Академический Документы
Профессиональный Документы
Культура Документы
CEH & Security+ Training Program
Загружено:
ahaque08Исходное описание:
Оригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
CEH & Security+ Training Program
Загружено:
ahaque08Авторское право:
Доступные форматы
2016-17
aaca
Certified Ethical
12000+
students Hacker (CEH) &
Lifetime
Certification
Security+ Training
Access
Program
HD Training
Kick start your Cyber Security Career
45 hours+
Video
Community
support
14121 NE Airport Way, Portland EH Academy
Certified Ethical Hacker (CEH) & Security+ Training Program
CEH SERIES
Footprinting Reconnaissance
Duration: 75 Minutes Duration: 75 Minutes
Quizzes: 3 Quizzes: 3
Footprinting is the gathering of information Reconnaissance is an exploration that is conducted
related to a particular computer and its users and to gain information. In this module, you will be
systems. In this module you will learn the various learning the tools and steps for assessing
tools and techniques used in footprinting as well computers, computer systems, networks, and
as prevention and countermeasures that you can applications. We will include in-depth demos that
take to protect yourself and your systems. We will go into further detail on the uses of many of these
pair this with in-depth demos on some of the tools tools.
and their uses.
Footprinting /Reconnaissance Reconnaissance
Methodology Footprinting
Tools Scanning
Countermeasures Countermeasures
Banner Grabbing Enumeration
Duration: 75 Minutes Duration: 75 Minutes
Quizzes: 3 Quizzes: 3
Banner grabbing is a technique used to grab Every system has its own services running on the
information about computer systems on a network network; in many cases those services can reveal
and the services running its open ports. In the sensitive information about network topology,
module, Banner Grabbing, you will be learning the users and groups, etc. Services like LDAP or NTP
tools and techniques used in the process of banner can be enumerated to reveal such information. In
grabbing. You will learn how to take inventory of this module you will be introduced to enumeration
the systems and services on your networks. You and the many different uses it has in computer
will be able to identify potential risks of banner systems. This course will include demos on the
grabbing and learn steps to take to protect your different tools and uses of enumeration.
networks and systems from the potential threat of
an intruder using banner grabbing. We will pair Enumerating Services and
this course with demos on the tools you will be Countermeasures
discussing. Enumeration
Banner Grabbing
Countermeasures
Linux Fundamentals Configuring Linux for Pentesting
Duration: 75 Minutes Duration: 75 Minutes
Quizzes: 3 Quizzes: 3
Linux was developed as a free operating system Servers are primary targets for attackers.
for Intel x86 based personal computers. It is a Pentesting is an attack on a system in hopes of
EH Academy | +1 503 334-3704 1
Certified Ethical Hacker (CEH) & Security+ Training Program
leading operating system on servers. Linux runs on finding security weaknesses. In the course
embedded systems. The most widely used Configuring Linux for Pentesting, you will be
operating system for mobile technology (tablets learning the steps to configure Linux for pentesting
and smartphones) is built on top of the Linux and tools used for pentesting on a Linux system.
kernel. In this module you will be learning the This course will be combined with demos that will
fundamentals of Linux. We will be pairing this delve deeper and give you real world examples of
course with demos with a more in-depth look into the tools and programs that Linux uses to
some of the fundamentals and tools of Linux. accomplish pentesting.
Introduction to Linux Configuring Linux for Pentesting
Working in Linux Pentesting on Linux.
System Hacking Spyware & Keyloggers
Duration: 90 Minutes Duration: 90 Minutes
Quizzes: 4 Quizzes: 3
Ensure that you know everything involved in You will take a good look at spyware, the activities
securing a Windows system against attack. During it performs, different types of spyware, and the
this course you’ll get into Windows passwords — countermeasures needed in order to prevent
how they’re created, how they’re stored, and hackers from utilizing these types of techniques
different methods used to crack them. You’ll against your company. You will also spend time
discover different methods used for guessing studying different types of keyloggers. There are
passwords and breaking the different security three different types of keyloggers that we see
methods used within the Windows operating used in today’s environments: hardware, software,
system. You’ll find discussions on responding to and kernel/driver keyloggers. A good pen tester or
privilege escalation. You’ll also spend some time ethical hacker cannot perform his or her job
going through a couple of scenarios demonstrating properly without understanding the
how to use key defense tools. Overall, the topics countermeasures for all of the hacking techniques
explored here will teach you how to increase used against today’s computer systems. Overall,
security on your Windows machines, as well as these topics will help prepare you for certification
show the required procedures and tools to exams from vendors, such as Linux, CompTIA, and
prepare for different certification exams from EC- EC-Council.
Council, CompTIA, Linux, and CISSP.
Spyware Uncovered
Windows Hacking Keyloggers
Password Attacks
Alternate Data Streams
Steganography
Rootkits
Course Summary
Viruses and Worms Denial of Service
Duration: 90 Minutes Duration: 90 Minutes
Quizzes: 3 Quizzes: 4
Become familiar with the following concepts:
You will discover what viruses and worms are and denial-of service, distributed denial-of-service, and
how they can infect computers and systems. You’ll how the denial of-service and distributed denial-
EH Academy | +1 503 334-3704 2
Certified Ethical Hacker (CEH) & Security+ Training Program
study their nature, how they function, and their of-service attacks take place. You will also see
impact. You will also spend time going through what botnets are and how they are used to attack
discussions on varieties of each, along with some your system or network. You will find explanations
real life examples. Refine your understanding of on the tools that are used to attack, and how you
viruses and worms to better your system. The can detect such attacks. You will be introduced to
knowledge you gain here will prepare you to be a different countermeasures, so that you can plan,
more effective network administrator. prepare, and establish the relevant
Furthermore, the topics covered here will help countermeasures to protect your organization.
with preparing you for security certification exams You will also learn how DoS and DDoS can be used
offered by EC-Council, CompTIA, and Linux. in penetration testing. You will go through
discussions on how to protect your organization
Viruses from the distributed denial-of-service attacks and
Worms denial-of service penetration testing. Altogether,
these topics focus on deepening your
Vulnerability Assessment understanding of security concepts and practices,
Duration: 75 Minutes so that you’re a more efficient network
Quizzes: 3 administrator. With the skills you gain here, you’re
equipped to pursue a number of security
Our course Vulnerability Assessment you will certifications from CompTIA, EC-Council, and CEH.
introduce to the concepts of: Vulnerability
Assessment, Vulnerability Assessment Tools, and Denial-of-Service & Distributed Denial-of-
Patch Management. It will offer demos on several Service
of the vulnerability assessment tools that are Digital Attack Map
available, as well as in-depth discussions on the Botnets
benefits of these tools. We will discuss the process DoS/DDoS Attack Tools and Detection
of analyzing the scan results that the vulnerability DoS/DDoS Countermeasures
assessment tools provide. Finally, we will discuss DoS/DDoS in Penetration Testing
patch management and some tools that are
available for this process and at the end of this Covering Tracks
course you will be able to create a comprehensive Duration: 75 Minutes
VA program, identify key vulnerabilities, and Quizzes: 3
perform mitigation actions before those
vulnerabilities can be exploited. This course will be going over various ways that
attackers have at their disposal to cover any tracks
Testing Vulnerabilities that may lead to their unwanted eviction or worse
Results, Reports, and Remediation yet to an audit trail that would lead directly back
to them. In this module we will be discussing
Disaster Recovery and Risk Management disabling auditing during or after an event, steps to
Duration: 30 Minutes take once it is disabled, and destroying any
Quizzes: 3 evidence. We will be going over various ways to
avoid detection on Linux machines, and this will
Since you are a part of IT operations in your include several in-depth demos on various
enterprise, you could be involved in planning and operations for the Linux machines.
