoverStyle BackColor="Maroon" ForeColor="White" />
<StaticMenuItemStyle HorizontalPadding="5px" VerticalPadding="2px"
/>
225
ONLINE AUCTION 084991223
<StaticSelectedStyle BackColor="#5D7B9D" />
</asp:Menu>
</td>
<td class="style2"
style="background-image: url('images/view-admin-single.jpg');
background-repeat: no-repeat"
valign="top">
</td>
</tr>
<tr>
<td class="style3" valign="top">
<strong>Welcome Admin<br />
<br />
<br />
<br />
</strong></td>
</tr>
<tr>
<td>
</td>
</tr>
</table>
</asp:Content>
226
ONLINE AUCTION 084991223
Auction Details
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="AuctionDetails.aspx.cs"
Inherits="admin_AuctionDetails" %>
<%@ Register src="AdminMenus.ascx" tagname="AdminMenus"
tagprefix="uc1" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
width: 178px;
}
.style2
{
width: 630px;
}
.style57
{
width: 88px;
height: 89px;
}
.style58
{
227
ONLINE AUCTION 084991223
width: 88px;
height: 55px;
}
.style59
{
height: 117px;
width: 98px;
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:100%;">
<tr>
<td class="style1" valign="top">
<uc1:AdminMenus ID="AdminMenus1" runat="server" />
</td>
<td class="style2" valign="top">
<asp:GridView ID="gvauctions" runat="server" AutoGenerateColumns="False"
Height="937px"
Width="769px">
<Columns>
<asp:TemplateField>
<ItemTemplate>
<table class="style59" style="border: thin solid #C0C0C0; ">
228
ONLINE AUCTION 084991223
<tr>
<td class="style57" style="border: thin solid" valign="top">
<asp:Image ID="Image1" runat="server"
BorderColor="#33CC33" Height="90px"
ImageUrl="<%# getSRC(Container.DataItem) %>"
Width="85px" />
</a>
<br />
<asp:HyperLink ID="HyperLink1" runat="server"
Text="<%# itemtype(Container.DataItem)
%>"></asp:HyperLink>
</a>
</td>
</tr>
</table>
</ItemTemplate>
</asp:TemplateField>
<asp:BoundField DataField="Startingdate" HeaderText="Starting Date" />
<asp:BoundField DataField="endingdate" HeaderText="Ending Date" />
<asp:BoundField DataField="Userid" HeaderText="User id" />
</Columns>
</asp:GridView>
</td>
<td>
</td>
229
ONLINE AUCTION 084991223
</tr>
<tr>
<td class="style1">
</td>
<td class="style2">
</td>
<td>
</td>
</tr>
<tr>
<td class="style1">
</td>
<td class="style2">
</td>
<td>
</td>
</tr>
</table>
</asp:Content>
230
ONLINE AUCTION 084991223
Contact Details
<%@ Page Title="" Language="C#" MasterPageFile="~/MasterPage.master"
AutoEventWireup="true" CodeFile="Contactdetails.aspx.cs"
Inherits="admin_Enquirydetails" %><%@ Register src="AdminMenus.ascx"
tagname="AdminMenus" tagprefix="uc1" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
<style type="text/css">
.style1
{
}
</style>
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<table style="width:100%;">
<tr>
<td class="style1" colspan="3">
</td>
</tr>
<tr>
<td class="style1" valign="top">
<uc1:AdminMenus ID="AdminMenus1" runat="server" />
</td>
<td colspan="2">
<asp:GridView ID="gvenquiry" runat="server" AllowPaging="True"
231
ONLINE AUCTION 084991223
AutoGenerateColumns="False" BackColor="White"
BorderColor="#CCCCCC"
BorderStyle="None" BorderWidth="1px" CaptionAlign="Top"
CellPadding="3"
Height="87px" PageSize="8"
style="margin-right: 0px; margin-top: 2px; margin-left: 0px;"
Width="768px">
<Columns>
<asp:BoundField DataField="i_autoid" HeaderText="Id" />
<asp:HyperLinkField DataTextField="Name" HeaderText="Name"
/>
<asp:BoundField DataField="Email" HeaderText="Email id" />
<asp:BoundField DataField="Mobileno" HeaderText="Mobile no"
/>
<asp:BoundField DataField="msg" HeaderText="Description" />
<asp:BoundField DataField="Createdate" HeaderText="Date And
Time" />
</Columns>
<EmptyDataTemplate>
</EmptyDataTemplate>
<FooterStyle BackColor="White" ForeColor="#000066" />
<HeaderStyle BackColor="#006699" Font-Bold="True"
ForeColor="White" />
<PagerStyle BackColor="White" ForeColor="#000066"
HorizontalAlign="Left" />
<RowStyle ForeColor="#000066" />
232
ONLINE AUCTION 084991223
<SelectedRowStyle BackColor="#669999" Font-Bold="True"
ForeColor="White" />
<SortedAscendingCellStyle BackColor="#F1F1F1" />
<SortedAscendingHeaderStyle BackColor="#007DBB" />
<SortedDescendingCellStyle BackColor="#CAC9C9" />
<SortedDescendingHeaderStyle BackColor="#00547E" />
