Академический Документы
Профессиональный Документы
Культура Документы
zxr10 2910eps PDF
Загружено:
joko handoyoОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
zxr10 2910eps PDF
Загружено:
joko handoyoАвторское право:
Доступные форматы
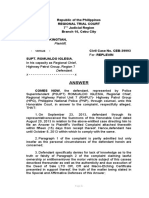
ZXR10 2900E Series
Easy-maintenance Secure Switch
Configuration Guide
Version: 2.05.10
ZTE CORPORATION
NO. 55, Hi-tech Road South, ShenZhen, P.R.China
Postcode: 518057
Tel: +86-755-26771900
Fax: +86-755-26770801
URL: http://ensupport.zte.com.cn
E-mail: support@zte.com.cn
Downloaded from www.Manualslib.com manuals search engine
LEGAL INFORMATION
Copyright © 2011 ZTE CORPORATION.
The contents of this document are protected by copyright laws and international treaties. Any reproduction or
distribution of this document or any portion of this document, in any form by any means, without the prior written
consent of ZTE CORPORATION is prohibited. Additionally, the contents of this document are protected by
contractual confidentiality obligations.
All company, brand and product names are trade or service marks, or registered trade or service marks, of ZTE
CORPORATION or of their respective owners.
This document is provided “as is”, and all express, implied, or statutory warranties, representations or conditions
are disclaimed, including without limitation any implied warranty of merchantability, fitness for a particular purpose,
title or non-infringement. ZTE CORPORATION and its licensors shall not be liable for damages resulting from the
use of or reliance on the information contained herein.
ZTE CORPORATION or its licensors may have current or pending intellectual property rights or applications
covering the subject matter of this document. Except as expressly provided in any written license between ZTE
CORPORATION and its licensee, the user of this document shall not acquire any license to the subject matter
herein.
ZTE CORPORATION reserves the right to upgrade or make technical change to this product without further notice.
Users may visit ZTE technical support website http://ensupport.zte.com.cn to inquire related information.
The ultimate right to interpret this product resides in ZTE CORPORATION.
Revision History
Revision No. Revision Date Revision Reason
R1.0 2012-07-02 First edition
Serial Number: SJ-20120409144109-002
Publishing Date: 2012-07-02(R1.0)
Downloaded from www.Manualslib.com manuals search engine
Contents
About This Manual ......................................................................................... I
Chapter 1 System Overview ...................................................................... 1-1
Chapter 2 Usage and Operation................................................................ 2-1
2.1 Configuration Modes .......................................................................................... 2-1
2.2 Command Modes............................................................................................... 2-7
2.3 Common Command Parameters ........................................................................2-11
2.4 Usage of Command Line .................................................................................. 2-12
Chapter 3 System Management ................................................................ 3-1
3.1 File System Operation ........................................................................................ 3-1
3.2 Configuring the TFTP Server............................................................................... 3-3
3.3 Configuring the FTP Server................................................................................. 3-5
3.4 Importing and Exporting Configuration ................................................................. 3-7
3.5 Backing Up and Recovering Files ........................................................................ 3-7
3.6 Downloading Software Version Automatically ....................................................... 3-8
3.7 Configuring Automatic Saving of a Configuration File.......................................... 3-10
3.8 Software Version Upgrade .................................................................................3-11
3.9 File System Configuration Commands ............................................................... 3-15
Chapter 4 Service Configuration............................................................... 4-1
4.1 Management Configuration ................................................................................. 4-2
4.2 Port Configuration .............................................................................................. 4-5
4.3 PoE Configuration .............................................................................................. 4-6
4.4 Port Mirroring ..................................................................................................... 4-9
4.5 VLAN Configuration.......................................................................................... 4-12
4.6 MAC Table Operation ....................................................................................... 4-14
4.7 LACP Configuration.......................................................................................... 4-17
4.8 IGMP Snooping Configuration ........................................................................... 4-20
4.9 MLD Snooping Configuration ............................................................................ 4-24
4.10 IPTV Configuration ......................................................................................... 4-26
4.11 STP Configuration .......................................................................................... 4-32
4.12 ACL Configuration .......................................................................................... 4-42
4.13 QoS Configuration .......................................................................................... 4-50
4.14 PVLAN Configuration...................................................................................... 4-56
4.15 Layer 2 Protocol Transparent Transmission Configuration ................................. 4-59
Downloaded from www.Manualslib.com manuals search engine
4.16 IPv4 Layer 3 Configuration.............................................................................. 4-61
4.17 IPv6 Layer 3 Configuration.............................................................................. 4-63
4.18 DAI Configuration ........................................................................................... 4-64
4.19 Access Service Configuration.......................................................................... 4-66
4.20 MAC Authentication Configuration ................................................................... 4-74
4.21 QinQ Configuration......................................................................................... 4-75
4.22 Syslog Configuration....................................................................................... 4-77
4.23 NTP Configuration .......................................................................................... 4-78
4.24 GARP/GVRP Configuration............................................................................. 4-80
4.25 DHCP Configuration ....................................................................................... 4-82
4.26 DHCPv6 Configuration.................................................................................... 4-87
4.27 VBAS Configuration........................................................................................ 4-90
4.28 PPPoE-PLUS Configuration ............................................................................ 4-92
4.29 ZESR Configuration........................................................................................ 4-93
4.30 OAM Configuration ........................................................................................ 4-111
4.31 SQinQ Configuration...................................................................................... 4-117
4.32 VLAN Mapping Configuration ......................................................................... 4-119
4.33 sFlow Configuration.......................................................................................4-122
4.34 PP Configuration ...........................................................................................4-123
4.35 LLDP Configuration .......................................................................................4-125
4.36 Single Port Loop Detection Configuration ........................................................4-128
4.37 UDLD Configuration ......................................................................................4-131
4.38 TACACS+ Configuration ................................................................................4-133
4.39 Time Range Configuration .............................................................................4-135
4.40 Voice VLAN Configuration..............................................................................4-136
4.41 802.1AG Configuration ..................................................................................4-138
4.42 Y.1731 Configuration .....................................................................................4-144
4.43 MAC-based VLAN Command Configuration ....................................................4-149
4.44 DHCP Relay Configuration.............................................................................4-150
Chapter 5 Management .............................................................................. 5-1
5.1 REMOTE-ACCESS ............................................................................................ 5-1
5.2 SSH .................................................................................................................. 5-3
5.3 PRIVILEGE........................................................................................................ 5-6
5.4 SNMP Overview................................................................................................. 5-7
5.5 RMON Overview .............................................................................................. 5-12
5.6 ZGMP ............................................................................................................. 5-15
5.7 sFlow .............................................................................................................. 5-22
II
Downloaded from www.Manualslib.com manuals search engine
5.8 WEB................................................................................................................ 5-23
5.9 M_Button ......................................................................................................... 5-43
5.10 Telnet ............................................................................................................ 5-45
Chapter 6 Maintenance .............................................................................. 6-1
6.1 Routine Maintenance.......................................................................................... 6-1
6.2 Virtual Line Detection.......................................................................................... 6-2
6.3 Common Fault Handling ..................................................................................... 6-3
6.3.1 Introduction to Common Fault ................................................................... 6-3
6.3.2 The Configuration by Console Port Fails .................................................... 6-3
6.3.3 Failed Telnet Connection .......................................................................... 6-4
6.3.4 WEB Management Cannot be Connected.................................................. 6-4
6.3.5 Losing the Login Username or Password ................................................... 6-5
6.3.6 Losing Enable Enable Password ............................................................... 6-6
6.3.7 The Two Devices Cannot Interconnect in The Same VLAN ......................... 6-7
6.3.8 The Solution to Authentication Timeout Fault in Campus Network ............... 6-7
6.3.9 The Solution to ARP Attack in Campus Network......................................... 6-9
Figures............................................................................................................. I
Tables .............................................................................................................V
Glossary .......................................................................................................VII
III
Downloaded from www.Manualslib.com manuals search engine
IV
Downloaded from www.Manualslib.com manuals search engine
About This Manual
Purpose
This manual is suitable for easy-maintenance secure switches of ZXR10 2900E (V2.05.10)
series (ZXR10 2910E-PS/2918E-PS/2918E/2928E-PS/2928E/2952E, also ZXR10 2900E
series in the body, and switches, or this series of switches in the general part). These
switches include:
l ZXR10 2910E-PS easy-maintenance secure switch
l ZXR10 2918E-PS easy-maintenance secure switch
l ZXR10 2918E easy-maintenance secure switch
l ZXR10 2928E easy-maintenance secure switch
l ZXR10 2928E-PS asy-maintenance secure switch
l ZXR10 2952E easy-maintenance secure switch
What Is in This Manual
ZXR10 2900E (V2.05.10) series switch user manual contains the following chapters:
Chapter Summary
Chapter 1 Safety Instruction Provides safety description and safety signs.
Chapter 2 System Overview Describes the ZXR10 2900E system.
Chapter 3 Usage and Describes the configuration mode, command mode and command
Operation line use of ZXR10 2900EE.
Chapter 4 System
Describes system management.
Management
Chapter 5 Service
Describes service configuration.
Configuration
Chapter 6 Management Describes management configuration.
Describes routine maintenance, common detection method and
Chapter 7 Maintenance
common fault processes.
Downloaded from www.Manualslib.com manuals search engine
II
Downloaded from www.Manualslib.com manuals search engine
Chapter 1
System Overview
The ZXR10 2900E series switches are a very important part of the ZXR10 series Ethernet
switches. ZXR10 2900E series products are 100 mega L2+ (between Layer 2 and Layer 3)
Ethernet switches used for 100 M network access and convergence. 1 Gb is available for
uplinks. ZXR10 2900E series products provide Ethernet access ports of different counts
and types as well as a cost-effective access and convergence scheme with a higher speed
and effect. It is applied in the access layer of the carrier network and enterprise network.
For the ports that the ZXR10 2900E supports, refer to the following table.
Switch Type Fixed Port Other
8 10/100 BASE-T Ethernet ports
2 Gigabit Ethernet ports are combo
ZXR10 2910E-PS 2 10/100/1000BASE-T Ethernet ports
electro-optic multiplexing ports.
2 100/1000BASE-X ports
16 10/100 BASE-T Ethernet ports
2 Gigabit Ethernet ports are combo
ZXR10 2918E-PS 2 10/100/1000BASE-T Ethernet ports
electro-optic multiplexing ports.
2 100/1000BASE-X ports
16 10/100 BASE-T Ethernet ports
2 Gigabit Ethernet ports are combo
ZXR10 2918E 2 10/100/1000BASE-T Ethernet ports
electro-optic multiplexing ports.
2 100/1000BASE-X ports
24 10/100 BASE-T Ethernet ports
4 10/100/1000BASE-T Ethernet ports Two Gigabit Ethernet ports are combo
ZXR10 2928E
2 100/1000BASE-X ports optoelectronic multiplex ports.
2 1000BASE-X interfaces
RS-29EC-4GE-SFP subcards,
24 10/100 BASE-T Ethernet ports RS-29EC-4GE-RJ45 subcards, and
ZXR10 2928E-PS
1 subcard slot RS-29EC-4FE-SFP subcards are
supported.
48 10/100BASE-TX Ethernet ports
ZXR10 2952E -
4 1000BASE-X ports
Switching Capability
The ZXR10 2900E series switches satisfy the layer-2 line-speed switching requirement
on all ports. The data message can be forwarded at wire-speed after being filtered and
processed by flow classification. Ports provide high throughput, low packet discarding rate
and low time delay and jitter, which satisfy the demand of the key application.
1-1
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Reliability
The ZXR10 2900E ensures the redundancy backup and fast switch through
STP/RSTP/MSTP. These switches support the 802.3ad LACP function and it supplies
load sharing and link backup. It supports ZESR Ethernet ring network mode to provide
fast protection switching, which ensures that the user service will not be interrupted.
Service Characteristics
Operation characteristics and controls are as follows:
l It provides flexible VLAN classification mode. It can be classified by types of port,
protocol, MAC address and so on.
l It provides VPN on layer-2 which flexibly controls outer layer label and makes
operation and plan convenient.
l It provides user port location technology such as VBAS, DHCP Option82 and PPPoE+.
l It provides L2 multicast technology including IGMP-snooping and proxy function,
fast-leaving characteristic and Multicast-Vlan Switching (MVS) function, which
supports for opening IPTV service.
Security Control
The functions of security control are listed below.
l User level security control is provided.
à IEEE 802.1x implements dynamic and port-based security, which provides the
user ID authentication function.
à It supports MAC/IP/VLAN/PORT combination at random, which prevents illegal
user from accessing the network effectively.
à Port isolation is helpful to make sure that users can not monitor or access to other
users on the same switch.
à It supports GuestVlan and anti-proxy function, which helps the application in the
education network and other complicated networking environment.
à DHCP monitoring prevents spiteful users deceiving the server and sending
spurious address, so it can start IP source protection and create a binding table
for the IP address of the user, MAC address, ports and VLAN to prevent user
deceiving or using IP address of other users.
l Equipment level security is provided.
à CPU security control technology can resist DoS attack from CPU.
à SSH/SNMPv3 protocol supplies network management security.
à Multilevel security of console can prevent unauthenticated users changing the
switch configuration.
à RADIUS/TACACS+ identification authentication puts the switch under the
centralized control and prevents unauthorized user from modifying configuration.
1-2
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 1 System Overview
l Network security control is provided.
à ACL based on port or Trunk makes it possible for users to apply security strategy
to the ports of switches or Trunk.
à MAC address binding and the filter based on source or destination provide
effective flow control based on address.
à Port mirroring function provides an effective tool for network management
analysis.
