Академический Документы
Профессиональный Документы
Культура Документы
L16B Basic Features PDF
Загружено:
Prabhakar SinghОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
L16B Basic Features PDF
Загружено:
Prabhakar SinghАвторское право:
Доступные форматы
Basic Feature Overview
4/006 51-LZA 701 6014 Uen K
Copyright
© Ericsson AB 2015-2016. All rights reserved. No part of this document may be
reproduced in any form without the written permission of the copyright owner.
Disclaimer
The contents of this document are subject to revision without notice due to
continued progress in methodology, design and manufacturing. Ericsson shall
have no liability for any error or damage of any kind resulting from the use
of this document.
Trademark List
All trademarks mentioned herein are the property of their respective owners.
These are shown in the document Trademark Information.
4/006 51-LZA 701 6014 Uen K | 2016-05-17
Contents
Contents
1 Basic Feature List 1
2 Feature Summary 5
2.1 16-QAM Uplink 5
2.2 64-QAM Downlink 5
2.3 Access Control Lists 5
2.4 Adjustable CRS Power 5
2.5 Admission Control 5
2.6 Autointegration of RBS 6
2.7 Basic Load Management 6
2.8 Battery Test 6
2.9 Bridged Virtual Interface 6
2.10 Cascadable Radio Units 7
2.11 Cascaded RET Support 7
2.12 Certificate Handling 7
2.13 Clock Source over NTP 7
2.14 CMPv2 8
2.15 Contention Free Random Access 8
2.16 CPRI Link Observability 8
2.17 Dual Band Support 8
2.18 Dynamic Cell Status 8
2.19 Emergency Call Prioritization 8
2.20 Enhanced Observability 9
2.21 eNodeB ID in X2 Traces 9
2.22 Ethernet Switching 9
2.23 Fallback from Time and Phase Synchronization 9
2.24 Firmware Download of Antenna Line Devices 10
2.25 Fractional Pathloss Power Control 10
2.26 ICIC - Autonomous Resource Allocation 10
2.27 Idle Mode Support 10
2.28 Intra-LTE Handover 10
2.29 IP Loopback Interface 10
2.30 Jumbo Frames 11
4/006 51-LZA 701 6014 Uen K | 2016-05-17
Basic Feature Overview
2.31 Maximum Cell Range 11
2.32 Multiple Digital Units 11
2.33 O&M Security 11
2.34 Paging 11
2.35 PDCCH Coverage Extension 12
2.36 Port Mirroring 12
2.37 Power Control 12
2.38 Radio Bearer Service 12
2.39 Random Access 12
2.40 RET Support 13
2.41 RRC Connection Re-establishment 13
2.42 Scheduler 13
2.43 Secure Execution Environment 13
2.44 Signed Software 13
2.45 Simplex and Duplex Radio Ports 13
2.46 Static Routing 14
2.47 Support for 15km CPRI Link 14
2.48 System Information Modification 14
2.49 TMA Support 14
2.50 VSWR Antenna Supervision 15
2.51 X2 Configuration 15
4/006 51-LZA 701 6014 Uen K | 2016-05-17
Basic Feature List
1 Basic Feature List
This document contains an overview of basic features, their related features,
and system requirements.
Table 1 lists the basic features in alphabetic order.
For a summary of each feature, see subsections in Section 2 on page 5. For a
detailed description, refer to the feature description.
If a feature is not listed or only listed for one of the node types in the Basic
Features table, see if the feature is listed in Licensed Feature Overview.