applying policies related to risk management
and/or disaster recovery. In our course disaster Avoiding Detection on Windows Machines
recovery and risk management, you will receive an Avoiding Detection on Linux Machines
introduction to the basics of risk management and Destroying the Evidence
EH Academy | +1 503 334-3704 3
Certified Ethical Hacker (CEH) & Security+ Training Program
disaster recovery. When you have completed the Log Protection Techniques
course, you will be able to identify a risk and the
effect that it has on daily operations. You will gain Trojans and Backdoors
an understanding of security measures and how Duration: 90 Minutes
they are implemented, as well as, the importance Quizzes: 4
and the process of managing risk in your
environment. We will partner this with a detailed As an ethical hacker, there are times when you
demo on the process of risk assessment. You will need to hide software from the company that you
gain an understanding of disaster recovery, be able are performing the test against in order to verify
to define what a disaster is, rank a disaster, and that the defensive strategy is able to find your
create a plan that will define how to recover from software. Trojans and Backdoors is the course
a disaster, as well as, successfully recovering your where our software is going to be going
data. undercover. In this module we are going to define
malware and take a look at how a payload is
Disaster Recovery delivered. We will overview the various Trojan
Risk Management tools, and tools used to generate Trojan programs,
as well as, learning about Netcat. We will spend
Introduction to Ethical Hacking time going over countermeasures and various anti-
Duration: 90 Minutes Trojan software and hardware, and preventive
Quizzes: 3 methods that can be used to prevent attacks. We
will also be incorporating several demos on the
Ethical hacking is testing the resources for a good many tools that we will be discussing in this
cause and for the betterment of technology. In our module.
course Introduction to Ethical Hacking, you will be
introduced to various concepts on ethical hacking. Defining Malware
We will be talking about vulnerabilities, exploits, Malware
defense strategy, penetration testing, pentest Tools of the Trade
types and methodology, vulnerability Countermeasures
management, incident management, and security Course Summary
policy development, and at the end of this course
we hope you will have a basic understanding of Penetration Testing
the various concepts involved in ethical hacking. Duration: 60 Minutes
Quizzes: 3
Introduction to Hacking
Security Management Pentesting is an intentional attack on a system to
discover security weaknesses. These can be left
Port Scanning either by the security officer or the security
Duration: 60 Minutes controls. Penetration Testing is our course that
Quizzes: 3 covers security, vulnerabilities, different types of
tests, and when to test as a pen tester. We have
When a port is scanned on a server, the port paired this with an in-depth demo on vulnerability
returns a response indicating that the port is open assessment using the tool Nexpose. At the end of
and a service is listening. In our course Port this course we will have reviewed security and
Scanning, you will learn how ports can be scanned, vulnerability assessment, and the differences
how a hacker can break into your network through between automatic and manual testing.
the ports, and the countermeasures you can take
to protect your device or network. Our course will Penetration Testing Introduction
EH Academy | +1 503 334-3704 4
Certified Ethical Hacker (CEH) & Security+ Training Program
offer in-depth discussions on port scanning Organizational Considerations
methods and techniques, port scanning tools, and
port scanning countermeasures. We will partner Sniffers
this with detailed demos on Ping, Ping tester, and Duration: 90 Minutes
Netstat. Quizzes: 3
Port Scanning A sniffer is our course where we take a look at
Advanced Techniques Network Sniffing. We will be covering the basics of
packet sniffing, ARP cache poisoning, DNS
Advanced Exploitation Techniques spoofing, SSL sniffing, VoIP phone calls and sniffing
Duration: 90 Minutes remote desktop connections. This will be coupled
Quizzes: 3 with demos on Wireshark, ARP poisoning, and
XARP.
Exploit is a common term in the computer security
community that refers to a piece of software that Network Sniffing
takes advantage of a bug or glitch. In our course Security Measures
Advanced Exploitation Techniques, you will learn
what advanced exploitation techniques are and Advanced Exploitation Techniques
how you can use them in your penetration testing. Duration: 90 Minutes
You will also learn how to use Metasploit to exploit Quizzes: 3
vulnerabilities. This will be coupled with in-depth
demos on using Metasploit, and other Metasploit Exploit is a common term in the computer security
tools, such as, Meterpreter, Armitage, and community that refers to a piece of software that
Armitage-mimkatz. takes advantage of a bug or glitch. In our course
Advanced Exploitation Techniques, you will learn
Advanced Exploiting Techniques what advanced exploitation techniques are and
Penetration Testing how you can use them in your penetration testing.
Exploits You will also learn how to use Metasploit to exploit
vulnerabilities. This will be coupled with in-depth
Scanning Networks demos on using Metasploit, and other Metasploit
Duration: 60 Minutes tools, such as, Meterpreter, Armitage, and
Quizzes: 3 Armitage-mimkatz.
Network scanning is the scanning of public or Advanced Exploiting Techniques
private networks to find out which systems are Penetration Testing
running, their IP addresses, and which services Exploits
they are running. In our course Network Scanning,
you will learn techniques for private and public Hacking Web and App Servers
network scanning using various tools. Duration: 75 Minutes
Accompanied with, in-depth demos and Quizzes: 3
discussions on how to use Angry IP, Nmap, Hping,
and Zmap network scanners. Through this, you will Hacking Web and Application Servers course, is a
learn the steps to network scanning, how to draw course that will give us a good idea about
a network map, and plan an attack accordingly. vulnerabilities and attacks available for web
servers and web applications. This course includes
Private and Public Network Scanning in-depth demos on several of the tools used for
Using Zmap hacking web servers and application servers. These
EH Academy | +1 503 334-3704 5
Certified Ethical Hacker (CEH) & Security+ Training Program
tools include Apache2, Netcraft, Website
SQL Injections Mirroring, W3AF, and WMAP. By the end of this
Duration: 60 Minutes course we will have discussed various ways to
Quizzes: 3 collect information from web servers, application
server attacks, and finding vulnerabilities in a
SQL injection is the most used of all attacks. In this server.
module, SQL Injections, you will be learning how
SQL injections can be initiated, cause damage or Web Server Attacks
loss, prevention against such attacks, and Web Application Attacks
discussing detection tools. This course includes
demos demonstrating BSQL tool as well as SQL Session Hijacking
Injection Username and Password. By the end of Duration: 90 Minutes
this course you will have covered SQL injection Quizzes: 3
methodology, attacks, buffer overflow exploit,
testing for SQL injection, countermeasures and Have you heard the words “session hijacking”?
