Академический Документы
Профессиональный Документы
Культура Документы
Security Awareness
Загружено:
DigitaliasАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Security Awareness
Загружено:
DigitaliasАвторское право:
Доступные форматы
Seven steps to security awareness
by Dr Gary Hinson MBA CISSP
Last updated: January 2014
Executive summary
The paper describes these seven steps involved in preparing and launching an awareness program:
2 3 4 7
1 Prepare Secure 5 6
Clarify Shortlist Launch
Start requirements
plan & funds &
options
Evaluate Select
program Stop
checklist support
Introduction
Are you thinking about running a security awareness program but are not quite sure whats
involved? This paper outlines the seven key steps involved in specifying, designing and launching
an awareness program. We have done our level best to make this a generic vendor-neutral paper,
but its up to you to fit the process to your specific circumstances.
Step 1. Clarify and specify your requirements
The first and most important step is to think very carefully about exactly what you are trying to
achieve through security awareness. Until your objectives are clear, you will have problems
planning and organizing the awareness program, let alone evaluating and choosing the products
and services you may need.
Here are some rhetorical questions to ask yourself for a start:
Do you have an information security awareness program already running, or is this an entirely
new concept for the organization? If not information security, are there other awareness
programs running that might act as role models?
Does/should the program involve awareness, training and education, or only one of these?
What topics does/should the program cover? Are other aspects of information security
important to your organization?
How often does/should the program address individuals? Is that frequent enough to keep
information security on their agenda?
Does/should the program go into sufficient depth to provide useful advice and guidance where
appropriate, or it is only meant to give a superficial overview?
Does/should the program apply to all employees from their first to their last day at work?
Does/should it extend to third parties working in a similar capacity to employees e.g. consultants,
contractors and other associates working on site?
Copyright 2014 IsecT Ltd. Page 1 of 5
Seven steps to security awareness
Now set your imagination free. Picture yourself in the future. Imagine how things will be when your
awareness program is running smoothly. Consider:
1. Do you simply want to make people "aware" of information security in a very general sense, or
do you in fact want them to behave differently as a result of being aware? Awareness is
worthwhile in itself but is not the ultimate goal. Your program plan needs to aim beyond simply
raising awareness.
2. Who are you trying to reach with your awareness campaign? Do you have one homogenous
audience, or are there distinct groups with markedly different perspectives and needs? Does
your management, for instance, understand and support what you are doing in information
security? Are there particular teams (such as software development projects, IT Operations and
the IT Help Desk) with even more specific requirements? What about your contractors,
consultants, business partners and customers?
3. Are you looking for generalized across-the-board security awareness, or more in-depth training
on particular problem areas, or both? What kinds of things do you want to make people aware
of? Is this a fixed list of topics or a dynamic list that will change over the coming months and
years? Answering this question will tell you whether it is feasible to cover the whole planned
syllabus in one hit or whether you need to think long term to avoid information overload
4. which leads on to: do you plan to run the awareness campaign on an ongoing basis or are you
looking for a one-off fire-and-forget or similar short term initiative to address a specific issue?
Both approaches are valid in the right circumstances, sometimes a combination approach is
needed.
5. Does your organization have a strong security culture already, or are you constantly fighting to
get anyone to take security seriously? In other words, how mature is your organization in its
approach to information security? If security is already ingrained in the organization, its people
and its processes (like, for example, in most banks) you will have an easier time promoting
information security awareness than if its an entirely alien concept. Do you have a
comprehensive set of information security policies in place already, for instance, and are they
maintained up-to-date, or will your program need to develop these as well as promoting
them? Be realistic in your planning about the time and effort it will probably take to reach your
goal: remember, its better to under-promise and over-perform than vice versa!
6. Will the awareness program be funded and run as a business- or IT-led activity? Who will run it,
and what qualifications and experience do they have in (a) information security and (b) security
awareness, training and education, to equip them for the task? If you are in charge, could you
do with some additional training or consultancy assistance to get things off the ground? A little
bit of assistance in the planning and initiation stage can help avoid a lot of wasted effort and
aggravation later.
