Академический Документы
Профессиональный Документы
Культура Документы
PC Networking Level 5
Загружено:
pavanraniИсходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
PC Networking Level 5
Загружено:
pavanraniАвторское право:
Доступные форматы
PC NETWORKING Level 5
- An Introduction to PC Networking.
© Copyright by CTF Services Limited 2005
All rights reserved worldwide. No part of this book may be reproduced or transmitted in
any form, or by any means, electronic or mechanical, including photocopying, recording,
or by any information storage and retrieval system, without the written permission of the
publisher, except where permitted by law.
Published by
CTF Services Limited, 19 Regent St, Timaru 8601, New Zealand
Distributed by
www.ebooksctf.co.nz
PC Networking Level 5.doc 1
PC NETWORKING Level 5
– An Introduction to PC Networking.
PREFACE.
Welcome to the exciting world of PC Networking. This is a huge growth area
worldwide.
I hope you enjoy doing this course, and will want to learn more after you finish.
This course is arranged as follows:
Four Theory Chapters
USE the Bookmarks and Thumbnails to help you to navigate this pdf document.
Please E-Mail us if you have any questions or comments.
Our E-Mail address is ctf77@xtra.co.nz
Please include (where possible) the Course Name and the Page Number (these
can be found on the footer of each page)
Enjoy the journey. We look forward to your continual success.
PC Networking Level 5.doc 2
CONTENTS.
CHAPTER ONE INTRODUCTION to LANs
Why Network?
Definitions
Types of Network
Cabling and Topologies
Media Access Control
CHAPTER TWO LAN STANDARDS
A Network Model
Network Operating Systems
Hardware and Peripherals
The Network Interface Card
Interconnection
Class Exercise
CHAPTER THREE LAN STRATEGIES
Server Based LANs
Peer-to-Peer Networking
Client / Server Computing
Overview of Network Management
CHAPTER FOUR. PROTOCOLS, STANDARDS and INTERCONNECTION
Protocols
IEEE 802 Standards
Links between LANs
Repeaters, Bridges and Routers
THIS COURSE SHOULD BE COMBINED WITH:
a) “PC NETWORKING PRACTICAL EXERCISES” and
b) “Network + (2005)”
PC Networking Level 5.doc 3
Majestic Mt Aoraki is an awe inspiring site.
My pledge to my students:
To help you with your “Learning Climb” which is like scaling the heights of
Mt Aoraki.
There are times when you will be stretched beyond your comfort zone,
and there will be other days when the upward journey seems difficult (just
like bad weather on the mountain).
Aoraki is not the easiest challenge.
There are many easier, but less rewarding climbs.
Remember the words of Winston Churchill –
"Never, ever give up."
If you are willing to learn, and willing to work, then I am willing to
be your guide in your learning climb.
The view from the peak is even more awe inspiring than the view from the lake.
One day, you will reach the top, if you follow the right path, and have the right
self belief.
Nick Thorne
Director of CTF Services
PC Networking Level 5.doc 4
CHAPTER ONE.
INTRODUCTION to LANs.
A. WHY NETWORK?
B. DEFINITIONS.
C. TYPES of NETWORK.
D. CABLING and TOPOLOGIES.
E. MEDIA ACCESS CONTROL.
PC Networking Level 5.doc 5
A. WHY NETWORK?
Networking is one of the biggest growth areas in the computing world -
there is a real shortage of experts in the area.
A network is a system of interconnection between computers that allows them to
share facilities. Typically, these facilities might be printers, disk space and
software. A Network allows different users to communicate, and to pass data
from one Network Resource to another.
It makes sense for a group of users to share an expensive item, such as a colour
Laser Printer. Even to share a colour laser between a group could mean that the
total printing cost is less than if each individual had a colour dot matrix -- and the
quality of the output would be a lot better.
Typically, a Network will consist of any number of terminal devices (intelligent
work stations such as IBM compatible PCs, or “dumb” terminals) connected to a
large processor, which contains most of the software needed for operation. The
large processor containing most of the software is called the File Server. The
devices attached to the file server are called Workstations.
Networking allows us to get good use out of our resources for all our users.
When you have just one computer, what you have loaded on that computer is all
you have access to. To transfer data from one computer to another, data must
be copied to a backup device, and then copied from the backup device to the
second computer. This can be cumbersome and time consuming.
If the computers were linked, transfer of data would be easier.
The basic reasons why computers are networked are:
To share resources such as files, printers, modems and fax machines
To share application software e.g. 10 Workstations share MS Office, rather
than have 10 individual licences
To increase productivity (make it easier to share data among users)
PC Networking Level 5.doc 6
Imagine a Small Business office in which a number of users all require access to
common information. If the users’ computers are connected via a network, they
can share files, exchange mail, schedule meetings, send faxes and print
documents all from any point in the network.
It would not be necessary for users to transfer files via floppy disk, electronic
mail, hard copy or any other format. Each user could access the information they
needed. Less time would be wasted, and productivity would be improved.
PC Networking Level 5.doc 7
B. DEFINITIONS.
A computer network is a communications system connecting two or more
computers together to exchange information and share resources.
Reasons to network may include:
Internal electronic mail
centralized file storage
sharing files (you can get access
(if permitted!) to other's files
without having to use floppy disks
for transfer)
sharing applications (you may
have access to a larger range of
software than you would have on
your own hard disk)
relative ease in adding new
software
sharing printers and other
hardware such as DVD drives,
modems and disk drives
central management including
security and backups
to provide a gateway to the
internet
GROUP ACTIVITY.
Discuss the listed "Reasons to Network".
Explain what they mean.
Can you think of any other reasons why you might network computer
resources?
PC Networking Level 5.doc 8
OTHER ADVANTAGES OF NETWORKING PCS.
Lower Software Costs.
No need to purchase multiple copies of the same Application Software.
One copy held on the Server (Network Version of the Software) and the
correct Software Licence Agreement (or Site Licence) to cover the
maximum number of concurrent users (Network Operating System eg
Netware is also required)
Ability to share software eg databases among several users
simultaneously
Group access to external services and other file servers
Lower Hardware Costs.
Perhaps one printer is shared between 6 PCs i.e. Print Sharing
No need for the Workstations to have a Hard Disk drive (depending on the
Network Operating System used) (if a Windows Workgroup, smaller Hard
Disk required than for a Stand Alone).
However, each PC must have a Network Card and a Network Link, such
as co-axial cable.
Ability to use less expensive PCs (essentially, you need a processor and
RAM, plus input and output devices)
Lower cost that a Mini Computer, and probably more versatile
Data Integrity/Data Security/Reliability.
All users have access to the same Database. There is only one copy,
therefore the data is consistent (called better integrity)
Centralised control of data, for better security
Files can be password protected at all levels.
Backups from server (easier)
ADVANTAGES OF USING STAND-ALONE PCs instead of LANs
Less complex
A breakdown only impacts the one PC
PC Networking Level 5.doc 9
C. TYPES OF NETWORK.
Traditionally computing has moved from batch processing to time sharing
(possibly from dumb terminals) to file servers to client/servers and possibly to
Thin Client (i.e. back to dumb terminals!)
Mainframe
centralised large computer
"dumb" workstations
Peer to Peer
workstations can make available their resources
no central server running a network operating system (NOS)
security is the responsibility of each workstation
each station runs compatible operating system
can still have centralised storage of data
Workstation OSs (operating systems) that support peer to peer networking
include Windows 3.11 and Windows 9x (95 and 98).
Fileserver
workstations communicate with a central server (a high end computer)
security is enforced by a network administrator from the server
resources in the workstation disk are not normally made available to the
network
server runs special networking software which may allow computers to be
connected across different platforms
NOS (Network Operating Systems) that reside on the server include Novell
NetWare, Windows NT Server (soon to become Windows 2000 Server), Unix (or
Linux) and AppleTalk.
PC Networking Level 5.doc 10
Client/Server
In a file server environment, when you load a database file, the whole of the file
will transfer from the fileserver hard disk (HDD) to the RAM of the workstation.