</asp:GridView>
</td>
</tr>
<tr>
<td class="style1">
</td>
<td>
</td>
<td>
</td>
</tr>
233
ONLINE AUCTION 084991223
ERROR HANDLING
An Exception occurs when a program encounter any unexpected
problems. Such as running out of memory or attempting to read from a
file that no longer exists. These problems are not necessarily caused by a
programming error but they mainly occur be cause of violation of
assumption that you might have made about the execution environment.
When a program encounters an exception the default behavior is to
throw the exception which generally translates to abruptly, terminating
the program after displaying an error message. But this is not a
characteristic of a robust application.
But the best way is to bindle the exception situations if possible,
gracefully recover from them. This is called exception handling.
I used try, catch, finally and throw in my project to handle the exception.
The Try Block:
Place the code that might cause exception in a try block. A typical try
block looks like this
Try
{
//Code that may cause exception
}
234
ONLINE AUCTION 084991223
A try block can have another try block inside when an exception occurs
at any point rather than executing any further lines of code, the CLR
(Common Language Runtime)
Secures for the nearest try block that enclosure this code. This code. The
control is then passed to a matching catch block if any and then to the
kindly block associated with this try block.
Catch Block:
There can be no of catch blocks immediately following a try block. Each
catch block handles an exception of a particular type. When an exception
occurs in a statement placed inside the try block the CLR looks for a
mainly block that is capable of handling the type of exception.
Throw block:
A throw statement explicitly generates an exception in code. You can
throw when a particular path in code results in an anomalous situation.
Finally Block:The finally block contains the code that always executes
whenever or not any exception occurs.
235
ONLINE AUCTION 084991223
PARAMETER PASSING
Passing parameters from one page to another is a very common task in
Web development. There are still many situations in which you need to
pass data from one Web page to another. One of the simplest and most
efficient ways of passing parameters among pages is to use the
querystring. Unfortunately, packing data into the querystring via string
manipulations can quickly lead to cumbersome and often difficult to
maintain code, especially as the parameter list grows. To overcome this
problem, Ive used Session in my project. Session has no. of advantages
over the
QueryString some of them are described below
Query String is client side. But Session is server side.
The information or data stored in Query String is visible to every
one. But in Session it is hidden and cant be viewed easily.
Query String can store only a piece of information but in Session
we can store the more and more data.The Query String speed never
falls as the load increase because it stores a piece of information.
But on the other hand Session increase congestion as the loads
increase.
236
ONLINE AUCTION 084991223
237
ONLINE AUCTION 084991223
Validation Checks
(1) Date Validation: The validation on date data type has been
specified to
be of
the format DD/MM/YY. Any other format is
unacceptable.
(2) Time validation: The validation on time data type has been
specified to be of
the format hours-minutes-seconds. Any other
format is unacceptable.
(5) Number field validation: The field specified with number as then
their data- type will not accept character.
(6) User Authentication: When a Customer/user logs on to the
system to access data from tables and database, the Id & password
needs to be checked.
(7) Password change Validation: Only authorized users are allowed
to change the
password and the process requires asking the old
password before changing it to the new one.
238
ONLINE AUCTION 084991223
TESTING
Test Case Execution
The workflow diagram below depicts the high level steps necessary to follow in
order to set up and execute test based on the Test Case Template.