Table 1 Basic Features
Feature Name Feature CXC Numbe DU Base Condition
Identity r Radio band s
Node, Radio
First Node,
Releas First
e Release
16-QAM Uplink FAJ 121 0488 11A 15B
64-QAM Downlink FAJ 121 0487 11A 15B
Access Control Lists FAJ 121 0487 – 15B
FAJ 121 4376
Adjustable CRS Power FAJ 121 0487 10: 15B
FDD
FAJ 121 3049
12A:
TDD
Admission Control FAJ 121 1857 11B: 15B
FDD
12A:
TDD
Autointegration of RBS FAJ 121 0999 10: –
FDD
12A:
TDD
Basic Load Management FAJ 121 3092 14A 16A
Battery Test FAJ 121 1824 12B 15B
Bridged Virtual Interface FAJ 121 4414 – 15B
4/006 51-LZA 701 6014 Uen K | 2016-05-17 1
Basic Feature Overview
Table 1 Basic Features
Feature Name Feature CXC Numbe DU Base Condition
Identity r Radio band s
Node, Radio
First Node,
Releas First
e Release
Cascadable Radio Units FAJ 121 1820
Cascaded RET Support FAJ 121 0705 11A 15B
Certificate Handling FAJ 121 4417 – 15B
Clock Source over NTP FAJ 121 0496 – 16A
CMPv2 FAJ 121 4142 14B 15B
Contention Free Random FAJ 121 2055 – 16A
Access
CPRI Link Observability FAJ 121 3045 15B 16A
Dual Band Support FAJ 121 1822 – 15B
Dynamic Cell Status FAJ 121 1746 – 15B
Emergency Call FAJ 121 1039 16A 16A
Prioritization
Enhanced Observability FAJ 121 1044 – 15B
eNodeB ID in X2 Traces – 15B –
Ethernet Switching FAJ 121 4413 – 15B
Fallback from Time and FAJ 121 4374 15B –
Phase Synchronization
Firmware Download of FAJ 121 0925 – 15B
Antenna Line Devices
Fractional Pathloss Power FAJ 121 3033 14A
Control
ICIC - Autonomous FAJ 121 1074 – 15B
Resource Allocation
Idle Mode Support – – 15B
Intra-LTE Handover FAJ 121 0489 11A 15B
IP Loopback Interface FAJ 121 4411 – 15B
Jumbo Frames FAJ 121 1896 – 15B
Multiple Digital Units FAJ 121 3038 12B: –
FDD
O&M Security FAJ 121 4416 – 15B
Paging – – 15B
2 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Basic Feature List
Table 1 Basic Features
Feature Name Feature CXC Numbe DU Base Condition
Identity r Radio band s
Node, Radio
First Node,
Releas First
e Release
PDCCH Coverage FAJ 121 4629 16B 16B
Extension
Port Mirroring FAJ 121 4550 – 16A
Power Control – – 15B
Radio Bearer Service – – 15B
Random Access – – 15B
RET Support FAJ 121 2175 12A 15B
RRC Connection FAJ 121 3019 12B 15B
Re-establishment
Scheduler – – 15B
Secure Execution FAJ 121 4419 – 15B
Environment
Signed Software FAJ 121 4418 – 15B
Simplex and Duplex Radio FAJ 121 0879 11B: –
Ports FDD
Static Routing FAJ 121 4412 – 15B
Support for 15km CPRI FAJ 121 1100 11B: 15B
Link FDD
12A:
TDD
System Information FAJ 121 1042 11B: 15B
Modification FDD
12A:
TDD
TMA Support FAJ 121 0498 11A 15B
VSWR Antenna FAJ 121 0706 – 15B
Supervision
X2 Configuration – – 15B
4/006 51-LZA 701 6014 Uen K | 2016-05-17 3
Basic Feature Overview
4 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Feature Summary
2 Feature Summary
2.1 16-QAM Uplink
The maximum bitrate on the uplink may be increased to 16 QAM modulation.
For more information, see 16-QAM Uplink.
2.2 64-QAM Downlink
The maximum bitrate on the downlink may be increased to 64 QAM modulation.
For more information, see 64-QAM Downlink.
2.3 Access Control Lists
This feature provides configurable firewall protection of ingress and egress
traffic at external IPv4 interfaces.
The main purpose of introducing the Access Control Lists (ACL) feature is
to provide Layer 3 firewall functionality for ingress and egress traffic on IP
interfaces. The operator can use this functionality to prevent unwanted
and/or malicious traffic from entering the node, and to prevent traffic from
unintentionally exiting the node via an interface towards a foreign network
domain.
Fore more information, see Access Control Lists.
2.4 Adjustable CRS Power
Adjustable CRS power provides means to optimize the power distribution
on resource elements according to the network topology for improved DL
throughput, for example in dense networks, or extended coverage in rural
environments.
For more information, see Adjustable CRS Power.
2.5 Admission Control
The purpose of Admission Control is to accept or reject E-RABs in such a
way that the requested Quality of Service can be maintained for all admitted
E-RABs. Based on the requested Guaranteed Bit Rate (GBR) received over
4/006 51-LZA 701 6014 Uen K | 2016-05-17 5
Basic Feature Overview
S1 or X2 this feature controls the load for GBR traffic on the S1-U interface to
keep it below an operator configurable threshold.
For more information, see Admission Control.
2.6 Autointegration of RBS
Autointegration of RBS consists of functions in RBS and in Operations Support
System – Radio and Core (OSS-RC).
Autointegration of RBS reduces workload for preparations, on-site activities,
and work-staff coordination for the process of integrating RBSs with a network.
Only a limited amount of data must be scanned or entered on-site to initiate the
automated integration bringing an RBS into service.
For more information, see Autointegration of RBS.
