Академический Документы
Профессиональный Документы
Культура Документы
Learning Module - Empowerment Technologies
Загружено:
Neil Trezley Sunico BalajadiaАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Learning Module - Empowerment Technologies
Загружено:
Neil Trezley Sunico BalajadiaАвторское право:
Доступные форматы
Matutum View Academy
The School of Faith
Acmonan, Tupi, South Cotabato
Empowerment
Technologies
Learning Module
First Grading
Teacher: Dave Gaurino
Contact Number: 09081568177
Facebook: www.facebook.com/davegaurino
Email: davemvamedia@gmail.com
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 1
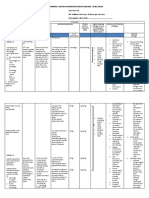
Table of Contents
LESSON 1: INTRODUCTION TO INFORMATION AND COMMUNICATION TECHNOLOGIES.....................2
Vocabularies/ Glossary of Terms.......................................................................................................................................2
Features of Web 2.0..........................................................................................................................................................3
Web 3.0 Problems:............................................................................................................................................................3
Trends in ICT...................................................................................................................................................................... 3
Internet Threats................................................................................................................................................................ 4
ACTIVITY 1.1........................................................................................................................................................5
ACTIVITY 1.2........................................................................................................................................................7
LESSON 2: RULES OF NETIQUETTE...........................................................................................................................8
Protecting Reputations Online..........................................................................................................................................8
Copyright Infringement.....................................................................................................................................................8
Online Research................................................................................................................................................................ 8
ACTIVITY 2.1........................................................................................................................................................9
ACTIVITY 2.2........................................................................................................................................................9
LESSON 3: ADVANCED WORDS PROCESSING SKILLS........................................................................................10
Mail Merge...................................................................................................................................................................... 10
Kinds of Materials........................................................................................................................................................10
Image Placement.........................................................................................................................................................11
ACTIVITY 3.........................................................................................................................................................12
LESSON 4: ADVANCED SPREADSHEET SKILLS....................................................................................................13
Excel Vocabularies / Glossary of Terms...........................................................................................................................13
ACTIVITY 4.........................................................................................................................................................13
Empowerment Technologies - Notes & Activities
Lesson 1: Introduction to Information and Communication Technologies
What is Information and Communications Technology?
Vocabularies/ Glossary of Terms
Information and Communication Technology - Deals with the use of different communication technologies such as
mobile phones, telephone, Internet to locate, save, send and edit information.
Computer - an electronic device for storing and processing data, typically in binary form, according to instructions
given to it in a variable program.
Internet - is a worldwide system of computer networks which the users at any one computer can use to get
information from any other computer.
World Wide Web - an information system on the internet that allows documents to be connected to other
documents by hypertext links, enabling the user to search for information by moving from one document to
another.
Web page - is a hypertext document connected to the World Wide Web. It is a document that is suitable for the
World Wide Web.
Web 1.0 - static websites without interactivity.
Web 2.0 - websites that contain dynamic content.
Web 3.0 - a concept of the World Wide Web that is designed to cater to the individual user.
Static - refers to web pages that are the same regardless of the user.
Dynamic - refers to web pages that are affected by user input or preference.
Hashtag - used to "categorize" posts in website.
Convergence - the synergy of technological advancements to work on a similar goal or task.
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 2
Social media - websites, applications, or online channels that enable users to create, co-create, discuss, modify, and
exchange user-generated content.
Features of Web 2.0
1. Folksonomy - allows users to categorize and classify/arrange information.
2. Rich User Experience - content is dynamic and is responsive to user's input.
3. User Participation - the owner of the website is not the only one who is able to put content. Others are able to place
a content of their own by means of comments, reviews, and evaluation, Some websites allow readers to comment
on an article, participate in a poll, or review a specific product.
4. Long Tail - services that are offered on demand rather than on a one-time purchase.
5. Software as a Service - users will subscribe to a software only when needed rather than purchasing them.
6. Mass Participation - diverse information sharing through universal web access. The content is based on people from
various cultures.
Tim Berners-Lee - the inventor of the World Wide Web.
Semantic Web - provides a common framework that allows data to be shared and reused across application, enterprise,
and community boundaries.
Web 3.0 Problems:
1. Compatibility - HTML files and current web browsers could not support Web 3.0.
2. Security - the user's security is also in question since the machine is saving his or her preferences.
3. Vastness - the World Wide Web already contains billions of web pages.
4. Vagueness - Certain words are imprecise or inaccurate.
5. Logic - there are certain limitations for a computer to be able to predict what the user is referring to at a given time.
Trends in ICT
1. Convergence - is the synergy of technological advancements to work on a similar goal or task.
2. Social media - a website, application, or online channel that enables web users to create, co-create, discuss, and
exchange user-generated content.
a) Social Networks - these are sites that allow you to connect with other people with the same interests or
background. Examples: Facebook and Google+
b) Bookmarking Sites - these are sites that allow you to store and manage links to various websites and resources.
Most of these sites allow you to create a tag that allows you and others to easily search or share them.
Examples: StumbleUpon and Pinterest
c) Social News - these are sites that allow users to post their own news items or links to other news sources. The
users can also comment on the post and comments may also be ranked. They are also capable of voting on
these news articles of the website. Those who get the most amount of votes are shown most prominently.
