Академический Документы
Профессиональный Документы
Культура Документы
Critical Thinking Assignment 4-2 Critical Thinking Assignment 4-2
Загружено:
Cristhian ChahuayoИсходное описание:
Оригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Critical Thinking Assignment 4-2 Critical Thinking Assignment 4-2
Загружено:
Cristhian ChahuayoАвторское право:
Доступные форматы
lOMoARcPSD|5111856
Critical Thinking Assignment 4-2
Applications in Information Security (State College of Florida, Manatee-Sarasota)
StuDocu no está patrocinado ni avalado por ningún colegio o universidad.
Descargado por henry lazo (lazo13579@gmail.com)
lOMoARcPSD|5111856
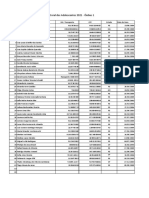
Critical Thinking 4-2: Recommended Crypto-periods
How long should a key be used before it is replaced? Search the Internet
for information regarding crypto-periods for hash, symmetric, and asymmet-
ric algorithms. Find at least three sources for each of the algorithms. Draw a
table that lists the algorithms and the recommended time, and then calculate
the average for each. Do you agree or disagree? What would be your recom-
mendation on crypto-periods for each? Why?
Algorithm Max Time Average Sources
Hash 2yrs 1.8yrs https://web.ar-
chive.org/web/
1.5yrs 20110617055733/
http://www.cse-
2yrs cst.gc.ca/its-sti/ser-
vices/crypto-ser-
vices-crypto/ca-ac-
eng.html
https://infos-
cience.epfl.ch/record/
164539/files/NPDF-
32.pdf
https://info.-
townsendsecurity.-
com/definitive-guide-
to-encryption-key-
management-funda-
mentals
Symmetric 2yrs 2yrs https://nvlpubs.nist.-
gov/nistpubs/Spe-
2yrs cialPublications/
NIST.SP.800-
2yrs 57pt1r4.pdf
https://
www.keylength.com/
en/4/
https://csrc.nist.gov/
Projects/Key-Manage-
ment
Descargado por henry lazo (lazo13579@gmail.com)
lOMoARcPSD|5111856
Algorithm Max Time Average Sources
Asymetric 3yrs 2.7yrs https://securityncom-
pliance.wordpress.-
3yrs com/2014/04/19/
cryptographic-keys-
2yrs and-their-cryptope-
riod-nist-recommen-
dations-2012/
https://nvlpubs.nist.-
gov/nistpubs/Spe-
cialPublications/
NIST.SP.800-
57pt1r4.pdf
https://www.gronau-
it-cloud-comput-
ing.de/en/crypto-
graphic-key-length-
recommendation-
from-organizations/
The cryptoperiods suggested are only rough guidelines; longer or shorter cryptope-
riods may be warranted, depending on the application and environment in which
the keys will be used. However, when assigning a longer cryptoperiod than that
suggested below, serious consideration should be given to the risks associated with
doing so. Shorter is always better even though it might not be easier to apply. I
would recommend the shortest time for each cryptoperiod because of the risks as-
sociated with longer periods.
