Академический Документы
Профессиональный Документы
Культура Документы
Efficient Bitcoin Miner System Implemented On Zynq SoC
Загружено:
Edison EnriquezОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Efficient Bitcoin Miner System Implemented On Zynq SoC
Загружено:
Edison EnriquezАвторское право:
Доступные форматы
XCELLENCE IN NETWORKING
Efficient Bitcoin Miner
System Implemented
on Zynq SoC
16 Xcell Journal Third Quarter 2013
XCELLENCE IN NETWORKING
by Alexander Standridge
MSc Candidate The integration of programmable
California State University, Northridge
astandridge@gmail.com logic with a processor subsystem
Calvin Ho in one device allows for the
MSc Candidate
California State University, Northridge development of an adaptable
calvin.ho.67@my.csun.edu
Shahnam Mirzaei
and affordable Bitcoin miner.
Assistant Professor
California State University, Northridge itcoin is a virtual currency that has become increas-
shahnam.mirzaei@csun.edu
Ramin Roosta
Professor
B ingly popular over the past few years. As a result,
Bitcoin followers have invested some of their assets in
support of this currency by either purchasing or “mining”
California State University, Northridge Bitcoins. Mining is the process of implementing mathematical
ramin.roosta@csun.edu calculations for the Bitcoin Network using computer hard-
ware. In return for their services, Bitcoin miners receive a
lump-sum reward, currently 25 Bitcoins, and any included
transaction fees. Mining is extremely competitive, since net-
work rewards are divided up according to how much calcula-
tion all miners have done.
Bitcoin mining began as a software process on cost-ineffi-
cient hardware such as CPUs and GPUs. But as Bitcoin’s pop-
ularity has grown, the mining process has made dramatic
shifts. Early-stage miners had to invest in power-hungry
processors in order to obtain decent hash rates, as mining
rates are called. Although CPU/GPU mining is very inefficient,
it is flexible enough to accommodate changes in the Bitcoin
protocol. Over the years, mining operations have slowly grav-
itated toward dedicated or semi-dedicated ASIC hardware for
optimized and efficient hash rates. This shift to hardware has
generated greater efficiency in mining, but at the cost of lower
flexibility in responding to changes in the mining protocol.
An ASIC is dedicated hardware that is used in a specific
application to perform certain specified tasks efficiently. So
although ASIC Bitcoin miners are relatively inexpensive and
produce excellent hash rates, the trade-off is their inflexibili-
ty to protocol changes.
Like an ASIC, an FPGA is also an efficient miner and is rel-
atively inexpensive. In addition, FPGAs are more flexible than
ASICs and can adjust to Bitcoin protocol changes. The current
problem is to design a completely efficient and fairly flexible
mining system that does not rely on a PC host or relay device
to connect with the Bitcoin Network. Our team accomplished
this task using a Xilinx® Zynq®-7000 All Programmable SoC.
THE BIG PICTURE
To accomplish our goal of implementing a complete mining sys-
tem, including a working Bitcoin node and a miner that is both
efficient and flexible, we needed a powerful FPGA chip not
only for flexibility, but also for performance. In addition to the
FPGA, we also needed to use a processing engine for efficiency.
Third Quarter 2013 Xcell Journal 17
XCELLENCE IN NETWORKING
At its simplest, the Bitcoin mining process boils down to a SHA-256
process and a comparator. The SHA-256 process manipulates
the block header information twice, and then compares it with
the Bitcoin Network’s expanded target difficulty.
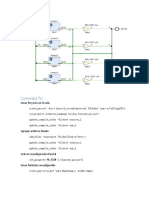
On this complete system-on-chip fairly inexpensive for its class (see card slot for mass storage. It enabled
(SoC), we would need an optimized http://www.zedboard.org/buy). The us to put the entire updated Bitcoin
kernel to run all required Bitcoin activ- Zynq-7020 SoC chip contains a pair of program onto it.