Examples: reddit and Digg
d) Media Sharing - These are sites that allow you to upload and share media content like images, music, and video.
Most of these sites have additional social features like liking, commenting, and having user profiles. Examples:
Flicker, YouTube, and Instagram.
e) Microblogging - these are sites that focus on short updates from the user. Those subscribed to the user will be
able to receive these updates. Examples: Twitter and Plurk
f) Blogs and Forums - these websites allow users to post their content. Other users are able to comment on the
said topic. There are several free blogging platforms like Blogger, WordPress, and Tumblr.
3. Mobile Technologies
Smartphones and tablets - devices with capability to do tasks that were originally found in personal computers. Several
of these devices are capable of using high-speed Internet. Today, the latest mobile devices use 4G Networking (LTE),
which is currently the fastest mobile network.
Different mobile devices Operating Systems:
a) iOS - used in Apple devices such as the iPhone and iPad.
b) Android — an open source operating system developed by Google.
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 3
c) Blackberry OS - used in Blackberry devices
d) Windows Phone OS - a closed source and proprietary operating system developed by Microsoft
e) Symbian - the original smartphone OS; used by Nokia devices
f) WebOS - originally used for smartphones; now used for smart TVs
g) Windows Mobile - developed by Microsoft for smartphones and pocket PCs
Open Source - means several mobile phone companies use this OS for free.
4. Assistive Media - a service to help people who have visual and reading impairments.
Internet Threats
1. Malware - stands for malicious software.
a) Virus - a malicious program designed to replicate itself and transfer from one computer to another either
through the Internet and local networks or data storage like flash drives and CDs.
b) Worm - a malicious program that transfers from one computer to another by any type of means. Often, it uses a
computer network to spread itself. For example, the ILOVEYOU worm (Love Bug Worm) created by a Filipino.
c) Trojan - a malicious program that is disguised as a useful program but once downloaded or installed, leaves your
PC unprotected and allows hackers to get your information.
*Rogue security software - tricks the user into posing that it is a security software, It asks the user to pay to improve
his/her security but in reality, they are not protected at all.
d) Spyware - a program that runs in the background without you knowing it (thus called "spy"). It has the ability to
monitor what you are currently doing and typing through keylogging.
*Keyloggers - used to record the keystroke done by the users. This is done to steal their password or any other
sensitive information. It can record email, messages, or any information you type using your keyboard.
e) Adware - a program designed to send you advertisements, mostly as pop-ups.
2. Spam - unwanted email mostly from bots or advertisers. It can be used to send malware.
3. Phishing - Its goal is to acquire sensitive personal information like passwords and credit card details. This is done by
sending you an email that will direct the user to visit a website and be asked to update his/her username, password,
credit card, or personal information.
*Pharming - a more complicated way of phishing where it exploits the DNS (Domain Name Service) system.
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 4
ACTIVITY 1.1
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 5
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 6
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 7
ACTIVITY 1.2
Exploration: Identifying the correct web platform for social change.
1. Identify a problem in your community (e.g. littering, garbage disposal, blocked drainages, quarantine, etc.)
2. Imagine that you are going to create social awareness to persuade both community leaders and members to solve
this problem.
3. Read the “Trends in ICT” lesson on page 3 to answer this activity.
Community Problem: ______________________________________________________________________________
Vicinity: ________________________________________________________________________________________
Campaign Name:__________________________________________________________________________________
Type of Social Media Used: __________________________________________________________________________
Website Used: ____________________________________________________________________________________
1. What will be the content of your social media site?
________________________________________________________________________________________________
________________________________________________________________________________________________
________________________________________________________________________________________________
________________________________________________________________________________________________
2. Why did you choose that type of social media?
________________________________________________________________________________________________
__________________________________________________________________________________________________
__________________________________________________________________________________________________
____________________________________________________________________________________________
3. Why did you choose that website?
________________________________________________________________________________________________
__________________________________________________________________________________________________
__________________________________________________________________________________________________
____________________________________________________________________________________________
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 8
Lesson 2: Rules of Netiquette
Protecting Reputations Online
1. Before you post something on the web, ask these questions to yourself: Would you want your parents or
grandparents to see it? Would you want your future boss to see it? Once you post something on the web, you have
no control of who sees your posts.
2. Your friends depend on you to protect their reputation online. Talk to your friends about this serious responsibility.
3. Set your post to "private." In this way, search engines will not be able to scan that post.
4. Avoid using names. Names are easy for search engines to scan.
5. If you feel that a post can affect you or other's reputation, ask the one who posted it to pull it down or report it as
inappropriate.
Copyright Infringement
Intellectual property - If you create something: an idea, an invention, a form of literary work, or a research, you have
the right as to how it should be used by others.
Here are some tips that could help you avoid copyright infringement:
1. Understand. Copyright protects literary works, photographs, paintings, drawings, films, music (and lyrics),
choreography, and sculptures, but it generally does NOT protect underlying ideas and facts. This means that you can
express something using your own words, but you should give credit to the source.
2. Be responsible. Even if a material does not say that it is copyrighted, it is not a valid defense against copyright. Be
responsible enough to know if something has a copyright.
3. Be creative. Ask yourself whether what you are making is something that came from you or something made from
somebody else's creativity. It is important to add your own creative genius in everything that will be credited to you.
