Академический Документы
Профессиональный Документы
Культура Документы
Cybersecurity Systems Management in Aviation
Загружено:
Saim TeamОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Cybersecurity Systems Management in Aviation
Загружено:
Saim TeamАвторское право:
Доступные форматы
Cybersecurity Systems Management in Aviation
Cybersecurity Systems Management in Aviation
1. Information security: overview - 1
Cybersecurity Systems Management in Aviation
What is information security?
“Security is a process, not a product” - Bruce Schneier
“Security is a form of protection where a separation is created between the assets
and the threat. This includes but is not limited to the elimination of either the
asset or the threat” – OSSTMM (Open Source Security Testing Methodology
Manual)
“Information security (infosec) is the practice of protecting information by mitigating
information risks.
It typically involves preventing or at least reducing the probability of
unauthorized/inappropriate access, use, disclosure, disruption,
deletion/destruction, corruption, modification, inspection, recording or devaluation.
It may also involve reducing the adverse impacts of incidents. Information may take
any form, e.g. electronic or physical, tangible (e.g. paperwork) or intangible (e.g.
knowledge).” - http://en.wikipedia.org/wiki/Information_security
1. Information security: overview - 2
Cybersecurity Systems Management in Aviation
CIA triad
Information security's primary focus is the balanced protection of the confidentiality,
integrity and availability of data (also known as the CIA triad):
Confidentiality assumes that information is made available only to people and
systems on a “need-to-know” basis. In other words, unauthorized access,
intentional or accidental, must be prevented. Confidentiality can be provisioned
through encryption and the use of access controls.
The concept of integrity requires the detection and elimination of any data that
suffered an unauthorized modification.
The information also needs to be made available at all times, since limited access
to data may have a similar impact to the loss of integrity.
More: http://www.forcepoint.com/cyber-edu/cia-triad
1. Information security: overview - 3
Cybersecurity Systems Management in Aviation
CIA triad
The opposites of the CIA Triad is DAD
(Disclosure, Alteration and Destruction):
Disclosure – Someone not
authorized gets access to your
information.
Alteration – Your data has been
changed.
Destruction – Your Data or Systems
has been Destroyed or rendered
inaccessible.
1. Information security: overview - 4
Cybersecurity Systems Management in Aviation
CIA triad vs. OSSTMM Operation Controls
The CIA triad Operation Controls
Confidentiality
Privacy
Confidentiality
Authentication
Resilience
Integrity
Integrity Non-repudiation
Subjugation
Continuity
Availability Indemnification
Alarm
1. Information security: overview - 5
Cybersecurity Systems Management in Aviation
OSSTMM interactive controls
Authentication involves the validation of credentials through a process of
identification and authorization
Indemnification involves a contract between the asset's owner and its
interacting parties, in form of legal repercussions in case the posted rules are
not followed; these actions may come as a result of public legislative protection
or from third parties
Resilience covers the interactions to maintain the protection of assets in the event
of corruption and failure
Subjugation assures that all interactions with the assets follow a defined
process; this covers the liability of loss from the interacting party and limits their
choice of interactions
Continuity covers all interactions meant to assure the assets' availability
1. Information security: overview - 6
Cybersecurity Systems Management in Aviation
OSSTMM defensive operations
Non-repudiation prevents all parties from denying their roles in any interactions
Confidentiality insures the assets' availability only to those authorized parties
Privacy assumes that the means to access the assets are known only by the
authorized parties and cannot be shared outside their circle
Integrity assures that the interacting parties can detect any changes to the
assets
Alarm controls the notification of past and present interactions
1. Information security: overview - 7
Cybersecurity Systems Management in Aviation
Cryptographic systems
Useful for all objectives of information
security: confidentiality, integrity,
and availability
Symmetric-key cryptosystem
– same key is used for encryption
and decryption
– system with 1000 users requires
499,500 keys
– each pair of users requires a
different key
Public-key cryptosystem
– separate keys for encryption and
decryption
– system with 1000 users requires
2000 keys
– each individual user has exactly
two keys
1. Information security: overview - 8
Cybersecurity Systems Management in Aviation
Digital signatures: confidentiality
Electronic equivalent of handwritten
signatures
Handwritten signatures are hard to forge
Electronic information is easy to
duplicate
Digital signatures using public key
encryption
– Bob uses his private key to “sign”
a message
– Alice verifies signature using
Bob’s public key
Data authentication provided by digital
signatures
1. Information security: overview - 9
Cybersecurity Systems Management in Aviation
Digital signatures: Authentication
Alice wants to send message M to Bob
– uses Bob’s public key to encrypt
M
Bob uses his private key to decrypt M
– only Bob has key
– no one else can decipher M
Identification provided by public key
encryption
But… anyone can send message to Bob
using his public key
– how are we sure the message
came from Alice?
