Академический Документы
Профессиональный Документы
Культура Документы
Big Security Guide V3 No Sponsor
Загружено:
Janko ZindovićАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Big Security Guide V3 No Sponsor
Загружено:
Janko ZindovićАвторское право:
Доступные форматы
The Big Security Guide
About this Guide
Security is a broad, and at times unruly, topic. As IT
Table of Contents
infrastructure environments evolve, security must
Educational Articles evolve with them, especially as more data is moved to
virtualized and cloud environments. In this definitional
What is SD-Branch Security? . . . . . . . . . . . . . . . . . . 1
guide, we bring together our top security content from
How to Approach Cloud-Native Security . . . . . . .2
across SDxCentral’s education materials and news
What Are the Top 5G Security Challenges? . . . . 4 articles, ranging from SDN to 5G to IoT. In anticipation of
What is Docker Security? . . . . . . . . . . . . . . . . . . . . 6 RSA Conference 2020, particular focus has been placed
on anticipated hot topics that will be discussed at the
What is Cloud-Based Security? . . . . . . . . . . . . . . . 7
show.
Five Elements of Cloud Security . . . . . . . . . . . . . . 8
Data Center Security and Virtualization . . . . . . . 10
What is Security Virtualization? . . . . . . . . . . . . . . 12
Edge Computing Security Challenges . . . . . . . . 13
What is SD-WAN Security? . . . . . . . . . . . . . . . . . . 15
News Articles
What’s So Sassy About SASE . . . . . . . . . . . . . . . . 17
NSA Ranks Cloud Security Risks . . . . . . . . . . . . . 19
Will SD-WAN Solve IoT’s Toughest Questions? 22
Cisco Study: Data Privacy ROI for Businesses . 24
About SDxCentral
SDxCentral is the leading resource for IT infrastructure
knowledge.
IT infrastructure is under more demand and more
scrutiny than ever. The way we build networks has
fundamentally changed, with new technologies
constantly popping up to solve new challenges. At the
same time, the role of IT departments and of individuals
within the department is changing. While vendors and
executives strategize around new technologies, those in
the trenches scramble to keep up.
These guides are independent content designed to
share knowledge and help technology professionals stay
ahead of the curve.
This guide was assembled by Connor Craven.
© 2020 SDxCentral LLC. All Rights Reserved.
The Big Security Guide | What is SD-Branch Security?
What is SD-Branch Security?
SD-branch security refers to the tools and techniques Things to Consider When Setting Up
used to secure the software-defined branch. SD-branch SD-Branch Security
deployments are protected by multi-function appliances
Evaluate the Vendor
with security in the branch office. All web traffic in and
out of the branch travels through these appliances. The Not all SD-branch offerings are created equal. Likewise,
legacy fixed-function hardware boxes are condensed not all organizations’ needs are the same. When starting
into a smaller number of appliances that use security business with an SD-branch provider, it is good practice
virtual network functions (VNFs). The exact appliances for an organization to ensure that the vendor fits as
and VNFs an organization deploys varies in number and many of an organization’s needs as possible at an
type, based on the organization’s needs. Aligned with affordable rate. If the vendor has cloud-based security
other aspects of the SD-branch, the goal is to simplify partners, those partners also need to be evaluated.
the management and orchestration of the branch.
Recent Appliance Purchases
SD-Branch and Security
SD-branch products and services are still relatively new
SD-branch security relies on virtualization and SDN to the market. An organization can’t be blamed if it
technology. Virtualizing networking and security had recently started or completed the deployment of
functions allows multiple functions to run in a single a different type of branch infrastructure before hearing
box, reducing the total amount of hardware needed at a of SD-branch. Wide-spread deployments take time and
branch location. money that make an organization hesitant to replace the
deployments too quickly. If the branch still meets the
As with other networking functions, the security
organization’s needs and regulatory requirements with
functionality in an SD-branch deployment can be
the non-SD-branch technology, there is little reason to
updated from a central location via management
change. Alternatively, an organization might not be able
software. Updates can reflect changes in business and
to afford another refresh of hardware so quickly.
security policy, or can be patches to software bugs.
The concept of continuous integration and continuous Regulation Compliance
delivery (CI/CD) can be applied to this so the software
Different verticals have different regulatory requirements
remains secure and effective.
around security to meet. A bank with global reach
There are multiple layers of security. Software for would need more advanced security in its SD-branch
firewalls, antivirus, anti-malware, intrusion detection solution than a restaurant with a handful of locations.
and intrusion prevention systems, unified threat An organization must study the specifics of a vendor’s
management, web and content filtering, and dynamic appliances to ensure that the security aspects meet
segmentation are all seen in various combinations regulation requirements.
in different SD-branch offerings. Some of the listed
examples can also be found in SD-WAN technology
because SD-branch is an extension of SD-WAN, and
includes SD-WAN’s features.
It is also common for SD-branch vendors to partner with
third-party cloud-based security vendors. Vendors can
then integrate their SD-branch technology with best-in-
class cloud-based security vendors to round out their
SD-branch offering and relieve any customer concerns.
© 2020 SDxCentral LLC. All Rights Reserved. 1
The Big Security Guide | How to Approach Cloud-Native Security
How to Approach Cloud-Native Security
Cloud-native security should be approached by moving applications, a small change can have a large impact for
away from traditional manual techniques. IT departments the worse.
should focus on automation and integrating security
In a DevSecOps scenario, developers are able to focus
personnel into DevOps teams to form DevSecOps.
on a specific piece of a project, producing better results.
Cloud-native apps are able to scale much faster than
Disadvantages
legacy apps because of their microservice architecture
packaged in a container-based infrastructure. This speed When a cloud-native application is scaled up for high
means automation is required instead of manual security traffic, there is a massive number of microservices
approaches, which are too slow. functioning. Because of all the APIs that the
microservices have to communicate to ports, there is an
Bringing security teams into DevOps groups ensures
exponential increase in attack surface.
security is built into the code of an application instead of
being retrofitted once problems are identified. This also Cloud-Native Security and Containers
makes responses to problems faster and more precise.
Benefits
Cloud-Native Security and Microservices To reduce the attack surface of the application and its
Benefits microservices, container images are kept small. If there’s
less there, then it is harder to attack. There is also an
Microservices allow DevSecOps teams to decompose emphasis on giving containers a short lifespan. A short
security programs into smaller, individual, and easier existence means a short window of attack. When using
to manage services. However, the rate of change in a container registries as a resource, a safe bet is to use
cloud-native application is magnitudes greater than in a a managed container registry like Google’s Container
traditional app, and the sheer amount of microservices Registry or Docker Trusted Registry that scans container
in a given app makes manual security approaches images for infections. Alternatively, tools like Anchore
untenable. The shift to automation tools makes for are available that are separate from a registry, and
improved control and management of microservices for analyze downloaded containers and enforce policy.
security purposes
Kubernetes, an open source container platform,
The continuous integration and continuous delivery allows for visibility of the containers it orchestrates so
(CI/CD) approach that is common to cloud-native developers can see what their program is doing. Using
apps can keep any application up to date. Traditional declarative language, containers deviating from an app’s
applications, which did not have microservices, needed declared ideal state are automatically replaced with the
software patches that were often large and complicated. previous stable version.
Microservices allow for updates to be fast, small, and
Containers also have an immutable aspect. When there
immutable. Immutable means that the microservice
are issues, individual containers are replaced, instead of
is unchangeable. Once the object is created, it is
being modified.
uneditable.