ities, including network maintenance ARM® Cortex™-A9 processors embed- Using the ZedBoard, we implement-
and transactions handling. The hard- ded in 85,000 Artix®-7 FPGA logic ed our SoC Bitcoin Miner. It includes a
ware that satisfied all these conditions cells. The ZedBoard also comes with host, a relay, a driver and a miner, as
was the Zynq-7020 SoC residing on the 512 Mbytes of DDR3 memory that seen in Figure 1. We used the non-
ZedBoard development board. At enabled us to run our SoC design graphical version of the original
around $300 to $400, the ZedBoard is faster. Lastly, the ZedBoard has an SD Bitcoin client, known as Bitcoind, as a
#define ROTR(x,n) ( (x >> n) | (x << (32 - n)))
// Logic operations
#define s0(x) (ROTR(x,7) ^ ROTR(x,18) ^ (x >> 3))
Bitcoin Network #define s1(x) (ROTR(x,17) ^ ROTR(x,19) ^ (x >> 10))
#define s2(a) (ROTR(a,2) ^ ROTR(a,13) ^ ROTR(a,22))
#define s3(e) (ROTR(e,6) ^ ROTR(e,11) ^ ROTR(e,25))
#define w(a,b,c,d) (s1(d) + c + s0(b) + a)
#define maj(x,y,z) ((x&y)^(x&z)^(y&z))
#define ch(x,y,z) ((x&y)^((~x)&z))
Bitcoind (Host)
#define t1(e,f,g,h,k,w) (h + s3(e) + ch(e,f,g) + k + w)
#define t2(a,b,c) (s2(a) + maj(a,b,c))
for( i = 0; i < 64; i++){
Relay
// loop 64 times
if( i > 15) {
W[i] = w(W[i-16],W[i-15],W[i-7],W[i-
2]); // Temp values
}
Driver
unsigned int temp1 = t1(e,f,g,h,K[i],W[i]);
unsigned int temp2 = t2(a,b,c);
h = g;
// Round results
g = f;
Miner
f = e;
e = d + temp1;
SOC Miner d = c;
c = b;
b = a;
Figure 1 – The basic data flow of a = temp1 + temp2;
the miner showing the relation- }
ships between the components
and the Bitcoin Network
Figure 2 – Vivado HLS implementation of the SHA-256 process
18 Xcell Journal Third Quarter 2013
XCELLENCE IN NETWORKING
input data is larger than 63 bytes. In
80-Byte Input
this case, the data is padded out to the
Header
nearest multiple of 64, with the last
byte reserved for the data length. Each
SHA-256 Process 64-byte chunk is then run through the
SHA-256 Process
SHA-256 process one after another,
32 Bytes
using the output of the previous
32 Bytes chunk, known as the midstate, as the
SHA-256 Process basis for the next chunk.
With Vivado HLS, the implementa-
Comparator 32 Bytes
tion of the SHA-256 process is a simple
“for” loop; an array to hold the con-
1 Bit
Comparator stants required by each round; an
additional array to hold the temporary
A 1 Bit B values used by later rounds; eight vari-
ables to hold the results of each
round; and definitions for the logic
64-Byte Input 80-Byte Input
operations, as seen in Figure 2.
At its simplest, the Bitcoin mining
SHA-256 Process Midstate
process boils down to a SHA-256
SHA-256 Process
32 Bytes process and a comparator. The SHA-
Midstate
16 bytes 32 Bytes 256 process manipulates the block
+Padding
SHA-256 Process header information twice, and then
Padding
SHA-256 Process compares it with the Bitcoin Network’s
32 Bytes
expanded target difficulty, as seen in
Padding
SHA-256 Process 32 Bytes Figure 3A. This is a simple concept that
32 Bytes becomes complicated in hardware,
Comparator because the first-version Bitcoin block
SHA-256 Process header is 80 bytes long. This means that
1 Bit C 1 Bit D the initial pass requires two runs of the
SHA-256 process, while the second pass
requires only a single run, as seen in
Figure 3B. This double pass, defining
Figure 3 – A (top left) is the simplest form of the core, showing the general flow. two separate SHA-256 modules, compli-
B splits the single, universal SHA-256 process module into a pair of dedicated
modules for each phase. C breaks down the specific SHA-256 processes into a cates the situation because we want to
single generic module that can be repeatedly used. D utilizes a quirk in the block keep the SHA-256 module as generic as
header information allowing the removal of the first generic SHA-256 process. possible to save development time and
to allow reuse. This generic require-
host to interact with the Bitcoin exploring the details of the mining- ment on the SHA-256 module defines
Network. The relay uses the driver to core structure, it’s useful to look at the the inputs and outputs for us, setting
pass work from the host to the miner. basics of the SHA-256 process. them as the 32-byte initial values, 64-
The SHA-256 process pushes 64 byte data and 32-byte hash. Thus, with
THE DEPTHS OF bytes through 64 iterations of bitwise the core aspect of the SHA-256 process
THE MINING CORE shifts, additions and exclusive-ors, isolated, we can then manipulate these
We started developing the mining core producing a 32-byte hash. During the inputs to any layout we desire.
