Академический Документы
Профессиональный Документы
Культура Документы
Social and Ethical Issues in Software Design
Загружено:
Oliver Lin0 оценок0% нашли этот документ полезным (0 голосов)
118 просмотров4 страницыSocial and Ethical issues relating to Software Design and Development
Авторское право
© © All Rights Reserved
Доступные форматы
DOCX, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документSocial and Ethical issues relating to Software Design and Development
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
118 просмотров4 страницыSocial and Ethical Issues in Software Design
Загружено:
Oliver LinSocial and Ethical issues relating to Software Design and Development
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 4
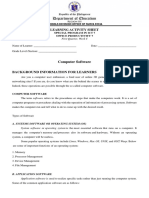
Social and Ethical Issues
The Impact of Software
Data Structures
Data Structure: A way of organising data in computer storage to ensure it can be
used efficiently (and accurately!).
o Primitive: Characters, integers
o Composite: Arrays, dictionaries, records, classes
Limitations of Computer Data structures:
o Word size: The computers preferred size for moving units of information
around. It defines the width of your processors registers, which holds data
during arithmetic and logical calculations. In the 1980s most computers had a
word size of 16 bits.
o Total memory storage: How many bits / bytes of storage. In 1980s a typical
computer could store.
o Processing speed: How many bits can be processed.
Malware
Malware = Malicious software
Tasks:
o Suggest characteristics of each.
o Write down definitions using the text (p4) or online.
o Find a recent example of one of these. Share on Google Classroom.
Virus
Characteristics
o Commonly attached or embedded within apparently legitimate software or
files.
o Able to execute, duplicate itself and perform its malicious processing.
Worms
Characteristics
o A type of virus which aims to slow down the system
o Exploits a security flaw in the OS and then install themselves on the hard
drive (often as hidden files).
o Begins to replicate itself over and over again, consuming the entire hard disk
over time.
o Typical symptoms include RAM being completely consumed by the worm.
Trojan Horse
Characteristics
o A malware that enables an outside user (or program) to take control of your
computer.
o
Spyware
Characteristics
o Aims to obtain your information without your knowledge.
o Able to capture your web browsing habits, read your email contacts or even
read keystrokes as you enter passwords and credit card details.
Ransomware
Characteristics
o A type of malicious software designed to block access to a computer system
until a sum of money is paid
Reliance on Software
For individuals, our reliance on software and being let down when it does not
perform as expected is usually just an inconvenience.
What issues could you envision for large companies that rely on software?
o $$$
Rights and Responsibilities
Response to Problems
When a user identifies a problem within a system, the developers have a responsibility to
respond and address the problem in a reasonable time frame, depending on the severity
and frequency of the issue.
Critical Affecting normal operations Immediate response
with no workaround.
Causing financial loss
Major Affecting normal operations
but there is an inconvenient
workaround available
Normal Affecting normal operations
but there is an accessible
workaround available.
Cosmetic No effect on normal As time allows
operations, but an
opportunity for
enhancement and
improvement
Ergonomics
Ergonomics: The study of the relationship between human workers and their work
environments.
In software, the issue of ergonomics is considered by:
o Considering the users needs from an ergonomic perspective
o Designing a user interface that allows users to work naturally, intuitively and
efficiently. The design should be consistent and follow design standards, use
screen elements (e.g. radio button) correctly, use colour and fonts
appropriately, align and group elements, be forgiving (allow users to reverse
an action)
o Performing usability testing to measure your success in addressing
ergonomics issues in your software design.
Privacy
Flickr
What information is collected
o Email address
o IM names
o Real name
o Current city
o Uploaded photos
o Photo data
How the information is used analytics, communication, sharing with businesses
o Advertisements associated with the photo you are seeing, or the search term
you entered.
Why they store personal information
When the policy applies e.g. to whom
o
Disclosure of potential future changes
o This page describes current Yahoo practices with respect to this particular
service. This information may change as Yahoo revises this service by adding
or removing features or using different service providers.
How the information is managed and kept secured
o
How to change your information / settings
o You can delete individual photos
o Visit your Flickr account information to edit your profile, settings and more.