Descargado por henry lazo (lazo13579@gmail.com)
Вам также может понравиться
- Basic Knowledge Requirements For Cybersecurity and HackinДокумент65 страницBasic Knowledge Requirements For Cybersecurity and Hackinshriram1082883Оценок пока нет
- AFCEH Top Hacking Tools ListДокумент3 страницыAFCEH Top Hacking Tools Listermohitjindal100% (2)
- Ebook - List of Ebook SitesДокумент5 страницEbook - List of Ebook Sitesapi-3697394Оценок пока нет
- Useful LinksДокумент13 страницUseful LinksAshlee RouseyОценок пока нет
- Development of Modern International Law and India R.P.anandДокумент77 страницDevelopment of Modern International Law and India R.P.anandVeeramani ManiОценок пока нет
- ReferencesДокумент4 страницыReferencesJohnОценок пока нет
- Incident Response GuideДокумент10 страницIncident Response GuideRapacitorОценок пока нет
- Embedded Systems Security: Practical Methods for Safe and Secure Software and Systems DevelopmentОт EverandEmbedded Systems Security: Practical Methods for Safe and Secure Software and Systems DevelopmentРейтинг: 4.5 из 5 звезд4.5/5 (2)
- E Commerce AssignmentДокумент40 страницE Commerce AssignmentHaseeb Khan100% (3)
- NIST RMF Categorize Step-FAQsДокумент17 страницNIST RMF Categorize Step-FAQsPeteОценок пока нет
- Essay R JДокумент5 страницEssay R Japi-574033038Оценок пока нет
- Construction Companies in MauritiusДокумент4 страницыConstruction Companies in MauritiusJowaheer Besh100% (1)
- Authentic8 GD Financial Crime Research Tools PublicДокумент32 страницыAuthentic8 GD Financial Crime Research Tools Publicnabeen saifiОценок пока нет
- LinksДокумент2 страницыLinksAbhishek SahuОценок пока нет
- Garvida V SalesДокумент1 страницаGarvida V SalesgemmaОценок пока нет
- Ice Cream CaseДокумент7 страницIce Cream Casesardar hussainОценок пока нет
- TS4F01-1 Unit 3 - Master DataДокумент59 страницTS4F01-1 Unit 3 - Master DataLuki1233332100% (1)
- AДокумент31 страницаAZake CarderОценок пока нет
- 3 Longman Academic Writing Series 4th Edition Answer KeyДокумент21 страница3 Longman Academic Writing Series 4th Edition Answer KeyZheer KurdishОценок пока нет
- CEH v10 Module 21 - References ESДокумент7 страницCEH v10 Module 21 - References ESKaren GarzaОценок пока нет
- New Text DocumentДокумент1 страницаNew Text DocumentRezen Rana BhatОценок пока нет
- PQ Index - What Does It MeanДокумент5 страницPQ Index - What Does It MeanAnibal RiosОценок пока нет
- 6 Types of Artificial Neural Networks Currently Being Used in MLДокумент16 страниц6 Types of Artificial Neural Networks Currently Being Used in MLSyed Zain BukhariОценок пока нет
- Top 7 Data Streaming Tools For Real-Time AnalyticsДокумент8 страницTop 7 Data Streaming Tools For Real-Time AnalyticsGuru VelmathiОценок пока нет
- RG - Computer Science-SSC - After IRC On 29 Mar 2019 PDFДокумент9 страницRG - Computer Science-SSC - After IRC On 29 Mar 2019 PDFediealiОценок пока нет
- Levantamento Informações Forense DigitalДокумент2 страницыLevantamento Informações Forense DigitalGustavo ZTОценок пока нет
- A Comprehensive Study On Social Network Mental Disorders Detection Via Online Social Media Mining - 2018Документ1 страницаA Comprehensive Study On Social Network Mental Disorders Detection Via Online Social Media Mining - 2018caxorar516Оценок пока нет
- INFORMÁTIДокумент2 страницыINFORMÁTILu1zxDОценок пока нет
- Dokumentasi Dan Distribusi Laporan Hasil Analisis EfekДокумент8 страницDokumentasi Dan Distribusi Laporan Hasil Analisis Efekary mllОценок пока нет
- Linc 2Документ12 страницLinc 2tovih27684Оценок пока нет
- Customer Satisfaction Towards Online Shopping at Electronics Shopping Malls in Vietnam - A Conceptual Model To Enhance Business Success Through Efficient Websites and Logistics ServicesДокумент14 страницCustomer Satisfaction Towards Online Shopping at Electronics Shopping Malls in Vietnam - A Conceptual Model To Enhance Business Success Through Efficient Websites and Logistics ServicesSanthosh Family100% (1)
- Links e Documentazione AggiuntivaДокумент8 страницLinks e Documentazione AggiuntivaFederico PastorinoОценок пока нет