Legend
1 - BII WG4 Test Case Template.doc. The Test Case template used to define and
set up the Test Case Description.
2 The test object specification provides a reference to the object subject to test
or if required, enter a copy of the object description excerpted from the object
description for the test object. When referenced, the reference should include at
least :
239
ONLINE AUCTION 084991223
SYSTEM TESTING:
System testing is the expensive and time-consuming process. There
are two strategies for testing software that we use for testing our system:
Code Testing and Specification Testing. In Code testing, we developed
those cases to execute every instructions and path in the program. In
specification testing, we examined the program specification and then
wrote test data to determine how the program operates under specified
condition..
Client
Acceptance
Needs
Testing
Requirements
System
Testing
Design
Integration
Testing
Code
Unit
240
ONLINE AUCTION 084991223
Testing
We have tested each module separately i.e. have completed
unit testing first and system testing was done after combining /linking
all different Modules with different menus and thorough testing was
done. Testing is a very important part of SDLC and takes
approximately 50%of the time.
Once the system is a live one, Maintenance phase is important.
Service after sale is a must and users/ clients must be helped after
the system is implemented. If he/she faces any problem in using the
system, one or two trained persons from developers side can be
deputed at the clients site, so as to avoid any problem and if any
problem occurs immediate solution may be provided.
OVERVIEW OF TESTING:
Testing: Testing involves executing the program (or part of it) using
sample data and inferring from the output whether the software
performs correctly or not. This can be done either during module
development (unit testing) or when several modules are combined
(system testing).
Defect Testing:
Defect testing is testing for situation where the
program does not meet its fictional specification. Performance testing
tests a system's performance or reliability under realistic loads. This
241
ONLINE AUCTION 084991223
may go some way to ensuring that the program meets its nonfunctional requirements.
Debugging: Debugging is a cycle of detection, location, repair and
test. Debugging is a hypothesis testing process. When a bug is
detected, the tester must form a hypothesis about the cause and
location of the bug. Further examination of the execution of the
program (possible including many returns of it) will usually take place
to confirm the hypothesis. If the hypothesis is demonstrated to be
incorrect, a new hypothesis must be formed. Debugging
tools that show the state of the program are useful for this, but
inserting print statements is often the only approach. Experienced
debuggers use their knowledge of common and/or obscure bugs to
facilitate the hypothesis testing process. After fixing a bug, the system
must be reset to ensure that the fix has worked and that no other
bugs have been introduced. This is called regression testing. In
principle, all tests should be performed again but this is often too
expensive to do.
TEST PLANNING:
Testing needs to be planned to be cost and time effective. Planning is
setting out standards for tests. Test plans set out the context in which
individual engineers can place their own work. Typical test plan
contains:
242
ONLINE AUCTION 084991223
Overview of testing process
>Requirements trace ability (to ensure that all requirements are tested)
>List of item to be tested
>Schedule
>Recording procedures so that test results can be audited
>Hardware and software requirement
243
ONLINE AUCTION 084991223
OVERVIEW OF TESTING STRATEGIES:
Large system usually tested using a mixture of strategies. Different
strategies may be needed for different parts of the system or at a
stage of the process.
Top-down testing:
This approach tests high levels of system before detailed components.
This is an appropriate when developing the system top-down likely to
show up structural design errors early (and therefore cheaply) has
advantage that a limited, working system available early on.
Validation
(as
distinct
from
verification)
can
begin
early.
Its
disadvantage is that stubs needs to be generated (extra effort) and
might be impracticable if component is complex (e.g. converting an
array into a linked list; unrealistic to generate random list; therefore
end up implementing unit anyway). Test output may be difficult to
observe (needs creation of artificial environment). This is not
appropriate for OO systems (except within a class).
Bottom-up testing:
244
ONLINE AUCTION 084991223
This is opposite of top-down testing. This testing test low-level unit
then works up hierarchy. Its advantages and disadvantages of
bottom-up mirror those of top-down. In this testing there is need to
write test drivers for each unit. These are as reusable as the unit
itself. Combining top-down development with bottom-up testing
means that all parts of system must be implemented before testing
can begin, therefore does not accord with incremental approach
discussed above. Bottom-up testing less likely to reveal architectural
faults early on. However, bottom-up testing of critical low-level
components is almost always necessary. Appropriate for OO systems.
