Академический Документы
Профессиональный Документы
Культура Документы
Ap Soc
Загружено:
Krishna CooldudeОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Ap Soc
Загружено:
Krishna CooldudeАвторское право:
Доступные форматы
Government of Andhra Pradesh
Andhra Pradesh Technology Services
__________________________________________________
Tender Ref: APTS/N/CYBERSECURITY/AP-SOC/2017
Andhra Pradesh Cyber Security Operation Center (AP-
SOC) services
in the
State of Andhra Pradesh
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Table of Contents
Due Diligence ......................................................................................................................................................13
Abbreviations ......................................................................................................................................................14
1. Key Information .............................................................................................................................................16
1.1. Fact Sheet ................................................................................................................................................16
1.2. Purpose of this RFP ................................................................................................................................18
2. Background – Cyber Security .......................................................................................................................19
3. APTS Overview ..............................................................................................................................................21
4. Attractive Investment Avenue – The State of Andhra Pradesh .................................................................22
5. AP Cyber Security Project Vision .................................................................................................................23
6. Project Objective ............................................................................................................................................24
7. Project Coverage and Duration.....................................................................................................................25
7.1. Coverage .................................................................................................................................................25
7.1.1. AP Government Infrastructure ......................................................................................................25
7.1.2. Small and Medium Enterprise (SME) ...........................................................................................25
7.1.3. Other Clients..................................................................................................................................25
7.2. Duration ..................................................................................................................................................26
7.2.1. Design & Implementation phase ...................................................................................................26
7.2.2. Operations & Management of AP-SOC phase ..............................................................................26
8. Proposed Services – Core Services ................................................................................................................27
8.1. Threat Monitoring, Analytics & Incident Management ..........................................................................27
8.2. Security Infrastructure Device Management ..........................................................................................27
8.3. Threat Surface Management Services.....................................................................................................27
8.4. Brand Monitoring and Protection Services .............................................................................................27
9. Responsibilities of the Stakeholders ..............................................................................................................28
9.1. Responsibilities of the Bidder/Service Provider .....................................................................................28
9.1.1. Technology infrastructure .............................................................................................................28
9.1.2. People/Resources...........................................................................................................................28
9.1.3. Processes .......................................................................................................................................28
9.2. Responsibilities of the Departments / Agencies......................................................................................29
9.3. Responsibilities of APTS ........................................................................................................................29
9.3.1. AP-SOC Facility ............................................................................................................................29
9.3.2. Responsibility Matrix ....................................................................................................................29
9.4. Services commitment by GoAP/APTS ...................................................................................................30
10. Detailed Scope of Work................................................................................................................................31
10.1. Threat Monitoring, Analytics & Incident Management ........................................................................31
Andhra Pradesh Technology Services Page 2 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
10.1.1. Service Objective.........................................................................................................................31
10.1.2. Service Coverage & scope...........................................................................................................31
10.1.3. Design, Operations & Sizing consideration: ...............................................................................31
10.2. Security Infrastructure Device Management ........................................................................................33
10.2.1. Service Objective.........................................................................................................................33
10.2.2. Service Coverage & scope...........................................................................................................33
10.2.3. Design, Operations & Sizing consideration ................................................................................34
10.3. Threat Surface Management Services...................................................................................................36
10.3.1. Service Objective.........................................................................................................................36
10.3.2. Service Coverage & Scope ..........................................................................................................36
10.3.3. Design, Operations & Sizing consideration ................................................................................36
10.3.4. Features and Success criteria .......................................................................................................37
10.4. Brand Monitoring & Protection Services..............................................................................................37
10.4.1. Service Objective.........................................................................................................................37
10.4.2. Service Coverage and Scope .......................................................................................................37
10.4.3. Features and Success criteria .......................................................................................................38
10.5. Establishment and Operationalization of DR........................................................................................39
10.6. Tools/Services Required as part of the Scope of the RFP ....................................................................39
10.7. Design Principles of AP-SOC ...............................................................................................................39
10.8. Scalability .............................................................................................................................................39
10.9. Availability ...........................................................................................................................................39
10.10. Functional Principles...........................................................................................................................40
10.11. Video Wall ..........................................................................................................................................40
10.12. Infrastructure to be deployed in the AP-SOC .....................................................................................40
11. Project Implementation Timelines ..............................................................................................................42
11.1. Reports ..................................................................................................................................................45
12. Instructions to the Bidder ............................................................................................................................46
12.1. Language of the Bid ..............................................................................................................................46
12.2. Validity of the Proposal ........................................................................................................................46
12.3. Acceptance of the Proposal ...................................................................................................................46
12.4. Fraud and Corruption ............................................................................................................................46
12.5. Amendment of Tender Document.........................................................................................................47
12.6. Clarification on RFP Response .............................................................................................................47
12.7. Purchase of RFP Documents.................................................................................................................47
12.8. Bid Format ............................................................................................................................................48
12.9. Information for Proposal Submission ...................................................................................................48
12.9.1. Contact Details ............................................................................................................................48
Andhra Pradesh Technology Services Page 3 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
12.9.2. Authentication of Bid ..................................................................................................................48
12.10. Pre Qualification Criteria ....................................................................................................................48
12.10.1. The Bidder .................................................................................................................................48
12.10.2. Conflict of Interest.....................................................................................................................51
12.10.3. Right to Terminate the Bid Process ...........................................................................................51
12.10.4. Earnest Money Deposit .............................................................................................................51
13. Bidding Process.............................................................................................................................................52
13.1. Pre-Bid Meeting and Clarifications ......................................................................................................52
13.2. Supplementary Information/ Corrigendum / Amendment to the RFP ..................................................53
13.3. Cost of Bid Preparation .........................................................................................................................53
13.4. Bid Submission .....................................................................................................................................53
13.4.1. Availability of Tender Documents ..............................................................................................53
13.4.2. Registration of Vendors ...............................................................................................................54
13.4.3. Late Bids......................................................................................................................................54
13.4.4. Digital Certificate Authentication ...............................................................................................54
13.4.5. Payment of Transaction fee .........................................................................................................54
13.4.6. Corpus fund .................................................................................................................................54
13.4.7. Mode of Submission ....................................................................................................................54
13.4.8. Bid Submission Acknowledgement.............................................................................................54
13.4.9. Deactivation of Bidders ...............................................................................................................55
13.4.10. Submission of original EMD, Tender document fee and Proposal Documents ........................55
13.5. Proposal Format ....................................................................................................................................56
13.5.1. Pre-qualification Proposal ...........................................................................................................56
13.5.2. Technical Bid...............................................................................................................................56
13.5.3. Commercial Proposal ..................................................................................................................57
13.6. Modification and Withdrawal of Bids ..................................................................................................58
13.7. Conditions under which this RFP is issued ...........................................................................................59
13.8. Rights to the Content of Proposal .........................................................................................................60
13.9. Non-Conforming Proposals ..................................................................................................................60
14. Bid Opening and Bid Evaluation Process...................................................................................................61
14.1. Bid Opening ..........................................................................................................................................61
14.2. Bid Evaluation Process .........................................................................................................................61
14.2.1. Preliminary Scrutiny ....................................................................................................................61
14.2.2. Evaluation of Pre-Qualification Criteria......................................................................................61
14.2.3. Evaluation of Technical Bids ......................................................................................................61
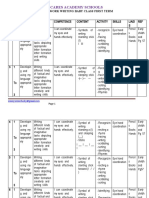
14.2.4. Criteria for Technical Evaluation ................................................................................................62
14.2.5. Proposed Man Power ...................................................................................................................63
Andhra Pradesh Technology Services Page 4 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
14.2.6. Qualifications required for the proposed Team ...........................................................................64
14.2.7. Technical Presentations ...............................................................................................................67
14.3. Commercial Bid Opening and Evaluation Process ...............................................................................67
14.3.1. Bid Opening.................................................................................................................................67
14.3.2. Announcement of Bids ................................................................................................................67
14.3.3. Clarification on Commercial Bids ...............................................................................................67
14.3.4. Evaluation of Commercial Bids ..................................................................................................68
14.3.5. Total Bid Evaluation....................................................................................................................68
14.4. Award of Contract.................................................................................................................................68
14.4.1. Notification of Award..................................................................................................................68
14.4.2. Performance Security ..................................................................................................................69
14.4.3. APTS’s Right to accept / reject any proposal or all proposals ....................................................69
14.4.4. Signing of Contract......................................................................................................................69
14.4.5. Failure to agree with the Terms & Conditions of the RFP ..........................................................69
14.5. Disqualification .....................................................................................................................................69
15. Service Level Agreement..............................................................................................................................71
15.1. Definitions.............................................................................................................................................71
15.2. Interpretation & General Instructions ...................................................................................................71
15.3. Implementation Phase related Performance Levels ..............................................................................72
15.4. Operations .............................................................................................................................................74
15.4.1. (AP-SOC) ....................................................................................................................................74
15.4.2. Security Device Management......................................................................................................78
15.4.3. Threat Surface Management Services .........................................................................................81
15.4.4. Brand Monitoring and Protection Services .................................................................................81
15.4.5. Others SLA ..................................................................................................................................82
16. Payment and Invoicing Process ...................................................................................................................83
16.1. Payment Process ...................................................................................................................................83
16.1.1. Payment Milestones for BOM as specified in the RFP ...............................................................83
16.1.2. Payment Milestones for the Services to be delivered as per the scope of the RFP .....................83
16.2. Volume discounts..................................................................................................................................84
16.3. Invoicing & Settlement Process ............................................................................................................84
17. Bid Submission Forms and Undertakings
..............................................................................................................................................................................Er
ror! Bookmark not defined.
17.1. Forms for Submission of Pre-Qualification
.......................................................................................................................................................................E
rror! Bookmark not defined.
Andhra Pradesh Technology Services Page 5 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
17.1.1. Form P1: Bid Application Form
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.2. Form P2: Details of the Bidder
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.3. Form P3: Bidders Authorization Letter
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.4. Form P4: Undertaking form for AP GST Registration
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.5. Form P5: Certificate from Statutory Auditor stating average annual turnover of the firm
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.6. Form P6: Certificate from Statutory Auditor stating Average annual turnover of the firm from
Information Security services
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.7. Form P7: Experience of the Bidder – SOC Services
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.8. Form P8: Experience of the Bidder – MSS based Services
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.9. Form P9: Declaration regarding clean track record
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.10. Form P10: Experience of the Bidder – SIEM
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.11. Form P11: Technically Qualified Personnel’s
.................................................................................................................................................................E
rror! Bookmark not defined.
17.1.12. Form P11: Manufacturers Authorization Form
.................................................................................................................................................................E
rror! Bookmark not defined.
Andhra Pradesh Technology Services Page 6 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
17.2. Forms for Submission of Technical Criteria
.......................................................................................................................................................................E
rror! Bookmark not defined.
17.2.1. Form T1 – Total Average Annual Turnover
.................................................................................................................................................................E
rror! Bookmark not defined.
17.2.2. Form T2 – Total Average Annual Turnover exclusively from Information Security Services
.................................................................................................................................................................E
rror! Bookmark not defined.
17.2.3. Form T3- Details of Projects with Successful Implementation of proposed SIEM
.................................................................................................................................................................E
rror! Bookmark not defined.
17.2.4. Form T4 – Details of AP-SOC Assignments in last 3 financial years
.................................................................................................................................................................E
rror! Bookmark not defined.
17.2.5. Form T5 – Details of MSS (Managed Security Services) Assignments in last 3 financial years
.................................................................................................................................................................E
rror! Bookmark not defined.
17.2.6. Form T6 – Details of Technically Qualified Personnel from the area of IT Security Services and
are on the Bidders payroll for the past three years
.................................................................................................................................................................E
rror! Bookmark not defined.
17.3. Instructions and Forms for Submission of Price Bid
.......................................................................................................................................................................E
rror! Bookmark not defined.
17.3.1. General Instructions
.................................................................................................................................................................E
rror! Bookmark not defined.
17.3.2. Price Bid Letter
.................................................................................................................................................................E
rror! Bookmark not defined.
18. Format for EMD
..............................................................................................................................................................................Er
ror! Bookmark not defined.
19. Formats for Performance Security/Bank Guarantee
..............................................................................................................................................................................Er
ror! Bookmark not defined.
Andhra Pradesh Technology Services Page 7 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
20. Non-Disclosure Agreement
..............................................................................................................................................................................Er
ror! Bookmark not defined.
21. Draft Master Service Agreement
..............................................................................................................................................................................Er
ror! Bookmark not defined.
Definitions
.......................................................................................................................................................................E
rror! Bookmark not defined.
General Eligibility
.......................................................................................................................................................................E
rror! Bookmark not defined.
Bid forms
.......................................................................................................................................................................E
rror! Bookmark not defined.
Cost of bidding
.......................................................................................................................................................................E
rror! Bookmark not defined.
Clarification of bidding documents
.......................................................................................................................................................................E
rror! Bookmark not defined.
Amendment of bidding documents
.......................................................................................................................................................................E
rror! Bookmark not defined.
Period of validity of bids
.......................................................................................................................................................................E
rror! Bookmark not defined.
Submission of bids
.......................................................................................................................................................................E
rror! Bookmark not defined.
Deadline for submission of bids
.......................................................................................................................................................................E
rror! Bookmark not defined.
Late bids
.......................................................................................................................................................................E
rror! Bookmark not defined.
Andhra Pradesh Technology Services Page 8 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Modification and withdrawal of bids
.......................................................................................................................................................................E
rror! Bookmark not defined.
General Business information
.......................................................................................................................................................................E
rror! Bookmark not defined.
Bid security i.e. earnest money deposit (EMD)
.......................................................................................................................................................................E
rror! Bookmark not defined.
Preparation of financial bid
.......................................................................................................................................................................E
rror! Bookmark not defined.
Bid currency
.......................................................................................................................................................................E
rror! Bookmark not defined.
Taxes
.......................................................................................................................................................................E
rror! Bookmark not defined.
Term and Extension of Contract
.......................................................................................................................................................................E
rror! Bookmark not defined.
Suspension of Work
.......................................................................................................................................................................E
rror! Bookmark not defined.
Limitation of Liability
.......................................................................................................................................................................E
rror! Bookmark not defined.
Force majeure
.......................................................................................................................................................................E
rror! Bookmark not defined.
Terminate the Contract
.......................................................................................................................................................................E
rror! Bookmark not defined.
Termination
.......................................................................................................................................................................E
rror! Bookmark not defined.
Andhra Pradesh Technology Services Page 9 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Termination for insolvency
.......................................................................................................................................................................E
rror! Bookmark not defined.
Termination for convenience
.......................................................................................................................................................................E
rror! Bookmark not defined.
Right of Monitoring, Inspection and Periodic Audit
.......................................................................................................................................................................E
rror! Bookmark not defined.
Risk Management
.......................................................................................................................................................................E
rror! Bookmark not defined.
Publicity
.......................................................................................................................................................................E
rror! Bookmark not defined.
Resolution of disputes
.......................................................................................................................................................................E
rror! Bookmark not defined.
Governing language
.......................................................................................................................................................................E
rror! Bookmark not defined.
Applicable law
.......................................................................................................................................................................E
rror! Bookmark not defined.
Notices
.......................................................................................................................................................................E
rror! Bookmark not defined.
Taxes and duties
.......................................................................................................................................................................E
rror! Bookmark not defined.
Arbitration (As per the State Government Rules)
.......................................................................................................................................................................E
rror! Bookmark not defined.
Confidentiality and Intellectual Property Rights (IPR)
.................................................................................................................................................................E
rror! Bookmark not defined.
Andhra Pradesh Technology Services Page 10 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Conflict of Interest
.................................................................................................................................................................E
rror! Bookmark not defined.
22. Compliance Requirements
..............................................................................................................................................................................Er
ror! Bookmark not defined.
22.1. Pre- Qualification Compliance
.......................................................................................................................................................................E
rror! Bookmark not defined.
22.2. Technical Compliance
.......................................................................................................................................................................E
rror! Bookmark not defined.
23. Annexure: Network and IT Infrastructure in the State of AP
..............................................................................................................................................................................Er
ror! Bookmark not defined.
Andhra Pradesh Technology Services Page 11 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
DISCLAIMER
The information contained in this Tender or subsequently provided to bidders, whether verbally or in
documentary or any other form by or on behalf of the APTS herein called the Authority or any of its
employees or advisers, is provided to bidders on the terms and conditions set out in this Tender and
such other terms and conditions subject to which such information is provided.
This Tender is issued by the Andhra Pradesh Technology Services, Vijayawada. This Tender is not an
agreement and is neither an offer nor invitation by the Authority to the prospective bidders or any other person.
The purpose of this Tender is to is to solicit Techno commercial offers from interested parties for taking part in
the implementation and management of cyber security operations center in the scope of work as mentioned in
this document. This Tender includes statements, which reflect various assumptions and assessments arrived at
by the Authority in relation to the Implementation and Management of Cyber Security Operation Center. Such
assumptions, assessments and statements do not purport to contain all the information that each Applicant may
require. This Tender may not be appropriate for all persons, and it is not possible for the Authority, its
employees or advisers to consider the objectives, technical expertise and particular needs of each party who
reads or uses this Tender. The assumptions, assessments, statements and information contained in this
Tender, may not be complete, accurate, adequate or correct. Each Applicant should, therefore, conduct its
own investigations and analysis and should check the accuracy, adequacy, correctness, reliability and
completeness of the assumptions, assessments and information contained in this Tender and obtains
independent advice from appropriate sources.
Information provided in this Tender to the bidders is on a wide range of matters, some of which depends upon
interpretation of law. The information given is not an exhaustive account of statutory requirements and should
not be regarded as a complete or authoritative statement of law. The Authority accepts no responsibility for the
accuracy or otherwise for any interpretation or opinion on the law expressed herein.
The Authority, its employees and advisers make no representation or warranty and shall have no liability to any
person including any Applicant under any law, statute, and rules or regulations or tort, principles of restitution
or unjust enrichment or otherwise for any loss, damages, cost or expense which may arise from or be incurred
or suffered on account of anything contained in this Tender or otherwise, including the accuracy,
adequacy, correctness, reliability or completeness of the Tender and any assessment, assumption,
statement or information contained therein or deemed to form part of this Tender or arising in any way in this
Selection of Service Provider.
The Authority also accepts no liability of any nature whether resulting from negligence Or otherwise
however caused arising from reliance of any Bidder upon the statements contained in this Tender. The
Authority may in its absolute discretion, but without being under any obligation to do so, update, amend or
supplement the information, assessment or assumption contained in this Tender. The issue of this Tender
does not imply that the Authority is bound to select an Bidder or bidders, as the case may be, for the
selection of Cyber AP-SOC services and the Authority reserves the right to reject all or any of the Proposals
without assigning any reasons whatsoever.
The Bidder shall bear all its costs associated with or relating to the preparation and submission of its Proposal
including but not limited to preparation, copying, postage, delivery fees, expenses associated with any
demonstrations or presentations which may be required by the Authority or any other costs incurred in
connection with or relating to its Proposal. All such costs and expenses will remain with the Bidder and the
Authority shall not be liable in any manner whatsoever for the same or for any other costs or other
expenses incurred by a Bidder in preparation or submission of the Bid, regardless of the conduct or outcome of
the Selection Process.
Andhra Pradesh Technology Services Page 12 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Due Diligence
The Bidder is expected to examine all instructions, forms, terms and specifications in this RFP and study the
Bid Document carefully. Bid shall be deemed to have been submitted after careful study and examination of
this RFP with full understanding of its implications.
Each Bidder should, at its own costs without any right to claim reimbursement, conduct its own
investigations, analysis and should check the accuracy, reliability and completeness of the information in
this RFP and wherever felt necessary obtain independent advice. The Bid should be precise, complete
and in the prescribed format as per the requirement of this RFP. Failure to furnish all information required by
this RFP or submission of a Bid not responsive to this RFP in each and every respect shall be at the
Bidder’s own risk and may result in rejection of the Bid and for which the APTS shall not be held responsible.
Any decision taken by APTS as to completeness of the Bid and/or rejection of any/ all Bid(s) shall be
final, conclusive and upon the Bidder(s) and shall not be question / challenged by the Bidder(s).
