Академический Документы
Профессиональный Документы
Культура Документы
Ic3 Correlation Lesson
Загружено:
Sanny Jean Rosa-utОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Ic3 Correlation Lesson
Загружено:
Sanny Jean Rosa-utАвторское право:
Доступные форматы
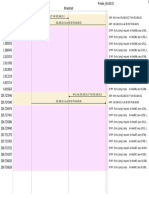
Century 21 Jr.
: Computer Applications and Input Technologies
IC3 Correlation
(Internet and Core Computing Certification)
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
Module 1: Computing Fundamentals
Objective 1.1 Identify types of computers, how they process
information and how individual computers interact
with other computing systems and devices.
1.1.1 Categorize types of computers based on their size, power, Lessons 1 and 78 (pp. 4–10,
and purpose. 315–320)
1.1.2 Identify types of microcomputers. Lesson 1 (pp. 4–10)
1.1.3 Identify other types of computing devices. Lessons 1, 56, and 57 (pp. 4–
10, 188–195, 195–203)
1.1.4 Identify the role of the central processing unit. Lesson 1 (pp. 4–10)
1.1.5 Identify how the speed of the microprocessor is measured. See Web Reading 2
1.1.6 Identify the role of types of memory and storage and Lesson 1–partial (pp. 4–10)
purpose of each, including RAM, ROM, and CD ROMs.
1.1.7 Identify concepts related to how memory is measured, See Web Reading 2
including bits, bytes, and megabytes.
1.1.8 Identify the flow of information between storage devices Lessons 1 and 5 (pp. 4–10,
(such as floppy or hard disks) to the microprocessor and 35–38)
RAM in relation to everyday computer operations.
1.1.9 Identify the differences between large systems and desktop Lesson 1 (pp. 4–10)
computers and appropriate uses for large vs. small systems.
1.1.10 Identify that computers integrate into larger systems in a Chapter 9 Supplemental
variety of ways. Activity (on Web)
1.1.11 Identify how computers share data, files, hardware, and Lessons 1, 66, and 83 (pp. 4–
software. 10, 262–268, 340–342); also
Chapter 9 Supplemental
Activity (on web)
Objective 1.2 Identify the functions of computer hardware
components.
1.2.1 Identify the types and purposes of external computer Lesson 1 (pp. 4–10)
components, including standard input and output devices.
1.2.2 Identify the types and purposes of internal computer Lessons 1, 56, 57, and 65 (pp.
components. 4–10, 188–194, 195–203,
255–262)
1.2.3 Identify the types and purposes of specialized input Lessons 1, 3, 66, 68, and 78
devices (e.g., digital cameras and touch screens). (pp. 4–10, 262–268, 277–279,
315–320)
1.2.4 Identify the types and purposes of specialized output See Web Reading 6
devices (e.g., projectors).
1.2.5 Identify the types and purposes of storage media (e.g., Lesson 5 (pp. 35–38)
DVDs and network drives).
1.2.6 Identify ports used to connect input and output devices to a Lesson 68 (pp. 277–279); also
3
C21 Jr. IC Correlation 1
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
computer (e.g., USB ports and Ethernet ports). Chapter 9 Supplemental
Activity (on Web)
1.2.7 Identify how hardware devices are installed on a computer Lesson 65 (pp. 255–262)
system.
Objective 1.3 Identify the factors that go into an individual or
organizational decision on how to purchase computer
equipment.
1.3.1 Identify criteria for selecting personal computers. See Web Reading 1
1.3.2 Identify factors that affect computer performance. See Web Reading1
1.3.3 Identify hardware and software considerations when See Web Reading 1
purchasing a computer
1.3.4 Identify other factors that go into decisions to purchase a See Web Reading 1
computer including warranties and support agreements.
Objective 1.4 Identify how to maintain computer equipment and
solve common problems relating to computer
hardware.
1.4.1 Identify how to protect computer hardware from theft or See Web Reading 4
damage.
1.4.2 Identify factors that can cause damage to computer See Web Reading 4
hardware or media (e.g., heat and humidity).
1.4.3 Identify how to protect computer hardware from See Web Reading 4
fluctuations in the power supply, power outages, and other
electrical issues..
1.4.4 Identify common problems associated with computer See Web Reading 4
hardware such as inoperable hardware devices.
1.4.5 Identify common problems that can occur if hardware is See Web Reading 4
not maintained properly.
1.4.6 Identify maintenance that can be performed routinely by See Web Readings 4 and 5
users such as cleaning and defragmenting hard drives.
1.4.7 Identify maintenance that should ONLY be performed by See Web Reading 4
experienced professionals.
1.4.8 Identify the steps required to solve computer-related See Web Reading 5
problems.