Stress testing:
Test system's ability to cope with a specified load (e.g. transactions
per second). Plan tests to increase load incrementally. Go beyond
design limit until system fails (this test particularly important for
distributed systems (check degradation as network exchange data).
Back-to-back testing:
245
ONLINE AUCTION 084991223
Comparison of test results from different versions of the system (e.g.
compare with prototype, previous version or different configuration).
Process - Run first system, saving test case results. Run second
system, also saving its results. Compare results files. Note that no
differences dont imply no bugs. Both systems may have made the
same mistake.
Defect testing: A successful defect test is a test that causes the system
to behave incorrectly. Defect testing is not intended to show that a
program meets its specification. If tests don't show up defects it may
mean that the tests are not exhaustive enough.
Exhaustive testing is not always practicable. Subset has to be defined
(this should be part of the test plan, not left to the individual
programmer). Possible methods:
Test capabilities rather than components (e.g. concentrate on tests for
data loss over ones for screen layout).
>Test old in preference to new (users less effected by failure of new
capabilities).
>Test typical cases rather than boundary ones (ensure normal operation
works properly).
246
ONLINE AUCTION 084991223
Three approaches to defect testing. Each is most appropriate to
different types of component. Studies show that black box testing is
more effective in discovering faults than white-box testing. However,
the rate of fault detection (faults detected per unit time) was similar
for each approach. Also showed that static code reviewing was more
effective and less expensive than defect testing.
Black-box (Functional) Testing:
247
ONLINE AUCTION 084991223
Testing against specification of system or component. Study it by
examining its inputs and related outputs. Key is to devise inputs that
have a higher likelihood of causing outputs that reveal the presence
of defects. Use experience and knowledge of domain to identify such
test cases. Failing this a systematic approach may be necessary.
Equivalence partitioning is where the input to a program falls into a
number of classes. E.g. positive numbers vs. negative numbers.
Programs normally behave the same way for each member of a class.
Partitions exist for both input and output. Partitions may be discrete
or overlap. Invalid data (i.e. outside the normal partitions) is one or
more partitions that should be tested. Test cases are chosen to
exercise each portion. Also test boundary cases (atypical, extreme,
zero) since these frequently show up defects. For completeness, test
all combinations of partitions. Black box testing is rarely exhaustive
(because one doesn't test every value in an equivalence partition) and
sometimes fails to reveal corruption defects caused by "weird"
combination of inputs. Black box testing should not be used to try
and reveal corruption defects caused, for example, by assigning a
248
ONLINE AUCTION 084991223
pointer to point to an object of the wrong type. Static inspection (or
using a better programming language!) is preferable for this.
White-box (structural) Testing:
Testing based on knowledge of structure of component (e.g. by looking
at source code). Advantage is that structure of code can be used to
find out how many test case need to be performed. Knowledge of the
algorithm (examination of the code) can be used to identify the
equivalence partitions. Path testing is where the tester aims to
exercise every independent execution path through the component.
All conditional statements tested for both true and false cases. If a
unit has n control statements, there will be up to 2n possible paths
through it. This demonstrates that it is much easier to test small
program units than large ones. Flow graphs are a pictorial
representation of the paths of control through a program (ignoring
assignments, procedure calls and I/O statements). Use flow graph to
design test cases that execute each path. Static tools may be used to
make this easier in programs that have a complex branching
structure. Tools support. Dynamic program analyzers instrument a
program with additional code. Typically this will count how many
times each statement is executed. At end, print out report showing
which statements have and have not been executed. Problems with
flow graph derived testing:
249
ONLINE AUCTION 084991223
> Data complexity not taken into account.
> Does not test all paths in combination.
> Really only possible at unit and module testing stages because beyond
that complexity is too high.
Interface testing:
Usually done at integration stage when modules or sub-systems are
combined. Objective is to detect errors or invalid assumptions about
interfaces between modules. Reason these are not shown up in unit
testing is that test case may perpetuate same incorrect assumption
made
by
module
designer.
Particularly
important
when
OO
development has been used. Four types of interface:
1. Parameter: data (or occasionally function references) passed from one
unit to another.
2. Shared memory: block of memory shared between units (e.g. global
variable) .One places data there and the other retrieves it.