Andhra Pradesh Technology Services Page 13 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Abbreviations
Abbreviation Description
API Application Programming Interface
APT Advances Persistent Threat
APTS Andhra Pradesh Technology Services , Also referred as “Authority”
BG APTS Guarantee
CERT Computer Emergency Response Team
CISA Certified Information Systems Auditor
CISSP Certified Information Systems Security Professional
AP-SOC AP Cyber Security Operations Centre
CND Computer Network Defence
DAM Database Activity Monitoring
DD Demand Draft
DLP Data Loss Prevention
DR Disaster Recovery
EMD Earnest Money Deposit
EPS Events Per Second
FRS Functional Requirement Specifications
GIS Geographic Information System
GoAP Government of Andhra Pradesh
GRC Governance, Risk and Compliance
GST Goods and Service Tax
ICT Information and Communication Technology
IDS Intrusion Detection System
IoT Internet of Things
IPS Intrusion Prevention System
ISO International Standards Organization
IT E&C
IT Electronics & Communication Department
Department
ITIL Information Technology Infrastructure Library
LOI Letter of Intent
MD Managing Director
NAC Network Access Control
NIST National Institute of Standards and Technology
OEM Original Equipment Manufacturer
OSWAP Open Web Application Security Project
PIM Privileged Identity Manager
QCBS Quality and Cost based Selection
RFP Request For Proposal
SAN Storage Access Network
Andhra Pradesh Technology Services Page 14 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Abbreviation Description
SAP Systems, Applications, Products in Data Processing
SI Systems Integrator
SIEM Security Information and Event Management tool
SLA Service Level Agreement
SME Subject Matter Expert
AP-SOC AP Security Operations Center
SOP Standard Operation Procedure
SPOC Single Point of Contact
SQL Structured Query Language
SRS System Requirement Specifications
SSH Services or Secure Shell
SSL Secure sockets Layer
T&M Time and Material
TTP Tactics, Techniques and Procedures
User Department The Departments which shall use these services as per the scope of this document
VA Vulnerability Assessment
VPN Virtual Private Network
VLAN Virtual Local Area Network
WAF Web Application Firewall
Andhra Pradesh Technology Services Page 15 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
1. Key Information
1.1. Fact Sheet
S. No Item Details
1. RFP reference No and Date APTS/N/CYBERSECURITY/AP-SOC/2017
Rs. 50,000/- (Rupees Fifty Thousand only) (DD in the
2. Non-Refundable Tender Cost favour of The Managing Director, Andhra Pradesh
Technology Services Limited payable at Vijayawada.
Publication of Tender Document through e-
3. 08/09/2017
Tender
15/09/2017, 5.00PM (No written Queries would be
4. Last date for Submission of Pre-Bid Queries
considered beyond the said date and time)
16/09/2017, AT 10.3o AM at Conference Hall, 3rd
5. Pre-Bid Conference Date, Time & Venue
Floor, APSFL, RTC Bhavan, Vijayawada, AP
6. Publish Response to Pre-bid queries 21/09/2017
7. Last Date and Time for Submission of Bids 27/09/2017, 2.00 PM
Venue/ Locations for opening of technical
8. On e-procurement Website
bids and Financial bids
Prequalification Bid opening date on e-
9. 27/09/2017, 2.30 PM
procurement platform
10. Indicative date for Technical presentation 04/10/2017 and 5/10/2017
11. APTS Contact Person for any Queries Mr. K.Dhavuryan Naik, Manager (Cyber Security)
12. APTS Contact Person E-Mail ID dhavuryannaik.k@gov.in,
13. APTS Contact Person Contact Number Mr. K.Dhavuryan Naik: 09963029418
The method of selection is Least Cost (L1) among the
14. Method of Selection
technically qualified bidders.
Three-Stage Bid System
1. Pre-qualification Bid
15. Bid Process Stages
2. Technical Bid
3. Financial / Price Bid
16. EMD Rs. 25,00,000/-
Date and Time of submission of original
copies of EMD (Physical Copy), tender
17. document fee (Physical Copy) and 1 hard 27/09/2017, 2.30PM
copies of Technical Proposal and One
Softcopy to the O/o MD APTS
18. Performance Security Rs. 10% of contract value
1. Submission of PBG within 7 calendar days
2. PBG validity: 90 days beyond contract period
19. Performance Security validity period
Submission of PBG: Within 10 days of receipt of letter
of notification of award
Andhra Pradesh Technology Services Page 16 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
S. No Item Details
Maximum period to sign the contract is 12 calendar
20. Period of Signing the contract
days from the date of issue of Letter of Award (LoA).
180 working days from the date of submission of
21. Bid Validity
online bids
22. Contract period As per the timelines defined in the RFP
Minimum of 75 Marks
23. Technical Evaluation Minimum Cut off
Score
Andhra Pradesh Technology Services Page 17 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
1.2. Purpose of this RFP
Purpose of this RFP is for Selection of Service Provider for AP Cyber Security Operation Centre (AP-SOC)
services in the state of Andhra Pradesh.
RFP Format
The intent of this RFP is to invite proposals from the prospective bidders and the contents are provided in
following Sections:
RFP Body: Scope, Bidding Instructions and Terms & Conditions
This RFP document consists of the instructions to the respective bidders on the process of bids submission
with respective forms to be submitted by the bidder for each category of bid evaluation
Andhra Pradesh Technology Services Page 18 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
2. Background – Cyber Security
Andhra Pradesh has been a pioneer in the use of ICT for delivery of public services. The state has one of the
largest number of e-governance services. Be it the Meeseva portal offering certificates, District Portal for
aggregating information, HUDHUD portal for efficient enumeration, AP-SRDH aligning Aadhaar with state
govt. welfare schemes, AP State portal for various govt. departments, eProcurement for automating state
government procurement and purchase procedures, Citizen Friendly Services of Transport Department (CFST),
Computer aided Administration of Registration Department (CARD), state of AP has delivered abundant
digitization initiatives catering to vision of Digital India initiative: Digital infrastructure as a core utility to
every citizen, Governance and Services on Demand, Digital empowerment of citizens.
Within India, Security incidents in 2016 have increased by around 82% from 2015. The types of incidents
handled were mostly related to malicious code, phishing, website intrusion, spam, network scanning and
probing and malware propagation. A report by the National Crime Records Bureau (NCRB), Ministry of Home
Affairs, Government of India, titled Crime in India-2014, shows a 69% increase in cases reported under the
Information Technology (IT) Act in 2014 from the year before.
It is necessary to highlight that a cyber security program is just not about existing technology – it is also about
developing standards & guidelines to promote security, developing a capacity in terms of both law
enforcement, and niche technical skills, and creating a governance structure to ensure public and private sector
entities adhere to the state guidelines.
Government of India had notified the “National Cyber Security Policy in 2013”. The National Policy lays down
a number of strategies for realizing the vision of ‘building a secure and resilient cyberspace for citizens,
businesses and Government’. These strategies seek to create an assurance framework; strengthen the regulatory
framework; create capabilities and systems required for assessment of risks, early warning and incident
management; protect Critical Information Infrastructure; secure e-Government services; develop human
resources, and above all, create an all-round awareness of the importance of cyber security.
The e-Pragati Program being currently implemented by the Government is based on a whole-of-government
approach, whereby all the e-Governance systems are interconnected and integrated and provide a wide range of
services online. Core datasets like the People Hub, Land Hub, Entity Hub, GIS Hub and IoT Hub will be
created and extensively used in providing digital services. The AP FibreNet initiative will make universal
access to Internet a reality soon.
In this context, it is all the more necessary for Andhra Pradesh to fortify its cyber security mechanisms and
create a robust security ecosystem in the State. The Government feels it expedient to establish the Andhra
Andhra Pradesh Technology Services Page 19 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Pradesh Cyber Security Policy, to complement and supplement the National Cyber Security Policy 2013, and to
give a practical effect to it in the State.
The State of Andhra Pradesh has been a pioneer in the use of ICTs extensively for delivery of public services
and felt the need to establish “Andhra Pradesh Cyber Security Policy” to complement and supplement the
National Cyber Security Policy 2013 and issued a vide G.O MS 2 dated 01.03.2017 “Andhra Pradesh Cyber
Security Policy 2017”.
Please visit www.goir.ap.go.in for G.O.MS NO.2, Dated 01-03-2017.
Andhra Pradesh Technology Services Page 20 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
3. APTS Overview
Andhra Pradesh Technology Services (APTS) is a government owned company incorporated in the year 1986,
under the administrative control of IT, E&C Department.
APTS is a self-sustained company whose major activities are Implementation of major IT Projects in Andhra
Pradesh, Software development, IT Consultancy services, Partnerships, Audits and Appraisals etc.
APTS is also focusing on Establishing MoUs, JVs and SPVs with technology partners for adopting new &
innovative technologies and to promote and market the technologies across the country.
APTS is identified by government as nodal agency for implementation of Cyber Security Policy.
Andhra Pradesh Technology Services Page 21 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
4. Attractive Investment Avenue – The State of
Andhra Pradesh
An effective policy for the development of IT should base itself on the four pillars, namely, Human Capital,
Infrastructure, Incentives and above all, a system of Good Governance
Andhra Pradesh has published the vision as below:
“To develop AP as an Innovation Society of global repute, with a focus on enhancing the Quality of
Life of its citizens, through high-quality Education and Healthcare, increased productivity in
Agriculture and allied activities, creation of Employment by promoting Electronics and IT, and above
all, by providing Good Governance”
Some of the Incentives are as part of the IT Policy are as follows:
S.No Incentives Applicable as per the Policy
1. In case of Mega Projects with Land, fiscal incentive will be @INR 50,000 per employee OR 6
months CTC (cost to company), whichever is lower.
2. In case of General Projects with Land, fiscal incentive will be @INR 50,000 per employee OR 6
months CTC (cost to company), whichever is lower.
3. In case of General Projects without Land, fiscal incentive will be @INR 1,00,000 per employee
OR 6 months CTC (cost to company), whichever is lower.
4. In case of MSME/ BC/ SC/ ST/ Women/ Rural IT Projects, fiscal incentive will be @INR
1,50,000 per employee OR 6 months CTC (cost to company), whichever is lower.
Bidders are requested to go through the link below to understand the detailed policy incentives for IT in AP
1. AP IT Policy 2014-20
http://www.apiic.in/wp-content/uploads/2015/07/AP-IT-Policy-2014-2020.pdf
2. Amendments to AP IT Policy 2014-20
http://www.apit.ap.gov.in/Other%20Docs/2016ITC_MS21.PDF
The AP-SOC Service Provider shall open an office and operate, deliver the services from the jurisdiction of AP
CRDA region.
Andhra Pradesh Technology Services Page 22 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
5. AP Cyber Security Project Vision
The State of Andhra Pradesh has been a pioneer in the use of ICTs extensively for delivery of public services.
The e-Pragati Program being currently implemented by the Government is based on a whole-of-government
approach, whereby all the e-Governance systems are interconnected and integrated and provides a wide range
of services online.
Core datasets like the People Hub, Land Hub, Entity Hub, GIS Hub and IoT Hub will be created and
extensively used in providing digital services. The AP FibreNet initiative will make universal access to Internet
a reality soon. In this context, it is all the more necessary for Andhra Pradesh to fortify its cyber security
mechanisms and create a robust security ecosystem in the State.
The vision of Andhra Pradesh Cyber Security Policy is “to create a robust ecosystem, wherein the citizens can
transact online securely and take steps to protect their identity, privacy and finances online, the businesses
conduct their operations without any disruption or damage and the Government ensures that its data and ICT
systems are secure”
The Policy outlines the specific steps and initiatives to be taken by the Government and all other stakeholders
to realize the Vision stated above.
Andhra Pradesh Technology Services Page 23 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
6. Project Objective
In view of the growing use of IT and evolving new threat and vulnerable environment, Government of Andhra
Pradesh intends to select a Service Provider with suitable security solution to implement the Cyber Security
Operations Centre (AP-SOC) in well-phased manner clearly demonstrating value to all beneficiaries of the
project and provides comprehensive awareness and of cyber threats to the Government and SME’s across the
state. AP-SOC will act as state of art and shall also act as center for detection and defense with its excellence
where as it will also provide logical security to different department within state.
Government of Andhra Pradesh (GoAP) intends to select a service provider with suitable security service to
implement the Andhra Pradesh Cyber - Security Operations Centre (AP-SOC) in well-phased manner clearly
demonstrating value to all Stakeholders. AP-SOC will act as state of art and shall act as center for
Identification, detection and response to Cyber Security to various departments in the state. As part of the
roadmap, Government of AP would like to setup Computer Emergency Response Team (CERT) in the State
and would like to leverage AP-SOC for the same. AP-SOC will help the government to baseline security across
the state departments and improve the security awareness and monitoring to build CERT-AP in the state.
APTS intends to invite bids from suitable Service Provider to design, implementation and operations of a
Andhra Pradesh Cyber - Security Operations Centre (AP-SOC) to provide comprehensive information security
monitoring and possible remediation. The overview of the initiative is as follows:-
1. Select AP-SOC Service Provider to provide Security Monitoring Services in the State on a Service Model –
“Pay as per usage”.
2. Provide Security Monitor services for the Government and Critical Information Infrastructure (CII) and can
also extend the services to Small and Medium Enterprises (SME) in State to promote investment and create
job opportunities.
3. Bidder is responsible for the Implementation and Operations of services covering core technology
components , People and Process. APTS is responsible to provide the Data centre space and AP-SOC
facility.
4. Core services proposed to be provided include
a. Threat monitoring, Analytics and Incident Management
b. Security Infrastructure Device Management
c. Threat Surface Management Services
d. Brand Monitoring and Protection Services.
Andhra Pradesh Technology Services Page 24 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
7. Project Coverage and Duration
The selected AP-SOC service provider will perform the design, operations and management of security
services for the various Government departments in the state of Andhra Pradesh. The services can also be
extended to SME’s in the state and other states in due course of action in discussions with APTS/any
designated authority
7.1. Coverage
AP-SOC will provide services to the following stakeholders as follows:
7.1.1. AP Government Infrastructure
AP-SOC will monitor Government assets and Infrastructure deployed at State Data Centre and other AP
Government Departments. To enable this, AP Govt. will make it mandatory by a Govt. Order for all AP Govt.
department to consume the AP-SOC services. Bidder will coordinate with Govt. Dept. to ensure AP-SOC is
integrated with Depts. assets. APTS will facilitate the communication and coordination, if required. Existing
infrastructure and department details are provided in the Annexure. There are number of IT initiatives in the
state which are in progress and these application/devices will also be integrated with AP-SOC over a period of
time.
Most of the state departments have hosted their applications in the State Data Centre (SDC). However, some of
the departments have their own Data centre as well. All these applications, IT infrastructure will be monitored
using AP-SOC over a period of time.
All the government applications shall eventually hosted in common data centre (Pi data centre) in
Andhra Pradesh
7.1.2. Small and Medium Enterprise (SME)
In order to promote investment in the State, Government is planning to provide Cyber Security monitoring
services to various SME clients who would like to operate from the State. Bidder is expected to maintain
logical and physical segregation between the AP-SOC consumer entities and will put security controls in place
to ensure zero data leakage between AP-SOC consumer entities. APTS may, from time to time, ask for
compliance report and can engage third parties to audit compliance.
7.1.3. Other Clients
APTS would like to create local employment opportunities and build local cyber security expertise in the State
and generate additional revenue. Bidder can offer the security services to other State Government and Private
Clients in the country. If required, APTS will extend support to bidder for the coordination and facilitation in
proposing these services to other State Government and PSU.
Bidders is expected to provide revenue sharing to APTS for any such services provided to other clients from the
same facilities. The price offered to other entities for similar service levels will not be lower than price offered
to AP Govt.
Bidder is expected to maintain logical segregation between the AP-SOC consumer entities and will put
appropriate controls in place to ensure zero data leakage between AP-SOC consumer entities. APTS may, from
time to time, ask for compliance report and can engage third parties to audit compliance.
Andhra Pradesh Technology Services Page 25 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Note: Services mentioned in the RFP and respective SLA is for the govt. of AP only or the
clients for which payment is made by GoAP. Bidder is free to provide additional services or
modified SLA to agencies/departments outside AP government client.
7.2. Duration
1. The partnership shall initially for a period of 3 years extendable by additional 2 years basis on the
performance and service provided by the selected bidder on a mutually agreed terms.
7.2.1. Design & Implementation phase
1. Bidder will design, procure and implement the AP-SOC services within 60 days from the signing of the
contract. This will include deployment and mobilization of critical resource, finalization of the core
process, implementation of core systems, and integration of critical devices (as mutually agreed).
2. As part of the implementation and operations, bidders is expected to integrate devices with EPS as
specified in the RFP.
7.2.2. Operations & Management of AP-SOC phase
1. Bidder is expected to provide core services as defined on 24*7*365 basis and manage day to day
operations for entire duration of contract period.
2. The key responsibilities include but not limited to staffing, reporting the SLAs, trainings for the staff,
reviewing SOPs and making required updates etc.
3. Bidder will also be required to maintain, manage and upgrade AP-SOC infrastructure to meet evolving
threats scenarios.
Andhra Pradesh Technology Services Page 26 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
8. Proposed Services – Core Services
8.1. Threat Monitoring, Analytics & Incident Management
The objective of this service is to respond and recover from a cyber-attack with minimal impact to the
information systems/ infrastructure by performing effective and efficiently incident monitoring and
detection, and near real time incident response. Security monitoring of the assets is the heart of AP-
SOC function and hence bidder is expected to deploy best in industry systems, people and process to
build incident detection, investigation and response capabilities. The key responsibilities shall include
continuous monitoring of systems for intrusions and/ or signs on anomalies and deploy appropriate
response in timely fashion. Bidder is expected to use security analytics systems and integrate third
party intelligence feeds for contextual awareness of incidents and identify advanced persistent threats.
8.2. Security Infrastructure Device Management
Bidder will be responsible to provide device maintenance and operations services for endpoints /
security systems / network devices / other critical assets including day to day patching, firmware
updates, log archiving, rules , config backups and other operations services etc. and maintenance of
ACLs , rules etc on request by asset owner.
8.3. Threat Surface Management Services
Bidder is expected to continuously assess and remediate vulnerabilities on all integrated devices as part
of effective vulnerability, assessment and remediation plan. Proactive remediation of devices will
reduce / avoid potential exploitation and will save on resources which can be better used for tacking
incidents which would have happened.
8.4. Brand Monitoring and Protection Services
To provide services for brand abuse monitoring & protection, anti-phishing, anti-malware & anti-
Trojan to safeguard the interests of department/agencies against Phishing, Pharming, Trojan and
malware attacks. This will also include monitoring and detection of any kind of unauthorized changes
on the website URL and web site defacement.
Andhra Pradesh Technology Services Page 27 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
9. Responsibilities of the Stakeholders
9.1. Responsibilities of the Bidder/Service Provider
9.1.1. Technology infrastructure
1. Bidder shall deploy world class AP-SOC infrastructure including but not limited to a Security
Information and Event Management (SIEM) solution, Incident management solution, third party threat
intelligence collation and analysis tools, malware analysis tools, Vulnerability assessment, penetration
testing tool kits etc.
2. Bidder shall procure additional hardware, software’s etc. on need basis during AP-SOC engagement to
onboard applications/ devices/ infrastructure to further strengthen and mature AP-SOC offerings to
meet SLA as defined in the RFP.
3. Bidder shall install all IT equipment such as but not limited to desktops, servers, software’s, biometrics
access controls, cameras, printers. video wall etc.
4. Bidder is responsible to procure all the required network elements for the establishment, installation
and operation of the AP-SOC.
5. Bidder is responsible for establishing connectivity with the client side and will ensure secure
connections. with client with a maximum of 10 connections within the state.
6. Bidder is expected to prepare a functional DR in passive mode and operate the DR as per the timelines
mentioned in the RFP.
7. The bidder is responsible to isolate/insulate the information pertaining to the GoAP and other clients as
part of this contract. The physical and logical isolation/ insulation to be established while provisioning
services to other clients.
8. The bidder is responsible for treating the raw power at mains (Provision of UPS and Generator as per
requirement)
9. The bidder is responsible for establishing the electrical and networking at the AP-SOC premises
10. SOC access controls, IP based video surveillance, Real time attendance management with required
application.
11. Bidder shall meet the operation expenses such as expenses towards power consumption, facility
management, consumables etc.
12. Furnish the deliverables to APTS including reports
13. Any additional requirements for Rack space will have to be borne by bidder.
14. Exit management
9.1.2. People/Resources
1. Bidder is expected to deploy sufficient resources to provide 24*7*365 services as defined to meet the
Service Levels.
2. Apart from the AP-SOC operations resources, Bidders is expected to deploy experienced resources to
coordinate with various Stakeholders to integrate, monitor and support in any security incident.
3. Bidder is expected to estimate the number of resources required to provide the services to meet the
SLA.
9.1.3. Processes
1. Bidder is responsible to prepare guidelines and SoP’s for the AP-SOC operations based on the
international standard and best practices including ISO 27001, ISO 9001, and Cert-In Guidelines etc.