with Vivado® HLS (high-level synthe- process, eight 4-byte registers hold The first of the three prototypes we
sis), using the U.S. Department of the results of each round, and when developed used a single SHA-256
Commerce’s specification for SHA-256. the process is done these registers Process module. From the beginning,
With Vivado HLS’ ability of fast behav- are concatenated to produce the we knew that this core would be the
ioral testing, we quickly laid out sever- hash. If the input data is less than 63 slowest of the three because of the
al prototype mining cores, ranging bytes, it is padded to 63 bytes and the lack of pipelining; however, we were
from a simple single-process to a com- 64th byte is used to store the length of looking to see how compact we could
plex multiprocess system. But before the input data. More commonly, the make the SHA-256 process.
Third Quarter 2013 Xcell Journal 19
XCELLENCE IN NETWORKING
With the results of our prototypes in
4
hand, we settled on a version of the
third core developed by the Bitcoin
3.5 open-source community specifically
for the Xilinx FPGAs.
3 ISE DEVELOPMENT
Bitcoin mining is a race to find a num-
2.5 ber between zero and 232-1 that gives
Worker Speed (MHps)
you a solution. Thus, there are really
only two ways to improve mining-
2 core performance: faster processing
or divide-and-conquer. Using a
Spartan®-3 and a Spartan-6 develop-
1.5
ment board, we tested a series of dif-
ferent frequencies, pipelining tech-
1 niques and parallelization.
For our frequency tests, we started
with the Spartan-3E development
0.5
board. However, it quickly became
apparent that nothing could be done
0 beyond 50 MHz and as such, we left
00:00 12:00 00:00 12:00 00:00 12:00 00:00 12:00
the frequency tests to the Spartan-6.
Figure 4 – The hash rate of the mining core over a four-day period of core-optimization We tested 50, 100 and 150 MHz on
testing. The graph is an average over time, giving a general idea of performance of the the Spartan-6 development board,
mining core. The results decreased due to hitting the routing limits of the test platforms. which resulted in predictable results,
achieving 0.8, 1.6 and 2.4 mega hashes
The second prototype contained process the last 16 bytes of the head- per second (MHps) respectively. We
three separate SHA-256 Process mod- er, for a significant hash rate boost also tried 75 MHz and 125 MHz during
ules chained together, as seen in (see Figure 3D). the parallelization and pipelining
Figure 3C. This configuration allowed The comparator is a major compo- tests, but these frequencies were only
for static inputs where the first nent, and properly designed can signif- a compromise to make the miner fit
process handles the first 64 bytes of icantly increase performance. A solu- onto the Spartan-6.
the header information. The second tion is a hash that has a numeric value One of the reasons we chose the
process handles the remaining 16 less than the 32-byte expanded target mining core from the open-source com-
bytes from the header plus the 48 bytes difficulty defined by the Bitcoin sys- munity was that it was designed with a
of required padding. The third process tem. This means we must compare depth variable to control the number of
handles the resulting hash from the each hash we produce and wait to see pipelined stages. The depth is an expo-
first two. These three separate if a solution is found. Due to a quirk nential value between 0 and 6, which
processes simplified the control logic with the expanded target difficulty, the controls the number of power-two iter-
and allowed for simple pipelining. first 4 bytes will always be zero regard- ations the VHDL “generate” command
The third and final prototype used less of what the difficulty is, and as the executes—namely, 20 to 26. We per-
two SHA-256 Process modules and network’s difficulty increases so will formed the initial frequency tests with a
took advantage of a quirk in the the number of leading zeros. At the depth of 0—that is, only a single round
Bitcoin header information and min- time of this writing, the first 13 bytes implemented for each process.
ing process that the Bitcoin mining of the expanded target difficulty were On the Spartan-3e we tested
community makes use of. The block zero. Thus, instead of comparing the depths of 0 and 1 before running into
header information is laid out in such whole hash to the target difficulty, we timing-constraint issues. The depth of
a way that only the first 64 bytes check to see if the first x number of 0 at 50 MHz gave us roughly 0.8 MHps,
change when the block is modified. bytes are zero. If they are zero, then while the depth of 1 achieved roughly
This means that once the first 64 we compare the hash to the target dif- 1.6 MHps.
bytes are processed, we can save the ficulty. If they are not zero, then we On the Spartan-6 we were able to
output data (midstate) and only toss the hash out and start over. reach a depth of 3 before running into
20 Xcell Journal Third Quarter 2013
XCELLENCE IN NETWORKING
USING THE EDK
After FPGA testing, our next step was
to tie the mining core into the Zynq
SoC’s AXI4 bus. Xilinx’s Embedded
SD Card
Development Kit (EDK) comes
loaded with a configuration utility
specifically designed for the Zynq
SoC, allowing us to easily configure
Ethernet every aspect. By default, the system
has the 512 Mbytes of DDR3, the
Ethernet, the USB and the SD inter-
face enabled, which is everything we
ARM needed for our Bitcoin SoC.