Disadvantages
There is also less risk of breaking a whole application
during an update than compared to a traditional There are a few concerns around containers and security.
application. As an architecture, microservices are loosely One is how trustworthy the source of a container
coupled to each other and are fairly independent, image is (supposing the developers did not make one
so a change to one does not have a huge impact on from scratch). According to Ben Hale, lead of Java on
another. In the tightly coupled architecture of traditional Cloud Foundry, a best practice is, “using official images
© 2020 SDxCentral LLC. All Rights Reserved. 2
The Big Security Guide | How to Approach Cloud-Native Security
provided by OS vendors to the public. These vendors are Friday without manager approval. The developer codes
close to their communities, are aware of vulnerabilities the system to check the day and time, and then request
before they are made public, and are strongly manager approval if it is 3 p.m. or later. Then, if the
incentivized to keep images safe.” manager approves it, the code can be deployed.
For the greatest degree of control over the process, Policy as code should be the same as any other code.
engineers can build containers from the ground up. Hale It should have the same syntax and the same approach
emphasizes this for images beyond the base OS images. to being changed as other code. Changes should be
tracked and commented on in the same way as well.
Another concern is how much access the container has
to the host OS. Using non-root containers with relatively Gating deployment of applications is another area
few privileges makes it so malicious code does not where automation is key. It would cost a lot of time for
spread as easily. humans to parse through all of the oplicies and enforce
them individually. Another issue is that interpretations of
Third, Kubernetes can widen the attack surface. The
policies are not the same from person to person.
orchestrator itself can be targeted by attackers. The
Kubernetes API can act as a backdoor where hackers Again, immutability has something to offer. It does not
may access any pod (group) of containers they want. cost much in resources to deploy new virtual machines
(VMs) or containers. It makes sense then to keep them
Cloud-Native Security and Infrastructure
static and just replace them with corrected versions.
The security of cloud-native applications does not have
For example, Capsule8, a cloud security company,
to be viewed through microservices and containers.
says that to ensure visibility, and therefore security,
There are infrastructure-based elements as well.
information should be gathered from the host, VMs,
Using a service mesh enhances communication in a containers, apps, and API services. That information
system by connecting the platform monitoring tool with should then be sent to an engine for real-time decision
the security infrastructure. Monitoring becomes more making. Capsule8 also says integration of workload
granular and can be managed in a more automated orchestrators and deployment automation tools allow
fashion with a declarative approach. security tools to be deployed automatically alongside
the workload the tools are protecting.
Policy as code is an approach to security that gives
DevSecOps teams more control and influence over the In Summary
security system.
Traditional security approaches cannot sufficiently
Policy as code means that a rule developers want keep pace in a cloud-native environment. Microservices
the program to always follow is written into code. and containers have their pros and cons: They make
An example from Justin Garrison and Kris Nova’s large attack surfaces but are immutable and easy to
2018 book, Cloud Native Infrastructure: Patterns for fix. Automation is the name of the cloud-native game,
Scalable Infrastructure and Applications in a Dynamic as well as including security teams in development
Environment, is about deployment gating. Say a pipelines to integrate security policies as code.
developer doesn’t want to deploy code after 3 p.m. on a
© 2020 SDxCentral LLC. All Rights Reserved. 3
The Big Security Guide | What Are the Top 5G Security Challenges?
What Are the Top 5G Security Challenges?
The top 5G security challenges include IoT devices and a surgery, and remote patient monitoring via IoT devices
spike in network breaches. among other advances. However, those advances are
tempered by the need for ever-stronger security. The
Telecoms are working to combat these challenges by
above Wipro report states that the healthcare industry
securing the edge and architecting their networks to
was the target of 48% of data breaches in 2018. It adds
detect breaches through automation.
that the growth of IoT device use will make dealing with
5G Security Threat Landscape increasing cybersecurity risks more challenging.
5G networks support a massive number of connected Smart homes: 5G-enabled smart homes will require
devices. They enable a huge increase of bandwidth stronger methods of authentication, such as biometric
over LTE, and create a threat landscape different from identification, seen in software made by Sensory
previous networks. Security challenges stem from the that uses voice and face recognition, or the bevy of
very attributes that make 5G such an improvement. fingerprint-access door locks available at hardware
stores. In December 2019, a set of breaches into
IoT, which is a major component of 5G network
Amazon’s home camera security product Ring sparked
architecture, remains a major security risk. IoT devices
outrage, as hackers were able to access cameras in
are one of the most-attacked types of hardware,
users’ homes and on their front porches.
making up over 78% of malware detection events in
communication service provider networks in 2018, In general, IoT devices and sensors will demand more
according to a report by Nokia. complex authentication to prevent unauthorized access.
“If an IoT device today is plugged into the network, 5G Security and New Network Architectures
and it doesn’t have protection in it, it’s infected in three
Cloud virtualization technologies such as software-
minutes or less,” said Mary O’Neill, VP of security at
defined networking (SDN) and network functions
Nokia at an MWC Los Angeles press conference in 2019.
virtualization (NFV) are thriving in anticipation of 5G
High-profile breaches are on the rise. In 2019, publicly- networks. However, they too come with new security
recorded breaches increased by 25%, and the rate of concerns. Because of their open, flexible, programmable
breaches is “exponentially increasing,” according to nature, SDN and NFV open up a new avenue of security
Wipro’s 2019 State of Cybersecurity Report. threats. For example, a network element of an SDN such
as the management interfaces could be used to attack
Securing New 5G Use Cases
the SDN controller or management system and bring
The coming 5G networks have the potential to explode down the system.
vertical industries, enabling the creation of a wide array
Research from the Journal of ICT Standardization
of new services — all of which will demand new, varying
suggests a multi-pronged approach to 5G security,
levels of security.
including trust models, authentication and key
Autonomous Vehicles: The threat of automotive agreement, and an extensible authentication protocol-
cyberattacks will rise as autonomous vehicles become based secondary authentication, among others.
more widespread. To combat this, the National Highway
The security of 5G network infrastructure must evolve
Traffic Safety Administration employs a multi-layered
alongside the standard. For example, because 5G
approach to cybersecurity as it approves driver
networks can be sliced into uniquely purposed slices,
assistance technologies.
each virtual network slice could demand unique
Healthcare: In the healthcare field, 5G capabilities will security capabilities based on the needs of different
help with faster transfer of large patient files, remote usage scenarios. Also, compromised Radio Access
© 2020 SDxCentral LLC. All Rights Reserved. 4
The Big Security Guide | What are the Top 5G Security Challenges
Network (RAN)-side 5G devices might present a larger exfiltration and VM-based attacks that come from
Distributed Denial of Service (DDoS) threat. east-west and north-south traffic. Network operators
should include hypervisor inspection and hardening
Tackling 5G Security
mechanisms in order to guard against such attacks.
Wipro’s report outlined five network components in
Finally, security through orchestration means taking
ensuring 5G security:
advantage of 5G’s software-defined, disaggregated
• A secure edge architecture, to orchestrate VNFs to automatically react
to a breach. VNFs can alert the orchestrator of a breach.
• A secure SDN controller
The orchestrator then instructs the SDN controller to
• Proactive analytics enact security protocol and control routers and firewalls
to halt the attack, as well as tighten access control.
• Hypervisor and container security
5G Security: Key Takeaways
• Security through orchestration
1. 5G security is more important than ever, as breaches
Securing the edge means ensuring real-time detection
continue to increase in frequency and volume.
capabilities at the edge. The network must find and stop
breaches before they make it to the core. 2. IoT devices pose a huge threat to the network.
Securing the SDN controller means enabling dynamic 3. 5G use cases, such as autonomous driving,
security protocol through northbound and southbound healthcare devices, and smart homes mean that
APIs. Northbound APIs gather intelligence about attackers have more access to personal data than
network activity. Southbound APIs control switches, ever.
routers, and firewalls to end attacks as they occur.