Objective 2.1 Identify how software and hardware work together to
perform computing tasks and how software is
developed and upgraded.
2.1.1 Identify how hardware and software interact. Lessons 2 and 67 (pp. 10–14,
276–277)
2.1.2 Identify simple terms and concepts related to the software See Web Reading 6
development process.
2.1.3 Identify issues relating to software upgrades such as the See Web Reading 6
pros and cons and methods to upgrade.
C21 Jr. IC3 Correlation 2
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
Objective 2.2 Identify different types of software, general concepts
relating to software categories, and the tasks to which
each type of software is most suited or not suited.
2.2.1 Identify fundamental concepts relating to word processing Lessons 4 and 57 (pp. 21–28,
and common uses for word-processing applications. 198–203)
2.2.2 Identify fundamental concepts relating to spreadsheets and Lesson 7 (pp. 45–49)
common uses for spreadsheet applications.
2.2.3 Identify fundamental concepts relating to presentation Lesson 103 (pp. 480–483)
software and common uses for presentation applications.
2.2.4 Identify fundamental concepts relating to databases and Lessons 115 and116 (pp. 557–
common uses for database applications. 559, 559–565)
2.2.5 Identify fundamental concepts relating to graphic and Lessons 64, 99, and 123 (pp.
multimedia programs and common uses for graphic and 248–255, 451–454, 603–609)
multimedia software.
2.2.6 Identify the types and purposes of different utility Lesson 13 (antivirus) (pp. 80–
programs. 84)
2.2.7 Identify other types of software. Lessons 56, 60, and 67
(pp.188–194, 214–220, 276–
277)
2.2.8 Identify how to select the appropriate application(s) for a See Web Readings 1 and 2
particular purpose, and problems that can arise if the
wrong software product is used for a particular purpose.
Objective 3.1 Identify what an operating system is and how it works,
and solve common problems related to operating
systems.
3.1.1 Identify the purpose of an operating system and the Lesson 2 (pp. 10–14)
difference between operating system and application
software.
3.1.2 Identify different operating systems including DOS, Lesson 2 (pp. 10–14)
Windows, and Macintosh.
3.1.3 Identify the difference between interacting with character- See Web Reading 5
based and graphical operating systems.
3.1.4 Identify the capabilities and limitations imposed by the Lesson 1, 123 (pp. 4–10, 603–
operating system. 609)
3.1.5 Identify and solve common problems related to operating Lesson 2 (pp. 10–14)
systems.
Objective 3.2 Manipulate and control the Windows desktop, files, and
disks.
3.2.1 Identify elements of the Windows desktop. Lessons 3 and 66 (pp. 14–21,
262–268)
3.2.2 Manipulate windows, such as minimizing windows. Lesson 3 (pp. 14–21)
3.2.3 Shut down, Logoff, and restart the computer. Lesson 2 (pp. 10–14)
3.2.4 Use the Windows Start menu and Taskbar. Lessons 2, 3, and 71 (pp. 10–
C21 Jr. IC3 Correlation 3
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
14, 14–21, 285–289)
3.2.5 Manipulate desktop folders and icons. Lessons 5, 6, 60, and 123, (pp.
35–39, 39–44, 214–220, 603–
609); also Chapter 2
Supplemental Activity,
Chapter 6 Supplemental
Activity (on Web)
3.2.6 Manage files using the Windows Explorer/File Manager Lessons 5, 6, and 9 (pp. 35–
39, 39–44, 55–58)
3.2.7 Identify precautions one should take when manipulating Lesson 9 (pp. 55–58)
files, including using standardized naming conventions.
3.2.8 Solve common problems associated with working with Lessons 5 and 64 (pp. 35–39,
files. 248–255)
Objective 3.3 Identify how to change system settings, install, and
remove software.
3.3.1 Display control panel. Lesson 56 (pp. 188–194)
Chapter1 Supplemental
Activity (on Web)
3.3.2 Identify different control panel settings. Lesson 56 (pp. 188–194); also
Chapter1 Supplemental
Activity (on Web)
3.3.3 Change simple control panel settings such as date and time Chapter 1 Supplemental
settings. Activity (on Web)
3.3.4 Display and update a list of installed printers. Lesson 4 (pp. 21–28
3.3.5 Identify precautions regarding changing system settings. See Web Reading 5
3.3.6 Install software including installing updates from online Lessons 57 and 60 (pp. 195–
sources. 203, 214–220)
3.3.7 Identify common problems associated with installing and See Web Reading 5
running applications.
Module 2: Key Applications
Objective 1.1 Be able to start and exit a Windows application and
utilize sources of online help.
