Академический Документы
Профессиональный Документы
Культура Документы
NS - 07 Legal - Ethics PDF
Загружено:
Gilang Raka Prima Febrianto0 оценок0% нашли этот документ полезным (0 голосов)
18 просмотров24 страницыОригинальное название
NS - 07 Legal _ Ethics.pdf
Авторское право
© © All Rights Reserved
Доступные форматы
PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
18 просмотров24 страницыNS - 07 Legal - Ethics PDF
Загружено:
Gilang Raka Prima FebriantoАвторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 24
NETWORK SECURITY
Ch. 7: Legal & Ethics
Term Hacker
• Most people think hackers have extraordinary skill and
knowledge that allow them to hack into computer
systems and find valuable information
• How your thought?
In reality
• a good hacker, or security professional acting as an
ethical hacker, just has to understand how a computer
system works and know what tools to employ in order to
find a security weakness
• Hackers use specialized computer software tools to gain
access to information
Ethical hacker act?
• Most ethical hackers are in the business of hacking for
profit, an activity known as penetration testing, or pen
testing for short
• Conduct themselves in a professional manner.
• Staying within the law is a must for the ethical hacker
Defining
• Gaining the trust of the client and taking all precautions
to do no harm to their systems during a pen test are
critical to being a professional
• gain permission from the data owner prior to accessing
the computer system
Purpose
• Can hacking be ethical?
• Ethical hackers are usually security professionals or
network penetration testers who use their hacking skills
and toolsets for defensive and protective purposes
Malicious hacker
• The term cracker describes a hacker who uses their
hacking skills and toolset for destructive or offensive
purposes such as disseminating viruses or performing
denial-of-service (DoS) attacks to compromise or bring
down systems and networks
• Note :
– White hacker
– Black Hacker
– Gray Hacker
Goals Attackers Try to Achieve
• All attacks are an attempt to breach computer system
security.
– Confidentiality
– Authenticity
– Integrity
– Availability
Security, Functionality,
and Ease of Use Triangle
How to Be Ethical
• An ethical hacker must do the following:
– Gain authorization from the client and have a signed contract
giving the tester permission to perform the test.
– Maintain and follow a nondisclosure agreement (NDA) with the
client in the case of confidential information disclosed during
the test.
– Maintain confidentiality when performing the test. Information
gathered may contain sensitive information. No information
about the test or company confidential data should ever be
disclosed to a third party.
– Perform the test up to but not beyond the agreed-upon limits
Ex: Security audit steps
Keeping It Legal
• An ethical hacker should know the penalties of
unauthorized hacking into a system.
• security audit should begin until a signed legal document
giving the ethical hacker express permission to perform
the hacking activities is received from the target
organization.
• to be judicious with their hacking skills and recognize the
consequences of misusing those skills.
Cyber Security Enhancement Act
and SPY ACT
• The Securely Protect Yourself Against Cyber Trespass
Act of 2007 (SPY ACT) deals with the use of spyware on
computer systems and essentially prohibits the following:
– Taking remote control of a computer when you have not been
authorized to do so
– Using a computer to send unsolicited information to people
(commonly known as spamming)
– Redirecting a web browser to another site that is not
authorized by the user
Cyber Security Enhancement Act
and SPY ACT (Cont.)
– Displaying advertisements that cause the user to have to close
out of the web browser (pop-up windows)
– Collecting personal information using keystroke logging
– Changing the default web page of the browser
– Misleading users so they click on a web page link or
duplicating a similar web page to mislead a user
18 USC §1029 and 1030
• The U.S. Code categorizes and defines the laws of the
United States by titles
– Title 18 details “Crimes and Criminal Procedure.”
– Section 1029, “Fraud and related activity in connection with
access devices,”
– Section 1030, “Fraud and related activity in connection with
computers,”
U.S. State Laws
• Many states have their own laws associated with hacking
and auditing computer networks and systems.
• The National Security Institute has a website listing all
the state laws applicable to com- puter crimes
– http://nsi.org/Library/Compsec/computerlaw/statelaws.html
Federal Managers Financial
Integrity Act
• Responsibility act to ensure that those managing
financial accounts are doing so with the utmost
responsibility and are ensuring the protection of the
assets
• The act essentially ensures that
– Funds, property, and other assets are safeguarded against
waste, loss, unauthorized use, or misappropriation.
– Costs are in compliance with applicable laws.
Freedom of Information Act
(FOIA)
• makes many pieces of information and documents about
organizations public.