4. A 5G network must be architectured to evolve to
Proactive security analytics uses machine learning growing security needs.
and AI to detect unusual activity in the network that
5. 5G requires end-to-end security that uses its
may indicate a breach. Detection of a brach is based
software-defined architecture to automatically
on previously-learned network patterns and trends in
detect and mitigate threats.
previous breach attempts.
Hypervisor and container security mean ensuring
that virtualized network elements are protected from
© 2020 SDxCentral LLC. All Rights Reserved. 5
The Big Security Guide | What is Docker Security?
What is Docker Security?
Docker security issues, and container security issues Docker Content Trust
generally, are not too different from the issues that
Docker Inc. has responded to the need for improved
container technology has faced for some time. Container
Docker security with containers and images by creating
technology arose from the need to run certain workloads
a system called Docker Content Trust, which forces
in isolation — not so much to protect those workloads,
developers who push images to Docker Hub and other
but to protect everything else from them.
registries to encrypt the image. In addition, images that
Security-related needs triggered the development trend have signatures from the creator(s) are filed under the
that eventually led to Docker. Although Docker is taking Verified Publisher section, which is more trustworthy.
steps to plug potential holes in container development
Organizations can automatically limit containers running
platforms, security is a moving target, and more work is
in a production environment to only those images whose
always needed.
constituent parts (including its master pulled from the
Docker Security Risks registry) are digitally signed and verifiable. This way,
organizations know they’re not running containers that
One problem large organizations face today when
have been tampered with, and can rely upon the good
adding Docker to their production environments is
standing of the institutions that signed the images.
ensuring that developers employ best-practices, as the
platform has no inherent security mechanism. Key Management Risk
A best practice for security engineers is to consider the It can be risky to rely exclusively on a method so
connection between containers and the kernel of the dependent on encryption for container security.
operating system (OS) that hosts their Docker daemon, Encryption can merely shift the single point of failure
and how exploitable the relationship could be. An exploit to the organization’s key management systems.
delivered by way of a container could conceivably attack However, there is little or no argument against the use of
the kernel of its host, rendering the OS vulnerable. encryption as part of a larger security system.
In an attempt to reduce the risk of kernel-OS In November 2015, Docker Inc. addressed the issue of
exploitation, organizations may deploy their Docker key management for Docker security by announcing
environments on virtual machines — rendering the support of YubiKey, a physical, USB-based digital
containers’ host kernels virtualized. Therefore, the kernel key manufactured by Yubico. YubiKey can be used
is partitioned exclusively from the processor’s native OS. in conjunction with an access control system that
While this eliminates the threat from one known exploit verifies the physical presence of the user logged in at a
vector, it also diminishes the performance of containers particular terminal. Operations involving the acquisition,
in production. composition, and deployment of containers can be
restricted to individuals whose YubiKey is accessible to
Compliance Guidelines
the host kernel.
Docker Inc. and its platform subscribe to container
compliance guidelines set by governmental and non-
governmental organizations, such as the Information
Technology Laboratory (ITL) of the National Institute
of Standards and Technology (NIST) and the Center for
Internet Security.
Encryption-Based Solutions for Docker
Security
© 2020 SDxCentral LLC. All Rights Reserved. 6
The Big Security Guide | What is Cloud-Based Security?
What is Cloud-Based Security?
Cloud based security services are migrating from New Architectures
dedicated hardware solutions to cloud-based security
Pursuing a cloud-based security model does have
services using a Software as a Service (SAAS) model.
challenges. In order to deliver comprehensive protection,
The increase in virtualized and cloud networks is security must be written into the architecture of a
boosting demand for cloud based security, because data network. There are also a wide range of security needs,
and applications are now more portable and distributed which all require different applications and needs. In
across a wide variety of networks. This means that addition, the move to cloud-based applications poses its
security applications need to live as software in the own threats.
cloud, rather than as dedicated hardware appliances
The three most pressing cloud issues for businesses
protecting specific points of the network.
remain email security, web security, and identity and
A Fast-Growing Market access management. Throw in bring your own device
(BYOD) trend from employees moving around within
Demand is rising for cloud based, SAAS security
their company, Distributed Denial of Service (DDoS)
solutions and the market is growing rapidly. These
attacks, and advanced threats, and many corporate
services can be provided as single features or as part of
IT managers are finding the need for a multi-faceted
a larger, integrated SaaS package. Most current security
approach to security.
systems possess outdated technology that relies on
human monitoring which opens the opportunity door for One of the largest challenges of implementing cloud-
more automated versions in the cloud. These security based security is the need to maintain consistent control
tools are also being integrated with software-defined and visibility across the different domains. With many
networking (SDN) SDN to deliver a network that can use existing networks, there is a combination of public and
real-time analytics and monitoring to protect against private (and even hybrid) cloud-based services, which
emerging threats. makes the integration of security services and strategy a
big task.
The entire managed security services saw 10% growth
in 2014, up to $15.8 billion, with cloud-based offerings
making up 46% ($7.2 billion) of that amount. That
equates to a 13.5% growth in the cloud-based market
from 2013 when it was worth $6.3 billion. The experts
at IHS/Infonetics predict that cloud-based security will
pass traditional Customer Provided Equipment (CPE)-
based security services by 2018.
Pricing is another main benefit of cloud based security,
through usage-based pricing. This model dictates that
there will be savings in the original investment, as well
as funding for later maintenance of the system. With
software continually being developed, you will not have
to replace large and pricey pieces of equipment.
© 2020 SDxCentral LLC. All Rights Reserved. 7
The Big Security Guide | Five Elements of Cloud Security
Five Elements of Cloud Security
The five elements of cloud security are a secure Cloud Security Compliance
architecture, enforcing compliance, practicing due
The next step is to analyze compliance. Many countries
diligence, monitoring the network, and incorporating
are imposing data privacy regulations and fines on
solid authentication protocol.
companies that do not adequately protect users’ data.
Architecture An example of this is the EU’s General Data Protection
Regulation (GDPR), which levies hefty fines for violations
While cloud typically means outsourcing some or all
– 4% of annual turnover or €20 million. Regularly
of an organization’s IT infrastructure, ultimately the
researching regulations is a priority for organizations.
organization is responsible for infrastructure security.
This starts with understanding cloud architecture. Practicing Due Diligence
Organizations should understand the security limitations Enterprises should constantly analyze and review their
of their cloud service. Such as what the provider compliance. As well, they should evaluate the security
offers and what the organization is responsible for. For measures currently in place and be up to date on the
example, if an enterprise chooses a service provider that latest security breaches. Hackers constantly discover
offers an Infrastructure-as-a-Service (IaaS) cloud, then new points of entry. It’s up to enterprises to remain
the enterprise is expected to handle most of the security educated on these new breaches to confront potential
set up. attacks head-on.
This is because the enterprise is in charge of the Monitoring and Visibility
software overlay, which is where most of the security
Investing in performance management tools is
features will be. While this creates more work, it also
another critical step to monitoring the health of the
gives the organization more direct control over how
cloud network. A network performance management
their security is set up.
(NPM) tool spots issues affecting the network, such as
On the flip side, if the cloud service provider is in traffic bottlenecks and suspicious activity, and alerts
charge of a cloud service software (software-as-a- IT professionals of the issues. Incorporating an NPM
service applications), the provider is expected to product helps enterprises stay informed on its network
enforce application and data security. This is less work activity. It also allows IT professionals to resolve any
for the organization but provides less control over issues that negatively affect the network’s computing as
cloud security as the service provider handles most the issues occur.
of the security enforcement. This is even more true
for organizations purchasing managed cloud services,
Authentication
where their IaaS is managed completely by a third party. Enterprises should implement centralized login
management systems, cloud access security brokers
Overall, organizations need to know the elements of
(CASBs), encryption, encryption key management,
cloud security architecture to understand potential gaps
tokenization, and two-step or multi-factor
in security coverage, what they are responsible for, and
authentication. All these tools add barriers to halt
how to secure weak points in cloud computing.
hackers from infiltrating sensitive data. Additionally,
Items that enterprises may need to implement backing up data and investing in data loss prevention
include virtual firewalls and intrusion detection tools keep an enterprise’s data accessible in case a
systems and intrusion prevention systems (IDS/IPS). hacker successfully enters cloud storage.