1. Information security: overview - 10
Cybersecurity Systems Management in Aviation
Digital signatures: Authentication
Alice wants assurance of real-time communication
Bob tries to provide assurance by digital signature
Alice is assured message originated from Bob
– digital signatures provide data origin authentication
– But … Eve can intercept signature and use it to authenticate herself as Bob at
– any later time
Signed challenge
– Alice sends random number (a challenge) to Bob
– Bob replies with challenge encrypted with signature
User authentication provided by signed challenges
– combination of digital signature and unpredictability of Alice's random
number challenge
1. Information security: overview - 11
Cybersecurity Systems Management in Aviation
Certification authority: Integrity
A third party trusted by all users that creates, distributes, revokes, & manages
certificates
Certificates bind users to their public keys
For example, if Alice wants to obtain Bob's public key
– she retrieves Bob's certificate from a public directory
– she verifies the CA's signature on the certificate itself
– if signature verifies correctly, she has assurance from the trusted CA this really
is Bob's public key
– she can use Bob's public key to send confidential information to Bob or to
verify Bob's signatures, protected by the assurance of the certificate
Integrity is provided by the certification authority
1. Information security: overview - 12
Cybersecurity Systems Management in Aviation
Survey of security issues (2004)
Rank Issue Description
1 Top management support
2 User awareness training & education
3 Malware (e.g., viruses, Trojans, worms)
4 Patch management
5 Vulnerability & risk management
...
9 Internal threats
10 Business continuity & disaster preparation
11 Low funding & inadequate budgets
...
14 Security training for IT staff
...
25 Standards issues
1. Information security: overview - 13
Cybersecurity Systems Management in Aviation
Terminology
1. Information security: overview - 14
Cybersecurity Systems Management in Aviation
Components of Information Security
1. Information security: overview - 15
Cybersecurity Systems Management in Aviation
NSTISSC Security Model
1. Information security: overview - 16
Cybersecurity Systems Management in Aviation
Computer as subject & object of an attack
1. Information security: overview - 17
Cybersecurity Systems Management in Aviation
Balancing Information Security & Information Access
1. Information security: overview - 18
Cybersecurity Systems Management in Aviation
Approaches to Information Security Implementation
1. Information security: overview - 19
Cybersecurity Systems Management in Aviation
SDLC Methodology – applied to Information security systems, too
1. Information security: overview - 20
Вам также может понравиться
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021От EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021Оценок пока нет
- Cyber Security Lecture Notes 01Документ19 страницCyber Security Lecture Notes 01Sampath Darshana100% (1)
- UNIT - I & II - 3R-Cryptography-Lectures - 2021-22 - VSMДокумент133 страницыUNIT - I & II - 3R-Cryptography-Lectures - 2021-22 - VSMpubgОценок пока нет
- CNS - Unit 1Документ25 страницCNS - Unit 1alameenОценок пока нет