Andhra Pradesh Technology Services Page 28 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
2. The above Guidelines and SoP's will be approved by the GoAP/ APTS.
9.2. Responsibilities of the Departments / Agencies
1. Department shall coordinate for the integration of their respective devices/ Applications.
2. Departments /agencies will take corrective action in case of gaps identified in the infrastructure/
Applications managed by them or their service provider.
9.3. Responsibilities of APTS
9.3.1. AP-SOC Facility
1. APTS will provide bidder with furnished office space with provision of monitoring room, meeting
rooms, training rooms etc. in Vijayawada.
2. APTS would provide the rent free space for the AP-SOC operations.
3. The total area of the furnished office space will be approximately, 7500 SFT and would be ready with
furniture.
4. The provided office space is expected to be utilized for AP-SOC related services only. Data Centre
APTS will provide bidder with space in Tier III data center in Amaravati to host AP-SOC IT
equipment’s. This space will be limited to maximum of 10 racks (5 racks for 1st year, 3 racks for 2nd
year, 2 racks for 3rd year)
5. APTS will also provide rack space in alternate Data center to cater to AP-SOC DR requirements. APTS
will provide 5 rack space for the DR at no additional cost. Any additional requirements for more space
will have to be borne by bidder.
9.3.2. Responsibility Matrix
The following table describes the responsibilities of the APTS, bidder, and Department. The APTS or in
certain cases consultant appointed by the GoAP/APTS shall conduct the acceptance test for the hardware
and software proposed by the Bidder before they take over the maintenance of the hardware and
software proposed by the Bidder.
APTS clients
Activity APTS Bidder
# (Departments)
1 AP-SOC Solution Strategy, Design & plan M &S P
2 AP-SOC Solution procurement and supply M&S P
3 Installation & integration of Cyber solutions M&S P
4 Training M &S P
5 Documentations M&S P
6 Acceptance of the AP-SOC solution M &S P
7 Ongoing AP-SOC Operations M&S - P
8 AP-SOC Operations Review M &S V&M P
9 SLA Reports M&S V&M P
0 Incident Resolution M P V&M
Andhra Pradesh Technology Services Page 29 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
“V” - Validated (Responsible for Validating the activity)
“P” - Performed (Primary responsibility for executing the activity)
“S” – Signed Off (Responsible for providing the go-ahead)
“M”- Monitoring (Responsible for continuous monitoring of activity)
9.4. Services commitment by GoAP/APTS
Type of Service Service Unit Year 1 Year 2 Year 3
Monitoring EPS 5,000 10,000 10,000
Device
Per Device 25 50 50
Management
Attack Surface Per Application
1000 1000 1000
Management (IP/Devices)
Brand Protection Per Website 200 400 400
Andhra Pradesh Technology Services Page 30 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
10. Detailed Scope of Work
As part of the AP-SOC, bidders are required to provide the following core services:
1. Threat Monitoring, Analytics & Incident Management
2. Security Infrastructure Device Management
3. Threat Surface Management services
4. Brand monitoring & protection services
10.1. Threat Monitoring, Analytics & Incident Management
10.1.1. Service Objective
To respond and recover from a cyber-attack with minimal impact to the information systems and
infrastructure by performing effectively and efficiently incident monitoring and detection, and near real
time incident response.
10.1.2. Service Coverage & scope
AP-SOC will be required to provide advance Security Monitoring & Incident Management Services
and below are list of requirements under the service domain:
a. 24x7 real-time monitoring, logging, analyzing, responding to stakeholders (security devices
management teams/vendors/ systems integrators) with mitigation advisories and recommendations.
b. Track and follow-ups with stockholders for resolution of reported security incidents tickets.
c. Deep packet inspection and analytics capability
d. Analyzing, advising and logging calls related to security advisories received from external agency
like State-CERT, National-CERT, security vendors/OEMs etc.
e. Develop and publish threat advisory.
f. Identify the origin threat, RCA (Route Cause Analysis), measures for preventive recurrence.
g. Log Management / storage service to ensure logs availability for live correlation, analysis and
forensics investigation.
10.1.3. Design, Operations & Sizing consideration:
10.1.3.1. No of devices/EPS required
The bidder shall be required to supply & install SIEM solution with minimum specified in the RFP and
solution should be modular, scalable and flexible to meet the additional requirements of all the
government departments/ business functions.
10.1.3.2. Availability/ DR consideration
1. The bidder shall be required to propose the entire solution including AP-SOC room components
(only active components), core technology components (SIEM, Incident response platform, service
desk tool, real time dash board, Threat intel platform, deep packet inspection), OS, Hardware,
software, applications, servers, racks, network, security components and analysts computing
equipment (laptops/desktops) and other equipment to ensure the High –availability requirements in
Primary site and Disaster recovery requirements.
Andhra Pradesh Technology Services Page 31 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
2. Bidder should consider, Vijayawada as Primary AP-SOC site and Hyderabad as secondary/ DR
site.
10.1.3.3. Log Storage & retention
1. Bidder should design & propose solution with proper sizing of storage (SAN/NAS) to fulfill the log
storage/ retention requirement of state Government/ department as per Government guidelines and
regulatory requirements.
2. The online log to be kept for a period of 3 months and offline log in external storage for period of 9
months. Logs older than year should be kept in tapes for a period of 5 years.
10.1.3.4. Backup & Restoration requirement
Bidder should design & propose solution with proper sizing of backup solution including backup
software/ application, offline backup drives/tape libraries, tape drive/cartage to fulfill the offline log/
data storage requirement of state Government/ department as per Government guidelines and
regulatory requirements.
10.1.3.5. Reporting and Metrics
Bidder should propose solution for online real-time reporting and dash board access to all the
stakeholders. Content/ frequency and communication plan shall be proposed and agreed during the
implementation phase by the bidder and APTS.
Bidder should define, develop, update and maintain metrics for measuring, monitoring and reporting
status and effectiveness of various activities mentioned in the SOW.
Bidder should define, develop, update and maintain metrics for implemented technology, identifying
efficiency and effectiveness of tools, activities used within the security program, people-based metrics
and process based metrics etc an same must be updated in real time and provide current status of
security posture to APTS stakeholders.
10.1.3.6. Security control
It would be full responsibility of bidder to ensure the physical & logical security of AP-SOC
infrastructure, application, systems and data / logs.
Bidder should identify and propose necessary security controls required to ensure end to end security &
privacy of data/logs/ other information systems.
All the resources working on the project should sign the NDA and should undergo background as per
the criteria defined.
10.1.3.7. Features and Success criteria
The following are key features expected in the proposed solution, but not limited to:
1. It should be able to collect machine data from any source (including logs, clickstreams, sensors, stream
network traffic, security devices, Web servers, Databases, custom applications, social media, and cloud
services). It must enable security operations to collect, store, search, and report on the data to gain
valuable security intelligence across the entire organization. Should be able to capture and process data
from Big Data source.
2. Collect logs and events from several sources including network assets, security devices, operating
systems, applications, databases, and identity and access management products
Andhra Pradesh Technology Services Page 32 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
3. Collect network flow data, including Layer 7 (application-layer) data, from switches and routers
4. Collects vulnerability information from network and application vulnerability scanners in real time and
offline.
5. Perform immediate event normalization and correlation for threat detection and compliance reporting
6. Ability to extend / integrate the platform with any other applications/ platforms utilizing custom apps
and APIs.
7. The proposed solution must be configured, managed, and monitored through a centralized management
console. It should be configured, managed, and upgraded easily, thereby allowing operations team to
focus on core operations activities.
8. Proposed solution should be accessible through web UI, and other interface.
9. Solution should have capability filter/analyze events and flows into a handful of actionable intelligence
with trend analytics, perform event and flow data searches in both real-time streaming mode or on a
historical basis to enhance analysis to prioritize and responds immediately.
10. Integration support to collect various global Threat Intelligence to identify activity associated with
suspicious IP addresses, such as those suspected of hosting malware
11. The proposed solution should be able to integrate with all the leading technologies out of the box. For
any specific technology bidder will be able to create connectors/ parsers and should be able to support
changes in the ecosystem.
12. Meets regulatory requirements around log management, retention, review, and continuous monitoring,
reporting as communicated from time to time.
13. Ability to do full-text search on any field in the indexed data based without any limitation.
14. Solution should enable the easy creation of a wide range of visualizations (not limited to fixed, pre-
canned reports).
15. Visualizations should have the ability to update in real-time and should be able to make clear
outliers/anomalies in need of further investigation
16. Visualizations all support drill-down, click-through capabilities to get from summaries to raw events
within seconds.
17. Threat Intelligence feeds (Indicators of Compromise – IP addresses, Domains, Hashes, etc.) from open
source and other commercial providers to be integrated with the proposed solution to provide advanced
security monitoring services.
10.2. Security Infrastructure Device Management
10.2.1. Service Objective
To manage the day to day security operations, maintenance and availability, change management
of security devices.
10.2.2. Service Coverage & scope
AP-SOC will be required to provide Security System Availability and health Monitoring, Incident
Management, Problem Management, Change Management and Service Request Services. Below are
list of requirements under the service domain
a. 24x7 real-time monitoring uptime, availability, health performance of security devices with
mitigation support.
b. Track and follow-ups with stockholders for resolution of reported incidents tickets.
c. Analyzing, advising and logging calls related to security advisories received from external agency
security vendors/OEMs for troubleshooting & resolving the incident, problem and changes for the
devices under management.
Andhra Pradesh Technology Services Page 33 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
d. Ensure systems are up and running, including their other aspects like Configuration, Re-
configuration, updates, upgrades, bug fixes, problem analysis, performance analysis, configuration
optimizations, migration of devices, audits, users profile management, root cause analysis, on-site
support.
e. Bidder should ensure facilitation support for implementation of new security products.
f. Bidder shall ensure logical and acceptable conclusion of all the monitoring, management,
mitigation, administration and reporting issues. This includes tracking of AMC renewal /
validation, RMA support and related vendor/OEM management etc.
g. Bidder must ensure a smooth handover of these devices from current vendor in specified and
declared timelines with proper project management
h. The bidder should deploy appropriate separate (other than monitoring) dedicated on-site manpower
resource to ensure the same.
i. Bidder also has to ensure smooth operations of the in-scope services and solutions.
j. Bidder should ensure the regular SLA tracking and MIS reporting.
10.2.3. Design, Operations & Sizing consideration
10.2.3.1. No of device under support
1. The bidder shall be required to supply & install NMS, Service desk tools solution which should
be scalable & flexibles to cater integration and monitoring requirements of for contact period.
2. The bidder needs to provide details of how the solution/service can scale to cater future
integration requirements.
3. Bidder should have a capacity of managing minimum of 25 devices (Firewall/ IPS/IDS etc) in the
first six month of operations.
10.2.3.2. Availability/ DR consideration
The bidder shall be required to propose the entire solution including AP-SOC room components,
NSM , Service desk, tool, real time dash board, underlying OS, hardware, software, applications,
servers, racks, network, security components and analysts computing equipment (laptops/desktops)
and other equipment to ensure the High –availability requirements in Primary site and Disaster
recovery requirements.
Bidder should consider, Vijayawada as Primary AP-SOC site and Hyderabad as secondary/ DR site.
10.2.3.3. Log Storage & retention
Bidder should be responsible for enabling logging on the required device for monitoring. Bidder will
provide support to integrate these devices with SIEM if required and coordinate with Security
Monitoring & Incident management team in case of issue.
10.2.3.4. Backup & restoration requirement
Bidder should design & propose solution with proper sizing of backup solution including backup
software/ application, offline backup drives/tape libraries, tape drive/cartage to fulfill the offline
configuration or log/data storage requirement of state Government/ department as per Government
guidelines and regulatory requirements.
Andhra Pradesh Technology Services Page 34 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
10.2.3.5. Reporting and Metrics
Bidder should propose solution for online real-time reporting and dash board access to all the
stakeholders. Content/ frequency and communication plan shall be proposed and agreed during the
implementation phase by the bidder and APTS.
Bidder should define, develop, update and maintain metrics for measuring, monitoring and reporting
status and effectiveness of various activities mentioned in the SOW.
Bidder should define, develop, update and maintain metrics for implemented technology, identifying
efficiency and effectiveness of tools, activities used within the security program, people-based
metrics and process based metrics etc an same must be updated in real time and provide current status
of security posture to APTS stakeholders.
10.2.3.6. Features and Success criteria
Bidder shall provide 24*7*365 management of security devices with following activities in broad
level, but not limited to:
1. The bidder has to maintain the devices in the optimal configuration as required by APTS client’s
organization security architecture.
2. Provide centralize management of the security products and to have tight control on the security
rules.
3. Perform periodic review and fine tuning of these devices to fit organization network environment
and requirement, sub-sequence management, monitoring and support (24x7) through AP-SOC.
4. Assist the department in the Device lifecycle management, License management and OEM co-
ordination.
5. The change management of all the devices must be adhering to standards and policies of APTS or
the respective department and respective SLA will be applicable to the selected bidder.
6. Create, update and delete access control rules, groups, and policies in security devices after
obtaining approval.
7. Quarterly review of rules, policies etc. of security devices and recommend optimization of the
same.
8. In case of any hardware/software malfunctioning, patch management, firmware Upgradation and
other OEM related tasks of the device, the bidder has to coordinate with stakeholders for faster
resolution.
9. Monitor and report the hardware and software related SLA’s of all security device / solutions
managed by the bidder.
10. SOP Documentation and OEM/Service Provider SLA management has to be designed,
documented, implemented and fine-tuned by the bidder
11. Quarterly review of capacity planning of security devices. Details of underutilized and over
utilized security devices.
12. Inform about Hardware / software system failure of Security equipment / tools. Provide detailed
explanation of outage whether the same is due to hardware or software or due to wrong
configuration failure and its likely impact on the security posture of the organization.
13. Review existing SLAs entered for Security devices in scope and assist for new SLAs as and when
entered with bidder and recommend measures to improve the Service Level Agreements (SLAs).
14. Take backup of the OS, signatures, policies, routing tables, logs etc. with configuration files of
security devices. Maintain Backup register.
15. Review backup plans for each site on quarterly basis. Review backup configuration and business
continuity procedures to be followed in the event of security devices failure.
Andhra Pradesh Technology Services Page 35 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
16. Conduct Recovery exercise of above backup on quarterly basis or as per the APTS/department
guidelines.
1.
10.3. Threat Surface Management Services
10.3.1. Service Objective
To manage the attack surface by continuously identifying, tracking, and closing vulnerabilities,
configuration flaws and reducing threat landscape.
10.3.2. Service Coverage & Scope
AP-SOC will be required to provide Threat and vulnerability Management Services as per the agreed
terms and period. Below are list of requirements under the service domain:
a. Continuous identification, monitoring of threat landscape and attacks surface.
b. Perform Vulnerability scanning, Penetration testing, mobile application testing for identify the
known/unknown vulnerability, follow-ups with stakeholders and ensure the remedial action.
c. Continuously monitor for the missing patches, recommend for necessary patches and ensure
remedial action.
d. Coordinate with external agency like State-CERT, National-CERT, and security
vendors/OEMs etc. for new /zero day vulnerabilities and solution and remedial action.
10.3.3. Design, Operations & Sizing consideration
10.3.3.1. No of device under support
1. The bidder shall be required to have a capacity to perform VA/PT for atleast 250 IPs to begin with.
The bidder needs to provide details of how the solution/service can scale to cater future
requirement.
10.3.3.2. Availability/ DR consideration
1. The bidder shall be required to propose the various tools required to perform Threat Management
services and other equipment to ensure the High –availability requirements in Primary site and
Disaster recovery requirements.
2. Bidder should consider, Vijayawada as Primary AP-SOC site and Hyderabad as secondary/ DR
site.
10.3.3.3. Log Storage & retention
Bidder should be responsible for maintain the scan tool reports and manual reports for a period of 3
yrars from the assessment.
10.3.3.4. Backup & restoration requirement
Bidder should design & propose solution to ensure all the reports and data is available for the contract
period.
Andhra Pradesh Technology Services Page 36 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
10.3.3.5. Reporting and Metrics
1. Bidder should propose solution to integrate the Threat surface management data is integrated to
provide better visibility of the risk exposure and provide appropriate response.
2. Bidder should define, develop, update and maintain metrics for measuring, monitoring and
reporting status and effectiveness of various activities mentioned in the SOW.
10.3.4. Features and Success criteria
1. Bidder to perform Vulnerability Management services for the critical devices. Bidder to provide
vulnerability assessment report with recommendation for required remediation.
2. Bidder is expected to perform VA as per the frequency agreed with the APTS across infrastructures
and servers and provide reports for the same as per SLA.
3. Solution should be able of integrating with SIEM solution to provide a correlated view of threats
and vulnerabilities associated with them along with remediation mechanism.
4. Bidder is responsible to carry out external and internal PT and need to allocate sufficient resources
to perform the services.
5. WEB Security testing for external (internet) & Internal facing application & related webservers for
bug/vulnerability within application.
6. Security testing for Network/WiFi Access points for security vulnerability/possible hacktivism and
their probable Reconnaissance Attack.
7. Bidder is responsible to carry out WEB Application Security Assessment with the help of
commercial and open source tool and manual testing.
8. Bidder shall perform Security Testing for different application over WEB/Servers/Mobile, for
security bug, data leaks and unusual behavior of the application.
9. Bidder shall perform “Secure App Code Review” for error correction/bug fixation/loopholes within
coding and provide secure code review report with recommendation & remediation.
10.4. Brand Monitoring & Protection Services
10.4.1. Service Objective
1. To provide services for brand abuse monitoring & protection, anti-phishing, anti-malware &
anti-Trojan to safeguard the interests of department/agencies against Phishing, Pharming,
Trojan and malware attacks.
2. This will also include monitoring and detection of any kind of unauthorized changes on the
website URL and web site defacement.
10.4.2. Service Coverage and Scope
To provide Brand Monitoring & Incident Management Services to Govt. departments/ businesses
functions in the state. Below are list of requirements under the service domain
1. Bidder should monitor the customer/citizens facing websites/portals on 24x7 real-time
monitoring of any brand abuse incidents on the state Government and department/business
websites.
2. Bidder has to provide the solution that monitor the Logo, URLs, domain name, rogue mobile
application, social media monitoring, spoofed email ids etc.
Andhra Pradesh Technology Services Page 37 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
3. Bidder shall continuously monitor, detect and responsible for take down phishing sites, brand
abuse, retrieval of compromised customer information and forensic details of such attacks and
take down the sites and provide appropriate solution.
4. Bidder should implementation of real time detection mechanisms and alerts
5. Track and follow-ups with stakeholders for resolution of reported security incidents tickets.
6. Analyzing, advising and logging calls related to security advisories received from external
agency like State-CERT, National-CERT, security vendors/OEMs etc.
7. Identify the origin threat, RCA, measures for preventive recurrence.
10.4.3. Features and Success criteria
Bidder shall provide 24*7*365 management of brand abuse incidents with following activities in
broad level under security device management, but not limited to:
1. Track hosting of phishing sites through implementation of watermark and other means.
2. Monitoring similar domain name registration.
3. Monitoring junk e-mail messages.
4. Monitoring spam traps to detect phishing mails.
5. Monitor networks known to be sources of attacks and/or points of collection of compromised data.
6. Monitor any fraudulent/rouge mobile apps targeting customers to capture their credentials for
fraudulent transactions.
7. Remove fraudulent/rouge mobile app targeting customers to capture their credentials hosted on
popular app stores provided by companies such as Google, Apple, and Microsoft etc.
8. Perform Web site analysis to detect phishing sites.
9. Taking down of phishing sites anywhere in the world either on bidder own reach or through
partnerships. Bidder should have alternative response mechanisms other than web site take down to
minimize impact of phishing.
10. Blocking of the phishing sites in web browsers including but not limited to the following browsers
a. Internet Explorer
b. Mozilla Firefox
c. Google Chrome
d. Opera
11. Providing incident reports on phishing attacks and fraudulent/rouge mobile apps involving threat
analysis and threat categorization.
12. Anti-malware monitoring of websites/portals and implement all the measures as may be necessary
from time to time to mitigate the evolving threats.
13. Bidder must have capability for 24X7 monitoring for Malicious Mobile Code (MMC) infection of
the websites.
14. Service should be tool based automated solution with e-mail & SMS alerts.
15. Service should support scanning to a depth of multiple pages for static and dynamic links.
16. Solution must support checking all website links against well-known global black lists.
17. Bidder must manage incidents for MMC infection/injection including solution, coordination for
recovery in the shortest possible time.
18. Solution must provide online interface to see previous online reports of all the websites under
monitoring.