detection tools. Simply put, it is defined as an intruder taking over
a genuine session between two computers and
SQL Injections using if for sinister purposes. In the course Session
Protecting Against SQL Injections Hijacking, you will learn details about session
hijacking, well-known techniques employed by
Buffer Overflows aggressors, the steps involved in session hijacking,
Duration: 75 Minutes various types of session hijacking, tools for
Quizzes: 3 hijacking sessions, ways you can protect
yourselves from session hijacking, and how
Buffer overflow occurs when you try to store more pentesting can be used to identify vulnerabilities.
data than what the allocated buffer or storage
area can hold. In this module you will be Session Hijacking
introduced to the concepts of buffer overflows, Countermeasures
how they happen, and how attackers take
advantage of them. You will also learn how to Hacking Wireless Networks
defend against buffer overflow attacks, and what Duration: 60 Minutes
security measures you can take to protect your Quizzes: 3
data. We will accompany this with several demos
that will delve deeper and help you understand Wireless attacks have become easy; even unskilled
some of the specific topics that will be discussed. people with little computer literacy can accomplish
them. This is because of the many automated tools
Buffer Flow available to perform this hack. In our course
Program and Application Vulnerability Hacking Wireless Networks, we will not be
Defense, Countermeasures, and Security focusing on weaknesses of your wireless networks
or how to protect them, instead, we will focus on
Social Engineering showing you how to gain access to a wireless
Duration: 60 Minutes network.
Quizzes: 3
Hacking Wireless Networks
Social engineering is the art of extorting Hacking Windows
employees for information. It can take the form of
human-based or digital. In our course Social
EH Academy | +1 503 334-3704 6
Certified Ethical Hacker (CEH) & Security+ Training Program
Engineering, you will learn what social engineering Authentication Systems
is, who’s at risk, and how to protect and educate Duration: 60 Minutes
your employees against social engineering. You Quizzes: 3
will learn the importance of creating a security
policy, and how to deal with the threat of human- Whenever we login to a computer system, we
based attacks from both outside and inside the provide information to identify ourselves. We refer
company. You will learn what kind of risks to this as authentication. Authentication has been
computer-based attacks and social media present. developed to contain more than just username
We will couple this with in-depth demos on and password because we are looking for added
phishing email, SET-webTemplate, SET-spear layers of security. In this module we will be
phishing, SET-trojan, and SET SMS Spoofing. covering authentication factors, forms of
authentication, and authentication protocols. We
Social Engineering will also be going over RADIUS, LDAP, and SSO. We
Social Engineering Demos will pair this with several demos depicting practical
uses of the many tools that we will discuss in this
Cryptography Weaknesses module.
Duration: 75 Minutes
Quizzes: 3 Introduction
Authentication Protocols
Cryptography is the science of writing in secret RADIUS, LDAP, and SSQ
code and is considered an ancient art. The first
documented use of cryptography dates back to Cross-Site Scripting
circa 1900 B.C. In our course Cryptography Duration: 60 Minutes
Weaknesses, we will discuss weaknesses in Quizzes: 3
cryptography and ways to improve your security.
We will also cover the use of symmetric and As a security tester or security analyst, it is
asymmetric keys and the use of hybrid keys, as important that you are aware of cross-site
well as, the use of hashing algorithms and digital scripting vulnerabilities and how they may be
signatures. We will pair this with several demos to exploited by attackers. In our course Cross-site
show you how each of these works in practical Scripting, you will gain a comprehensive
situations. understanding of cross-site scripting, you will learn
how to prevent it, and how you can test to identify
Encryption cross-site scripting vulnerabilities. You will also
Symmetric Encryption learn what cross-site scripting is and what the
Asymmetric Encryption different types of cross-site scripting you may
Hashing Algorithms come across. This course will also be paired with
Digital Signatures several demos that give you a real world view of
what we have and will cover in this module.
Mobile Hacking Basics
Duration: 90 Minutes Cross-Site Scripting
Quizzes: 3 Types of Cross-Site Scripting
Preventing Cross-Site Scripting
Mobile hacking can be anything from searching for
unlocked Wi-Fi networks, to the hacking of Physical Security
Android OS or IOS systems. In our course Mobile Duration: 75 Minutes
Hacking Basics, we will give you a basic Quizzes: 4
introduction of the tools and concepts behind
EH Academy | +1 503 334-3704 7
Certified Ethical Hacker (CEH) & Security+ Training Program
mobile hacking with demos giving you a look at What kind of security measures do you take to
some of these tools in action. protect your facilities, equipment, resources,
personnel, and property from damage caused by
Securing Mobile Basics unauthorized access? In this module, Physical
Mobile Security Considerations Security, these are questions that we will be
Hardening Mobile Devices answering. You will be learning how to recognize
the potential risks of unauthorized access to your
Evading Firewalls and Honeypots business and personnel, and how to counteract
Duration: 75 Minutes these risks by learning the steps to creating a
Quizzes: 3 security policy for you and your personnel to
implement. We have included demos that will help
Evading Firewalls and Honeypots, is the course you better understand the concepts that will be
where we will not only discuss what firewalls and discussed in this module.
honeypots are, but how attackers get around
these preventive programs. You will learn about Physical Security
the different types of firewalls and how they may Internal Support Systems
be evaded. You will also learn what honeypots are Perimeter Security
and how they are set-up to divert any would be Audits, Testing & Drills
attacker’s attention. You will be learning how
attackers anticipate honeypots and how Evading IDS
penetration testing can help you in dealing with Duration: 75 Minutes
these attackers. We have paired this course with Quizzes: 4
several demos that will cover more in-depth the
topics that we will be discussing and help you gain Intrusion Detection System (IDS) is a device or
a broader understanding of those topics. software that monitors network activities and
system activities. While monitoring, it looks for
Working with Firewalls suspicious activities and security policy violations.
Working with Honeypots In this module Evading IDS we will be discussing
the vulnerabilities in an IS, types of IDS, types of
Wireless Types and Vulnerabilities evasion, techniques used to evade IDS, IDS tools,
Duration: 75 Minutes and how to carry out penetration testing so you
Quizzes: 3 can put a prevention plan in place. We will
combine this with an in-depth demo on how to
Wireless types, such as WLAN, are also known as avoid IDS.