Cortex-A9 The twin Cortex-A9 processors fea-
Mining Core
ture the AXI4 interface instead of the
ARM PLB system used by previous soft-core
Cortex-A9 systems. All of the peripherals are
attached to processors through the
AXI4 interface, as shown in Figure 5.
The EDK custom peripheral wizard
DDR3 RAM provides code stubs for the different
variants of the AXI4 interface and
serves as the basis for the develop-
ment of the mining core’s AXI inter-
face. For simplicity, we used the AXI4-
Processor
Subsystem Programmable Lite interface, which provides simple
(PS) Logic (PL) read and write functionality to the
AXI4 Bus
mining core. Ideally, developers would
want to use the regular AXI4 interface
Figure 5 – The relatively new AXI4 interface connects the ZedBoard’s hard to take advantage of the advanced
peripherals with the ARM processors and Artix FPGA logic. interface controls, such as data bursts.
Keeping with the goal of simplicity,
timing-constraint issues. At 50 MHz, the The final performance improvement we used three memory-mapped regis-
Spartan-6 achieved the same results as we tested was parallelization. With ters to handle the mining-core I/O. The
the Spartan-3 at a depth of 0 and 1. We only minor modifications, we doubled first register feeds the host data packet
noticed an interesting trend at this and quadrupled the number of SHA- to the miner. This register keeps track
point. Doubling the frequency had the 256 sets. A set consists of two SHA-256 of the amount of data passed and locks
same effect as increasing the depth of Process modules. This modification itself after 11 words have been trans-
the pipeline. The upper limit was set by effectively cut the potential number ferred. This lock is removed automati-
the availability of routing resources, range for each set into halves, for the cally when a solution is found. We can
with our peak averaging out at roughly doubled number of SHA-256 sets, or remove the lock manually if necessary
3.8 MHps, as seen in Figure 4. fourths for the quadrupled number. To through the status register.
The SHA-256 Process module has fit these extra SHA processes onto the We defined the second register as
10 different 32-bit additions. In this Spartan-6, we had to reduce the system the status register, flagging certain
implementation, we are attempting to frequency. Four sets of the SHA-256 bits for the various states the mining
do all of them in a single clock cycle. Process modules would run at 75 MHz, core goes through. With the simplicity
To shorten the longest path, we tried while two sets would run at 125 MHz. of our design, we used only three
to divide the adder chains into a series The hash rate improvements were dif- flags: a loaded flag, a running flag and
of stages. However, doing so radically ficult to document. We could easily see a solution-found flag. The loaded flag
changed the control logic for the the hash rate of an individual SHA-256 is triggered when the mining core
whole mining core and required a set; however, a multiple-set mining receives 11 words, as mentioned
complete rewrite. We dropped these core could find a solution faster than before, and is cleared when we write
changes to save time and effort. the hash rate implied. to it. The start/running flag is set by us
Third Quarter 2013 Xcell Journal 21
XCELLENCE IN NETWORKING
to start the mining core, and is
cleared by the mining core when a
To improve on our current design without
solution is found. The final register is
the output register, which is loaded
jeopardizing the adaptability, we could add more
with the solution when one is found.
We tested each stage of the AXI4-
mining cores that connect to the main Bitcoin node.
Lite interface development before
adding the next component. We also
These additions could boost the performance
tested the AXI4-Lite interface in
Xilinx’s Software Development Kit
and provide a higher overall hash rate.
using a bare-bones system. The test
served two purposes: first, to confirm that before we can use the reserved from Bitcoind to the mining core
that the mining core’s AXI4-Lite inter- address we have to request an address through the driver, and return results. As
face was working correctly and sec- remap for the mining core. The kernel a matter of course, the relay program
ond, to ensure that the mining core gives us a virtual address through the would check to see if Bitcoind was run-
was receiving the data in the correct remap, which we can then use to com- ning and that the mining core was ready
endian format. municate to the mining-core registers. and operating properly. Since the relay
Now that we have access to the program would normally sit idle for the
EMBEDDED LINUX hardware, the initialization function majority of the time, we will implement
With the mining core tied into the then runs a simple test on the mining a statistics compilation subsystem to
processors, we moved to software core to confirm that the core is operat- gather data and organize it in a log file.