3. Procedural: object-oriented or abstract data type form of interface,
encapsulating several procedures.
4. Message passing: one sub-system requests a service by passing a
message. Client-server interface also used by some OO architectures.
Three common kinds of interface error:
250
ONLINE AUCTION 084991223
> Interface misuse: caller gives wrong number/types/order of parameters
or sends invalid message.
> Interface misunderstanding: caller misunderstanding specification of
called component and provides or receives data in legal but unexpected
form.
> Timing errors: producer/consumer of data operate at different speeds
and data is accessed before being ready. "Race conditions".
Common manifestations are when each unit assumes the other one is
checking for invalid data (failure to check return status) and the
consequences of when such a fault is propagated to other units.
TESTING PROCESS
Best testing process is to test each subsystem separately, as we have
done in my project. Best done during implementation. Best done after
small sub-steps of the implementation rather than large chunks.
Once each lowest level unit has been tested, units are combined with
related
units
and
retested
in
combination.
This
proceeds
hierarchically bottom-up until the entire system is tested as a whole.
Typical levels of testing:
> Unit -procedure, function, method
> Module -package, abstract data type, class
251
ONLINE AUCTION 084991223
Sub-system - collection of related modules, cluster of classes, methodmessage paths> Acceptance testing - whole system with real data (involve
customer, user, etc)
Alpha testing is acceptance testing with a single client (common for
bespoke systems).
Beta testing involves distributing system to potential customers to use
and provide feedback. In, this project, Beta testing has been followed.
This exposes system to situations and errors that might not be
anticipated by us.
252
ONLINE AUCTION 084991223
Debugging And Code Improvement
In ideal worlds, all programmers would be so skilled and attentive to
detail that they would write bug-free code. Unfortunately, we do not live
in an ideal world. As such, debugging, or tracking down the source of
errors and erroneous result, is an important task that all developers
need to perform before they allow end-user to use their applications. We
will discuss some techniques for reducing the number of bugs in code up
front.
There are three categories of bugs
Syntax error:
These errors occur when code breaks the rule of the language, such as
visual Basic sub statement without a closing End sub, or a forgotten
closing curly braces ({}) in c#. Theses error the easiest to locate. The
language complier
or integrated development environment (IDE) will
alert you to them and will not allow you to compile your program until
you correct them.
Semantic error
These errors occur in code that is correct according to rules of the
compiler, but that causes unexpected problems such as crashes or
hanging on execution. A good example is code that execute in a loop but
never exists the loop, either because the loop depends on the variable
whose values was expected to be something different than it actually was
253
ONLINE AUCTION 084991223
or because the programmer forget to increment the loop counter. Another
category of errors in this area includes requesting a field from a dataset,
there is no way to tell if the field actually exists at compile time. these
bugs are harder to detect and are one type of running error.
Logic error
Logic errors are like semantic errors, logic errors are runtime error. That
is, they occur while the program is running. But unlike semantic errors,
logic errors do not cause the application to crash or hang. Logic error
results in unexpected values or output. This can be a result of something
as simple as a mistyped variables name that happens to match another
declared variable in the program. This type of error can be extremely
difficult to track down to eliminate.
Preventing Debug Write readable code
Develop and make consistent use of naming and coding standards. It not
that important which standard we use, such as Hungarian notation or
Pascal, Casing (First Name) or other naming conventions, as long as we
use one. We should also strive for consistency in our comments and
encourage liberal commenting code.
Create effective test plan
The only effective way to eliminate logic error is to test very path of your
application with every possible data values that a user could enter. This
is difficult to manage without effective planning. We should create our
254
ONLINE AUCTION 084991223
test plan at the same time we are designing the application, and we
should update these plans as you modify the application design
Code Improvement
We make the Class Datacontext in our project which is useful for
reducing the code redundancy and make code consistency. Datacontext
function improves the code, when by using the Class Datacontext we
can create a connection with database, open the database, close the
database, dispose the database, Through the Datacontext Class can
access the datatable. In our project we can create the object of the
Datacontext then after creating the object we do not need to write the
functions, such as database connectivity, open connection, close
connection, dispose connection, get data table connection. Datacontext
Class make the code improvement in our project. Through the
Datacontext function we can insert, delete, update the records and
show the datatables and check the database so can say that the
Datacontext function is more useful and make code improve.