WiFi networks and they are susceptible to security
lapses that wired networks are exempt from. In Introduction to IDS
this module you will learn about different wireless Evading IDS
types and their vulnerabilities. You will learn about Points of Vulnerability in IDS
several different tools that will help you take DE synchronization
countermeasures against these vulnerabilities. We Intrusion Detection Tools
will complete this course with demos on different IDS Evading Tools
tools that we will be discussing. Countermeasures
Intrusion Detection Tools
Wireless Authentication IDS Evading Tools
Authentication Systems Countermeasures
EH Academy | +1 503 334-3704 8
Certified Ethical Hacker (CEH) & Security+ Training Program
SECURITY+ (SY0-401)
SERIES
Business Continuity
Security Incidents
Duration: 30 Minutes
Duration: 30 Minutes
Quizzes: 3
Quizzes: 3
Business continuity plans are important if the
Handling incidents often needs preparation. There
organization wishes to continue its normal
are plans and procedures to be taken, and drills to
operations in disasters, whether they are man-
prepare the team. A successful handling team can
made or natural. Business continuity plans study
prevent loss of money for an organization in case
all kinds of threats and estimates the damage
of incident. It is an investment rather than a cost if
resulting from those threats. In the course
it is done correctly. In the course Incident
Business Continuity, you will learn the different
Handling, you will learn how to recognize what an
categories that the events that threaten your
incident is and where they potentially come from.
business are classified under. You will also learn
You will then learn the steps to handling incidents
the steps in creating a business continuity plan.
and implementing those steps into your everyday
You will also delve further into the development
policies and procedures.
process for a business continuity plan, and learn all
the necessary steps that are involved in initiating
Incident Handling the plan as well.
Incident Procedures
BCP
Reviewing and Implementing BCP
Network Design and Security Controls
Duration: 60 Minutes System Hacking
Quizzes: 3 Duration: 90 Minutes
Quizzes: 4
Today’s threats and cyber intelligence have made
it mandatory for us to use devices for protection. Ensure that you know everything involved in
Threats can come from inside our network and the securing a Windows system against attack. During
Internet. This makes it so that a firewall alone is this course you’ll get into Windows passwords —
not sufficient. We need to design a secure how they’re created, how they’re stored, and
network. In Network Design and Security Controls, different methods used to crack them. You’ll
you will learn the steps and the tools to designing discover different methods used for guessing
a secure network. You will also learn of the many passwords and breaking the different security
security devices that you have at your disposal, methods used within the Windows operating
with an in-depth discussion on firewalls and their system. You’ll find discussions on responding to
uses. Included in this module will be detailed privilege escalation. You’ll also spend some time
demos on Firewall and proxy-nat, DMZ, and IDS- going through a couple of scenarios demonstrating
IPS. how to use key defense tools. Overall, the topics
explored here will teach you how to increase
Network Design security on your Windows machines, as well as
Security Devices show you required procedures and tools to
EH Academy | +1 503 334-3704 9
Certified Ethical Hacker (CEH) & Security+ Training Program
Spyware & Keyloggers prepare for different certification exams from EC-
Duration: 90 Minutes Council, CompTIA, Linux, and CISSP.
Quizzes: 3
Windows Hacking
You will take a good look at spyware, the activities Password Attacks
it performs, different types of spyware, and the Alternate Data Streams
Countermeasures needed in order to prevent Steganography
hackers from utilizing these types of techniques Rootkits
against your company. You will also spend time Course Summary
studying different types of keyloggers. There are
three different types of keyloggers that we see Viruses and Worms
used in today’s environments: hardware, software, Duration: 90 Minutes
and kernel/driver keyloggers. A good pen tester or Quizzes: 3
ethical hacker cannot perform his or her job
properly without understanding the You will discover what viruses and worms are and
countermeasures for all of the hacking techniques how they can infect computers and systems. You’ll
used against today’s computer systems. Overall, study their nature, how they function, and their
these topics will help prepare you for certification impact. You will also spend time going through
exams from vendors, such as Linux, CompTIA, and discussions on varieties of each, along with some
EC-Council. real life examples. Refine your understanding of
viruses and worms to better your system. The
Spyware Uncovered knowledge you gain here will prepare you to be a
Keyloggers more effective network administrator.
Furthermore, the topics covered here will help
with preparing you for security certification exams
Denial of Service offered by EC-Council, CompTIA, and Linux.
Duration: 90 Minutes
Quizzes: 4 Viruses
Worms
Become familiar with the following concepts:
denial-of-service, distributed denial-of-service, and Vulnerability Assessment
how the denial-of-service and distributed denial- Duration: 75 Minutes
of-service attacks take place. You will also see Quizzes: 3
what botnets are and how they are used to attack
your system or network. You will find explanations Our course Vulnerability Assessment will introduce
on the tools that are used to attack, and how you you to the concepts of: Vulnerability Assessment,
can detect such attacks. You will be introduced to Vulnerability Assessment Tools, and Patch
different countermeasures, so that you can plan, Management. It will offer demos on several of the
prepare, and establish the relevant vulnerability assessment tools that are available,
countermeasures to protect your organization. as well as in-depth discussions on the benefits of
You will also learn how DoS and DDoS can be used these tools. We will discuss the process of
in penetration testing. You will go through analyzing the scan results that the vulnerability
discussions on how to protect your organization assessment tools provide. Finally, we will discuss
from the distributed denial-of-service attacks and patch management and some tools that are
denial-of-service penetration testing. Altogether, available for this process and at the end of this
these topics focus on deepening your course you will be able to create a comprehensive
understanding of security concepts and practices, VA program, identify key vulnerabilities, and
EH Academy | +1 503 334-3704 10
Certified Ethical Hacker (CEH) & Security+ Training Program
so that you’re a more efficient network perform mitigation actions before those
administrator. With the skills you gain here, you’re vulnerabilities can be exploited.
equipped to pursue a number of security
certifications from CompTIA, EC-Council, and CEH. Testing Vulnerabilities
Results, Reports, and Remediation
Denial-of-Service & Distributed Denial-of-
Service Disaster Recovery and Risk Management
Digital Attack Map Duration: 30 Minutes
Botnets Quizzes: 3
DoS/DDoS Attack Tools and Detection
DoS/DDoS Countermeasures Since you are a part of IT operations in your
DoS/DDoS in Penetration Testing enterprise, you could be involved in planning and
applying policies related to risk management
and/or disaster recovery. In our course disaster
Covering Tracks recovery and risk management, you will receive an
Duration: 75 Minutes introduction to the basics of risk management and
Quizzes: 3 disaster recovery. When you have completed the
course, you will be able to identify a risk and the
In Covering Tracks this course will be going over effect that it has on daily operations. You will gain
various ways that attackers have at their disposal an understanding of security measures and how
to cover any tracks that may lead to their they are implemented, as well as, the importance
unwanted eviction or worse yet to an audit trail and the process of managing risk in your
that would lead directly back to them. In this environment. We will partner this with a detailed
module we will be discussing disabling auditing demo on the process of risk assessment. You will
during or after an event, steps to take once it is gain an understanding of disaster recovery, be able
disabled, and destroying any evidence. We will be to define what a disaster is, rank a disaster, and
going over various ways to avoid detection on create a plan that will define how to recover from
Linux machines, and this will include several in- a disaster, as well as, successfully recovering your
depth demos on various operations for the Linux data.
machines.
Risk Management
Avoiding Detection on Windows Machines Disaster Recovery
Avoiding Detection on Linux Machines
Destroying the Evidence Introduction to Ethical Hacking
Log Protection Techniques Duration: 90 Minutes
Quizzes: 3
Ethical hacking is testing the resources for a good
Trojans and Backdoors cause and for the betterment of technology. In our
Duration: 90 Minutes course Introduction to Ethical Hacking, you will be
Quizzes: 4 introduced to various concepts on ethical hacking.