There are some excellent sources of advice on security awareness including NISTs Special
Publication 800-50, Rebecca Herolds handbook, and ENISAs guide. If the six issues above have got
you thinking, broaden your horizons and deepen your analysis by exploring other resources.
Step 2. Prepare a plan and checklist
Awareness programs do not run themselves, especially as many organizations start from a fairly
negative or cynical position. It will take concerted effort to overcome that inertia, get the
organization up to speed on information security, and then keep it rolling. In other words, you need
Copyright 2014 IsecT Ltd. Page 2 of 5
Seven steps to security awareness
to design the program, develop a plan to establish the program and then manage it effectively in
order to deliver the projected benefits.
If you have a lot of ground to cover (e.g. the whole of information security!), we would definitely
recommend planning to cover it in discrete sections or chunks spread out over time, and wherever
possible framing those chunks in terms that make sense to your target audiences. Take, for
example, the virus problem: anyone who uses an IT system should have a basic understanding of
viruses. In explaining about viruses, you may want to mention issues such as configuration
management, network/systems access and so on, but you need not go into depth on all of these at
the same time. Its perfectly acceptable to say We will tell you more about this later or even Visit
Information Securitys intranet site or Call the IT Help Desk for more information.
An ideal way of crystallizing your thoughts from step 1 above in parallel with developing your plan
is to prepare a product evaluation checklist containing rows for each of the criteria that are
important to you, and columns for the criteria and their weightings (e.g. 3 = essential, 2 = important,
1 = nice-to-have), and then further columns for comments and scores against each of the products
you are evaluating.
As you work through the checklist, you will in effect be defining and refining your requirements for
the program, making it easier to develop an associated plan. Thats why we treat these two activities
as one step.
Step 3. Secure funding and management support
Getting your senior management on board with the whole idea of an awareness program is, I
humbly suggest, by far the most important thing you can achieve in the next few months and will
pay big dividends in the long run. How you actually achieve this is down to you: we can only hint at
things that have worked for us and our clients.
Depending on the organization, you may or may not need to make a strong financial case for the
investment. Some senior managers respond better to gut feel than raw numbers. Our generic
business case paper may be a useful straw-man if you need to persuade your management to fund
and support the awareness program (by all means call us for the editable MS Word version of the
paper if that will save time). It includes some hints on financial modeling for risk reduction projects
like yours.
Work with your CISO, CIO or IT Director, for sure, and ideally other influential managers who have
an interest in seeing the awareness program succeed (friends in HR, Risk, Compliance and Facilities
will be extremely helpful, both now and later once the program is running). Time spent privately
and patiently explaining your plans to these stakeholders will help (a) refine your plan; (b) identify
any concerns; (c) deflect criticism and (d) line them up to support your program, especially during
this critical early phase.
By the way, its often worthwhile getting explicit management support for information security
during this process, meaning at least one strong quote from a senior manager which unequivocally
mandates compliance with the organizations information security policies and associated
requirements. You may need to draft the statement for the CEO in practice but her signature on
the bottom will add weight to your awareness program way beyond its apparent value. Believe me,
clout works!
During step 3, do not be afraid to continue refining your plan and requirements. All the time, you
are thinking about it and learning about the possibilities. Dont waste that brain energy!
Copyright 2014 IsecT Ltd. Page 3 of 5
Seven steps to security awareness
Step 4. Identify and shortlist possible options
Now you are in a good position to go looking for what you might need. Start by looking within your
own organization for suitable resources, for example in your IT, HR, Internal/Corporate
Communications and Training and Development functions. Take advice from colleagues running
other internal awareness, training and educational programs (such as Health and Safety or IT
training). Simply asking your colleagues for advice is worthwhile as it may help get their support for
delivering the program later on, whereas not asking them may inadvertently set their minds against
it.
When it comes to finding public free and commercial offerings, Google is your friend! Search for
terms such as security awareness, information security awareness, security awareness
posters and so forth. Check out the industry magazines and professional societies for help and
advice. Be wary of low quality materials, and dont mistake Published on the web for free: take
note of the copyright restrictions. Pretty soon, you will have amassed a list of interesting products
and services. Be systematic about the way you gather the information and you will make the
remaining steps easier.