Understanding the security architecture is the first step
to understanding cloud computing security.
© 2020 SDxCentral LLC. All Rights Reserved. 8
The Big Security Guide | Data Center Security and Network Virtualization
Data Center Security and Network
Virtualization
Data center security refers to the process of using fluctuates, or when an organization’s needs shift.
physical and virtual components (such as firewalls)
Accounting is the final element and refers to the
to protect a data center from malicious activity. In
collection of network data for analysis and auditing.
recent years, network virtualization has improved and
Without authentication, the network management
expanded what security tools are available to data
software would be lacking critical information giving
center operators.
context for who or what generated certain data.
Virtualized Data Center Security Essentials Virtualization is critical for accounting because it adds
visibility to the network, which increases the amount of
In a data center network, the core elements are
data that can be collected.
authentication, authorization, and accounting, or AAA.
Authentication of users is done through multi-factor Role-Based Access Control
authentication where users enter a password in addition
Role-based user access (RBAC) is a key component
to something like a YubiKey or a code that was sent to
of data center security. By virtualizing the network,
their phone. Authentication is foundational to the other
administrators can establish rules through centralized
two elements.
management software. The software can often
Authorization is the curation of an access list that intelligently identify users through multi-factor
determines what level of access employees have. It authentication. Different users are given different
relies on having the identity of the employee, which is degrees of access to network resources depending on
provided through authentication. Virtualization improves what the user needs to do their job. For example, some
authorization because, with it, authorizations can be users may be granted total access to working with data
changed on demand from a central location. Changes center resources, while other users may only be able to
may be in order when the scope of an employee’s job view application traffic flow.
© 2020 SDxCentral LLC. All Rights Reserved. 9
The Big Security Guide | Data Center Security and Network Virtualization
Software-defined networking (SDN), a complementary to other servers in their network. By segmenting the
technology to network virtualization, also makes network, a data center limits the risk of attacks being
RBAC easier by centralizing network management and able to move to other applications or servers because
enabling direct programmability in the network. This there are fewer instances of them talking to each other.
means administrators can program the network to adjust
The security policies that are part of virtualizing the
to the needs of the organization on-demand and modify
network can route traffic through virtual firewalls within
user permissions when needed.
a segment before it goes to another server. This is
Microsegmentation commonly implemented through service chaining. In a
traditional data center network, traffic steering would
Microsegmentation enables security architects to
send information through multiple different devices
separate different parts of the data center into precise
for each of the security and networking functions. This
segments. The granularity can go down to a server’s
slowed processes down and was inefficient compared
individual workloads. Unique policies can be established
to the more modern technique in use by VMware’s NSX
to the different segments that have been created. The
platform. The platform uses service chaining, which is
degree of security established by the policies depends
the insertion of multiple functions, like firewalls or load
on the regulatory and compliance requirements of the
balancers, into a forwarding path
segment’s data.
Data Center Security: Key Takeaways
Microsegmentation is possible thanks to network
virtualization. It is similar to how VMs split up the space 1. The three core elements of data center security are
on a server to have multiple distinct instances run at the authentication, authorization, and accounting.
same time. Virtualized networks are overlays on physical
2. Access control software is able to identify users, find
infrastructure, which is basically used as the connections
out how much access to network resources they are
data travels through. Changes to the network can be
assigned, and keep them within those limits.
done as needed because the virtual network is an
abstracted overlay. Changes include microsegmentation 3. Software definition of a data center brings
to new workloads to keep them isolated and secure. intelligence and centralized control to the data
center’s network.
Isolation of VMs, for example, can prevent the lateral
spread of an attack from application to application. This 4. Microsegmentation of the network can be highly
east-west communication has become more common in granular and prevents attacks from spreading from
data center networks as servers are increasingly talking application to application or server to server.
© 2020 SDxCentral LLC. All Rights Reserved. 10
The Big Security Guide | What is Security Virtualization?
What is Security Virtualization?
Security virtualization is the shift of security functions to VMs. The security can also manage security policies
from dedicated hardware appliances to software that for access to virtual networks and workloads themselves.
can be easily moved between commodity hardware or
Two common concepts in virtualized security are
run in the cloud.
segmentation and isolation. With segmentation, specific
The increased virtualization of the computing and network resources are only accessible to specified
network environments is putting more requirements applications and users. This can be achieved with virtual
on flexible, cloud-based security. Networks and data software in addition to physical security devices.
centers dynamically create software-based networks
Another important approach is isolation, which
and computing functions such as virtual machines
allows discrete applications and workloads to operate
(VMs), so the security functions must also be virtualized
independently on the same network. An example of this
in a portable way to move with the applications and
would be segmenting the portion of the network dealing
computing workloads.
with sensitive information, such as credit-card data.
From Physical to Virtual
With the advent of software-defined networking (SDN),
Physical security devices are typically inserted on the segmentation can be built into virtual network fabrics.
perimeter of a network to provide protection, enabling For example, an SDN network could be set up to have
access to the network by authenticated users. In a virtual several secure layers, depending on policies assigned to
environment, networks, workloads, and virtual machines various applications. Microsegmentation is another trend
are consistently being set up, torn down, and moved in SDN security that is driving security virtualization.
around inside a data center or network, shifting the With microsegmentation, additional layers of security
focus of the security needs. can be added at the application and workload level.
In addition, because multiple virtual networks Microsegmentation applies specific security policies to
can operate across the same underlying physical workloads and applications, in a manner that can enable
infrastructure, security must address each layer of the security functions to follow workloads around the
virtualization. VMs, for example, have additional security network if they are moved, an approach that is common
complexity. They pose security risks because they in today’s virtual infrastructure.
operate as digital files that can be moved, regardless of
Security virtualization is a strong trend and is likely
physical infrastructure. These trends have driven more
to remain that way as more applications are run in
security virtualization.
the cloud and networks grow increasingly virtualized.
Segmentation and Isolation New forms of security software than can be installed
to monitor and manage security policies on virtual
Security virtualization uses software installed on virtual
infrastructure will be needed.
networks to monitor workloads, applications, and access
© 2020 SDxCentral LLC. All Rights Reserved. 11
The Big Security Guide | Edge Computing Security Challenges
Edge Computing Security Challenges
The top edge computing security challenges are having IEEE published a research paper outlining important
network visibility, secure operating systems, encrypted requirements for edge security and privacy. Important
data, and user authentication mechanisms. As edge points include:
computing adoption rises, the heightened exposure of
• Information integrity is key to assuring that
user data has security experts focusing on detecting and
data is securely transmitted without undetected
addressing the ways sensitive data could be breached.
modification. If integrity exists, then trust follows.
Why is Edge Security Important?
• Security mechanisms should guarantee the
Edge security is important because it maintains privacy outsourcing information of users, such as data,
of the user and preserves user trust in the edge and personal identity, and location, is kept secret from
other networks. adversaries.
The network edge can be a weak point in the network • Suggested security mechanisms include encryption,
because of a lack of physical security and the absence integrity audits, and features like authentication and
of or weakness of security measures in the devices using access control.
edge computing.
Who or What is Targeted on the Edge?