We will be talking about vulnerabilities, exploits,
As an ethical hacker, there are times when you defense strategy, penetration testing, pentest
need to hide software from the company that you types and methodology, vulnerability
are performing the test against in order to verify management, incident management, and security
that the defensive strategy is able to find your policy development, and at the end of this course
software. Trojans and Backdoors is the course we hope you will have a basic understanding of
where our software is going to be going
EH Academy | +1 503 334-3704 11
Certified Ethical Hacker (CEH) & Security+ Training Program
undercover. In this module we are going to define the various concepts involved in ethical hacking.
malware and take a look at how a payload is
delivered. We will overview the various Trojan Introduction to Hacking
tools, and tools used to generate Trojan programs, Security Management
as well as learn about Net cat. We will spend time
going over countermeasures and various anti- Port Scanning
Trojan software and hardware, and preventive Duration: 105 Minutes
methods that can be used to prevent attacks. We Quizzes: 3
will also be incorporating several demos on the
many tools that we will be discussing in this When a port is scanned on a server, the port
module. returns a response indicating that the port is open
and a service is listening. In our course Port
Defining Malware Scanning, you will learn how ports can be scanned,
Malware how a hacker can break into your network through
Tools of the Trade the ports, and the countermeasures you can take
Countermeasures to protect your device or network. Our course will
Course Summary offer in-depth discussions on port scanning
methods and techniques, port scanning tools, and
port scanning countermeasures. We will partner
Penetration Testing this with detailed demos on Ping, Ping tester, and
Duration: 60 Minutes Netstat.
Quizzes: 3
Port Scanning
Pentesting is an intentional attack on a system to Advanced Techniques
discover security weaknesses. These can be left
either by the security officer or the security Advanced Exploitation Techniques
controls. Penetration Testing is our course that Duration: 90 Minutes
covers security, vulnerabilities, different types of Quizzes: 3
tests, and when to test as a pen tester. We have
paired this with an in-depth demo on vulnerability Exploit is a common term in the computer security
assessment using the tool Nexpose. At the end of community that refers to a piece of software that
this course we will have reviewed security and takes advantage of a bug or glitch. In our course
vulnerability assessment, and the differences Advanced Exploitation Techniques, you will learn
between automatic and manual testing. what advanced exploitation techniques are and
how you can use them in your penetration testing.
Penetration Testing Introduction You will also learn how to use Metasploit to exploit
Organizational Considerations vulnerabilities. This will be coupled with in-depth
demos on using Metasploit, and other Metasploit
tools, such as, Meterpreter, Armitage, and
Armitage-mimkatz.
Sniffers
Duration: 90 Minutes
Advanced Exploiting Techniques
Quizzes: 3
Penetration Testing
A sniffer is our course where we take a look at Exploits
Network Sniffing. We will be covering the basics of
packet sniffing, ARP cache poisoning, DNS
spoofing, SSL sniffing, VoIP phone calls and sniffing
EH Academy | +1 503 334-3704 12
Certified Ethical Hacker (CEH) & Security+ Training Program
remote desktop connections. This will be coupled Scanning Networks
with demos on Wireshark, ARP poisoning, and Duration: 60 Minutes
XARP. Quizzes: 3
Network Sniffing Network scanning is the scanning of public or
Security Measures private networks to find out which systems are
running, their IP addresses, and which services
they are running. In our course Network Scanning,
Cryptography you will learn techniques for private and public
Duration: 75 Minutes network scanning using various tools.
Accompanied with, in-depth demos and
Traditional cryptography uses a secret key for discussions on how to use Angry IP, Nmap, Hping,
encrypting and decrypting a message. This is also and Zmap network scanners. Through this, you will
known as symmetric keys. In public key learn the steps to network scanning, how to draw
cryptography, the CA creates private and public a network map, and plan an attack accordingly.
keys using the same algorithm, it functions
asymmetrically. In the course Cryptography, you Private and Public Network Scanning
will discuss Public Key Infrastructures, Certificate Using Zmap
Authorities, and Certificate management. We will
combine that with in-depth demos on PKI Hacking Web and App Servers
Installation, Config-complete, CRL, Enroll Duration: 75 Minutes
Certificate, and CA Management. We will discuss Quizzes: 3
the steps to create and manage a public key
infrastructure, and the relationship between public Hacking Web and Application Servers, is a course
key infrastructures and certificate authority, as that will give us a good idea about vulnerabilities
well as both traditional cryptography and public and attacks available for web servers and web
key cryptography, the implementation of applications. This course includes in-depth demos
certificates, and managing certificates. on several of the tools used for hacking web
servers and application servers. These tools
Certificates include Apache2, Netcraft, Website Mirroring,
Using Secure Certificates W3AF, and WMAP. By the end of this course we
will have discussed various ways to collect
information from web servers, application server
attacks, and finding vulnerabilities in a server.
SQL Injections
Duration: 60 Minutes
Quizzes: 3 Web Server Attacks
Web Application Attacks
SQL injection is the most used of all attacks. In this
module, SQL Injections, you will be learning how Buffer Overflows
SQL injections can be initiated, cause damage or Duration: 75 Minutes
loss, prevention against such attacks, and Quizzes: 3
discussing detection tools. This course includes
demos demonstrating the BSQL tool as well as SQL Buffer overflow occurs when you try to store more
Injection Username and Password. By the end of data than what the allocated buffer or storage
this course you will have covered SQL injection area can hold. In this module you will be
methodology, attacks, buffer overflow exploit, introduced to the concepts of buffer overflows,
testing for SQL injection, countermeasures and how they happen, and how attackers take
EH Academy | +1 503 334-3704 13
Certified Ethical Hacker (CEH) & Security+ Training Program
detection tools. advantage of them. You will also learn how to
SQL Injections defend against buffer overflow attacks, and what
Protecting Against SQL Injections security measures you can take to protect your
data. We will accompany this with several demos
that will delve deeper and help you understand
Session Hijacking some of the specific topics that will be discussed.
Duration: 90 Minutes
Quizzes: 3 Buffer Flow
Program and Application Vulnerability
Have you heard the words “session hijacking”? Defense, Countermeasures, and Security
Simply put, it is defined as an intruder taking over
a genuine session between two computers and Hacking Wireless Networks
using if for sinister purposes. In the course Session Duration: 60 Minutes
Hijacking, you will learn details about session Quizzes: 3
hijacking, well-known techniques employed by
aggressors, the steps involved in session hijacking, Wireless attacks have become easy; even unskilled
various types of session hijacking, tools for people with little computer literacy can accomplish
hijacking sessions, ways you can protect them. This is because of the many automated tools
yourselves from session hijacking, and how available to perform this hack. In our course
pentesting can be used to identify vulnerabilities. Hacking Wireless Networks, we will not be
focusing on weaknesses of your wireless networks
Session Hijacking or how to protect them, instead, we will focus on
Countermeasures showing you how to gain access to a wireless
network.