2.7 Basic Load Management
The purpose of Basic Load Management is to protect the eNodeB and it's cells
from overload while minimizing the impact to the traffic.
For more information, see Basic Load Management.
2.8 Battery Test
Battery Test is a feature that allows for continuous monitoring of the battery
condition. In this way, the operator is informed remotely when the batteries start
to degrade and need to be changed.
For more information, see Battery Test.
2.9 Bridged Virtual Interface
Bridged Virtual Interface (BVI) provides functionality to send and receive routed
Layer 3 traffic through a Layer 2 bridge. This allows it to work as a gateway
between a switched and a routed network.
The BVI feature is used to provide a gateway for a bridge that connects two
or more network segments. This creates an aggregate Ethernet network, and
allows routed traffic to use a built-in bridge as a link layer.
For more information, see Bridged Virtual Interface.
6 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Feature Summary
2.10 Cascadable Radio Units
The Cascadable Radio Units feature enables cascades of Radio Units for each
Common Public Radio Interface (CPRI) link. This enables a configuration with
more Baseband (Radio) units than number of available ports on the Baseband
unit.
For more information, see Cascadable Radio Units.
2.11 Cascaded RET Support
The RET function enables the operator to control and optimize the coverage
area by modifying the inclination of installed antennas, without the need for
climbing masts. Configuring a number of RET units in cascade allows the
operator to improve end-user service while keeping operating costs to a
minimum. By cascading, that is, connecting a number of RET units to the same
multidrop bus, a number of antennas are controlled over the antenna interface
on one radio unit.
Cascaded RET units provides means to add tilting capability for antennas to
co-sited base stations without support for RET control.
For more information, see Cascaded RET Support.
2.12 Certificate Handling
The node relies on asymmetric cryptography and digital signatures to
authenticate communicating peers and validate signed files. Certificates and
trust relationships ordered in a Public-Key Infrastructure (PKI) are required to
ensure the correctness and validity of the keys used.
Trust categories are used for grouping trusted certificates and building
certificate chains.
For more information, see Manage Security.
2.13 Clock Source over NTP
An NTP reference, that is, an NTP client, provides frequency synchronization
service to a node. Examples of services that require frequency synchronization
are LTE FDD mode, GSM and WCDMA.
To enable services that require frequency synchronization, the node must
be synchronized to a stable network synchronization reference. The NTP
reference uses the standard NTP protocol over the IP backhaul towards an
NTP server. NTP provides the frequency accuracy required by 3GPP.
For more information, see Clock Source over NTP.
4/006 51-LZA 701 6014 Uen K | 2016-05-17 7
Basic Feature Overview
2.14 CMPv2
Certificate Management Protocol version 2 (CMPv2) is an option for Node
Credential Enrollment.
For more information, see Manage Security.
2.15 Contention Free Random Access
The Contention Free Random Access (CFRA) procedure avoids contention by
dedicating resources for UE to use for random access.
For more information, see Contention Free Random Access.
2.16 CPRI Link Observability
The Common Public Radio Interface (CPRI) Link Observability feature
provides improvements in the observation of LTE and WCDMA systems. The
improvements include fault detection, fault localization, fault isolation, and
alarm handling to CPRI links and Small Form-Factor Pluggable (SFP) modules.
For more information, see CPRI Link Observability.
2.17 Dual Band Support
Enables the use of spectrum resources on two bands with one Digital Unit (DU).
For more information, see Dual Band Support.
2.18 Dynamic Cell Status
Enables the operator to retrieve a snapshot of attached UEs and used radio
bearers on a per cell level.
For more information, see Dynamic Cell Status.
2.19 Emergency Call Prioritization
Emergency calls are prioritized in the admission control during initial access,
E-RAB establishment and incoming handover. The prioritization is achieved by
reservation of resources that can only be used for emergency calls.
For more information, see Emergency Call Prioritization.
8 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Feature Summary
2.20 Enhanced Observability
PM counters and events, that provides increased granularity for PM data,
including peak/min values and distributions of key events and procedures, and
QCI separation of E-RAB establishment observability. Measurements such as
procedure times and processor load are also introduced.
For more information, see Enhanced Observability.
2.21 eNodeB ID in X2 Traces
This feature provides the source and target global E-UTRAN Node B (eNodeB)
IDs for all supported standardized X2 messages in trace, both in streaming and
Result Output Period (ROP) mode. It is beneficial for operators to investigate
X2 related analysis and troubleshoot by cell trace.
For more information, see eNodeB ID in X2 Traces.
2.22 Ethernet Switching
This feature controls network bridging. Bridging allows two or more
communication networks, or two or more network segments, to create an
aggregate network. A network bridge is a network device that connects multiple
network segments. Bridge behavior is defined by IEEE 802.1Q.