QoS Guarantee
Applications of QoS are shown below:
l Standard 802.1p CoS and DSCP field sort can be labeled and sorted again based on
single packet with source and destination IP address, source and destination MAC
address, and TCP/UDP port number.
l It provides queue schedule algorithm: Strict Priority (SP) and combination schedule
(SP+WRR). Of which WRR is the abbreviation of Weighted Round Robin.
l It supports Committed Access Rate (CAR) function. It manages the asynchronous
uplink and downlink data flow from end stage or up link by utilizing input strategy
and output shaping. Input strategy control supplies the bandwidth control with
minimal increment of 8kbps. When network congestion occurs, it still can satisfy the
QoS demands of discarding packets, time delay and time jitter. As a result, queue
congestion can be avoided effectively.
Management Modes
Switch management refers to:
l It supports SNMPv1/v2c/v3 and RMON.
l It supports ZXNM01 uniform network management platform.
l It supports CLI command lines including Console, Telnet and SSH to access the
switch.
l It supports Web network management.
l It supports ZTE Group Manage Protocol (ZGMP) group management.
Functions
ZXR10 2900E series switches use the Store and Forward mode, and supports layer-2
switching at wire-speed. Full wire-speed switching is implemented at all ports.
ZXR10 2900E series switches have the following functions:
l 100Mbps ports support 10/100M self adaption and MDI/MDIX self adaption.
l Gigabit electrical ports support port 10/100/1000M self adaption and MDI/MDIX self
adaption.
l It supports port-based 802.3x flow control (full duplex) and back-pressure flow control
(half duplex).
l It supports Virtual Circuit Tester (VCT) function.
1-3
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l It supports VLAN complying with 802.1q. The maximum number of VLANs can be up
to 4094.
l It supports VLAN stacks function (QINQ), and outer label is optional (SQinQ).
l It supports GVRP dynamic VLAN.
l It has the capability of MAC addresses self-learning. The size of the MAC address
table is up to 16K.
l It supports port MAC address binding and addresses filtering.
l It supports MAC address automatic fixed function. The MAC can be recovered when
the device is power off.
l It supports the function of port security and port isolation.
l It supports the STP defined in the 802.1d, RSTP defined in the 802.1w, and MSTP
defined in the 802.1s. MSTP can have up to 4 examples.
l It supports ZESR technology and linkhello/linkdown mechanism.
l It supports LACP port binding defined in 802.3ad and port static binding. At most 15
port groups can be bound and each group contains at most 8 ports.
l It supports 1024 multicast groups, cross-VLAN ICMP snooping and MVS controllable
multicast technology.
l It supports single port loop test.
l It supports 802.1x user authentication.
l It supports VBAS, DHCP-OPTION82 and PPPOE+.
l It supports DHCP-SNOOPING.
l It supports DHCP Client function, which can automatically apply management
interface from DHCP Server.
l It supports the DHCP relay function, which allows an access device to request the
DHCP server for a host address across different network segments.
l It supports DAI dynamic ARP detection technology, which prevents ARP attack.
l It supports broadcast storm suppression.
l It supports port ingress and egress mirror, and flow-based mirror and statistics.
l It supports remote mirroring RSPAN.
l It supports ACL function based on port and VLAN. The ACL rule can be set according
to time segment.
l It supports IETF-DiffServ and IEEE-802.1p standard. All ports support 8 priority
queues. Ingress supports CAR. The queue scheduling supports SP and combination
(SP+WRR) scheduling method. It supports egress shaping and tail-drop.
l Port-based speed control includes input speed limit and output speed limit. Input
speed limit supports flow rate limit of multiple buckets. The minimal granularity is
8Kbps.
l It provides detailed port flow statistics.
l It supports 802.3ah Ethernet OAM.
l It supports SFLOW.
l It supports L2 protocol transparent transmission.
l It supports syslog function.
l It supports the function of NTP client end..
l It supports network management static route configuration.
l It supports ZGMP group manage.
1-4
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 1 System Overview
l It supports SNMPv1/v2c/v3 and RMON.
l It supports Console configuration, Telnet remote login.
l It supports SSHv2.0.
l It supports WEB function.
l It supports ZXNM01 unified network management.
l It supports the uploading and downloading of TFTP version/configuration.
l It supports the uploading and downloading of FTP version/configuration.
l ZXR10 2910E-PS/2918E-PS/2928E-PS supports PoE function complying with the
802.3af standard. At most 30 W power supply is supported.
1-5
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
This page intentionally left blank.
1-6
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2
Usage and Operation
Table of Contents
Configuration Modes ..................................................................................................2-1
Command Modes .......................................................................................................2-7
Common Command Parameters ..............................................................................2-11
Usage of Command Line..........................................................................................2-12
2.1 Configuration Modes
ZXR10 2900E provides several configuration modes, as shown in Figure 2-1, select a
configuration mode according to the network connected.
Figure 2-1 ZXR10 2900E CONFIGURATION MODES
Configuring Through Console Port
This is main configuration mode of ZXR10 2900E. ZXR10 2900E debugging configuration
is implemented through the console port connection. The console port connection
configuration uses VT100 terminal mode.
1. Select Start > Programs > Accessories > Communications > HyperTerminal on
the PC screen to start the HyperTerminal, see Figure 2-2.
2-1
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 2-2 Starting HyperTerminal
2. Enter the related local information in the open dialog box, see Figure 2-3.
Figure 2-3 Location Information Dialog Box
After the Connection Description dialog box appears, enter a name and select an
icon for the new connection, see Figure 2-4.
2-2
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
Figure 2-4 Connection Description Dialog Box
3. Based on the serial port connected to the console cable, select COM1 or COM2 as
the serial port to be connected, see Figure 2-5.
Figure 2-5 Connect To Dialog Box
2-3
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
4. Enter the properties of the selected serial port, see Figure 2-6. The port property
configuration includes Bits per Second 9600, Data bit 8, Parity None, Stop bit 1 and
Data flow control None.
Figure 2-6 COM1 Properties Dialog Box
Power on and boot the switch to initialize the system and enter operational use
configuration.
Configuration through TELNET Session
Telnet mode is often used for configuring a remote switch. A user can log in to the remote
switch through the Ethernet port of the local host. The login username and password must
be configured on the switch and the IP address of the layer-3 port on the switch can be
successfully pinged through on the local host (For configuration of the IP address of the
layer-3 port, see “Layer 3 Configuration”).
Use the command create user <name>{admin | guest}[<0-15>] (the length of user name does
not exceed 15 characters) to create a new management user, and the command set user
local <name> login-password [<string>] (the length of login-password does not exceed 16
characters) to set the login password.
2-4
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
Use the command set user {local | radius| tacacs-plus}<name> admin-password <string>
(the length of admin-password does not exceed 16 characters) to set the administrator
password.
Note:
The default username is admin and the password is zhongxing. The default management
password is null.
Suppose the IP address of the layer-3 port is 192.168.3.1 and this address can be pinged
from the local host. Then perform the following remote configuration operations:
1. Run the Telnet command on the host, see Figure 2-7.
Figure 2-7 Run Telnet
2. Click OK. A Telnet window is displayed, see Figure 2-8.
Figure 2-8 Telnet Window
3. Enter the username and password to enter the user mode of the switch.
2-5
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Configuration through SNMP Connection
SNMP (Simple Network Management Protocol) is the most popular network management
protocol at present. With this protocol, all devices in the network can be managed by a
network management server.
SNMP applies the management mode of server/client end. The back-end network
management server serves as the SNMP server. The front-end network device serves as
the SNMP client. The front end and back end share one MIB management database and
communicate with each other through the SNMP protocol.
The back-end network management server must be installed with the network
management software supporting the SNMP protocol. The switch is configured and
managed by the network management software. For the detailed configuration of SNMP
on ZXR10 2900E series switches, refer to the section of “SNMP”.
Configuration through WEB Connection
Web is another way to implement remote switches management and is similar to Telnet.
A user can log in to a remote switch through the Ethernet port of the local host. The login
username, login password and administrator password must be configured on the switch
and the Web function must be enabled. Also the IP address of the layer-3 port on the switch
can be successfully pinged through on the local host (For configuration of IP address of
the layer-3 port, refer to Layer 3 Configuration).
1. Create a new management user
create user <name>{admin | guest}[<0-15>]
user <name>: the length cannot exceed 15 characters.
2. Configure login password
set user local <name> login-password <string>
login-password <string>: the length cannot exceed 16 characters.
3. Configure administrator password
set user {local|radius}<name> admin-password <string>
admin-password <string>: the length cannot exceed 16 characters.
4. Enable web network management function (by default, this function is disabled) and
set listening port.
set web enable
set web listen-port < 80,1025-49151 >
2-6
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
Note:
The default username is admin and the password is zhongxing. The administrator
password is empty. If login with administrator account number, administrator password
cannot be empty. Therefore set administrator password first. The default http listening
port is 80.
For the detailed WEB remote login and configuration, refer to the topic of “WEB”.
2.2 Command Modes
To facilitate the configuration and management of the switch, the commands of this series
switches are allocated to different modes according to the functions and authorities. A
command can be executed only in the specified mode.
The command modes include:
User Mode
When you log in to the switch through the HyperTerminal,Telne or SSHt, you can enter the
user mode after entering the login username and password. The prompt character in the
user mode is the host name followed by “>” as shown below:
zte>
The default host name is zte. The user can modify the host name by using the command
hostname <name> (the name length cannot exceed 200 characters).
In the user mode, you can use the command exit to exit the switch configuration or use
the command show to view the system configuration and operation information.
Note:
The command show can be executed in any mode.
Global Configuration Mode
In the user mode, enter the enable command and the corresponding password to enter the
global configuration mode, as follows:
zte>enable
Password:***
zte(cfg)#
2-7
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
In the global configuration mode, you can configure various functions of the switch. Thus,
use the command set user <name> admin-password [<string>] to set the password for
entering the global configuration mode to prevent the login of unauthorized users.
To return to the user mode from the global configuration mode, use the exit command.
SNMP Configuration Mode
In the global configuration mode, you can use the command config snmp to enter the SNMP
configuration mode, as shown below:
zte(cfg)#config snmp
zte(cfg-snmp)#
In the SNMP configuration mode, you can set the SNMP and RMON parameters.
To return to the global configuration mode from the SNMP configuration mode, use the
command exit or press <Ctrl+Z>.
Layer 3 Configuration Mode
In the global configuration mode, use the command config router to enter the layer-3
configuration mode, as shown below:
zte(cfg)#config router
zte(cfg-router)#
In the Layer 3 configuration mode, the user can configure the Layer 3 port, static router,
and ARP entities.
To return to the global configuration mode from the layer-3 configuration mode, use the
command exit or press <Ctrl+Z>.
File System Configuration Mode
In the global configuration mode, use the command config tffs to enter the file system
configuration mode, as shown below:
zte(cfg)#config tffs
zte(cfg-tffs)#
In the file system configuration mode, you can operate on the switch file system,
including adding file directory, deleting file or directory, modifying file name, displaying
file or directory, changing file directory, uploading/downloading files through TFTP,
uploading/downloading files through FTP, copying files, and formatting Flash.
To return to the global configuration mode from the file system configuration mode, use
the command exit or press <Ctrl+Z>.
NAS Configuration Mode
In the global configuration mode, use the command config nas to enter the NAS
configuration mode, as shown below:
zte(cfg)#config nas
2-8
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
zte(cfg-nas)#
In the NAS configuration mode, the user can configure the switch access service, including
the user access authentication and management.
To return to the global configuration mode from the NAS configuration mode, use the
command exit or press <Ctrl+Z>.
Cluster Management Configuration Mode
In the global configuration mode, use the command config group to enter the cluster
management configuration mode, as shown below:
zte(cfg)#config group
zte(cfg-group)#
In the cluster management configuration mode, you can configure the switch cluster
management service.
To return to the global configuration mode from the cluster management configuration
mode, use the command exit or press <Ctrl+Z>.
Basic Ingress ACL Configuration Mode
In the global configuration mode, use the command config ingress-acl basic number <1-99>
to enter the basic ingress ACL configuration mode, as shown below:
zte(cfg)#config ingress-acl basic number 10
zte(ingress-basic-acl)#
In the basic ingress ACL configuration mode, you can add, delete and move the rules of
basic ingress ACL with specific ACL number .
To return to the global configuration mode from basic ingress ACL configuration mode, use
the command exit or press <Ctrl+Z>.
Extended Ingress ACL Configuration Mode
In the global configuration mode, use the command config ingress-acl extend number <100
-199> to enter extended ingress ACL configuration mode, as shown below:
zte(cfg)#config ingress-acl extend number 100
zte(ingress-extend-acl)#
In the extended ingress ACL configuration mode, you can add, delete and move the rules
of extended ingress ACL with specific ACL number.
To return to the global configuration mode from extended ingress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Layer 2 Ingress ACL Configuration Mode
In the global configuration mode, use the command config ingress-acl link number <200-2
99> to enter layer-2 ingress ACL configuration mode, as shown below:
2-9
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#config ingress-acl link number 200
zte(ingress-link-acl)#
In the layer-2 ingress ACL configuration mode, you can add, delete and move the rules of
layer-2 ingress ACL with specific ACL number.
To return to the global configuration mode from layer-2 ingress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Hybrid Ingress ACL Configuration Mode
In the global configuration mode, use the command config ingress-acl hybrid number <30
0-399> to enter hybrid ingress ACL configuration mode, as shown below:
zte(cfg)#config ingress-acl hybrid number 333
zte(ingress-hybrid-acl)#
In the hybrid ingress ACL configuration mode, you can add, delete and move the rules of
hybrid ingress ACL with specific ACL number.
To return to the global configuration mode from hybrid ingress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Global Ingress ACL Configuration Mode
In the global configuration mode, use the command config ingress-acl global to enter global
ingress ACL configuration mode, as shown below:
zte(cfg)#config ingress-acl global
zte(ingress-global-acl)#
In the global ingress ACL configuration mode, you can add, delete and move the rules of
global ingress ACL with specific ACL number.