Now go through your list of internal and external resources and home-in on those parts which you
think may suit your needs. By all means discard the others but be careful - it is easy to overlook
useful resources that are badly marketed, incompletely described or simply unfamiliar. If you have
the time and energy, it may be safer to shortlist most if not all potential suppliers at this stage and
trim the list later. There is no harm in contacting companies for initial information at this stage but
be wary of overt sales pitches: the next step in the process works best if you approach it objectively
on your terms, not theirs.
Step 5. Evaluate potential solutions
For commercial offerings, this is the conventional tendering stage:
Prepare a formal Request For Proposals containing your requirements derived from your
dreaming, planning and evaluation criteria (which you probably do not want to disclose);
Send the RFP to potential bidders (without identifying who is being invited to bid), along with a
deadline to respond;
Receive questions from some bidders, and respond quickly to all bidders without disclosing who
originated the questions;
When the deadline expires, reject any further bids/proposals and start systematically evaluating
and scoring them using the checklist written earlier (we suggest a percentage score against each
criterion, taking the weighting into account);
Focus on the essential requirements first - you may be able to exclude some bidders immediately
if they simply do not satisfy your essential needs;
Dont neglect any additional offers made by the bidders - sometimes, they will suggest useful,
valuable ideas you had overlooked, and they can help reach a final decision if the scores are close
between a number of offers;
Look at the quality of the bids/proposals as well as any sample awareness systems or materials
sent for evaluation - these are all valid indicators of the professionalism and quality of the
bidders;
Copyright 2014 IsecT Ltd. Page 4 of 5
Seven steps to security awareness
Do the math: final score for each bidder = (sum of (score for each criterion x weighting for that
criterion)) divided by maximum possible score x 100 percent.
Your Procurement people should be falling over themselves to help you with the tendering process,
especially if there are substantial sums of money involved. They will want to ensure that the process
is fair, objective and entirely above-board. This is their profession: take their advice!
For in-house and free offerings, the shortlisting, evaluation and assessment process is similar. It is
entirely possible that you may wish to take advantage of commercial and free awareness materials,
for example, and combine them with internal resources. Its your choice.
Step 6. Select and obtain your chosen solutions
The end result of step 5 may be a single winning bidder, or perhaps different ones covering separate
parts of your requirement. It is possible you are unable to decide between the last few bidders.
Step 6 generally involves a bit of negotiation with the suppliers, perhaps some clarification of the
price, the terms of the offer, and another hard look at what they offered. Finally you make the
decision, prepare the Purchase Order, sign the contract and move swiftly along. This is known as
doing the business.
Step 7. Implement and launch the awareness program
Let the fun commence! Whilst the previous 6 steps may perhaps have seemed a rather bureaucratic
and pointless diversion, you may well find the opposite in practice. Just as with a software
development project, time spent deciding the requirements, designing the solution and testing the
system pays off in the end with a smoother and more effective implementation.
You have a well-written plan and the necessary resources to deliver it. Now is the time to call on
the support of your colleagues and suppliers to build and deliver the awareness program of your
dreams.
Conclusion
In this paper, we have given a flavor of what is normally involved in launching a security awareness
program. Your mileage may well vary but we hope this helps turn a somewhat confusing process
into a straightforward set of steps. Good luck!
NoticeBored is IsecT Ltds innovative information security awareness subscription service. We
do the hard work for you, researching, preparing and polishing a fresh package of high quality
security awareness materials (seminar slides, briefings, newsletters, policies, checklists, FAQs,
glossaries, posters, mind-maps and diagrams, case studies, policies, crosswords, quizzes, tests,
screensavers, surveys etc.) covering a different information security topic every month. Browse
NoticeBored.com for more information. If you are really busy, the product data sheet sums it
up in just two sides.