Hacking Wireless Networks
Social Engineering
Duration: 60 Minutes Hacking Windows
Quizzes: 3
Authentication Systems
Social engineering is the art of extorting Duration: 60 Minutes
employees for information. It can be human-based Quizzes: 3
or digital. In our course Social Engineering, you will
learn what social engineering is, who’s at risk, and Whenever we login to a computer system, we
how to protect and educate your employees provide information to identify ourselves. We refer
against social engineering. You will learn the to this as authentication. Authentication has been
importance of creating a security policy, and how developed to contain more than just username
to deal with the threat of human-based attacks and password because we are looking for added
from both outside and inside the company. You layers of security. In this module we will be
will learn what kind of risks computer-based covering authentication factors, forms of
attacks and social media present. We will couple authentication, and authentication protocols. We
this with in-depth demos on phishing email, will also be going over RADIUS, LDAP, and SSO. We
SETwebTemplate, SET-spear phishing, SET-trojan, will pair this with several demos depicting practical
and SET SMS Spoofing. uses of the many tools that we will discuss in this
module.
Social Engineering
Social Engineering Demos Introduction
Authentication Protocols
EH Academy | +1 503 334-3704 14
Certified Ethical Hacker (CEH) & Security+ Training Program
RADIUS, LDAP, and SSQ
Cryptography Weaknesses Cross-Site Scripting
Duration: 75 Minutes Duration: 60 Minutes
Quizzes: 4 Quizzes: 3
Cryptography is the science of writing in secret As a security tester or security analyst, it is
code and is considered an ancient art. The first important that you are aware of cross-site
documented use of cryptography dates back to scripting vulnerabilities and how they may be
circa 1900 B.C. In our course Cryptography exploited by attackers. In our course Cross-Site
Weaknesses, we will discuss weaknesses in Scripting, you will gain a comprehensive
cryptography and ways to improve your security. understanding of cross-site scripting; you will learn
We will also cover the use of symmetric and how to prevent it, and how you can test to identify
asymmetric keys and the use of hybrid keys, as cross-site scripting vulnerabilities. You will also
well as, the use of hashing algorithms and digital learn what cross-site scripting is and what the
signatures. We will pair this with several demos to different types of cross-site scripting you may
show you how each of these works in practical come across. This course will also be paired with
situations. several demos that give you a real world view of
what we have and will cover in this module.
Encryption
Symmetric Encryption Cross-Site Scripting
Asymmetric Encryption Types of Cross-Site Scripting
Hashing Algorithms Preventing Cross-Site Scripting
Digital Signatures
Physical Security
Duration: 75 Minutes
Mobile Hacking Basics Quizzes: 4
Duration: 90 Minutes
What kind of security measures do you take to
Quizzes: 3
protect your facilities, equipment, resources,
Mobile hacking can be anything from searching for personnel, and property from damage caused by
unlocked Wi-Fi networks, to the hacking of unauthorized access? In this module, Physical
Android OS or IOS systems. In our course Mobile Security, these are questions that we will be
Hacking Basics, we will give you a basic answering. You will be learning how to recognize
the potential risks of unauthorized access to your
introduction of the tools and concepts behind
mobile hacking with demos giving you a look at business and personnel, and how to counteract
some of these tools in action. these risks by learning the steps to creating a
security policy for you and your personnel to
implement. We will include demos that will help
Securing Mobile Basics
you better understand the concepts that will be
Mobile Security Considerations
discussed in this module.
Hardening Mobile Devices
Physical Security
Internal Support Systems
Evading Firewalls and Honeypots Perimeter Security
Duration: 75 Minutes Audits, Testing, & Drill
Quizzes: 3
EH Academy | +1 503 334-3704 15
Certified Ethical Hacker (CEH) & Security+ Training Program
Evading Firewalls and Honeypots, is the course Evading IDS
where we will not only discuss what firewalls and Duration: 75 Minutes
honeypots are, but how attackers get around Quizzes: 4
these preventive programs. You will learn about
the different types of firewalls and how they may Intrusion Detection System (IDS) is a device or
be evaded. You will also learn what honeypots are software that monitors network activities and
and how they are set-up to divert any would be system activities. While monitoring, it looks for
attacker’s attention. You will be learning how suspicious activities and security policy violations.
attackers anticipate honeypots and how In this module, Evading IDS, we will be discussing
penetration testing can help you in dealing with the vulnerabilities in an IS, types of IDS, types of
these attackers. We have paired this course with evasion, techniques used to evade IDS, IDS tools,
several demos that will cover more in-depth the and how to carry out penetration testing so you
topics that we will be discussing and help you gain can put a prevention plan in place. We will
a broader understanding of those topics. combine this with an in-depth demo on how to
avoid IDS.
Working with Firewalls
Working with Honeypots Introduction to IDS
Evading IDS
Points of Vulnerability in IDS
Wireless Types and Vulnerabilities De-synchronization
Duration: 75 Minutes Intrusion Detection Tools
Quizzes: 3 IDS Evading Tools
Countermeasures
Wireless types, such as WLAN, are also known as
WiFi networks and they are susceptible to security
lapses that wired networks are exempt from. In
this module you will learn about different wireless
types and their vulnerabilities. You will learn about
several different tools that will help you take
countermeasures against these vulnerabilities. We
will complete this course with demos on different
tools that we will be discussing.