Software Piracy & Copyright
Classification
Commercial
You are purchasing a license to use the software.
o https://www.adobe.com
o https://www.office.com
o https://www.autodesk.com
o
Open Source
The source code is developed collaboratively and is available to all to modify and
redistribute.
o https://www.blender.org
o http://www.chromium.org
o https://www.mozilla.org/en-US/firefox/
o https://www.mozilla.org/en-US/thunderbird/
o http://www.videolan.org/vlc/
o https://handbrake.fr
o https://sourceforge.net/projects/audacity/
o https://www.virtualbox.org
o https://www.gimp.org
o
Shareware
Covered by copyright. You are required a license to use the product. Purchasers are
allowed to make and distribute copies of the software.
o https://www.rarlab.com
Public Domain
o http://www.prongo.com/tictac/index.html
Вам также может понравиться
- Operating Systems and Open Source Software ExplainedДокумент10 страницOperating Systems and Open Source Software ExplainedLaras Raras RassОценок пока нет
- SE - Unit - 1 NotesДокумент20 страницSE - Unit - 1 NotesYuvraj AgarkarОценок пока нет
- SDD Notes - From Class of 2015Документ36 страницSDD Notes - From Class of 2015Aryan GuptaОценок пока нет
- Diab Computer 4Документ43 страницыDiab Computer 4RadОценок пока нет
- Software Engineering Assignment OverviewДокумент24 страницыSoftware Engineering Assignment OverviewKeerthi LuckyОценок пока нет
- Ost Question BankДокумент55 страницOst Question BankEpic online earning MasterОценок пока нет
- Effect of Software ProgramДокумент17 страницEffect of Software ProgramSanchithya AriyawanshaОценок пока нет
- Unit 14: A. Reading Comprehension - 5 Operating Systems: Hidden SoftwareДокумент4 страницыUnit 14: A. Reading Comprehension - 5 Operating Systems: Hidden SoftwareMuhammad Rizky Andriansyah SurataОценок пока нет
- Types of SoftwareДокумент10 страницTypes of SoftwareMunyaradzi ChizombaОценок пока нет
- Unit-1 Part-BДокумент6 страницUnit-1 Part-BGaurav KumarОценок пока нет
- SDD HSC NotesДокумент29 страницSDD HSC NotesHarrison HuОценок пока нет
- 7 Op Week 4 Computer Software - Leilani - MildredДокумент6 страниц7 Op Week 4 Computer Software - Leilani - MildredDonna Marie ArcangelОценок пока нет
- 1928 - How To Be A ProgrammerДокумент59 страниц1928 - How To Be A ProgrammerAshish ChoudharyОценок пока нет
- Literature Review On Software PiracyДокумент8 страницLiterature Review On Software Piracyea46krj6100% (1)
- Bug Tracking System ThesisДокумент7 страницBug Tracking System Thesisaprildavislittlerock100% (2)
- Chapter 3 Application SoftwareДокумент21 страницаChapter 3 Application SoftwarefuadmisbahОценок пока нет
- Department of Computer ScienceДокумент30 страницDepartment of Computer Sciencehardik chawdaОценок пока нет
- In The Context of Mobile Application DevelopmentДокумент5 страницIn The Context of Mobile Application DevelopmentDebОценок пока нет
- Lesson 5Документ48 страницLesson 5Princess Rose MendozaОценок пока нет
- Computer Software-ICT ClassДокумент4 страницыComputer Software-ICT Classkentbabayson15Оценок пока нет
- Research Paper On Operating SystemДокумент6 страницResearch Paper On Operating Systemc9sqf3ke100% (1)
- Chapter 2-1 - AppsДокумент3 страницыChapter 2-1 - AppsHazel Mae Dadivas GadinganОценок пока нет
- Facerecognitionattendence - Devansh GoswamiДокумент29 страницFacerecognitionattendence - Devansh Goswamisengaraniruddha15Оценок пока нет
- Research Paper On SpywareДокумент6 страницResearch Paper On Spywarefvf2nnj9100% (1)
- Living in It Era Module: Data Center College of The Philippines College of Criminal Justice Education Laoag CityДокумент6 страницLiving in It Era Module: Data Center College of The Philippines College of Criminal Justice Education Laoag CityJedmar AgotoОценок пока нет
