Академический Документы
Профессиональный Документы
Культура Документы
Embedded Systems Design - 2ed - 0750655461
Загружено:
Jabang Aru SaputroАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Embedded Systems Design - 2ed - 0750655461
Загружено:
Jabang Aru SaputroАвторское право:
Доступные форматы
Journal of Computer Science 2012, 8 (11), 1834-1838
ISSN 1549-3636
© 2012 Science Publications
doi:10.3844/jcssp.2012.1834.1838 Published Online 8 (11) 2012 (http://www.thescipub.com/jcs.toc)
Classification of Attacks on Embedded Systems
1
Noura Ouerdi, 1M’hammed Ziane, 1Abdelmalek Azizi and 2Mostafa Azizi
1
Department of Mathematical and Computer, Lab. ACSA, Faculty of Sciences,
Mohammed First University, Oujda, Morocco
2
Department of Computer, Lab. MATSI, ESTO, Mohammed First University,
ENSAO BP 669 Complexes Universities Al Qods Oujda 60000, Oujda, Morocco
Received 2012-06-13, Revised 2012-07-20; Accepted 2012-08-07
ABSTRACT
The current growth of the number of Embedded Systems (ES) and their use in sensitive systems attract the
attention of attackers. They are exposed to real threats and incur significant risks especially when they are
involved in specific military or industrial systems. It is important to study the subject from different angles
to understand, predict and learn how to protect our products against these attacks. So, evaluators of
Embedded Systems (ES) need to organize structure and classify attacks in order to choose the relevant test
sets. To do this, we propose a new classification of attacks on Embedded Systems, based on Classification
Tree Method (CTM). As a result, thanks to our proposal, we were able to classify the various attacks en
Embedded Systems (ES) to generate test cases automatically and usually select the relevant test cases. This
allows to properly evaluate Embedded Systems (ES) especially since this type of system is very critical and
requires a systematic evaluation.
Keywords: Embedded System (ES), Attack, Classification Tree Method (CTM), Security
1. INTRODUCTION systematic and also allows the selection of attack test
cases via Classification Tree Editor (CTE) tool.
An ES is a small specialized system computer, The remainder of this article is organized as follows:
which is completely encapsulated in a device. The First, we present materials and methods where we treat
security of this type of system is a common topic and the old taxonomies. Then, we analyze these old
this can quickly become a problem, even bigger than the classifications and we propose, as result, our new
computer’s security. One reason for the lack of security is classification based on CTM method. Finally, we
the constraint of hardware devices in the application of conclude the article.
security measures. For instance, a mal-packet can exploit
memory-related vulnerabilities and use existing 2. MATERIALS AND METHODS
application code in a sensor without disrupting the
sensor’s functionality (Gu et al., 2011). The other reason According to (Bishop, 1995), six factors are used to
is the cost of security. So the question is: how to classify the attacks:
effectively test and be sure that the ES behaves correctly? • Nature: The nature of the vulnerability
A trivial solution is to construct representative and • Timing: When the vulnerability was introduced
meaningful classifications for all attacks. The idea is to • Area of operation: What is gained through the
reduce considerably the possible cases by constructing exploitation
classes of attacks so that the test will take one element of • Effect: Which can be affected by the vulnerability
each class. To improve verification techniques, we • The minimum number of components required to
propose in the following new classification based on exploit this vulnerability
CTM. This classification makes the evaluation of ES more • Source of the vulnerability
Corresponding Author: Noura Ouerdi, Department of Mathematical and Computer, Lab. ACSA, Faculty of Sciences,
Mohammed First University, Oujda, Morocco
Science Publications 1834 JCS
Noura Ouerdi et al. / Journal of Computer Science 8 (11) (2012) 1834-1838
In his classification, Bishop focused more on
vulnerabilities rather than attacks themselves which is
not the goal of taxonomy. However, it presents a good
background for proposing a new taxonomy.
Howard (1997) presents a taxonomy which takes
into the motivation and objectives of the attacker. This
taxonomy consists of five steps:
• The attacker: Who can launch an attack
• Tools used by the attacker to access the system
• Access to the system by exploiting the design,
implementation or configuration of the system
• The result
• The objectives of the attacker
Howard was interested to the process of an attack
from the first step “attackers” to the last one “objectives”
and not to the attack.