Wireless Authentication
Authentication Systems
EH Academy | +1 503 334-3704 16
Вам также может понравиться
- Complete Tutorial On Hacking Into Paypal AccountsДокумент3 страницыComplete Tutorial On Hacking Into Paypal AccountsfsdfsdfdsdsОценок пока нет
- MSIM 602 Simulation Fundamentals AssignmentДокумент2 страницыMSIM 602 Simulation Fundamentals Assignmentahaque08Оценок пока нет
- Trusted Bank Logs VendorsДокумент5 страницTrusted Bank Logs Vendorstylermoore100% (4)
- Ethical Hacking and Network DefenseДокумент4 страницыEthical Hacking and Network DefenseCristian RamirezОценок пока нет
- Toronto University Cyber PTДокумент14 страницToronto University Cyber PTSahil VarmaОценок пока нет
- Certified Ethical Hacker Cehv12 Course ContentДокумент23 страницыCertified Ethical Hacker Cehv12 Course ContentM3iatОценок пока нет
- Cryptography and Cyber SecurityДокумент162 страницыCryptography and Cyber SecuritycygnusvesaliusОценок пока нет
- Ethical Hacking CourseДокумент22 страницыEthical Hacking CourseDeviLОценок пока нет
- 5 Linux Skills You Must Master To Be A Cybersecurity ProfessionalДокумент1 страница5 Linux Skills You Must Master To Be A Cybersecurity ProfessionalmotojimeОценок пока нет
- TranchulaДокумент6 страницTranchulaTariq ZafarОценок пока нет
- Penetration Testing Concepts Attack Methods DefenseДокумент6 страницPenetration Testing Concepts Attack Methods DefenseDedy HariyadiОценок пока нет
- LCEH Course DescriptionДокумент17 страницLCEH Course DescriptionRedCodeLinuxОценок пока нет
- KALI LINUX: Mastering the Art of Ethical Hacking and Penetration Testing (2023 Guide)От EverandKALI LINUX: Mastering the Art of Ethical Hacking and Penetration Testing (2023 Guide)Оценок пока нет
- Advanced Penetration Testing For Highly-Secured Environments: The Ultimate Security GuideДокумент32 страницыAdvanced Penetration Testing For Highly-Secured Environments: The Ultimate Security Guidejagdevs7234Оценок пока нет
- Lecture 1 HLДокумент43 страницыLecture 1 HLsaparovbek700Оценок пока нет
- Malware Analysis ProfessionalДокумент21 страницаMalware Analysis ProfessionalZeeshan RanaОценок пока нет
- PenTest StarterKit 2013Документ70 страницPenTest StarterKit 2013Albin BajrambasicОценок пока нет
- Cse320 At2Документ12 страницCse320 At2Barnny StinsonОценок пока нет
- Cybersecurity Boot Camp Cybersecurity Boot Camp: The Uoft ScsДокумент14 страницCybersecurity Boot Camp Cybersecurity Boot Camp: The Uoft ScsAmd HОценок пока нет
- Lecture 1 Information Security DesignДокумент55 страницLecture 1 Information Security DesignHùng Hùng Nguyễn NguyễnОценок пока нет
- CSL Module-3Документ23 страницыCSL Module-3Gaurav WankhedeОценок пока нет
- Name: Grade/Score: Year/ Section/ Row #: DateДокумент1 страницаName: Grade/Score: Year/ Section/ Row #: DateLouella Jane Racho MartinezОценок пока нет
- Penetration Testing: An Art of Securing The System (Using Kali Linux)Документ8 страницPenetration Testing: An Art of Securing The System (Using Kali Linux)Carolus GazaОценок пока нет
- Cyber Security Specialist: Live InstructionДокумент1 страницаCyber Security Specialist: Live InstructionNkikaОценок пока нет
- Cehv9 BrochureДокумент11 страницCehv9 BrochureAyahnyaAzkaAzmiОценок пока нет
- Certified Ethical Hacking: Ron Woerner, CISSP, CEHДокумент35 страницCertified Ethical Hacking: Ron Woerner, CISSP, CEHranjithc24Оценок пока нет
- Cybersecurity Boot Camp: Arizona State UniversityДокумент13 страницCybersecurity Boot Camp: Arizona State UniversityKrishna JandhyalaОценок пока нет
- Practical Malware Analysis Based On SandboxingДокумент6 страницPractical Malware Analysis Based On SandboxingHamza sultanОценок пока нет
- Kali Linux Advanced Methods and Strategies To Learn Kali Linux (BooxRack)Документ110 страницKali Linux Advanced Methods and Strategies To Learn Kali Linux (BooxRack)Carlos Mayorga100% (2)
- Network Security Master Thesis PDFДокумент6 страницNetwork Security Master Thesis PDFallisonschadedesmoines100% (2)
- Cyber Security at SeaДокумент30 страницCyber Security at SeaJoseph GraciousОценок пока нет
- Cert Exercises HandbookДокумент88 страницCert Exercises HandbookDaniel Checchia100% (1)
- كتاب الهكر الأخلاقي PDFДокумент188 страницكتاب الهكر الأخلاقي PDFoussama100% (1)
- Acker Attack Techniques and Tactics: Understanding Hacking StrategiesДокумент14 страницAcker Attack Techniques and Tactics: Understanding Hacking Strategiesplotinus63Оценок пока нет
- STДокумент5 страницSTJinto Thomas KidangattilОценок пока нет
- Secured Authentication Using 3D Password by Applying Ultimate Planar AlgorithmДокумент46 страницSecured Authentication Using 3D Password by Applying Ultimate Planar AlgorithmSoumya Sambit100% (1)
- Cyber Hacker Project 1Документ17 страницCyber Hacker Project 1Jai ShreeramОценок пока нет
- Certified Ethical Hacker v9Документ9 страницCertified Ethical Hacker v9JJ Asonyer100% (1)
- Cehv9 Brochure PDFДокумент11 страницCehv9 Brochure PDFMuhammad AliОценок пока нет
- Practical Linux Security Cookbook - Sample ChapterДокумент25 страницPractical Linux Security Cookbook - Sample ChapterPackt Publishing100% (1)
- CEHday 1Документ121 страницаCEHday 1Yo YoОценок пока нет
- Linux Hardening PDFДокумент4 страницыLinux Hardening PDFAnoopОценок пока нет
- Nostarch Wintersampler 2018 EbookДокумент40 страницNostarch Wintersampler 2018 EbookAlvaro GenettiОценок пока нет
- CEHДокумент5 страницCEHanil0% (1)
- Cyberthreya Elite MasteryДокумент17 страницCyberthreya Elite MasteryPa1Оценок пока нет
- Ethical HackingДокумент3 страницыEthical Hackingpandeyshourya000Оценок пока нет
- CU CybersecurityДокумент4 страницыCU CybersecurityAugustus CaesarОценок пока нет
- Secure SystemДокумент3 страницыSecure Systemfareehaali4560Оценок пока нет
- CO 405 Internet Security Lab ReportДокумент27 страницCO 405 Internet Security Lab ReportUtkarshPrasad100% (1)
- Module 01 RealAttackScenarioДокумент49 страницModule 01 RealAttackScenarioAyad KamaliОценок пока нет
- Welcome This Comprehensive Ethical Hacking CourseДокумент7 страницWelcome This Comprehensive Ethical Hacking CoursevarshaОценок пока нет
- Portals 0 Images CEH-brochureДокумент12 страницPortals 0 Images CEH-brochureAnOop KaUshalОценок пока нет
- SEC401 Course OutlineДокумент28 страницSEC401 Course OutlinebbbbОценок пока нет
- Top 30+ Ethical Hacking Tools and Software For 2022Документ20 страницTop 30+ Ethical Hacking Tools and Software For 2022popzy malikОценок пока нет
- Ethical Hacking Proactive TrainingДокумент16 страницEthical Hacking Proactive TrainingMarcelo JuniorОценок пока нет
- CEH-Certified Ethical Hacker: Required PrerequisitesДокумент3 страницыCEH-Certified Ethical Hacker: Required PrerequisitessenejaniОценок пока нет