To return to the global configuration mode from global ingress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Basic Egress ACL Configuration Mode
In the global configuration mode, use the command config egress-acl basic number <400-4
99> to enter the basic egress ACL configuration mode, as shown below:
zte(cfg)#config egress-acl basic number 400
zte(egress-basic-acl)#
In the basic egress ACL configuration mode, you can add, delete and move the rules of
basic egress ACL with specific ACL number .
To return to the global configuration mode from basic egress ACL configuration mode, use
the command exit or press <Ctrl+Z>.
Extended Egress ACL Configuration Mode
In the global configuration mode, use the command config egress-acl extend number <500-
599> to enter extended egress ACL configuration mode, as shown below:
2-10
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
zte(cfg)#config egress-acl extend number 500
zte(egress-extend-acl)#
In the extended egress ACL configuration mode, you can add, delete and move the rules
of extended egress ACL with specific ACL number.
To return to the global configuration mode from extended egress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Layer 2 Egress ACL Configuration Mode
In the global configuration mode, use the command config egress-acl link number <600-69
9> to enter layer-2 egress ACL configuration mode, as shown below:
zte(cfg)#config egress-acl link number 600
zte(egress-link-acl)#
In the layer-2 egress ACL configuration mode, you can add, delete and move the rules of
layer-2 egress ACL with specific ACL number.
To return to the global configuration mode from layer-2 egress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Hybrid Egress ACL Configuration Mode
In the global configuration mode, use the command config egress-acl hybrid number <700
-799> to enter hybrid egress ACL configuration mode, as shown below:
zte(cfg)#config egress-acl hybrid number 700
zte(egress-hybrid-acl)#
In the hybrid egress ACL configuration mode, you can add, delete and move the rules of
hybrid egress ACL with specific ACL numbers.
To return to the global configuration mode from hybrid egress ACL configuration mode,
use the command exit or press <Ctrl+Z>.
Mac-Based-Vlan Configuration Mode
In global configuration mode, execute the config mac-based-vlan session <1-64> command
to enter Mac-Based-Vlan configuration mode, as shown below:
zte(cfg)#config mac-based-vlan session 1
zte(mac-based-vlan)#
You can add or delete a rule of a specified session ID in Mac-Based-Vlan configuration
mode.
To exit Mac-Based-Vlan configuration mode and shift to global configuration mode, use
the exit command or press the <Ctrl+Z> keys.
2.3 Common Command Parameters
The common command parameters of ZXR10 2900E are listed in Table 2-1.
2-11
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Table 2-1 Common Command Parameters
Parameter Description
<portlist> Port number, port name or port number range separated by a
comma, for example:
l 1, 2, 4-8, 18
l p1, pp2, 4-8, port18
p1, pp2, port18 are the port names that users create.
Add the slot ID before the port ID of the devices supporting a
daughter card, for example, for the ZXR10 2928E-PS device:
l 1/1, 1/2, 1/4-8, 1/18
l 2/1, 2/2
<vlanlist> VLAN ID, VLAN name or VLAN range separated by a comma,
for example:
l 1-19,77,88,100-900
l vlan1,v1,10,100-200
<trunklist> Trunk ID or trunk range separated by a comma, for example,
1-5,7,10
<portname> A port number or port name can be entered once
<vlanname> A VLAN ID or VLAN name can be entered once
<trunkid> A trunk ID can be entered once.
<HH.HH.HH.HH.HH.HH> MAC address, such as 00.22.33.44.55.66
<A.B.C.D> IP address, such as 10.40.47.254
<A.B.C.D/M> IP address and mask bit, It must be the integer from 1 to 32,
such as 10.40.47.254/24
<string> A string without spaces
<mib-oid> Dotted decimal with variable length such as 1.3.6.2.19.2
<name> Name, a string without spaces
<sessionlist> Session list
2.4 Usage of Command Line
Online Help
In any command mode, enter a question mark (?) behind the DOS prompt of the system,
a list of available commands in the command mode will appear. You can use the online
help to get keywords and parameter list of any command.
1. In any command mode, enter a question mark "?" behind the DOS prompt of the
system, and a list of all commands in the mode and the brief description of the
commands will appear. For example:
2-12
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
zte>?
enable enable configure mode
exit exit from user mode
help description of the interactive help system
show show config information
list print command list
zte>
2. Enter a question mark behind a character or string, commands or a list of keywords
starting with the character or string can be displayed. Note that there is no space
between the character (string) and the question mark. For example:
zte(cfg)#c?
cfm clear config cpu-threshold createconfig clear create
zte(cfg)#c
3. Enter a question mark behind a command, a keyword or a parameter, the next keyword
or parameter to be input will be listed, and also a brief explanation will be given. Note
that a space must be entered before the question mark. For example:
zte(cfg)#config ?
egress-acl enter egress acl config mode
group enter group management config mode
ingress-acl enter ingress acl config mode
mac-based-vlan enter mac-based vlan config mode
nas enter nas config mode
router enter router config mode
snmp enter SNMP config mode
tffs enter file system config mode
4. If you enter a wrong command, keyword, or parameter and press Enter, the message
“Command not found” will be displayed on the interface. For example:
zte(cfg)#conf ter
% Command not found (0x40000034)
In the following example, the online help is used to help create a username.
zte(cfg)#cre?
zte(cfg)#create ?
acl create descriptive name for acl
cfm create CFM information
port create descriptive name for port
protocol-protect create a rule for protocol protect
user create a user
vlan create descriptive name for vlan
zte(cfg)#create user
% Parameter not enough (0x4000003f)
zte(cfg)#create user ?
<string>
user name(maxsize:15)
zte(cfg)#create user houyx ?
2-13
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
admin create an administrator
guest create a guest
zte(cfg)#create user houyx guest ?
<cr>
<0-15> specify user's priviledge
zte(cfg)#create user houyx guest
zte(cfg)#
<cr>
Command Abbreviations
In ZXR10 2900E, a command or keyword can be shortened into a character or string that
uniquely identifies this command or keyword. For example, the command exit can be
shortened as ex, and the command show port shortened as sh por.
Historical Commands
The user interface supports the function of recording entered commands. A maximum of
20 historical commands can be recorded. The function is very useful in re-invoking of a
long or complicated command.
To re-invoke a command from the record buffer, do one of the following.
Command Function
<Ctrl+P> or <↑> Invoke a historical command in the buffer forward
<Ctrl+N> or <↓> Invoke a historical command in the buffer backward
Functional Keys
The ZXR10 2900E provides a lot of functional keys for the user interface to facilitate user
operations. Table 2-2 lists the functional keys.
Table 2-2 Functional Keys Descriptions
Functional Key Usage
<Ctrl+P> or <↑> Recovers the last command (Roll back in the historical
records of commands).
<Ctrl+N> or <↑> Recovers the next command (Roll forward in the historical
records of commands).
<Ctrl+B> or <←> Moves left in the command line currently indicated by the
prompt.
<Ctrl+F> or <→> Moves right in the command line where the prompt is
currently located.
Tab After entering a character or string, if there is only one
command starting with the character or string, pressing this
key will show the complete command.
2-14
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 2 Usage and Operation
Functional Key Usage
<Ctrl+A> Skips to the beginning of the command line.
<Ctrl+E> Skips to the end of the command line.
<Ctrl+K> Deletes the characters from the cursor to the end.
Backspace or<Ctrl+H> Deletes the character on the left of the cursor.
<Ctrl+C> Cancels the command and displays the prompt character.
<Ctrl+L> Clears the screen.
<Ctrl+Y> Recovers the last command executed.
<Ctrl+H> Returns to the global configuration mode.
If the command output exceeds one page, the output is split into several pages
automatically and the prompt “—– more —– Press Q or <Ctrl+C> to break —–” appears
at the bottom of the current page. You can press any key to turn pages or press Q or
<Ctrl+C> to stop the output.
2-15
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
This page intentionally left blank.
2-16
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3
System Management
Table of Contents
File System Operation ................................................................................................3-1
Configuring the TFTP Server......................................................................................3-3
Configuring the FTP Server ........................................................................................3-5
Importing and Exporting Configuration........................................................................3-7
Backing Up and Recovering Files...............................................................................3-7
Downloading Software Version Automatically .............................................................3-8
Configuring Automatic Saving of a Configuration File ...............................................3-10
Software Version Upgrade........................................................................................3-11
File System Configuration Commands......................................................................3-15
3.1 File System Operation
In the ZXR10 2900E, the FLASH memory is the major storage device. Both the version
file and configuration file of the switch are saved in the FLASH memory. Operations, such
as version upgrade and configuration saving, should be conducted in the FLASH memory.
l The name of the version file is zImage. By default, it is saved in the /img directory.
l The name of configuration file is startrun.dat. By default, it is saved in the /cfg
directory.
Directory Operation
The directory can be created and deleted. The current working directory, the file of the
specified directory can be viewed.
Configure directory operation at global mode.
Ste-
Command Function
p
Enters file system configuration
1 zte(cfg)#config tffs
mode.
2 zte(cfg-tffs)#md <directory name> Creates a directory.
3 zte(cfg-tffs)#rename <file-name> <file-name> Modifies the directory name.
Changes the current directory,
4 zte(cfg-tffs)#cd <directory name>
and opens this directory.
5 zte(cfg-tffs)#ls Lists the current directories.
3-1
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Use the remove <file-name> command to delete a specified directory. The img, cfg, and
data directories created by default and all non-empty directories cannot be deleted.
File Operation
The file system can delete a specified file, rename a file name, copy a file and view file
information.
File operation is configured in global configuration mode.
Ste-
Command Function
p
Enters file system configuration
1 zte(cfg)#config tffs
mode.
2 zte(cfg-tffs)#rename <file-name> <file-name> Changes a file name.
3 zte(cfg-tffs)#copy <source-pathname> <dest-pathname> Copies a file.
4 zte(cfg-tffs)#ls Lists the current files.
Use the remove <file-name> command to delete a specified file.
Version Download/Upload Through TFTP
Through the TFTP, you can back up and restore the version files and configuration files of
the switch. After the TFTP server is enabled at the back end, you can enter file system
configuration mode and perform related operations.
To download or upload a version through TFTP, perform the following steps.
Ste-
Command Function
p
Enters file system configuration
1 zte(cfg)#config tffs
mode.
2 zte(cfg-tffs)#cd <directory name> Enters the directory.
zte(cfg-tffs)#tftp <A.B.C.D> download <remote-file-name
Downloads/Uploads the version
3 >[<local-file-name>] zte(cfg-tffs)# tftp <A.B.C.D> upload
through TFTP.
<local-file-name>[<remote-file-name>]
Version Download/Upload Through FTP
Through the FTP, you can back up and restore the version files and configuration files of
the switch. After the FTP server is enabled at the back end, you can enter file system
configuration mode and perform related operations.
To download or upload a version through FTP, perform the following steps.
3-2
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
Ste-
Command Function
p
Enters file system configuration
1 zte(cfg)#config tffs
mode.
2 zte(cfg-tffs)#cd <directory name> Enters the directory.
zte(cfg-tffs)#ftp <A.B.C.D><remote-file-name>{download|uplo Downloads or uploads a version
3
ad}<local-file-name> username <string> password <string> through FTP.
Formatting Flash
Caution!
After the flash is formatted, all system software and configurations will be cleared.
Perform the following operations in global mode.
Ste-
Command Function
p
1 zte(cfg)#config tffs Enters file system configuration mode.
2 zte(cfg-tffs)#format Formats flash.
3.2 Configuring the TFTP Server
The switch version file and configuration file can be backed up or restored by TFTP. The
TFTP server application software is started at the back end to communicate with the switch
(TFTP client) to implement the file backup and recovery.
Steps
1. Run the tftpd software at the back-end host. The interface is shown in Figure 3-1.
3-3
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 3-1 TFTPD Server
2. Click Tftpd > Configure, in the dialog box that appears, click Browse and select the
directory with the version file or configuration file, for example, D:\IMG.
3. Click the second Browse to select the log file name, click OK to complete the
configuration, see Figure 3-2.
Figure 3-2 Tftpd Settings Dialog Box
After the TFTP configuration is completed, perform the TFTP operations on the switch.
For details, see the later sections.
– End of Steps –
3-4
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
3.3 Configuring the FTP Server
The switch version file and configuration file can be backed up or restored by FTP. The FTP
server application software is started at the back end to communicate with the switch (FTP
client) to implement the file backup and recovery. This section describes how to configure
the FTP server software FileZilla Server as an example for configuring the back-end FTP
server.
Steps
1. Run the FileZilla Server software on the back-end host and perform the operation as
shown in Figure 3-3. The FileZilla Server window is displayed, see Figure 3-4.
Figure 3-3 Connect to Server Dialog Box
Figure 3-4 FileZilla Server Window
2. Click Edit > Uers and create a user name and password by referring to Figure 3-5.
3-5
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 3-5 Users Dialog Box
3. Select Shared folders in the left pane and set a primary directory for the new user,
see Figure 3-6.
Figure 3-6 Directory Setting Area
After that, you can perform FTP application operations on the switch. The scenarios
for FTP and TFTP are the same, including the configuration import and export and
automatic software download. For details, refer to the following sections.
– End of Steps –
3-6
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
3.4 Importing and Exporting Configuration
Note:
The switch provides the configuration information import/export function, which makes it
easy to configure and manage the switch.
Export the configuration information
In global configuration mode, use the command write to export the current system
configuration to startrun.dat and save it in the FLASH memory. This file can also be
uploaded to the TFTP server for viewing, modification and bulk configuration.
zte(cfg-tffs)#cd cfg
zte(cfg-tffs)#tftp 192.168.1.102 upload startrun.dat
zte(cfg-tffs)#cd ..