4. Know the law. There are some limitations to copyright laws. For instance in the Philippines, copyrights only last a
lifetime (of the author) plus 50 years. There are also provisions for "fair use" which mean that an intellectual
property may be used without a consent as long as it is used in commentaries, criticisms, search engines, parodies,
news reports, research, library archiving, teaching, and education. If you have doubts that what you are doing does
not fall under the policy of fair use, seek permission first.
Another misconception is that fan-fiction is not copyright infringement. In reality, it is and some copyright holders
ignore them but they can opt to use their rights.
Online Research
1. Have a question in mind. Focus on a question you want answered. If it is a series of questions, start with one. Never
search everything on one go.
2. Narrow it down. Search engines like Google, Bing, or Yahoo use several filters to determine the most appropriate
result for you.
3. Advanced Search. The best way to filter information you get from search engines is by using the advanced search.
This will allow you to filter out information you do not need.
Symbol Function
Finds web pages that contain all the terms that are preceded by the + symbol; allows you to include
+ terms that are usually ignored.
“ ” Finds the exact words in a phrase.
( ) Finds or excludes web pages that contain a group of words.
AND or & Finds web pages that contain all the terms or phrases
NOT or - Excludes web pages that contain a term or phrase
OR or | Finds web pages that contain either of the terms or phrases
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 9
4. Look for a credible source. Some wikis, though filled with updated information, are not a credible source. This is due
to the fact that anyone can edit its content. When using wikis, check out the link of the cited text (indicated by
superscript number) to be navigated to the footnote where the list of sources is located. Click the source of the
information and see if it is credible.
5. Give credit. If you are going to use the information from source for educational purposes, give credit to the original
author of the page or information.
Cybercrime - a crime committed or assisted through the use of the Internet
Privacy policy - tells the user how the website will handle its data.
Copyright - a part of the law, wherein you have the rights to your work and anyone who uses it without your
consent is punishable by law.
Fair use - means that an intellectual property may be used without a consent as long as it is used in commentaries,
criticisms, search engines, parodies, news reports, research, library archiving, teaching, and education.
ACTIVITY 2.1
Essay: Write an explanation of the following questions.
1. Why should you “Think before you click”?
__________________________________________________________________________________________________
__________________________________________________________________________________________________
__________________________________________________________________________________________________
2. How would you feel if someone posted something embarrassing about you? What would you do?
__________________________________________________________________________________________________
__________________________________________________________________________________________________
__________________________________________________________________________________________________
ACTIVITY 2.2
TRUE OR FALSE: Write T if the statement is true. Write F if the statement is false.
1. _______ "Fair use" tells the user how the website will handle its data.
2. _______ A fan-fiction is not copyright infringement.
3. _______ Copyright does NOT protect literary works, photographs, paintings, drawings, films, music (and lyrics),
choreography, and sculptures.
4. _______ Copyright does NOT protect underlying ideas and facts.
5. _______ Copyright is a part of the law, wherein you have the rights to your work and anyone who uses it without
your consent is punishable by law.
6. _______ Copyright mean that an intellectual property may be used without a consent as long as it is used in
commentaries, criticisms, search engines, parodies, news reports, research, library archiving, teaching, and
education.
7. _______ Copyrights only last a lifetime (of the author) plus 5 years.
8. _______ Cyberspace is a crime committed or assisted through the use of the Internet.
9. _______ Google, Bing, and Yahoo are examples of web browser.
10. _______ If a material does not say that it is copyrighted, it is a valid defense against copyright.
11. _______ If you are going to use the information from source for educational purposes, give credit to the original
author of the page or information.
12. _______ Some wikis, though filled with updated information, are not a credible source.
13. _______ The best way to filter information you get from search engines is by using the advanced search.
14. _______ When you research something, never search everything on one go.
15. _______ Privacy policy means that an intellectual property may be used without a consent.
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 10
MATCHING TYPE: Match the symbol to its meaning. Write the letter of the correct answer on the space provided.
A. ( ) 16. _______ Excludes web pages that contain a term or phrase.
B. “ ” 17. _______ Finds or excludes web pages that contain a group of words.
C. + 18. _______ Finds the exact words in a phrase.
D. AND or & 19. _______ Finds web pages that contain all the terms or phrases.
E. NOT or - 20. _______ Finds web pages that contain all the terms.
F. OR or | 21. _______ Finds web pages that contain either of the terms or phrases.
Lesson 3: Advanced Words Processing Skills
Mail Merge
Mail Merge - this feature allows you to create documents and combine or merge them with another document or data
file. It is commonly used when sending out advertising materials to various recipients.
Two Components of Mail Merge
1. Form Document - the document that contains the main body of the message we want to convey or send. The main
body of the message that remains the same no matter whom you send it to from among your list.
Place holders, data fields or merge fields - marks the position on your form document where individual data or
information will be inserted.
2. Data File - this is where the individual information or data that needs to be plugged in (merged) to the form
document is placed and maintained.
Label Generator - it will print individual addresses to a standard form that it has already pre-formatted. It creates a
blank form document that simulates either a blank label or envelope of pre-defined size and will use the data file
that you selected to print the information, typically individual addresses.
Kinds of Materials
1. Pictures - are electronic or digital pictures or photographs you have saved in any local storage device. There are
three commonly used types of picture files.