1.1.1 Start a Windows application Lessons 3, 4, 7, 8, 9, 56, 57,
79, 90, and 92 (pp. 14–21,
21–28, 45–49, 50–54– 188–
194, 195–203, 321–323, 389–
393, 400–406)
1.1.2 Exit a Windows application. Lessons 3, 4, 7, 8, 9, 56, 57,
79, and 92 (pp. 14–21, 21–28,
45–49, 50–54– 188–194, 195–
203, 321–323, 400–406)
1.1.3 Identify and prioritize help resources, including online help Lesson 3 (pp. 14–21); also
C21 Jr. IC3 Correlation 4
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
within software and contacting a help desk. Chapter1 Supplemental
Activity (on Web)
1.1.4 Use various forms of automated help. Lessons 3 and 4 (pp. 14–21,
21,–28); also Chapter1
Supplemental Activity (on
Web)
Objective1.2 Identify common on-screen elements of Windows
applications, change application settings and manage
files within an application.
1.2.1 Identify on-screen elements common to Windows Lessons 3, 4, 7, 8, and 71 (pp.
applications (e.g., menus, toolbars, and document 13–21, 21–28, 45–49, 50–54,
windows) 285–289)
1.2.2 Display or hide toolbars. Lesson 4 (pp. 21–28)
1.2.3 Switch between open documents. Lesson 85 (pp. 356–361)
1.2.4 Change views. Lesson 85 (pp. 356–361)
1.2.5 Change magnification level. Lessons 3, 8, 64, and 90 (pp.
14–21, 50–54, 248–255, 389–
393)
1.2.6 Create files. Lessons 4, 7, and 61 (pp. 21–
28, 45–49, 221–226)
1.2.7 Open files within an application and from the Windows Lessons 4, 7, 8, 9, 71, and 121
desktop, identify file extension including .xls or .doc. (pp. pp. 21–28, 45–49, 50–54,
55–58, 285—289, 590–597)
1.2.8 Save files in specified locations/formats. Lessons 4, 7, 71, 84, 90, 121,
and 124 (pp. 21–28, 45–49,
285–289, 351–356, 389–393,
590–597, 609–613)
1.2.9 Close files Lessons 4, 7, and 8 (pp. 21–
28, 45–49, 50–54)
1.2.10 Identify and solve common problems relating to working Lesson 9 (pp. 55–58)
with files (e.g., product or version incompatibility)
Objective 1.3 Perform common editing and formatting functions.
1.3.1 Navigate around open files using scroll bars, keyboard Lessons 7, 59, 60, and 77 (pp.
shortcuts, etc. 45–49, 209–214, 214–220,
305–307); also Chapter 1
Supplemental Activity (on
Web)
1.3.2 Insert text and numbers in a file. Lessons 4, 7, 8, 60, 80, and 81
(pp. 21–28, 45–49, 50–54,
214–220, 324–327, 328–333)
1.3.3 Perform simple editing (e.g., cut, copy, and move Lessons 58, 59, 62, 73, 75, 76,
information). 81, 89, and 94 (pp. 204–209,
209–214, 227–233, 293–296,
299–302, 302–305, 328–333,
378–380, 410–414)
C21 Jr. IC3 Correlation 5
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
1.3.4 Use the Undo, Redo, and Repeat commands. Lesson 72–Voice (pp. 290–
293)
1.3.5 Find information. Lessons 8, 63, and 94 (pp. 50–
54, 234–239, 410–414)
1.3.6 Replace information. Lessons 94 and 118 (pp. 410–
414, 569–573); also Chapter
11 Supplemental Activity (on
Web)
1.3.7 Check spelling. Lessons 86 and 90 (pp. 361–
369, 389–393)
1.3.8 Perform simple text formatting. Lessons 60, 86. 99, and 100
(pp. 214–220, 361–369, 451–
454, 455–460); also Chapter
13 Supplemental Activity (on
Web)
1.3.9 Insert pictures in a file. Lessons 63, 65, 66, 100, 101,
and 107, also Chapter 7
Supplemental Activity (on
Web)
1.3.10 Modify pictures in a file. Lessons 63, 65, 66, 100, and
101 (pp. 234–239, 255–262,
262–268, 455–460, 461–465);
also Chapter 7 Supplemental
Activity (on Web)
1.3.11 Add drawn objects into a file, including creating and Lesson 63 (pp. 234–239)
modifying objects.
Objective 1.4 Perform common printing functions.
1.4.1 Format a document for printing. Lessons 4, 8, 59, 64, 77, 108,
110, and 120 (pp. 21–28, 50–
54, 2090214, 248–255, 305–
307, 502–505, 518–522, 578–
581)
1.4.2 Preview a file before printing. Lessons 8, 90, and 92 (pp. 50–
54, 389–393, 400–406); also
Chapter 2 Supplementary
Activity (on Web)
1.4.3 Print files, specifying common print options. Lessons 4, 8, 59, 64, 77, 108,
110, and 120 (pp. 21–28, 50–
54, 209–214, 248–255, 305–
307, 502–505, 518–522, 578–
581)
1.4.4 Manage printing and print jobs. Lessons 4 and 8 (pp. 21–28,
50–54)
1.4.5 Identify and solve common problems associated with See Web Reading 5
printing.