- Analyzing Malicious Documents Cheat SheetДокумент7 страницAnalyzing Malicious Documents Cheat SheetSandro MeloОценок пока нет
- Jobs Portal Doc - (WWW - Students3k.com)Документ134 страницыJobs Portal Doc - (WWW - Students3k.com)Prabhat SharmaОценок пока нет
- Standards Guidance Cited Privacy Framework Rfi Responses 2.27.19Документ13 страницStandards Guidance Cited Privacy Framework Rfi Responses 2.27.19Jose GarciaОценок пока нет
- BibliografiaДокумент1 страницаBibliografiamaria paula cuencaОценок пока нет
- BSOA OA7 Fundamentals of IT and MIS Concept TOPIC OUTLINE 2024Документ9 страницBSOA OA7 Fundamentals of IT and MIS Concept TOPIC OUTLINE 2024kabapota386Оценок пока нет
- Why The ISDA SIMM Methdology Is Not What I ExpectedДокумент5 страницWhy The ISDA SIMM Methdology Is Not What I Expected남상욱Оценок пока нет
- Hacking ResourcesДокумент1 страницаHacking Resourcesharibabuji nhbОценок пока нет
- NZISM 7.1. Detecting Information Security Incidents V. 3.7 February 2024Документ4 страницыNZISM 7.1. Detecting Information Security Incidents V. 3.7 February 2024naomisowunmiОценок пока нет
- E-Resources+Link and KingsmanДокумент1 страницаE-Resources+Link and KingsmanSundeep KumarОценок пока нет
- T/esr/viewing/index - PHP? Module Viewing - Poster& Task Viewsection&pi 124 598&ti 411708&si 1419& SearchkeyДокумент1 страницаT/esr/viewing/index - PHP? Module Viewing - Poster& Task Viewsection&pi 124 598&ti 411708&si 1419& Searchkeyjossy123456Оценок пока нет
- Networking StudyДокумент3 страницыNetworking StudybobsimbolonzОценок пока нет
- Communs Web Attack Reference PT.1Документ7 страницCommuns Web Attack Reference PT.1Angel CabralesОценок пока нет
- Top 11 Books On Cybersecurity That You Can Read On Your Kindle PDFДокумент9 страницTop 11 Books On Cybersecurity That You Can Read On Your Kindle PDFram prakashОценок пока нет
- High Voltage Engineering Book by Jeraldin AhilaДокумент2 страницыHigh Voltage Engineering Book by Jeraldin AhilaSenthilkumar RathinasamyОценок пока нет
- Computer Communications - Journal - ElsevierДокумент8 страницComputer Communications - Journal - ElseviersujiteduОценок пока нет
- Student PlannerДокумент4 страницыStudent PlannerPruthvi M JavaliОценок пока нет
- Laporan Praktikum Anfistum SelДокумент4 страницыLaporan Praktikum Anfistum SelFebiyolaОценок пока нет
- ArbolДокумент1 страницаArbolAndrés Jiménez LáinezОценок пока нет
- UntitledДокумент1 страницаUntitledBeatriz RAОценок пока нет
- Security in Oracle WebLogic - Realm, Security Provider, Authentication, Authorization, Users - Online Identity & Access ManagementДокумент12 страницSecurity in Oracle WebLogic - Realm, Security Provider, Authentication, Authorization, Users - Online Identity & Access ManagementAsad HussainОценок пока нет
- Enrolment Notice April Courses SY StudentsДокумент4 страницыEnrolment Notice April Courses SY Studentsrituparns22csОценок пока нет
- Reference PageДокумент1 страницаReference PageenelliganОценок пока нет
- LInk PKL 18-9-23Документ1 564 страницыLInk PKL 18-9-23Kipasangin kipasanginОценок пока нет
- LinksДокумент2 страницыLinksZekrom BlackОценок пока нет
- Temp 8655876524900479039Документ10 страницTemp 8655876524900479039ballerbell900Оценок пока нет
- Machine Learning in Auditing: Current and Future ApplicationsДокумент7 страницMachine Learning in Auditing: Current and Future ApplicationsGodfrey MakurumureОценок пока нет
- Getting Kernel Source For Amazon Linux (BUSCAR EN GOOGLE) ..........................Документ1 страницаGetting Kernel Source For Amazon Linux (BUSCAR EN GOOGLE) ..........................Paco Giner AyguadéОценок пока нет
- Ra 9194 Money LaunderingДокумент5 страницRa 9194 Money LaunderingJenevie DecenillaОценок пока нет
- Advanced APT Hunting With Splunk TakeawayДокумент7 страницAdvanced APT Hunting With Splunk TakeawayJJPОценок пока нет
- Requests Requests CountДокумент8 страницRequests Requests CountsureshОценок пока нет
- Consolidated Materials - CCF Batch 1: 1 MessageДокумент3 страницыConsolidated Materials - CCF Batch 1: 1 MessageEleazar Pelvera Chavez Jr.Оценок пока нет