19. Monitoring of compromised servers for forensic information related to APTS customers till the
primary incident is closed and provide complete forensic details to the APTS
20. The selected bidder shall ensure resolution of Phishing, Pharming, Trojans, and Malware related
incidents within 2 hours once it is reported by the bidder.
21. Once the phishing site is taken down, the IP and domain name where it was hosted should be kept
under continuous supervision so that the phishing site on the same IP and with the same domain
name does not resurface.
22. Bidder should provide a customized real time dashboard.
Andhra Pradesh Technology Services Page 38 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
10.5. Establishment and Operationalization of DR
The bidder has to
a) Prepare a functional DR and to establish at Hyderabad
b) The licenses for Primary DC and DR would be Active-Passive mode and would be only
operational when the Active mode is off/not working from Primary location
c) The connectivity between SDC and DR is responsibility of GoAP
d) The Connectivity between AP-SOC to SDC is responsibility of GoAP
e) The Storage at DR site is to be 100% as per the DC and compute for DR is to be established as
required in terms of the scope of the RFP
f) Operate the DR as per the timelines mentioned in the RFP.
10.6. Tools/Services Required as part of the Scope of the RFP
Bidder has to propose, supply and deploy below listed best in class tools/technology & application
listed in Gartner quadrants report dated only which must be fulfilling the above business
requirements. The proposed solutions should not be end of life or End of Support during contract
period.
S.No Category Category
1 SIEM Gartner Leadership quadrant (Report 2016)
2 Service Desk/Help Desk All Gartner Quadrants (Report 2016)
3 Threat Intelligent Feed All Gartner Quadrants (Report dated 2016)
4 Network Management Solutions Gartner Leadership & Challenger Quadrants
(Report 2016)
5 VAPT Commercial Tool
6 Network Security Policy Manager Commercial Tool
7 Incident Response Platform Commercial Tool
8 Anti Phishing/Spamming Commercial Tool
Note: All the components proposed should not be End of Life or End of Support during the contract
period.
10.7. Design Principles of AP-SOC
Bidder is adopt following design principles in the design and operation of the AP-SOC services.
10.8. Scalability
Since the APTS would like to extend the services to other department and states, proposed solutions offered
should be modular, scalable, and should be able to address the future requirements.
10.9. Availability
The services/ solutions in scope should be designed with adequate redundancy and fault tolerance to ensure
High Availability (HA) and disaster recovery requirement.
Andhra Pradesh Technology Services Page 39 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
10.10. Functional Principles
The intent for SOC solution is covered in the below functional principles:
Identification & Remediation of Security Threat and their breaches: The SOC
solution should be able to identify security threat\vulnerabilities across the identified
departments at ICT environment under Government of AP and remediate those
vulnerabilities.
Incident Management: Reporting and logging of security events/incidents through the use
of appropriate tools. Closely track and monitor the closure of those security incidents and
escalate them to appropriate teams/ individuals in the specific departments if required.
Continuous Improvement: Continuously improve SOC services/ operations, with proper
plan of action applied.
10.11. Video Wall
The Bidder is responsible for setting up of the video wall in the AP-SOC, the following is the
indicative specifications for the video wall.
Ultra-narrow bezels at 3.5mm to create virtually seamless video wall
46" Professional Large
Video wall size(in terms of no of Tiles ) - 12 (W) * 2 (H)
Format LED video wall
1 Each Display Resolution (Single Display)-Full HD (1920*1080)
- 12*2 for detection
Overall video wall resolution - 7680 * 2160
wall
Switching and interface video processor equipment for multi display options
Ultra-narrow bezels at 3.5mm to create virtually seamless video wall
46" Professional Large Video wall size(in terms of no of Tiles ) - 2 (W) * 2 (H)
Format LED video wall Overall video wall size - 2024mm * 1154mm
2 - 2*2 one each for
Switching and interface video processor equipment for multi display options
Response and Hunt
teams Each Display Resolution (Single Display)-Full HD (1920*1080)
Overall video wall resolution - 3840 * 2160
Ultra HD Resolution (3840*600)
Ultra stretch display - 1
3 58:9 Extended Wide Format
number
4 Divided PBP in Landscape or Portrait
Multiple Content Creation
48" Professional Large 16/7 Professional grade display
4 Format LED Display Display Resolution - Full HD (1920 * 1080)
for DTH - 1 Number
10.12. Infrastructure to be deployed in the AP-SOC
S.No Item Quantity
1 Video Wall 12*2 1
2 video wall - 2*2 2
3 Ultra stretch display 1
4 48" Professional Large Format LED with DTH 1
5 21 inches i7 based All In One Desktops 25
Andhra Pradesh Technology Services Page 40 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
6 UPS as per the requirement with common battery bank 2
7 Network Cabling 1
8 Leased line/MPLS connectivity of 2 MBPS within AP 1
9 LCD Projectors 2
10 Access Control 1
11 IP based Video Conference 1
12 Network based Duplex Multi- Function Printer 2
13 Fire Extinguishers As reqd.
Andhra Pradesh Technology Services Page 41 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
11. Project Implementation Timelines
Milesto Deliverabl
Freque Durati ne es/expecte
Require Description ncy on d
#
ments outcomes
1 Strategy The bidders shall develop the strategy and One One T0+1 Service
operating framework for AP-SOC design, time Weeks Strategy
Week
implementation and operations as per the contract Framewor
period for integration & monitoring requirements k
for APTS.
2 Design & The bidder shall develop architecture design for One One T0+2 Solution
Plan AP-SOC and provide the detailed plan for time Week Weeks Design
implementation of AP-SOC as per the design in and Plan
terms of people, process, and technology and AP-
SOC infrastructure.
3 Procurem The bidder shall identify, procure and supply the One Six T0+8 Technolog
ent & best in class technology solution and equipment for time Weeks Weeks y
Supply setting up AP-SOC infrastructure, which includes Solutions
Core technologies (SIEM, Incident response
platform, Threat intel platforms, ticketing tools
etc.), underlying, software, Operating systems,
servers, storage, backup solution, racks, network,
security devices along with desktops / laptops for
analysts, Audio-video setup with extended displays,
collaboration tools, phone sets and other system
requirement to build a fully equipped AP-SOC.
4 Installati 1. Installation of underlying infrastructure One Six T0+14 Server/
on & network & server racks, servers, network and time Weeks Data
Weeks
Integratio security equipment as per design requirements. center
n 2. Installation & integration of core AP-SOC tools setup
& technology as per design for threat
AP-SOC
monitoring, detection and response.
technology
3. Integration of log sources for log collection,
implement
storage, correlation, monitoring & reporting.
ed
4. Process / workflow implementation
5. Installation & integration of user computing AV
(laptops/ desktops/ monitors etc), collaboration installation
tools, phone sets & related infrastructure. Process/
6. Audio-Video (AV) installation & integration as
workflow
per design. implement
7. Installation & integration of solution for Patch
management, Vulnerability assessment, penetration
ed
testing, mobile testing.
Andhra Pradesh Technology Services Page 42 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Milesto Deliverabl
Freque Durati ne es/expecte
Require Description ncy on d
#
ments outcomes
5 Training Provide training to the identified APTS personnel/ One 5 days T0+15 Training
AP-SOC team on the product architecture, time at Weeks Agenda &
functionality and the solution design – to be the time contents
provided before the implementation of solution implem
Training
entation
schedule
& half
yearly Training
during delivery
operatio
ns
6 Documen 1. Develop and provide all the technical, process, One One T0+16 Project
tation SOP documents. time & Week Weeks documents
2. Technical product installation & configuration regular
Implement
guide (customized guide as per design & updatio
ation
implementation). n
document
SOP for
AP-SOC
operations
7 Testing Parallel T0+16
and Trial activity Weeks
Run along
with
Docum
entation
7 Operatio 1. 24x7 real-time monitoring, logging, analyzing, Ongoin Contrac T0+17 Incident
ns responding to stakeholders (security devices g after t period Weeks Monitorin
management teams/vendors/ systems Go live to g, &
integrators) with mitigation advisories and T0+156 reporting
recommendations. Weeks through
2. Track and follow-ups with stockholders for alerts,
resolution of reported security incidents tickets. reports,
3. Analyzing, advising and logging calls related to dashboard
security advisories received from external s
agency like State-CERT, National-CERT,
Threat
security vendors/OEMs etc.
advisory
4. Ensure systems are up and running condition,
their other aspects like Configuration, Re- Log
configuration, upgrades, bug fixes, problem storage
analysis, performance analysis, configuration Use case
optimizations, migration of devices, audits, developme
users profile management, root cause analysis, nt &
on-site support. enhancem
5. Bidder should ensure facilitation support for ent
implementation of new security products.
6. Bidder shall ensure logical and acceptable
conclusion of all the monitoring, management,
mitigation, administration and reporting issues.
Andhra Pradesh Technology Services Page 43 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Milesto Deliverabl
Freque Durati ne es/expecte
Require Description ncy on d
#
ments outcomes
This includes tracking of AMC renewal /
validation, RMA support and related
vendor/OEM management etc.
7. Bidder must ensure a smooth handover of these
devices from current vendor in specified and
declared timelines with proper project
management
8. The bidder should deploy appropriate separate
(other than monitoring) dedicated on-site
manpower resource to ensure the same.
9. Bidder also has to ensure smooth operations of
the in-scope services and solutions.
10. Bidder should ensure the regular SLA tracking
and MIS reporting
11. Continuous identification, monitoring of threat
landscape and attacks surface for APTS and
associated departments/ business functions.
12. Perform Vulnerability scanning, Penetration
testing, application code reviews, mobile testing
for identify the known/unknown vulnerability,
follow-ups with stakeholders and ensure the
remedial action.
13. Continuously monitor for the missing Patches,
recommend for necessary patches and ensure
remedial action.
14. Coordinate with external agency like State-
CERT, National-CERT, and security
vendors/OEMs etc. for new /zero day
vulnerabilities and solution and remedial action.
15. Bidder has to provide the solution that monitor
the Logo, URLs, domain name, rogue mobile
application, Social media monitoring etc
16. Bidder shall continuously monitor, detect and
responsible for take down phishing sites, brand
abuse, retrieval of compromised customer
information and forensic details of such attacks
and take down the sites and provide appropriate
solution.
17. Bidder should implementation of real time
detection mechanisms and alerts
18. Track and follow-ups with stockholders for
resolution of reported security incidents tickets.
19. Analyzing, advising and logging calls related to
security advisories received from external
agency like State-CERT, National-CERT,
security vendors/OEMs etc.
20. Identify the origin threat, RCA, measures for
preventive recurrence
21. Identify the origin threat, RCA, measures for
preventive recurrence.
22. Log Management / storage service to ensure
Andhra Pradesh Technology Services Page 44 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Milesto Deliverabl
Freque Durati ne es/expecte
Require Description ncy on d
#
ments outcomes
logs availability for live correlation, analysis
and forensics investigation. Perform on-going
optimization, configure additional use-cases,
and suggest improvements as a Continuous
Improvement Process.
23. Perform log backup and archival as per policy
requirements, and applicable legal and statutory
requirements.
11.1. Reports
Expected Reports in the Operation Stage
Following are the minimum reports, bidders shall provide in the operation phase to APTS.
1. Daily Reports:
1. Top attacker and Target report
2. Top firewall ports access report (inbound/outbound)
3. Top Signature triggered
4. Top Account brute forced
5. Top systems infected
6. Top virus infection in the network
7. SIEM/monitoring tool performance report
8. Daily firewall utilization report (CPU and Memory)
9. Firewall availability report
2. Weekly Reports
1. Weekly security incidents status report
2. Daily device utilization report
3. Device availability report
4. Antivirus and Patch compliance status report
5. Anti-phishing and Anti-malware status report
6. Device: Incident, Service request and Change status report
7. Weekly threat advisory and vulnerability report
Monthly Reports
1. Executive summary report for all the services
2. Monthly Security incident status report
3. Monthly security incident trend analysis
4. Monthly device availability report
Quarterly Reports
1. Quarterly Security incident status report
2. Quarterly security incident trend analysis
3. Quarterly device availability report
Andhra Pradesh Technology Services Page 45 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
12. Instructions to the Bidder
12.1. Language of the Bid
The proposal and various documents related to the RFP should be in English language only. All
correspondence between APTS and the bidder would also be in English language. Supporting documents and
printed literature furnished by the bidders shall be in English language or in case in another language they
should be accompanied by an accurate translation in English language.
12.2. Validity of the Proposal
APTS requires that the proposal submitted in response to this document remain valid for acceptance for a
period as specified in the RFP Datasheet from the date of submission of online bids. The bidders should state in
their response, any longer period for which their response remains valid.
A proposal valid for shorter period may be rejected as non-responsive. APTS may seek the selected applicant’s
consent to an extension of proposal validity (but without the modification in proposals). Where the applicant
claims confidentiality or seeks to reserve intellectual property rights in respect of any part of its response or
requests such part should be treated as “confidential” or “commercial in confidence”, they must:
• Clearly mark the part of the document in respect of which the claim is made
• State the basis of claim for confidentiality for each item marked (a blanket claim cannot be reasonably
made)
• Convince APTS that such a claim is reasonable
12.3. Acceptance of the Proposal
APTS reserves the right in its absolute discretion in relation to:
• Accepting or rejecting a response
• Seek written clarification from any or all of the bidders in relation to their responses, during the
evaluation of bids
• Varying or discounting the procurement process if it deems reasonable conditions exist to do so
• Providing additional information to any or all bidders
• Cancelling, adding to or amending the information, requirements, terms, procedures or processes set
out in this document. In such a case APTS shall publish these on the website and notify the bidders
• Identifying opportunities for collaborative responses to be offered for the delivery of specified services
• Issue an open tender/RFP
• Waive any small/ minor informalities in the process
12.4. Fraud and Corruption
APTS require that Bidder (Firm) selected through this RFP must observe the highest standards of ethics during
the performance and execution of such contract. In pursuance of this policy, APTS define, for the purposes of
this provision, the terms set forth as follows:
• “Corrupt practice” means the offering, giving, receiving or soliciting of anything of value to influence
the action of APTS or any personnel of Bidder in contract execution
Andhra Pradesh Technology Services Page 46 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
• “Fraudulent practice” means a misrepresentation of facts, in order to influence a procurement process
or the execution of a contract, to APTS , and includes collusive practice among Bidder (prior to or after
Proposal submission) designed to establish bids at artificially high or non-competitive levels and to
deprive APTS of the benefits of free and open competition.
• “Unfair trade practices” means supply of services different from what is ordered on, or change in the
Scope of Work which was given by the APTS.
• “Coercive practices” means harming or threatening to harm, directly or indirectly, persons or their
property to influence their participation in the execution of contract.
• APTS will reject a proposal for award, if it determines that the Bidder recommended for award is
engaged in corrupt, fraudulent, unfair, or coercive trade practices.
APTS will declare a Firm Blacklist either indefinitely or for a stated period of time, for awarding the contract,
if it at any time determines that the Firm has engaged in corrupt, fraudulent and unfair trade practice in
competing for, or in executing, the contract.
12.5. Amendment of Tender Document
At any time before the deadline for submission of bids, APTS may, for any reason, whether at its own initiative
or in response to a clarification requested by a prospective bidder, modify the Tender Document by amending,
modifying and/or supplementing the same. All prospective Bidders who have received this tender document
shall be notified of any amendments by e-mail, and all such amendments shall be binding on them without any
further act or deed on APTS part. Such amendments will also be available on the websites on which RFP
notification is published. In the event of any amendment, APTS reserves the right to extend the deadline for the
submission of the bids, in order to allow prospective Bidders reasonable time in which to take the amendment
into account while preparing their bids. If APTS deems it appropriate to revise any part of this RFP or to issue
additional data to clarify an interpretation of provisions of this RFP, it may issue supplements to RFP. Any such
supplement shall be deemed to be incorporated by this reference into this RFP.
12.6. Clarification on RFP Response
During Technical and Commercial evaluation of the Proposals, APTS may, at its discretion, ask any
Bidder for clarifications on their proposal.
12.7. Purchase of RFP Documents
i. The detailed bid documents would be made available online and interested bidders can
download the detailed tender documents. Hard copies of the tender documents will be
available at APTS. Interested bidders can obtain the same upon payment of the non-refundable
payment as mentioned in the bid data sheet while submitting their Bids/Responses in the form
of Demand Draft drawn from any nationalized bank / scheduled bank in favor of “The
Managing Director Andhra Pradesh Technology Services Limited”, Payable at
Vijayawada towards bid document charges.
ii. The bids submitted by the Bidder without furnishing the receipt of purchase of bid document
will be summarily rejected. Also, the relevant bids submitted online will not be opened.
iii. The bid documents purchased by the bidders from APTS are not transferable.
Andhra Pradesh Technology Services Page 47 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
12.8. Bid Format
The Bid shall be submitted as per the formats provided in the RFP, shall be page numbered and Indexed with
content table in the beginning.
12.9. Information for Proposal Submission
12.9.1. Contact Details
All inquiries concerning this procurement other than pre-bid queries are to be directed to the
Managing Director, APTS for meetings, conferences or technical discussions. Unauthorized contact
will be cause for immediate rejection of the proposer’s RFP response. Substantive questions will be
dealt with in writing.
For further details and Bid documents please contact:
The Managing Director
APTS
3rd Floor, Bhanu Krishna Nilayam
Vellanki Rammohana Rao Street
Moghulrajpuram
Vijayawada
12.9.2. Authentication of Bid
The Proposal should be accompanied by a power-of-attorney (POA) in the name of the signatory of
the Proposal by the Bidder. A scanned copy of the power-of-attorney should also be uploaded on the
e-Procurement portal along with the other documents.
12.10. Pre Qualification Criteria
12.10.1. The Bidder
The use of the term “Bidder” in the Tender means the AP-SOC Service Provider (or) Selected Service Provider
who must meet the following pre-qualification requirements to become eligible for the Technical &
Commercial Evaluation.
Mandatory documentary
# Pre-Qualification Criteria
evidence to be submitted
The Bidder must be a registered company in India,
registered under the Companies Act 1956/ 2013. Copy of Certificate of
1. The Bidder should be operating in India for the last
Incorporation - Format P#2
three years as on 31/03/2017
GST Registration Certificate in AP.
The Bidder should have valid GST registration Bidders without APGST, shall submit an
2. number in Andhra Pradesh
undertaking to register within 3 months Format
P#4
The Bidder should have an Average Annual Copy of the audited Profit & Loss Statements for
3. Turnover of at least Rs.100 crore (Rupees hundred
each of the last 3 financial years
crores) in the last three financial years as on
Andhra Pradesh Technology Services Page 48 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Mandatory documentary
# Pre-Qualification Criteria
evidence to be submitted
31/03/2017. Certificate from the statutory auditor stating the
Average Annual Turnover of the firm in the last 3
financial years
-- Form P5
Copy of the audited Profit & Loss Statements for
The bidder should have an Average Annual turnover each of the last 3 financial years
of at least Rs. 25 crore (Rupees Twenty Five Certificate from the statutory auditor stating the
4. crores) in each of the last three financial years from
income from Information Security based security
Information Security Services as on 31/03/2017
services revenue
-- Form P6
The bidder should have completed:
At least 2 SOC completed projects in India/Global
in last 3 financial years, each with value not less
than Rs. 5 Crores.
(OR)
At least 3 SOC completed projects in India/Global
in last 3 financial years, each with value not less Copy of the Work Orders along with client
than Rs. 3 Crores. certificate / work completion certificate stating the
5. scope and progress of the project.
(OR)
-- Form P7
At least 5 SOC completed projects in India/Global
in last 3 financial years, each with value not less
than Rs. 2 Crore.
* Note: SOC Revenue to include SOC design,
implementation and operations. SOC will be
considered as Security Monitoring and Security
Device management.
Bidder is providing Managed Security Operations Copy of the Work Orders along with client
Services (MSS) to 3 clients with minimum 5000 certificate / work completion certificate stating the
6. EPS for last 3 financial year in India as on date of scope and progress of the project
submission of bid. -- Form P8
Copies of the valid ISO 27001 certificate from
7. The Bidder should have an ISO 27001 certification
authorized agencies
The Bidder should not have been blacklisted by Self-declaration by the Bidder duly signed by the
8. Central Government / Any State Government / Any authorized signatory as per the format specified at -
PSUs in India as on the date of bid submission. - Form p9
The bidder should be a System Integrator (SI) for
the proposed SIEM solution during the last three Enclosed copies of reference letter /completion
financial years as on date of bid submission, and certificate provided by clients where SIEM solution
9. should have successfully implemented the is implemented.
proposed SIEM at a minimum of two Public/
Private Organization in India or Globally.