Import the configuration information
startrun.dat is the configuration file in text and is generated by using the command
write. Contents can be edited manually as needed and then downloaded to /cfg of the
switch by using the command tftp. After the configuration file is downloaded to the flash
of switch, reboot the switch to import the configuration.
zte(cfg-tffs)#cd cfg
zte(cfg-tffs)#tftp 192.168.1.102 download startrun.dat
zte(cfg-tffs)#cd ..
3.5 Backing Up and Recovering Files
Note:
The files mentioned here refer to the configuration file and version file in the FLASH
memory.
Back up the configuration file
If a command is used to modify the switch configuration, the data is running in the memory
in real time. If the switch is restarted, all the contents newly configured will be lost. To avoid
this, use the write command to save the current configuration in the FLASH memory. The
following shows the write command:
zte(cfg)#write
3-7
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
To prevent damage to the configuration data, back up the configuration data by using the
command tftp.
The following command can be used to back up a configuration file in the FLASH memory
to the back-end TFTP Server:
zte(cfg-tffs)#cd cfg
zte(cfg-tffs)#tftp 192.168.1.102 upload startrun.dat
zte(cfg-tffs)#cd ..
Recover the configuration file
Execute the following command to download the configuration file in the back-end TFTP
server to the FLASH memory
zte(cfg-tffs)#cd cfg
zte(cfg-tffs)#tftp 192.168.1.102 download startrun.dat
zte(cfg-tffs)#cd ..
Back up the version file
Similar to the configuration file, you can use the tftp command to upload the front-end
version file to the back-end TFTP server. For example:
zte(cfg-tffs)#cd img
zte(cfg-tffs)#tftp 192.168.1.102 upload zImage
zte(cfg-tffs)#cd ..
Recover the version file
Version file recovery is used to retransmit the back-end backup version file to the front
end through TFTP. Recovery is very important in the case of upgrade failure. The version
recovery operation is basically the same as the version upgrade procedure. For details,
refer to software version upgrade.
3.6 Downloading Software Version Automatically
Note:
The automatic software version download function is used for an undeployed device.
When the switch is powered on for the first time, the system identifies that the automatic
download flag is set (default configuration upon shipment from factory) in the NVRAM and
no configuration file exists, so the system triggers automatic download.
The system obtains the version file name and (or) the configuration file name by interacting
with a DHCP server. It downloads the files by interacting with a TFTP server. If the
3-8
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
download succeeds (even if one file is downloaded successfully), the automatic download
flag in the NVRAM is cleared and the switch is restarted.
For the relation between the files transferred by the DHCP server and the triggered
download operations, refer to the table below:
Name Whether to Download the Whether to Download
Version File Configuration
zImage Yes No
config.dat No Yes
startrun.dat No Yes
*.dat No Yes
config.dat@zImage Yes Yes
startrun.dat@zImage Yes Yes
*.dat@zImage Yes Yes
*.dat, wherein, “*” is a wild card indicating a device type. This means the configuration file
automatically adapts in accordance with the device type.
The name of the file to be downloaded is a character string configured on the DHCP server,
and it cannot be modified locally.
By executing the show dhcp command, you can see the configuration file to be downloaded
to the current device, for example, the ZXR10_2928E.dat file downloaded from the TFTP
server to the ZXR10 2928E device.
The following table lists the complete adaption relation:
ID Device Configuration File Name
1 ZXR10 2910E-PS ZXR10_2910E-PS.dat
2 ZXR10 2918E-PS ZXR10_2918E-PS.dat
3 ZXR10 2918E ZXR10_2918E.dat
4 ZXR10 2928E-PS ZXR10_2928E-PS.dat
5 ZXR10 2928E ZXR10_2928E.dat
6 ZXR10 2952E ZXR10_2952E.dat
zte(cfg)#show dhcp
DHCP download flag is disabled, config file is found.
DHCP download will not startup, when system reboot.
DHCP config file(option-67) *.dat will be translated to ZXR10_2928E.dat.
DHCP snooping-and-option82 is disabled.
DHCP client is enabled.
DHCP client broadcast-flag is enabled.
3-9
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 3-7 Network Architecture of Automatic Configuration File Downloading
The network architecture is shown in Figure 3-7. Set the TFTP server address and version
file name on the DHCP server. For example, set the TFTP server address to 10.40.89.78,
and set the file name to *.dat@zImage. After powered on, the system downloads ZXR10
2918E.dat (assume that the device type is ZXR10 2918E) and zImage from the TFTP
server. After downloading the file successfully, the system is restarted.
3.7 Configuring Automatic Saving of a Configuration
File
Note:
The function of automatic saving of a configuration file helps you to upload switch
configurations to the back end.
The uploaded configuration files include startrun.dat and toPmac.dat. When the
time set by period is counted down to 0, the switch uploads the startrun.dat file to the
TFTP server at a local time between 00:00 and 00:01, and uploads the toPmac.dat file
one minute later. The automatically uploaded files are stored in the flash sub folder in
theupload/download directory configured by the TFTP server. The names of the files
respectively are startrun mm_dd_yy.dat and toPmac mm_dd_yy.dat, where “mm”,
“dd”, and “yy” indicate the date on which the upload occurs.
3-10
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
Figure 3-8 Network Structure of Automatic Configuration File Uploading
The network is shown in Figure 3-8. Before configuring the following commands, make
sure that the switch can ping the server successfully. Assume that the TFTP server
address is 10.40.89.78, and the configuration is save to the server once per 10 days. The
configuration commands are as follows:
zte(cfg)#set auto-saveconfig serverip 10.40.89.78
zte(cfg)#set auto-saveconfig period 10
zte(cfg)#set auto-saveconfig enable
Caution!
The enable command should be configured after the server IP is configured. If the server IP
is not configured, the system displays a prompt. The automatic uploading function cannot
be enabled successfully. If a communication exception occurrs between the switch and
the server when the uploading function is triggered last time, the configuration files cannot
be uploaded successfully this time. The system uploads the configuration files when the
next triggering time comes.
3.8 Software Version Upgrade
Note:
Normally, version upgrade is needed only when the original version does not support some
functions or the equipment operate abnormally due to some special causes. Improper
version upgrade operations may result in upgrade failure and startup failure of the system.
Therefore, before version upgrade, get familiar with the principles and operations of the
ZXR10 2900E and master the upgrade procedure.
3-11
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Version upgrade operations performed in proper and improper switch systems are
different.
Displaying the Version Information
If the system status allows, check the version information before and after the upgrade.
In global configuration mode, use the command show version to display the system
hardware and software version information.
The displayed contents are as follows:
zte(cfg)#show version
ZXR10 Router Operating System Software, ZTE Corporation:
ZXR10 2928E Version Number : 2928E Series V2.05.10.05
Copyright (c) 2001-2012 By ZTE Corporation
Compiled: 01:09:36 Mar 6 2012
System uptime is 0 years 0 days 0 hours 0 minutes 16 seconds
Main processor : arm926ejs
Bootrom Version : v1.08 Creation Date : Feb 27 2012
System Memory : 128 M bytes System Flash : 256 M bytes
EPLD Version (Dno.) : V1.0
PCB Version (Dno.) : V1.0
Startup From : net
Switch's Mac Address: 00.d0.d0.3c.3b.00
Module 0: ZXR10 2928E; fasteth: 0; gbit: 28;
Version Upgrade When the System is Normal
If the switch runs normally, upgrade the version as follows:
1. Connect Console port of the switch to the serial port of the back-end host using
the self-contained configuration cable. Connect an Ethernet port of the switch to
the network port of the back-end host using a network cable. Check whether the
connections are correct.
2. Set the IP address of the Ethernet port on the switch. Set the IP address of the
back-end host used for upgrade. The two IP addresses must be in the same network
segment so that the host can ping the switch.
3. Start the TFTP server software on the back-end host and configure it by referring to
FTP Configuration.
4. On the switch, use the command show version to check the information of current
operating version.
5. Enter the file system configuration mode and use the command remove to delete the
old version file in the FLASH memory. If the FLASH memory has sufficient space,
change the name of the old version file and keep it in the FLASH memory.
zte(cfg)#config tffs
zte(cfg-tffs)#cd img
zte(cfg-tffs)#remove zImage
3-12
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
zte(cfg-tffs)#cd ..
6. Use the command tftp to upgrade the version. The following shows how to download
the version file from the TFTP server to the FLASH memory:
zte(cfg-tffs)#cd img
zte(cfg-tffs)#tftp 10.40.89.78 download zImage
.................................................
.................................................
.................................................
7,384,016 bytes downloaded
zte(cfg-tffs)#ls
zte(cfg-tffs)#ls
/img/
. <DIR>
.. <DIR>
zImage 7,536,884 bytes
240,568,768 bytes free
7. Restart the switch. After successful startup, check the version under running and
confirm whether the upgrading is successful.
Version Upgrade When the System is Abnormal
If the switch cannot be started normally or runs abnormally, upgrade the version as follows:
1. Connect Console port of the switch to the serial port of the background host by using
the self-contained configuration cable. Connect an Ethernet port of the switch to the
network port of the background host by using a network cable. Check whether the
connections are correct.
2. Restart the switch. At the HyperTerminal, press any key as prompted to enter the
[ZXR10 Boot] status.
ZXR10 2928E BootRom Version v1.08
Compiled Feb 27 2012 10:32:29
Copyright (c) 2010 by ZTE Corporation.
boot location [0:Net,1:Flash] : 0
actport : 1
serverip : 10.40.89.78
netmask : 255.255.255.0
ipaddr : 10.40.89.100
bootfile : /img/zImage
username : ZXR10
password : 123456
MAC : 00:d0:d0:3c:3b:00
3-13
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
[ZXR10 Boot]
3. Enter c in the ZX10 Boot status and press Enter to enter the parameter modification
status. Set the IP addresses of the Ethernet port and the TFTP server. The two
addresses are set to be in the same network segment.
[ZXR10 Boot]: c
boot location [0:Net,1:Flash] :
0/*start by tftp or flash */
actport : 1
/*select the panel port that tftp enables*/
serverip : 10.40.89.78
/*ftp/tftp server address*/
netmask : 255.255.255.0
/*subnet mask*/
ipaddr : 10.40.89.79
/*local interface address*/
bootfile : /img/zImage
/*version file location*/
username : ZXR10
/*the username when the file is downloaded by ftp*/
password : ZXR10
/*the password when the file is downloaded by ftp */
MAC : 00:d0:d0:30:20:10
/*Switch MAC address*/
4. Set the IP address of the back-end host to be the same as that of the above TFTP
server.
5. Start the TFTP server software on the back-end server and configure the TFTP by
referring to the TFTP configuration.
6. In the ZX10 Boot status, enter zte, enter the BootManager status of the switch. Enter
? to display the command list for this state.
[ZXR10 Boot]:zte
[bootManager]: ?
? - alias for 'help'
cd - change current path
exit - exit from bootManager mode
format - format flash
ftp - get/put file from/to FTP server
help - print online help
l - load zImage
ls - list files in current directory
mv - change [source] name to [destination] name
reboot - perform REBOOT of the CPU
rm - remove file
setBOOTpassword - set password for BOOT mode
setPtype- set packaged type
show - show board information
3-14
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 3 System Management
update - update boot or firmware
[bootManager]:
7. In the BootManager status, enter the reboot command to restart the switch and load
the new version file. The following shows how to download the version file from the
TFTP server to the FLASH memory:
FTP directory format: ftp get<filename>. The file will be downloaded to the current
directory. If the current directory requires check, use the ls command. The port
address used in ftp and panel port information can be modified in the c directory in
ZX10 Boot. Take port 1 as the example.
boot location [0:Net,1:Flash] : 1
actport : 1
serverip : 10.40.89.78
netmask : 255.255.255.0
ipaddr : 10.40.89.79
bootfile : /img/zImage
username : ZXR10
password : ZXR10
MAC : 00:d0:d0:30:20:10
Hit any key to stop autoboot: 0
[ZXR10 Boot]:
[ZXR10 Boot]:zte
[bootManager]: cd img
[bootManager]: ftp get zImage
............................................
............................................
............................................
Ftp get zImage successfully, 7397428 bytes received.
[bootManager]:
8. In the BootManager status, use the reboot command to restart the switch by using
the new version. If the switch is started normally, use the show version command to
check whether the new version is operating in the memory. If the switch cannot be
started normally, it indicates the version upgrade fails. In this case, repeat the above
upgrade procedure from step 1.
3.9 File System Configuration Commands
File system configuration includes the following commands:
Command Function
zte(cfg-tffs)#md <directory name> Creates a directory.
zte(cfg-tffs)#remove <file-name> Deletes a file or directory.
zte(cfg-tffs)#rename <file-name><file-name> Modifies a file or directory name.
zte(cfg-tffs)#ls Displays a sub-directory and file.
3-15
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg-tffs)#cd <directory name> Changes the current directory.
zte(cfg-tffs)#tftp <A.B.C.D>{download | upload}<remote-file-name>[<l Uploads or downloads files to/from the
ocal-file-name>] TFTP server.
zte(cfg-tffs)#tftp commander {download | upload}<remote-file-name Uploads or downloads files to/from the
>[<local-file-name>] cluster commander.
zte(cfg-tffs)#copy <source-pathname><dest-pathname> Copies files.
zte(cfg-tffs)#format Formats Flash.
zte(cfg-tffs)#update bootrom Updates bootrom.
zte(cfg)#set dhcp download{enable | disable} Enables or disables automatic
download function of a DHCP client.
zte(cfg)#set auto-saveconfig {enable | disable} Enables or disables the system to
automatically upload the configuration
file to a TFTP server.
zte(cfg)#set auto-saveconfig serverip <A.B.C.D> Sets the IP address of the TFTP server
to which the system automatically
uploads the configuration file.
zte(cfg)#set auto-saveconfig period <1-30> Sets the interval for automatically
uploading the configuration file (unit:
day).
show auto-saveconfig (all configuration mode) Displays the status of the automatic
upload function.