Ethernet bridging allows operators to save IP addresses. Ethernet bridging
also makes it easy to add new site equipment without impact on the network
IP address planning.
For more information, see Ethernet Switching.
2.23 Fallback from Time and Phase Synchronization
Certain features in the eNodeB require accurate time and phase synchronization
to work properly. If a synchronization source malfunction occurs in the
eNodeB, either the features dependent on time and phase synchronization
or the whole eNodeB must be disabled. Otherwise, the time and phase
synchronization-dependent features cause negative impact on:
• The affected eNodeB
• The UEs served by the affected eNodeB
• The neighbor eNodeBs
4/006 51-LZA 701 6014 Uen K | 2016-05-17 9
Basic Feature Overview
2.24 Firmware Download of Antenna Line Devices
This feature enhances the antenna system management capabilities in that it
allows the operator to remotely upgrade the firmware on any 3GPP Iuant (AISG
v2) compliant antenna near unit directly from OSS-RC, instead of having to
visit the site.
For more information, see Firmware Download of Antenna Line Devices.
2.25 Fractional Pathloss Power Control
For more information, see Fractional Pathloss Power Control.
2.26 ICIC - Autonomous Resource Allocation
ICIC (Inter Cell Interference Coordination) distributes the interference between
cells.
For more information, see ICIC - Autonomous Resource Allocation.
2.27 Idle Mode Support
In idle mode, the User Equipment (UE) has no active connection to the RAN.
The Idle Mode Support feature enables the UE in idle mode to access the
network and be reached from the network within acceptable delay..
For more information, see Idle Mode Support.
2.28 Intra-LTE Handover
Intra-LTE Handover is the basic mobility function for UEs in active mode. When
one or more neighbor cells are better than current serving cell the UE is ordered
to handover to best cell. Best cell evaluation is based on measurements of
neighbor cells, serving cell and evaluation algorithm controlling parameters
set by the node.
For more information, see Intra-LTE Handover.
2.29 IP Loopback Interface
The main purpose of the IP Loopback Interface feature is to provide resilient
transport for node internal applications.
The Loopback IP Interface feature provides the possibility for an application to
use one source address for all traffic. This is useful for management purposes,
10 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Feature Summary
as it prevents packets being assigned different source addresses depending
on the used port.
For more information, see IP Loopback Interface.
2.30 Jumbo Frames
This basic feature introduces support to configure the S1-U MTU to greater
than 1500 bytes as a means to manage excess packet fragmentation and
reassembly.
Not all operators will need to enable this feature, particularly if they are not
experiencing a problems with fragmentation in their network. Others will not
be able to use this feature if their network nodes do not support MTU greater
than 1500 bytes.
For more information, see Jumbo Frames.
2.31 Maximum Cell Range
The Maximum Cell Range feature provides support for a maximum cell range of
100 km for FDD, and 93 km for TDD.
For more information, see Maximum Cell Range.
2.32 Multiple Digital Units
The Multiple Digital Unit feature allows the connection of a second Digital Unit
through the use of the IDL port, IDL1: Up to two Digital Units can be connected
using this port.
For more information, see Multiple Digital Units.
2.33 O&M Security
O&M interfaces are secured by encryption, SSH and TLS. Access to the O&M
interfaces is possible by using the TN and LMT ports.
For more information, see Manage Security.
2.34 Paging
Paging is used by the core network to notify specific UE in Radio Resource
Control (RRC) RRC_IDLE state about incoming data sessions. Paging
messages are sent by the core network to all RBSs in the tracking area.
4/006 51-LZA 701 6014 Uen K | 2016-05-17 11
Basic Feature Overview
For more information, see Paging.
2.35 PDCCH Coverage Extension
The PDCCH Coverage Extension feature increases the PDCCH coverage
for downlink assignments in limited RF conditions, by using a more robust
DCI format.
For more information, see PDCCH Coverage Extension.
2.36 Port Mirroring
Port Mirroring allows the operator to mirror all traffic from any Ethernet port to
any other Ethernet port. This is very useful when troubleshooting networking
and protocol problems. This feature must only be used by Ericsson and
operator trusted personnel.
For more information, see Port Mirroring.
2.37 Power Control
Power control and power configuration reduce inter-cell interference and power
consumption. This leads to higher cell capacity and the control of the maximum
data rate for User Equipment (UE) at cell edge. In addition, it helps to prolong
the battery life of the UE.
For more information, see Power Control.