Lough (2001) has proposed a new taxonomy called
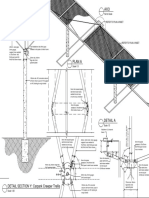
Fig. 1. Taxonomy of Ravi
Validation Exposure Randomness Deallocation Improper
Conditions Taxonomy (VERDICT) (Lough, 2001) which For these reasons, we thought of a new classification
is based on the characteristics of attacks: based on the classification Tree. The main goal is to
• Improper validation: Incorrect validation results provide ES test cases that are relevant and representative
• Improper exposure of different attacks.
• Improper randomness 2.2. New Classification based on Classification
• Improper deallocation: When the information is not Tree Method (CTM)
properly deleted
Classification trees have been introduced in the early
In majority, Lough’s taxonomy is general and does
90s by Grimm and Grochtmann for presentation of test
not include attacks in term of worms, viruses, Trojans. In
cases (Grochtmann et al., 1995). The construction of
addition to attacks in terms of time that are crucial for
classification trees is implemented by the CTM method
real time systems.
The classification of (Ravi et al., 2004) depends on which is derived from the Category Partition Method
the objective and the method used by attacks. Attacks are method (CPM) (Ostrand and Balcer, 1988). The CTM
classified into four categories based on the final goal of provides a formal method to represent test cases
the attack (Grochtmann et al., 1995): Cloning, graphically. It can be used to transform the specifications
Theft-of- Service, Spoofing and Feature unlocking. The of a problem to a set of test cases.
second level of classification is the functional objective of The test execution is a crucial step in the process of
the attack. There are attacks against privacy; attacks against a system developing. However, the planning of these
integrity and attacks against availability. The third level of tests often raises the same questions:
classification is based on the method used to execute the
• What is the number of test cases to run
attack, i.e., physical, side-channel and software attacks. The
Fig. 1 describes the Ravi’s classification. • How can we avoid applying the same tests (same
Ravi considers the vision of the attacker and not that class)
of ES. Such approaches often ignore some important • How testers know that the test case is relevant
features of the attacks, as seen by system administrators. Everyone can confront these issues and it would be
2.1. Analysis of Older Taxonomies interesting to know that the CTM method answers to all
these questions. Indeed, it offers a systematic procedure
The older taxonomies are not really suitable for the to create test cases specific to the problem.
assessment of ES security. The reasons can be broadly The basic idea of the CTM method is to ignore the
summarized in the following points (Ravi et al., 2004): test data and to separate the input domain of the test
• They usually consider the vision of the attacker and into distinct subsets (called class) according to the
his objectives aspects considered relevant by the tester. Then, the
• They are not accompanied by selection and test cases are generated by combining classes of
generation of test cases different classifications.
Science Publications 1835 JCS
Noura Ouerdi et al. / Journal of Computer Science 8 (11) (2012) 1834-1838
2.3. Classification Tree Editor (CTE) Tool • Action: An action performed by an attack can be
execution of a command, de-packaging, probing or
CTE tool is based on CTM method. It supports use of electromagnetic fields
systematic test case determination for software testing, • Network: This mean concerns the four layers:
verification and reliability (Grochtmann and Grimm, 1993). Application, logical, transport and network layer
CTE tool provides a friendly and easy interface that • Target: It may cover the hardware or software
allows you to draw the tree based on class, classification • Hardware: An attack can target the various system
or composition. Once the tree is created, it is possible to components including memory, CPU, input/output
generate test cases automatically, just type the rule in the control units and clock. Since an ES is a real time
“Test case Generator Editor” window and Test case system. Therefore, a simple clock delay can cause a
group will be generated in higher quality and in system malfunction. This is the case of systems
reduced time. Therefore the final interface will contain embedded in planes, satellites
the tree drawn in the middle of the interface. Below the • Software: The attack can be related to the IP
window, you will have the list of generated test cases. address, denial of service or Operating Systeml
Despite CTE tool is easy application, it is • Source of the attack (Remote or local)
exceptionally helpful in analyzing and verification of • Privilege: We distinguished four privilege classes
the system. It is successfully used in various domains aimed by the attacker. The ”root”,”user”,”system”
especially in safety and security area like Intrusion and “none” privilege
Detection Systems (IDS) verification process • Vulnerability: The exploited vulnerabilities are
(Gadelrab et al., 2007). related to configuration, implementation or design;
In this study, we exploit the usability of CTE editor
In what follows, we use this classification to present
to analyze ES and generate appropriate test cases.
a simple approach for selecting test cases. For this
objective, we propose to use the CTM method.