When this happens, there are a number of issues that need to be addressed to
do with file, table or record locking so that more than one person is not updating
data at the same time.
Limitations of using the file server technology on a LAN:
excessive data movement
need for powerful workstations
decentralized data control
Server does not need to be as powerful as a thin client server but needs more
power than file server.
In a client/server environment, only the data required is transferred to the client.
Additional software is run on the server to manage this (e.g. SQL Server). This
system is like a combination of the mainframe/dumb Concurrent access is
managed from the server. Processes like queries are performed on the server.
However the application program is still run on the client (unlike the mainframe
situation)
Note that the word server can refer to hardware, software or both terminal and
file server environments.
PC Networking Level 5.doc 11
Thin Client
This relatively recent development (or maybe it's old ideas being readapted)
allows modern software to be run on aging PC workstations - the workstation
acts as a dumb terminal with all applications and processing being achieved on
the server. An example of this technology is Windows NT Terminal Server.
All of the above categories of network are either examples of central processing
(all processing done on the central computer) or distributed processing (some or
all processing done on the workstations).
Mainframe
Mainframe Terminal
Application
Data
Presentation
Processing
File Server
Server Client
Application *
Data
Presentation
Processi ng
Client/Server
Server Client
Application
Data
Presentation
Processing
* Some applications run are loaded off the file server (e.g. MYOB) but the
processing still happens in the client.
PC Networking Level 5.doc 12
Local Area Networks (LAN)
Used for small localised clusters of computers. High data speeds over short
distances are provided - up to 100Mb/sec for (say) 2km. Inexpensive cable
owned by the user, baseband (often not multiplexed).
Wide Area Networks (WAN)
Operate over a much wider area (even globally). Speed is limited by the
capability of the telecommunications network and the cost involved in leasing
high speed lines (digital or analogue).
Some texts add a definition in between the LAN and WAN - that of the MAN
(Metropolitian Area Network). This network goes beyond the 2km limit but is not
inter-city.
A WAN can be a number of LANs inter-connected together.
The main distinction between WANs and LANs is mainly the physical links
between Network resources. In general, LANs:
extend over a much shorter distance
carry a very high volume of traffic over this short distance
Equipment and circuitry is “locally” owned. Although a LAN can have
gateways to other Networks, processing is done independently of any other
Computer other than the workstation being used.
PC Networking Level 5.doc 13
D. CABLING and TOPOLOGIES.
Like any computer system, a network includes hardware and software.
The transmission medium used is also important. Examples of transmission
medium are:
Cable (Unshielded Twisted Pair (UTP), Shielded Twisted Pair (STP), Thin
Co-axial, Thick Co-axial and Fibre Optic
High Frequency Carrier (Radio Waves, Infra Red, Microwave)
A Topology is the pattern by which network resources are interconnected. There
are a variety of methods for connecting LANs and WANs, and the topology
chosen depends very much on the amount of functionality you require, and the
cost you are prepared to pay. Some topologies are listed below:
Star
Originally used for relatively dumb terminals connected to a central server. The
terminals had little processing power in themselves.
Each station is attached to a common central switch whose job it is to
route traffic to specific stations depending on addresses. This
configuration provides a convenient central point for network maintenance
and testing but does require a separate cable pathway to each
workstation.
The star is also used today with twisted pair cabling and hubs. A popular
topology that is easy to fault find.
STAR
Where resources are independently linked to a central node
If one link breaks, the rest of the network is intact
Higher cost of cabling
PC Networking Level 5.doc 14
Bus Used for PC networks - e.g. Xerox's "Ethernet" topology.
Coaxial cable in a bus system has two ends (terminated with resistors to stop the
signal from reflecting i.e. the signal is absorbed). When a signal is transmitted, it
travels in both directions (full duplex system) from the station until it reaches the
resistors. Every station receives the signal but only the station that the data is
addressed to copies the data.
A station listens to see if the bus is busy (called contention)- if some other station
is using the bus then it waits a predetermined length of time and listens again.
When the bus is not busy, the station transmits. If two stations transmit at the
same time, there is a collision - each station waits a random period of time before
trying again.
This access method is called CSMA/CD - Carrier Sense Multiple Access with
Collision Detection.
BUS
Several resources connected in a line, and hang off that main feeder (Bus)
A bad link can be bypassed
PC Networking Level 5.doc 15
LOOP or RING
Cheap cost (don’t confuse with IBM Token Ring, which is really a Star topology)
If a link is broken, the entire loop is lost
Mesh
Used often for WANs to give extra reliability - there are multiple routes between
computers in case of telecommunications failure - you can't afford the whole
network to go down if a cable across the Tasman Sea is cut.
Real networks are usually combinations of topologies - e.g. a network with some
coax (bus system) and some TP (star system). In this case the network will still
be CSMA/CD with the star portion acting as a logical bus.
Every workstation is interconnected
Complex and expensive
PC Networking Level 5.doc 16
IBM Token Ring.
Used for PC networks - e.g. IBM's "Token Ring" topology.
The signal is transmitted around the ring in one direction - each station receives
the signal from the station before it and repeats it to the next station. When a
station transmits, it gives the data the address of some other station in the ring -
it passes from station to station and is copied by the one it is addressed to. When
the signal returns to the originating station, it is removed from the ring. The
system can check to see if the data has been received by using a status bit.
A station can only transmit when it is in possession of the token (which it can
have only for a limited period of time).
Technically the token ring MAC is a logical ring - in reality token ring calls for a
central hub. Token ring is a lot more technically sophisticated than the Ethernet
bus but handles heavy traffic better. Everything is more expensive than Ethernet
- cable, NICs, etc.
PC Networking Level 5.doc 17
TRANSMISSION MEDIA (CABLING).
Essentially, there is CABLE and HIGH FREQUENCY CARRIER WAVE
Your choice of which transmission medium depends on:
Distance of transmission
Susceptibility of interference
Cost
Bandwidth required
Volume of Traffic
Twisted Pair cable (UTP and STP) has the following characteristics:
The most economical wiring system
It may already be installed in the form of the telephone system
It is susceptible to some outside interference
Coaxial cable has the following characteristics:
It may be effected by outside interference
Harder to bend and terminate than UTP
It has grounding problems
It is more expensive than twisted pair, but it has a greater bandwidth.
Fibre Optic cable has the following characteristics:
It is the most expensive
It has the best potential
It does not emit an electromagnetic signal, and therefore can be used in
high security areas
Price approx $5 per metre (single strand)
Termination not easy
PC Networking Level 5.doc 18
E. MEDIA ACCESS CONTROL – ACCESS METHODS.
CSMA / CD (Carrier Sense Multiple Access / Collision Detect)
Used on Bus Topology Networks, typically with Ethernet All Work Stations have
separate Ids. Before transmitting, a Work Station listens to see if the Bus is busy.
If not, a message is sent. If 2 work stations transmit simultaneously, a “collision”
is detected, and both terminals must wait a random time before re-transmitting.
If traffic usage (throughput) is high, severe performance fall off
Token Passing.
Used mainly with IBM Token Ring Networks. A token, consisting of an ALL
CLEAR message, is circulated continuously on the ring. A Work Station wishing
to send a message will use the circulating token. The token’s message code
changes to IN USE, and attaches the message, along with the address (to and
from) and an error checking code.
Only one message can be circulated at a time. Each node (network resource or
junction point, capable of communicating with the other network devices)
includes a Repeater, which regenerates the Token to maintain it’s signal
strength.
Each node will inspect the IN USE token, to see if the token contains the node’s
address. The intended node will copy the message, and return the message to
the originating node. The message is cleared, and the ALL CLEAR signal is
restored.
Polling.
Ideally suited to a Star Topology. The server continually polls each workstation in
turn, asking if it wishes to use the network. In a Star Network, the message is
then directed (via the server, if Star) to the address required.