development. Ideally we wanted to ing properly. If it is, we register the Ideally, we would use a Web host inter-
build our own firmware, potentially major and minor numbers—which are face for configuration, statistical display
with a Linux core, to maximize per- used to identify the device in user pro- and device status.
formance. For ease of development, grams—with the kernel. Every func-
we leveraged a full Linux installation. tion has a counter, and the exit function COMPLETE, EFFICIENT
We used Xillinux, developed by is the counter to the initialization func- MINING SYSTEM
Xillybus, an Ubuntu derivative for tion. In this function, we undo every- Our solution to an efficient and com-
rapid embedded-system development. thing done during initialization— plete Bitcoin mining system is the Xilinx
Our first order of business was to specifically, release the major and Zynq-7000 All Programmable SoC on the
compile Bitcoind for the Cortex-A9 minor numbers used by the driver, then ZedBoard. This board is flexible to
architecture. We used the original open- release the mapped virtual address. changes in the Bitcoin protocol and also
source Bitcoin software to ensure com- When we first call the mining core offers a high-performance FPGA solu-
patibility with the Bitcoin Network. from the relay program, the open func- tion along with SoC capability. To
Testing Bitcoind was a simple tion runs. All we do here is to confirm improve on our current design without
matter. We ran the daemon, waited that the self-test run during the initial- jeopardizing the adaptability, we could
for the sizable block chain to down- ization function is successful. If the add more mining cores that connect to
load and then used the line command self-test fails, then we throw a system- the main Bitcoin node. These additions
to start Bitcoind’s built-in CPU min- error message and fail out. The close could boost the performance significant-
ing software. function is called when the device is ly and provide a higher overall hash rate.
For the Linux driver, you must released from the relay program. Another improvement that could
implement a handful of specific func- However, since we only check the self- further optimize this design is to have
tions and link them to the Linux kernel test results in the open function, there dedicated firmware. Our current
for correct operation. When the driver is nothing to do in the close function. design is running Ubuntu Linux 12.04,
is loaded a specific initialization func- The read function looks at the data which has many unnecessary process-
tion runs, preparing the system for buffer and determines which port the es running concurrently with the
interaction with the hardware. In this user is reading, and it then gets the Bitcoin program, like SSH. It is a
function, we first confirm that the data from the mining core and passes waste of the board’s resources to run
memory address to which the mining it back. The write function determines these processes while Bitcoin is run-
core is tied is available for use, then which register the user is writing to ning. In a future build, we would elim-
reserve the address. Unlike a bare- and passes the data to the mining core. inate these processes by running our
bones system, Linux uses a virtual The final component of our system own custom firmware dedicated to
memory address scheme, which means is a small relay program to pass work only Bitcoin tasks.
22 Xcell Journal Third Quarter 2013
Вам также может понравиться
- Overview & Whitepaper: A Defi Coin With Accounting ProtocolДокумент19 страницOverview & Whitepaper: A Defi Coin With Accounting ProtocolMarvie Longgos100% (1)
- Ethereum Concise: Ethereum for Beginners: The Basics on History, Present and Future, on Ethereum and Ethereum Classic, Ether, Ethereum Tokens, DApps, Smart Contracts, and Ethereum WalletsОт EverandEthereum Concise: Ethereum for Beginners: The Basics on History, Present and Future, on Ethereum and Ethereum Classic, Ether, Ethereum Tokens, DApps, Smart Contracts, and Ethereum WalletsОценок пока нет