2.38 Radio Bearer Service
The Radio Bearer Service feature provides the service of establishment,
maintenance and release of Signaling Radio Bearers (SRBs) and Data Radio
Bearers (DRBs).
For more information, see Radio Bearer Service.
2.39 Random Access
User Equipment (UE) uses the Random Access (RA) process to gain new or
renewed access and uplink timing synchronization to the network.
For more information, see Random Access.
12 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Feature Summary
2.40 RET Support
RET Support is a feature that provides 3GPP-compliant support for managing
Remote Electrical Tilt (RET) antenna in the Radio Access Network (RAN).
Antenna tilting is a key method to ensure high capacity by limiting interference.
Changes to the antenna tilt are required during initial tuning. Recalculating
antenna tilt is also part of mature network management.
For more information, see RET Support.
2.41 RRC Connection Re-establishment
The feature allows the UE to re-establish RRC connection in serving cell in
case of radio link failure.
For more information, see RRC Connection Re-establishment.
2.42 Scheduler
The Scheduler feature distributes radio interface and RBS resources between
various user and control data flows requesting transmission in the cell.
For more information, see Scheduler.
2.43 Secure Execution Environment
This feature introduces a secure environment that greatly improves the
protection against eavesdropping and other attacks.
For more information, see Manage Security.
2.44 Signed Software
The feature Signed Software improves the software security on the node.
The Signed Software feature stops executable software that is not signed by
Ericsson.
For more information, see Manage Security.
2.45 Simplex and Duplex Radio Ports
The Simplex and Duplex Radio Ports feature makes it possible to connect
an antenna system with separate ports for receive and transmit, that is,
4/006 51-LZA 701 6014 Uen K | 2016-05-17 13
Basic Feature Overview
simplex reception and transmission connections, as opposed to the default
receive/transmit duplex connection.
A typical configuration requiring this feature is a Distributed Antenna System
(DAS). These systems often have separate ports for transmission and
reception. Some DAS systems also support duplex operations, in which case
the default Rx/Tx duplex port is used.
For more information, see Simplex and Duplex Radio Ports.
2.46 Static Routing
Static Routing provides functionality to forward IPv4 datagrams between
external links, and between external links and internal termination points.
Static Routing enables transport and routing of IPv4 datagrams in an IPv4
network, enabling the node to function as a router in an IPv4 network. Static
Routing enables the configuration of the routing table that controls the routing
of datagrams toward their destinations.
For more information, see Static Routing.
2.47 Support for 15km CPRI Link
Increases support for long optical fiber between Radio and Baseband to 15
kilometers.
For more information, see Support for 15km CPRI Link.
2.48 System Information Modification
This feature makes it possible to modify the System Information broadcasted in
the cell without doing a lock/unlock operation on the cell.
For more information, see System Information Modification.
2.49 TMA Support
The 3GPP compatible Tower Mounted Amplifier (TMA) is installed on an
antenna tower, connected directly to the antenna feeder cable. The TMA is
used to compensate for feeder loss on the uplink, allowing antennas to be
placed with some distance from the RBS.
For more information, see TMA Support.
14 4/006 51-LZA 701 6014 Uen K | 2016-05-17
Feature Summary
2.50 VSWR Antenna Supervision
The VSWR Antenna Supervision feature enables supervision of the feeder
cables. Measurements are made on the reflected radio power and it is possible
to detect breaks in the cable connected to the Radio Unit (RU). An alarm is
raised if return loss is below the configured VSWR sensitivity value.
For more information, see VSWR Antenna Supervision.
2.51 X2 Configuration
The X2 Configuration feature supports operators in the management of
neighbor relations. It automates the management of X2 connections, data
about external RBSs and data about external cells. Automated behavior
reduces the need for manual configuration and optimization, supporting the
concepts of the self-organizing network.
For more information, see X2 Configuration.