If a Workstation is monopolizing the network, the messages will be broken up
into smaller pieces. Only so many pieces (bytes) will be accepted with each poll.
FDDI.
Fibre Distributed Data interface - a MAC that employs a pair of fibre optic rings
and tokens. Can support very high data transfer rates over long distances.
PC Networking Level 5.doc 19
IEEE 802 STANDARDS.
A set of standards developed by IEEE (Institute of Electrical and Electronics
Engineers) to define methods of access and control on Local Area Networks
(LANs).
The IEEE 802 standards correspond to the Physical and Data-Link layers of the
widely accepted ISO Open System Interconnection (OSI) Model, but they divide
the Data-Link layer into 2 sublayers (Logical Link Control and Media Access
Control).
Three primary IEEE 802 standards exist:
802.3 for Bus Networks that use Carrier Sense Multiple Access with
Collision Detection (CSMA / CD). Based on the Ethernet network
developed by Xerox Corporation.
802.4 for Bus Networks that use Token Passing to regulate network
access and traffic control
802.5 for Ring Networks that use Token Passing (token ring networks)
PC Networking Level 5.doc 20
For each of the networks shown below:
Identify the typology of the network and
Describe how the signal is transmitted around the network.
PC Networking Level 5.doc 21
Questions on Network Topologies:
1. Topology means:
2. What is the terminating resistor for in the bus system?
3. What piece of hardware is required in a 10BaseT network that is not
needed in a physical bus system?
4. What intelligence is built into a physical star wired ring typology?
5. What makes a typology "logical bus"? What frame transmission method is
used?
6. Describe the media access method for the logical ring topology.
7. Some switches are designed to support multiple ……………………….
8. Some networks can support IBM compatibles and Apple Mac PCs - true or
false? How can this happen?
PC Networking Level 5.doc 22
CHAPTER TWO.
LAN MODEL.
A. A NETWORK MODEL.
B. NETWORK OPERATING SYSTEMS.
C. HARDWARE and PERIPHERALS.
D. The NETWORK INTERFACE CARD.
E. INTERCONNECTION.
F. CLASS EXERCISE.
PC Networking Level 5.doc 23
A. A NETWORK MODEL.
Networks are for sharing resources.
The Computers interoperate.
Every sharing activity has it’s rules of operation.
In Networking, we call these rules standards and protocols.
STANDARDS describe how things should be. Typically, they outline the
minimum level of performance.
PROTOCOLS are sets of rules and agreements, that describe how various
elements interact.
The ETHERNET set of standards and protocols was developed by Xerox
Corporation.
The ARCNET set of standards and protocols was developed by Datapoint
Corporation quite independent of Xerox’s Ethernet. Datapoint kept ARCnet as a
proprietary set of specifications, and it didn’t have the commercial success of
Ethernet.
The TOKEN-RING set of standards and protocols was developed by IBM
Corporation later on in the 1980s.
These early Local Area Network (LAN) architectures tended to combine inflexible
hardware specifications with strict protocol descriptions. Specific types of cable,
cable connectors, topologies and software were required to satisfy each LAN
definition. Interoperability was not easy, and to be successful at installation, it
paid to stick to consistent equipment throughout the LAN.
Due to Industry and Market demand, standards today are a lot more flexible, and
do allow more mixing and matching. While the move to purely Open Protocols
(protocols that do not favour a single manufacturer) has lost some momentum
compared with the 1980s, the idea was good. Today (the 1990s), the emphasis
is more on the tried and proven protocols, but with the development of more tools
and programs to enable different computers eg IBM PC and Apple MacIntosh to
link effectively and interoperate.
Also, there has been considerable development with Software, as well as with
Hardware, and with the above mentioned development of interoperability with
standards and protocols. Workgroup productivity programs, and Workflow
software have come to be. This makes it easier to search for data, organise data
and link data (and even embed it). Sharing now means more than queuing up for
a file or a printer.
PC Networking Level 5.doc 24
THE NETWORK MODEL.
Here are the major components of a network:
Network Operating System.
The NOS consists of a family of programs that control the operation of the
network. Some of these programs provide the ability to share files and hardware
devices.
Servers are computers that share their resources. This is software controlled.
Clients are programs that give a user the ability to use the shared resources
provided by the server.
It is quite common today to have client and server software running in the same
Computer. This enables you to use resources on another Computer, and for
other users to use resources on your Computer.
Network Hardware and Peripherals.
These are Hardware peripherals, such as printers and modems, which have
special internal processors that run networking server software. They don’t have
to be directly attached to a computer. Different computers eg IBM and Apple,
providing they have the appropriate client application program can use these
networked peripherals, and the effect is that it looks as though they are locally
attached (even though they aren’t).
Network Interface Card (LAN Adapter).
The low-powered digital signals inside a computer are not powerful enough to
travel long distances, without fading.
The Network Interface Card:
Changes the signals that come from inside the computer into more powerful
signals that can be transmitted down a network cable ie Amplification.
Packages the data for transmission.
Controls access to the shared network cable (the cable is shared by the
linked workstations).
Network Interconnection eg Cabling.
Computers can send messages using:
Electrical pulses over Copper Cable (UTP, STP, Co-axial).
Pulses of light over fibre optic cable.
Radio or light waves through air.
and even combinations of all of these.
PC Networking Level 5.doc 25
B. NETWORK OPERATING SYSTEMS.
The function of the network software is to:
ensure that information is transmitted and received reliably - the network
protocol defines a set of rules for this
make the system transparent to the user
provide security
enable resources to be shared.
Examples of network software include Novell NetWare, Apple Appletalk,
Microsoft Windows NT, Unix and Linux.
Just as a PC requires an “Operating System” such as DOS to control it, so a
Network needs to have a Network Operating System (NOS) to control it.
Special software enables the workstation’s to share peripherals. Most of the
software is located in the network server, but some is located in each
workstation. One of the most popular LAN software systems (NOS) is NetWare,
marketed by Novell Incorporated. In a Novell network, the network server
contains the NetWare operating system and each workstation contains a
NetWare Shell. It is called a shell because it fits around the micro’s operating
system.
The software allows you to connect various machines with different operating
systems within a building or over a wide area. The technology involved in
networking is improving and expanding every day leading toward intelligent
houses and buildings. It is estimated that within the next twenty years, only one
fibre optic communication cable will enter your house. Your TV, computer and
telephone will all run off the same system.
Network Operating Systems are a combination of programs that give some
computers and peripherals the ability to accept requests for service across the
network, and give other computers the ability to correctly use those services.
Servers are computers that share their hard-disk drives, attached peripherals
such as printers and CD-ROM drives and communication circuits. A request for a
service is made to the server. The server will inspect the request for proper
authorisation, check for any conflicts and then, providing the checks are passed,
provide the requested service.
File Servers store files created by application programs, or may store the
application program itself. The file server must have a large enough hard-disk to
store enough to store the data. File servers also allow more than one workstation
simultaneous access to the same file. Access can be controlled ie who can
access what, and when. Excellent system for shared Databases eg an Airline
Booking System.
PC Networking Level 5.doc 26
Print Servers accept print jobs sent by anyone across the network. Spooling
(Spool = Simultaneous Print Operations On Line) print jobs is a critical function of
print-server software. Why?
The print-server can also report on status of jobs waiting for printing, and sorts
out priorities.
Practically any number of printers can be shared on a single network in a variety
of ways.
Client Software works with the internal operating system of a computer, so it
can route requests from application programs and user request via input devices
such as keyboard and mouse to the File Server and Print Servers on the
network.
The principal element of the Client Software is called a redirector.
The redirector captures service requests that it has been programmed to
recognise, and routes these requests to the appropriate place in the network for
service.
Network Communications Software packages requests from the Client
Computer and sends the request across the network. This software must
conform to specific protocols for addressing, ensuring deliver, and ensuring
accuracy.
Typical suites of network communications protocols include:
Apple’s Apple File Protocol (AFP).