- Information SecurityДокумент17 страницInformation SecuritymahmoodghanemОценок пока нет
- Introduction To Computer SecurityДокумент49 страницIntroduction To Computer Securityshantanu YadavОценок пока нет
- Is - Lecture 1Документ49 страницIs - Lecture 1Tayyab AslamОценок пока нет
- Lectures 1 MergedДокумент154 страницыLectures 1 MergedDiana IsmailОценок пока нет
- UNIT - 1 NotesДокумент21 страницаUNIT - 1 NotesSushant YadavОценок пока нет
- BSC Year1sem1 Information SecurityДокумент27 страницBSC Year1sem1 Information SecurityBiyegon kОценок пока нет
- Security C 1 Part 1Документ20 страницSecurity C 1 Part 1keyeronОценок пока нет
- Chapter OneДокумент42 страницыChapter OneMagarsa BedasaОценок пока нет
- Lesson 3 SecurityДокумент31 страницаLesson 3 Securitydawit gebreyohansОценок пока нет
- Computer SecurityДокумент18 страницComputer Securitytai pawarОценок пока нет
- Lecture 1 Introduction of AptДокумент43 страницыLecture 1 Introduction of AptNurdin YussufОценок пока нет
- Network Security InfiДокумент13 страницNetwork Security Infivice pyОценок пока нет
- Module 1 PPT 2Документ19 страницModule 1 PPT 2VATSAL SINGH 21BCE10011Оценок пока нет
- Information Assurance and Security: ITPC23 - SUMMER 2021-2022Документ18 страницInformation Assurance and Security: ITPC23 - SUMMER 2021-2022eliza marie luisОценок пока нет
- 1 Introduction 1Документ46 страниц1 Introduction 1Srikesh NairОценок пока нет
- Adobe Scan Apr 14, 2023Документ20 страницAdobe Scan Apr 14, 2023Roma SoniОценок пока нет
- Information Sec For StudentДокумент113 страницInformation Sec For Studentmuumina aadamОценок пока нет
- BIS 321 Chapter One Part OneДокумент18 страницBIS 321 Chapter One Part OneEyob TemesgenОценок пока нет
- Unit-1 - Part-IДокумент8 страницUnit-1 - Part-IRam Prasad Reddy SadiОценок пока нет
- CMP 318 Network Security IssuesДокумент144 страницыCMP 318 Network Security IssuesEYIMOFE AYOMIDELE PINNICK Jr.Оценок пока нет
- SLM - Unit 01Документ22 страницыSLM - Unit 01SureshОценок пока нет
- Ias Quiz 1 Lesson 1Документ3 страницыIas Quiz 1 Lesson 1Iñakie PulusanОценок пока нет
- ECEG-6530 Computer (And Network) Security: Introduction and Course OverviewДокумент32 страницыECEG-6530 Computer (And Network) Security: Introduction and Course OverviewYekeber AddisОценок пока нет
- Mobile SecurityДокумент3 страницыMobile SecurityRodjean SimballaОценок пока нет
- Lecture 1 - Information Security BasicsДокумент8 страницLecture 1 - Information Security BasicsI careОценок пока нет
- Information Security: Dr. Pranita UpadhyayaДокумент35 страницInformation Security: Dr. Pranita UpadhyayaMANOJОценок пока нет
- CH 1Документ45 страницCH 1Rossy100% (1)
- Chapter One Introduction To Information Security Definition of Information System SecurityДокумент15 страницChapter One Introduction To Information Security Definition of Information System SecurityGetnete degemuОценок пока нет
- Cryptography and Network Security Overview & Chapter 1Документ6 страницCryptography and Network Security Overview & Chapter 1Natural MicОценок пока нет
- HND - SEC - W1 - Introduction To IT SecurityДокумент15 страницHND - SEC - W1 - Introduction To IT SecurityAnojan AnojОценок пока нет
- Ecommerce SecurityДокумент60 страницEcommerce SecurityHarshithОценок пока нет
- Lec 13Документ15 страницLec 13Aqsa gulОценок пока нет