JPG - this type of image file can support 16.7 million colors that is why it is suitable for use when working with full
color photographic images. Unfortunately, it does not support transparency and therefore, images of this file type
can be difficult to integrate in terms of blending with other materials or elements in your document. If you are
looking for the best quality image to integrate with your document, then this is the image file type for you. .JPG does
not work well on lettering, line drawings, or simple graphics. .JPG images are relatively small in file size.
GIF - this type of image file is capable of displaying transparencies. Therefore, it is good for blending with other
materials or elements in your document. It is also capable of displaying simple animation. This may not be too useful
on a printed document but if you are sending documents electronically or through email, or even post documents
into a website, then this could be quite impressive. It can only support up to 256 colors so it is good mostly on logos
and art decors with very limited, and generally solid colors. .GIF is much better for logos, drawings, small text, black
and white images, or low-resolution files.
PNG - this type of image file is for transporting images on the Internet at faster rates. It is also good with
transparencies but unlike .GlFs, it does not support animation but it can display up to about 16 million colors, so
image quality for this image file type is also remarkably improved. .PNG allows the control of the transparency level
or opacity of images.
2. Clip Art - this is generally a .GIF type; line art drawings or images used as generic representation for ideas and
objects that you might want to integrate in your document.
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 11
3. Smart Art - predefined sets of different shapes grouped together to form ideas that are organizational or structural
in nature. If you want to graphically represent an organization, process, relationships, or flow for infographic
documents, then you will find this easy and handy to use.
4. Chart - allows you to represent data characteristics and trends. This is quite useful when you are preparing reports
that correlate and present data in a graphical manner.
Image Placement
Text Wrap - adjusts how the image behaves around other objects or text.
In Line with Text - it treats your image like a text font with the bottom side totally aligned with the text line. This
setting is usually used when you need to place your image at the beginning of a paragraph.
Square - this setting allows the image you inserted to be placed anywhere within the paragraph with the text going
around the image in a square pattern like a frame.
`
Tight - in this setting the text "hugs" or conforms to the general shape of the image. This allows you to get a more
creative effect on your document.
Through - this setting allows the text on your document to flow even tighter, taking the contours and shape of the
image.
Top and Bottom - this setting pushes the texts away vertically to the top and/or the bottom of the image so that the
image occupies a whole text line on its own.
Behind Text - This setting allows your image to be dragged and placed anywhere on your document but with all the
texts floating in front of it. It effectively makes your image look like a background.
In Front of Text - this setting allows your image to be placed right on top of the text as if your image was dropped
right on it. That means whatever part of the text you placed the image on, it will be covered by the image.
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 12
ACTIVITY 3
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 13
Lesson 4: Advanced Spreadsheet Skills
Excel Vocabularies / Glossary of Terms
Accounting Number Format - a number format that is used for accounting.
Orientation - the angle at which a text is displayed.
Count - a function used to count the cells with content in a range.
Sum - a function used to compute for the summation of the number of a range.
Average - a function used to compute for the average of the number of a range.
COUNTIF - a function used to count the cells with a specified content within range.
SUMIF - a function used to compute for the summation of a range if a certain condition is met.
AVERAGEIF - a function used to compute for the average of a range if a certain condition is met.
Range - the range of cells where you want to look for the criteria.
Criteria - a value or label that determines if a cell is part of the range to be averaged.
Average Range - the actual range of cells that will be averaged, if omitted, the range will be used instead.
ACTIVITY 4
Teacher: Dave R. Gaurino EMPOWERMENT TECHNOLOGIES - MATUTUM VIEW ACADEMY Page 14
Вам также может понравиться