Copyright 2014 IsecT Ltd. Page 5 of 5
Вам также может понравиться
- Security Awareness Programs A Complete Guide - 2019 EditionОт EverandSecurity Awareness Programs A Complete Guide - 2019 EditionОценок пока нет
- Cybersecurity ISMS Policies And Procedures A Complete Guide - 2020 EditionОт EverandCybersecurity ISMS Policies And Procedures A Complete Guide - 2020 EditionОценок пока нет
- Security Vulnerability Threat Assessments A Complete Guide - 2019 EditionОт EverandSecurity Vulnerability Threat Assessments A Complete Guide - 2019 EditionОценок пока нет
- Business Continuity Management And IT Disaster Recovery Management A Complete Guide - 2021 EditionОт EverandBusiness Continuity Management And IT Disaster Recovery Management A Complete Guide - 2021 EditionОценок пока нет
- Security PrinciplesДокумент10 страницSecurity PrinciplessecureuxОценок пока нет
- Industrial Security Operations Book Two: The Security Officers HandbookОт EverandIndustrial Security Operations Book Two: The Security Officers HandbookОценок пока нет
- Information Security Plan DraftДокумент12 страницInformation Security Plan DraftAxcelОценок пока нет
- Information Security Governance FrameworkДокумент2 страницыInformation Security Governance Frameworkth3.pil0tОценок пока нет
- Security Policy (Including The Prevention and Control of Violence & Aggression)Документ19 страницSecurity Policy (Including The Prevention and Control of Violence & Aggression)ahmed100% (1)
- Operational Risk Management System A Complete Guide - 2020 EditionОт EverandOperational Risk Management System A Complete Guide - 2020 EditionОценок пока нет
- Threat Intelligence Platform Complete Self-Assessment GuideОт EverandThreat Intelligence Platform Complete Self-Assessment GuideОценок пока нет
- Information Security and Privacy in Network Environments: September 1994Документ248 страницInformation Security and Privacy in Network Environments: September 1994Master fskmОценок пока нет
- RohitДокумент75 страницRohitRobin PalanОценок пока нет
- Dynamic Application Security Testing A Complete Guide - 2019 EditionОт EverandDynamic Application Security Testing A Complete Guide - 2019 EditionОценок пока нет
- Nformation Ecurity Olicy: HapterДокумент51 страницаNformation Ecurity Olicy: HapterBin FlanОценок пока нет
- Security And Risk Management Tools A Complete Guide - 2020 EditionОт EverandSecurity And Risk Management Tools A Complete Guide - 2020 EditionОценок пока нет
- Security Policy 02Документ3 страницыSecurity Policy 02prabir_kalna5601Оценок пока нет
- ISO27k Organization of Information SecurityДокумент5 страницISO27k Organization of Information Securityvishnukesarwani100% (1)
- Warisan Condo SSДокумент6 страницWarisan Condo SSjothi subra0% (1)
- Five Best Practices For Communicating Security Awareness Training ImpactДокумент11 страницFive Best Practices For Communicating Security Awareness Training ImpactManixhome MmОценок пока нет
- Perations Ecurity Olicy: Inspiring Business InnovationДокумент20 страницPerations Ecurity Olicy: Inspiring Business InnovationrontechtipsОценок пока нет
- Bussiness - Case - ISO27001 - 27002 Data Center On AMF and Internal Procedures and Policies!Документ3 страницыBussiness - Case - ISO27001 - 27002 Data Center On AMF and Internal Procedures and Policies!Denisa PriftiОценок пока нет
- Introduction To Operations Security (OPSEC) : 1 Security Is Everyone's Responsibility - See Something, Say Something!Документ16 страницIntroduction To Operations Security (OPSEC) : 1 Security Is Everyone's Responsibility - See Something, Say Something!Lawrence R. San Juan100% (2)