3-16
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4
Service Configuration
Table of Contents
Management Configuration ........................................................................................4-2
Port Configuration ......................................................................................................4-5
PoE Configuration ......................................................................................................4-6
Port Mirroring .............................................................................................................4-9
VLAN Configuration..................................................................................................4-12
MAC Table Operation ...............................................................................................4-14
LACP Configuration..................................................................................................4-17
IGMP Snooping Configuration ..................................................................................4-20
MLD Snooping Configuration....................................................................................4-24
IPTV Configuration ...................................................................................................4-26
STP Configuration ....................................................................................................4-32
ACL Configuration ....................................................................................................4-42
QoS Configuration....................................................................................................4-50
PVLAN Configuration ...............................................................................................4-56
Layer 2 Protocol Transparent Transmission Configuration ........................................4-59
IPv4 Layer 3 Configuration .......................................................................................4-61
IPv6 Layer 3 Configuration .......................................................................................4-63
DAI Configuration .....................................................................................................4-64
Access Service Configuration...................................................................................4-66
MAC Authentication Configuration............................................................................4-74
QinQ Configuration...................................................................................................4-75
Syslog Configuration ................................................................................................4-77
NTP Configuration....................................................................................................4-78
GARP/GVRP Configuration ......................................................................................4-80
DHCP Configuration.................................................................................................4-82
DHCPv6 Configuration .............................................................................................4-87
VBAS Configuration .................................................................................................4-90
PPPoE-PLUS Configuration .....................................................................................4-92
ZESR Configuration .................................................................................................4-93
OAM Configuration................................................................................................. 4-111
SQinQ Configuration .............................................................................................. 4-117
VLAN Mapping Configuration ................................................................................. 4-119
sFlow Configuration................................................................................................4-122
PP Configuration ....................................................................................................4-123
LLDP Configuration ................................................................................................4-125
Single Port Loop Detection Configuration ...............................................................4-128
UDLD Configuration ...............................................................................................4-131
4-1
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
TACACS+ Configuration.........................................................................................4-133
Time Range Configuration......................................................................................4-135
Voice VLAN Configuration ......................................................................................4-136
802.1AG Configuration ...........................................................................................4-138
Y.1731 Configuration ..............................................................................................4-144
MAC-based VLAN Command Configuration ...........................................................4-149
DHCP Relay Configuration .....................................................................................4-150
4.1 Management Configuration
Management Configuration Overview
Management configuration includes the following commands:
1. Mode switch configuration
2. Console attribute configuration
3. Global information configuration
4. Switch user access configuration
Configuring Management Service
The configuration of management service includes the following commands:
Command Function
zte(cfg)#config group Enters cluster management configuration mode
zte(cfg)#config router Enters layer-3 interface configuration mode.
zte(cfg)#config snmp Enters SNMP configuration mode.
zte(cfg)#config tffs Enters file system configuration mode.
zte(cfg)#config nas Enters service configuration mode.
zte(cfg)#config mac-based-vlan Enters mac based vlan configuration mode.
exit (All configuration mode) Returns to the original command line mode.
Enters global configuration mode from user configuration
zte>enable
mode.
list (all configuration modes) Lists all valid configuration commands in current mode.
zte(cfg)#set auto-reset <2-120> Sets switch Console automatic log-out time.
zte(cfg)#line-vty timeout <1-12> Sets Telnet user login timeout time.
zte(cfg)#set date <yyyy-mm-dd> time <hh:mm:ss> Sets switch date and time.
zte(cfg)#set date summer-time {one-year Sets the time period when the daylight saving time is used.
| repeating}{date <yyyy-mm-dd><hh:m
m:ss><yyyy-mm-dd><hh:mm:ss>| week
<week><day><month><year><hh:mm:ss><wee
k><day><month><year><hh:mm:ss>}[<60-1440>]
4-2
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#clear summer-time Deletes the configuration of the daylight saving time.
zte(cfg)#hostname <name> Sets or changes the host name.
zte(cfg)#promptlen <0-48> Sets the length of the host name.
zte(cfg)#sysLocation <string> Sets the location information of switch.
zte(cfg)#reboot Reboots the switch immediately.
zte(cfg)#reboot-time <hh:mm> Sets the time when the switch is rebooted.
Logs in to the Telnet server. You can select the source
zte(cfg)#telnet <A.B.C.D>[<A.B.C.D>]
address.
zte(cfg)#create user <name>{admin | guest}[<0-15>] Creates a new local user.
zte(cfg)#set loginauth {local | radius|local+ra
dius|radius+local|tacacs-plus| local+tacacs-plus | Sets login authentication mode.
tacacs-plus+local}
zte(cfg)#set user local <name> login-password
Sets local user login password.
[<string>]
zte(cfg)#set adminauth {local|radius|lo
cal+radius|radius+local|none|tacacs-plus| Sets management authentication mode.
local+tacacs-plus|tacacs-plus+local}
zte(cfg)#set user local <name> admin-password
Sets a local user management password.
[<string>]
zte(cfg)#set user radius purview {admin | guest} Sets a RADIUS authentication user login authority.
zte(cfg)#set user radius admin-password [<string>] Sets a RADIUS user management password.
zte(cfg)#set user tacacs-plus purview {admin | Sets login permissions of TACACS+ authentication users
guest}
zte(cfg)#set user tacacs-plus admin-password Sets the TACACS user management password.
[<string>]
zte(cfg)#set user multi-user {enable | disable} Sets the multi-user login function.
zte(cfg)#cpu-threshold <30-90> Sets the CPU usage threshold.
zte(cfg)#mem-threshold <60-90> Sets the memory usage threshold.
Saves the current configuration information to FLASH and
zte(cfg)#write
recovers when the switch is rebooted.
zte(cfg)#clear user <name> Deletes a user.
zte(cfg)#clear reboot-time Clears automatic reboot configuration.
Permits or forbids printing the real alarm log information to
zte(cfg)#terminal monitor {on | off}
the terminal.
zte(cfg)#terminal log {on | off} Permits or forbids writing log.
4-3
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg)#terminal log toFile Saves the log in RAM to FLASH.
zte(cfg)#terminal log timer {enable | disable |
Sets automatic saving of log information.
interval <1-720>}
zte(cfg)#set bootpassword to <string> Sets the password for logging in to boot mode
zte(cfg)#set bootpassword clear Deletes the password for logging in to boot mode
zte(cfg)#set fan mode {auto | manual} Sets the fan operating mode.
zte(cfg)#set fan speed Sets the fan operating speed.
zte(cfg)#readconfig <filename> Reads the local file on the device as the configuration.
zte(cfg)#set temperature-alarm <0-100> Sets the threshold for over temperature alarms on the switch.
zte(cfg)#clear terminal-log Clears log information.
zte(cfg)#terminal log module {all|arp-inspection|d Allows/forbids writing logs of a module.
hcp|radius|AAA }{ off | on }
zte(cfg)#terminal monitor module {all| Allows/forbids printing real-time alarm logs of a module for
arp-inspection|dhcp|radius|AAA }{ off | on } the terminal.
list include <string> (all configuration modes) Displays the commands including a specific string.
show terminal log include <string> (all configuration
Displays alarm log information including a specific string.
modes)
show reset-time (all configuration modes) Displays switch Console automatic logout time configuration.
show line-vty (all configuration modes) Displays Telnet user login timeout time configuration.
show loginauth (all configuration mode) Displays login authentication mode.
Displays management authentication state and authentication
show adminauth (all configuration modes)
mode.
show terminal (all configuration modes) Displays terminal log configuration information.
show terminal log (all configuration modes) Displays the terminal log information in RAM.
Displays the user configured on the switch and current login
show user (all configuration modes)
user information.
show version (all configuration modes) Displays the system information.
show running-config [{include | begin}<string>] (all
Displays all current system non-default configuration.
configuration modes)
Displays all non-default configuration when system is written
show start-config (all configuration modes)
at last.
show date-time (all configuration modes) Displays the current date and time.
show reboot-time (all configuration modes) Displays automatic reboot configuration.
show cpu (all configuration modes) Displays CPU usage at the duration of 5 s, 30 s and 2 m.
4-4
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
show memory (all configuration modes) Displays the current RAM use.
show fan (all configuration modes) Displays the fan status.
show summer-time(all configuration modes) Displays DST configuration.
show bootpassword(all configuration modes) Displays the password for logging in to boot mode
show Etag(all configuration modes) Displays the electronic labels of devices.
show temperature(all configuration modes) Displays the device temperature.
4.2 Port Configuration
Port Configuration Overview
The port parameters can be configured on the ZXR10 2900E. They include
auto-negotiation, duplex mode, rate and line detection. The commands include the
following types:
1. Port basic parameters configuration
2. Port diagnosis
3. Port information view
Configuring a Port
The port configuration includes the following commands:
Command Function
zte(cfg)#set port <portlist>{enable | disable} Enables or disables the port.
zte(cfg)#set port <portlist> work-mode {fiber | copper |
Sets the combo port to switch in electrooptic mode.
auto [ prefer {first-up | fiber | copper}]}
Sets the advertisement of the maximum port speed duplex
zte(cfg)#set port <portlist> speedadvertise maxspeed
information.
zte(cfg)#set port <portlist> speedadvertise {speed10 |
Sets the advertisement of port speed duplex information.
speed100 | speed1000}{fullduplex | halfduplex}
zte(cfg)#set port <portlist> duplex {full | half | auto} Sets the working mode of port to full duplex or half duplex.
Sets the speed of port to 10 Mbps, 100 Mbps, or 1000
zte(cfg)#set port <portlist> speed {10 | 100 | 1000 | auto}
Mbps.
zte(cfg)#set port <portlist> mdix {auto | normal |
Sets line sequence identification function.
crossover}
zte(cfg)#set port <portlist> flowcontrol {enable | disable} Enables or disables port flow control function.
zte(cfg)#set port <portlist> description <string> Sets port description information.
4-5
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg)#set port <portlist> accept-frame {tag | untag |
Sets the packet type that the port allows to accept.
all}
zte(cfg)#set jumbo port <portlist>{enable | disable } Enables or disables the port jumbo function.
zte(cfg)#set port <portlist> pvid <1-4094> Sets a default port PVID.
zte(cfg)#set port statistics mode {ingress | egress | both} Sets packet statistics mode.
zte(cfg)#set sleep-mode {enable | disable} Enables or disables port sleep mode.
zte(cfg)#create port <portid> name <string> Creates a port name.
zte(cfg)#clear port <portlist>{name | statistics | Clears the port name, port statistics data, port description,
description| multicast-filter} and the multicast filter flag.
Displays the configuration and status information of all
show port (all configuration modes)
ports.
show port [<portlist>] (all configuration modes) Displays port configuration and status information.
show port <portlist> statistics (all configuration modes) Displays the statistics of the current port.
show port <portlist> statistics [1min_unit | 5min_unit]
Displays port statistics data.
(all configuration modes)
show port <portlist> utilization (all configuration modes) Displays port bandwidth utilization.
show port <portlist> brief (all configuration modes) Displays port brief.
show port <portlist> vlan (all configuration modes) Displays the location of VLAN.
show jumbo (all configuration modes) Displays the jumbo configuration of all ports.
show jumbo [<portlist>] (all configuration modes) Displays port jumbo configuration information.
show vct port <portid> (all configuration modes) Displays port virtual line detection result.
Displays the up/down status of each port and VCT
show cable-diag(all configuration modes)
detection result.
zte(cfg)#set port <portlist> protect {enable | disable } Enables or disables the port protection function.
zte(cfg)#set port <portlist> protect time <1-10> Sets the port protection period in port protection status.
4.3 PoE Configuration
PoE Configuration Overview
Power over Ethernet (Briefed as PoE) is the extended feature that supports network device
with Ethernet electrical port. The network devices supporting PoE function (Switch or
router) can provide power supply through Twisted Pair for remote PD such as IP phone,
WLAN AP, Network Camera, which realizes remote power supply.
Ethernet remote power supply sometimes is named as network power supply. It is a
kind of technology that delivers a little electricity and provides power supply through 10
4-6
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
BASE-T and 100 BASE-TX. In the case that the current Ethernet Cat.5 cabling basic
structure is not changed, PoE can provide DC power supply for the device based on IP
(such as IP phone, wireless local network AP and network camera) when it data signals
are transmitted. PoE technology can reduce the cost mostly when the current structural
cabling security is ensured. Figure 4-1 shows the typical PoE application.
Figure 4-1 PoE Application
ZXR10 2900E-PS series switch supports the following PoE features:
l ZXR10 2900E-PS series switch includes ZXR10 2910E-PS,ZXR10 2918E-PS and
ZXR10 2928E-PS.The device can provide power supply for the PD complying with
802.3af/802.3at standard and the single port can provide up to 30 W power.
l ZXR10 2900E-PS series switch supports both DC and AC power input. When ZXR10
2900E-PS series switch acts as a PSE, the maximum output power depends on the
RPS if the switch uses DC power input, or the maximum output power is 250 W if
the switch uses AC power input. A power module provides 400 W output power. To
replace a power module, read the instructions or name plate of the power module.
l ZXR10 2900E-PS series switch provides the following configuration and management
functions for convenient use.
1. Sets integrated device maximum output power.
2. Sets port maximum output power.
4-7
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
3. Sets port power supply priority. System provides three types of priorities for each
port. When the total power of all ports exceeds the device maximum output power,
the device will decide which devices are given power supply according to port
power supply priority. The port with high power supply priority will provide power
in advance. The port with lowest priority will stop power supply. If the two ports
have the same power supply priority, the priority of port will be decided by its port
number, the less the port number, the higher the priority and provide power in
advance.