- Practical-6: Aim: Explain Confidentiality, Integrity and Availability. ConfidentialityДокумент4 страницыPractical-6: Aim: Explain Confidentiality, Integrity and Availability. ConfidentialityAnonymous aQxekTRОценок пока нет
- Chapter 1fundamental of Software SecurityДокумент7 страницChapter 1fundamental of Software SecurityhaileОценок пока нет
- Introduction To Computer Security: Unit 1Документ39 страницIntroduction To Computer Security: Unit 1Sukrit KumarОценок пока нет
- Chapter-1-Introduction and Security Trends NotesДокумент69 страницChapter-1-Introduction and Security Trends NotesVrushaliОценок пока нет
- Is Unit1Документ38 страницIs Unit1SaniyaОценок пока нет
- Unit - I: Attacks On Computers and Computer Security: Introduction, The Need of SecurityДокумент14 страницUnit - I: Attacks On Computers and Computer Security: Introduction, The Need of SecurityhafeezaОценок пока нет
- Introduction To Cyber SecurityДокумент11 страницIntroduction To Cyber SecurityDeepika SharmaОценок пока нет
- Unit 1aДокумент38 страницUnit 1achimdesa infosaОценок пока нет
- Module 1-Introduction: No. Detailed Contents HrsДокумент43 страницыModule 1-Introduction: No. Detailed Contents HrsBhavya DedhiaОценок пока нет
- DIGI112 - ICT-SecurityДокумент86 страницDIGI112 - ICT-SecuritygОценок пока нет
- Chapter 1 Introduction and Security TrendДокумент10 страницChapter 1 Introduction and Security TrendNARESH BADWEОценок пока нет
- Information Security: Security Tools Presented By: Dr. F. N MusauДокумент23 страницыInformation Security: Security Tools Presented By: Dr. F. N Musausteng5050Оценок пока нет
- Lecture 2 - Introduction To SecurityДокумент33 страницыLecture 2 - Introduction To SecurityIrfan NaufalОценок пока нет
- Computer SecurityДокумент34 страницыComputer SecurityInshal AyazОценок пока нет
- Introduction To Computer SecurityДокумент39 страницIntroduction To Computer Securitypiyush20patel0% (1)
- NS Yst Em: Gagandeep AP in CSE Deptt. PPIMT, HisarДокумент69 страницNS Yst Em: Gagandeep AP in CSE Deptt. PPIMT, HisarAnkur MittalОценок пока нет
- Information Security PresentatationДокумент19 страницInformation Security PresentatationMuhammad Ather AmeenОценок пока нет
- Week 6 - WatermarkДокумент146 страницWeek 6 - Watermarkshailesh karthikОценок пока нет
- INFORMATION SECURITY HandoutsДокумент63 страницыINFORMATION SECURITY HandoutsKumkumo Kussia KossaОценок пока нет
- IT SecurityДокумент6 страницIT SecurityRicky PrasojoОценок пока нет
- IM Information SecurityДокумент82 страницыIM Information SecurityAngelica AngelesОценок пока нет
- Security in E-Commerce: Monir ArabjafariДокумент59 страницSecurity in E-Commerce: Monir ArabjafariChandra ShekarОценок пока нет
- Chapter One: Introduction To Information Assurance and Security (ITEC4143)Документ19 страницChapter One: Introduction To Information Assurance and Security (ITEC4143)Dires NegashОценок пока нет
- All NS Slides CombinedДокумент350 страницAll NS Slides CombinedNehal KhanОценок пока нет
- Project Report On Online Class SystemДокумент91 страницаProject Report On Online Class Systemapurva singh100% (1)
- Kodu Brochure CurriculumДокумент15 страницKodu Brochure CurriculumConker WorldОценок пока нет
- 20 D3DДокумент6 страниц20 D3Demre ozayvazОценок пока нет