Andhra Pradesh Technology Services Page 49 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Mandatory documentary
# Pre-Qualification Criteria
evidence to be submitted
The bidder should have at least 100 full time Self-declaration by the Bidder duly signed by the
Technically Qualified Personnel on its rolls in the authorized signatory.
10. area of Security and IT services on its payroll for
the past three years. -- Form P11
The bidder should submit the MAF as per Form
P10 for every product that is being proposed/ used
as part of the project, as per the Form P10 attached
Manufacturer’s Authorization Form (MAF) to all in the RFP, specific to this tender issued by OEM/
11. the products as proposed in the Proposal. Principal authorizing the bidder to submit the bid
for tendering which is deemed as an agreement in
between the bidder and OEM/ Principal for the
support and spares till the warranty period.
12. Proof of Bid Purchase Receipt to be Submitted as per Form#P2
13. Declaration as Per the G.O MS 12 Declaration to be submitted
Power of Attorney Power of Attorney (POA) or Board Resolution
14. authorizing the person signing the proposal to sign
on behalf of the firm or Letter of Authorization
Note:
• Sub-contracting / out sourcing not allowed
• Bidder should operate the teams from Andhra Pradesh, preferable from AP CRDA region.
• In case, the bidder is not having GST registration in AP at the time of bid submission, an under taking
must be submitted that they will obtain GST in AP. The successful bidders has to obtain the GST in
AP. The eligible payments shall be released on submission of the GST registration certificate.
As per G.O MS No 12, dated 08.06.2016 , AP Procurement Policy for e-Governance
1. Bidders can submit their bids with self-declarations in respect of the pre-qualification criteria
prescribed in the RFP
2. The procuring agency shall evaluate the bids based on the self-declaration and select the successful
bidder
3. The successful bidder should submit the documents to prove their pre-qualification as specified in the
RFP, within 5 working days from the date of declaration of successful bidder
4. APTS will receive support documentations, verify the compliance with the requirements of the RFP
and if they are in order, issue the award notification
5. Failure to submit all support documents by the successful bidder within specified time or non-
compliance with the self-declaration or non-fulfillment of the pre-qualification criteria specified in the
RFP, upon their verification, shall entail forfeiting the EMD and Blacklisting of such bidder for a
period of two years. In such cases, the procuring agency may proceed further with the next-ranked bid.
However, Bidder should submit the following support documents mandatorily as part of the bid
response
Andhra Pradesh Technology Services Page 50 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
i. Power of Attorney (POA) or Board Resolution authorizing the person signing the proposal to sign
on behalf of the firm or Letter of Authorization
ii. Self-declaration confirming the truth of the data or information furnished by the bidder.
iii. Receipt of purchase of bid
12.10.2. Conflict of Interest
As requires that the bidder must provide professional, objective, and impartial advice and at all times
hold APTS interests paramount, strictly avoid conflicts with other assignments/jobs or their own
corporate interests and act without any consideration for future work.
12.10.3. Right to Terminate the Bid Process
APTS may terminate the Bid process at any time without assigning any reason. APTS makes no
commitments, express or implied, that this process will result in a business transaction with anyone.
This RFP does not constitute an offer by APTS. The bidder’s participation in this process may result in
APTS selecting the bidder for APTS to engage in further discussions toward execution of a contract.
The commencement of such discussions does not, however, signify a commitment by APTS to execute
a contract or to continue negotiations. APTS may terminate discussions at any time without assigning
any reason.
12.10.4. Earnest Money Deposit
i. Bidders shall submit, along with their bids, EMD of amount as specified in the RFP Datasheet in the
form of a Bank Guarantee (BG) drawn from any scheduled/nationalized bank in favor of “The
Managing Director, Andhra Pradesh Technology Service Limited” payable at Vijayawada valid for
days specified in data sheet from the date of submission of the bid. EMD in any other form shall not be
entertained.
ii. The EMD shall be denominated in Indian Rupees only. No interest will be payable to the bidder on the
amount of the EMD.
iii. Unsuccessful bidder’s EMD will be discharged/ returned as promptly as possible, but not later than 30
days after the award of the contract to the selected implementation agency.
iv. Scanned copy of the receipt of bid purchased from APTS should be uploaded through e-Procurement
process.
v. The physical copies of EMD fee shall be submitted to the concerned as per the details mentioned in the
data sheet. Bids submitted without adequate EMD will be liable for rejection.
vi. The EMD may be forfeited:
a. If a bidder withdraws his bid or increases his quoted prices during the period of bid validity or its
extended period, if any; or
b. In the case of a successful bidder if the bidder fails to sign the contract for any reason not
attributable to the APTS or to furnish Performance Bank Guarantee (PBG) within specified time in
accordance with the format given in the RFP.
c. Bids Submitted with EMD not valid in the specified period will also be rejected
d. During the bid process, if any information is found wrong / manipulated / hidden in the bid. The
decision of APTS regarding forfeiture of the EMD and rejection of bid shall be final & shall not be
called upon question under any circumstances.
Andhra Pradesh Technology Services Page 51 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
13. Bidding Process
13.1. Pre-Bid Meeting and Clarifications
After release of the RFP, APTS will accept Request for Clarification from the interested parties. All
clarifications should be sent in writing as per the format provided in the table below.
S. page number section number in RFP Content of RFP requiring Points of
No. in RFP clarification clarification
required
All clarifications should be sent from email ID of Prime contact person of the bidder on or before the deadline
mentioned in the RFP. Telephone calls will not be accepted for clarifying the queries.
All enquiries / clarifications from the prospective bidders for this RFP must be directed to the contact person
notified by APTS as given in the data sheet. In no event will APTS be responsible for ensuring that Bidders’
inquiries have been received by APTS. APTS may at its option share the replies to the queries by publishing it
in the website www.apts.gov.in/ apeProcurement portal. However, APTS makes no representation or warranty
as to the completeness of any response, nor does APTS undertake to answer all the queries that have been
posed by the Bidder. The bidders or their designated representatives may attend the Pre–Bid Meeting at their
own cost, at the venue on date specified in the RFP Datasheet. It is not mandatory for all the prospective
bidders to attend the pre bid meeting to participate in the pre bid discussions & to receive the clarifications
issued during the pre-bid.
The purpose of the meetings will be to clarify issues and to answer questions on any matter relating to the RFP
that may be raised at that stage. Participants to the Pre-Bid meeting should carry-
1. Proof of purchase of the bid document
2. An Authorization Letter issued from their company.
3. An identity proof issued by their company
4. Not more than 5 representatives for the Bidder
It may be noted that participants not carrying the above documents will not be allowed to attend the Pre-Bid
meeting. The participants are advised to be present 30 minutes in advance to the scheduled time of the Pre-Bid
Meeting.
• Please note that not attending the Pre–Bid Meeting will not be a cause for disqualification of a bidder.
• No queries will be answered in regard to the tender document before the Pre-Bid meeting.
• After issue of pre bid clarifications, no further clarifications shall be entertained.
Andhra Pradesh Technology Services Page 52 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
13.2. Supplementary Information/ Corrigendum / Amendment to the
RFP
i. If APTS deems it appropriate to revise any part of this RFP or to issue additional data to clarify an
interpretation of the provisions of this RFP, it may issue supplements/corrigendum to this RFP. Such
supplemental information will be communicated to all the bidders who participated in the pre-bid
meeting by e-mail and will also be made available on www.apts.gov.in/ apeProcurement portal. Any
such supplement shall be deemed to be incorporated by this reference into this RFP.
ii. At any time prior to the deadline (or as extended by APTS) for submission of bids, APTS, for any
reason, whether at its own initiative or in response to clarifications requested by prospective bidder,
APTS may modify the RFP document by issuing amendment(s). All bidders who have attended the
pre-bid meeting will be notified of such amendment(s) and will also be made available on
www.apts.gov.in/ apeProcurement portal, and these will be binding on all the bidders.
iii. In order to allow bidders a reasonable time to take the amendment(s) into account in preparing their
bids, APTS, at its discretion, may extend the deadline for the submission of bids.
13.3. Cost of Bid Preparation
The bidder shall bear all costs associated with the preparation and submission of its bid and APTS
shall in no event or circumstance be held responsible or liable for these costs, regardless of the
conduct or outcome of the bidding process. All costs incurred in connection with participation in the
bidding process, including, but not limited to, costs incurred in participation in meetings/ discussions/
presentations, preparation of proposal, in providing any additional information required by APTS to
facilitate the evaluation process and in negotiating a definitive contract or all such activities related to
the bid process will be borne by the bidder. This RFP does not commit APTS to award a contract.
Further, no reimbursable cost may be incurred in anticipation of award. Bidders shall furnish the
required information on their technical and commercial proposals in the enclosed formats only. Any
deviations in format will make the tender liable for rejection.
13.4. Bid Submission
13.4.1. Availability of Tender Documents
For the detailed tender notice, please visit our website https:// tender.eprocurement.gov.in and
www.apts.gov.in. For participation in e-tender please visit e-tender website
http://www.eprocurement.gov.in.The bidders are expected to purchase the tender documents as per the
details mentioned in this RFP and examine all instructions, forms, terms, project requirements and
other information in the RFP documents. Failure to furnish all information required as mentioned in
the RFP documents or submission of a proposal not substantially responsive to the RFP documents in
every respect will be at the bidder's risk and may result in rejection of the proposal and forfeiture of
the bid Security.
Andhra Pradesh Technology Services Page 53 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
13.4.2. Registration of Vendors
For registration and online bid submission bidders may contact help desk of M/s APTS,
www.apeprocurement.gov.in or https://tender.apeprocurement.gov.in
13.4.3. Late Bids
Bids received after the due date and the specified time (including the extended period if any) for any
reason whatsoever, shall not be entertained. The bidders have to adhere to the timings mentioned in
the RFP datasheet for submitting the bid through e-Procurement portal.
13.4.4. Digital Certificate Authentication
The bidder shall authenticate the bid with his Digital Certificate for submitting the bid electronically on e-
Procurement platform and the bids not authenticated by digital certificate of the bidder will not be accepted on
the e-Procurement platform. For obtaining Digital Signature Certificate, in case the bidder does not have, they
may contact the persons named in the RFP datasheet
Contact Registration Authorities of any Certifying Authorities in India. The list of CAs is available by clicking
the link: https://tender.apeprocurement.gov.in/DigitalCertificate/signature.html
13.4.5. Payment of Transaction fee
All the participating bidders shall pay transaction fee @ 0.03% (plus GST towards taxes on
transaction fee amount) of quoted value in the commercial bid with a cap of Rs.10,000/- (Rupees Ten
Thousand Only) quoted value in the commercial bid up to Rs.50 Crores and Rs,25,000/- (Rupees
Twenty Five Thousand Only) for quoted value in the commercial bid above Rs.50 Crores at the time
of bid submission, electronically, For tenders wherever ECV is not available (i.e.) for goods and
services, the transaction free shall be calculated on quoted values.
13.4.6. Corpus fund
In addition to the above, the successful bidder shall pay corpus fund to APTS at 0.04% of the contract value
with a cap of Rs.10,000/- (Rupees Ten Thousand Only) for contract value up to Rs.50 Crores and Rs.25,000/-
(Rupees Twenty Five Thousand Only) for the contract value above Rs.50 Crores to sustain ‘e’ procurement
initiatives, Research and Development of software application for automation for processes is user departments.
13.4.7. Mode of Submission
Bids have to be submitted through e-Tendering process (Online – www.eprocurement.gov.in) which
shall be digitally signed. However, the EMD shall be submitted to the concerned person as per the
details mentioned in the data sheet. Bids submitted without EMD will be liable for rejection. Bidders
are requested to submit the bids after issue of minutes of the pre bid meeting duly considering the
changes made if any, during the pre-bid meeting. Bidders are totally responsible for incorporating/
complying the changes/ amendments issued if any during pre-bid meeting in their bid. However, one
(1) hard copies of Pre-Qualification bid& Technical Qualification bids separately and one (1) softcopy
preferably in a Pen Drive with password protection consisting of Pre-Qualification bid & Technical
Qualification separately to be submitted to APTS in separate sealed covers with appropriate titles as
per timelines given in the bid data sheet.
13.4.8. Bid Submission Acknowledgement
The bidder shall complete all the processes and steps required for Bid submission. The system will
generate an acknowledgement with a unique bid submission number after completing all the
prescribed steps and processes by the bidder. Bidders may also note that the bids for which an
Andhra Pradesh Technology Services Page 54 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
acknowledgement is not generated by the e-Procurement system are treated as invalid or not saved in
the system. Such invalid bids are not made available to the Tender Inviting Authority for processing
the bids. The GoAP and APTS are not responsible for incomplete bid submission by bidders.
13.4.9. Deactivation of Bidders
As per the GO. Ms. No. 174 - I&CAD dated: 1-9-2008, if the bidder fails to submit the original hard
copies of uploaded certificates/documents, DD/BG towards EMD within stipulated time or if any
variation is noticed between the uploaded documents and the hardcopies submitted by the bidder, as
the successful bidder will be suspended from participating in the tenders on e-Procurement platform
for a period of 3 years. The e-Procurement system would deactivate the user ID of such defaulting
bidder based on the trigger/recommendation by the Tender Inviting Authority in the system. Besides
this, the department shall invoke all processes of law including criminal prosecution of such
defaulting bidder as an act of extreme deterrence to avoid delays in the tender process for execution of
the development schemes taken up by the government. Other conditions as per tender document are
applicable.
13.4.10. Submission of original EMD, Tender document fee and Proposal
Documents
After uploading the documents, the copies of the uploaded statements, certificates, proposal
documents (except for the Commercial Proposal) are to be submitted by the bidder to the O/o The
Managing Director, APTS, Moghulrajpuram, Vijayawada as per the timelines given in the RFP data
sheet.
a. Submission of original BG which were scanned and uploaded towards EMD and tender
document fee by participating bidders should be submitted to the tender inviting authority on
or before date and time as per the details mentioned in the data sheet.
b. All the bidders shall invariably upload the scanned copies of BG in e-Procurement system and
this will be the prime requirement to consider the bid responsive.
c. The APTS shall carry out the technical evaluation solely based on the uploaded
certificates/documents, BG towards EMD and tender document fee in the e-Procurement
system and open the pre-qualification bid of the responsive bidders.
d. Failure to furnish any of the uploaded documents, certificates, will be entitled in rejection of
the bid. The APTS shall not hold any risk on account of postal delay. Similarly, if any of the
certificates, documents, etc., furnished by the Bidder are found to be false/ fabricated/ bogus,
the bidder will be disqualified, blacklisted, action will be initiated as deemed fit and the Bid
Security will be forfeited.
e. APTS will not hold any risk and responsibility regulating non-visibility of the scanned and
uploaded documents.
f. The Documents that are uploaded online on e-procurement platform will only be considered
for Bid Evaluation.
g. Important Notice to Contractors, Suppliers and Department users
(i) In the endeavour to bring total automation of processes in e-Procurement, the Govt. has
issued orders vide G.O.Ms. No. 13 dated. 5.7.2006 permitting integration of electronic
Payment Gateway of ICICI/ HDFC/ Axis Banks with e-Procurement platform, which
provides a facility to participating suppliers/ contractors to electronically pay the
transaction fee online using their credit cards.
Andhra Pradesh Technology Services Page 55 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
13.5. Proposal Format
The bidder is expected to examine all the instructions, guidelines, terms and conditions and formats in the RFP.
Failure to furnish all the necessary information as required by the RFP on submission of a proposal not
substantially responsive to all the aspects of the RFP shall be at bidders own risk and may be liable for
rejection. The proposal as mentioned shall be submitted in three parts. Information to be included, formats
required in each part are given below:
:
13.5.1. Pre-qualification Proposal
This part shall contain the following documents
a. Pre-Qualification Compliance requirements as per format given in section 23 of this document
b. Bid Application form as prescribed in RFP Form P1
c. Details of the Bidder as prescribed in Form P2
d. Bidder Authorization Letter as prescribed in Form P3
e. Undertaking form for AP GST registration as prescribed in Form P4
f. Certificate from Statutory Auditor stating average annual turnoverForm P5
g. Certificate from statutory auditor stating average annual turnover of the firm from Information security
services as prescribed in Form P6
h. Experience of the Bidder – SOC services as prescribed in Form P7
i. Experience of the bidder MSS as a service form as prescribed in Form P8
j. Declaration regarding clean track record from as prescribed in Form P9
k. Experience of the Bidder form as prescribed in the Form P10
l. Technically Qualified professionals as prescribed in the Form P11
m. Manufacturers Authorization Form as prescribed in the Form P12
13.5.2. Technical Bid
i. The Technical Bid will comprise of a cover letter, documents/annexure as proof against technical
evaluation criteria, details of COTS Product & maintenance facilities, project staffing plan, undertaking
(as given in RFP). Please note that no price information should be indicated in the Technical Bid and
shall only be quoted in the Commercial Bid. Failure to comply with the same may result in the rejection
of the Bid. In submitting additional information, please mark it as ‘Supplemental’ to the required
response. If the bidder wishes to propose additional services (or enhanced levels of services) beyond the
scope of this RFP, the proposal must include a description of such services as a separate attachment to
the proposal.
ii. APTS may seek clarifications from the Bidder on the technical proposal. Any clarifications by the
Bidder on the technical proposal should not have any commercial implications.
iii. Technical approach, methodology and work plan are key components of the technical proposal. Bidders
shall present their technical proposal containing:
A. Compliance requirements: Technical Compliance requirements as per section 27
B. Understanding of Project: This section shall contain a clear and concise understanding of project
requirements along with activities to be performed and deliverables to be provided based on the
scope of work.
C. Technical Approach and Methodology: In this part, bidders should explain their understanding of
the objectives of the assignment, approach to the assignment, proposed solution, proposes
Andhra Pradesh Technology Services Page 56 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
technology methodologies for carrying out activities and obtaining the expected outputs, and the
degree of detail of such output. Bidders should also explain the proposed methodologies and
highlight the compatibility of those methodologies to the proposed approach and the needs of the
project. Applicant shall also include the risk management plan, security, business continuity plan,
disaster recovery plan and quality assurance plans as a part of approach and methodology, Work
methodology & Work Plan: In this part the applicant should propose the main activities of the
assignment, their content and duration, phasing and interrelations, meetings, milestones (including
interim approvals by the client), and delivery dates of the reports/ documents. The proposed work
plan should be consistent with the technical approach and methodology, showing understanding of
the scope of work and ability to translate them into a feasible working plan. A list of the final
documents, including reports to be delivered as final output, should be included here. The work plan
should be consistent with the work schedule, milestones, deliverables, meetings and presentations
shall be clearly mentioned
D. Organization and staffing: In this part the applicant should propose the structure and composition
of team for the main disciplines of the assignment, the key expert/ firm responsible, and proposed
technical and support staff may be provided. Capacity building: Bidder should submit a brief
approach note on training of APTS/ITE&C Department staff during implementation and post-
implementation. Bidder should provide hands on training before requesting for acceptance and
completion of implementation. Training and manual details should be provided to all the users.
E. Approach for Project implementation: Detailed approach for carrying out the project
implementation along with the support and maintenance during the contract. Bidders should submit
a detailed approach for both first and second phase implementation. Bidders need to give detailed
approach how they would implement complete project with integration plan.
F. Company profile: Details of the point of contact along with brief work profile of the Bidder as well
as other partner firms including relevant experiences of executing similar projects. Bidder may
include relevant case studies and attested copies of completion certificates from clients in support of
the case studies.
G. Innovation: If any, on the RFP to improve performance in carrying out the project. Innovativeness
in terms of proposing the functional services that can be taken up by the APTS/ITE&C Department
beyond what is already provided in the RFP shall be appreciated.
H. Other Information: Any other information relevant to the solution as preferred by the bidder can
also be placed in the document.
I. Technical Forms: The Bidder shall submit the technical Forms as per the list given below
i. Form T1: Form T1 : Total Average Annual turnover
ii. Form T2 : Total average annual turnover from Information Security services
iii. Form T3 : Details of projects with successful implementation of proposed SIEM
iv. Form T4 : Details of AP-SOC assignments in last three financial years
v. Form T5 : Details of MSS
vi. Form T6 : Details of Technically Qualified Personnel from the area of IT Security
Services and are on the Bidders payroll for the past three years
13.5.3. Commercial Proposal
A. The commercial bid form as prescribed in the e-Tendering website and in section 22.3.2 of the
RFP as per the Financial Proposal submission form as prescribed:
B. Bidder shall clearly mention unit rates and total amount for each component. Any discrepancy
between words and figures noted against each item of the RFP and between unit rates and total
Andhra Pradesh Technology Services Page 57 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
amount, the decision of APTS will be final and binding on the proposals (in case of
discrepancy, the amount in words will be considered as final).