- Empowerment Technologies Module1 1 3Документ48 страницEmpowerment Technologies Module1 1 3chwe sevenith100% (1)
- Emptech ModuleДокумент44 страницыEmptech ModuleANNELIESEОценок пока нет
- Empowerment Technologies ACID PLANДокумент14 страницEmpowerment Technologies ACID PLANHendrix Antonni Amante100% (6)
- Empowerment Technologies Lesson 1Документ38 страницEmpowerment Technologies Lesson 1Marck LeanОценок пока нет
- Empowerment 2Документ16 страницEmpowerment 2gRascia Ona100% (1)
- Empowerment Technology Learners PacketДокумент45 страницEmpowerment Technology Learners PacketphinОценок пока нет
- Empowerment Technology REVISED Lesson 1 17finalДокумент127 страницEmpowerment Technology REVISED Lesson 1 17finalJefferson Medinaceli Malayao100% (7)
- Lesson Plan - EmTech - 12 - Q3L2 - Online Safety, Security, Ethics and EtiquetteДокумент4 страницыLesson Plan - EmTech - 12 - Q3L2 - Online Safety, Security, Ethics and Etiquettejfmefrannz50% (2)
- Empowerment 3Документ15 страницEmpowerment 3gRascia Ona0% (1)
- L2 Rules of NetiquetteДокумент55 страницL2 Rules of NetiquetteAnonymous yleNWzd9Оценок пока нет
- Module 4 - E. Tech.Документ7 страницModule 4 - E. Tech.Darry BlanciaОценок пока нет
- ICT - Empowerment Technologies Quarter1Module4 PDFДокумент56 страницICT - Empowerment Technologies Quarter1Module4 PDFGie DanОценок пока нет
- Empowerment TechnologiesДокумент3 страницыEmpowerment TechnologiesStephany Bryan Diez ItaoОценок пока нет
- EMPOWERMENT MODULE 1 - New VerДокумент29 страницEMPOWERMENT MODULE 1 - New VergRascia Ona100% (2)
- Ict As Platform For ChangeДокумент3 страницыIct As Platform For ChangeJhelie ChagulonОценок пока нет
- FINAL Module 1 Empowerment Technology GR 11Документ14 страницFINAL Module 1 Empowerment Technology GR 11Mars Indy100% (2)
- Empowerment Module 5Документ21 страницаEmpowerment Module 5gRascia Ona81% (21)
- Empowerment Technology: Quarter 1 - Module 1Документ49 страницEmpowerment Technology: Quarter 1 - Module 1Juvy Banlaoi Reyes Domingo100% (1)
- Empowerment Technology Lesson 1Документ31 страницаEmpowerment Technology Lesson 1Rowel Elca0% (1)
- Empowerment Technology: Guided Learning Activity KitДокумент16 страницEmpowerment Technology: Guided Learning Activity KitMlyn100% (2)
- Lesson 3 Advanced - Word - Processing - SkillsДокумент19 страницLesson 3 Advanced - Word - Processing - SkillsChristine Jade Montera0% (1)
- Online Safety, Security, Ethics, and EtiquetteДокумент24 страницыOnline Safety, Security, Ethics, and EtiquetteSherwin SantosОценок пока нет
- Empowerment TechnologyДокумент43 страницыEmpowerment TechnologyBryan GianganОценок пока нет
- Empowerment Technologies - Lesson 5Документ23 страницыEmpowerment Technologies - Lesson 5Marck LeanОценок пока нет
- Lesson Plan in Empowerment TechnologiesДокумент5 страницLesson Plan in Empowerment TechnologiesArcee Ardiente Mondragon78% (9)
- Lesson Exemplar IDEA em TechДокумент8 страницLesson Exemplar IDEA em TechTjhay Noche100% (1)
- EmpTech11 - Q1 - Mod1 - ICT in The Context of Global Communication - Ver3 PDFДокумент52 страницыEmpTech11 - Q1 - Mod1 - ICT in The Context of Global Communication - Ver3 PDFMark Marasigan100% (6)
- SHS Empowerment Technology Weeks 1 2Документ13 страницSHS Empowerment Technology Weeks 1 2John Benedict Albay100% (1)
- Empowerment TechnologiesДокумент4 страницыEmpowerment Technologieskristoffer50% (6)
- Empowerment Technology SHS DocsДокумент60 страницEmpowerment Technology SHS DocsAllan IgbuhayОценок пока нет
- Empowerment Module 1Документ37 страницEmpowerment Module 1Arthur CapawingОценок пока нет
- Lesson 2.1: Online Safety, Security and NetiquetteДокумент11 страницLesson 2.1: Online Safety, Security and NetiquetteJared Panes SiaОценок пока нет
- TVL Empowerment Technologies q3 m1Документ14 страницTVL Empowerment Technologies q3 m1Ofelia Oredina67% (3)
- Lesson Plan - EmTech - 12 - Q3L4 - Applied Productivity Tools With Advanced Application TechniquesДокумент4 страницыLesson Plan - EmTech - 12 - Q3L4 - Applied Productivity Tools With Advanced Application Techniquesjfmefrannz100% (3)
- EmpTech - Q1 - Mod1 - Current State of ICTДокумент10 страницEmpTech - Q1 - Mod1 - Current State of ICTjecelyn mae BaluroОценок пока нет
- EmpTech - Q1 - Mod11 - Imaging Design For Online EnvironmentДокумент12 страницEmpTech - Q1 - Mod11 - Imaging Design For Online Environmentjecelyn mae BaluroОценок пока нет
- Cs Ict11 12 Ictpt Ia B 1sesion3&4Документ3 страницыCs Ict11 12 Ictpt Ia B 1sesion3&4Milton Pates100% (6)
- Empowerment Technology Teacher's GuideДокумент25 страницEmpowerment Technology Teacher's Guidekaren bacquialОценок пока нет
- Applied Productivity Tools With Advanced Application TechniquesДокумент5 страницApplied Productivity Tools With Advanced Application TechniquesGrace RedondoОценок пока нет
- Empowerment Technologies ADM WEEK 1Документ18 страницEmpowerment Technologies ADM WEEK 1Kristi Madanlo83% (6)