3. RESULTS
The complexity of ES consisting of hardware and 4. DISCUSSION
software is increasing and it poses a challenge in
verifying their correctness. Then, to be sure that the ES We can note by CTM/ES, the classification tree
works correctly, the evaluators must test the system specific to ES (Krupp and Muller, 2009). The
regularly, hence the need for automating the generation classification tree has several advantages. First, the
of test cases. To do this, it was first necessary to identification of all possible test cases and the selection
determine the dimensions of an attack on ES. of relevant test cases are done in a systematic manner,
Indeed, by analyzing the previous taxonomies which makes easier its management and helps to reduce
including the taxonomy of attacks on Intrusion Detection or eliminate certain errors. Moreover, its graphical
System (Gadelrab et al., 2007), we were required to representation improves visualization and facilitates
adapt it to the ES. Therefore, we have defined different communication between people who build the
dimensions such as time since the ES is a real time specification, both who are involved in developing and
system. We also took into account the attacks in terms of who manage the testing. To do this, we use the CTE tool.
analyzing of energy consumption. Thus, from our new classification, we generate all
Our classification is based on five dimensions. possible combinations of subclasses using the CTE tool.
These dimensions are: These combinations represent test cases for possible attacks.
More precisely, the CTE offers a simple and powerful
• Means by which the attack was carried out; here, the formalism for constraints expression by combining some
means can be rules which include some sub-ones. Between brackets
• Consumption: This dimension is taken into account (under a predicting form), some connectors such as:
by the covert channels. In this case, the attacker
makes observations of system behavior in terms of • and (*)
energy consumption and execution time for detecting • or (+)
information. Indeed, the particularity of an ES is that • no (NOT)
the analysis of its execution time or its power We propose a rule which represents Physical Attacks:
consumption may help the attacker to find the
information. If we take as example the smart card, the Local * ( CPU + Clock ) * Privilege _ None * (De − packaging
card consumption depends on the values manipulated
by the card (Giraud, 2007) + Probing) * ( Design + Implementation )
Science Publications 1836 JCS
Noura Ouerdi et al. / Journal of Computer Science 8 (11) (2012) 1834-1838
Fig. 2. Classification tree of ES attacks and generated test cases via CTE
Science Publications 1837 JCS
Noura Ouerdi et al. / Journal of Computer Science 8 (11) (2012) 1834-1838
With this rule, we have eight test cases, generated Gadelrab, M.S., A.A. El Kalam and Y. Deswarte, 2007.
automatically (Fig. 2). Defining categories to select representative attack
We can propose rules for other attacks like covert test-cases. Proceedings of the 2007 ACM Workshop
channels: on 5 Quality of Protection, (QoP’ 07), ACM Press,
USA., pp: 40-42. DOI: 10.1145/1314257.1314270
( Local + Remote ) * ( I / O control Units + Clock ) Giraud, C., 2007. Attacks against cryptosystems and
* ( Admin + System ) * ( Transport L. + Network L.) board-related measures. Ph.D Thesis, Superior
* ( Probing + Electromagnetic _ fields ) * Normal School, University of Versailles Saint-
Quentin-en-Yvelines, Paris, France.