Objective 2.1 Be able to format text and documents including the
3
C21 Jr. IC Correlation 6
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
ability to use automatic formatting tools.
2.1.1 Identify on-screen formatting information, including 4, 16, 34, 38 (pp. 21–28, 99–
breaks, paragraph markers, etc. 101, 137–139, 150–151)
2.1.2 Select word, line, paragraph, or document. 62, 84 (pp. 227–233, 351–
356)
2.1.3 Change line and paragraph spacing. 62, 72, 84, 87 (pp. 227–233,
290–292, 351–356, 369–374)
2.1.4 Indent text. 87 (pp. 369–374)
2.1.5 Create and modify bulleted and numbered lists. 61, 88, 122 (pp. 221–226,
375–378, 598–602)
2.1.6 Use outline structure to format a document. 62, 86 (pp. 227–233, 361–
369)
2.1.7 Insert symbols/special characters. 41, 42, 43, 44, 45, 46, 47, 48,
49, 50 (pp. 156–157, 158–
159, 160–161, 162–163, 164–
165, 166,–167, 168–169, 170–
171, 172–173, 174–175)
2.1.8 Insert date and time. 78, 82, 92 (pp. 315–320, 334–
340, 400–406)
2.1.9 Insert, view, and print document comments. See Web Reading 8
2.1.10 Display the ruler. 86 (pp. 361–369)
2.1.11 Use tabs. 86, Chapter11 Supplemental
Activity (pp. 361–369)
2.1.12 Insert and delete a page break or section break. Ch6–apply, 87, 102 (pp. 241,
369–374, 466–470
2.1.13 Insert, modify, and format page numbers. 85 (pp. 356–361)
2.1.14 Create, modify, and format headers and footers. 85 (pp. 356–361)
2.1.15 Create, modify, and format footnotes and endnotes. 87 (pp. 369–374)
2.1.16 Apply borders and shading to text paragraphs. 100, Chapter13 Supplemental
Activity (pp. 455–460)
2.1.17 Create, modify, and apply styles. 85, 86, 87, 88, Chapter10
Supplemental Activity (pp.
356–361, 361–369, 369–374,
375–378)
2.1.18 Copy formatting (Format Painter). See Web Reading 8
2.1.19 Use language tools. 57, 70 (pp. 195–203, 283–
285)
2.1.20 Use track changes in a document. See Web Reading 8
2.1.21 Display document statistics See Web Reading 8
Objective 2.2 Be able to insert, edit, and format tables in a document.
2.2.1 Create a table. Lessons 95, 98, 106, and 115
(pp. 424–429, 441–443, 491–
495, 551–559); also Chapter
12 Supplemental Activity (o
Web)
C21 Jr. IC3 Correlation 7
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
2.2.2 Insert and edit data in a table. Lessons 95, 96, 97, 98, 115,
117, and 118 (pp. 424–429,
430–436, 436–440, 441–443,
551–559, 565–569, 569–573);
also Chapter 16 Supplemental
Activity (on Web)
2.2.3 Modify table structure. Lessons 95, 96, 97, and 117
(pp. 424–429, 430–436, 436–
440, 565–573)
2.2.4 Format tables. Lessons 95, 96, 97, 98, 117
(pp. 424–429, 430–436, 436–
440, 441–443, 565–573); also
Chapter12 Supplemental
Activity (on Web)
2.2.5 Sort data in a table. Lessons 98 and 119 (pp. 441–
443, 573–577)
Objective 3.1 Be able to modify worksheet data and structure and
format data in a worksheet.
3.1.1 Identify how a table of data is organized in a spreadsheet Lessons 7 and 109 (pp. 45–49,
513–517)
3.1.2 Select information with the keyboard and mouse including Lessons 109 and 112 (pp.
selecting rows, columns, and worksheets. 513–517, 527–531)
3.1.3 Insert and modify data. Lessons 7, 109, 111, and 112
(pp. 45–49, 513–517, 522–
526, 527–531)
3.1.4 Modify table structure. Lessons 110, 113, and 124,
(pp. 518–522, 531–537, 609–
613); also Chapter 15
Supplemental Activity (on
Web)
3.1.5 Identify and change number formats, including currency, Lesson 111 (pp. 522–526)
date and time, and percentage formats.