- Empowerment Summative TestДокумент3 страницыEmpowerment Summative TestEl-el Galindo MascariňasОценок пока нет
- Publishing An Ict Project: Quarter 2-Module 4Документ45 страницPublishing An Ict Project: Quarter 2-Module 4Carl Jade Regacion100% (11)
- I. Objectives: School Grade Level Teacher Learning Area Time & Dates QuarterДокумент3 страницыI. Objectives: School Grade Level Teacher Learning Area Time & Dates Quarterlyndon Reciña100% (1)
- Imaging and Design For Online EnvironmentДокумент1 страницаImaging and Design For Online EnvironmentRichard Melvin GarciaОценок пока нет
- Empowerment 1Документ23 страницыEmpowerment 1gRascia OnaОценок пока нет
- Module 5-6 Empowerment Technology-Week 5 - 6Документ27 страницModule 5-6 Empowerment Technology-Week 5 - 6aldrin joseph100% (9)
- Empowerment Technology Week 3-4Документ15 страницEmpowerment Technology Week 3-4Sonia Agustin100% (3)
- Etech q2 Mod4 How To Manage An Online ICT Project For Social ChangeДокумент34 страницыEtech q2 Mod4 How To Manage An Online ICT Project For Social ChangeRochelle VentirezОценок пока нет
- Empowerment TechnologyДокумент10 страницEmpowerment TechnologyCharles100% (2)
- TVL Empowerment Technologies q3 m2Документ15 страницTVL Empowerment Technologies q3 m2Micah Diane FamorcanОценок пока нет
- Empowerment Technologies: Quarter 1 - Module 3: Contextualized Online Search and Research SkillsДокумент23 страницыEmpowerment Technologies: Quarter 1 - Module 3: Contextualized Online Search and Research SkillsDeonise rafaela Ibayan100% (2)
- Basic Techniques of Image ManipulationДокумент8 страницBasic Techniques of Image ManipulationAllyza Princess Peradilla MagpantayОценок пока нет
- Empowerment 2Документ39 страницEmpowerment 2Lee Oh100% (2)
- Application Development and Emergin TechnologiesДокумент3 страницыApplication Development and Emergin TechnologiesMarvic Vinuya AblazaОценок пока нет
- EMP TECH Q2 Multimedia and ICTДокумент12 страницEMP TECH Q2 Multimedia and ICTPRACTICAL RESEARCH1100% (1)
- Inc. Integrated Basic Education Department: Lourdes CollegeДокумент12 страницInc. Integrated Basic Education Department: Lourdes CollegeLar KenОценок пока нет
- Empowerment Tech Module 1Документ8 страницEmpowerment Tech Module 1Don BesicОценок пока нет
- Emptech Module 1stДокумент44 страницыEmptech Module 1stDENNIS JOHN ACOSTAОценок пока нет
- Empowerment Technology: Senior High School Instructional ModuleДокумент25 страницEmpowerment Technology: Senior High School Instructional ModuleRica VillanuevaОценок пока нет
- ICT Empowerment-Technologies Q1 Module1Документ18 страницICT Empowerment-Technologies Q1 Module1Luckyluige Nagbuya100% (1)
- Research Design RequirementДокумент15 страницResearch Design RequirementNeil Trezley Sunico BalajadiaОценок пока нет
- Matutum View Academy: (The School of Faith)Документ13 страницMatutum View Academy: (The School of Faith)Neil Trezley Sunico BalajadiaОценок пока нет
- FABM2 Q1 Mod2 Statement-Of-Comprehensive-Income v2Документ24 страницыFABM2 Q1 Mod2 Statement-Of-Comprehensive-Income v2Neil Trezley Sunico BalajadiaОценок пока нет
- Dedication LitanyДокумент1 страницаDedication LitanyNeil Trezley Sunico BalajadiaОценок пока нет
- Math11statprob FinalsДокумент28 страницMath11statprob FinalsNeil Trezley Sunico BalajadiaОценок пока нет
- Matutum View Academy: (The School of Faith)Документ7 страницMatutum View Academy: (The School of Faith)Neil Trezley Sunico BalajadiaОценок пока нет
- Matutum View Academy: (The School of Faith)Документ8 страницMatutum View Academy: (The School of Faith)Neil Trezley Sunico BalajadiaОценок пока нет
- GRADE 11 Learning Module 2 Semester Finals: General MathematicsДокумент10 страницGRADE 11 Learning Module 2 Semester Finals: General MathematicsNeil Trezley Sunico BalajadiaОценок пока нет
- Matutum View Academy: (The School of Faith)Документ9 страницMatutum View Academy: (The School of Faith)Neil Trezley Sunico BalajadiaОценок пока нет
- Matutum View Academy: (The School of Faith)Документ14 страницMatutum View Academy: (The School of Faith)Neil Trezley Sunico BalajadiaОценок пока нет
- Good Day Grade 10 Students. I Am MR. Neil Trezley S. Balajadia I Am Your Math TeacherДокумент11 страницGood Day Grade 10 Students. I Am MR. Neil Trezley S. Balajadia I Am Your Math TeacherNeil Trezley Sunico BalajadiaОценок пока нет
- GRADE 11 Learning Module 2 Semester Prelims: General MathematicsДокумент14 страницGRADE 11 Learning Module 2 Semester Prelims: General MathematicsNeil Trezley Sunico BalajadiaОценок пока нет
- GRADE 11 Learning Module 2 Semester Midterms: General MathematicsДокумент9 страницGRADE 11 Learning Module 2 Semester Midterms: General MathematicsNeil Trezley Sunico BalajadiaОценок пока нет
- Good Day Grade 10 Students. I Am MR. Neil Trezley S. Balajadia I Am Your Math TeacherДокумент11 страницGood Day Grade 10 Students. I Am MR. Neil Trezley S. Balajadia I Am Your Math TeacherNeil Trezley Sunico BalajadiaОценок пока нет