• Most records and government documents can be
obtained via the FoIA
Federal Information Security
Management Act (FISMA)
• Basically gives ethical hackers the power to do the types
of testing they perform and makes it a mandatory
requirement for government agencies.
Privacy Act of 1974
• Ensures nondisclosure of personal information and
ensures that government agencies are not disclosing
information without the prior written consent of the
person whose information is in question.
USA PATRIOT Act
• Gives the government the authority to intercept voice
communications in computer hacking and other types of
investigations.
Government Paperwork
Elimination Act (GPEA)
• Requires federal agencies to allow people the option of
using electronic communications when interacting with a
government agency.
• GPEA also encourages the use of electronic signatures.
Cyber Law in Indonesia
• Other countries each have their own applicable laws
regarding protection of information and hacking attacks
– UU-ITE-11-2008
– UU14th2008 KIP
– RUU Rahasia Negara
– 19-02 UU Hak Cipta
– PP-60 TAHUN 2008-SISTEM PENGENDALIAN INTERNAL
PEMERINTAH
– SNI 7512 2008 Pengelolaan Insiden Keamanan Informasi
UU ITE
• BAB VII PERBUATAN YANG DILARANG
– Pasal 27, …. Pasal 39
• Pidana
– Jail up to 10 years
– Denda 12 Million
Вам также может понравиться
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (894)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Ungrounded SystemДокумент13 страницUngrounded SystemSaurabh Kumar SinghОценок пока нет
- Sample ISMS Metrics and MeasuresДокумент3 страницыSample ISMS Metrics and MeasuresJohn Manni100% (1)
- CCNA Security LabДокумент39 страницCCNA Security LabSagar JamdadeОценок пока нет
- Vivares Vs Sta Theresa College DigestДокумент1 страницаVivares Vs Sta Theresa College DigestCJОценок пока нет
- Cvss Based Patch PolicyДокумент4 страницыCvss Based Patch PolicyJamie RandolphОценок пока нет
- The Effectiveness of Data Processors in Correlation To GDPRДокумент12 страницThe Effectiveness of Data Processors in Correlation To GDPROliver SmithОценок пока нет
- Cyber Kill Chain Wrozek PDFДокумент30 страницCyber Kill Chain Wrozek PDFCarolina MorenoОценок пока нет
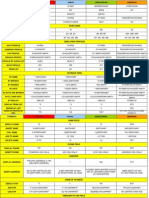
- GDS All in One Conversion SheetДокумент10 страницGDS All in One Conversion SheetAnca Dragan90% (10)
- Network Security Guide: Network Attacks and CategoriesДокумент66 страницNetwork Security Guide: Network Attacks and CategoriesGilang Raka Prima FebriantoОценок пока нет
- Information Technology PolicyДокумент9 страницInformation Technology PolicyfanoustОценок пока нет
- UD25290B - Baseline - Network-Video-Recorder - User-Manual - V4.70.000 - 20210917Документ98 страницUD25290B - Baseline - Network-Video-Recorder - User-Manual - V4.70.000 - 20210917Gilang Raka Prima FebriantoОценок пока нет
- PT. Falcon Prima Tehnik: Permintaan Pengadaan BarangДокумент7 страницPT. Falcon Prima Tehnik: Permintaan Pengadaan BarangGilang Raka Prima FebriantoОценок пока нет
- NS - 06 Applying Cryptography PDFДокумент45 страницNS - 06 Applying Cryptography PDFGilang Raka Prima FebriantoОценок пока нет
- NS - 04 Information Assurance PDFДокумент39 страницNS - 04 Information Assurance PDFGilang Raka Prima FebriantoОценок пока нет
- Floboss S600+ Flow Computer: S600+ Product Data SheetДокумент11 страницFloboss S600+ Flow Computer: S600+ Product Data SheetGilang Raka Prima FebriantoОценок пока нет
- NS - 02 VulnerabilitiesДокумент30 страницNS - 02 VulnerabilitiesYunar PribadiОценок пока нет
- Floboss S600+ Flow Computer Instruction Manual: Part Number D301150X412Документ126 страницFloboss S600+ Flow Computer Instruction Manual: Part Number D301150X412Gilang Raka Prima FebriantoОценок пока нет