3.1.6 Apply borders and shading to cells. Lesson 110 (pp. 518–522)
3.1.7 Specify cell alignment (e.g., wrapping text within a cell). Lesson 113 (pp. 531–537)
3.1.8 Apply table AutoFormats. Chapter 12 Supplemental
Activity (on Web)
Objective 3.2 Be able to sort data, manipulate data using formulas
and functions and add and modify charts in a
worksheet.
3.2.1 Sort worksheet data. Lesson 113 (pp. 531–537)
3.2.2 Demonstrate an understanding of absolute versus relative Lessons 109 and 111 (pp.
cell addresses. 513–517, 522–526)
3.2.3 Insert arithmetic formulas into worksheet cells. Lesson 111 (pp. 522–526)
3.2.4 Demonstrate how to use common worksheet functions Lesson 111 (pp. 522–526)
( e.g., SUM, AVERAGE and COUNT).
C21 Jr. IC3 Correlation 8
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
3.2.5 Insert formulas that include worksheet functions into cells. Lesson 111 (pp. 522–526)
3.2.6 Modify formulas and functions. Lesson 111 (pp. 522–526)
3.2.7 Use AutoSum. Lesson 111 (pp. 522–526)
3.2.8 Identify common errors made when using formulas and Lessons 109 and 111 (pp.
functions. 513–517, 522–526)
3.2.9 Draw simple conclusions based on tabular data in a Lesson 113 (pp. 531–537)
worksheet.
3.2.10 Insert and modify charts in a worksheet. Lesson 114 (pp. 537–541);
also Chapter14 and Chapter15
Supplemental Activities (on
Web)
3.2.11 Be able to identify if a presented chart accurately Lesson 114 (pp. 537–541);
represents worksheet data shown in a table. also Chapter14 and Chapter15
Supplemental Activities (on
Web)
3.2.12 Identify appropriate chart types for presenting different Lesson 114 (pp. 537–541);
types of information. also Chapter14 and Chapter15
Supplemental Activities (on
Web)
Objective 4.1 Be able to create and format simple presentations.
4.1.1 Identify effective design principles for simple Lesson 103 (pp. 480–483)
presentations.
4.1.2 Manage slides (e.g., delete a slide). Lesson 106 (pp. 491–495)
4.1.3 Add information to a slide. Lessons 104, 105, and 107
(pp. 483–486, 487–491, 496–
502)
4.1.4 Change slide view. Lesson 104 (pp. 483–486)
4.1.5 Change slide layout. Lessons 105 and 106 (pp.
487–491, 491–495)
4.1.6 Modify a slide background. Lesson 105 (pp. 487–491)
4.1.7 Assign transitions to slides. See Web Reading 8
4.1.8 Change the order of slides in a presentation. Lesson 107 (pp. 496–502)
4.1.9 Create different output elements (speaker’s notes, Lessons 108 and 24 (pp. 502–
handouts, etc.) 505, 609–613)
4.1.10 Preview the slide show presentation. Lessons 104 and 108 (pp.
483–486, 502–505)
4.1.11 Navigate an on-screen slide show. Lessons 106 and 108 (pp.
491–495, 502–505)
Module 3: Living Online 2005
Objective 1.1 Identify network fundamentals and the benefits and
risks of network computing.
1.1.1 Identify terminology relating to telecommunications, Lessons 11 and 121 (pp. 68–
networks, and the Internet. 75, 590–597)
1.1.2 Identify types of networks. Lesson 11 (pp. 68–75)
C21 Jr. IC3 Correlation 9
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
1.1.3 Identify how networks work. Lesson 11 (pp. 68–75)
1.1.4 Identify benefits of networked computing. Lesson 11 (pp. 68–75)
1.1.5 Identify the risks of networked computing. Lesson 13 (pp. 80–84)
1.1.6 Identify fundamental principles of security on a network Lesson 13 (pp. 80–84)
Objective 1.2 Identify the relationship between computer networks,
other communications networks (like the telephone
network) and the Internet.
1.2.1 Identify the different ways the telephone system is used to Lesson 11 (pp. 68–75)
transmit information.
1.2.2 Identify that telecommunication devices such as modems See Web Reading 3
convert information from analog to digital and digital to
analog formats.
1.2.3 Identify the units used to measure data transmission rates. See Web Reading 3
1.2.4 Identify the Internet as a “super network” of smaller Lesson 121 (pp. 590–597)
computer networks and that computers connect to the
Internet via the “onramp” of a smaller computer network.
1.2.5 Identify the hardware and software required to connect to Lesson 11 (pp. 68–75)
the Internet.
1.2.6 Identify different types of Internet connections and the Lesson 11 (pp. 68–75)
advantages and disadvantages of each connection type.