Artisoft’s (Lantastic) Network Basic Input Output System (NETBIOS).
Microsoft’s NetBIOS Extended User Interface (NETBEUI) ) (“net-boo-ee”).
Novell’s Sequential Packet Exchange (SPX) and Internetwork Packet
Exchange (IPX).
Driver (regulates or drives a device) Software works between the Network
Interface Card and the Network Communications Software. At one time, you
needed to generate a special configuration of the Network Operating System for
every make of LAN adapter. Today, adapter (NIC) manufacturers supply drivers
that conform to Microsoft’s Network Driver Interface Standard (NDIS) (“N-diss”)
or Novell’s Open Data-Link Interface (ODI). This enables you to choose which
Network Operating System you use.
PC Networking Level 5.doc 27
C. HARDWARE and PERIPHERALS.
Server
Your network may have a file server, application server or both installed.
Workstations
Depending on your network, these may be of one or more platforms.
Hubs
Not needed with thinnet. Also known as concentrators. Provides good fault
tolerance because all workstations are attached separately to the hub. Able to
connect four, eight, sixteen or twenty four PCs.
Switches
Used to reduce congestion on the network. The network is broken up into
sections so that traffic that has no business on parts of the network are not sent
there.
Printers
Network or personal. Network printers are more robust, print faster and hence
cost more than personal printers. Printers can be connected in the following
manners:
On a workstation for local use only.
On a workstation shared with the network.
On a dedicated workstation set up as a print server (old XT or 286).
On a print server box.
On the file server.
Direct onto the network (if printer is capable).
Uninterruptible Power Supply
Provides uninterruptible power source for servers so time as available to shut
down properly in the event of a prolonged power cut.
PC Networking Level 5.doc 28
INTERCONNECTION BETWEEN NETWORKS.
Bridge
Used to connect together LANs of the same type. The bridge reads all the
messages and addresses, and only passes on the messages that are intended
for the other LAN. Messages are either blocked or redirected. This avoids
overloading on either network.
Bridges filter and forward packets by using the physical address of the network
cards on the nodes - they operate at the OSI Data Link Layer.
Router
Device to connect physically separate networks of different types (e.g. a bus to a
token ring network). Has software and a processor to enable it to connect
different protocols and topologies; is able to find all other hardware on the
network and route according to use and traffic. Can be simply a computer with
several NICs and software to enable routing.
Routers are able to interconnect between different network types since they filter
traffic by logical address rather than physical address.
Brouter
A brouter is a device that can function both as a bridge and a router.
Not many around these days – switches or routers are more the norm.
Gateway
Used to connect a LAN to a WAN (e.g. a Novell network to the internet)
Tape Backup Drive
Or alternative device is needed to enable easy backup and restoration of lost
data.
DISCUSSION:
Discuss other types of Hardware that could be used in a LAN
How would your choice of hardware and peripherals be dictated by the User's
need?
PC Networking Level 5.doc 29
D. THE NETWORK INTERFACE CARD.
The Network Interface Card, or LAN adapter, functions as an interface between
the computer and the network cabling. Inside the Computer, the NIC must be
able to move data to and from RAM (over the parallel bus). Outside the
computer, the NIC controls the flow of data in and out of the network cable
system. The NIC has a specialised port that matches the electrical signalling
standards used on the cable and the specific type of cable connector.
The NIC must also buffer the data between the computer and the cable. The
computer is typically a lot faster than the network. The NIC must also change the
form of the data from a wide parallel stream (within the computer) to a narrow,
one bit at a time, serial data stream (outside the NIC).
The jobs that the NIC performs means that it needs special on board processors.
These processors can have their own RAM added, and can also include a
special transceiver to handle the electrical interface to the cable.
Some NICs have a socket for a special Boot ROM. This allows a PC to start
DOS from a file on a server, eliminating the need for an Internal Hard Disk Drive.
You must choose a NIC that matches your computer’s data bus and the network
cable. EISA or PCI adapters prove their worth in servers. Most workstations still
use the ISA adapters. If you use adapters that use EISA, IBM PS/2s MCA or PCI
buses, you can also choose products that use bus-mastering. Bus Mastering can
move data to and from RAM without interrupting the computer’s processor,
hence lightening the load.
On the Network Cable side, the LAN adapter performs 3 important functions:
Generates the electrical signals that travel over the network cable.
Follows the rules controlling access to the cable.
Makes the physical connection to the cable.
Adapters for Ethernet and Token-Ring use the same basic system of electrical
signalling over the cable. A technique called MANCHESTER ENCODING
provides a way to transmit 0s and 1s using DC (Direct Current) Voltage pulses
ranging from -15 Volts to +15 Volts. The LAN adapters translate each change in
voltage level as a character in the ASCII data alphabet.
PC Networking Level 5.doc 30
An interface card is the interface between the Local Area Network (LAN) cabling
and the Computer itself. The Network Interface Card (Network Adapter) does
many things, such as:
Converts data that is sent down the Computers Bus in parallel form into the
serial form required for the LAN cabling.
Provides buffering.
Amplifies signals.
Provides addresses for each work station.
Obeys the rules of the Network Operating System and the Media Access
Control method being used.
Try to find some examples of Network Interface Card, and (if possible) LAN
Cabling (especially for the Practical Exercises)
NIC or network adaptor. Connector required for thinnet is BNC; for 10BaseT, RJ-
45. A combo card has both connectors installed. If you have a Pentium PC with a
PCI bus, then it is advantageous to use a 32 bit PCI NIC. Some of the functions
of the NIC include:
Converts data that is sent down the Computers Bus in parallel form into the
serial form required for the LAN cabling.
Provides buffering.
Amplifies signals.
Provides addresses for each work station.
Obeys the rules of the Network Operating System and the Media Access
Control method being used. Forms the data into frames.
Deciding factors for NICs:
Access method and protocol.
Transmission speed.
Amount of an-board memory for buffering frames of data.
Bus design - ISA, PCI.
Compatibility with motherboard chipsets.
DMA usage.
IRQ and I/O addressing.
Connector design.
PC Networking Level 5.doc 31
E. INTERCONNECTION.
Media
Transmission media for LANs fall into two general categories - guided and
unguided (radio).
Media suitable for LANs fall into five categories:
Broadcast radio (wireless )
twisted pair wiring
baseband coaxial cable
broadband coaxial cable
optical fibre
microwave radio
For WANs we can add satellite to the list.
Cable
Thick coax was the original Ethernet cable - too inflexible and expensive.
Needs a drop cable to interconnect the network cable and the workstation.
Thinnet with T- connector at each computer is common. Max. length of
section is 185m and 30 computers or a repeater is needed.
Twisted pair (unshielded twisted pair, UTP, 10baseT). Cheapest method -
same as used for the phone system - convenient. Twisted pair can be
shielded for noisy environments (STP). Comes in various standards, such
as:
category 3 which is normal telephone cable - good to 16Mbps
category 5 - 100Mbps
Fibre optic - used for high speed connection between parts of the network.
Examples of abbreviations for ethernet cabling (distances are without signal
regeneration) are:
10base2 (10Mbps baseband ethernet over coaxial cable to a maximum
distance of 185m - known as thin ethernet).
10base5 (10Mbps baseband ethernet over coaxial cable to a maximun of
500m - known as thick Ethernet).
10baseT (10Mbps baseband transmission on twisted pair (cat 3 or 5 UTP)
to 100m using a star configuration with hub(s)).
100baseTX (100Mbps to 100 meters using cat 5 UTP or STP).
100baseFX (100Mbps baseband on fibre to 2000m).
Question?
Which cabling system would you use for a small network say at home?
PC Networking Level 5.doc 32
Coaxial cable
A type of wire that consists of a center copper conductor surrounded by
insulation and then a grounded shield of braided wire. The shield minimizes
electrical and radio frequency interference.