(Power + Executiontime) *
Grand, J., 2004. Practical secure hardware design for
( Design + implementation + configuration ) embedded systems. Proceedings of the 2004
Embedded Systems Conference, Mar. 29-Apr. 1,
With this complex rule, we have generated one San Francisco, California.
hundred ninety-two test cases. Grochtmann, M. and K. Grimm, 1993. Classification
Now, we are able to generate test cases
trees for partition testing. Software Test. Verific.
automatically in order to test our ES against potential
Reliab., 3: 63-82. DOI: 10.1002/stvr.4370030203
attacks. Simply, we should determine the generation rule
from the tree and the rest will be made by the CTE tool. Grochtmann, M., J. Wegener and K. Grimm, 1995. Test
case design using classification trees and the
5. CONCLUSION classification-tree editor CTE. Proceedings of the
8th International Software Quality Week, (ISQE’
This study presents two approaches for improving 95), pp: 1-11.
the ES evaluation process: Gu, Q., C. Ferguson and R. Noorani, 2011. A study of
• A systematic method of generating test cases self-propagating mal-packets in sensor networks:
• Selecting test cases based on an appropriate attacks Attacks and defenses. Comput. Security, 30: 13-27.
classification DOI: 10.1016/j.cose.2010.10.002
Howard, J.D., 1997. An analysis of security incidents on
We can, thus, have a better knowledge of space the internet 1989e1995. Ph.D Thesis, Carnegie
attacks and improve our understanding of attack Mellon University.
instances, including the most recent and therefore have a Krupp, A. and W. Muller, 2009. Systematic model-in-
security level conditioned by the verification phase. the-loop test of embedded control systems. IFIP
Regarding the design phase, usually, the security of Adv. Inform. Commun. Technol.
ES is not taken into account in an earlier stage and it is
Lough, D.L., 2001. A taxonomy of computer attacks
difficult to implement it once the product is achieved.
Security must be integrated into the product during the with applications to wireless networks. Ph.D Thesis,
design phase (Design for Security). However, the Virginia Polytechnic Institute and State University.
implementation of security measures is not enough. It Ostrand, T.J. and M.J. Balcer, 1988. The category-
must also verify the effectiveness of these measures and partition method for specifying and generating
check hidden threats. The product must be regularly fuctional tests. Commun. ACM, 31: 676-686. DOI:
monitored and updated to have the greatest impact 10.1145/62959.62964
against attacks. In addition, the security measures should Ravi, S., A. Raghunathan and S. Chakradhar, 2004.
be taken upon detection of a problem (Grand, 2004). In Tamper resistance mechanisms for secure embedded
the same context, (Weingart, 2000) describes the various systems. Proceedings of the 17th Internatioanal
mechanisms ranging from the easiest and cheapest to the Conference of VLSI Design, (VLSID’ 04), IEEE
most difficult and extremely expensive. To conclude, the Xplore Press, pp: 605-611. DOI:
definition of new methodologies for safety assessment, 10.1109/ICVD.2004.1260985
which takes into account the changing of security nature, Weingart, S.H., 2000. Physical security devices for
could ensure security of our products. computer subsystems: A survey of attacks and
6. REFERENCES defences. Proceedings of the 2nd International
Workshop on Cryptografic Hardware and Embedded
Bishop, M., 1995. A taxonomy of UNIX system and Systems, (CHES’ 00), ACM Press, London, pp:
network vulnerabilities. University of California at 302-317.
Davis, Davis, CA.