- Special Issue On Security and Privacy in Big Data and Cloud - Call For Papers - ElsevierДокумент7 страницSpecial Issue On Security and Privacy in Big Data and Cloud - Call For Papers - ElsevierSarah Jean TrajanoОценок пока нет
- Repaso Ut0Документ1 страницаRepaso Ut0Luis de BlasОценок пока нет
- New Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNAОт EverandNew Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNAОценок пока нет
- Pro Cryptography and Cryptanalysis: Creating Advanced Algorithms with C# and .NETОт EverandPro Cryptography and Cryptanalysis: Creating Advanced Algorithms with C# and .NETОценок пока нет
- Information Security of Intelligent Vehicles Communication: Overview, Perspectives, Challenges, and Possible SolutionsОт EverandInformation Security of Intelligent Vehicles Communication: Overview, Perspectives, Challenges, and Possible SolutionsРейтинг: 5 из 5 звезд5/5 (1)
- Romances of RizalДокумент4 страницыRomances of RizalMaria Elena PanchoОценок пока нет
- S No Clause No. Existing Clause/ Description Issues Raised Reply of NHAI Pre-Bid Queries Related To Schedules & DCAДокумент10 страницS No Clause No. Existing Clause/ Description Issues Raised Reply of NHAI Pre-Bid Queries Related To Schedules & DCAarorathevipulОценок пока нет
- Airport Planning and Engineering PDFДокумент3 страницыAirport Planning and Engineering PDFAnil MarsaniОценок пока нет
- Mt-Requirement-01 - Feu CalendarДокумент18 страницMt-Requirement-01 - Feu CalendarGreen ArcОценок пока нет
- Grile EnglezaДокумент3 страницыGrile Englezakis10Оценок пока нет
- Biology ProjectДокумент7 страницBiology ProjectChitwan GuptaОценок пока нет
- QBE 2022 Sustainability ReportДокумент44 страницыQBE 2022 Sustainability ReportVertika ChaudharyОценок пока нет
- Berkshire Hathaway Inc.: United States Securities and Exchange CommissionДокумент48 страницBerkshire Hathaway Inc.: United States Securities and Exchange CommissionTu Zhan LuoОценок пока нет
- Corporate Social Responsibility in Bangladesh:: A Comparative Study of Commercial Banks of BangladeshДокумент12 страницCorporate Social Responsibility in Bangladesh:: A Comparative Study of Commercial Banks of BangladeshSaima Binte IkramОценок пока нет
- Upsc 1 Year Study Plan 12Документ3 страницыUpsc 1 Year Study Plan 12siboОценок пока нет
- MOP Annual Report Eng 2021-22Документ240 страницMOP Annual Report Eng 2021-22Vishal RastogiОценок пока нет
- Coral Dos Adolescentes 2021 - Ônibus 1: Num Nome RG / Passaporte CPF Estado Data de NascДокумент1 страницаCoral Dos Adolescentes 2021 - Ônibus 1: Num Nome RG / Passaporte CPF Estado Data de NascGabriel Kuhs da RosaОценок пока нет
- Security Incidents and Event Management With Qradar (Foundation)Документ4 страницыSecurity Incidents and Event Management With Qradar (Foundation)igrowrajeshОценок пока нет
- Declarations On Higher Education and Sustainable DevelopmentДокумент2 страницыDeclarations On Higher Education and Sustainable DevelopmentNidia CaetanoОценок пока нет
- RamadanДокумент12 страницRamadanMishkat MohsinОценок пока нет
- Balkan Nationalism (Shodhangana Chapter) PDFДокумент40 страницBalkan Nationalism (Shodhangana Chapter) PDFsmrithiОценок пока нет
- Reading Job Advertisements 4Документ2 страницыReading Job Advertisements 456. Trần Thị Thanh Tuyền100% (1)
- Basavaraju Reservation Under The Constitution of India Issues and PerspectivesДокумент9 страницBasavaraju Reservation Under The Constitution of India Issues and PerspectivesK ThirunavukkarasuОценок пока нет
- Active Critical ReadingДокумент22 страницыActive Critical ReadingYonn Me Me KyawОценок пока нет
- ATI PN Maternal Newborn Proctored Exam Test Bank (38 Versions) (New-2022)Документ7 страницATI PN Maternal Newborn Proctored Exam Test Bank (38 Versions) (New-2022)kapedispursОценок пока нет
- Presentation On Ethics in ManagementДокумент20 страницPresentation On Ethics in Managementnasif al islamОценок пока нет
- Chapter 5A - PartnershipsДокумент6 страницChapter 5A - PartnershipsRasheed AhmadОценок пока нет