- Dismiss The Myths Open Source EbookДокумент7 страницDismiss The Myths Open Source EbookSerigne Modou NDIAYEОценок пока нет
- ITE101 - Lesson 2Документ9 страницITE101 - Lesson 2Jabelle Mae DoteОценок пока нет
- Reverse Engineering:An ExplorationДокумент7 страницReverse Engineering:An Explorationdevpgm08Оценок пока нет
- Mcad2222 Sest ModulesДокумент114 страницMcad2222 Sest ModulesLEARNING LABS CONSULTINGОценок пока нет
- .Trashed 1687492846 1 Chapter Software Devlopment ProcessДокумент72 страницы.Trashed 1687492846 1 Chapter Software Devlopment ProcessRaj DebadwarОценок пока нет
- Definition of SoftwareДокумент10 страницDefinition of SoftwaretadigechОценок пока нет
- Fake Logo Detection System: 1) Background/ Problem StatementДокумент7 страницFake Logo Detection System: 1) Background/ Problem StatementAJAY SinghОценок пока нет
- Op SystemДокумент11 страницOp SystemNabeel AhmedОценок пока нет
- R4ndom Tutorial 1Документ5 страницR4ndom Tutorial 1tahirmfarooqОценок пока нет
- Research Paper On Application SoftwareДокумент8 страницResearch Paper On Application Softwaregzzjhsv9100% (3)
- Is A Collection Of: Computer Programs Data ComputerДокумент5 страницIs A Collection Of: Computer Programs Data ComputervaradatejaОценок пока нет
- A-Detailed-Lesson-Plan-Applicaion InstallationДокумент8 страницA-Detailed-Lesson-Plan-Applicaion InstallationMark Gil GomezОценок пока нет
- Chapter 2: Computers in Our Daily Life: Lesson 1: Apps: Their Relevance To Our Day-to-Day ActivitiesДокумент3 страницыChapter 2: Computers in Our Daily Life: Lesson 1: Apps: Their Relevance To Our Day-to-Day ActivitiesBY TTOОценок пока нет
- Chapter 3 Computer Software - SummaryДокумент5 страницChapter 3 Computer Software - SummaryNyana4395Оценок пока нет
- Debugging Esc 468Документ10 страницDebugging Esc 468bharat013@gmail.comОценок пока нет
- Testing the Installer: A Crucially Important CogДокумент28 страницTesting the Installer: A Crucially Important CogBárbara Cabral da ConceiçãoОценок пока нет
- Dwnload Full Fundamentals of Information Systems 8th Edition Stair Solutions Manual PDFДокумент35 страницDwnload Full Fundamentals of Information Systems 8th Edition Stair Solutions Manual PDFmiking7h100% (9)
- GCSE Computer Studies Software RevisionДокумент7 страницGCSE Computer Studies Software Revisionallen1987allenОценок пока нет
- Chapter 1 EXДокумент3 страницыChapter 1 EXhosam hasanОценок пока нет
- Dynamic Program Analysis and ToolsДокумент6 страницDynamic Program Analysis and ToolsZohaib Hassan Noor KhanОценок пока нет
- 1.1 Provide at Least Five Additional Examples of How The Law of Unintended Consequences Applies To Computer SoftwareДокумент85 страниц1.1 Provide at Least Five Additional Examples of How The Law of Unintended Consequences Applies To Computer SoftwareSherry Iran Farda TV CoolОценок пока нет
- Chapter 1 & 2 Questions SummaryДокумент10 страницChapter 1 & 2 Questions SummarySofia LivelyОценок пока нет
- Troubleshooting and Debugging TechniquesДокумент15 страницTroubleshooting and Debugging Techniquespunit soniОценок пока нет
- Computer Exam QuestionsДокумент15 страницComputer Exam QuestionsNiro ChweetyОценок пока нет
- SOFTWARE BASICS LESSON 2Документ6 страницSOFTWARE BASICS LESSON 2Prody LacasaОценок пока нет
- What Is The Significance of Software Crisis in Reference To Software Engineering DisciplineДокумент8 страницWhat Is The Significance of Software Crisis in Reference To Software Engineering DisciplineSuman pranav TuduОценок пока нет