Carelessly-made Internet of Things (IoT) devices, or
The edge network user, IoT devices, the data on the
weak passwords on employee-owned devices, create
network, and the edge network itself are all targets for
vulnerabilities for the whole network. Establishing a
attack on the edge.
uniform level of security for all hosts, and keeping all of
them patched, is a way to make edge computing less IoT devices are major targets because they have implicit
risky. trust for other devices and do not verify the credibility
© 2020 SDxCentral LLC. All Rights Reserved. 12
The Big Security Guide | Edge Computing Security Challenges
of connections. They are also often released before networking (NDN) instead of a traditional IP addressing,
they have suitable security measures included so the and authenticated users.
company can be the first to market.
VPN and General Encryption of All Data
Edge computing’s vulnerabilities come from its
Whether the edge is being used for IoT or to increase
distributed nature, whether there is limited physical
throughput at an enterprise’s location, data encryption is
security, or difficulties around total network visibility.
recommended.
How Companies Can Secure Edge Nodes It is not guaranteed an edge computing device will be
Visibility encrypted or support transport layer security (TLS),
although devices can have these capabilities. If there
A key component to securing any network is visibility.
is no form of encryption, a VPN is a good option for
An operator needs to know what is happening on the data encryption and secure transmission because of its
network to ensure that it is working properly and that availability and reliability with options like OpenVPN.
users are behaving properly.
User Access Management
This is particularly important in the IoT world, as devices
send potentially sensitive data to clouds that users The IEEE paper referenced above included specifications
cannot be certain are safe. Moreover, the vast majority on user access control, which regulates who can access
the network and how they can use it, specifically the
of applications for users to interact with or monitor IoT
reading and writing of data.
devices have little to no security testing.
Authentication mechanisms are necessary to keep out
Secure Operating System for Edge Platforms
malicious users and deny unauthorized users access
Internet Technology Letters published a proposal to resources in the edge and core. The IEEE paper
regarding a new security architecture for when IoT recommends a fine-grained access control system
devices use edge computing. The architecture focuses for every trust domain in the edge network by using
mainly on an operating system for edge computing. attribute-based encryption or role-based encryption.
Elements of a secure edge operating system include Another approach to ensure security is to use trusted
authenticated network nodes, using named data platform modules (TPMs).
© 2020 SDxCentral LLC. All Rights Reserved. 13
The Big Security Guide | What is SD-WAN Security?
What is SD-WAN Security?
SD-WAN security is based largely on the use of SD-WAN Security Basics: IPsec and VPNs
IP security (IPsec), VPN tunnels, next-generation
IPsec-based VPNs are nearly universal to all SD-WANs.
firewalls, and the microsegmentation of application
Since an SD-WAN uses the public internet in addition
traffic. Network administrators centrally manage and
to MPLS connections, a VPN or IPsec tunnel is required
orchestrate these security elements through software
to, at the very least, ensure traffic is not interfered with
that grants granular visibility into the network through a
between the sender and receiver.
single dashboard.
This is done by:
The combination of WAN virtualization and the practice
of placing applications in the cloud has extended • Authenticating the sender, receiver, and packets that
the network perimeter out from the organization’s are sent
headquarters. This necessitates security functionality to
• Using encryption keys already shared by the hosts
be at an organization’s headquarters, branch locations,
sending and receiving the data, or using public and
and the cloud.
private key encryption
Virtualized security network functions can better keep
• Ensuring packets have not been tampered with by
up with evolving security threats and to control the cost
using the Encapsulating Security Payload (ESP)
of updating and upgrading security elements. SD-WAN
protocol
security’s use of virtual machines means software
updates can be installed on existing hardware, rather • Confirming that the origin of packets is trusted
than having to install new hardware for every update, through an Authentication Header (AH) that looks at
saving time and money. the IP header
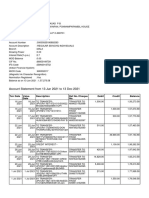
This depiction of end-to-end segmentation from Cisco shows the path of data in an SD-WAN to and from the WAN edges through
the network connections. The vSmart component is Cisco’s SD-WAN controller that handles routing. Source: Cisco
© 2020 SDxCentral LLC. All Rights Reserved. 14
The Big Security Guide | What is SD-WAN Security?
Visibility NGFW for SD-WAN Security
A major benefit of SD-WANs over traditional WANs A next-generation firewall (NGFW) is a key element
is the level of visibility into the network SD-WAN of SD-WAN security. Deployed at branches as well as
provides. Network administrators are able to manage headquarters, an NGFW is a virtualized and improved
and orchestrate the network centrally, monitoring traffic version of traditional hardware-based firewalls. An
for inconsistencies. With this functionality, network NGFW runs multiple virtual network functions (VNFs),
administrators can ensure applications are performing such as application awareness, intrusion detection and
sufficiently, troubleshoot network problems, and confirm prevention, URL and web content filtering, malware
security elements and policies are running correctly. detection, and antivirus protection. NGFWs and the
VNFs they run can be based in the cloud in addition to
However, the degree of visibility depends on the
on-premises.
SD-WAN vendor. Some vendors go down to the user/
device level, while others only go to the application level. Microsegmentation
The information the SD-WAN gathers from the user,
In an SD-WAN, it is possible to segment the traffic from
device, or application gives insight on whether the traffic
different applications based on its characteristics and
is coming from a trusted or less trusted source.
the network policies established for the SD-WAN by
Application-level visibility of network traffic gives network administrators. Segmentation is the creation
network administrators details on what applications of virtual networks within the SD-WAN’s virtualized
are using bandwidth, how much resources they are network overlay. Segmentation allows traffic from
using, and how well they are performing. Network different applications or groups of applications to be
administrators use visibility to granularly establish segregated from each other. The attack vector is then
security policies for what applications or IP addresses eliminated and security policy and quality of service can
users can access. be applied much more granularly. Different policies can
be applied to individual segments.
Additionally, nearly all other security features in an
SD-WAN are reliant on the amount of network visibility Microsegmentation is able to segment traffic down to
because the software can only interact with the traffic it the workload. By keeping very specific types of traffic
can detect. Next-generation firewalls are not reliant on separate from each other, traffic that is coming from
network visibility because they are analyzing all traffic a less secure location cannot interact with sensitive
passing through them. information.
Device-level visibility goes beyond just showing data
about the applications creating traffic, but on the device
using the application, and the person using the device —
if there are identifiers connecting the user to the device.
Device-level visibility gives greater granularity of security
policies that can be applied to the network. It can group
users and determine their level of access to the network
and what they are doing on the network.
© 2020 SDxCentral LLC. All Rights Reserved. 15
The Big Security Guide | What’s So Sassy About SASE?
NEWS
What’s So Sassy About SASE?
by Tobias Mann October 20, 2019
The secure access service edge (SASE) promises and instead shifts to a model that connects users and
to address changing enterprise traffic patterns, and equipment at an individual level to a centralized cloud-
threatens to render SD-WAN stalwarts irrelevant in the based service.
coming years, according to a recent Gartner report.
In traditional enterprise networks the data center
In its 2019 Hype Cycle report, Gartner defines SASE is the focal point for access. Gartner contends that
— pronounced “sassy” — as an emerging market that this approach has become increasingly ineffective as
combines elements of SD-WAN and network security businesses transition to software-as-a-service (SaaS),
into a single cloud-managed package. cloud services, and edge compute platforms.