1.2.7 Identify the roles and responsibilities of an Internet Service Lessons 11 and 91 (pp. 68–75,
Provider (ISP). 394–400)
Objective 2.1 Identify how electronic mail works.
2.2.1 Identify how electronic mail works on a network and on Lesson 91 (pp. 394–400)
the Internet.
2.2.2 Identify the components of an electronic mail message. Lesson 91 (pp. 394–400)
2.2.3 Identify the components of an electronic mail address. Lesson 91 (pp. 394–400)
2.2.4 Identify when to use different electronic mail options. Lesson 91 (pp. 394–400); also
Chapter11 Supplemental
Activity (on Web)
2.2.5 Identify different ways electronic mail is accessed. Lesson 91 (pp. 394–400)
2.2.6 Identify the difference between standard electronic mail See Web Reading 1
and other forms of messaging, such as paging or Instant
Messaging.
Objective 2.2. Identify how to use an electronic mail application.
2.2.1 Read and send electronic mail messages. Lesson 91, (pp. 394–400);
also Chapter11 Supplemental
Activity (on Web)
2.2.2 Identify ways to supplement a mail message with Lesson 91 (pp. 394–400)
additional information.
2.2.3 Manage attachments. Lesson 91 (pp. 394–400); also
Chapter11 Supplemental
Activity (on Web)
2.2.4 Manage mail. Lesson 91 (pp. 394–400)
2.2.5 Manage addresses. Lesson 91 (pp. 394–400)
C21 Jr. IC3 Correlation 10
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
2.2.6 Identify the purpose of frequently used mail-configuration Lesson 91 (pp. 394–400)
options.
Objective 2.3 Identify the appropriate use of e-mail and e-mail
related “netiquette”.
2.3.1 Identify the advantages of electronic mail. Lesson 91 (pp. 394–400)
2.3.2 Identify the common problems associated with electronic Lessons 13 and 91 (pp. 80–84,
mail. 394–400)
2.3.3 Identify the elements of professional and effective e-mail Lesson 91 (pp. 394–400)
messages.
2.3.4 Identify when other forms of correspondence are more Lesson 91 (pp. 394–400)
appropriate than e-mail.
2.3.5 Identify when to include information from an original e- Lesson 91 (pp. 394–400)
mail message in a response as a method of tracking the
“history” of e-mail communication.
2.3.6 Identify appropriate use of e-mail attachments and other Lesson 91 (pp. 394–400)
supplementary information.
2.3.7 Identify issues regarding unsolicited e-mail (“spam”) and Lesson 13 (pp. 80–84)
how to minimize or control unsolicited mail.
2.3.8 Identify effective procedures for ensuring the safe and Lesson 91 (pp. 394–400)
effective use of electronic mail
Objective 3.1 Identify different types of information sources on the
Internet.
3.1.1 Identify terminology related to the Internet. Lessons 11, 12, 13. 14 , and
121 (pp. 68–75, 75–79, 80–
84, 84–88, 590–597)
3.1.2 Identify the purpose of a browser in accessing information Lessons 11, 12, and 121 (pp.
on the World Wide Web. 68–75, 75–79, 590–597)
3.1.3 Identify different elements of a Web site. Lessons 11, 12, and 121 (pp.
68–75, 75–79, 590–597)
3.1.4 Identify different types of Web sites by their extensions, Lessons 11 and 121 (pp. 68–
and the purposes of different types of sites. 75, 590–597)
3.1.5 Identify the difference between secure and unsecure Web Lessons 13 and 14 (pp. 80–84,
sites (such as password-protected sites or sites secure for 84–88)
online transactions) and how to tell if a Web site is secure.
3.1.6 Identify different ways of communicating and Lessons 11 and 91 (pp. 68–75,
corresponding via the Internet. 394–400)
Objective 3.2 Be able to use a Web browsing application.
3.2.1 Identify the make-up of a Web address/Uniform Resource Lessons 11 and 121 (pp. 68–
Locator (URL). 75, 590–597)
3.2.2 Navigate the Web using a browser. Lessons 11, 12 and 121 (pp.
68–75, 75–79, 590–597)
3.2.3 Reload/Refresh the view of a Web page. Lesson 11 (pp. 68–75)
3.2.4 Show a history of recently visited Web sites and delete the Lesson 12 (pp. 75–79)
list of recently visited Web sites.
3.2.5 Find specific information on a Web site. Lesson 12 (pp. 75–79)
C21 Jr. IC3 Correlation 11
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
3.2.6 Manage Bookmarked sites/Favorite sites. Lesson 12 (pp. 75–79)
3.2.7 Save the content of a Web site for offline browsing. Lesson 12 (pp. 75–79)
3.2.8 Copy elements of a Web site including copying text or Lessons 12 and 63 (pp. 75–79,
media to another application. 234–239)
3.2.9 Print all or specified parts of a Web site. Lesson 12 (pp. 75–79)
3.2.10 Download a file from a Web site to a specified location. Lesson 14 (pp. 84–88)
Identify settings that can be modified in a Web browser Lesson 12 (pp. 75–79)
application.