- Understanding the Basics About Bitcoin & Other Cryptocurrencies, the Beginner’s 101 Guide - An Introductory Explanation for Beginners Part 1 the First Most Comprehensive Book to Understanding Cryptocurrency With Step-By-Step Instructions to Get StartedОт EverandUnderstanding the Basics About Bitcoin & Other Cryptocurrencies, the Beginner’s 101 Guide - An Introductory Explanation for Beginners Part 1 the First Most Comprehensive Book to Understanding Cryptocurrency With Step-By-Step Instructions to Get StartedОценок пока нет
- The Bitcoin Genesis:: Bitcoin and Cryptocurrency TechnologiesMining, Investing, Trading Through Time.От EverandThe Bitcoin Genesis:: Bitcoin and Cryptocurrency TechnologiesMining, Investing, Trading Through Time.Оценок пока нет
- Bitcoin Guide For Beginners: Bitcoin Trading and Mining Made EasyОт EverandBitcoin Guide For Beginners: Bitcoin Trading and Mining Made EasyОценок пока нет
- Mastering LiteCoin: A Beginner's Guide to Start Making Money with LiteCoinОт EverandMastering LiteCoin: A Beginner's Guide to Start Making Money with LiteCoinОценок пока нет
- Navigating the Materials World: A Guide to Understanding Materials BehaviorОт EverandNavigating the Materials World: A Guide to Understanding Materials BehaviorОценок пока нет
- Bitcoin: Strategies to Make Money with Bitcoin: Bitcoin Investing SeriesОт EverandBitcoin: Strategies to Make Money with Bitcoin: Bitcoin Investing SeriesОценок пока нет
- DeadwaxДокумент114 страницDeadwaxbonifax1Оценок пока нет
- Stable Money: What we can learn from Bitcoin, Libra, and Co.От EverandStable Money: What we can learn from Bitcoin, Libra, and Co.Оценок пока нет
- 2010 Topps Baseball Card ChecklistДокумент5 страниц2010 Topps Baseball Card ChecklistGeoff ScottОценок пока нет
- Ethereum: A Comprehensive Guide For Ethereum And How To Make Money With ItОт EverandEthereum: A Comprehensive Guide For Ethereum And How To Make Money With ItОценок пока нет
- How to Buy, Sell and Trade Bitcoin: A guide to getting into bitcoinОт EverandHow to Buy, Sell and Trade Bitcoin: A guide to getting into bitcoinОценок пока нет
- Bitcoin: Beginner's Simplified Guide to Make Money with Bitcoin: Bitcoin Investing Series, #1От EverandBitcoin: Beginner's Simplified Guide to Make Money with Bitcoin: Bitcoin Investing Series, #1Оценок пока нет
- Bitcoin Beginners Bible: How You Can Profit from Trading and Investing in Bitcoin By Stephen SatoshiОт EverandBitcoin Beginners Bible: How You Can Profit from Trading and Investing in Bitcoin By Stephen SatoshiОценок пока нет
- NFT Creation Explained Non Fungible Tokens The Works Inside and Out.: Digital money, Crypto Blockchain Bitcoin Altcoins Ethereum litecoin, #1От EverandNFT Creation Explained Non Fungible Tokens The Works Inside and Out.: Digital money, Crypto Blockchain Bitcoin Altcoins Ethereum litecoin, #1Оценок пока нет
- The Big Directory of Cryptocurrencies: What You Should Know Before Investing in Alternative Cryptocurrencies - The 30 Most Important Cryptocurrencies Besides of BitcoinОт EverandThe Big Directory of Cryptocurrencies: What You Should Know Before Investing in Alternative Cryptocurrencies - The 30 Most Important Cryptocurrencies Besides of BitcoinОценок пока нет
- Piminer Raspberry Pi Bitcoin MinerДокумент18 страницPiminer Raspberry Pi Bitcoin MinerAdrian AdrОценок пока нет
- CryptocurrencyДокумент36 страницCryptocurrencyMohammed AdasОценок пока нет
- Bitcoin Mining PoolДокумент2 страницыBitcoin Mining Poolanonimous 1919Оценок пока нет
- www19 Cryptojacking PDFДокумент12 страницwww19 Cryptojacking PDFAndrew SqwОценок пока нет
- Raja Balwant Singh Engineering Technical Campus: BitcoinДокумент18 страницRaja Balwant Singh Engineering Technical Campus: Bitcoinshailaja kОценок пока нет
- The Mathematics of Bitcoin: Cyril Grunspan, Ricardo Pérez-MarcoДокумент9 страницThe Mathematics of Bitcoin: Cyril Grunspan, Ricardo Pérez-MarcoThamaraiОценок пока нет