- Mathematics Statistics: Matutum View AcademyДокумент7 страницMathematics Statistics: Matutum View AcademyNeil Trezley Sunico BalajadiaОценок пока нет
- Mathematics Statistics: Matutum View AcademyДокумент10 страницMathematics Statistics: Matutum View AcademyNeil Trezley Sunico BalajadiaОценок пока нет
- GRADE 11 Learning Module 2 Semester Semi - Finals: General MathematicsДокумент14 страницGRADE 11 Learning Module 2 Semester Semi - Finals: General MathematicsNeil Trezley Sunico BalajadiaОценок пока нет
- Gift of Prophecy Module 1st Grading FinalДокумент13 страницGift of Prophecy Module 1st Grading FinalNeil Trezley Sunico BalajadiaОценок пока нет
- Prelim Prob StatДокумент2 страницыPrelim Prob StatNeil Trezley Sunico BalajadiaОценок пока нет
- Daily Lesson Log of M11Gm-Iij-2Документ2 страницыDaily Lesson Log of M11Gm-Iij-2Neil Trezley Sunico BalajadiaОценок пока нет
- Education System of Babylon and AssyriaДокумент31 страницаEducation System of Babylon and AssyriaNeil Trezley Sunico Balajadia100% (2)
- The Japanese Education System1Документ4 страницыThe Japanese Education System1Neil Trezley Sunico BalajadiaОценок пока нет
- 11 STEM General Biology 1 FIRST QUARTER LMsДокумент10 страниц11 STEM General Biology 1 FIRST QUARTER LMsNeil Trezley Sunico Balajadia50% (2)
- 11 STEM Physics FIRST QUARTER LMsДокумент22 страницы11 STEM Physics FIRST QUARTER LMsNeil Trezley Sunico BalajadiaОценок пока нет
- 1st Quarter Prelim g9Документ2 страницы1st Quarter Prelim g9Neil Trezley Sunico BalajadiaОценок пока нет
- The Japanese Education SystemДокумент4 страницыThe Japanese Education SystemNeil Trezley Sunico BalajadiaОценок пока нет
- Ethics of Job DiscriminationДокумент14 страницEthics of Job DiscriminationDaniyal AliОценок пока нет
- Ashlee Dillingham Teach Resume 2 1Документ2 страницыAshlee Dillingham Teach Resume 2 1api-547670474Оценок пока нет
- Roelandt 1999 Cluster AnalysisДокумент17 страницRoelandt 1999 Cluster AnalysisAndra Andra BОценок пока нет
- Student General Information: Republic of The Philippines University of Rizal System Tanay, RizalДокумент2 страницыStudent General Information: Republic of The Philippines University of Rizal System Tanay, RizalChessmyssОценок пока нет
- Bend, Curl, Hold, Lift, Lower, Pull, PushДокумент3 страницыBend, Curl, Hold, Lift, Lower, Pull, Pushapi-595082074Оценок пока нет
- Study Id70354 Ecommerce-In-IndiaДокумент61 страницаStudy Id70354 Ecommerce-In-IndiaSaksham SinhaОценок пока нет
- Biodiversity & Intellectual Property RightsДокумент34 страницыBiodiversity & Intellectual Property RightsSushil JindalОценок пока нет
- Orleans Jail Jan 19 ReportДокумент111 страницOrleans Jail Jan 19 ReportEthan BrownОценок пока нет
- Important Themes of Indian ConstitutionДокумент59 страницImportant Themes of Indian ConstitutionKunal BazalaОценок пока нет
- grBKmJyRKC - Tata Motor Finance JDДокумент7 страницgrBKmJyRKC - Tata Motor Finance JDVanya AroraОценок пока нет
- B. Has No Definite End Date A Project DoesДокумент3 страницыB. Has No Definite End Date A Project DoesManoj Saralaya0% (1)
- Las Week 5Документ6 страницLas Week 5Muzically Inspired100% (1)
- Leader Mai Kieu LienДокумент2 страницыLeader Mai Kieu LienÁnh NguyệtОценок пока нет
- Nike ppt14822Документ24 страницыNike ppt14822Harmeet singhОценок пока нет
- G.i.6 - 004 Near Miss Reporting ProcessДокумент5 страницG.i.6 - 004 Near Miss Reporting ProcessSantos Rex100% (2)
- Counselling in A Digital WorldДокумент2 страницыCounselling in A Digital WorldIhin Nur FarihinОценок пока нет
- My New ResumeДокумент1 страницаMy New Resumeapi-412394530Оценок пока нет
- CRID PowerPoint Slides - Aviation Revenue Generation Presentation - 3 Lean MGTДокумент58 страницCRID PowerPoint Slides - Aviation Revenue Generation Presentation - 3 Lean MGTTobzОценок пока нет
- Pita Vs CaДокумент8 страницPita Vs CaBasri JayОценок пока нет
- Typical Standard Details Traffic Calming Measures: City of TshwaneДокумент1 страницаTypical Standard Details Traffic Calming Measures: City of Tshwanescelo butheleziОценок пока нет
- Purdue OWL AnnotatedДокумент6 страницPurdue OWL AnnotatedbvwdavisОценок пока нет
- The National Artist of The Philippines Guidelines.: BackgroundДокумент30 страницThe National Artist of The Philippines Guidelines.: BackgroundJizza che Mayo100% (1)
- Ho20210088 - CB 2Документ3 страницыHo20210088 - CB 2Santosh BendkhaleОценок пока нет
- Be Able To - GrammarДокумент1 страницаBe Able To - GrammarbrunaОценок пока нет
- Wits Lesson PlanДокумент2 страницыWits Lesson Planapi-317043268Оценок пока нет
- List of Unauthorized Construction of Building Department-I, South Zone 01.02.2019 To 31.07.2019Документ10 страницList of Unauthorized Construction of Building Department-I, South Zone 01.02.2019 To 31.07.2019BALAJI ASSOCIATESОценок пока нет
- Anatomy and Physiology (BPE)Документ8 страницAnatomy and Physiology (BPE)Shiela MantillaОценок пока нет