C. Prices quoted by the Bidder shall be final (exclusive of all taxes, duties, insurance, license fee
and other costs). No variation in prices will be allowed under any circumstances during the
entire period of project. No Conditional and open ended bid shall be evaluated and the
same is liable for rejection.
D. The commercial proposal submitted by the Bidder should be inclusive of all the items in the
technical proposal and should incorporate all the clarifications provided by the Bidder on the
technical proposal during the evaluation of the technical proposal.
E. Prices shall be quoted in Indian Rupees (INR) only.
F. The Bidder shall quote the price for all the components, the services of the solution to meet the
requirements of C-SOC as listed in this RFP.
G. Bids with price adjustment shall be rejected.
H. The price quoted in the commercial proposal shall be the only payment, payable by APTS to
the successful Bidder for completion of the contractual obligations by the successful Bidder
under the Contract, subject to the terms of payment specified as in the proposed commercial
bid or the one agreed between APTS and the Bidder. The price would be inclusive of all taxes,
duties, charges and levies as applicable.
I. The prices, once offered, must remain fixed and must not be subject to escalation for any
reason whatsoever within the period of the validity of the proposal and the contract (for
successful bidder). A proposal submitted with an adjustable price quotation or conditional
proposal may be rejected as nonresponsive.
J. Bidder should provide all prices, quantities as per the prescribed format given in volume II of
this RFP. Bidder should not leave any field blank. In case the field is not applicable, Bidder
must indicate “0” (zero) in all such fields.
K. It is mandatory to provide breakup of all taxes, duties and levies wherever applicable and/or
payable. All the taxes of any nature whatsoever shall be borne by the Bidder.
L. The bid amount shall be inclusive of packing, forwarding, transportation, insurance, delivery
charges and any other charges as applicable till the end of the contract period.
M. APTS / ITE &C Department reserves the right to ask the Bidder to submit proof of payment
against any of the taxes, duties, levies indicated within specified time frames.
N. Price Commitment and Validity: As part of the technical proposal, the Bidder will be asked to
provide a complete Bill of Materials (along with the complete technical specifications for each
of the individual items) for the procurement of the components required for APTS/ITE&C
Department and for their maintenance as specified in this RFP. In the Commercial bid, the
Bidder will be asked to provide pricing for the same. Managing Director, APTS reserves the
right to procure (by itself) the proposed components from the Bidder at rates not exceeding the
rates proposed by the Bidder as part of their Commercial Proposal.
13.6. Modification and Withdrawal of Bids
a. No bid may be withdrawn, substituted, or modified in the interval between the bid submission deadline
and the expiration of the bid validity period specified by the Bidder in the Bid Submission Form, or any
extension thereof agreed to by the Bidder. Modification/Withdrawal of the Bid sent through any other
means shall not be considered by the Purchaser
Andhra Pradesh Technology Services Page 58 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
b. The Bidder may withdraw, substitute, or modify its bid on the e-procurement portal, in accordance with
the process specified below, no later than the date and time specified in the BDS
c. The process of modification & withdrawal of bid:
i. The bidder can withdraw/modify the bid submitted by him previously. However, if a bid is
withdrawn, the bidder can’t participate in the bid again.
ii. After entering with the Login ID and Password, the bidder can modify or resubmit the bid
for any number of times till the last date of submission by clicking on the option “My bid”.
The lists of tenders which the bidder participated previously are displayed here with the bid
ID.
iii. Each Bid ID has a corresponding “Action” column containing the list of icons for ‘Rebid
Submission, EMD Resubmission, Tender Fee Resubmission, Financial Bid Resubmission,
Bid Withdrawal’ are displayed.
iv. After resubmission, the bidder will get an acknowledgment with Re-Bid Attempts Counter
Number for that particular bid. As the bidder attempts further rebid submissions, the Re-
Bid Attempts Counter number goes on increasing.
v. In Case of withdrawal of bid, the bidder need to click the “Withdraw Bid “Icon under
“Action” column of respective bid ID in ‘My Bid’ Section. Once the bidder with draws the
bid, he/she cannot participate in the bid again. For further details please refer ‘Bidders
Manual KIT’ by logging into https://eprocure.gov.in/eprocure/app
d. No bid may be modified subsequent to the deadline for submission of bids. No bid may be withdrawn
in the interval between the deadline for submission of bids and the expiration of period of bid validity
specified by the Bidder on the bid form. Withdrawal of a bid during this interval may result in the
forfeiture of EMD of the bidder.
13.7. Conditions under which this RFP is issued
a. This RFP is not an offer and is issued with no commitment. APTS reserves the right to
withdraw the RFP and change or vary any part thereof at any stage. APTS also reserves the
right to disqualify any bidder should it be so necessary at any stage.
b. Timing and sequence of events resulting from this RFP shall ultimately be determined by
APTS
c. No oral conversations or agreements with any official, agent, or employee of APTS/ ITE & C
Department shall affect or modify any terms of this RFP and any alleged oral agreement or
arrangement made by a bidder with any department, agency, official or employee of Andhra
Pradesh shall be superseded by the definitive agreement that results from this RFP process.
Oral communications by Pasto bidders shall not be considered binding on APTS, nor shall any
written materials provided by any person other than MD, APTS
d. Neither the bidder nor any of the bidder’s representatives shall have any claims whatsoever
against APTS or any of their respective officials, agents, or employees arising out of or
relating to this RFP or these procedures (other than those arising under a definitive service
agreement with the bidder in accordance with the terms thereof).
e. Until the contract is awarded and during the currency of the contract, bidders shall not, directly
or indirectly, solicit any employee of APTS or any other officials involved in this RFP process
to leave APTS in order to accept employment with the bidder, or any person acting in concert
with the bidder, without prior written approval of APTS.
Andhra Pradesh Technology Services Page 59 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
13.8. Rights to the Content of Proposal
All proposals and accompanying documentation of the Technical proposal will become the property
of APTS and will not be returned after opening of the technical proposals. APTS shall not be bound
by any language in the proposal indicating the confidentiality of the proposal or any other restriction
on its use or disclosure.
13.9. Non-Conforming Proposals
A proposal may be construed as a non-conforming proposal and ineligible for consideration:-
a. If it does not comply with the requirements of this RFP. Failure to comply with the technical
requirements, and acknowledgment of receipt of amendments, are common causes for holding
proposals non-conforming
b. If a proposal appears to be “canned” presentations of promotional materials that do not follow
the format requested in this RFP or do not appear to address the particular requirements of the
proposed solution, and any such bidders may also be disqualified
Andhra Pradesh Technology Services Page 60 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
14. Bid Opening and Bid Evaluation Process
14.1. Bid Opening
APTS will open all the bids submitted online, in the presence of bidders’ representatives who choose to attend
the Bid opening as per the RFP Datasheet. Bid opening will be performed at three stages as per the dates
specified in RFP data sheet
i. Pre-Qualification Bid
ii. Technical Bid
iii. Commercial Bid
14.2. Bid Evaluation Process
14.2.1. Preliminary Scrutiny
The APTS will examine the bids to determine whether they are complete, whether any computational errors
have been made, whether required sureties have been furnished, whether the documents have been properly
signed, and whether the bids are generally in order.
The tenders that do not conform to the tender conditions and tenders from firms without EMD, Bid document
fee shall be straight away rejected.
Subsequent to the preliminary scrutiny and identification of qualified bidders, further evaluation of the bids will
be done in three stages and at the end of every stage short listed bidders will be informed of the result to have a
fair and transparent competition.
14.2.2. Evaluation of Pre-Qualification Criteria
The evaluation committee as per the GO.Rt.5, dated 13.01.2016, ITE&C Department, issued by Government of
Andhra Pradesh, will evaluate all pre-qualification bids to determine if they are responsive and meeting all the
pre-qualification requirements of the RFP. APTS will prepare a list of firms based on the compliance to the pre-
qualification criteria. The tenders that do not conform to the tender conditions and tenders from firms without
adequate capabilities as per pre-qualification criteria in Volume II of this RFP shall be straight away rejected.
All eligible tenders will be considered for further evaluation. The decision of APTS will be final in this regard.
14.2.3. Evaluation of Technical Bids
The evaluation of the Technical bids will be carried out in the following manner:
1. The technical bid will be examined by an evaluation committee as per the GO.Rt.5, dated 13.01.2016, ITE
&C Department, Government of Andhra Pradesh, based on the evaluation criteria and the points system
specified in this RFP.
2. The bidders, who score an aggregate technical score of 80, will qualify for the evaluation of the commercial
bid.
3. Non Compliance of any technical specification in the hardware proposed from the RFP requirements, the
proposal shall be summarily rejected.
Andhra Pradesh Technology Services Page 61 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
14.2.4. Criteria for Technical Evaluation
1. The Evaluation Committee feels that the following parameters are critical for the success of an e-
governance project and expects the bidders to provide accurate and precise information in their responses.
2. Technical proposal of the bidders will be opened and evaluated who meets all the prequalification criteria.
The evaluation committee will evaluate the Technical Proposals on the basis of the technical evaluation
criterion as provided below. The bidder has to follow the structure while drafting the RFP as per the Forms
provided against each criterion. The bidder should attain a qualifying score of 75 marks to be considered
for the Commercial bid. The bidder who fails to attain 75 marks overall in Technical score would be
considered as dis-qualified
Max Form
S. No. Evaluation Criteria
Score No
The Average Annual Turnover of the bidder in the last three 4 T1
financial years (In FY 2016-17, FY 2015-16 and FY 2014-15).
I a) Rs 100 cr to <=200 cr 2 Marks (or)
b) >Rs200 cr to <500cr 3 Marks (or)
c) >=Rs 500 cr 4 Marks
II The Annual Turnover of the bidder in the last three financial years 6 T2
exclusively from Information Security services (In FY 2016-17,
FY 2015-16 and FY 2014-15).
a) Rs 25 to <=50 cr 4 Marks (or)
b) >50 to <=75 cr 5 Marks (or)
c) >Rs 75 cr 6 Marks
The Bidder’s successful implementation experience with proposed 10 T3
SIEM at Public/ Private Organization in India or Globally in last
three years.
III a) <2 to <=4 6Marks (or)
b) >4 to <=6 8 Marks (or)
c) >6 10 Marks
Number of SOC completed /go-live projects in India/Global in last 10 T4
3 financial years, each with value not less than Rs. 5 Crores value
in last 3 years
IV a) 2 to <=4 6 Marks (or)
b) >4 to <=6 8 Marks (or)
c) >6 10 Marks
Number of Managed Security Operations Services (MSS) to 15 T4
Clients (India/Global) with minimum 5000 EPS for last 3 financial
years
V a) <5 clients 10 Marks
b) >=5 and <7 clients 12 Marks
c) >=8 Clients 15 Marks
Proposed Organization Structure and team profiles. This will cover 20 T4
the number of resources proposed, Education/certification and
experience
VI Project Director –6 Marks
Andhra Pradesh Technology Services Page 62 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Max Form
S. No. Evaluation Criteria
Score No
a) Project Manager –4 Marks
b) Design Lead 4 Marks
c) L3 Profiles - 6 Marks
Approach and Methodology 15 T4
Bidder approach and methodology to design, implement and
operate the AP-SOC.
VII a) Understanding of the Project objective and requirement - 1
marks
b) Approach for AP-SOC integration and operations – 3
Marks
c) SLA Management methodology, SLA monitoring console
for PMU – 3 Marks
d) Approach for positing services to other State Government
Departments and private organizations – 3 Marks
e) Risk Management Strategy – Highlight the associated
risks/problem and plans for mitigations - 3 Marks
f) Proposed timelines activities. Sequencing and dependencies
amount activities and WBS –2 Marks
VIII Technology Solution design/ Architecture proposed 15
a) Solution Design and Architecture – 10 Marks
b) Proposed tools/ products and roadmap – 5 Marks
IX Exit Management 5
a. Comprehensiveness & completeness of the plan for exit
management – 5 Marks
100
14.2.5. Proposed Man Power
Bidder is required to carry out due diligence for the number of resources to run the operations successfully. However,
bidder is required to propose the following minimum resources. The following is indicative number of resources for the
first year and consider for evaluation
S.No Track Role Resources Expected
required time
window
1. Governance and Management Project Director 1 General
Shift
2. Governance and Management Project Manager 1 General
Shift
3. Engineering and Architecture Design Lead 1 General
( on boarding) Shift
4. Monitoring L3 Security Analysts 3 General
shift
L2 Security Analysts 9 24/7
L1 Security Analysts 9 24/7
5. Brand Management/ Track Lead 3 General
Protection shift
6. Device configuration & L1Security Analysts 5 24*7
Andhra Pradesh Technology Services Page 63 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
7. Management Team L2 Security Analysts 3 General
Shift
L3 Security Analysts 3 General
Shift
Total 38
Help Desk
Bidder will provision sufficient number of resources and also the required infrastructure as per the
requirement.
14.2.6. Qualifications required for the proposed Team
Minimum Preferred
S.No Role Minimum Key Roles & Responsibilities
Qualifications Certifications
1. Monitor Client events for malicious
traffic
2. Monitor Alerts which are triggered
1. Engineering
for the client
Graduate/MCA
3. Escalate the Alerts/Malicious traffic
2. Minimum of 1-3
to SOC Analyst/Shift lead for their
L1 Security year of
Review
Analyst experience in the CCNA, CCSP,
4. Update Signatures for IDS/IPS for
IT security CEH
1. managed Customer
industry,
5. Follow-up with the SOC Analyst for
preferably
open tickets
working in a
6. Follow-up with vendors for open
SOC/NOC
issues
environment
7. Perform tasks as identified in a daily
task list
8. Administor tools, patching, and DR
1. Engineering
Graduate/MCA
1. Support implementation
2. Minimum of 3-5
of SOC processes and perform
year of
periodic check for compliance CCNA, CCSP,
L2 Security experience in the
2. Handle Incident Escalations CEH
2. Analyst IT security
from SOC L1
industry,
3. Conduct periodic Vulnerability
preferably
Assessment and Reporting
working in a
4. Client Engagement
SOC/NOC
environment
1. Engineering 1. Prior work experience in SOC or Security or
Graduate/MCA NOC environment Network
2. Minimum of 5-8 2. Familiarity needed with several certification is
L3 Security
year of key security technologies Cisco desirable, with
3. Analyst
experience in the Security products, Checkpoint relevant
IT security firewalls, Juniper firewalls, DLP certifications like
industry, tools( MacAfee) , Source fire CISSP, CISM,
preferably IDS, MacAfee/splunk SIEM , CISA or GIA
Andhra Pradesh Technology Services Page 64 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Minimum Preferred
S.No Role Minimum Key Roles & Responsibilities
Qualifications Certifications
working in a Certificate and key management
SOC/NOC tools, Firewall monitoring and
environment OS compliance checkers.
3. System administration
background in Linux/Unix
Strong analytical and problem
solving skills
4. Assessment and Reporting
5. Client Engagement
1. Lead and manage Security
Operations Center
2. Primarily responsible for security
event monitoring, management and
1. Engineering
response
Graduate/MCA/P
3. Ensure incident identification, 1. CEH
ost Graduate with
assessment, quantification, 2. Additionally
certification or
reporting, communication, one more
SOC specialization in
mitigation and monitoring certification in
Manager domain areas
4. Ensure compliance to SLA, process information
2. Minimum of 10+
adherence and process improvisation security
4. Years’
to achieve operational objectives domain.
experiencein the
5. Revise and develop processes to 3. CISSP
IT security
strengthen the current Security 4. PMP
industry,
Operations Framework, Review 5. GCIH
preferably
policies and highlight the challenges 6. GSEC
working in a
in managing SLAs
SOC/NOC
6. Responsible for team & vendor
environment
management, overall use of
resources and initiation of corrective
action where required for Security
Operations Center
1. Engineering
Graduate/MCA/P
ost Graduate with 1. CEH
certification or 2. Additionally
specialization in one more
domain areas. certification in
2. 1. Design and Implement information
Solution Minimum of 8 of SOC Architecture and perform security
5.
Architect Years’ periodic check for compliance domain.
experiencein the 3. CISSP
IT security 4. PMP
industry, 5. GCIH
preferably 6. GSEC
working in a
SOC/NOC
environment
Andhra Pradesh Technology Services Page 65 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Minimum Preferred
S.No Role Minimum Key Roles & Responsibilities
Qualifications Certifications
1. Engineering
Graduate/MCA
2. Minimum of 1-2
year of 1. L1 Operations of Network Security
experience in the devices
CCNA or Tool
L1 Device IT security 2. Patch Management
6. based
Management industry, 3. Updating devices
certifications
preferably 4. Tickets Handling
working in a
SOC/NOC
environment
1. Engineering
Graduate/MCA
2. Minimum of 3
1. L2 Operations of Network Security
year of
devices CCNA or Tool
experience in the
2. Patch Management based
L2 Device IT security
7. 3. Troubleshooting and testing certifications
Management industry,
4. Updating devices
preferably
5. Tickets Handling
working in a
SOC/NOC
environment
1. Familiarity needed with several
key security technologies Cisco
Security products, Checkpoint
1. Engineering
firewalls, Juniper firewalls, DLP
Graduate/MCA
tools( MacAfee) , Source fire
Minimum of 5-6
IDS, MacAfee/splunk SIEM ,
year of
Certificate and key management
experience in the CCNP and Any
L3 Device tools, Firewall monitoring and
8. IT security other Tool based
Management OS compliance checkers.
industry, certifications
2. System administration
preferably
background in Linux/Unix
working in a
Strong analytical and problem
SOC/NOC
solving skills
environment
3. Assessment and Reporting
Client Engagement
1. Engineering
Graduate/MCA
Brand 2. Minimum of 3-5
Management year of
9. CEH/OSCP/CISM
and experience in the
Protection IT security
industry
Andhra Pradesh Technology Services Page 66 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
14.2.7. Technical Presentations
Bidder has to make presentations at APTS premises or at a place decided by APTS to facilitate the procurement
committee in understanding the bidder’s capabilities to execute the project. The date for presentation will be
communicated in advance. Bidder are expected to communicate the requirements for conducting this exercise 2
days in advance to APTS. Bidder shall ensure that the representative carries a valid photo ID and
authorization letter from the bidder.
The presentations should cover cases of installations of the software in an environment similar to APTS/ITE&C
requirements. The objective of the presentation is to:
1. Understand software solution’s features in greater detail
2. Approach and Methodology
3. Project plan
4. Technical solution proposed in the technical bid
5. Innovative services proposed in the technical proposal
6. Hardware phasing, deployment and maintenance
7. Other important components of the proposal
14.3. Commercial Bid Opening and Evaluation Process
14.3.1. Bid Opening
Commercial Bids will be opened and compared after the technical evaluation has been completed for
those bidders who are technically qualified with the 80% qualifying marks.
14.3.2. Announcement of Bids
The commercial bids will be opened, in the online presence of bidders or their representatives who
choose to attend the commercial bid opening on date and time to be communicated to all the
technically qualified bidders. In the event of the specified date of bid opening being declared a holiday
for APTS, the bids shall be opened at the appointed time and location on the next working day.
The Bidders/Bidder’s representatives present at the commercial bid opening shall sign a register
evidencing their attendance.
14.3.3. Clarification on Commercial Bids
To assist in the evaluation, comparison and an examination of bids, APTS may, at its sole discretion,
ask the bidder for a clarification of its bid including breakdown of unit rates. The request for
clarification and the response shall be in writing. If the response to the clarification is not received
before the expiration of deadline prescribed in the request, APTS reserves the right to make its own
reasonable assumptions at the total risk and cost of the bidder
Andhra Pradesh Technology Services Page 67 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
14.3.4. Evaluation of Commercial Bids
14.3.4.1. Change in the Quantities
The Contracting authority reserves it right to alter the scope (increase quantity / remove certain items)
up to approximate (±10 %) units
14.3.4.2. Commercial Evaluation Process
The Commercial Bids of the Bidders who qualify in the First Stage will be evaluated as per the
Evaluation Criteria mentioned below:
a. The prices should be all exclusive of taxes but inclusive of all Out of Pocket Expenses (OPEs.)
b. All expenses related to travel, boarding, lodging etc. would be inclusive and no separate claims
on any account would be entertained.
c. All the taxes and other levies indicated in the price bid will be taken for the price bid
evaluation.
d. The total value of the price bid shall be arrived based on the total value quoted by the bidder
for Capital expenditure and Operational expenditure
The Commercial Bids of the Bidders who qualify in the Technical Stage will be evaluated as per the Evaluation
Criteria mentioned below:
a. The commercial evaluation shall be based in accordance with the following criteria
i. All the bids will be compared on the basis of their Lowest Grand Total specified in the section
Note: Arithmetical Errors in Commercial Proposals - If there is a discrepancy between the unit price
and the total price that is obtained by multiplying the unit price and quantity, the unit price shall
prevail and the total price shall be corrected. If there is a discrepancy between the rates in
words and figures, the rate in words will govern. If the bidder does not accept the correction of
errors, the bid will be rejected and EMD may be forfeited. Bidder is advised to exercise
adequate care in quoting the prices. No excuse for corrections in the quoted figures will be
entertained after the commercial proposals are received by APTS.