- Olevel 1 Ittnb b3 08apr20 ARTДокумент3 страницыOlevel 1 Ittnb b3 08apr20 ARTUndergraduate LibraryОценок пока нет
- Advantages of Open Source SoftwareДокумент8 страницAdvantages of Open Source SoftwareVino LakshmiОценок пока нет
- Software Design and Development Prelim NotesДокумент5 страницSoftware Design and Development Prelim NotesAqua Dreamweaver TutorialsОценок пока нет
- Software Troubleshooting: Team Yamete KudasaiДокумент43 страницыSoftware Troubleshooting: Team Yamete KudasaiRose ann BagoodОценок пока нет
- Mod 1, Lesson 3 HandoutДокумент5 страницMod 1, Lesson 3 HandoutJames CharlesОценок пока нет
- In-The-Wild Testing: White PaperДокумент9 страницIn-The-Wild Testing: White PaperIvanОценок пока нет
- Purpose and Functions of Software ComponentsДокумент4 страницыPurpose and Functions of Software ComponentsShanice RussellОценок пока нет
- Software Engineering Q-AДокумент85 страницSoftware Engineering Q-Amoha100% (1)
- 2015 Ascham HSC Chemistry Trials & SolutionsДокумент42 страницы2015 Ascham HSC Chemistry Trials & SolutionsOliver LinОценок пока нет
- German Beg HSC Exam 2009Документ26 страницGerman Beg HSC Exam 2009Oliver LinОценок пока нет
- German Beg HSC Exam 2008Документ26 страницGerman Beg HSC Exam 2008Oliver LinОценок пока нет
- German Beg HSC Exam 2013Документ22 страницыGerman Beg HSC Exam 2013Oliver LinОценок пока нет
- German Beg HSC Exam 2012Документ20 страницGerman Beg HSC Exam 2012Oliver LinОценок пока нет
- German Beg HSC Exam 2010Документ20 страницGerman Beg HSC Exam 2010Oliver LinОценок пока нет
- German Beg HSC Exam 2011Документ24 страницыGerman Beg HSC Exam 2011Oliver LinОценок пока нет
- BOSTES German Beginners HSC Exam 2015Документ22 страницыBOSTES German Beginners HSC Exam 2015Oliver LinОценок пока нет
- BOSTES Agriculture HSC Exam 2015Документ24 страницыBOSTES Agriculture HSC Exam 2015Oliver LinОценок пока нет
- BOSTES 2016 HSC German BeginnersДокумент24 страницыBOSTES 2016 HSC German BeginnersOliver LinОценок пока нет
- German Beg HSC Exam 2014Документ20 страницGerman Beg HSC Exam 2014Oliver LinОценок пока нет
- BOSTES 2016 HSC Agriculture ExamДокумент28 страницBOSTES 2016 HSC Agriculture ExamOliver LinОценок пока нет
- NESA 2017 HSC German BeginnersДокумент24 страницыNESA 2017 HSC German BeginnersOliver LinОценок пока нет
- BOSTES 2016 HSC German BeginnersДокумент24 страницыBOSTES 2016 HSC German BeginnersOliver LinОценок пока нет
- BOSTES Agriculture HSC Exam 2014Документ24 страницыBOSTES Agriculture HSC Exam 2014Oliver LinОценок пока нет
- Ah 2010 HSC Exam Ancient HistoryДокумент30 страницAh 2010 HSC Exam Ancient Historynaomi1210Оценок пока нет
- NESA 2017 HSC Agriculture ExamДокумент26 страницNESA 2017 HSC Agriculture ExamOliver LinОценок пока нет
- Aboriginal Studies HSC Exam 2014 PDFДокумент16 страницAboriginal Studies HSC Exam 2014 PDFOliver LinОценок пока нет
- Command Line CheatsheetДокумент2 страницыCommand Line CheatsheetOliver LinОценок пока нет
- BOSTES 2015 Aboriginal Studies HSC ExamДокумент16 страницBOSTES 2015 Aboriginal Studies HSC ExamOliver LinОценок пока нет
- BOSTES 2016 HSC Aboriginal StudiesДокумент24 страницыBOSTES 2016 HSC Aboriginal StudiesOliver LinОценок пока нет
- JavaScript CheatsheetДокумент1 страницаJavaScript CheatsheetOliver LinОценок пока нет
- Truancy GameДокумент7 страницTruancy GameOliver LinОценок пока нет
- Ah 2010 HSC Exam Ancient HistoryДокумент30 страницAh 2010 HSC Exam Ancient Historynaomi1210Оценок пока нет
- CGR (22318) Chapter 1 NotesДокумент10 страницCGR (22318) Chapter 1 Notespdijgqam1nОценок пока нет
- Cantor's Diagonal ArgumentДокумент5 страницCantor's Diagonal ArgumentLe Nguyen Thang LongОценок пока нет