3.2.12 Identify problems associated with using a Web browser. See Web Reading 7
Objective 3.3 Be able to search the Internet for information.
3.3.1 Identify the ways a search engine classifies and looks for Lesson 14 (pp. 84–88)
Web sites.
3.3.2 Identify other ways of searching for information on the Lesson 12 (pp. 75–79)
Web.
3.3.3 Use a search engine to search for information based on Lesson 14 (pp. 84–88)
specified keywords.
3.3.4 Search effectively. Lessons 12 and 14 (pp. 75–79,
84–88)
3.3.5 Identify issues regarding the quality of information found Lesson 14 (pp. 84–88)
on the Internet.
3.3.6 Identify how to evaluate the quality of information found Lesson 14 (pp. 84–88)
on the Web.
Objective 4.1 Identify how computers are used in different areas of
work, school, and home.
4.1.1 Identify how computers and the Internet are used to Lesson 11 (pp. 68–75)
collect, organize, and evaluate information and promote
learning.
4.1.2 Identify the technology and processes involved with Lesson 10 (pp. 64–68)
computers operating “behind the scenes” in everyday
activities
4.1.3 Identify the impact of electronic commerce (e-commerce) Lessons 10 and 11 (pp. 64–68,
on business, individuals and governments. 68–75)
4.1.4 Identify technologies that support or provide opportunities Lessons 67, 68, 69, 70, 71, 72,
to the disabled and disadvantaged, such as voice 73, 74, 75, 76, and 77 (pp.
recognition. 276–277, 277–279, 279–283,
283–285, 290–293, 293–296,
296–299, 299–302, 302–305,
305–307); also , Chapter 8
Supplemental Activity (on
Web)
Objective 4.2 Identify the risks of using computer hardware and
software.
4.2.1 Identify how to maintain a safe working environment that Lessons 15, 16, 18, 19, 20,
complies with legal health and safety rules. and 21 (pp. 95–98, 99–101,
105–106, 107–108, 109–110,
C21 Jr. IC3 Correlation 12
Standard Standard Lesson Number
Number Correlation (page #) or Web
Reference
(www.c21jr.swlearning.com)
111–112)
4.2.2 Identify injuries that can result from the use of computers Lesson 45 and 46 (pp. 164–
for long periods of time. 165, 166–167)
4.2.3 Identify risks to personal and organizational data. Lesson 13 (pp. 80–84)
4.2.4 Identify software threats, including viruses and WORMS. Lessons 13 and 91 (pp. 80–84,
394–400)
Objective 4.3 Identify how to use computers and the Internet safely,
legally, ethically, and responsibly.
4.3.1 Identify reasons for restricting access to files, storage Lesson 13 and 14 (pp. 80–84,
devices, computers, networks, and certain Internet sites. 84–88)
4.3.2 Identify concepts related to intellectual property laws, Lesson 14 (pp. 84–88)
including copyrights, trademarks, and plagiarism.
4.3.3 Identify the principles regarding when information can or Lesson 14 (pp. 84–88)
cannot be considered personal, including the difference
between computer systems owned by schools or business
that may have rules and guidelines as to who owns data
stored on the system, and computers owned by individuals.
4.3.4 Identify how to avoid hazards regarding electronic Lessons 13 and 14 (pp. 80–84,
commerce, including giving credit card information only 84–88)
on secure sites.
4.3.5 Identify how to protect privacy and personal security Lessons 13, 14, Chapter 3
online, including understanding how Web sites track an Apply (pp. 80–84, 84–88);
activity online using “cookies” and other “behind-the- also Chapter 3 Supplemental
scenes” systems. Activity (on Web)
4.3.6 Identify how to find information about rules regarding the Lessons 4 and 14 (pp. 21–28,
use of computers and the Internet, including laws, used 84–88)
policies at school, and company guidelines at places of
employment.
4.3.7 Identify how to stay informed about changes and See Web Readings 1 and 2
advancements in technology.