It’s a technology that Gartner has called Gartner acknowledges that the enterprise data center
“transformational.” isn’t going anywhere soon, but maintains that it will
become less relevant as service move to the cloud. The
“SASE will be as disruptive to network and network
enterprise data center effectively becomes just another
security architectures as [infrastructure-as-a-service]
branch.
was to the architecture for data center design,” the
report claims. “A branch office is simply a place where multiple users
are concentrated,” the Gartner report states. The same is
SASE vs. SD-WAN
true for a salesperson working remotely, only they are a
Unlike a traditional WAN, SASE does away with the branch of one.
concept of connecting the branch to the central office
According to Gartner, SASE brings with it several
© 2020 SDxCentral LLC. All Rights Reserved. 16
The Big Security Guide | What’s So Sassy About SASE?
NEWS
advantages over existing technologies, not the least Emerging SASE Market
of which include greater flexibility for the end-user,
While still a relatively new technology with less than 1%
reduced operational complexity and costs, and better
adoption, Gartner anticipates many vendors will begin
performance.
rolling out SASE products over the next several months.
Distributed Access
Gartner reports that no vendors are offering a
The distributed nature of SASE will make the number comprehensive SASE product today, but notes there
of points of presence (P0Ps) offered by a vendor an are several SD-WAN and cloud-based security providers
important factor for customers evaluating a solution. well-positioned to move into the space in short order.
Even then the technology isn’t expected to reach
“The SASE solution should offer distributed [PoPs] and
mainstream appeal for another five to 10 years, and is
a portfolio of traffic-peering relationships,” the report
likely to undergo significant changes within that span of
notes.
time.
This approach means enterprise data will only rely on
Because of this, Gartner warns early adopters to limit
the open internet to get to one of the SASE vendor’s
contracts to no more than two years and include
PoPs.
acquisition protection clauses. It also warns customers
An Emphasis on Security should be wary of vendors trying to link several services
together using virtual machine (VM) service chaining to
SASE will also open the door to enhanced security
reduce the time to market.
features including support for content inspection and
zero-trust network access. Enterprises using a SASE “This approach may speed time to market but will result
platform supporting content inspection could scan in inconsistent services, poor manageability, and high
active sessions for malware and sensitive content latency,” the vendor explains.
regardless of where the device or user are located.
And because SASE doesn’t rely on the IP address or
physical location of the device for policy enforcement,
Gartner says enterprises can employ a zero-trust
approach to networking, allowing for consistent policy
enforcement and security wherever the user is working.
© 2020 SDxCentral LLC. All Rights Reserved. 17
The Big Security Guide | NSA Ranks Cloud Security Risks
NEWS
NSA Ranks Cloud Security Risks
by Jessica Lyons Hardcastle January 31, 2020
Moving to the cloud can improve a company’s security Shared Responsibility
posture — but cloud services aren’t without risks, and
The NSA report also discusses the concept of shared
organizations should both understand and address
responsibility. This is important because security vendors
these risks before buying these services and deploying
and cloud service providers alike say many of their
workloads in the cloud. To that end, the National
Security Agency (NSA) published new guidance titled customers still don’t have a strong grasp on this model
“Mitigating Cloud Vulnerabilities.” and how it works. Cloud providers like Amazon Web
Services (AWS) and Microsoft Azure are responsible
The report targets companies’ leadership and for protecting their public cloud infrastructure and
technical staff. It highlights the basic components of implementing logical controls to separate customer data.
cloud architecture and threat actors. And then it also The customer, however, is responsible for configuring
ranks four different types of cloud security risks — application-level security controls, and for protecting
misconfiguration, poor access control, shared tenancy
its workloads running on cloud servers. In other words,
vulnerabilities, and supply chain vulnerabilities — that,
both the cloud provider and the customer have a shared
according to the NSA, account for the vast majority of
responsibility when it comes to cloud security.
known security flaws.
“Shared-responsibility model is a tough one,” said James
While each cloud service providers’ architecture will be
Christiansen, VP of cloud security transformation at
slightly different, most clouds have four components in
Netskope. Part of the difficulty comes from “a mindset
common. This includes identity and access management
that when you outsource something, you wash your
— these are controls in place for customers to protect
hands of it.”
access to their resources and controls that the service
providers use to protect back-end cloud resources — as In other words, when companies move from their
well as compute, networking, and storage. on-premises infrastructure and into the public cloud,
© 2020 SDxCentral LLC. All Rights Reserved. 18
The Big Security Guide | NSA Ranks Cloud Security Risks
NEWS
often they just assume that AWS or Azure is responsible Organizations can mitigate poor access control by
for all the security measures needed to protect the enforcing strong authentication protocols such as multi-
resources running in the cloud. However, this is not the factor authentication and using automated tools to audit
case. access logs.
Also, Christiansen says he’s not a fan of the term No. 3, shared tenancy vulnerabilities, remain rare,
“shared responsibility.” Instead, “I would just go with according to the report, and require a high level of
a responsibility matrix: these are your responsibilities, sophistication. But these types of vulnerabilities in cloud
and these are ours,” he added. “There are very distinct hypervisors or container platforms can be especially
responsibilities, and when you see those failures, it’s severe.
often the failure of not understanding the part that they
To mitigate these, the NSA advises enforcing encryption
are responsible for.”
of data at rest and in transit. And for especially sensitive
NSA’s Top 4 Cloud Vulnerabilities workloads, companies should use dedicated or bare-
metal cloud instances.
The NSA categorizes cloud vulnerabilities and
mitigations into four groups. It also says how prevalent If companies don’t use a dedicated instance,
each one is, and what level of sophistication it requires Christiansen suggests requiring that the cloud provider
for an attacker to pull it off. perform a forensic analysis of the logs, separating your
logs from those of the other tenants. Organizations
Misconfiguraiton, a widespread threat that requires a should write this into the contract when they initially buy
low level of sophistication, tops the list. According to the cloud services, he said.
NSA, misconfiguration of cloud resources remains the
most prevalent cloud vulnerability. Supply Chain Security
“Often arising from cloud service policy mistakes or Finally, the NSA says the No. 4 vulnerability — supply
misunderstanding shared responsibility, misconfiguration chain security flaws — remain rare, and require highly
has an impact that varies from denial of service sophisticated attackers. But many threat hunters and
susceptibility to account compromise,” the report says. security vendors agree supply chain security risks are
“The rapid pace of [cloud service providers’] innovation becoming more common and they expect to see these
creates new functionality but also adds complexity to types of attacks increase this year.
securely configuring an organization’s cloud resources.” Supply chain vulnerabilities include inside attackers,
intentional flaws and backdoors in hardware and
The report says least privilege and defense in depth
software, as well as companies’ partners and suppliers
are two of the security principles that organizations
whose security may not by up to par, and thus, allow
should apply from the planning phase. A least-privilege
attackers to access their targets’ cloud resources via
model restricts access for accounts to only the resources
their suppliers’ networks.
required to perform routine, legitimate activities.
Defense in depth involves placing multiple layers of Christiansen agrees that attackers need be pretty
security controls throughout an IT system. sophisticated to pull off a supply chain attack, but says
he was surprised to see it rated rare.