4/006 51-LZA 701 6014 Uen K | 2016-05-17 15
Вам также может понравиться
- LTE Integration ProcedureДокумент77 страницLTE Integration Procedurenazib422021Оценок пока нет
- OBF - Radio Configuration DrawingДокумент3 страницыOBF - Radio Configuration DrawingEmmanuel Adu-KissieduОценок пока нет
- Free Download Here: Ericsson Evo Controller 8200 at Askives PDFДокумент2 страницыFree Download Here: Ericsson Evo Controller 8200 at Askives PDFKao Sun HoОценок пока нет
- How To Get CE License and CE Number at The RBS Through MOSHELLДокумент12 страницHow To Get CE License and CE Number at The RBS Through MOSHELLMENANI ZineddineОценок пока нет
- Common Issues and ResolutionsДокумент9 страницCommon Issues and Resolutionsanon_496339251Оценок пока нет
- E RAN Integration 2 YrsДокумент1 страницаE RAN Integration 2 YrsShahbaz AlamОценок пока нет
- SW UpgradeG1&G2Документ24 страницыSW UpgradeG1&G2ivanaru404Оценок пока нет
- Moshell Amos CommandsДокумент18 страницMoshell Amos CommandsWUSHUОценок пока нет
- RBS6601 Informacion GeneralДокумент42 страницыRBS6601 Informacion GeneralLucas Lopes dos SantosОценок пока нет
- GuidelineДокумент20 страницGuidelinejuan carlos LPОценок пока нет
- 2-2 Ericsson Ruffini Sync in MobileStandards Ruffini-Rev3-Tot PDFДокумент20 страниц2-2 Ericsson Ruffini Sync in MobileStandards Ruffini-Rev3-Tot PDFsushiОценок пока нет
- ERANДокумент7 страницERANjuan carlos LPОценок пока нет
- WCDMA RAN 2019 - 2020 - Rev A - Course Program PDFДокумент45 страницWCDMA RAN 2019 - 2020 - Rev A - Course Program PDFlivrijaОценок пока нет
- SRS Trainning MaterialДокумент24 страницыSRS Trainning MaterialIboro PeterОценок пока нет
- Cisco ITP Exercise and Answer v00.02Документ23 страницыCisco ITP Exercise and Answer v00.02bayoubgoor100% (1)
- SCU ENM CMDДокумент2 страницыSCU ENM CMDDanny AguirreОценок пока нет
- Tigo LTE X2 Link Failure InvestigationДокумент10 страницTigo LTE X2 Link Failure InvestigationbuntyloverОценок пока нет
- Ericsson RBS SeriesДокумент2 страницыEricsson RBS SeriesJonattan Da SilvaОценок пока нет
- 411 2133 525 - 06.12Документ952 страницы411 2133 525 - 06.12Daniel ChapmanОценок пока нет
- Ericsson Rbs6102 - Document TranscriptДокумент12 страницEricsson Rbs6102 - Document TranscriptDonald AbidjoОценок пока нет
- BaseBand Integration SAMYДокумент16 страницBaseBand Integration SAMYBOURAS Ihabe - بوراس إيهابОценок пока нет
- Ericsson FileДокумент5 страницEricsson FileBeza GetachewОценок пока нет
- Nexius Generic MOP LTE L17Q3 BB5216 MigrationДокумент11 страницNexius Generic MOP LTE L17Q3 BB5216 Migrationgururou100% (1)
- 3 Baseband 6630 Integration Guide - Compress PDFДокумент55 страниц3 Baseband 6630 Integration Guide - Compress PDFRabie DrizaОценок пока нет
- Lte Ericsson NSN Feature Mapping v10Документ166 страницLte Ericsson NSN Feature Mapping v10Amir Moshfegh KiaОценок пока нет
- Ericsson KPI FormularДокумент3 страницыEricsson KPI FormularChange LeeОценок пока нет
- Total Alarm Count Alarm Text: Data - 1Документ14 страницTotal Alarm Count Alarm Text: Data - 1Manu KulshreshthaОценок пока нет
- ANOME MoshellДокумент47 страницANOME MoshellYacoubaОценок пока нет
- Formule Stat4gДокумент8 страницFormule Stat4gjoramiandrisoaОценок пока нет
- Ericsson FeaturesДокумент58 страницEricsson FeaturesDorra Labidi100% (1)
- Method of Procedure Semi Auto Integration On Site XL Axiata ProjectДокумент10 страницMethod of Procedure Semi Auto Integration On Site XL Axiata ProjectbintangОценок пока нет
- CORE Nodes Backup ProceduresДокумент7 страницCORE Nodes Backup ProceduresAnees PeerzadaОценок пока нет
- CNAI DumpДокумент2 страницыCNAI DumpHarish KumarОценок пока нет