- The Ethical Issues Arising From The Relationship Between Police and MediaДокумент76 страницThe Ethical Issues Arising From The Relationship Between Police and Mediaj_townendОценок пока нет
- Cyber Security Policy TemplateДокумент3 страницыCyber Security Policy TemplateJacob YeboaОценок пока нет
- CSSP Manual v2014!3!1Документ144 страницыCSSP Manual v2014!3!1sanjuan_97100% (2)
- Security Awarness (Email Security and Phishing)Документ20 страницSecurity Awarness (Email Security and Phishing)MardiyahОценок пока нет
- Bizmanualz Business Security Policies and Procedures SampleДокумент6 страницBizmanualz Business Security Policies and Procedures SampleHasanОценок пока нет
- Patrol 2Документ21 страницаPatrol 2VioletОценок пока нет
- Division of Information Technology Policy 18.2aДокумент3 страницыDivision of Information Technology Policy 18.2aBara DanielОценок пока нет
- Physical and Environmental Security Policy: Nformation Ecurity OlicyДокумент9 страницPhysical and Environmental Security Policy: Nformation Ecurity Olicypenumudi233Оценок пока нет
- Security Incident Reporting and Management SopДокумент14 страницSecurity Incident Reporting and Management SopandrisurantiОценок пока нет
- Security Awareness Workshop: This Summary Paper Is Divided Into Five Sections, CoveringДокумент22 страницыSecurity Awareness Workshop: This Summary Paper Is Divided Into Five Sections, Coveringralph3horses7192Оценок пока нет
- Integrated Enterprise SecurityДокумент16 страницIntegrated Enterprise SecuritykflimОценок пока нет
- Unit 5 Assignment 2 Define An Acceptable Use PolicyДокумент2 страницыUnit 5 Assignment 2 Define An Acceptable Use PolicyLeeYoungОценок пока нет
- Physical SecurityДокумент17 страницPhysical Securitydirava7622Оценок пока нет
- Security Risk ManagementДокумент28 страницSecurity Risk ManagementKrishna ChaitanyaОценок пока нет
- Physical Security ChecklistДокумент7 страницPhysical Security ChecklistdexterОценок пока нет
- Workplace Security REVISEDДокумент12 страницWorkplace Security REVISEDJason ReacherОценок пока нет
- Incident ResponseДокумент63 страницыIncident ResponseANIRUDH B K 19BIT0348Оценок пока нет
- Basic Investigation ProceduresДокумент2 страницыBasic Investigation ProceduresAnthony Dela TorreОценок пока нет
- Campus Security - Brent International School DTD 03aug2014 HandoutsДокумент5 страницCampus Security - Brent International School DTD 03aug2014 HandoutsAlvinMatabang100% (2)
- Advancing Security Professionals PDFДокумент35 страницAdvancing Security Professionals PDFIrfan-e-IlahiОценок пока нет
- Information Security Roles & Responsibilities: PurposeДокумент5 страницInformation Security Roles & Responsibilities: PurposeLuis Fernando Quintero HenaoОценок пока нет
- Industrial and Security ManagementДокумент16 страницIndustrial and Security ManagementJose Li ToОценок пока нет
- For: From: Chief Security Officer SUBJECT: Investigation Report Re: Vandalism Date: 4 June 2017 CC: DM, FileДокумент3 страницыFor: From: Chief Security Officer SUBJECT: Investigation Report Re: Vandalism Date: 4 June 2017 CC: DM, FileRJay JacabanОценок пока нет
- Types of Security ControlsДокумент17 страницTypes of Security ControlsManish MaharjanОценок пока нет
- Baseline Security Controls PolicyДокумент5 страницBaseline Security Controls PolicyClyde Ben BaleteОценок пока нет
- UNIT IV: Lesson 4 - Document & Information Security (Week 14-18)Документ27 страницUNIT IV: Lesson 4 - Document & Information Security (Week 14-18)Judy LawaanОценок пока нет
- USArmy PsyOpsTacticsДокумент250 страницUSArmy PsyOpsTacticsKika Spacey Ratm100% (1)