255
ONLINE AUCTION 084991223
Input Output Reports
Registration Input
256
ONLINE AUCTION 084991223
Output Registration
257
ONLINE AUCTION 084991223
Input Login
258
ONLINE AUCTION 084991223
Output Login
259
ONLINE AUCTION 084991223
Contact Input
260
ONLINE AUCTION 084991223
Contact Output
261
ONLINE AUCTION 084991223
Feedback Input
262
ONLINE AUCTION 084991223
Feedback Output
263
ONLINE AUCTION 084991223
Admin login
264
ONLINE AUCTION 084991223
Output After Login
265
ONLINE AUCTION 084991223
Add Type Input
266
ONLINE AUCTION 084991223
Add Type Output
267
ONLINE AUCTION 084991223
Password Recovery Input
268
ONLINE AUCTION 084991223
Password Recovery Output
269
ONLINE AUCTION 084991223
LIMITATION OF PROJECT
Only registered users can do a auction in the websites and registered users can
place bid on website.
User can only do auction on given categories.
User cant bid lower then last bid.
Users can not create his own series of categories.
270
ONLINE AUCTION 084991223
FUTURE SCOPE OF THE PROJECT
This Portal give Option to User to sell and purchase of a product on line On
different Auction. At this time every person have shortage of time so User can sell
and purchase the product at online. This project can have so many option to selling
and purchasing . in future people will buy and sell by auction through this website.
Users can perform their auction and can sell theirs properties on this website.
271
ONLINE AUCTION 084991223
Biblography
1. An
Integrated
Approach
to
Software
Engineering:
PANKAJ JALOTE
2. Professional Active Server Pages 4.0: Appress
3. HTML: Sams Teach Your Self: Dick Oliver
4. SQL Server 2008; Database Design Study Guide: Kevin
Hough
5. Structured Analysis and Design (CS-05) of IGNOU
6. http://webdev.wrox.co.uk
272
Вам также может понравиться
- Installation of Ubuntu 14Документ111 страницInstallation of Ubuntu 14Maneesh Bradiyil100% (1)
- Online Manager: Bachelor of Computer ApplicationДокумент108 страницOnline Manager: Bachelor of Computer ApplicationManeesh BradiyilОценок пока нет
- RAHUL BiodataДокумент2 страницыRAHUL BiodataManeesh BradiyilОценок пока нет
- VC++ BookДокумент92 страницыVC++ BookManeesh BradiyilОценок пока нет
- Uid Model QuestionsДокумент3 страницыUid Model QuestionsManeesh BradiyilОценок пока нет
- SNGCEДокумент6 страницSNGCEManeesh BradiyilОценок пока нет
- Warehouse Management System (WMS)Документ4 страницыWarehouse Management System (WMS)Maneesh BradiyilОценок пока нет
- Building Cost EstimatorДокумент118 страницBuilding Cost EstimatorManeesh BradiyilОценок пока нет
- Classifying Malware Attacks in IaaS Cloud Environments - VVДокумент47 страницClassifying Malware Attacks in IaaS Cloud Environments - VVManeesh BradiyilОценок пока нет
- Extraa TopicsДокумент1 страницаExtraa TopicsManeesh BradiyilОценок пока нет
- Summary Description For Class1Документ3 страницыSummary Description For Class1Maneesh BradiyilОценок пока нет
- Curriculum For Master of Computer Applications (MCA) 2016: Apj Abdul Kalam Technological UniversityДокумент13 страницCurriculum For Master of Computer Applications (MCA) 2016: Apj Abdul Kalam Technological UniversityManeesh BradiyilОценок пока нет
- It6503 Web Programming SyllabusДокумент2 страницыIt6503 Web Programming SyllabusManeesh BradiyilОценок пока нет
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Q4-PPT-Music10 - Lesson 2 (Philippine Ballet)Документ35 страницQ4-PPT-Music10 - Lesson 2 (Philippine Ballet)Anji Gatmaitan100% (1)