4. Provides the monitoring function for fan.
5. Provides various alarm informations and abnormal monitors and alarm report
mechanisms such as Terminal log, SNMP Trap and Syslog.
Configuring PoE
The PoE configuration includes the following commands:
Command Function
zte(cfg)#set poe port <portlist>{enable | disable} Enables or disables the port function.
zte(cfg)#set poe port <portlist> pd-max-power {15.4 | 4.0 | 7.0 | ext.18 Sets the maximum power supply of the
| ext.27 | ext.30} port.
zte(cfg)#set poe port <portlist> priority {critical | high | low} Sets the port power supply priority.
Enables or disables the port force-power
zte(cfg)#set poe port <portlist> forcepower {enable |disable}
function.
Enables or disables the port extended
zte(cfg)#set poe port <portlist> extend-detection {enable |disable}
detection function.
Sets device maximum output power
zte(cfg)#set poe power maxvalue <1–500>[threshold <0-30>]
and protection threshold.
zte(cfg)#set poe port <port list> enable time-range <word> Enables the port PoE.
show poe device (all configuration modes) Displays the PoE status of the device.
show poe status [port <portlist>] (all configuration modes) Displays the PoE status of the port.
show poe config [port <portlist>] (all configuration modes) Displays PoE configuration information.
PoE Configuration Instance
l Configuration Description
DUT device is directly connected to PD.
Configure power supply device of PS type. The type that supports power supply
includes ZXR10 2910E-PS,ZXR10 2918E-PS and ZXR10 2928E-PS . Take ZXR10
2918E-PS as an example, provide 15.4 W power supply complying with AF standard
for 16 ports. Each PD is about 13 W.
l Configuration Procedure
zte(cfg)#set poe port 1-16 pd-max-power 15.4
4-8
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zte(cfg)#set poe port 1-16 priority low
zte(cfg)#set poe port 1-16 enable
l Configuration Verification
zte(cfg)#show poe status port 12
port: 12
power up : on
power device : delivering power
power device type : standard power device
802.3af classification : class 0
current-power : 12.9 watt
avgerage-power : 12.9 watt
peak-power : 13.0 watt
zte(cfg)#show poe status port 13
port: 13
power up : on
power device : delivering power
power device type : standard power device
802.3af classification : class 0
current-power : 13.2 watt
avgerage-power : 13.2 watt
peak-power : 13.2 watt
zte(cfg)#show poe device
PSE firmware version : ZTE 3.3
PSE max power : 250 watt
PSE power threshold : 10 watt
PSE current power : 207.1 watt
PSE average-power : 207.1 watt
PSE peak-power : 207.2 watt
PSE critical-power : 0 watt
From the results, we can see that the DUT device provides a power supply for PD
stably.
4.4 Port Mirroring
Port Mirroring Overview
Port mirroring is used to mirror data packets of the switch port (ingress mirroring port) to an
ingress destination port (ingress monitoring port), or mirror the data packets of the switch
port (egress mirroring port) to an egress destination port (egress monitoring port).
By using mirroring, data packets flowing in or out of a certain port can be monitored. Port
mirroring provides an effective tool for the maintenance and monitoring of the switch.
4-9
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
ZXR10 2900E adds the RSPAN function, that is, when the packet is sent from the
destination, the specified tag such as priority or vid can be added, which provides support
for remote mirroring.
Note:
By default, switches do not have mirroring ports or monitoring ports. The correct data
packets received by ingress mirroring port are mirrored onto the monitoring ports, but data
packets directly discarded on the ingress port (for example, because of CRC errors) are
not mirrored.
Configuring Port Mirroring
The port mirroring configuration includes the following commands:
Command Function
zte(cfg)#set mirror session <1-3> add source-port <portlist>{ingress | Adds an egress or ingress mirroring
egress} source port according to session.
zte(cfg)#set mirror session <1-3> add dest-port <1-28>{ingress | egress| Adds an egress or ingress mirroring
rspan} destination port according to session.
zte(cfg)#set mirror session <1-3> delete source-port <portlist>{ingress Deletes an egress or ingress monitoring
| egress} port according to session.
zte(cfg)#set mirror session <1-3> delete dest-port <1-28>{ingress | egress| Deletes an egress or ingress monitoring
rspan} (destination) port according to session.
zte(cfg)#set mirror rspan-tag vlan-id <1-4094> priority <0-7>{ingress Sets RSPAN tag format including
| egress} VLAN-ID and priority.
Sets ingress or egress port mirroring
zte(cfg)#set mirror statistic sample-interval <1-2047>{ingress | egress}
sample frequency.
Clears the configuration in session of
zte(cfg)#clear mirror session <1-3>
mirror.
Displays the configuration information
show mirror [session <1-3>] (all configuration modes)
of mirror session.
Displays the ingress or egress RSPAN
show mirror rspan (all configuration modes)
configuration information.
Displays ingress or egress sample
show mirror statistical (all configuration modes)
frequency configuration information.
Port Mirroring Configuration Instance
l Configuration Description
4-10
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
This instance describes how to configure port mirroring on a switch and port 2 can
monitor the packets on port 1, see Figure 4-2.
Figure 4-2 Port Mirroring Configuration Instance
l Configuration Procedure
1. The following example describes how to set port mirroring in ingress direction.
zte(cfg)#set mirror session 1 add source-port 1 ingress
zte(cfg)#set mirror session 1 add dest-port 2 ingress
zte(cfg)#set mirror statistical sample-interval 100 ingress
/*set the port sample-interval of mirror statistic*/
zte(cfg)#set mirror rspan-tag vlan-id 100 priority 7 ingress
/*set VLAN tag added after port mirroring*/
2. The following example describes how to set port mirroring in egress direction.
zte(cfg)#set mirror add source-port 1 egress
zte(cfg)#set mirror add dest-port 2 egress
zte(cfg)#set mirror statistical sample-interval 100 egress
/*set the port sample-interval of mirror statistic*/
zte(cfg)#set mirror rspan-tag vlan-id 100 priority 7 engress
/*set VLAN tag added after port mirroring*/
l Configuration Verification
Check port mirroring configuration
zte(cfg)#show mirror session 1
Session 1:
Ingress mirror information:
---------------------------
Source port : 1
Destination port: 2
Egress mirror information:
---------------------------
Source port : 1
Destination port: 2
zte(cfg)#show mirror rspan
Ingress Rspan VLAN tag: priority 7, vlan 100
Egress Rspan VLAN tag: priority 7, vlan 100
zte(cfg)#show mirror statistical
Ingress statistical mirror: sample-interval 100
Egress statistical mirror: sample-interval 100
4-11
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
4.5 VLAN Configuration
VLAN Overview
The Virtual Local Area Network (VLAN) protocol is a basic protocol of layer-2 switching
equipment, which enables the administrator to divide a physical LAN into multiple VLANs.
Each VLAN has a VLAN ID to identify it uniquely in the entire LAN. Multiple VLANs share
the switching equipment and links of the physical LAN.
Logically, a VLAN is like an independent LAN. All frame flows in the same VALN are
restricted in this VLAN. Cross-VLAN visit can only be implemented through forwarding
on layer-3. In this way, the network performance is improved, and the overall flow in the
physical LAN is effectively lowered.
The VLAN has the following functions:
1. Reduce the broadcast storms of network.
2. Enhance the network security.
3. Provide centralized management and control.
The ZXR10 2900E also supports the tagged-based VLAN. This is a mode defined in IEEE
802.1Q and also is a universal working mode. In this mode, the division of VLAN is based
on the VLAN information about the port (PVID: port VLAN ID) or the information in the
VLAN tag. Also, the ZXR10 2900E supports the division of VLAN according to packet
protocol type, that is, protocol VLAN.
Configuring a VLAN
The VLAN configuration includes the following commands:
Command Function
zte(cfg)#set vlan <vlanlist>{enable | disable}. Enables or disables a VLAN.
Adds a port into VLAN and configures
zte(cfg)#set vlan <vlanlist> add port <portlist>[untag | tag]
the location in VLAN.
zte(cfg)#set vlan <vlanlist> delete port <portlist> Deletes the port from VLAN.
Adds a trunk into VLAN and configures
zte(cfg)#set vlan <vlanlist> add trunk <trunklist>[tag | untag]
the trunk location in VLAN.
zte(cfg)#set vlan <vlanlist> delete trunk <trunklist> Deletes a trunk from VLAN.
zte(cfg)#set port <portlist> vlan-attribute <vlanlist>{tag | untag} Adds ports into VLAN one by one.
Enables or disables the VLAN function
zte(cfg)#set port <portlist> protocol-vlan {enable | disable}
of the protocol.
zte(cfg)#set vlan protocol-mapping session-no <1-8>{ethernet2 | llc |
Sets the VLAN template of the protocol .
snap}<0xHHHH> vlan <1-4094>
4-12
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#create vlan <1-4094> name <name> Creates a VLAN name.
zte(cfg)#clear vlan <vlanlist> name Clears a VLAN name.
Clears the VLAN template configuration
zte(cfg)#clear vlan protocol-mapping session-no <1-8>
of the protocol.
show vlan [<vlanlist>] (all configuration modes) Displays the basic VLAN information.
Displays the VLAN configuration of the
show vlan protocol-mapping (all configuration modes)
protocol.
VLAN Configuration Example One
l Configuration Description
Configure VLAN 100. Add untagged ports 1 and 2 and tagged ports 7 and 8. The
detailed configuration is as follows:
Note:
By default, VLAN1 is enabled, all ports are in VLAN1 and in untag mode.
l Configuration Procedure
zte(cfg)#set vlan 100 add port 1, 2 untag
zte(cfg)#set vlan 100 add port 7, 8 tag
zte(cfg)#set port 1, 2 pvid 100
zte(cfg)#set vlan 100 enable
l Configuration Verification
zte(cfg)#show vlan 100
VlanId : 100 VlanStatus: enabled
VlanName:
VlanMode: Static
Tagged ports : 7-8
Untagged ports: 1-2
Forbidden ports:
VLAN Configuration Example Two
l Configuration Description
As shown in Figure 4-3, switch A is connected to switch B through port 16. Port 1
of switch A and port 2 of switch B are members of VLAN 2. Port 3 of switch A and
port 4 of switch B are members of VLAN 3. The members in the same VLAN can
communicate with each other.
4-13
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-3 VLAN Transparent Transmission Configuration InstanceNetwork
Topology
l Configuration Procedure
1. Configuration of switch A
zte(cfg)#set vlan 2 add port 16 tag
zte(cfg)#set vlan 2 add port 1 untag
zte(cfg)#set vlan 3 add port 16 tag
zte(cfg)#set vlan 3 add port 3 untag
zte(cfg)#set port 1 pvid 2
zte(cfg)#set port 3 pvid 3
zte(cfg)#set vlan 2-3 enable
2. Configuration of switch B
zte(cfg)#set vlan 2 add port 16 tag
zte(cfg)#set vlan 2 add port 2 untag
zte(cfg)#set vlan 3 add port 16 tag
zte(cfg)#set vlan 3 add port 4 untag
zte(cfg)#set port 2 pvid 2
zte(cfg)#set port 4 pvid 3
zte(cfg)#set vlan 2-3 enable
4.6 MAC Table Operation
MAC Table Overview
MAC table operations mainly include MAC addition/deletion, MAC aging time
configuration, MAC filtering function, MAC learning control, MAC learning number limit,
MAC alarm control, MAC fixed function and MAC related information display.
l MAC addition/deletion: users can manually add static and fixed MACs and delete
dynamic, static and fixed MAC table entry through command line.
l MAC table aging time refers to the period from the latest update of dynamic MAC
address in the FDB table to the deletion of this address.
4-14
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
l MAC filtering function: When the switch receives the packets with specified source
address or destination address, it drops them according to source MAC address and
destination MAC address.
l MAC address learning control means MAC learning can provide three types of learn-
ing modes including hardware wire-speed learning, CPU controlled learning and non
learning to satisfy various user requirements. In addition, MAC learning can provide
global, port-based, TRUNK-based and VLAN-based independent switches.
l MAC learning number limit can configure the maximum learning MAC address number
based on global, port, TRUNK and VLAN. When the value is reached, the new MAC
cannot be learnt.
l MAC alarm control can configure the output of the common alarm information of MAC
function, for example, the MAC learning number limit is exceeded and address drift.
l MAC address fixed function can transform the dynamic MAC entry to static or fixed
MAC entry in batch. After transformation, static entry cannot drift. When the device
is rebooted, MAC fixed entry can recover and cannot disappear.
l MAC information display means the current MAC function configuration and state
information can be checked.
Note:
The MAC address of Ethernet NIC is a group of 48–bit number. The 48 bits include two
parts. The previous 24 bits are used to represent the manufacturer indicating Ethernet
NIC. The following 24 bits are a group of sequence numbers designated by manufacturer
and named as OUI (Organizationally Unique Identifier). The lowest bit ( the most left bit in
the structure) is named as private or group bit. If this bit is set to 0, the rest address is a
private address. If 1, it means the remaining address domain identifies the group address
requiring more resolution. If the whole OUI is set to 1, each site of the whole network is
destination. That is the special engagement supported by OUI.
Configuring an MAC Table
The MAC table configuration includes the following commands:
Command Function
Enables or disables the security function of a
zte(cfg)#set port <portlist> security {enable | disable}
port.
Enables or disables the unregistered multicast
zte(cfg)#set port <portlist> multicast-filter {enable | disable}
filter function of a port.
Enables or disables the unregistered multicast
zte(cfg)#set port <trunklist> multicast-filter {enable | disable}
filtering function of a trunk.
zte(cfg)#set mac add static <HH.HH.HH.HH.HH.HH> port <1-28> Adds an MAC static entry based on port and
vlan <1-4094> VLAN.