- DUW PresentationДокумент64 страницыDUW PresentationOnjanohasoavina MANANJARASOAОценок пока нет
- 12 1551-Lza7016012-V6uen.n.pico7Документ8 страниц12 1551-Lza7016012-V6uen.n.pico7roy100% (1)
- Acceptance Testing of BSC in GSM (Ericsson Make)Документ17 страницAcceptance Testing of BSC in GSM (Ericsson Make)bahibahi1978Оценок пока нет
- Netconf Manager Adaptor, System Administrator GuideДокумент37 страницNetconf Manager Adaptor, System Administrator GuideDiego MaradoОценок пока нет
- MOP Configuring EC Bus XL ProjectДокумент16 страницMOP Configuring EC Bus XL Projectslamet aminudinОценок пока нет
- Course Name: Ericsson Lte Enodeb Solution: Persons Having Previous Knowledge of Gsm/Wcdma/Lte Would Be PreferredДокумент3 страницыCourse Name: Ericsson Lte Enodeb Solution: Persons Having Previous Knowledge of Gsm/Wcdma/Lte Would Be PreferredGauravSwamiОценок пока нет
- 3G RNC Node B Radio Access EngineerДокумент4 страницы3G RNC Node B Radio Access EngineerSaidul Islam100% (2)
- Port Assigment Macro Ph12.4 (Black Cell) Rev A 280818Документ61 страницаPort Assigment Macro Ph12.4 (Black Cell) Rev A 280818Mr.Sutha GomenaekОценок пока нет
- WMRR 1Документ23 страницыWMRR 1Luigi RambaldiОценок пока нет
- RBS 6501 Installation InstructionsДокумент37 страницRBS 6501 Installation InstructionsLeo DuranОценок пока нет
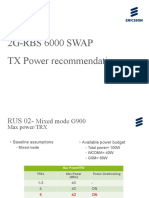
- 2G Power Settings in RBS6000Документ10 страниц2G Power Settings in RBS6000Da AОценок пока нет
- DXB5658 - Baseband 6648 Ericsson Faulty ReportДокумент1 страницаDXB5658 - Baseband 6648 Ericsson Faulty ReportNoura Sayed AbdraboОценок пока нет
- Ericsson Lte Halted Cells Checking ProcessДокумент5 страницEricsson Lte Halted Cells Checking Processmb botОценок пока нет
- LMTB Cable PDFДокумент4 страницыLMTB Cable PDFOscar SiriasОценок пока нет
- LTE FDD Network Planning and OptimizationДокумент23 страницыLTE FDD Network Planning and OptimizationLiba BaliОценок пока нет
- Ericsson Tools - LteДокумент4 страницыEricsson Tools - LteLAMKADEMОценок пока нет
- 3gip JL Pahlawan Capture Before 190702 090552Документ51 страница3gip JL Pahlawan Capture Before 190702 090552Addi CumsОценок пока нет
- Learnings eNB Integration and RF Idea LTE LaunchДокумент9 страницLearnings eNB Integration and RF Idea LTE LaunchJitendra VОценок пока нет
- HWFrequent AlarmДокумент51 страницаHWFrequent AlarmIbrahim MkaiesОценок пока нет
- Solution For IUB CongestionДокумент3 страницыSolution For IUB CongestionMarolop Hengki RiantoОценок пока нет
- Wireless Site Alarm Maintenance-NokiaДокумент20 страницWireless Site Alarm Maintenance-Nokiarookie.caozhongzeОценок пока нет
- Ericsson 2G Site Lock Down V1.1Документ8 страницEricsson 2G Site Lock Down V1.1Vod MonkeyОценок пока нет
- 03.KDR Training RBS 6601 OverviewДокумент16 страниц03.KDR Training RBS 6601 Overviewwafa wafaОценок пока нет
- L1CM6336A ENM Fallback ScriptДокумент1 страницаL1CM6336A ENM Fallback ScriptShahid MajeedОценок пока нет
- Idle Mode Cell Selection & ReselectionДокумент7 страницIdle Mode Cell Selection & ReselectionPrabhakar SinghОценок пока нет
- GSM Interactive Frequency Analysis - Dakar - Z3 - V3Документ20 страницGSM Interactive Frequency Analysis - Dakar - Z3 - V3Prabhakar SinghОценок пока нет
- NR: 3GPP's 5G Radio Access Technology: John M Meredith Director, ETSI Mobile Competence CentreДокумент62 страницыNR: 3GPP's 5G Radio Access Technology: John M Meredith Director, ETSI Mobile Competence CentrePrabhakar SinghОценок пока нет
- Network Architecture of 5G Mobile Technology: By: Ravi Shekhar 1000000071Документ18 страницNetwork Architecture of 5G Mobile Technology: By: Ravi Shekhar 1000000071Prabhakar SinghОценок пока нет