The No. 2 vulnerability — poor access control — happens
when companies have weak authentication methods in “You think about the big corporations and they have
place to allow access to cloud resources, or when these done a really good job of fortifying their security,” he
cloud resources have flaws that enable attackers to said. “But then when they go to a third party, the third
bypass these methods. The NSA deems this vulnerability party doesn’t have the same level of security, and that’s
widespread and says it requires a moderate level of when you are seeing the weakest-link problem. We’ve
sophistication to pull off. seen this as far back as the Target breach. It’s a very
© 2020 SDxCentral LLC. All Rights Reserved. 19
The Big Security Guide | NSA Ranks Cloud Security Risks
NEWS
big attack surface, and I believe that third parties are cloud environment, where organizations may run some
absolutely a target for state-sponsored attacks and workloads on AWS, others on Azure, and still others in
organized attacks.” a private cloud. “How do we bring all these multi-cloud
threat detection tools and be able to monitor these
While cloud service providers “mitigate the risk of inside
different environments? That point got a little lost. You
attackers through controls such as role separation,
have to look at not just one cloud provider, but all the
two-person integrity for especially sensitive operations,
cloud providers, and bring those all together in a single
and alerting on suspicious administrator activities,”
pane of glass.”
enterprises can improve their security posture against
supply chain compromise, the report says. This includes He also suggests putting controls in place to ensure that
encrypting data at rest and in transit, and also selecting the security and IT teams know when a business unit
cloud offerings that have had critical components uses a company credit card to purchase a new cloud
evaluated against National Information Assurance instance or even software-as-a-service. “A business unit
Partnership (NIAP) Protection Profiles (PPs). could do this, load confidential information on it, and it
would be completely insecure because we didn’t even
You Can’t Secure What You Can’t See
know about [it],” Christiansen said. “You can’t do all
Christiansen suggests the NSA report could have those things in the [NSA] guidance if you don’t know
included a couple additional pieces of cloud security about it.”
guidance.
Meet with the procurement and financial groups to
“The real salient parts are the right ones, and those are review credit card statements and look for cloud
the things companies should be looking at when they purchases, he said. And then, implement a policy that
evaluate their security strategy,” he said. “But where says “thou shalt not do this, enforce that policy, and
it’s less obvious” is in companies’ multi- and hybrid- educate your staff.”
© 2020 SDxCentral LLC. All Rights Reserved. 20
The Big Security Guide | Will SD-WAN Solve IoT’s Tough Questions?
NEWS
Will SD-WAN Solve IoT’s Tough Questions?
by Tobias Mann January 15, 2020
IoT and SD-WAN might not sound like they belong According to Casey, SD-WAN not only has the potential
to address many of the security concerns associated
together, but ask VMware’s VeloCloud or managed
with IoT, but it can also solve the operational challenges
service provider Apcela and you might be surprised by
of managing large deployments.
what they have to say. The two companies see SD-WAN
as the key to making large IoT deployments manageable Here, Apcela has some experience. The company has
at a human scale. been working with Itron, one of the leading makers of
smart water and energy meters, for the past two years.
Sanjay Uppal, who co-founded VeloCloud and now
serves as the head of VMware’s SD-WAN division, said Is SD-WAN the IoT Security Antidote?
the expanding scope of SD-WAN has opened the door Of all the challenges facing widespread IoT adoption,
to several applications that the technology wouldn’t security is undoubtedly the biggest concern. To this
normally be associated with, and IoT is one of them. point, Mary O’Neill, VP of security at Nokia, said IoT
devices represent just 16% of traffic but account for 78%
“You think of IoT, it’s not just IoT running on a cellular
of the malware on mobile networks.
network or IoT running on Bluetooth. You could
absolutely run IoT on your enterprise SD-WAN,” Uppal “If an IoT device today is plugged into the network,
said in an earlier interview. “Just think of that IoT traffic and it doesn’t have protection in it, it’s infected in three
as a new data type that you will steer across the WAN minutes or less,” she said during a press conference at
and you can add services to it as it is steered.” MWC Los Angeles in 2019.
While IoT may not be a new concept, with some Opening the edge to all of these devices poses a
companies having been in the business for decades, security challenge that isn’t easy to address, adds Casey.
the rise of IoT to the mainstream is forcing networks to “It’s one of the big things that companies are struggling
with.”
change, said Apcela CEO Mark Casey. “The evolution of
IoT requires a more agile and more nimble environment He explained that in a traditional architecture
to accelerate it, and for [IoT companies] to accelerate maintaining security would involve forcing device traffic
and grow their own revenue.” back to the data center.
© 2020 SDxCentral LLC. All Rights Reserved. 21
The Big Security Guide | Will SD-WAN Solve IoT’s Tough Questions?
NEWS
“So the ability to process things at the edge, manage to manually log into 100 routers to change the
security at the edge doesn’t really exist because of this configuration to accommodate the new traffic.
security issue,” Casey said. But that changes when you
“With SD-WAN everything is templatized. I can simply
apply an SD-WAN, he added. “Now we can treat traffic
enable a template for a new type of IoT traffic or a
very specifically.”
new customer, and I’m able to immediately deploy that
Itron builds smart meters for all kinds of customers, segmentation instantaneously because I have centralized
including water and energy companies as well as utilities orchestration, and that orchestration pushes the
and municipalities. configuration out to all of the edge locations,” he said.
“That doesn’t matter whether I have 10, 100, 1,000, or
“SD-WAN enables us to treat those traffic types — all
10,000 [locations].”
the way down to an individual IoT device — with an
independent profile,” Casey said. “We can take a specific Seeing the Problem
device for a specific customer and give that a specific
But even with the advantages SD-WAN offers in terms of
template that allows us to treat it from a security automation and orchestration, there remains a visibility
perspective uniquely and it allows us to treat it from an challenge. Just how do you manage a network with
edge processing standpoint uniquely.” the millions or billions of IoT devices that 5G networks
The result is finer-grained control over these massive IoT promise to enable? Some say the answer is artificial
deployments. “That’s one of the powerful things about intelligence (AI).
software-defined WAN,” he said. According to Ken Gold, director of test, monitoring,
But while SD-WAN may help address IoT’s security and analytics solutions at EXFO, the implicit complexity
challenges, not everyone is convinced it will be enough. associated with massive 5G IoT deployments is only
going to make identifying and resolving network
“Security is one of the biggest factors limiting IoT anomalies all the more challenging.
expansion,” said Bill Curtis, resident analyst at Moor
He said for most customers, a dropped call or
Insights & Strategy in an earlier interview with
broadband service outage isn’t a big deal. But
SDxCentral. “The bottom line,” he said, is that ”IoT
IoT deployments are less forgiving. And as these
security has to be built-in, not added on.”
deployments march toward large-scale adoption, the
IoT Management on a Human Scale need for accurate bandwidth and traffic demands is
going to accelerate rapidly.
However, even if SD-WAN can’t fully address IoT’s
security challenges, it at least stands a chance to make Gold says machine learning, and eventually AI, has the
the networks supporting them more manageable. potential to make these networks more reliable and
manageable.
Casey explained that SD-WAN enables network
programmability and automation. This means that new In the near term, Casey sees these kinds of tools as a
types of devices can be added to the network without way to enable network operators to quickly address
the need for additional backend hardware. “I can just and resolve performance issues, and perhaps eventually
reprogram the software to deal with a new type of IoT resolve them automatically based on policy.
device or a new type of IoT traffic,“ he said.
“The reality is when you have an application
This has the potential to reduce the operational performance problem, 80% of the time is spent finding
requirements of managing these networks at scale. the problem, and only 20% is spent fixing it,” he said.
Casey said if an IoT company with 100 locations
across the United States wants to add a new device,
that traditionally would mean someone would have
© 2020 SDxCentral LLC. All Rights Reserved. 22
The Big Security Guide | Cisco Study: Data Privacy ROI for Businesses
NEWS
Cisco Study: Data Privacy ROI for Businesses
by Sydney Sawaya January 27, 2020
On the eve of World Privacy Day (Jan. 28), findings from surveyed saw at least double the return on their privacy
Cisco‘s 2020 data privacy study show that privacy is, in investment.
fact, a very good investment.
“I think companies are beginning to recognize that this
Where companies used to prioritize things like function privacy thing is important, not just as a compliance issue
and scalability over data privacy and security, consumer or a boardroom issue, but because it matters to the
backlash to privacy leaks in recent years has elicited customers, building loyalty and trust in the company,”
a global response for new legislation. Regulatory data explained Robert Waitman, Cisco’s director of privacy
privacy laws like the EU’s General Data Protection insights and innovation, in an interview with SDxCentral.