4-15
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg)#set mac add static <HH.HH.HH.HH.HH.HH> trunk Adds an MAC static entry based on trunk and
<1-15> vlan <1-4094> VLAN.
zte(cfg)#set mac add permanent <HH.HH.HH.HH.HH.HH> port Adds the MAC permanent entry based on port
<1-28> vlan <1-4094> and VLAN.
zte(cfg)#set mac add permanent <HH.HH.HH.HH.HH.HH> trunk Adds the MAC permanent entry based on trunk
<1-15> vlan <1-4094> and VLAN.
zte(cfg)#set mac delete Deletes all MAC address entries.
zte(cfg)#set mac delete mac-address <HH.HH.HH.HH.HH.HH>
Deletes an MAC address entry.
vlan <1-4094>
zte(cfg)#set mac delete {port <1-28>| trunk <1-15>| vlan Deletes all dynamic/static/permanent MAC
<1-4094>}[dynamic | static | permanent] address entries based on port/trunk/VLAN.
zte(cfg)#set mac delete dynamic Deletes all dynamic MAC address entities.
zte(cfg)#set mac delete permanent Deletes all permanent MAC address entities.
zte(cfg)#set mac delete static Deletes all static MAC address entities.
zte(cfg)#set mac aging-time <60-600> Sets device MAC address aging time.
zte(cfg)#set mac filter {source | destination | both}<HH.HH.HH.HH Sets the source MAC address or destination
.HH.HH> vlan <1-4094> MAC address filter function.
zte(cfg)#set mac learning {global | port <1-28>| trunk <1-15>| vlan Sets MAC address learning mode based on
<1-4094>}{enable | disable | mode {automatic | cpu-controlled}} global/port/trunk/VLAN.
zte(cfg)#set mac limit {global | port <1-28>| trunk <1-15>| vlan Sets the MAC address number limit function
<1-4094>} limit-num <0-16384> based on global/port/trunk/VLAN.
zte(cfg)#set mac unknown-filter {global | port <1-28>| trunk Sets the function of filtering unknown source
<1-15>} limit-num <0-16384> packets based on global/port/trunk.
zte(cfg)#set mac to permanent {port <1-28>| trunk <1-15>}{enable Sets the function of batch converting MAC
| disable | max-number <1-128>} addresses as permanent.
Sets the time when MAC addresses converted
zte(cfg)#set mac to permanent auto-save-time <300-7200>
to permanent ones are automatically saved .
zte(cfg)#set mac to static {port <1-28>| trunk <1-15>| vlan Sets the function of converting MAC address to
<1-4094>}{enable | disable} static ones in batch.
zte(cfg)#set mac logging-alarm {station-move | threshold-state}{en Enables or disables the MAC event alarm
able | disable} function.
zte(cfg)#set mac logging-alarm interval <1-900> Sets the MAC event alarm output interval.
show mac (all configuration modes) Displays MAC address entry content.
show mac running-config (all configuration modes) Displays MAC configuration information.
show mac all-type {port <1-28>| trunk <1-15>| vlan <1-4094>} Displays MAC address entry content based on
(all configuration modes) port/trunk/VLAN.
4-16
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Displays various MAC function configurations
show mac {dynamic | learning | limit | permanent | static}[port
and MAC address entries based on
<1-28>| trunk <1-15>| vlan <1-4094>] (all configuration modes)
global/port/trunk/VLAN.
show mac mac-address <HH.HH.HH.HH.HH.HH> (all configuration Displays the MAC address entry content of a
modes) specified MAC address.
show mac unknown-filter [port <1-28>| trunk <1-15>] (all Displays the filter function of the packet with the
configuration modes) unknown source based on global/port/trunk.
show mac aging-time (all configuration modes) Displays device MAC address aging time.
Displays source MAC address or destination
show mac filter (all configuration modes)
MAC address filtering function.
show mac logging-alarm (all configuration modes) Displays MAC event alarm configuration.
zte(cfg)#set mac learning except session <1-100>{clear Sets the function of not learning specified MAC
|mac-address <HH.HH.HH.HH.HH.HH.HH> mac-mask addresses
<HH.HH.HH.HH.HH.HH.HH>[vlan <1-4094>]}
zte(cfg)#set mac learning except {port <portlist>| trunk Debinds ports/trunks and all sessions.
<trunklist>}session unbind
zte(cfg)#set mac learning except {port <portlist>| trunk Sets the binding relation between ports/trunks
<trunklist>}session <1-100>{bind|unbind} and all sessions.
Displays the configuration of sessions for which
show mac learning except session [<1-100>]
specified source MAC learning is not needed.
Displays the binding relation between
show mac learning except {port <portlist>|trunk<trunklist>}
ports/trunks and sessions.
4.7 LACP Configuration
LACP Overview
Link Aggregation Control Protocol (LACP) is a standard protocol defined in IEEE 802.3ad.
Link aggregation means that physical links with the same transmission media and
transmission rate are “bound” together, making them look like one link logically. This
concept is also known as Trunk. It allows the bandwidths of parallel physical links between
the switches or between the switch and the server to increase in multiples simultaneously.
As a result, it becomes an import technology in broadening link bandwidth and creating
link transmission flexibility and redundancy.
An aggregated link is also called trunk. If a port of the trunk is blocked or faulty, the data
packets will be distributed to other ports of this trunk for transmission. If this port recovers,
the data packets will be re-distributed to all the normal ports of this trunk for transmission.
4-17
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
The ZXR10 2900E supports up to 15 aggregation groups. In each aggregation group, the
number of aggregated links does not exceed eight. Aggregated links must have the same
transmission media type and transmission rate.
Configuring LACP
The LACP configuration includes the following commands:
Command Function
zte(cfg)#set trunk <trunklist> pvid <1-4094> Sets the default trunk VID.
zte(cfg)#set lacp {enable | disable} Enables or disables the LACP function.
Adds or deletes a specified port to/from
zte(cfg)#set lacp aggregator <1-15>{add | delete} port <portlist>
an LACP aggregation group.
Sets aggregation mode of an LACP
zte(cfg)#set lacp aggregator <1-15> mode {dynamic | static | mixed }
aggregation group.
Sets the mode used by the port to
zte(cfg)#set lacp port <portlist> mode {active | passive}
participate in the aggregation.
Sets the timeout information of the port
zte(cfg)#set lacp port <portlist> timeout {long | short}
participating in the aggregation.
zte(cfg)#set lacp priority <1-65535> Sets the priority of LACP.
zte(cfg)#set lacp load-balance {port | packet {L2 | L3 | L4}} Sets LACP load balance mode.
Displays the PVIDs of all trunks
show trunk (all configuration modes) and unregistered multicast filtering
configuration.
Displays the trunk PVID and
show trunk [<trunklist>] (all configuration modes) unregistered multicast filtering
configuration.
Displays the VLAN configuration of
show trunk <trunklist> vlan (all configuration modes)
trunk.
Displays the LACP global configuration
show lacp (all configuration modes)
information.
Displays all LACP aggregation groups
show lacp aggregator (all configuration modes)
brief information.
Displays independent LACP
show lacp aggregator <1-15> (all configuration modes) aggregation group detailed status
information.
Displays aggregation status information
show lacp port (all configuration modes)
of all the LACP member ports.
Displays LACP member port
show lacp port [<portlist >] (all configuration modes)
aggregation status information.
4-18
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#clear trunk <trunklist>{ multicast-filter} Clears the flag of the port multicast filter.
LACP Configuration Instance
l Configuration Description
As shown in Figure 4-4, switch A and switch B are connected through the aggregation
port (binding the port 15 and port 16). Port 1 of switch A and port 2 of switch B belong
to VLAN2. Port 3 of switch A and port 4 of switch B belong to VLAN3. Members of
the same VLAN can communicate with each other.
Figure 4-4 LACP Configuration Instance
l Configuration Procedure
1. The detailed configuration of switch A is as follows:
zte(cfg)#set lacp enable
zte(cfg)#set lacp aggregator 3 add port 15-16
zte(cfg)#set lacp aggregator 3 mode dynamic
zte(cfg)#set lacp load-balance packet L2
zte(cfg)#set vlan 2 add trunk 3 tag
zte(cfg)#set vlan 2 add port 1 untag
zte(cfg)#set vlan 3 add trunk 3 tag
zte(cfg)#set vlan 3 add port 3 untag
zte(cfg)#set port 1 pvid 2
zte(cfg)#set port 3 pvid 3
zte(cfg)#set vlan 2-3 enable
2. The detailed configuration of switch B is as follows:
zte(cfg)#set lacp enable
zte(cfg)#set lacp aggregator 3 add port 15-16
zte(cfg)#set lacp aggregator 3 mode dynamic
zte(cfg)#set lacp load-balance packet L2
zte(cfg)#set vlan 2 add trunk 3 tag
zte(cfg)#set vlan 2 add port 2 untag
4-19
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#set vlan 3 add trunk 3 tag
zte(cfg)#set vlan 3 add port 4 untag
zte(cfg)#set port 2 pvid 2
zte(cfg)#set port 4 pvid 3
zte(cfg)#set vlan 2-3 enable
l Configuration Verification
The results of implementing the following command on the two switches are similar.
zte(cfg)#show lacp
Lacp is enabled.
Lacp priority is 32768.
Load-balance is based on L4 hash mode.
PortNum GroupNum GroupMode LacpTime LacpActive
----------- ----------- ----------- ----------- -----------
15 3 Dynamic Long True
16 3 Dynamic Long True
zte(cfg)#show lacp aggregator 3
Group 3
Actor Partner
---------------------------- ----------------------------
Priority : 32768 32768
Mac : 00.d0.d0.fa.29.20 00.d0.d0.fc.88.63
Key : 258 258
Ports : 16, 15 16, 15
The above displayed result proves that the link aggregation is successful. If it is not
successful, the result is shown as follows after executing the show lacp aggregator 3
command.
zte(cfg)#show lacp aggregator 3
% Group 3 is not active!
Generally, the problem of the physical link causes the result. Check the physical link
status.
4.8 IGMP Snooping Configuration
IGMP Snooping Overview
Because the multicast address is not in the source address of the packet, the switch cannot
learn the multicast address. When the switch receives a multicast message, it broadcasts
the message to all the ports in the same VLAN. If no measures are not taken, unwanted
multicast messages may be spread to each node of the network, causing a great waste of
network bandwidth resource.
With the IGMP Snooping function, the IGMP communication between the host and router
is snooped, so that the multicast packets are sent to the ports in the multicast forwarding
4-20
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
table, instead of all ports. This restricts the wide spread of multicast messages in the LAN
switch, reduces the waste of network bandwidth, and improves the utilization rate of the
switch.
Configuring IGMP Snooping
The IGMP Snooping configuration includes the following commands:
Command Function
Enables or disables the IGMP Snooping
zte(cfg)#set igmp snooping {enable | disable}
function.
Adds or deletes the IGMP Snooping
zte(cfg)#set igmp snooping {add | delete} vlan <vlanlist>
function to/from a specified VLAN.
Sets or clears the maximum multicast
zte(cfg)#set igmp snooping {add | delete} maxnum <1-1024>{vlan
group number on the specified
<vlanlist>| port <portlist>}
VLAN/port.
Enables or disables the IGMP ring
zte(cfg)#set igmp snooping monitor-ring {enable | disable}
monitoring function.
zte(cfg)#set igmp snooping vlan <1-4094>{add | delete} group Adds or deletes static multicast group
<A.B.C.D>[port <portlist>| trunk <trunklist>] based on VLAN.
zte(cfg)#set igmp snooping vlan <1-4094>{add | delete} smr {port <portlist>| Adds or deletes routing port or trunk on
trunk <trunklist>} the specified VLAN.
Adds private multicast group and
zte(cfg)#set igmp snooping private-group {<A.B.C.D>| enable | disable} enables or disables private multicast
group function.
Sets multicast member or route
zte(cfg)#set igmp snooping timeout <100-2147483647>{host | router}
time-out.
zte(cfg)#set igmp snooping query-interval <10-2147483647> Sets the snooping interval.
zte(cfg)#set igmp snooping response-interval <10-250> Sets the snooping response interval.
Sets the snooping interval of last
zte(cfg)#set igmp snooping last-member-query <10-250>
member.
Enables or disables the query function
zte(cfg)#set igmp snooping query vlan <vlanlist>{enable | disable}
on the specified VLAN.
Sets the IGMP version of the query
zte(cfg)#set igmp snooping query version {v2 | v3}
packet sent by switch.
zte(cfg)#set igmp snooping fastleave {enable | disable} Enables or disables fast leave function.
zte(cfg)#set igmp snooping v3 {enable | disable} Enables or disables IGMP V3 function.
Sets the version of the query message
zte(cfg)#set igmp snooping proxy version {v2 | auto}
that the switch responses to the router.
4-21
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables switch cross-VLAN
zte(cfg)#set igmp snooping crossvlan {enable | disable}
function.
zte(cfg)#set igmp filter {enable | disable} Enables or disables filtering function.
Adds or deletes the filtering of group in
zte(cfg)#set igmp filter {add | delete} groupip <A.B.C.D.> vlan <vlanlist>
the specified VLAN.
Adds or deletes the filtering of source in
zte(cfg)#set igmp filter {add | delete} sourceip <A.B.C.D.> vlan <vlanlist>
the specified VLAN.
Displays IGMP Snooping global
show igmp snooping (global configuration modes)
configuration information.
show igmp snooping vlan [<1-4094>[host | route]] (global configuration Displays the configuration of IGMP
modes) snooping result.
Displays port maximum multicast group
show igmp snooping port [<portlist>] (global configuration modes) number and current multicast group
number.
show igmp snooping v3 {port <1-28>| trunk <1-15>} (global configuration Displays the v3 multicast snooping
modes) results of the port or trunk.
show igmp filter (global configuration modes) Displays the configuration of IGMP filter.