Coaxial cabling is the primary type of cabling used by the cable television
industry and is also widely used for computer networks. Although more
expensive than standard telephone wire, it is much less susceptible to
interference and can carry much more data. Because the cable television
industry has already connected millions of homes with coaxial cable, many
analysts believe that they are the best positioned to capitalize on the much-
heralded Information highway.
Coaxial cable can provide both baseband and broadband communications.
Broadband coax could allow the media to be shared with other services such as
CCTV. However the cost is higher and often it is easier and cheaper to install
multiple baseband cables instead.
Fibre optic cable
A technology that uses glass threads (fibres) of about 50m in diameter to
transmit data. A fiber optic cable consists of a bundle of glass threads coated in
plastic, each of which is capable of transmitting messages modulated onto light
waves.
Fibre can either be: single mode
Or multi-mode
Fibre optics has several advantages over traditional metal communication lines:
Fibre optic cables have a much greater bandwidth than metal cables including
coax). This means that they can carry more data (at speeds of about 1Gbps).
Fibre optic cables are less susceptible than metal cables to interference.
Fibre optic cables are much thinner and lighter than metal wires.
Data can be transmitted digitally (the natural form for computer data) rather
than analogically.
PC Networking Level 5.doc 33
The main disadvantage of fibre optics is that the cables are expensive to install.
In addition, they are more fragile than wire and are difficult to join. Terminal
equipment is usually quite expensive.
Fibre optics is a particularly popular technology for Local Area Networks. In
addition, telephone companies are steadily replacing traditional telephone lines
with fiber optic cables. In the future, almost all communications will employ fibre
optics.
Twisted Pair Cable
A type of cable that consists of two independently insulated wires twisted around
one another to reduce "crosstalk". The cable pair (or pairs) is then covered in a
PVC sheath. Twisted-pair cable is used by telephone networks, and is the least
expensive type of LAN cable.
Wireless
Can be radio waves or light - generally used for slower speeds (<10Mbps). Light
usually requires a close to line of sight situation to work. Radio LANs generally
use very high frequencies (approximately 18 GHz).
PC Networking Level 5.doc 34
F. CLASS EXERCISE.
Remembering the Network Model, ie:
NOS
NIC
CABLING
HARDWARE and PERIPHERALS
In your groups (in the time allowed), produce a design for the following situations:
A. A Tertiary School Class using a Server Based Network and 20
Workstations.
B. A Small Business with five staff.
Consider exactly what you need to have in each Network (Price is not a problem)
and how you would go about things.
Appoint a spokesperson (you will be required to do a Group Presentation to the
class).
Appoint a recorder.
PC Networking Level 5.doc 35
PC Networking Level 5.doc 36
CHAPTER THREE.
LAN STRATEGIES.
A. SERVER BASED LANs.
B. PEER-to-PEER NETWORKING.
C. CLIENT/SERVER COMPUTING.
D. OVERVIEW of NETWORK MANAGEMENT.
E. E-MAIL.
PC Networking Level 5.doc 37
A. SERVER-BASED LANs.
There are four types of servers:
File Servers.
Application Servers (see C. Client / Serving Computing).
Print Servers.
Communications Servers (sometimes called Web Servers).
However, under different strategies, various devices on the network can also
perform the functions that the server does.
Server-based networking relies on a single, powerful computer dedicated to
providing all server functions for many (perhaps 500 or more) client computers
on the network.
Peer-to-Peer networking is where the server functions are distributed among
many computers. They act as file or print servers, and can also run application
programs at the same time.
Server-based networks, compared to Peer-to-Peer networks, have:
Higher start-up cost (but there is an economy of scale as more client
computers that share the Server’s resources are added).
More technical expertise needed to install and manage (in general).
Features of a dedicated file server are:
Large amount of cabinet space for drives and other components.
Large Power Supply Unit to handle the load.
Fast interface bus.
Ability to expand RAM capacity considerably.
Fast processor.
Several Network Interface Cards, each with separate segments of cabling.
Benefits of Server-based systems are:
Better Data Integrity and Data Management (important records and files are
in one place, making management and control of data easier, and allowing
easier backups).
Multitasking Operating system so that several programs can run at the same
time.
Good Network Administration from special Network Management software
(even includes Client invoicing for access time).
Security.
Fast response.
Room for expansion.
Ease of backup.
PC Networking Level 5.doc 38
B. PEER-to-PEER NETWORKING.
The processing power and storage capacity is shared between the networked
computers. Peer-to-Peer networking provides cost economy, because the
computers are probably already available as “Stand Alones”, and are no doubt
not utilized to the maximum potential. This means there are resources that can
be shared.
Some Peer-to-Peer networks run file server networking software as well as Client
Networking Software, Application Programs and, of course, an underlying
Operating System consistent across the network. This type of peer-to-peer
networking software is part of MS Windows 95, MS Windows for Workgroups
Version 3.11 and the Apple Macintosh Operating Environment.
Not all of the Computer Resources are automatically available to every user on
the network. The person using a particular PC can decide what files, directories,
drives and peripheral devices (such as printers) can be shared with other
networked computers. It is also possible to combine Peer-to-Peer Networking
with a Server-based architecture.
Peer-to-Peer networking typically doesn’t have the powerful management and
auditing features found in server-based software. This is because the processing
power is used by local applications. Also the power (at a $ cost) and specialist
software of a dedicated server is probably not available in any of the Peer-to-
Peer networked computers. With the power of modern PCs increasing rapidly,
and costs falling, the performance of Peer-to-Peer networking is improving.
Benefits of Peer-to-Peer networking are:
Ease of installation.
Ease of maintenance.
Low Start-up costs.
Simplicity.
Sufficient power to satisfy many organizational needs.
PC Networking Level 5.doc 39
C. USE of CLIENT/SERVER COMPUTING.
We have previously described several types of SERVER and CLIENTS
(workstations). However, the term CLIENT/SERVER COMPUTING does have a
special meaning. CLIENT/SERVER COMPUTING is where work is shared
between the client and the server, so that each device performs the task that it
can do the most efficiently.
The best example of client/server computing is in Database Management
Systems. In older Database technology, each workstation runs a Database
Program. Large Data Files are called from the File Server, processed at the
Workstation, and a Report is generated with the desired information. The newer
Client/Server model distributes the task.
The client computer sends a request to a special program called a database
engine (also known as Database Server), which runs in the File Server. The
Database Engine indexes, sorts, and searches the shared files, without sending
them over the network. The Database Engine will only respond to what is
specifically requested, meaning no waste of resource. It also means that the
client computer (workstation) can allocate it’s resources to running other
applications.
Resources can be allocated anywhere. A Workgroup is a good example of a
Client / Server application --- especially for things such as Personal Management
and Scheduling, Project Management and general workflow. Such automation
and integration of tasks produces better productivity.
SQL = Structured Query Language
Discuss what the Redirector does
In a LAN, software that routes workstation (client) requests for data to the server.
In an MS Windows network, the redirector program is added to the PC to
intercept requests for files and printers and direct them to the appropriate remote
device if applicable. Starting with Windows 95 and Windows NT 4.0, the
redirector recognizes UNC names as well as drive letters that have been mapped
to remote servers. The counterpart in NetWare is known as the Requester.
PC Networking Level 5.doc 40
D. OVERVIEW of NETWORK MANAGEMENT.
Computers have become an essential part of Business Operation and
Manufacturing Operations, and their role is becoming more and more important.
Computer Networking has enabled Computer users to share resources. Network
Management is extremely important.
Network Management Programs run in Servers, Wiring hubs and even on
Network Interface Cards and Uninterruptable Power Supplies. They gather
statistics on data movement, and watch for conditions that exceed thresholds
(safe limits that are programmed in). If a problem is detected (or even
suspected), the Network Management Program will take action. Actions might
include restarts, rerouting of data, call for human assistance or reallocation of a
resource (such as extra loading on a load balanced power supply).
Manufacturers of Network equipment have adopted several sets of standards for
operating Network Management Software. SNMP (Simple Network Management
Protocols) is a popular set of standards, and a set of standards that many
systems will either directly follow, or run to a similar style.