4.3.8 Identify how to be a responsible user of computers and the Lessons 13 and 14 (pp. 80–84,
Internet. 84–88)
C21 Jr. IC3 Correlation 13
Вам также может понравиться
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Embedded Design With The Microblaze Soft Processor Core: Fpga and Asic Technology Comparison - 1Документ39 страницEmbedded Design With The Microblaze Soft Processor Core: Fpga and Asic Technology Comparison - 1FelipeОценок пока нет
- ACI Muti-PodДокумент59 страницACI Muti-PodAlisamiirОценок пока нет
- Database ProgrammingДокумент441 страницаDatabase ProgrammingWahyu Koerniawan100% (1)
- Rights and ResponsibilitiesДокумент3 страницыRights and ResponsibilitiesSanny Jean Rosa-utОценок пока нет
- Next Session Starts In: Minutes SecondsДокумент10 страницNext Session Starts In: Minutes SecondsSanny Jean Rosa-utОценок пока нет
- Conduct: (Ethical Issues of Education)Документ18 страницConduct: (Ethical Issues of Education)Sanny Jean Rosa-utОценок пока нет
- How, and How Not, To Improve The Schools by Diane RavitchДокумент25 страницHow, and How Not, To Improve The Schools by Diane RavitchSanny Jean Rosa-utОценок пока нет
- Importance of Assessing Student Performance: Sanny Jean Rosa-UtДокумент15 страницImportance of Assessing Student Performance: Sanny Jean Rosa-UtSanny Jean Rosa-utОценок пока нет
- Cisco Series300 ManualДокумент704 страницыCisco Series300 ManualHậu SmileОценок пока нет
- Asrock X370M ManualДокумент76 страницAsrock X370M Manualvirustest99Оценок пока нет
- ZTE Quick Commissioning GuidelinesДокумент149 страницZTE Quick Commissioning GuidelinesKamlesh MehtaОценок пока нет
- NameДокумент24 страницыNameSumbulОценок пока нет
- CC102 - Module 1Документ2 страницыCC102 - Module 1Judielyn CualbarОценок пока нет
- Canteen Management SystemДокумент13 страницCanteen Management SystemModase Tanish100% (1)
- Gocast: Gossip-Enhanced Overlay Multicast For Fast and Dependable Group CommunicationДокумент10 страницGocast: Gossip-Enhanced Overlay Multicast For Fast and Dependable Group CommunicationDung VanОценок пока нет
- 24G Presentation Process Flow 03062011Документ75 страниц24G Presentation Process Flow 03062011ShreekumarОценок пока нет
- DRAM PackagingДокумент4 страницыDRAM Packagingrakista yec100% (1)
- 3.3.4 Packet Tracer - Deploy and Cable Devices - ILMДокумент2 страницы3.3.4 Packet Tracer - Deploy and Cable Devices - ILMMarcela Andrea Orellana SilvaОценок пока нет
- Installing OpenWRT On D-Link Dwl-2100ap A4Документ5 страницInstalling OpenWRT On D-Link Dwl-2100ap A4fessat150% (2)
- QoS in PAN-OSДокумент21 страницаQoS in PAN-OSnashvillewebnetОценок пока нет
- AWS Certified SysOps AdministratorДокумент3 страницыAWS Certified SysOps AdministratorbhaskarОценок пока нет
- Computer Fundamentals and Office AutomationДокумент297 страницComputer Fundamentals and Office AutomationbogasrinuОценок пока нет
- SuperServer-3-2011 Super Micro ProductДокумент52 страницыSuperServer-3-2011 Super Micro ProductLopaishaОценок пока нет
- File PcapДокумент1 страницаFile Pcapmuhammad dzulfiqarОценок пока нет
- Gprs Tunneling Protocol LinuxДокумент3 страницыGprs Tunneling Protocol LinuxNancyОценок пока нет
- Ncse Level 1Документ4 страницыNcse Level 1Hugo AstudilloОценок пока нет
- Ashwin KalaichandranДокумент2 страницыAshwin KalaichandranAshton BerylОценок пока нет
- HP EVA Storage - Capturing Log Files, Configuration and Performance DataДокумент3 страницыHP EVA Storage - Capturing Log Files, Configuration and Performance DatalittleheartОценок пока нет
- Running-ConfigCGR2010 + Complete DescriptionДокумент103 страницыRunning-ConfigCGR2010 + Complete DescriptioneguevaraОценок пока нет
- Wecon RtuДокумент16 страницWecon RtuJoséAlexHuertasCastilloОценок пока нет
- Mpls Layer 3 VPN Pe-Ce Ospf Sham LinkДокумент9 страницMpls Layer 3 VPN Pe-Ce Ospf Sham LinkEmad MohamedОценок пока нет
- LogДокумент93 страницыLogayoolaabdulakeem546Оценок пока нет
- Man Eng Mov11.6 Web ClientДокумент32 страницыMan Eng Mov11.6 Web ClientjosemОценок пока нет
- Devops SyllabusДокумент4 страницыDevops SyllabusdipeshОценок пока нет
- Infinix Note 12 USB Driver For Windows (Official Mobile Driver)Документ4 страницыInfinix Note 12 USB Driver For Windows (Official Mobile Driver)Kurdo KurdОценок пока нет