- How To Invest in BitcoinДокумент15 страницHow To Invest in BitcoinOsereОценок пока нет
- Manual CryptoParty HandbookДокумент336 страницManual CryptoParty HandbookArkan AnimeОценок пока нет
- Bitcoin CleaningДокумент12 страницBitcoin CleaningkayoОценок пока нет
- BitCoin Under The HoodДокумент11 страницBitCoin Under The HoodSilky BabeОценок пока нет
- Rules and Terms of Exchange Rules and Terms of Exchange: MagnatuscomДокумент1 страницаRules and Terms of Exchange Rules and Terms of Exchange: MagnatuscomMessaoud amrouneОценок пока нет
- Keys To Bitcoin - Learn How Bitcoin Really WorksДокумент146 страницKeys To Bitcoin - Learn How Bitcoin Really WorksTamara NawotnyОценок пока нет
- Bank 2020 - Blockchain Powering The Internet of Value - Whitepaper PDFДокумент50 страницBank 2020 - Blockchain Powering The Internet of Value - Whitepaper PDFIvan ArroyoОценок пока нет
- 36 Vasek PDFДокумент9 страниц36 Vasek PDFGungaa JaltsanОценок пока нет
- Bitsclusive Bitcoin Trading For BeginnersДокумент31 страницаBitsclusive Bitcoin Trading For BeginnersDavid CharlesОценок пока нет
- Bitcoin A Definitive Guide For InvestorsДокумент12 страницBitcoin A Definitive Guide For InvestorsEstefaniaОценок пока нет
- Using The Bitcoin Transaction Graph To Predict The Price of BitcoinДокумент8 страницUsing The Bitcoin Transaction Graph To Predict The Price of BitcoinharshvОценок пока нет
- READMEДокумент12 страницREADMERoda RodaОценок пока нет
- Bitcoin Master FileДокумент21 страницаBitcoin Master FileJeevan ManojОценок пока нет
- Quantum One High-Level WhitepaperДокумент7 страницQuantum One High-Level WhitepaperRobert Mourey JrОценок пока нет
- Trainers Guide Specimen en PDFДокумент24 страницыTrainers Guide Specimen en PDFMohammed AldaffaieОценок пока нет
- FON4-T11 Hacking BlockchainДокумент37 страницFON4-T11 Hacking BlockchainYonatan PeñaОценок пока нет
- Bitcoin Probablistic PaymentsДокумент2 страницыBitcoin Probablistic PaymentsjhonОценок пока нет
- New Kenyan Currency Poster A3 Low ResolutionДокумент1 страницаNew Kenyan Currency Poster A3 Low ResolutionEliakim ShiunduОценок пока нет
- Blockchain Technology ExplainedДокумент2 страницыBlockchain Technology ExplainedMohak VelankarОценок пока нет
- The Cryptocurrency WalletДокумент3 страницыThe Cryptocurrency WalletElenaОценок пока нет
- Bitcoin Mining Using Raspberry Pi PDFДокумент20 страницBitcoin Mining Using Raspberry Pi PDFarieza.perdhana8233Оценок пока нет
- C23 Cryptocurrencies Investment, Money, or Gamble AДокумент20 страницC23 Cryptocurrencies Investment, Money, or Gamble Avenkata muraliОценок пока нет
- CryptoassetsДокумент49 страницCryptoassetsWeimingОценок пока нет
- Work Home - All DocumentДокумент94 страницыWork Home - All Documentnjau njeriОценок пока нет
- The Bitcoin Brain Drain: A Short Paper On The Use and Abuse of Bitcoin Brain WalletsДокумент9 страницThe Bitcoin Brain Drain: A Short Paper On The Use and Abuse of Bitcoin Brain WalletsmonicaОценок пока нет
- The Requested URL Was Rejected. Please Consult With Your Administrator. Your Support ID Is: 2932946450064200471Документ1 страницаThe Requested URL Was Rejected. Please Consult With Your Administrator. Your Support ID Is: 2932946450064200471boonyongchiraОценок пока нет
- IRENA Planning For The Renewable Future 2017Документ136 страницIRENA Planning For The Renewable Future 2017Rene CantorОценок пока нет
- How To Create A Project For A Simple UClinux Ready MicroBlaze 4.0 Design On XPS (Xilinx Platform Studio) For Spartan-3EДокумент6 страницHow To Create A Project For A Simple UClinux Ready MicroBlaze 4.0 Design On XPS (Xilinx Platform Studio) For Spartan-3EEdison EnriquezОценок пока нет
- How To Create A Project For A Simple UClinux Ready MicroBlaze 4.0 Design On XPS (Xilinx Platform Studio) For Spartan-3EДокумент13 страницHow To Create A Project For A Simple UClinux Ready MicroBlaze 4.0 Design On XPS (Xilinx Platform Studio) For Spartan-3EIvan RomoОценок пока нет