14.3.5. Total Bid Evaluation
The Bidder with the lowest grand total is the successful bidder
14.4. Award of Contract
14.4.1. Notification of Award
Notification of Award shall be to the Best Value Bid. Prior to the expiration of the bid validity period, APTS
will notify the successful bidder in writing or by fax or email, to be confirmed in writing by letter, that its
proposal has been accepted. The notification of award will constitute the formation of the contract. Upon the
successful bidder's furnishing of performance bank guarantee, APTS will promptly notify each unsuccessful
bidder and return their bid security.
Andhra Pradesh Technology Services Page 68 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
14.4.2. Performance Security
On receipt of notification of award from APTS, the successful bidder shall furnish the performance security in
accordance with the conditions of contract, as mentioned in forms of volume II of the RFP.
a. A PBG for an amount of xxxx should be furnished by the bidder in the form of a Bank Guarantee
as per the format provided in this RFP Forms from Nationalized/ scheduled banks in India
b. The PBG should be furnished within the stipulated working days mentioned in the bid data sheet
from the signing of the contract and should be valid for entire term of the contract.
c. The Performance Bank Guarantee should be valid for the period specified in Bid Data Sheet
d. The performance guarantee shall be returned to the Bidder within 30 days of the date of successful
discharge of all contractual obligations at the end of the period of the agreement by the APTS
e. In the event of any amendments to agreement, the bidder shall within 15 days of receipt of such
amendment furnish the amendment to the performance guarantee as required.
Failure of the successful bidder to sign the contract in the specified period, proposed in this document and as
may be modified, elaborated or amended through the award letter, shall constitute sufficient grounds for the
annulment of the award and forfeiture of the bid security, in which event APTS may make the award to another
bidder or call for new bids.
14.4.3. APTS’s Right to accept / reject any proposal or all proposals
APTS reserves the right to accept or reject any proposal, and to annul the tendering process and reject all
proposals at any time prior to award of contract, without thereby incurring any liability to the affected bidder or
bidders or any obligation to inform the affected bidder or bidders of the grounds for APTS action.
14.4.4. Signing of Contract
At the same time as APTS notifies the successful bidder that its proposal has been accepted, Managing
Director, APTS shall enter into a contract, incorporating all agreements as indicated in this RFP and to be
discussed and agreed upon separately, if necessary, between APTS and the successful bidder.
14.4.5. Failure to agree with the Terms & Conditions of the RFP
Failure of the successful bidder to agree with the Terms & Conditions of the RFP shall constitute sufficient
grounds for the annulment of the award, in which event APTS may award the contract to the next best value
bidder as per this RFP or call for new proposals or invoke the EMD/PBG.
14.5. Disqualification
The proposal is liable to be disqualified under the following cases:
a. Proposal not submitted in accordance with this document.
b. Proposal is received in incomplete form.
c. Proposal is received after due date and time.
d. The bidder qualifies the proposal with his own conditions
e. Proposal is not accompanied by all requisite documents/EMD/Tender cost.
f. Information submitted is found to be misrepresented, incorrect or false, accidentally, unwittingly or
otherwise, at any time during the processing of the contract (no matter at what stage) or during the
tenure of the contract including the extension period if any.
Andhra Pradesh Technology Services Page 69 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
g. The price information, the pricing policy or pricing mechanisms or any document indicative of the
commercial aspects of the proposal are either fully or partially enclosed or is part of the Pre-
Qualification Bid/Technical Proposal Bid.
h. Bidder fails to deposit the Performance Bank Guarantee (PBG) at the time of signing the contract.
i. Bidder does not sign the contract within 15 days of the receiving the letter of acceptance from
APTS.
j. Bidder or any person acting on its behalf indulges in corrupt and fraudulent practices.
k. If bidder provides quotation only for a part of the project
l. In case any one bidder submits multiple proposals or if common interests are found in two or more
bidders, the bidders are likely to be disqualified, unless additional proposals/bidders are withdrawn
upon notice immediately
m. Bidders may specifically note that while evaluating the proposals, if it comes to APTS’s knowledge
expressly or implied, that some bidders may have colluded in any manner whatsoever or otherwise
joined to form an alliance resulting in delaying the processing of proposal then the bidders so
involved are liable to be disqualified for this contract as well as for a further period of three years
from participation in any of the tenders floated by APTS
n. The response to the pre-qualification criteria, technical proposal and the entire documentation
submitted should not contain any information on price, pricing policy, pricing mechanism or any
information indicative of the commercial aspects of the bid.
o. During validity of the proposal, or its extended period, if any, the Bidder increases prices quoted in
the commercial proposal.
Andhra Pradesh Technology Services Page 70 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
15. Service Level Agreement
Note:
1. Service levels will be monitored by APTS directly or by a third party appointed by APTS and selected
bidder is responsible to share the information for monitoring purposes
2. All the govt. data should be secure and should not go out of Indian territory
15.1. Definitions
a) Days: All Working and Non-working days (365 days in a calendar year)
b) “Scheduled Maintenance Time” shall mean the time that the System is not in service due to a scheduled
activity as defined in this SLA. The scheduled maintenance time would not be during 16X7 (7:00 am to 11:00
pm) timeframe preferably on weekends. Further, scheduled maintenance time is planned downtime taken after
permission of the client.
c) “Scheduled operation time” means the scheduled operating hours of the System for the month. All scheduled
maintenance time on the system would be deducted from the total operation time for the month to give the
scheduled operation time. The total operation time for the systems and applications within the DCs and near
DCs will be 24X7X365 (per year).
d) “System or Device downtime” means accumulated time during which the System is totally inoperable within
the Scheduled Operation Time but outside the scheduled maintenance time and measured from the time a call is
logged with the BIDDER of the failure or the failure is known to the BIDDER from the availability
measurement tools to the time when the System is returned to proper operation.
e) “Availability” means the time for which the services and facilities are available for conducting operations on
the system including application and associated infrastructure. Availability is defined as: {(Scheduled
Operation Time – System Downtime)/ (Scheduled Operation Time)} * 100%
f) “Helpdesk Support” shall mean the support centre which shall handle Fault reporting, Trouble Ticketing and
related enquiries during this contract. Helpdesk support is to be provided as per service window defined in this
RFP.
g) “Incident” refers to any event/abnormalities in the functioning of the any of IT Equipment/Services that may
lead to disruption in normal operations of the Data Centre, System or Device services.
15.2. Interpretation & General Instructions
a) During O&M phase, the SLA parameters shall be monitored on a monthly basis as per the individual SLA
parameter requirements. In case the service levels cannot be achieved at service levels defined in the tables
below, it shall result in a breach of contract and shall invoke liquidated damages.
b) SLAs would be reported monthly. A Service Level breach will occur if the bidder fails to meet Minimum
Service Levels on a monthly basis for a particular Service Level. Root cause analysis (RCA) to be prepared for
all cases of breach in SLA’s and shared with the client. For any exceptions or SLA breach beyond the control
of the bidder, the bidder may submit the RCA along with a justification, which may be considered by the client.
c) For certain incidents, RCA may be carried out by the client (or the client appointed agency).
d) Liquidated damages are mentioned as a percentage of certain components of cost. The liquidated damages
per quarter are capped at 20% of that year’s payment.
e) If on performance evaluation it is found that the SLA has not been met for two consecutive reporting periods,
the same shall result in doubling the liquidated damages of that measurement parameter.
Andhra Pradesh Technology Services Page 71 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
f) If liquidated damages calculations exceed 19% of the quarterly payment for two consecutive quarters, then
the client can take appropriate action including termination of the contract and forfeiting of Performance Bank
Guarantee. If liquidated damages calculations in any quarter exceed 30% of quarterly payment, then the client
can take appropriate action including termination of the contract and forfeiting of Performance Bank
Guarantee.
g) During the transition phase, the SLAs would be calculated but the liquidated damages may be applicable at a
reduced rate, as per the client’s discretion.
h) Bidder shall be responsible for the approval of all policy documents wherever applicable.
i) The severity levels of SLAs and the associated financial Liquidated Damages are defined as per the following
table:
Liquidated Damages as a percentage of Monthyl payment
Severity Level
applicable
1 2.0%
2 1.0%
3 0.5%
4 0.25%
15.3. Implementation Phase related Performance Levels
# SLA Parameter Definition Target Severity Level
1. Team mobilization of 1. The Bidder is expected to T = 30 Days Nil
Critical resources (as mobilize the team for
proposed by bidder ) commencement of work for 30 days < T < 45 4
and commencement of this project. days
work
2. Critical leads to be
deployed within 30 calendar 45 days < T < 60 3
days from the date of days
release of purchase order.
T > 60 Days 2
3. For Facilities Management
Services, commencement of
work would mean,
reporting of all proposed
FM resources at the
respective reporting
locations
4. For System Integration
Services, commencement of
work would mean reporting
of bidder resources at the
designated client location
for project &
implementation planning,
analysis and design.
Andhra Pradesh Technology Services Page 72 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
# SLA Parameter Definition Target Severity Level
2. Delay in any of the Measured as the difference T = 5 Days Nil
project milestones between the planned date for
(including transition) the milestone and the actual 5 day < T < 10 days 4
as agreed in the date of its completion.
Project Plan 10 days < T < 30 3
Target: <5 Days
days
31 days < T < 45 2
days
T > 45 Days 1
Note: In the event of circumstances beyond the control of vendor, the target dates may be revised with mutual
agreement.
Andhra Pradesh Technology Services Page 73 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
15.4. Operations
15.4.1. (AP-SOC)
# SLA Category Definition Target Severit
y
1. Integration of devices with SIEM having T>= 99% Nil
compatible connector/integrators within 10
days from the confirmation from the
client. T < 99% 4
Target: 99%
Frequency of measurement : monthly
Device Integration with
SIEM
Integration of devices with SIEM having T>= 95% Nil
non-compatible connectors/integrator
within 45 day from the conformation from T < 95% 4
the client.
Target: 95%
Frequency of measurement : monthly
2. % of logs captured as per logging level T>= 98% Nil
agreed.
Log Quality T < 98% 4
Target: 98% of the log source
Frequency of measurement : monthly
3. Correlation rules & Configuration of correlation rules & T=30 Days Nil
threshold values threshold values within 30 days from
Andhra Pradesh Technology Services Page 74 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
T + 5 days 4
T + 10 days 3
T + 20 days 2
T + 30 days 1
% of new correlation rules included on a T >=10% Nil
quarterly basis. Number of new correlation
rules configured or fine tuning of the < 10% 3
existing rules during the reporting
period/total number of existing correlation
rules
Frequency of measurement: quarterly
Uptime of the AP-SOC components/tools T>=99.99% Nil
4. as per system availability in percentage.
AP-SOC services Target: 99.99% 99.98% > T > 99.8 % 4
uptime (SIEM,
Frequency of measurement: monthly
Monitoring tool, ITSM 99.79%> T > 99.5 % 3
tool, Helpdesk portal Note: Availability shall be measured on
etc) each AP-SOC component. Final penalty to 99.49% > T > 99.0 % 2
be levied will be the average of the
individual penalties for each service 99% >= T 1
Monthly Update/Upgrade/Patching of T = once in a month Nil
5. SIEM as per agreed change management
process Deviation 2
SIEM Solution
Update/Upgrade/Patchi
ng Ad hoc Update/Upgrade/Patching of T = 1 days Nil
SIEM as per agreed emergency change
management process >T 2
24 x 7 x 365 monitoring of logs from all T=100% Nil
6. devices in scope.
100% > T >=99 % 4
Monitoring & Log Target: 100% devices
98.99%> T >= 98 % 3
Analysis Services
97.99% > T >= 97.0
2
%
97% > T 1
Based on criticality, priority events should
7. be logged as incident tickets by SIEM and
Incident management responded by the BIDDER.
P1 : Critical T>=99% Nil
Andhra Pradesh Technology Services Page 75 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
% of P1 tickets responded within 15 mins.
98.99% > T >= 98 % 4
97.99%> T >= 95 % 3
T < 95 % 2
P2 : High T>=99% Nil
% of P2 tickets responded within 30 mins. 98.99% > T >= 98 % 4
97.99%> T >= 95 % 3
T < 95 % 2
P3 : Medium T>=95% Nil
% of P3 tickets responded within 60 mins. 94.99% > T >= 90 % 4
90% > T >= 85 % 3
T < 85 % 2
P4 : Low T>=90% Nil
% of P4 tickets responded within 120 T < 90 % 4
mins.
Incident resolution for the devices /
solutions managed and administrated
by Bidder
T>=99% Nil
P1: 99 % of all critical incidents within 4
hours of the event identification
99% > T >=95 % 4
95%> T >= 92 % 3
92% > T >= 90 % 2
90% > T 1
T>=99% Nil
P2: 99% of all high priority incidents
within 8 hours of the event identification
99% > T >=95 % 4
95%> T >= 92 % 3
92% > T >= 90 % 2
90% > T 1
T>=99% Nil
P3: 99%of all medium priority incidents
Andhra Pradesh Technology Services Page 76 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
within 24 hrs of the event identification. 98.99% > T >= 98 % 4
97.99%> T >= 95 % 3
T < 95 % 2
T>=95% Nil
P4: 95% of all low priority incidents
within 72 hrs of the event identification
94.99% > T >= 90 % 4
Andhra Pradesh Technology Services Page 77 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
15.4.2. Security Device Management
Severity
# SLA Parameter Definition Target
Level
% of devices on-boarded within 30 days from T>= 99% Nil
written confirmation by the client.
99% > T >=98% 4
On boarding means operational transition of
devices from the existing service provider or
1 Device On-boarding 98% > T >=97% 3
after go live of any new security devices into
production.
97% > T >=95% 2
Target: 99%
Frequency of measurement: monthly T <=95% 1
T>= 99% Nil
% of devices for which Update / Upgrade /
Patching is completed as per agreed standard
99% > T >=98% 4
change management process.
Target: Patching and updating of all devices to 98% > T >=97% 3
be conducted within 5 days from release of
advisory. 97% > T >=95% 2
Update / Upgrade / Frequency of measurement: Quarterly
2 T <=95% 1
Patching
% of devices Update / Upgrade / Patching of T = 100% Nil
the devices as per agreed emergency change
management process (Highly Critical patches) 100% > T >=95% 2
Target: Patching and updating of all devices
within one day from release of advisory.
T <=95% 1
Frequency of measurement: Quarterly
Uptime = {1 - [(Device downtime) / (Total T = 99.99 % Nil
Time)- planned downtime]}
99.98% > T > 99.8
Total Time shall be measured on 24*7 basis 4
%
Target: 99.99% availability for all the devices
99.79%> T > 99.5 % 3
*Downtime required for maintenance, new
initiatives undertaken by BIDDER or for
99.49% > T > 99.0
performance enhancement measures shall be 2
%
done after deciding in advance by BIDDER &
3 Uptime client.
*Downtime shall be measured from the time
the application becomes unavailable (due to
any reasons whatsoever attributable to the
BIDDER) for Business processing either to the
T < 98.0 % 1
end user or external client for batch job
processing to the time it becomes fully
available for the above stated business
processes.
Note: Availability shall be measured on each
Andhra Pradesh Technology Services Page 78 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Severity
# SLA Parameter Definition Target
Level
device. Final penalty to be levied will be the
average of the individual penalties for each
device
Frequency of measurement: Monthly
T = 100 % Nil
% of devices for which backups are taken
based on the agreed backup policy. 100% > T >= 95 % 4
4 Backup
Target: 100%
95%> T >= 90 % 3
Frequency of measurement: Monthly
90% > T 2
T = 100 % Nil
% of successful restorations on devices for
which backups are taken based on the agreed
100% > T >= 95 % 4
restoration policy.
5 Restoration
Target: 100% 95%> T >= 90 % 3
Frequency of measurement: Quarterly
90% > T 2
T = 100 % Nil
% of devices for which configuration review
and fine tuning completed as per agreed
Configuration 100% > T >= 95 % 4
process.
6 review and
performance tuning Target: 100% 95%> T >= 90 % 3
Frequency of measurement: Quarterly
90% > T 2
% of instance for which user access T = 100 % Nil
management compliance has not met as per
agreed process. 100% > T >= 95 % 4
6 Access Management Instance includes creation of user id,
modification, deletion without approval. 95%> T >= 90 % 3
Target: 100%
90% > T 2
Frequency of measurement: Quarterly
T <=5 days Nil
For all P1 & P2 incidents resolved during the 7 days >=T >5 days 4
quarter, BIDDER to submit RCA reports.
Submission of root
10 days >=T >7 days 3
7 cause analysis Target: 5 working days post incident
(RCA) resolution
12 days >=T >10
2
Frequency of measurement: Monthly days
T >12 days 1
Security Inventory BIDDER must maintain & update the T = Once a week Nil
8
/License/OEM configuration management database (CMDB)
Andhra Pradesh Technology Services Page 79 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
Severity
# SLA Parameter Definition Target
Level
support as per the defined deadlines:
Management
Deviation 4
Target: Once a week
Andhra Pradesh Technology Services Page 80 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
15.4.3. Threat Surface Management Services
SLA Parameter Definition Target Severity Level
#
Vulnerability Vulnerability assessment and Penetration 100% Nil
1. Assessment / Web testing to be carried out as per the agreed
application security timelines.
assessment / Mobile <100% 3
Frequency of measurement: Monthly
application
Quality of the Missing of the critical / high risk finding as 100% Nil
2. assessment part the assessment.
<100% 3
APTS might get the assessment performed
by the third party to identify the missing
gaps. <95% 2
15.4.4. Brand Monitoring and Protection Services
Severity
Target
SLA Parameter Definition Level
#
Inform the client on any security events, <=2 hour Nil
presence of virus/worms/malicious code,
unauthorized activity / access, source of >2 hours 4
breach, vulnerability
Malicious Activity
1. <=2 hour Nil
Report the MMC attack / Iframe and other such
attempts on client websites >2 hour 4
1. 24X7X365 monitoring <= 60 min Nil
2. The phishing alert should be raised for a
phishing email in circulation within 60 >60 min 4
minutes.
Anti-phishing
Benchmarking reports and advisories
2. Services
suggesting controls required to minimize
Delay 3
impact from phishing attacks should be
submitted within first week of subsequent
month
<= 15 mins Nil
1. 24X7X365 monitoring
2. Alert within 15 minutes for code injection
attempts and attacks Alert >15 mins 4
Anti-Malware and <= 30 mins Nil
Initial remedial response within 30 minutes
Anti Trojan with action plan on locking/
3. scanning Services >30 mins 4
containment/recovery
<= 60 mins Nil
Resolution within 60 minutes
>60 mins 4
Andhra Pradesh Technology Services Page 81 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
15.4.5. Others SLA
Target Severity Level
SLA Parameter Definition
#
1 Nil
SOPs, Reports for incident Delay >1 day
management, change management &
1
problem management, Escalation 1 Day >T > 7 days
MIS reports and matrix specific to AP-SOC
dashboard infrastructure to be shared as per the 8 Days > T > 14
frequency agreed. 2
days
Frequency of measurement: Monthly
2 ISO Compliance delay > 1 month 4
AP-SOC to be compliant as per ISO
27001, 9001 standards within 9
months from start of AP-SOC delay > 3 month 3
operations
delay > 1 month 4
Annual Audit of ISO compliance to
be conducted for AP-SOC.
delay > 3 month 3
3
% of devices & services restored from T = 100 % Nil
the DR site with no data loss.
Target: 100% on time as per BCP
DR Drill
DR policy 100% > T >= 95 % 3
Frequency of measurement :
Quarterly
4
Complete restoration of all devices & T = 30 Min Nil
services from the DR site with no
30 Min < T < 40
data loss. 3
Adherence to Min
RTO This is applicable for both production
environment and during DR Drills 40 Min T < 50 Min 2
Target RTO: <=30 Minutes Min < T < 60 Min 1
5
T = 0 Minutes Nil
Complete restoration of all devices &
services from the DR site with no 0 Min < T < 10 Min 3
data loss.