- Standard Grammar Unit7 With AnswersДокумент1 страницаStandard Grammar Unit7 With AnswersJogi NeroОценок пока нет
- Duane Broe Capstone ProjectДокумент58 страницDuane Broe Capstone ProjectSelvi WulandariОценок пока нет
- Skills 30-36 VerbsДокумент16 страницSkills 30-36 Verbsapi-298565229Оценок пока нет
- Word-Order-In-English - Vi2 PDFДокумент6 страницWord-Order-In-English - Vi2 PDFwahyu chandra wijayaОценок пока нет
- Data Visualization Cheatsheet 1702209209Документ7 страницData Visualization Cheatsheet 1702209209valdezrominapyОценок пока нет
- 5 Reasons The Catholic Church Is The True ChurchДокумент31 страница5 Reasons The Catholic Church Is The True ChurchJj ArabitОценок пока нет
- Fce Writing Part 2 Short Stories ActivityДокумент7 страницFce Writing Part 2 Short Stories Activityhenniebennie0% (1)
- Offensive Security Evasion Techniques Pt.1Документ42 страницыOffensive Security Evasion Techniques Pt.1Felipe RodriguesОценок пока нет
- DDI0183G Uart Pl011 r1p5 TRMДокумент96 страницDDI0183G Uart Pl011 r1p5 TRMh2135741Оценок пока нет
- Chapt 2Документ213 страницChapt 2pawОценок пока нет
- HabilitationДокумент186 страницHabilitationAland MediaОценок пока нет
- Lesson Plan My FamilyДокумент4 страницыLesson Plan My FamilyKiara NavarroОценок пока нет
- 3.1 Basics of Hardware Design and Functions of Basic Passive ComponentsДокумент31 страница3.1 Basics of Hardware Design and Functions of Basic Passive ComponentsDr. M. Thillai Rani Asst Prof ECEОценок пока нет
- Software Development Engineer in TestДокумент5 страницSoftware Development Engineer in TestBharath MathivananОценок пока нет
- A. Grammar - Relative Clauses: Unit 8 - New Ways To LearnДокумент3 страницыA. Grammar - Relative Clauses: Unit 8 - New Ways To LearnDo YoungОценок пока нет
- Starvert: Compact & Powerful DriveДокумент44 страницыStarvert: Compact & Powerful DriveSamir AtabОценок пока нет
- Chapter One - Hashing PDFДокумент30 страницChapter One - Hashing PDFMebratu AsratОценок пока нет
- Module 1-Activity-Sheet-21st-C-LitДокумент3 страницыModule 1-Activity-Sheet-21st-C-LitAMYTHEEZ CAMOMOTОценок пока нет
- Python Module 4Документ115 страницPython Module 4SANAL KUMARОценок пока нет
- Most Common Types of INVERSION, FRONTING and EMPHASIS in "Alapvizsga"Документ1 страницаMost Common Types of INVERSION, FRONTING and EMPHASIS in "Alapvizsga"Vivien SápiОценок пока нет
- Sun Grid Engine UpdateДокумент55 страницSun Grid Engine UpdateYasser AbdellaОценок пока нет
- Clauses of Contrast and Purpose Whatever, Whenever, Etc.Документ5 страницClauses of Contrast and Purpose Whatever, Whenever, Etc.CARLOS VILLAMIZAR MONROYОценок пока нет
- Computer Science, 9618 Home Assignment (35 Marks)Документ5 страницComputer Science, 9618 Home Assignment (35 Marks)Saurya PandeyОценок пока нет
- Micro Controller Based Scientific CalculatorДокумент6 страницMicro Controller Based Scientific Calculators_aishwarya0% (1)
- CSA Unit 6 TemperatureAction FRQДокумент7 страницCSA Unit 6 TemperatureAction FRQKalpita AcharyaОценок пока нет
- Is 399 1963Документ91 страницаIs 399 1963Anonymous 8Ps6oyzwEОценок пока нет
- Eaton Fire Addressable Panel cf1100 Datasheet v1.1 0619Документ2 страницыEaton Fire Addressable Panel cf1100 Datasheet v1.1 0619DennisОценок пока нет
- John Caputo - The Return of Anti-Religion: From Radical Atheism To Radical TheologyДокумент93 страницыJohn Caputo - The Return of Anti-Religion: From Radical Atheism To Radical TheologyBlake Huggins100% (1)
- EvalExam2 Geometry SET AДокумент2 страницыEvalExam2 Geometry SET AEngr. HLDCОценок пока нет