- Aviation History: Lecture 6: Flight InstrumentsДокумент43 страницыAviation History: Lecture 6: Flight Instrumentszuliana86% (7)
- The Resistible Rise of Benito Mussolini and Fighting Fascism in Britain TodayДокумент5 страницThe Resistible Rise of Benito Mussolini and Fighting Fascism in Britain TodayIgor CrnoboriОценок пока нет
- Jurnal Hukum Laut Kel.2 (Bahasa Inggris)Документ18 страницJurnal Hukum Laut Kel.2 (Bahasa Inggris)Muhammad IqbalОценок пока нет
- Generative AI: The Insights You Need from Harvard Business ReviewОт EverandGenerative AI: The Insights You Need from Harvard Business ReviewРейтинг: 4.5 из 5 звезд4.5/5 (2)
- Cyber War: The Next Threat to National Security and What to Do About ItОт EverandCyber War: The Next Threat to National Security and What to Do About ItРейтинг: 3.5 из 5 звезд3.5/5 (66)
- Chaos Monkeys: Obscene Fortune and Random Failure in Silicon ValleyОт EverandChaos Monkeys: Obscene Fortune and Random Failure in Silicon ValleyРейтинг: 3.5 из 5 звезд3.5/5 (111)
- Scary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldОт EverandScary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldРейтинг: 4.5 из 5 звезд4.5/5 (55)
- Algorithms to Live By: The Computer Science of Human DecisionsОт EverandAlgorithms to Live By: The Computer Science of Human DecisionsРейтинг: 4.5 из 5 звезд4.5/5 (722)
- The E-Myth Revisited: Why Most Small Businesses Don't Work andОт EverandThe E-Myth Revisited: Why Most Small Businesses Don't Work andРейтинг: 4.5 из 5 звезд4.5/5 (709)
- The Future of Geography: How the Competition in Space Will Change Our WorldОт EverandThe Future of Geography: How the Competition in Space Will Change Our WorldРейтинг: 4 из 5 звезд4/5 (6)
- Digital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent MoneyОт EverandDigital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent MoneyРейтинг: 4 из 5 звезд4/5 (51)
- The Intel Trinity: How Robert Noyce, Gordon Moore, and Andy Grove Built the World's Most Important CompanyОт EverandThe Intel Trinity: How Robert Noyce, Gordon Moore, and Andy Grove Built the World's Most Important CompanyОценок пока нет
- AI Superpowers: China, Silicon Valley, and the New World OrderОт EverandAI Superpowers: China, Silicon Valley, and the New World OrderРейтинг: 4.5 из 5 звезд4.5/5 (399)
- The Infinite Machine: How an Army of Crypto-Hackers Is Building the Next Internet with EthereumОт EverandThe Infinite Machine: How an Army of Crypto-Hackers Is Building the Next Internet with EthereumРейтинг: 3 из 5 звезд3/5 (12)
- Excel Essentials: A Step-by-Step Guide with Pictures for Absolute Beginners to Master the Basics and Start Using Excel with ConfidenceОт EverandExcel Essentials: A Step-by-Step Guide with Pictures for Absolute Beginners to Master the Basics and Start Using Excel with ConfidenceОценок пока нет
- HBR's 10 Must Reads on AI, Analytics, and the New Machine AgeОт EverandHBR's 10 Must Reads on AI, Analytics, and the New Machine AgeРейтинг: 4.5 из 5 звезд4.5/5 (69)
- ChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindОт EverandChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindОценок пока нет
- Learn Python Programming for Beginners: Best Step-by-Step Guide for Coding with Python, Great for Kids and Adults. Includes Practical Exercises on Data Analysis, Machine Learning and More.От EverandLearn Python Programming for Beginners: Best Step-by-Step Guide for Coding with Python, Great for Kids and Adults. Includes Practical Exercises on Data Analysis, Machine Learning and More.Рейтинг: 5 из 5 звезд5/5 (34)
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveОт EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveОценок пока нет
- Evaluation of Some SMS Verification Services and Virtual Credit Cards Services for Online Accounts VerificationsОт EverandEvaluation of Some SMS Verification Services and Virtual Credit Cards Services for Online Accounts VerificationsРейтинг: 5 из 5 звезд5/5 (2)
- The Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldОт EverandThe Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldРейтинг: 4.5 из 5 звезд4.5/5 (107)
- Solutions Architect's Handbook: Kick-start your career as a solutions architect by learning architecture design principles and strategiesОт EverandSolutions Architect's Handbook: Kick-start your career as a solutions architect by learning architecture design principles and strategiesОценок пока нет
- The Bitcoin Standard: The Decentralized Alternative to Central BankingОт EverandThe Bitcoin Standard: The Decentralized Alternative to Central BankingРейтинг: 4.5 из 5 звезд4.5/5 (41)
- 100M Offers Made Easy: Create Your Own Irresistible Offers by Turning ChatGPT into Alex HormoziОт Everand100M Offers Made Easy: Create Your Own Irresistible Offers by Turning ChatGPT into Alex HormoziОценок пока нет