Under the SNMP Architecture, small management programs (in all sorts of
networked devices) monitor network devices and gather data. These small
management programs are called AGENTS.
The data collected by the agents comes in a special format, known as MIB
(rhymes with rib). MIB = Management Information Base. A central program
(MANAGEMENT CONSOLE PROGRAM) polls the agents regularly, and the
contents of their MIBs are downloaded. These Management Console Programs
typically displayed detailed graphical information (e.g. green / orange / red bar
graphs to indicate performance compared to thresholds) to a display screen
(console). They can also send detailed statistical data to specialized analytical
database programs.
Network Managers can use the Management Console to command changes to
the network eg status of a resource, activation of a link.
Good Network Management can dramatically enhance the performance of a
Network, and ensure successful operation. It is a very effective insurance policy,
even though the initial investment might be considered costly.
PC Networking Level 5.doc 41
RMON
(Remote MONitoring) Extensions to the Simple Network Management Protocol
(SNMP) that provide comprehensive network monitoring capabilities. In standard
SNMP, the device has to be queried to obtain information. RMON is proactive
and can set alarms on a variety of traffic conditions, including specific types of
errors. RMON2 can also monitor the kinds of application traffic that flow through
the network. The full RMON capabilities are very comprehensive, and generally
only portions of it are placed into routers and other network devices.
REMOTE ACCESS.
The ability to log on to a computer or network within an organization from an
external location. Remote access is typically accomplished by directly dialing up
analog or ISDN modems or via a connection to the Internet.
REMOTE CONTROL SOFTWARE
Software that lets a user control a local computer from a remote location via a
network connection. The software is installed at both ends, and both local and
remote users can control the machine. Each user sees the same screen display
as if they were both looking at the same machine.
Also known as "desktop sharing," "remote desktop sharing" and "application
sharing," remote control software is used to provide instruction and technical
support to remote users at their computers as well as take control of an
unattended computer from a remote location.
REMOTE CONTROL VS. REMOTE NODE
In remote control, only keystrokes and mouse movement are sent from the
remote machine, and only screen changes are sent back to the remote. All
application processing takes place in the local computer.
In contrast, a remote node setup is the normal way remote users log onto the
company network. All data flows to the remote machine as if it were a local PC.
With high-speed connections, remote node is the preferred method; however, if
an enormous amount of data on the network must be processed by a remote
user who has only a dial-up connection or perhaps a slow computer, the remote
control method can be used. Instead of passing all the data to the remote PC, the
user's unattended local PC performs the processing under the control of the
remote PC. The remote user will not have the actual data files, but will have the
results of the processing on the remote screen, which can be captured and
saved.
PC Networking Level 5.doc 42
E. ELECTRONIC-MAIL (E-MAIL).
Electronic Mail Systems (E-Mail) store messages, and deliver these messages
when the addresses are ready to receive them. These store are forward services
can partially replace phone calls and meetings, overcome any limitations of time
and work hours, and have the advantage of “Written Copy”.
In an electronic-mail system, software in each computer reads and writes to a
shared set of sub-directories in the network file server (or Workgroup Post
Master). Each electronic-mail subscriber runs a program that checks the files in
the subdirectories for any waiting mail. In larger networks, each LAN has it’s own
set of electronic-mail message files (generally called a Post Office). One
computer on each LAN, called the Postmaster, runs a program on a regular basis
that identifies messages identified for other Post Offices, collects them and
forwards them.
In many ways, this process is similar to NZ Post “Snail Mail”, except it is all done
electronically. If messages are destined for other electronic mail systems that use
different message formats or different address structures, a GATEWAY function
is required.
A good electronic Mail System is a superb (and cheap) method for disseminating
information between Business and other users.
PC Networking Level 5.doc 43
PC Networking Level 5.doc 44
CHAPTER FOUR.
PROTOCOLS, STANDARDS and
INTERCONNECTION.
A. PROTOCOLS.
B. IEEE 802 STANDARDS.
C. LINKS BETWEEN LANs.
D. REPEATERS, BRIDGES and ROUTERS.
PC Networking Level 5.doc 45
A. PROTOCOLS.
A protocol is a set of rules for communicating between computers. Protocols
govern format, timing, sequencing, and error control. Without these rules, the
computer will not make sense of the stream of incoming bits.
Communicating data from computer to computer takes many steps. Suppose you
are sending a file from one computer to another. The file must be broken into
pieces. The pieces have to be grouped in a certain fashion. Information must be
added to tell the receiver where each group belongs in relation to others. Timing
information and error correcting information must be added.
Because of this complexity, computer communication is broken down into steps.
Each step has its own rules of operation and, consequently, its own protocol.
These steps must be executed in a certain order, from the top down on
transmission and from the bottom up on reception. Because of this hierarchical
arrangement, the term protocol stack is often used to describe the steps in
computer communication. A protocol stack is a set of rules for communication,
and each step in the sequence has its own subset of rules.
What is a protocol, really? It is software that resides either in a computer's
memory or in the memory of a transmission device like a network interface card.
When data is ready for transmission, this software is executed. The software
prepares data for transmission and sets the transmission in motion. At the
receiving end, the software takes the data off the wire and prepares it for the
computer by taking off all the information added by the transmitting end.
The existence of many protocols often causes confusion. Novell does it one way.
3Com does it another. DEC does it a third way. IBM does it another way. And
since the transmitter and the receiver have to 'speak' the same protocol, these
four can't talk directly to each other. That's where protocol standards and the OSI
model fit in.
A protocol standard is a set of rules for computer communication that has been
widely agreed upon and implemented by many vendors, users, and standards
bodies. Ideally, a protocol standard should allow computers to talk to each other,
even if they are from different vendors. Computers don't have to use an industry-
standard protocol to communicate, but if they use a proprietary protocol then they
can only communicate with equipment of their own kind.
There are many standard protocols, none of which could be called universal.
The idea of a layered protocol is a little difficult to grasp so an example from
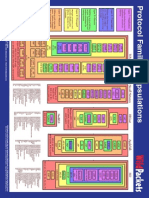
something that we are used to might help - writing a letter! An important part of
the layered protocol model is that each layer provides a service to the layers
above it.
PC Networking Level 5.doc 46
Protocol for what is said and in what order (i.e. acknowledge previous
correspondence, discuss your topic).
Protocol for formatting a letter (i.e. precede with address, date, then greeting.
Break into sentences - capitals and full stops).
Protocol for receiving/sending a letter to/from the PO (i.e. packaged according to
PO regulations (envelope size, stamp denomination, etc).
Going back up is like stripping off the lower level protocols.
Protocol for Protocol for
what is said and what is said and
in what order in what order
Protocol for Protocol for
formatting a formatting a
letter letter
Protocol for Protocol for
receiving/sendi receiving/sendi
ng a letter ng a letter
to/from the PO to/from the PO
PC Networking Level 5.doc 47
THE OSI MODEL
The Open System Interconnection (OSI) model is a set of protocols that
attempt to define and standardize the data communications process. The OSI
model is set by the International Standards Organization (ISO). The OSI
model has the support of most major computer and network vendors, many large
customers, and most governments, including the United States.
The OSI model is a concept that describes how data communications should
take place. It divides the process into seven layers. Into these layers fit protocol
standards developed by the ISO and other standards bodies, including the
Institute of Electrical and Electronic Engineers (IEEE), American National
Standards Institute (ANSI), and the Comittee Consultatif Internationale de
Telgraphique et Telephone (CCITT) (now called ITU-T)
The OSI model is not a single definition of how data communications actually
takes place in the real world. Numerous protocols may exist at each layer. The
OSI model states how the process should be divided and what protocols should
be used at each layer. If a network vendor implements one of the protocols at
each layer, its network components should work with other vendors' offerings.