- Cloud Native Application Security in USAДокумент2 страницыCloud Native Application Security in USAcyberultronОценок пока нет
- QSL9 G3 PDFДокумент2 страницыQSL9 G3 PDFMarcos HernandezОценок пока нет
- Shri Ram Institute of Science Technology Jabalpur: Course File ON Internal Combution Engine (SUB. CODE: 604)Документ8 страницShri Ram Institute of Science Technology Jabalpur: Course File ON Internal Combution Engine (SUB. CODE: 604)Risika ChoukseОценок пока нет
- CBS-154 Proficy HMI SCADA iFIX Fundamentals PDFДокумент2 страницыCBS-154 Proficy HMI SCADA iFIX Fundamentals PDFrmorenodx4587Оценок пока нет
- Lecture 2, OSДокумент8 страницLecture 2, OSMaria Akter LuthfaОценок пока нет
- Supra Ecu Pinout List PDFДокумент1 страницаSupra Ecu Pinout List PDFGuillermo AlfaroОценок пока нет
- Assignment Individual (Innovation)Документ11 страницAssignment Individual (Innovation)Nurul NasuhaОценок пока нет
- Assignment 2Документ11 страницAssignment 2nan.sayan30Оценок пока нет
- Gis User GuideДокумент2 страницыGis User GuideAniket GavhankarОценок пока нет
- Some of The Most Commonly Used SAPДокумент5 страницSome of The Most Commonly Used SAPnaveenraj111Оценок пока нет
- Overhaul Manual: O-360 and IO-360 Series EnginesДокумент9 страницOverhaul Manual: O-360 and IO-360 Series EngineswendyrunawaywmeОценок пока нет
- QuestionsДокумент8 страницQuestionsjustice100% (1)
- SRS Sample (New Capstone - IS)Документ188 страницSRS Sample (New Capstone - IS)Mở Thế GiớiОценок пока нет
- Control Design User Manual - LabVIEW 2020-12-29 18-13-06Документ251 страницаControl Design User Manual - LabVIEW 2020-12-29 18-13-06Captain HendoОценок пока нет
- DevSecOps Lecture Day1 PresentationДокумент8 страницDevSecOps Lecture Day1 PresentationSudipta Kr BanerjiОценок пока нет
- LumaxДокумент1 страницаLumaxpawan1501Оценок пока нет
- AUTOSAR SWS PlatformHealthManagementДокумент30 страницAUTOSAR SWS PlatformHealthManagementRobert FerenczОценок пока нет
- Power Curves: Hi Idle: Maximum Revolutions of The Engine With No LoadДокумент18 страницPower Curves: Hi Idle: Maximum Revolutions of The Engine With No Loadmijael1393100% (4)
- First Second Final Cold Hot: Description Torque Specs Clearance Item NOДокумент2 страницыFirst Second Final Cold Hot: Description Torque Specs Clearance Item NOBert De BorjaОценок пока нет
- SIL 2 Certificate For Complete ValveДокумент8 страницSIL 2 Certificate For Complete ValveKhanh PhamОценок пока нет
- Dynamic Application Security Testing1Документ25 страницDynamic Application Security Testing1api-561990701Оценок пока нет
- Inspection Test Plan (Itp) at Site: Natural Gas Transportation Development Project - Siak RiauДокумент6 страницInspection Test Plan (Itp) at Site: Natural Gas Transportation Development Project - Siak Riauanang_priОценок пока нет
- c8-r3: Advanced Software Engineering Note: 1. 2.Документ2 страницыc8-r3: Advanced Software Engineering Note: 1. 2.vikassonwalОценок пока нет
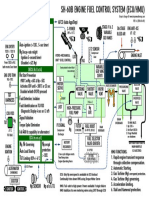
- SH 60b t700 Ge 401c Ecu Hmu Fuel ControlДокумент1 страницаSH 60b t700 Ge 401c Ecu Hmu Fuel ControlFrantišek KovaříkОценок пока нет
- Hotel WebsiteДокумент87 страницHotel WebsiteFreeProjectz.com78% (9)
- Java Applet NotesДокумент4 страницыJava Applet NotesSayani ChandraОценок пока нет
- Loop Checking Basic ProcedureДокумент4 страницыLoop Checking Basic ProcedureHamada Elsharawy100% (1)