- Quotation - PCB - Artix7Документ1 страницаQuotation - PCB - Artix7Edison EnriquezОценок пока нет
- 3Документ3 страницы3Edison EnriquezОценок пока нет
- Propuesta de Investigación: Desarrollo de Un Sistema Multiplatafoma Con Reconfigurar Parcial Dinámica en FPGAs (Borrador)Документ4 страницыPropuesta de Investigación: Desarrollo de Un Sistema Multiplatafoma Con Reconfigurar Parcial Dinámica en FPGAs (Borrador)Edison EnriquezОценок пока нет
- Propuesta de Maestria (Borrador)Документ4 страницыPropuesta de Maestria (Borrador)Edison EnriquezОценок пока нет
- Surtec 680: Protection UpgradedДокумент7 страницSurtec 680: Protection Upgradedyudhien4443Оценок пока нет
- Systemd CheatsheetДокумент1 страницаSystemd Cheatsheetzaffa11Оценок пока нет
- DevOps For VMware Administrators (VMware Press Technology) - 1-321Документ321 страницаDevOps For VMware Administrators (VMware Press Technology) - 1-321mailboxrohitsharma100% (1)
- Cs Acrovyn CatalogueДокумент83 страницыCs Acrovyn CatalogueBoboc AndreiОценок пока нет
- NE5521Документ9 страницNE5521Carlos TibussiОценок пока нет
- WAHLER Imagebroschuere SERIE enДокумент16 страницWAHLER Imagebroschuere SERIE ensagarpatel337Оценок пока нет
- Group 14 : Strainers, Traps, Fine-Mesh Filters Filling Device For Methanol Drain DeviceДокумент3 страницыGroup 14 : Strainers, Traps, Fine-Mesh Filters Filling Device For Methanol Drain DeviceLPG Equipment Consulting and ServicesОценок пока нет
- 30 StabilizersДокумент29 страниц30 StabilizersnjileoОценок пока нет
- Difference Between Forging and CastingДокумент2 страницыDifference Between Forging and CastingMOHAMMAD ALIОценок пока нет
- Cat Fines Presentation SlidesДокумент48 страницCat Fines Presentation SlidescaptkcОценок пока нет
- ChemicalEq DroppersДокумент13 страницChemicalEq DroppersUtkarsh SharmaОценок пока нет
- Open IVДокумент84 страницыOpen IVSokr AbdoОценок пока нет
- How Iso 27001 Compliance Is Impossible Without Privileged Management Technical Brief 17076Документ8 страницHow Iso 27001 Compliance Is Impossible Without Privileged Management Technical Brief 17076George VardangalosОценок пока нет
- Civil & Environmental Engineering: Dept. Report October 2002Документ40 страницCivil & Environmental Engineering: Dept. Report October 2002Leonardo HernandezОценок пока нет
- Application of Neutralization TitrationsДокумент21 страницаApplication of Neutralization TitrationsAsuncion Thea50% (2)
- Chemistry Lab 2 Flame TestsДокумент7 страницChemistry Lab 2 Flame Testshpcoutinho36Оценок пока нет
- CRISC BrochureДокумент2 страницыCRISC BrochureSpipparisОценок пока нет
- Basic Tanker Training (Oil, Chemical and Liquefied Gas Tanker)Документ487 страницBasic Tanker Training (Oil, Chemical and Liquefied Gas Tanker)Abdul Hafiz67% (3)
- WPH02 01 Que 20160120Документ24 страницыWPH02 01 Que 20160120Omar HashemОценок пока нет
- Iam MicroprojectДокумент2 страницыIam MicroprojectGabber IsbackОценок пока нет
- Technical Specification of Stay InsulatorДокумент11 страницTechnical Specification of Stay Insulatorraj_stuff006Оценок пока нет
- I20 Key Features Technical Specifications: DimensionsДокумент4 страницыI20 Key Features Technical Specifications: Dimensionsvaibhavsaini88Оценок пока нет
- Features: Self Reset Auxiliary Flag Relay - Two ElementДокумент3 страницыFeatures: Self Reset Auxiliary Flag Relay - Two ElementbledmikifrОценок пока нет
- IRFP240Документ8 страницIRFP240Hugo JimenezОценок пока нет
- Computer Graphics - Lesson PlanДокумент15 страницComputer Graphics - Lesson PlansoniadrallОценок пока нет
- MANSAVER Catalog PDFДокумент155 страницMANSAVER Catalog PDFDejanОценок пока нет
- 14 Upgrading of Safety Measures in The Arlberg Railway TunnelДокумент10 страниц14 Upgrading of Safety Measures in The Arlberg Railway TunnelvijyantbОценок пока нет
- C Aj 1609Документ2 страницыC Aj 1609vhin84Оценок пока нет
- Electrostatic Powder PaintingДокумент9 страницElectrostatic Powder PaintingfirdausОценок пока нет