- 1Документ3 страницы1Gilang Raka Prima FebriantoОценок пока нет
- Crypto PDFДокумент64 страницыCrypto PDFDanuNarendroОценок пока нет
- NS - 01 IntroductionДокумент32 страницыNS - 01 IntroductionGilang Raka Prima FebriantoОценок пока нет
- PressureДокумент12 страницPressureAndi R. NuryadinОценок пока нет
- An Introduction To Differential-Pressure Flow MetersДокумент22 страницыAn Introduction To Differential-Pressure Flow MetersisukuruОценок пока нет
- Xbee /Xbee-Pro RF Modules: Product Manual V1.Xex - 802.15.4 ProtocolДокумент69 страницXbee /Xbee-Pro RF Modules: Product Manual V1.Xex - 802.15.4 ProtocolMounesh PanchalОценок пока нет
- An Introduction To Differential-Pressure Flow MetersДокумент22 страницыAn Introduction To Differential-Pressure Flow MetersisukuruОценок пока нет
- Xbee /Xbee-Pro RF Modules: Product Manual V1.Xex - 802.15.4 ProtocolДокумент69 страницXbee /Xbee-Pro RF Modules: Product Manual V1.Xex - 802.15.4 ProtocolMounesh PanchalОценок пока нет
- Xbee /Xbee-Pro RF Modules: Product Manual V1.Xex - 802.15.4 ProtocolДокумент69 страницXbee /Xbee-Pro RF Modules: Product Manual V1.Xex - 802.15.4 ProtocolMounesh PanchalОценок пока нет
- Datasheet PDFДокумент12 страницDatasheet PDFRey TiburonОценок пока нет
- 200 IT Security Job Interview QuestionsДокумент6 страниц200 IT Security Job Interview QuestionsRizwan KhanОценок пока нет
- JPIA Membership Data Privacy Consent FormДокумент2 страницыJPIA Membership Data Privacy Consent FormShena RicamaraОценок пока нет
- MalwareДокумент16 страницMalwareVaiBhav AroraОценок пока нет
- (IJCST-V5I2P61) :irene Getzi SДокумент5 страниц(IJCST-V5I2P61) :irene Getzi SEighthSenseGroupОценок пока нет
- ECSAv10 BrochureДокумент14 страницECSAv10 BrochureJodieОценок пока нет
- Wa0003Документ163 страницыWa0003savan anvekarОценок пока нет
- Understanding Public Key CryptographyДокумент9 страницUnderstanding Public Key CryptographyjeremyОценок пока нет
- OpenSSL ChangeCipherSpecДокумент23 страницыOpenSSL ChangeCipherSpecdanayaОценок пока нет
- Prep4sure: ReviewДокумент6 страницPrep4sure: Reviewpeterfarouk01Оценок пока нет
- 8 2 5 IPSec-ISAKMPДокумент26 страниц8 2 5 IPSec-ISAKMPSaptarshi BhattacharjeeОценок пока нет
- Applying Ifrs Standards 4th Edition Picker Test BankДокумент25 страницApplying Ifrs Standards 4th Edition Picker Test BankDeniseRamseyonzr100% (49)
- GPG - Encryption & SigningДокумент18 страницGPG - Encryption & Signingopenid_1FLLsijKОценок пока нет
- ISOC GIR 2016-v1Документ148 страницISOC GIR 2016-v1EduardoОценок пока нет
- Digital Certificates and X.509 Authentication ServiceДокумент20 страницDigital Certificates and X.509 Authentication ServiceRameshChОценок пока нет
- Digital SignatureДокумент25 страницDigital Signaturehardiks110yahoocomОценок пока нет
- HTTP WWW - Don23Документ13 страницHTTP WWW - Don23bondy18Оценок пока нет
- Top 10 Cybercrime Stories of 2018Документ75 страницTop 10 Cybercrime Stories of 2018Mine SweeperОценок пока нет
- Exam Study Guide: CisspДокумент93 страницыExam Study Guide: CisspAndres Perez100% (1)
- A Review On Improving Authentication Methods For IEEE 802.11 Wireless LANДокумент5 страницA Review On Improving Authentication Methods For IEEE 802.11 Wireless LANInternational Journal of Application or Innovation in Engineering & ManagementОценок пока нет
- Passwd CommandДокумент6 страницPasswd CommandDarkoОценок пока нет
- Truths!!! - What They Don't Teach in Manuals!!!Документ10 страницTruths!!! - What They Don't Teach in Manuals!!!paul_17oct@yahoo.co.in100% (1)
- TBC PentestДокумент9 страницTBC PentestJam Tangan BrandedОценок пока нет