- KT - 23 Dec - 2014 - S4 PDFДокумент15 страницKT - 23 Dec - 2014 - S4 PDFPrabhakar SinghОценок пока нет
- Ccalls Date BSC Name Ccongs Ctcongs Ctralacc Cnscan Cndrop Cnuchcnt (Avg)Документ3 страницыCcalls Date BSC Name Ccongs Ctcongs Ctralacc Cnscan Cndrop Cnuchcnt (Avg)Prabhakar SinghОценок пока нет
- SIRADEL MMW Propagation 2Документ11 страницSIRADEL MMW Propagation 2Prabhakar SinghОценок пока нет
- Crowdsourcing POCДокумент23 страницыCrowdsourcing POCPrabhakar SinghОценок пока нет
- 09T030 FinalДокумент14 страниц09T030 FinalKriengsak RuangdechОценок пока нет
- Nuendo 4 Remote Control Devices EsДокумент24 страницыNuendo 4 Remote Control Devices EsRamon RuizОценок пока нет
- Ex Delta Ex Delta - Dia: OVAL CorporationДокумент8 страницEx Delta Ex Delta - Dia: OVAL CorporationDaniela GuajardoОценок пока нет
- RCJ&Y - Jubail Industrial City 2: Phase 3 and 4 Sea Water Cooling StationДокумент5 страницRCJ&Y - Jubail Industrial City 2: Phase 3 and 4 Sea Water Cooling Stationsalman KhanОценок пока нет
- 2ND 3RD Typical Floor Plan PDFДокумент1 страница2ND 3RD Typical Floor Plan PDFSamuel ZaraОценок пока нет
- GYANDOOT SamitiДокумент16 страницGYANDOOT SamitivinaykoolsОценок пока нет
- Wrights Mushroom ColumnДокумент33 страницыWrights Mushroom ColumnKeithy GandhiОценок пока нет
- Fuel Handling SystemДокумент4 страницыFuel Handling SystemRoel FranciscoОценок пока нет
- By George G. Meyerhof, F. Asce: J. Geotech. Engrg., 1983, 109 (6) : 797-806Документ10 страницBy George G. Meyerhof, F. Asce: J. Geotech. Engrg., 1983, 109 (6) : 797-806PoYing HuangОценок пока нет
- EFR32BG1 Blue Gecko BluetoothДокумент102 страницыEFR32BG1 Blue Gecko BluetoothLullaby summerОценок пока нет
- Problem 1-4Документ6 страницProblem 1-4Anonymous xIzzEifjPОценок пока нет
- 01 Cone Winding Study (Calculation)Документ4 страницы01 Cone Winding Study (Calculation)Hasan Istiaque Ahmed60% (5)
- Pt. Partono Fondas: Company ProfileДокумент34 страницыPt. Partono Fondas: Company Profileiqbal urbandОценок пока нет
- Lord!: KnowledgeДокумент161 страницаLord!: KnowledgeAsra Zafar khanОценок пока нет
- CTLG MINI08engДокумент48 страницCTLG MINI08enggadacz111Оценок пока нет
- d9 VolvoДокумент57 страницd9 Volvofranklin972100% (2)
- Brochure FDP - EG 16.08.2021-1-2-2Документ3 страницыBrochure FDP - EG 16.08.2021-1-2-2sri sivaОценок пока нет
- Overview On Sourcing: Oracle Fusion: 21D UpdatesДокумент24 страницыOverview On Sourcing: Oracle Fusion: 21D UpdatesMathi VathaniОценок пока нет
- JLG 600A 660AJ From Serial 0300177361 Service Manual (1) (1) Gabriel DSDДокумент4 страницыJLG 600A 660AJ From Serial 0300177361 Service Manual (1) (1) Gabriel DSDCASAQUI LVAОценок пока нет
- EM000039Rev1 PDFДокумент1 страницаEM000039Rev1 PDFGustavo RiveraОценок пока нет
- Cloud Computing - Feb-Mar 2017Документ40 страницCloud Computing - Feb-Mar 2017Abhishek SinghОценок пока нет
- Toyota Vios Ecu Wiring DiagramДокумент4 страницыToyota Vios Ecu Wiring DiagramSri Yuniati17% (6)
- RT 67Документ11 страницRT 67dinesh kumarОценок пока нет
- Desmophen 1200 - en - 00134597 17947398 20766463Документ3 страницыDesmophen 1200 - en - 00134597 17947398 20766463Sabri AeroChemОценок пока нет
- Sabre-Baggage Management and Analysis SystemДокумент24 страницыSabre-Baggage Management and Analysis Systemdifaini anugrahОценок пока нет
- DVMДокумент197 страницDVMLeonardLapatratОценок пока нет
- Chap 08Документ63 страницыChap 08Sam KashОценок пока нет
- Final App - FlsДокумент9 страницFinal App - Flsjunebug172100% (1)
- Hyundai Robex 220LC-9A SpecificationsДокумент14 страницHyundai Robex 220LC-9A SpecificationsKundan DhurveОценок пока нет
- Fasteners Lecture 11-20-03Документ67 страницFasteners Lecture 11-20-03laponggaОценок пока нет