Regulation (GDPR) paved the way for countries
from China to Brazil and even individual states — like Privacy Pays Profits
California and its new California Consumer Privacy Act 70% organizations said they found significant business
(CCPA) — to follow suit. In fact, U.S. legislators are also benefits from privacy, and 74% of respondents believed
considering an updated federal privacy law. that going above and beyond privacy regulation
For the report, Cisco researchers spoke with 2,800 compliance helped them build loyalty and trust with
security professionals in 13 countries about privacy and their customers.
data security practices within their organization. A key
“This is about doing the right thing so that your
finding quantified the return on investment (ROI) on
customers believe that you’re taking good care of their
privacy, which averaged a 270% ROI.
data, and want you to continue to do that,” Waitman
Organizations with an increased focus on privacy said. “Because, again, at the end of the day, privacy is
saw shorter sales delays, better security, and fewer about protecting people. And those people are your
data breaches. And more than 40% of the companies customers.”
© 2020 SDxCentral LLC. All Rights Reserved. 23
The Big Security Guide | Cisco Study: Data Privacy ROI for Businesses
NEWS
The survey reported 82% of companies had a breach in store them somewhere else,” Waitman said. “You might
the past year. make them even harder to get access, because at some
point an intruder is going to come in.”
Companies with higher accountability scores — as
assessed using the Centre for Information Policy Legislative processes such as GDPR have pressured
Leadership’s Accountability Wheel, which is a framework businesses to get their data houses in order —
for managing and assessing organizational maturity — protecting valuable assets and throwing out old ones
experienced shorter sales delays and higher financial to minimize the loss that might occur when and if that
returns. break in does happen.
In fact, of the companies with advanced privacy efforts, Although some businesses might see privacy regulations
28% went breach-free compared to the 13% of those as another hurdle to clear, Cicso’s findings position
with minimal privacy efforts. The more advanced legislative processes as a worthy ally in driving net
organizations had 90% less downtime from records benefits for businesses. Furthermore, the findings also
exfiltrated, which translates to cost. reaffirm Cisco’s 2019 privacy report, which found GDPR-
Get Your Data House in Order ready firms had fewer data breaches.
Data privacy and security converge in what Waitman While the study proves the positive benefits of
called the “data house,” and he used the analogy of regulation, Waitman stressed the need to proceed
preparing for a home invasion. He explained how you with caution. He said Cisco supports federal legislation
might prepare for a home invasion if you knew someone that would allow companies to pursue one standard to
was going to break into your house sometime this year establish consistency across all 50 states.
— even with no knowledge of when or where the break
“I think the idea of having a federal legislation would
in would occur.
be to avoid 50 different state regulations, but not
“You would probably take the most sensitive assets that to change, or perhaps hamper some of the valuable
you have, your most valuable things, and you would do protections that are in place for some of the industries
something further to either protect them, encrypt them, today,” Waitman said.
© 2020 SDxCentral LLC. All Rights Reserved. 24
SDxCentral, LLC
3511 Ringsby Ct, #101
Denver, CO 80216 USA
www.sdxcentral.com
Вам также может понравиться
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Priority ConservationДокумент6 страницPriority Conservationapi-213428788Оценок пока нет
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- Statistical Analysis With R - A Quick StartДокумент47 страницStatistical Analysis With R - A Quick StartPonlapat Yonglitthipagon100% (1)
- Different Approaches To Crack Monitoring of Buildings Using IOTДокумент11 страницDifferent Approaches To Crack Monitoring of Buildings Using IOTIJRASETPublicationsОценок пока нет
- Udacity Enterprise Syllabus Enterprise Security nd0035Документ15 страницUdacity Enterprise Syllabus Enterprise Security nd0035Saturnin DeglaОценок пока нет
- Iedscout: Versatile Software Tool For Working With Iec 61850 DevicesДокумент12 страницIedscout: Versatile Software Tool For Working With Iec 61850 DeviceshmhaidarОценок пока нет
- Region Memo Asd 16 Reinforcement of Guidelines and Process Flow On Reclassification of Teaching PersonnelДокумент7 страницRegion Memo Asd 16 Reinforcement of Guidelines and Process Flow On Reclassification of Teaching PersonnelJuan LorenzoОценок пока нет
- 2022 Visual Object Tracking A SurveyДокумент42 страницы2022 Visual Object Tracking A SurveyPaulОценок пока нет
- Account Statement From 13 Jun 2021 To 13 Dec 2021Документ10 страницAccount Statement From 13 Jun 2021 To 13 Dec 2021Syamprasad P BОценок пока нет
- Physics II ProblemsДокумент1 страницаPhysics II ProblemsBOSS BOSSОценок пока нет
- Udemy Bonus LecturesДокумент3 страницыUdemy Bonus LecturesAbhishekОценок пока нет
- ACESYS V8.0 - User Manual - AlternateДокумент12 страницACESYS V8.0 - User Manual - AlternateMohamed AdelОценок пока нет
- HUAWEI - SD-WAN SolutionДокумент235 страницHUAWEI - SD-WAN Solutionbuafac10Оценок пока нет
- TopFlite Components - Tinel - Lock® RingДокумент1 страницаTopFlite Components - Tinel - Lock® Ringbruce774Оценок пока нет
- St. Therese School Second Periodic Test Mapeh 2Документ4 страницыSt. Therese School Second Periodic Test Mapeh 2dona manuela elementary schoolОценок пока нет
- Chapter 7 - Inheritance and InterfacesДокумент53 страницыChapter 7 - Inheritance and Interfacesvicrattlehead2013Оценок пока нет
- Flitedeck Pro X: Release NotesДокумент28 страницFlitedeck Pro X: Release NotesŁukasz BarzykОценок пока нет
- TB6500 ManualДокумент11 страницTB6500 ManualEnrique BautistaОценок пока нет
- Awa Se E Dura GiyaДокумент6 страницAwa Se E Dura GiyaChathura KumaraОценок пока нет
- RobotStudio Simulation of Industrial PDFДокумент140 страницRobotStudio Simulation of Industrial PDFcabecavil100% (1)
- PNP Switching Transistor: FeatureДокумент2 страницыPNP Switching Transistor: FeatureismailinesОценок пока нет
- Contact NumbersДокумент22 страницыContact NumbersUsamaОценок пока нет
- 25+ Tricky SAP BODS Interview Questions 3Документ1 страница25+ Tricky SAP BODS Interview Questions 3pattabhikvОценок пока нет
- Technical SpecificationsДокумент9 страницTechnical SpecificationsVitalii LiakhОценок пока нет
- CS201 Introduction To Programming Solved MID Term Paper 03Документ4 страницыCS201 Introduction To Programming Solved MID Term Paper 03ayesharahimОценок пока нет
- Symbol Master Multi-Pass Symbolic Disassembler Manual V2.0 (Feb 2 1986)Документ68 страницSymbol Master Multi-Pass Symbolic Disassembler Manual V2.0 (Feb 2 1986)weirdocolectorОценок пока нет
- Pandapower PDFДокумент167 страницPandapower PDFAlen TatalovićОценок пока нет
- Lea Dardanos Efi-Controller eДокумент6 страницLea Dardanos Efi-Controller eadfumegaОценок пока нет
- Source Code Ijtima Falakiyin NUsanataraДокумент187 страницSource Code Ijtima Falakiyin NUsanataraUlum NiОценок пока нет
- An Open-Source Platform For Underwater Image and Video AnalyticsДокумент10 страницAn Open-Source Platform For Underwater Image and Video AnalyticsvijayforrockОценок пока нет
- MP Unit-3Документ24 страницыMP Unit-3SARTHAK PANWARОценок пока нет