- Student Perceptions of Teaching EvaluationsДокумент6 страницStudent Perceptions of Teaching EvaluationsPamela Francisca Bobadilla BurgosОценок пока нет
- Bangladesh National Jobs Strategy NJS Final DraftДокумент159 страницBangladesh National Jobs Strategy NJS Final DraftMuktadir IslamОценок пока нет
- Critical Reading and ReasoningДокумент34 страницыCritical Reading and Reasoningjollibee torresОценок пока нет
- Seminar PsychologyДокумент21 страницаSeminar PsychologywarkaoakaОценок пока нет
- Executive Order No. 292 BK V Title I Subtitle A Chapter 5 Personnel Policies and StandardsДокумент11 страницExecutive Order No. 292 BK V Title I Subtitle A Chapter 5 Personnel Policies and StandardsRoySantosMoralesОценок пока нет
- Assessment Task 1 BSBHRM506Документ13 страницAssessment Task 1 BSBHRM506kanika33% (6)
- Teachers' ManualДокумент69 страницTeachers' ManualNadeem naderОценок пока нет
- Human Rights City Edmonton Phase I: Feasibility Research ReportДокумент221 страницаHuman Rights City Edmonton Phase I: Feasibility Research ReportJohn Humphrey Centre for Peace and Human RightsОценок пока нет
- Learning at Work PDFДокумент432 страницыLearning at Work PDFlalagabrielle613Оценок пока нет
- A New Software Quality Model For Evaluating COTS ComponentsДокумент9 страницA New Software Quality Model For Evaluating COTS ComponentsPuan IslindaОценок пока нет
- Personnel Review: Emerald Article: Reviewing Sexual Harassment in The Workplace - An Intervention ModelДокумент20 страницPersonnel Review: Emerald Article: Reviewing Sexual Harassment in The Workplace - An Intervention Modelselina_inaОценок пока нет
- These NietoYДокумент107 страницThese NietoYAmrik SinghОценок пока нет
- Kings Photographyi f13s14Документ5 страницKings Photographyi f13s14api-212338676Оценок пока нет
- PMP Form Template v1.0Документ5 страницPMP Form Template v1.0Rashad MallakОценок пока нет
- Strategic Management: MegreyДокумент11 страницStrategic Management: MegreySHARMAINE CORPUZ MIRANDAОценок пока нет
- Quantitative Sample Aptitude QuestionsДокумент3 страницыQuantitative Sample Aptitude Questionsarunava0das-4Оценок пока нет
- Apm Competence FrameworkДокумент32 страницыApm Competence Frameworkvamsikirank100% (1)
- Community Assessment (CPHM)Документ8 страницCommunity Assessment (CPHM)KYLE SHANE LLORENTEОценок пока нет
- International Business ResearchДокумент11 страницInternational Business ResearchimadОценок пока нет
- Cover LetterДокумент1 страницаCover LetterAnonymous cx7JWToeSОценок пока нет
- 1541201682415141 (1)Документ3 страницы1541201682415141 (1)Niharika AgarwalОценок пока нет
- Proposal For Establishment of Boar Goats Breeding and Training Centre in Kibaale District Global Hand Org PDFДокумент17 страницProposal For Establishment of Boar Goats Breeding and Training Centre in Kibaale District Global Hand Org PDFmuyeghu011866100% (3)
- Evaluation Techniques For Affective ObjectivesДокумент15 страницEvaluation Techniques For Affective ObjectivesAnne MoralesОценок пока нет
- Spencer Research Grant GuidelinesДокумент18 страницSpencer Research Grant GuidelinesEmily May100% (1)
- Intel Lecture Chapter 2Документ45 страницIntel Lecture Chapter 2J NavarroОценок пока нет
- Physical EducationДокумент12 страницPhysical EducationArchitect No. 1Оценок пока нет
- ABE Level 5 UMAO Syllabus v2Документ7 страницABE Level 5 UMAO Syllabus v2Immanuel LashleyОценок пока нет
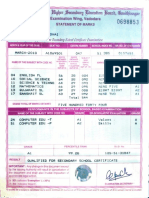
- Gujarat Ecortdary & Highersecomdarg Tducation Board, GndhinagarДокумент1 страницаGujarat Ecortdary & Highersecomdarg Tducation Board, GndhinagarRaji ChokshiОценок пока нет