The OSI model is modular. Each successive layer of the OSI model works with
the one below it. At least in theory, you may substitute one protocol with another
at the same layer without affecting the operation of layers above and below. For
example, Token Ring or Ethernet hardware should operate with multiple upper-
layer services, including the transport protocols, network operating system, inter
network protocols, and applications interfaces. However, for this interoperability
to work, vendors must create products to meet the OSI model's specifications.
PC Networking Level 5.doc 48
Each layer of the OSI model performs an essential function. Here's a look at what
each layer does.
Application The final layer is the interface between the software running
Layer in the computer and the network. It supplies functions to the
software in the computer, such as electronic mail or file
transfer. Note that this layer is not the applications
themselves! Protocols here include FTP, POP, SMTP, HTTP
and SHTTP.
Presentation The sixth or presentation layer is concerned with the
Layer presentation of data while in transit and performs code
conversion. It is the translator of the network, making sure the
computer is talking in the right language for the network (e.g.
EBCIDIC to ASCII conversion).
Session Layer The session layer decides when to turn communication on
and off between two computers. It coordinates the interaction
between them. Unlike the network layer, it deals with the
processes running in each machine to establish
conversations between them. Can provide for full or half
duplex operation.
Transport The fourth layer ensures data is sent successfully between
Layer the two computers in an orderly manner. If data is sent
incorrectly, this layer has the responsibility to ask for
retransmission of the data.
Network Layer The third layer establishes, maintains, and terminates
connections. The network layer is responsible for translating
logical addresses, or names, into physical addresses and
providing network routing. Makes sure a packet gets to it's
destination in a reasonable period of time. Is concerned with
routing.
Data-Link The second, or data-link, layer of the OSI model is
Layer responsible for getting data packaged and onto the network
cable. It manages the physical transfer, providing the blocks
of data, synchronization, error control, and flow control. The
data-link layer is often subdivided into two parts. These are
the Logical Link Control (LLC), which is designed to provide
a consistent level of service to the network layer regardless of
which MAC is used, and the Medium Access Control
(MAC), which is media dependent, and checks that the media
is free, encapsulates data into frames and checks for data
integrity using CRC.
Physical Layer The first, or physical layer, of the OSI model conveys the bits
that move along the cable (or media which can include radio).
It is responsible for making sure that the raw bits get from one
place to another, no matter what shape they are in. It deals
with the mechanical and electrical characteristics of the cable
and connectors. Signaling specifications are defined at this
level.
PC Networking Level 5.doc 49
Unfortunately, protocols in the real world do not conform precisely to these neat
definitions. Some network products and architectures combine layers. Others
leave out layers. Still others break apart layers. But no matter what, all working
network products achieve the same result, getting data from here to there. The
question is, do they do it in a way that is compatible with the rest of the world's
networks?
Interestingly not all protocols fit the OSI model - for example, Internet Protocols
(TCP/IP) does not.
PC Networking Level 5.doc 50
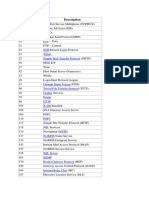
B. IEEE 802 STANDARDS.
In 1980, the IEEE (Institute of Electrical and Electronic Engineers) began work on
Project 802 - the formulation of standards for LANs. The 802 committee is
divided into a number of sub-committees:
IEEE 802.1: Standards related to Network Management.
IEEE 802.2: General standard for the data link layer in the Data Link
Layer in the OSI Reference Model. . The IEEE divides this layer into two
sublayers (the Data Link Control (DLC) Layer, and the media access
control (MAC) layer). The MAC layer varies for different network types
and is defined by standards IEEE 802.3 through IEEE 802.5.
IEEE 802.3: Defines the MAC layer for Bus Networks that use
CSMA/CD (contention). This is the basis of the Ethernet standard.
IEEE 802.4: Defines the MAC layer for bus networks that use a
token-passing mechanism (Token Bus networks).
IEEE 802.5: Defines the MAC layer for Token Ring networks.
IEEE 802.6: Standard for Metropolitan Area Networks (MANs).
IEEE 802.7: Broadband networks.
IEEE 802.8: Fibre optic networks.
IEEE 802.9: Integrated Data and Voice networks (e.g. ISDN).
IEEE 802.10: Interoperable LAN/MAN security.
IEEE 802.11: Wireless LAN media access control.
IEEE 802.12: Demand priority access method for the 100VG-anyLAN
system developed by HP.
IEEE 802.14: Standard protocol for cable TV broadband
communication networks.
<http://webopedia.internet.com/TERM/I/IEEE_802_standards.html>
PC Networking Level 5.doc 51
COMMON NETWORK PROTOCOLS.
NetBIOS (Network Basic Input/Output System) is not really a protocol, rather
an interface running on top of a common protocol on computers networked.
NetBEUI (NetBIOS Extended User Interface) is used on small networks, mainly
peer to peer. Was used on the first version of Windows NT.
Appletalk is a suite of protocols developed by Apple Computer for computer
networking. It was included in the original Macintosh (1984) and is now
deprecated by Apple in favor of TCP/IP networking.
DECnet is used for very large networks. DECnet is a proprietary suite of
network protocols created by Digital Equipment Corporation, originally released
in 1975 in order to connect two PDP-11 minicomputers. It evolved into one of the
first peer-to-peer network architectures, thus making DEC into a networking
powerhouse in the 1980s.
NetWare (IPX (Internet Packet Exchange), SPX (Sequenced Packet
Interchange), SAP (Service Access Protocol), RIP (Routing Information
Protocol), AFP (Apple Filing Protocol). Netware IPX/SPX is a variation of TCP/IP
that Novell developed.
OSI is designed to follow the 7 layer model.
TCP/IP was developed in the late 1970s for the Dept of Defense's ARPA
network. It is becoming even more common. Originally with UNIX, and Microsoft,
Apple and Novell use it as their native protocol now.
PC Networking Level 5.doc 52
C. LINKS between LANs.
In today’s Information Age, Computers are the Productivity Areas (Work
Stations). The Computer Network is like the Production Line and the Distribution
Centre, and even the Point of Sale. If Local Area Networks (LANs) are the “In-
House” production lines, the middle and long distance networks (MANs and
WANs) are the Transportation Links.
Due to a need to move data over greater distances than, say, 1 km, several
techniques have been developed for linking and extending LANs. The techniques
used to link LAN segments depend on:
Distance and speed needed.
Network Communication Protocols being used.
Cost.
Signal degradation and accumulated interference (eg noise) limit the distance
that a high transmission speed cable can extend. LAN to LAN connections move
data more slowly than Local Area Connections, and more technical equipment
and more quality checks are required.
When connections extend beyond a metropolitan area (MAN), it is typical to
lease circuits from suppliers such as Telecom for WAN links. The 3 general
categories for leased services are:
Circuit-switched (Equipment dials a connection, transfers data, and hangs
up when finished).
Full-Period (where a circuit is dedicated to your use all the time).
Packet-Switched (allow multi-point connections for bursts of short packets.
Follow ITU-T X.25 protocol or the newer frame relay standard).
There can also be Dial-Up services.
To lease a circuit to link LAN segments is costly. It makes sense to have good
Network Portal Devices for both ends of the link, so that the expensive circuits
can be used to maximum efficiency.
A PORTAL is the point where networks meet or connect. If you like, they are like
a shipping port (or dock). Portal devices (REPEATERS, BRIDGES and
ROUTERS) extend and segment the Local Area Network’s high-speed link. Each
device offers a different degree of data handling capability, discrimination and
directing capability.
Network Traffic typically follows specific paths, and travels within a group of
computers with common interests (a Workgroup). However, some traffic must
flow between Workgroups. If all Workgroups were linked on the same cable, and
allowed to communicate with each other without restrictions, the resources of the
cable would be severely extended.
PC Networking Level 5.doc 53
D. REPEATERS, BRIDGES and ROUTERS.
A PORTAL is the point where networks meet or connect. If you like, they are like
a shipping port (or dock). Portal devices (REPEATERS, BRIDGES and
ROUTERS) extend and segment the Local Area Network’s high-speed link. Each
device offers a different degree of data handling capability, discrimination and
directing capabilty.