Adherence to
10 Min < T < 25
RPO This is applicable for both production 2
Min
environment and during DR Drills
Target: 0 Minutes 25 Min < T < 40
1
Min
Andhra Pradesh Technology Services Page 82 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
16. Payment and Invoicing Process
16.1. Payment Process
In consideration of the Services and subject to the provisions of this Agreement and of the SLA, the
Contracting Authority shall pay the AP- SOC Service Provider for the Services rendered in pursuance of this
agreement.
The Contracting Authority shall release the payment to Service Provider only if the Service Provider is able to
achieve the Service Levels as specified in Service Level Agreement.
16.1.1. Payment Milestones for BOM as specified in the RFP
S.No Item Payment Milestone
1 Video Wall 12*2
2 video wall - 2*2
3 Ultra stretch display 70% upon
4 48" Professional Large Format LED with DTH Installation,
5 21 inches i7 based All In One Desktops configuration and
6 UPS as per the requirement with common battery bank acceptance and 30%
7 Network Cabling upon Go-Live of the
8 Leased line/MPLS connectivity of 2 MBPS within AP AP-SOC
9 LCD Projectors
10 Access Controls
11 Ip based Video Surveillance
12 Network based Duplex Multi- Function Printer
16.1.2. Payment Milestones for the Services to be delivered as per the scope of the
RFP
S.No Client (Who takes SOC AP- SOC Service APTS (Nodal Agency) Payment Timelines
service) Provider
Buy the service and pay
1. Provide Services to
AP Govt. Departments to AP- SOC service Quarterly
departments
provider
Buy the service and pay
2. SME-1 (Funding by the Provide Services to
to AP- SOC service Quarterly
govt.) SME
provider
3. Provide Services to
Other States/Govt. Not Applicable Not Applicable
other states
1. In case of servicing clients other than AP govt. departments /SME-1, bidder is entitled to share 10% of the
revenue share per service
2. All payments are subject to the application of liquidated damages and penalties defined and provided for in
this Agreement and the SLA.
Andhra Pradesh Technology Services Page 83 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
16.2. Volume discounts
The following is the discount patterns to be adhered by the bidders on the minimum assured quantities of the
Bid during the contract period.
Sr
Services Unit Range Range Range
No
1Monitoring EPS 5000-10000 10,001-20,000 20,000+
2Device Management Devices 25-50 51-100 100+
3Threat Surface Management IP 500-1000 1001-2500 2500+
4Brand Monitoring Website 50-100 101-250 250+
5Discount to be computed 10% 15% 20%
16.3. Invoicing & Settlement Process
The service charges for the Services the SOC Service Provider shall be eligible to receive payments in
accordance with payment schedule subject to the completeness of the Invoice and specific terms of each
Service Level Agreement, the Service Provider submit its invoices in accordance with the following
principles
1. APTS shall raise invoice to the departments and AP –SOC service provider will get the payment from
APTS
2. Generally and unless otherwise agreed in writing between the Parties or expressly set out in the Service
Level Agreement, the AP SOC Service Provider shall raise an invoice as per the terms of payment as
stated in this Schedule.
3. Any invoice presented in accordance with this Article shall be in a form agreed with APTS.
4. The completeness of the Invoice shall mean the submission of the Invoice along with the acceptance
certificate of the respective deliverables of the milestones and other associated dependencies to process
and approve the invoice.
5. Invoice should have the taxes at actuals at the prevailing rates at the time of submission of invoice.
6. Invoices shall be accurate and all adjustments to or changes in the terms of payment as stated in the
Terms of Payment Schedule shall be applied to the next payment invoice. The Service Provider shall
waive any charge for a Service that is not invoiced within six months after the end of the month in
which the terms of payment as stated in the Terms of Payment Schedule relating to such Service are
authorized or incurred, whichever is later.
7. Payments to AP-SOC service provider shall be made within one week of the receipt of payment by the
department, subject to adjustments if any for the previous performance.
8. The Contracting Authority (APTS) shall be entitled to delay or withhold payment of any invoice or part
of it delivered by the AP-SOC Service Provider under this Schedule where the Contracting Authority
disputes such invoice or part of it provided that such dispute is bona fide. The withheld amount shall be
limited to that which is in dispute. The disputed amount shall be settled in accordance with the
escalation procedure as set out in the Governance Schedule (Schedule IV of this Agreement). Any
exercise by the Contracting Authority (APTS) under this Article shall not entitle the AP-SOC Service
Provider to delay or withhold provision of the Services.
Andhra Pradesh Technology Services Page 84 of 85
RFP for Implementation and Management of AP-SOC in the state of Andhra Pradesh
9. The Service Provider shall pay all their sub-contractors in a timely fashion in accordance with a
mechanism, which will not prejudice the objective of the Project.
10. If any amount is due and payable by the Service Provider to the Contracting Authority (APTS) or Its
Nominated Agencies, the same shall be either adjusted by the Service Provider in the subsequent
Invoices or Paid to the Contracting Authority in a method as informed by the Contracting Authority or
its Nominated Agencies on a case to case basis.
11. APTS shall be responsible for withholding taxes from the amounts due and payable to the Service
Provider wherever applicable.
12. The Service Provider shall pay for all other taxes in connection with this Agreement, and SLA
including, but not limited to, property, sales, use, excise duty, value-added, goods and services,
consumption and other similar taxes (GST) or duties.
13. In the event of any increase or decrease of the rate of taxes due to any statutory notification/s or new
enactments during the Term of the Agreement the consequential effect shall be to the account of the
Contracting Authority. Taxes should be invoiced at actuals at the prevailing rates at the time of
submission of invoice.
14. In the event that any new laws or regulations imposing Taxes in respect of Supplier supplies/services
under this Agreement are enacted after the Effective Date, the party directly subject to such Taxes
under such laws or regulations shall be responsible for such Taxes. Where such Taxes are the
responsibility of supplier and supplier is entitled to charge them to contracting authority, contracting
authority shall pay/ Adjust as the case may be, these Taxes in addition/deduction of taxes to the
consideration payable under this Agreement.
Andhra Pradesh Technology Services Page 85 of 85
Вам также может понравиться
- Information Security Architect A Complete Guide - 2020 EditionОт EverandInformation Security Architect A Complete Guide - 2020 EditionОценок пока нет
- Designing Modern SOC - ChuvakinДокумент34 страницыDesigning Modern SOC - ChuvakinDigit OktaviantoОценок пока нет
- Building A Security Operations Center: Randy Marchany VA Tech IT Security Office and Lab Marchany@vt - EduДокумент28 страницBuilding A Security Operations Center: Randy Marchany VA Tech IT Security Office and Lab Marchany@vt - EduAhmad Alafeef0% (1)
- SOC, SecOps and SIEM - How They Work TogetherДокумент19 страницSOC, SecOps and SIEM - How They Work TogetherSamir Pathak100% (1)
- Successfull SOCДокумент10 страницSuccessfull SOCozi ridhoОценок пока нет
- Cism Exam GuideДокумент364 страницыCism Exam GuideNyengeterai Mafarachisi100% (1)
- NESA Compliance Service - Paladion Networks - UAEДокумент8 страницNESA Compliance Service - Paladion Networks - UAEPRASHANTH B SОценок пока нет
- How To Write An MSSP RFPДокумент14 страницHow To Write An MSSP RFPAdedapo AdewoleОценок пока нет
- Tenable Csis Compliance WhitepaperДокумент22 страницыTenable Csis Compliance Whitepapernaushad73Оценок пока нет
- Data Loss Prevention Pilot GuideДокумент93 страницыData Loss Prevention Pilot GuideHarold GardnerОценок пока нет
- A Framerwork of SOCДокумент11 страницA Framerwork of SOCrizaayhan0% (1)
- Mobile Application & Cloud VA - PT Proposal - CashifyДокумент4 страницыMobile Application & Cloud VA - PT Proposal - CashifyApoorva AroraОценок пока нет
- Pci Evidence Reference v1Документ192 страницыPci Evidence Reference v1mani karthikОценок пока нет
- Security Information and Event ManagementДокумент39 страницSecurity Information and Event ManagementeddieОценок пока нет
- Inspira's: Managed SOC ServicesДокумент3 страницыInspira's: Managed SOC ServicesmahimaОценок пока нет
- Cybrary CISMДокумент98 страницCybrary CISMFelix RiveraОценок пока нет
- SIEM Pro ConsДокумент58 страницSIEM Pro Conssagar gautam0% (1)
- PCI ChecklistДокумент3 страницыPCI Checklistfuckaccount1Оценок пока нет
- ISO27001 ComplianceДокумент6 страницISO27001 ComplianceEdgar SerratoОценок пока нет
- Security Operations Maturity Model White PaperДокумент31 страницаSecurity Operations Maturity Model White PaperFlávio RibeiroОценок пока нет
- FC FC FC: MC MC MC PC PC PC SC SC SCДокумент2 страницыFC FC FC: MC MC MC PC PC PC SC SC SCDB2Оценок пока нет
- SANS Top 20 Critical Controls ReportДокумент107 страницSANS Top 20 Critical Controls ReportCater AidОценок пока нет
- Sample Penetration Testing Report TemplateДокумент37 страницSample Penetration Testing Report TemplateMarcos GomezОценок пока нет
- Cyber Health Check Sample ReportДокумент19 страницCyber Health Check Sample ReportHassan AminОценок пока нет
- VAPT ProposalДокумент10 страницVAPT ProposalGaurav saboo100% (2)
- SOC 2 - SOC 2 ComplianceДокумент6 страницSOC 2 - SOC 2 CompliancehimalyasharmaОценок пока нет
- Security - Domain - RoadmapДокумент32 страницыSecurity - Domain - RoadmapVijay SrinivasanОценок пока нет
- Investing in CybersecurityДокумент78 страницInvesting in CybersecurityKriminologinjaОценок пока нет
- The Definitive Guide To Managed Detection and Response (MDR)Документ56 страницThe Definitive Guide To Managed Detection and Response (MDR)Alfredo Alejandro Márquez100% (1)
- Astra Security Sample VAPT ReportДокумент28 страницAstra Security Sample VAPT Reporthanuman1999Оценок пока нет
- IAM Baseline QA Report FINALДокумент13 страницIAM Baseline QA Report FINALvinkrishОценок пока нет
- SANS CISO Scorecard v1.2Документ1 страницаSANS CISO Scorecard v1.2Shun KamОценок пока нет
- SOC WorkshopДокумент64 страницыSOC WorkshopnagarjunaОценок пока нет
- Aqua Security 2021 - SOC 2 Type II - Auditor SummaryДокумент7 страницAqua Security 2021 - SOC 2 Type II - Auditor Summaryonge pa caxaОценок пока нет
- Best Practices - For - IAM - Solution - ImplementationДокумент6 страницBest Practices - For - IAM - Solution - Implementationsantuchetu1Оценок пока нет
- Cyber Risk Management FrameworkДокумент9 страницCyber Risk Management Frameworkleo58800% (1)
- Incident Response NotesДокумент45 страницIncident Response NotesneilhookОценок пока нет
- Future of MSSP-An OverviewДокумент19 страницFuture of MSSP-An OverviewattillathehunОценок пока нет
- Designing SOCДокумент52 страницыDesigning SOCMohammed Muneer100% (7)
- Security ArchitectureДокумент6 страницSecurity ArchitecturestudydatadownloadОценок пока нет
- Cyber Security Framework V1.01Документ42 страницыCyber Security Framework V1.01santanujoshiОценок пока нет
- Azure Commercial - Pen Test Report 2018 PDFДокумент78 страницAzure Commercial - Pen Test Report 2018 PDFjunk emailОценок пока нет
- Bulding A SOCДокумент41 страницаBulding A SOCIgnacio Cortez100% (1)
- EY Security Operations Centers Helping You Get Ahead of CybercrimeДокумент20 страницEY Security Operations Centers Helping You Get Ahead of Cybercrimeashish100% (1)
- VCISO Implementation RoadmapДокумент2 страницыVCISO Implementation RoadmapAОценок пока нет
- Cloud Security Policy TemplateДокумент16 страницCloud Security Policy TemplateSurnaz SinghОценок пока нет
- 4 SOC ConsultingДокумент54 страницы4 SOC Consultingriadelidrissi100% (3)
- Service VAPT PresentationДокумент14 страницService VAPT PresentationVinay wrksОценок пока нет
- Building A Successful Cloud Infrastructure Security & Compliance PracticeДокумент17 страницBuilding A Successful Cloud Infrastructure Security & Compliance Practicejose cardozoОценок пока нет
- Gartner Critical Capabilities For SIEMДокумент32 страницыGartner Critical Capabilities For SIEMalexioОценок пока нет
- CIS RAM v2.1 Core Document Online.22.01Документ27 страницCIS RAM v2.1 Core Document Online.22.01Raman GautaОценок пока нет
- Issap MindmapДокумент1 страницаIssap MindmapdeewanandОценок пока нет
- Security Threat and AWS Modeling Project LectureДокумент11 страницSecurity Threat and AWS Modeling Project LectureNopeОценок пока нет
- Rsa Sans Roadmap To Creating A World Class SocДокумент1 страницаRsa Sans Roadmap To Creating A World Class SocRoot100% (1)
- 3rd Party Outsourcing Information Security Assessment Questionnaire V1.4Документ15 страниц3rd Party Outsourcing Information Security Assessment Questionnaire V1.4Adil Raza SiddiquiОценок пока нет
- NYDFS Assessment ToolkitДокумент236 страницNYDFS Assessment ToolkitApoorva Badola33% (3)
- Information Security Management at HDFC Bank Contribution of Seven Enablers 1113Документ8 страницInformation Security Management at HDFC Bank Contribution of Seven Enablers 1113Đaŋush Ralston FoxОценок пока нет
- Anish BhagoriaДокумент5 страницAnish BhagoriaSourabh SharmaОценок пока нет
- SAMA Cyber Security Framework 1.0Документ56 страницSAMA Cyber Security Framework 1.0iawanОценок пока нет
- CISM Model QuestionsДокумент12 страницCISM Model QuestionsKumar0% (1)
- GeM Bidding 3702776Документ4 страницыGeM Bidding 3702776Sanmati RandiveОценок пока нет
- Telangana Data Centres PolicyДокумент28 страницTelangana Data Centres PolicyNaveen Lawrence100% (1)
- Women DevelopmentДокумент15 страницWomen DevelopmentSukanya RayОценок пока нет
- GeM Bidding 3641733Документ11 страницGeM Bidding 3641733Krishna CooldudeОценок пока нет
- Economic Survey Volume I Complete PDFДокумент226 страницEconomic Survey Volume I Complete PDFBaldev ChoyalОценок пока нет
- Kotak Wealth Hurun Leading Women Summit 2018 PDFДокумент22 страницыKotak Wealth Hurun Leading Women Summit 2018 PDFKrishna CooldudeОценок пока нет
- Abenomics: For Future Growth, For Future Generations, and For A Future Japan That Is RobustДокумент12 страницAbenomics: For Future Growth, For Future Generations, and For A Future Japan That Is RobustKrishna CooldudeОценок пока нет
- Michael Lewis-Liar's Poker - Rising Through The Wreckage On Wall Street-Penguin Books (1990)Документ20 страницMichael Lewis-Liar's Poker - Rising Through The Wreckage On Wall Street-Penguin Books (1990)Krishna CooldudeОценок пока нет
- Abenomics: For Future Growth, For Future Generations, and For A Future Japan That Is RobustДокумент12 страницAbenomics: For Future Growth, For Future Generations, and For A Future Japan That Is RobustKrishna CooldudeОценок пока нет
- Dena Bank SOC 1528967704150-ten-RFP-SOC-14-06-2018 PDFДокумент104 страницыDena Bank SOC 1528967704150-ten-RFP-SOC-14-06-2018 PDFKrishna CooldudeОценок пока нет
- Case Interviews CrackedДокумент208 страницCase Interviews CrackedSaurabhYadav100% (11)
- Special Calendercalender FBДокумент2 страницыSpecial Calendercalender FBKrishna CooldudeОценок пока нет
- Aqua Regia Science Quiz 2009 Prelims1Документ7 страницAqua Regia Science Quiz 2009 Prelims1Krishna CooldudeОценок пока нет
- Limca Book of World Record Quiz - VizagДокумент12 страницLimca Book of World Record Quiz - VizagKrishna Cooldude100% (1)
- Famous FiveДокумент2 страницыFamous FiveKrishna CooldudeОценок пока нет
- Advanced Signal Multi-ScannerДокумент8 страницAdvanced Signal Multi-ScannerneerajupmanyuОценок пока нет
- Guide Specification - SDP 200: GeneralДокумент10 страницGuide Specification - SDP 200: GeneralhbookОценок пока нет
- No Man Is An Island - Friendship LoyaltyДокумент4 страницыNo Man Is An Island - Friendship LoyaltyBryanОценок пока нет
- Mini Test PBD - SpeakingДокумент4 страницыMini Test PBD - Speakinghe shaОценок пока нет
- Chapter 4Документ21 страницаChapter 4Ahmad KhooryОценок пока нет
- Sample PREP-31 Standard Sample Preparation Package For Rock and Drill SamplesДокумент1 страницаSample PREP-31 Standard Sample Preparation Package For Rock and Drill SampleshОценок пока нет
- BDS PDFДокумент5 страницBDS PDFRobinsonRuedaCandelariaОценок пока нет
- Secured Steganography To Send Seceret Message: Project ID: 1029Документ33 страницыSecured Steganography To Send Seceret Message: Project ID: 1029Pravat SatpathyОценок пока нет
- Appendix F Sample Erosion and Sediment Control PlanДокумент11 страницAppendix F Sample Erosion and Sediment Control Planjhj01Оценок пока нет
- Sequential StatementДокумент12 страницSequential Statementdineshvhaval100% (1)
- Scheme of Work Writing Baby First TermДокумент12 страницScheme of Work Writing Baby First TermEmmy Senior Lucky100% (1)
- The Advanced Formula For Total Success - Google Search PDFДокумент2 страницыThe Advanced Formula For Total Success - Google Search PDFsesabcdОценок пока нет
- Fun33 LCNVДокумент6 страницFun33 LCNVnehalОценок пока нет
- Jump in A Teachers BookДокумент129 страницJump in A Teachers BookShei QuinterosОценок пока нет
- Ebook PDF Elementary Algebra 4th Edition by Michael III SullivanДокумент41 страницаEbook PDF Elementary Algebra 4th Edition by Michael III Sullivansean.cunningham518Оценок пока нет
- Decision Making Techniques: How To Make Good DecisionsДокумент10 страницDecision Making Techniques: How To Make Good DecisionsParanthaman RamanОценок пока нет
- 2 The Impact of Corporate Social Responsibility On Firms Financial PerformanceДокумент20 страниц2 The Impact of Corporate Social Responsibility On Firms Financial PerformanceFam KhanОценок пока нет
- Filmmaking 101Документ4 страницыFilmmaking 101maheshОценок пока нет
- Yaskawa Product CatalogДокумент417 страницYaskawa Product CatalogSeby Andrei100% (1)
- The Entrepreneurial Spirit From Schumpeter To Steve Jobs - by Joseph BelbrunoДокумент6 страницThe Entrepreneurial Spirit From Schumpeter To Steve Jobs - by Joseph Belbrunoschopniewit100% (1)
- 111Документ16 страниц111Squall1979Оценок пока нет
- Alpha-Qwerty Cipher: An Extended Vigenere CipherДокумент12 страницAlpha-Qwerty Cipher: An Extended Vigenere CipherAnonymous IlrQK9HuОценок пока нет
- Module 2 - Math PPT PresentationДокумент28 страницModule 2 - Math PPT PresentationjhonafeОценок пока нет
- GPS Equipment CalibrationДокумент10 страницGPS Equipment CalibrationAishah Drahman100% (1)
- Class 10 Mid Term Syllabus 202324Документ4 страницыClass 10 Mid Term Syllabus 202324Riya AggarwalОценок пока нет
- Sales Presentation of K&N ChickenДокумент25 страницSales Presentation of K&N ChickensanahansmukhОценок пока нет
- Fourier Transform Infrared Quantitative Analysis of Sugars and Lignin in Pretreated Softwood Solid ResiduesДокумент12 страницFourier Transform Infrared Quantitative Analysis of Sugars and Lignin in Pretreated Softwood Solid ResiduesDaisyOctavianiОценок пока нет
- Comparative Analysis of Oyo & Ginger Grp-9 PDFДокумент31 страницаComparative Analysis of Oyo & Ginger Grp-9 PDFadityakr2410100% (1)
- Professional Scrum Master I Simulator Test 1 PDFДокумент8 страницProfessional Scrum Master I Simulator Test 1 PDFRahul GandhiОценок пока нет