Science Publications 1838 JCS
Вам также может понравиться
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- GT Radial Indonesia - Partner OEMДокумент2 страницыGT Radial Indonesia - Partner OEMJabang Aru SaputroОценок пока нет
- Learning Drone-Control Actions in Surveillance Videos: Sunyoung Cho, Dae Hoe Kim, Yong Woon ParkДокумент4 страницыLearning Drone-Control Actions in Surveillance Videos: Sunyoung Cho, Dae Hoe Kim, Yong Woon ParkJabang Aru SaputroОценок пока нет
- Drones For PentestingДокумент34 страницыDrones For PentestingJabang Aru SaputroОценок пока нет
- Govindan2018 Article AHardwareTrojanAttackOnFPGA-BaДокумент15 страницGovindan2018 Article AHardwareTrojanAttackOnFPGA-BaJabang Aru SaputroОценок пока нет
- Modul Praktikum NmapДокумент31 страницаModul Praktikum NmapJabang Aru SaputroОценок пока нет
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- Nestlé CASEДокумент3 страницыNestlé CASEAli Iqbal CheemaОценок пока нет
- Student Exploration: Digestive System: Food Inio Simple Nutrien/oДокумент9 страницStudent Exploration: Digestive System: Food Inio Simple Nutrien/oAshantiОценок пока нет
- Manual: Functional SafetyДокумент24 страницыManual: Functional SafetymhaioocОценок пока нет
- Homework 1Документ8 страницHomework 1Yooncheul JeungОценок пока нет
- College of Computer Science Software DepartmentДокумент4 страницыCollege of Computer Science Software DepartmentRommel L. DorinОценок пока нет
- LM2TB8 2018 (Online)Документ252 страницыLM2TB8 2018 (Online)SandhirОценок пока нет
- Benko Gambit-Jacobs and Kinsman, 1999Документ163 страницыBenko Gambit-Jacobs and Kinsman, 1999johnson Greker100% (3)
- Unit 4Документ15 страницUnit 4David Lopez LaraОценок пока нет
- Digital SLR AstrophotographyДокумент366 страницDigital SLR AstrophotographyPier Paolo GiacomoniОценок пока нет
- CV ChristianДокумент2 страницыCV ChristianAlya ForeferОценок пока нет
- MECANISMOS de Metais de TransicaoДокумент36 страницMECANISMOS de Metais de TransicaoJoão BarbosaОценок пока нет
- Lesson: The Averys Have Been Living in New York Since The Late NinetiesДокумент1 страницаLesson: The Averys Have Been Living in New York Since The Late NinetiesLinea SKDОценок пока нет
- Revit 2023 Architecture FudamentalДокумент52 страницыRevit 2023 Architecture FudamentalTrung Kiên TrầnОценок пока нет
- Fmicb 10 02876Документ11 страницFmicb 10 02876Angeles SuarezОценок пока нет
- De DusterДокумент6 страницDe DusterArstОценок пока нет
- Tree PruningДокумент15 страницTree Pruningrita44Оценок пока нет
- NHM Thane Recruitment 2022 For 280 PostsДокумент9 страницNHM Thane Recruitment 2022 For 280 PostsDr.kailas Gaikwad , MO UPHC Turbhe NMMCОценок пока нет
- Topic Group Present (Week 8) Chapter 1:sociology and Learning ManagementДокумент2 страницыTopic Group Present (Week 8) Chapter 1:sociology and Learning ManagementLEE LEE LAUОценок пока нет
- Asus Test ReportДокумент4 страницыAsus Test ReportFerry RiantoОценок пока нет
- Department of Education: Income Generating ProjectДокумент5 страницDepartment of Education: Income Generating ProjectMary Ann CorpuzОценок пока нет
- 100 20210811 ICOPH 2021 Abstract BookДокумент186 страниц100 20210811 ICOPH 2021 Abstract Bookwafiq alibabaОценок пока нет
- Personal Finance Kapoor 11th Edition Solutions ManualДокумент26 страницPersonal Finance Kapoor 11th Edition Solutions Manualsiennamurielhlhk100% (28)
- Vernacular ArchitectureДокумент4 страницыVernacular ArchitectureSakthiPriya NacchinarkiniyanОценок пока нет
- Geotechnical Aspects of Open Stope Design at BHP Cannington: G C StreetonДокумент7 страницGeotechnical Aspects of Open Stope Design at BHP Cannington: G C StreetonJuan PerezОценок пока нет
- Antibiotics MCQsДокумент4 страницыAntibiotics MCQsPh Israa KadhimОценок пока нет
- Eu Schengen Catalogue enДокумент54 страницыEu Schengen Catalogue enSorin din ConstanțaОценок пока нет
- TrellisДокумент1 страницаTrellisCayenne LightenОценок пока нет
- FAO-Assessment of Freshwater Fish Seed Resources For Sistainable AquacultureДокумент669 страницFAO-Assessment of Freshwater Fish Seed Resources For Sistainable AquacultureCIO-CIO100% (2)
- Ideal Gas Law Lesson Plan FinalДокумент5 страницIdeal Gas Law Lesson Plan FinalLonel SisonОценок пока нет