A REPEATER can typically fit in your hand. It connects 2 segments of your
network cabling, retimes and boosts the digital signals, and sends the signals on.
Repeaters are relatively inexpensive, and are easy to install. However, the range
of a high-speed LAN is still very restricted (a couple of km), no matter how many
repeaters you have.
Bridges are more complex than repeaters. A BRIDGE will read the Station
Address of each Ethernet Packet, or of each Token-Ring frame. This is the
outermost envelope around the data. You might recall the HDLC frame from
DC100:Data Communications lessons:
F FCS DATA C A F
This determines the destination of the message. The bridge does not look inside
the package or frame to read NetBIOS, IPX or TCP/IP addresses (i.e. lower
layers of the Data Communications model).
A BRIDGE is a network portal device used to link Workgroup LANs. The bridge
can control what traffic is passed between LAN cable segments --- unlike a
REPEATER which passes all data between cable segments. The 2 purposes of a
BRIDGE are to extend the network, and to isolate network traffic.
A ROUTER is a more complex portal device than a bridge. They are more
expensive, and require more attention than a bridge. However, they are a lot
more efficient in examining and directing traffic, and also in doing Protocol
conversion between different types of LAN.
It digs deeper into the envelopes that surround the data, to find the destination
for the data packet. The router will read the information in each packet or frame,
and by a complex process will determine the appropriate network destination.
The outer envelopes are discarded, and the data is repackaged and
retransmitted. Accordingly, it doesn’t matter too much what type of hardware or
protocols are being used in each LAN segment, because the router handles the
conversion process in it’s repackaging.
PC Networking Level 5.doc 54
Routers also act as a safety barrier between segments. Data packets with errors
just don’t get through. Routers also (because they strip off the outer layers of
data) send information across the interLAN circuit more efficiently than bridges
do (less redundancy). Routers (because of their complex stripping of outer
layers, and network addressing processes) are generally slower than bridges.
They are also more costly.
In recent times, the differences between the capabilities of switches and routers
have narrowed. Routers are also becoming a lot more capable, and can handle
LAN to MAN, and even LAN to WAN that previously required a specialised
GATEWAY connection.
A GATEWAY performs efficient WAN protocol conversion (more about this in
Data Communications - WANs). Routers make very smart connections between
the elements of complex networks.
PC Networking Level 5.doc 55
PC Networking Level 5.doc 56
CONCLUSION.
THANK YOU.
I hope you have enjoyed your journey with this course PC Networking Level 5.
May this be a significant step in your journey of success? Success might be
defined as “the progressive realization of worthwhile goals”. We are very pleased
to be able to work with you.
Please refer to our Web Page at www.ebooksctf.co.nz under the section PC
Networks and Data Communications for other relevant Courses.
Please continue to E-Mail us if you have any questions or comments.
Our E-Mail address is ctf77@xtra.co.nz
Please also feel free to seek our advice about any area where you think
we can help.
Please include (where possible) the Course Name and the Page Number
(these can be found on the footer of each page) if it is a question about a
Course.
Please share your success stories with us. We are delighted to hear from you.
We look forward to your continual success.
PC Networking Level 5.doc 57
PC NETWORKING Level 5.
© Copyright by CTF Services Limited 2005
All rights reserved worldwide. No part of this book may be reproduced or transmitted in
any form, or by any means, electronic or mechanical, including photocopying, recording,
or by any information storage and retrieval system, without the written permission of the
publisher, except where permitted by law.
Published by
CTF Services Limited, 19 Regent St, Timaru 8601, New Zealand
Distributed by
www.ebooksctf.co.nz
PC Networking Level 5.doc 58
Вам также может понравиться
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Offensive Security PDFДокумент21 страницаOffensive Security PDFhariom bansiwalОценок пока нет
- Active Directory Port and Protocol RequirementsДокумент9 страницActive Directory Port and Protocol RequirementsCalvindin DieОценок пока нет
- XML Web Services For The Microsoft .NET PlatformДокумент388 страницXML Web Services For The Microsoft .NET PlatformterdesakОценок пока нет
- PortsДокумент60 страницPortsDerek Feschuk0% (1)
- Client ServerДокумент38 страницClient Serverannamyem100% (1)
- Port NumbersДокумент198 страницPort NumbersMickeyDaisyОценок пока нет
- List of TCP and UDP Port Numbers (Common) Ports 0 To 1023Документ9 страницList of TCP and UDP Port Numbers (Common) Ports 0 To 1023Hà GiangОценок пока нет
- Chapter - 4 - iNTERNET PROTOCOLSДокумент22 страницыChapter - 4 - iNTERNET PROTOCOLSMichael Rey MendozaОценок пока нет
- LAN Protocols and TCP/IP: © N. Ganesan, PH.DДокумент61 страницаLAN Protocols and TCP/IP: © N. Ganesan, PH.DemulatorОценок пока нет
- Lesson 3 Internet ProtocolsДокумент37 страницLesson 3 Internet ProtocolsReign Jay FerrerОценок пока нет
- Cs AbrevationДокумент35 страницCs AbrevationMalik UsmanОценок пока нет
- Lista de Portas PDFДокумент156 страницLista de Portas PDFMarcio GhОценок пока нет
- © 2018 Caendra, Inc. - Netbios HackingДокумент20 страниц© 2018 Caendra, Inc. - Netbios HackingSaw GyiОценок пока нет
- 01 - ReconocimientoДокумент19 страниц01 - ReconocimientoRicardoОценок пока нет
- Protocol EncapsulationДокумент1 страницаProtocol EncapsulationPratik P PatelОценок пока нет
- Acronyms System Security 2015 NGL 2015VI04Документ3 страницыAcronyms System Security 2015 NGL 2015VI04Jason Rocima PartaОценок пока нет
- Nwchapa 1&2Документ52 страницыNwchapa 1&2complicatedsolОценок пока нет
- Nbtstat Command Cheat SheetДокумент5 страницNbtstat Command Cheat SheetChanakyaОценок пока нет
- Interview Questions On Port NumbersДокумент9 страницInterview Questions On Port NumbersShitesh SachanОценок пока нет
- Administrator Reference 1: Operating InstructionsДокумент20 страницAdministrator Reference 1: Operating InstructionsWagner DuarteОценок пока нет
- How To Connect To iSCSI Targets On QNAP NAS Using MPIO On Windows 2008Документ30 страницHow To Connect To iSCSI Targets On QNAP NAS Using MPIO On Windows 2008Jazz OberoiОценок пока нет
- BECKHOFF NA02 TC - CX (v1.1)Документ32 страницыBECKHOFF NA02 TC - CX (v1.1)Jorge_Andril_5370Оценок пока нет
- Important Port NumberДокумент5 страницImportant Port NumberAbdul MohammedОценок пока нет
- 8.51 MailAdminДокумент75 страниц8.51 MailAdminShailesh SurroopОценок пока нет
- Ad 01Документ7 страницAd 01Tirthankar ChakrabortyОценок пока нет
- Canon ImageRUNNER IR3570 Network Management GuideДокумент278 страницCanon ImageRUNNER IR3570 Network Management GuidefranklynberryОценок пока нет
- List of TCP and UDP Port NumbersДокумент100 страницList of TCP and UDP Port NumbersKarthikeyan BalasubramaniamОценок пока нет
- Software, Configuration of SOMARIS 5 CSTD CT02-023.805.02 CT00-000.843.02Документ138 страницSoftware, Configuration of SOMARIS 5 CSTD CT02-023.805.02 CT00-000.843.02Klaus BöhmdorferОценок пока нет
- Used To Manage and Monitor The NetworkДокумент35 страницUsed To Manage and Monitor The NetworkFikru TesefayeОценок пока нет
- DP-301U Printer Compatibility ListДокумент4 страницыDP-301U Printer Compatibility ListAndry RAQAОценок пока нет