- SECURITY DOC'mДокумент26 страницSECURITY DOC'mvinod kapateОценок пока нет
- 100 Best Ethical Hacking Tools - 2023 (New List)Документ28 страниц100 Best Ethical Hacking Tools - 2023 (New List)PAUL VINCENT FAJARDO100% (1)
- What Does Infosec Mean? Infosec Refers To The Protection of Data ResourcesДокумент18 страницWhat Does Infosec Mean? Infosec Refers To The Protection of Data ResourcesGilgamesh berserkerОценок пока нет
- Red Team TrainingДокумент16 страницRed Team TrainingFernando da Costa CorreaОценок пока нет
- Lesson 3 Information Systems Security ManagementДокумент6 страницLesson 3 Information Systems Security ManagementkariukipolyОценок пока нет
- Learn Penetration Testing with Python 3.x: Perform Offensive Pentesting and Prepare Red Teaming to Prevent Network Attacks and Web Vulnerabilities (English Edition)От EverandLearn Penetration Testing with Python 3.x: Perform Offensive Pentesting and Prepare Red Teaming to Prevent Network Attacks and Web Vulnerabilities (English Edition)Рейтинг: 5 из 5 звезд5/5 (1)
- Become An Ethical Hacker That Can Hack Computer Systems And Secure Them Like Security ExpertsОт EverandBecome An Ethical Hacker That Can Hack Computer Systems And Secure Them Like Security ExpertsОценок пока нет
- Voting Smart Contract with DelegationДокумент22 страницыVoting Smart Contract with Delegationahaque08Оценок пока нет
- 04568517Документ6 страниц04568517ahaque08Оценок пока нет
- Cochet Terrasson98numerical PDFДокумент7 страницCochet Terrasson98numerical PDFahaque08Оценок пока нет
- Lecture1-IntroductionToCPS 0 PDFДокумент50 страницLecture1-IntroductionToCPS 0 PDFahaque08Оценок пока нет
- Cyber-Physical Systems From Theory To Practice - (Section VII - Sensors and Applications)Документ56 страницCyber-Physical Systems From Theory To Practice - (Section VII - Sensors and Applications)ahaque08Оценок пока нет
- Protecting Critical Infrastructure by Identifying Pathways of Exposure To RiskДокумент7 страницProtecting Critical Infrastructure by Identifying Pathways of Exposure To Riskahaque08Оценок пока нет
- Sample Recommendation LetterДокумент2 страницыSample Recommendation LetterJeemCarloFagelaPula100% (1)
- Software Defined Network Defense PDFДокумент64 страницыSoftware Defined Network Defense PDFahaque08Оценок пока нет
- Thesis Draft PDFДокумент191 страницаThesis Draft PDFahaque08Оценок пока нет
- International Flow of FundsДокумент42 страницыInternational Flow of FundsIrfan Baloch100% (1)
- EncryptionДокумент7 страницEncryptionRicardo Gómez ParedesОценок пока нет
- Multinational Financial Management: An Overview: South-Western/Thomson Learning © 2003Документ30 страницMultinational Financial Management: An Overview: South-Western/Thomson Learning © 2003Nafisa Afsana TaskiaОценок пока нет
- Multinational Cost of Capital & Capital Structure: South-Western/Thomson Learning © 2003Документ21 страницаMultinational Cost of Capital & Capital Structure: South-Western/Thomson Learning © 2003ahaque08Оценок пока нет
- Nova-Eco Develops 300MW Wind Project in UkraineДокумент7 страницNova-Eco Develops 300MW Wind Project in Ukraineahaque08Оценок пока нет
- Public Hospital Service QualityДокумент8 страницPublic Hospital Service Qualityahaque08Оценок пока нет
- Social Media ReportДокумент23 страницыSocial Media Reportahaque08Оценок пока нет
- PRINCE2 White Paper v3Документ4 страницыPRINCE2 White Paper v3ahaque08Оценок пока нет
- The Beauty of Stealing Internet - "Broadband Theft": Article Published On NW3C Informant MagazineДокумент5 страницThe Beauty of Stealing Internet - "Broadband Theft": Article Published On NW3C Informant MagazineNoorSoormallyОценок пока нет
- LivrosДокумент2 страницыLivrosLucas CardealОценок пока нет
- LESSON 1 Digital Security RisksДокумент17 страницLESSON 1 Digital Security Riskskrisaltheagazmenrafanan49Оценок пока нет
- Red Hat Enterprise Linux 6 Security Guide en USДокумент227 страницRed Hat Enterprise Linux 6 Security Guide en USAlejandro Henao MuñozОценок пока нет
- Professional and Social Issues Module1Документ50 страницProfessional and Social Issues Module1El JahrisonОценок пока нет
- CEH Sample Questions - Vamsi Krishna PDFДокумент7 страницCEH Sample Questions - Vamsi Krishna PDFvamsi krishnaОценок пока нет
- Types of Cyber CrimeДокумент22 страницыTypes of Cyber CrimeHina Aswani100% (1)
- Top 9 Certifications by SimplilearnДокумент31 страницаTop 9 Certifications by Simplilearncrustaceanzx100% (1)
- Know Your Enemy - Holt and Kilger - KYE - The Social Dynamics of HackingДокумент17 страницKnow Your Enemy - Holt and Kilger - KYE - The Social Dynamics of Hackingzakharia1Оценок пока нет
- Top 10 Most Notorious Hackers and Data Security RisksДокумент1 страницаTop 10 Most Notorious Hackers and Data Security RisksRishika Sharma SardiОценок пока нет
- Character Sheet and PrimerДокумент9 страницCharacter Sheet and PrimerBarbie TuricОценок пока нет
- Chapter 8Документ9 страницChapter 8mad maranОценок пока нет
- ECC - Cyber Brief April 2023Документ14 страницECC - Cyber Brief April 2023Ri VMОценок пока нет
- Crime and PuzzlementДокумент15 страницCrime and PuzzlementmonsterbobbyОценок пока нет
- Ethical HackingДокумент51 страницаEthical HackingAslam RecoveryОценок пока нет
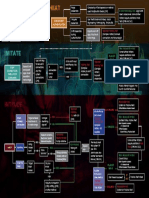
- EP2 Hacking FlowchartДокумент1 страницаEP2 Hacking FlowchartLars LawrensonОценок пока нет
- Master PackДокумент12 страницMaster PackAnsh SainiОценок пока нет
- Cyberguruajinkya: Ethical Hacker - CHFI - LPT - Josh Talk Speaker - Speaker - PodcasterДокумент24 страницыCyberguruajinkya: Ethical Hacker - CHFI - LPT - Josh Talk Speaker - Speaker - PodcasterDaksh PatwalОценок пока нет
- CYBER Crime & Security: BY:-Aditi GuptaДокумент16 страницCYBER Crime & Security: BY:-Aditi GuptaAditi Gupta100% (1)
- Cehv10 Version Change DocumentДокумент62 страницыCehv10 Version Change DocumentVijay GopalОценок пока нет
- 16Документ15 страниц16Rishab ChoubeyОценок пока нет
- Securing Information SystemsДокумент19 страницSecuring Information SystemsArbab AshrafОценок пока нет
- Chapter 6 Computer and Network SecurityДокумент56 страницChapter 6 Computer and Network SecurityHohes Opoil100% (1)
- Hacker2 Introduction Guide for Scanning, Cracking and Hacking NetworksДокумент7 страницHacker2 Introduction Guide for Scanning, Cracking and Hacking NetworksСлободан УрдовскиОценок пока нет
- CYREX - Application Security - Service DeckДокумент12 страницCYREX - Application Security - Service DeckJ Israel ToledoОценок пока нет
- II. Samle Analysis 1. Problem - SolutionДокумент6 страницII. Samle Analysis 1. Problem - Solutionly_narci380Оценок пока нет
- Web Application Hacking & Security Program GuideДокумент10 страницWeb Application Hacking & Security Program GuideZubair ChОценок пока нет