- Huawei LTE Radio Network FeaturesДокумент2 страницыHuawei LTE Radio Network FeaturesGauravSwamiОценок пока нет
- Richtek RT9742Документ20 страницRichtek RT9742zequinha2002Оценок пока нет
- ED6001 Project ReportДокумент9 страницED6001 Project Reportsaloni jainОценок пока нет
- Manufacturing KPI Dashboard Someka Excel Template V3 Free VersionДокумент11 страницManufacturing KPI Dashboard Someka Excel Template V3 Free VersionYoro Diallo50% (2)
- Reactor FuncionamientoДокумент24 страницыReactor FuncionamientoDaniel BahamondesОценок пока нет
- Uil Lincoln-Douglas Debate Research SeriesДокумент45 страницUil Lincoln-Douglas Debate Research SeriesAryan JasaniОценок пока нет
- M&a Product SummaryДокумент34 страницыM&a Product SummaryMartinez Mauricio Martinez GomezОценок пока нет
- Assurance Engagement OverviewДокумент94 страницыAssurance Engagement OverviewShahid MahmudОценок пока нет
- CCNA Security Ch01 Quiz AnswersДокумент7 страницCCNA Security Ch01 Quiz Answersdercole69Оценок пока нет
- Building Arduino PLCS: The Essential Techniques You Need To Develop Arduino-Based PlcsДокумент1 страницаBuilding Arduino PLCS: The Essential Techniques You Need To Develop Arduino-Based Plcs超揚林Оценок пока нет
- Amada Laser CuttingДокумент8 страницAmada Laser CuttingMahmud MaherОценок пока нет
- Test Sample 1 - May 30 2020 Easergy P3U30 Settings Report 2020-05-30 14 - 43 - 09Документ255 страницTest Sample 1 - May 30 2020 Easergy P3U30 Settings Report 2020-05-30 14 - 43 - 09jobpei2Оценок пока нет
- Accessories CatalogДокумент152 страницыAccessories Catalogsky100% (1)
- Cmu-4000 Og 5230790130Документ74 страницыCmu-4000 Og 5230790130roshan mungurОценок пока нет
- Review Questions For Chapter 1 Business Information SystemsДокумент2 страницыReview Questions For Chapter 1 Business Information Systemsrobj20076404Оценок пока нет
- Expert Systems TypesДокумент9 страницExpert Systems TypesOlaniyiOluwatosinFalomoОценок пока нет
- Philips Azurion Bi Plane Specifications 7b20 12Документ28 страницPhilips Azurion Bi Plane Specifications 7b20 12service iyadMedicalОценок пока нет
- F-RPO-02A Research Protocol AssessmentДокумент4 страницыF-RPO-02A Research Protocol AssessmentEuniece CepilloОценок пока нет
- ZTE ZXSDR R8861 Product Description PDFДокумент23 страницыZTE ZXSDR R8861 Product Description PDFНиколайИгоревичНасыбуллин100% (1)
- How To Upgrade Oracle From Version 1120311204 To 12 Apidekifiles39725howtoaaДокумент86 страницHow To Upgrade Oracle From Version 1120311204 To 12 Apidekifiles39725howtoaaAswin HadinataОценок пока нет
- Free Change Proposal Template PowerPoint DownloadДокумент3 страницыFree Change Proposal Template PowerPoint DownloadbiniОценок пока нет
- DMC Lab ManualДокумент67 страницDMC Lab ManualVS creationsОценок пока нет
- GrafcetДокумент6 страницGrafcetcesar_mosqueda836Оценок пока нет
- Spatial Database For GPS Wildlife Tracking Data: Ferdinando Urbano Francesca CagnacciДокумент271 страницаSpatial Database For GPS Wildlife Tracking Data: Ferdinando Urbano Francesca CagnacciMonse JuarezОценок пока нет
- Zebradesigner XML Release Notes v2509427Документ13 страницZebradesigner XML Release Notes v2509427atacaraОценок пока нет
- Electrical Engineering Technology Department Ms. Jen AndadorДокумент13 страницElectrical Engineering Technology Department Ms. Jen Andadorpeter vanderОценок пока нет
- Do-It-Yourself (DIY) Dog Training by Sharda BakerДокумент142 страницыDo-It-Yourself (DIY) Dog Training by Sharda Bakerbertspamintuan100% (3)
- Social Media Addiction and Its Effects TДокумент35 страницSocial Media Addiction and Its Effects TMekah EliОценок пока нет