Displays the specified VLAN multicast
show igmp filter vlan <1-4094> (global configuration modes)
group filtering configuration.
zte(cfg)#set igmp filter {add | delete} grouplist <A.B.C.D.> mask Adds/removes the group list filter
<A.B.C.D.> vlan <vlanlist> to/from a specified VLAN.
Enables or disables the IGMP multicast
zte(cfg)#set igmp snooping multicast-ring {enable | disable}
ring network function.
zte(cfg)#set igmp snooping multicast-ring {add | delete} cascade port Adds or deletes cascaded ports in a
<portlist> multicast ring network.
IGMP Snooping Configuration Instance
l Configuration Description
As shown in Figure 4-5, ports 1, 3, and 5 are connected to the host, port 10 is
connected to the router, add ports 10, 1, 3, and 5 to VLAN200, and users on ports 1,
3, and 5 send multicast join request packets with multicast addresses 230.44.45.167
and 230.44.45.157 respectively. Add multicast filter group address 230.44.45.167 on
VLAN200. The IGMP Snooping function and IGMP Filter function are enabled and
the snooping results are displayed.
4-22
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-5 Network Topology of IGMP Snooping Configuration Instance
l Configuration Procedure
zte(cfg)#set vlan 200 add port 1, 3, 5, 10 untag
zte(cfg)#set port 1, 3, 5, 10 pvid 200
zte(cfg)#set vlan 200 enable
zte(cfg)#set igmp snooping enable
zte(cfg)#set igmp snooping add vlan 200
zte(cfg)#set igmp snooping vlan 200 add smr port 10
zte(cfg)#set igmp filter enable
zte(cfg)#set igmp filter add groupip 230.44.45.167 vlan 200
l Configuration Verification
Display multicast listening and filtering result.
zte(cfg)#show igmp snooping vlan
Maximal group number: 1024
Current group number: 1
Num VlanId Group Last_Report PortMember
---- ------- --------------- --------------- ----------------
1 200 230.44.45.157 194.85.1.3 1,3,5,10
zte(cfg)#show igmp filter
IGMP Filter: enabled
Index Type IpAddress IpMask VlanList
----- -------- ---------------- ---------------- ---------------------
1 Groupip 230.44.45.167 255.255.255.255 200
zte(cfg)#show igmp filter vlan 200
The filter address list of this vlan:
4-23
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Index FilterIpAddress FilterIpMask Vlan Type
----- ---------------- ---------------- ----- --------
1 230.44.45.167 255.255.255.255 200 Groupip
4.9 MLD Snooping Configuration
MLD Snooping Overview
Corresponding to the IGMP protocol, MLD is a multicast management protocol in IPv6
environment. MLD v1/v2 is supported.
It is impossible to use a multicast address as a source address in a packet, so a switch
cannot learn the multicast address. When receiving a multicast message, a switch
broadcasts the message on all ports in the same VLAN. If no measures are not taken,
unwanted multicast messages may be spread to each node of the network, causing a
great waste of network bandwidth resource.
Multicast Listener Discovery (MLD) snooping monitors MLD protocol communication
between a host and a router. In this way, a multicast message is sent to the ports in the
multicast forwarding table instead of all ports. This limits multicast message spread on
LAN switches, reduces network bandwidth waste, and enhances switch usage.
Configuring MLD Snooping
The MLD snooping configuration includes the following commands:
Command Function
Enables or disables the MLD snooping
zte(cfg)#set mld snooping {enable | disable}
function globally.
Adds or deletes an MLD snooping
zte(cfg)#set mld snooping {add | delete} vlan <vlanlist>
VLAN.
Sets the maximum number of multicast
zte(cfg)#set mld snooping add maxnum <1-256> vlan <vlanlist>
groups of a specific VLAN.
zte(cfg)#set mld snooping vlan <1-4094> add group <ipv6-address> port Adds a static group to a specific VLAN
<portlist> and adds a port to the static group.
zte(cfg)#set mld snooping vlan <1-4094> delete group <ipv6-address>[port Clears static groups in a specific VLAN
<portlist>] and clears the ports in the static groups.
zte(cfg)#set mld snooping vlan <1-4094>{add | delete} mrouter port Adds or clears a routing ports in a
<port-id> specific VLAN.
Sets the time-out period between the
zte(cfg)#set mld snooping { host-time-out | mrouter-time-out }<30-65535>
router port and the host port.
Sets the interval for sending query
zte(cfg)#set mld snooping query-interval <30-65535>
packets.
4-24
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Sets the interval for sending report
zte(cfg)#set mld snooping query-response-interval <1000-25000>
packets.
Sets the time to waiting for a query
zte(cfg)#set mld snooping last-member-query <1-25>
response when the last member leaves.
Enables or disables the query function
zte(cfg)#set mld snooping query vlan <vlanlist>{enable | disable}
in a specific VLAN.
zte(cfg)#set mld snooping query version {v1 | v2} Sets the MLD version of query packets.
zte(cfg)#set mld snooping query {enable | disable} Enables or disables the query function.
Enables or disables the fast leave
zte(cfg)#set mld snooping fastleave {enable | disable}
function.
zte(cfg)#set mld snooping robustness <1-7> Sets the MLD robustness value.
Displays global MLD snooping
show mld snooping (all configuration modes)
configuration information.
show mld snooping vlan <1-4094>[group <ipv6-address>| port-info |
Displays the MLD snooping result.
group-source-filter | host-source-filter ] (all configuration modes)
show mld snooping mr-port-info (all configuration modes) Displays MLD router port information.
MLD Snooping Configuration Instance
l Configuration Description
As shown in Figure 4-6, Ports 1, Port 3 and Port 5 are connected to hosts, Port 10 is
connected to a router, ports 10, 1, 3 and 5 are in VLAN 200, users connected to Ports
1, 3 and 5 send multicast join requests to join the groups ff1e::22 and ff1e::11. Enable
the MLD snooping function on the switch and display the snooping result.
Figure 4-6 MLD Snooping Configuration Instance
4-25
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l Configuration Procedure
zte(cfg)#set vlan 200 add port 1, 3, 5, 10 untag
zte(cfg)#set port 1, 3, 5, 10 pvid 200
zte(cfg)#set vlan 200 enable
zte(cfg)#set mld snooping enable
zte(cfg)#set mld snooping add vlan 200
zte(cfg)#set mld snooping vlan 200 add smr port 10
l Configuration Verification
Display the snooping result:
zte(cfg)#show mld snooping vlan 200
MLD Snooping : enable
Querier : disable
Working Mode : proxy
Max Group Number : 256
Total Group Number : 2
Exist Host Group Number : 2
Index Vlan Group ID Prejoin LiveTime Ports
----- ---- -------------- ------- ---------- --------
1 200 ff1e::11 0 0:00:00:14 D:1,3, 5
2 200 ff1e::22 0 0:00:00:09 D:1,3,
4.10 IPTV Configuration
IPTV Overview
Internet Protocol television (IPTV) is also called Interactive Network TV. IPTV is a method
of distributing television content over IP that enables a more customized and interactive
user experience. IPTV could allow people who were separated geographically to watch a
movie together, while chatting and exchanging files simultaneously. IPTV uses a two-way
broadcast signal sent through the provider's backbone network and servers, allowing
viewers to select content on demand, and take advantage of other interactive TV options.
IPTV can be used through PC or “IP machine box + TV”.
Configuring IPTV
The IPTV configuration mainly includes the following contents:
l Configure channel attribute
l Configure package attribute
l Configure preview related attribute
l Configure CDR related attribute
l Configure port related attribute
The IPTV configuration includes the following commands:
4-26
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg-nas)#iptv control {enable | disable} Enables or disables the IPTV function.
Adds one channel (multicast group)
zte(cfg-nas)#iptv channel mvlan <1-4094> groupip <A.B.C.D>[name
to the specified VLAN and names the
<channel-name>[id <0-1031>]]
channel and allocates ID.
Adds channel (multicast group) to the
zte(cfg-nas)#iptv channel mvlan <1-4094> groupip <A.B.C.D> count
specified VLAN in batch and names
<1-1032>[prename <prename>]
channels in batch.
zte(cfg-nas)#iptv channel name <channel-name> rename <new-name> Modifies channel name.
zte(cfg-nas)#iptv channel {name <channel-name>| id-list < channel-list>} Enables or disables channel log
cdr {enable | disable} function.
zte(cfg-nas)#iptv channel {name <channel-name>| id-list Specifies the preview configuration file
<channel-list>}{viewfile-name <viewfile-name>| viewfile-id <0-1023>} of the channel.
Sets SMS (service management
zte(cfg-nas)#iptv sms-server <A.B.C.D>
system) server IP address.
zte(cfg-nas)#iptv sms-server-port <1025-65535> Sets SMS server TCP port.
Enables or disables CDR log function
zte(cfg-nas)#iptv cdr {enable | disable}
at global.
Manually triggers CDR log report in one
zte(cfg-nas)#iptv cdr report
time.
Sets the interval for creating CDR when
zte(cfg-nas)#iptv cdr create-period <1-65535>
user watches programs for long time.
Enables or disables CDR function when
zte(cfg-nas)#iptv cdr deny-right {enable | disable}
the access authorization is deny.
Enables or disables CDR function when
zte(cfg-nas)#iptv cdr prv-right {enable | disable}
the access authorization is preview.
Sets the number of CDRs for reporting
zte(cfg-nas)#iptv cdr report-threshold <1-32>
every time.
zte(cfg-nas)#iptv cdr report-interval <1-65535> Sets the time interval for CDR report.
zte(cfg-nas)#iptv cdr max-records <100-5000> Sets CDR maximum record items.
zte(cfg-nas)#iptv cdr warning-threshold <1-100> Sets CDR buffer alarm threshold.
zte(cfg-nas)#iptv package name <package-name>[id <package-id>] Creates multicast package.
Adds channels to package and
zte(cfg-nas)#iptv package name <package-name> channel {id-list
configures the authority of the channel
<channel-list>| name <channel-name>}{deny | order | preview}
in the package.
zte(cfg-nas)#iptv prv {enable | disable} Enables or disables preview function.
zte(cfg-nas)#iptv prv reset This resets the preview function.
4-27
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Automatically resets the preview
zte(cfg-nas)#iptv prv autoreset-time <HH:MM:SS>
function.
Sets recognition time. The short time
zte(cfg-nas)#iptv prv recognition-time <1-65534>
preview is not counted.
Enables or disables IPTV preview
zte(cfg-nas)#iptv prv overcount-cdr {enable | disable}
overcount-cdr function.
Creates IPTV preview configuration
zte(cfg-nas)#iptv view-profile name < viewfile-name>[id <1-1023>]
files.
zte(cfg-nas)#iptv view-profile name <viewfile-name>{count | duration | Creates IPTV preview configuration
blackout}<1-65535> files.
zte(cfg-nas)#iptv cac-rule {enable | disable} Enables or disables the CAC control.
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] service {start | remove |
Sets user service state.
pause | resume}
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] control-mode {package |
Sets user multicast control mode.
channel}
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] package {name
Allocates packages for user.
<package-name>| id-list <package-list>}
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] channel {name Allocates the visit authority of the
<channel-name>| id-list <channel-list>}{deny | order | preview | query} channel for user.
Enables or disables user CDR log
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] cdr {enable | disable}
record function.
Enables or disables the management
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] mac-base {enable | disable}
mode based on MAC address.
zte(cfg-nas)#iptv port <portlist>{add|delete} mvlan <1-4094> uvlan
Adds or deletes a duplicate rule.
<1-4094>
zte(cfg-nas)#clear iptv channel {name <channel-name>| id-list
Deletes a channel.
<channel-list>| all}
zte(cfg-nas)#clear iptv package {name <package-name>| id-list <
Deletes a package.
package-idlist >| all}
zte(cfg-nas)#clear iptv view-profile{name <viewfile-name>| id-list
Deletes a preview configuration file.
<viewfile-lis>| all}
zte(cfg-nas)#clear iptv port <portlist>[vlan <1-4094>] package {name Deletes the package allocated for
<package-name>| id-llist <package-idlist>} users.
zte(cfg-nas)#clear iptv client [index <0-255>| mac <HH.HH.HH.HH.HH.H
Deletes an IPTV user.
H>| port <portlist>[vlan <1-4094>]]
show iptv control (all configuration modes) Displays IPTV global configuration.
4-28
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Displays channel information (all
show iptv channel [name <channel-name>| id <channel-id>] (all
channels or some channel detailed
configuration modes)
information).
Without parameters, displays the
show iptv package [name<package-name>| id <0-127>] (all configuration
package names. With parameters, this
modes)
displays all channel lists in the package.
Displays IPTV preview global
show iptv prv (all configuration modes)
configuration information.
show iptv view-profile [name <viewfile-name>| id <0-1023>](all Displays preview configuration file
configuration modes) information.
Displays global CDR configuration
show iptv cdr (all configuration modes)
information.
show iptv client [{channel <0-1031>| index <0-255>| mac
<HH.HH.HH.HH.HH.HH>| port <portid>| vlan <1-4094>}] (all configuration Displays IPTV user information.
modes)
show iptv rule [ port <portid>][vlan <1-4094>][channel | package] (all
Displays IPTV rule information.
configuration modes)
Displays duplicate configuration
show iptv duplicate (all configuration modes)
information.
zte(cfg-nas)#clear iptv channel-group {name <channel-group-name>| Deletes a channel group.
id-list <channel-group-list>| all}
zte(cfg-nas)#iptv channel-group mvlan <1-4094> groupiplist Adds a channel group to a specified
<A.B.C.D>{<A.B.C.D>| mask <A.B.C.D>}}[name <channel-group-name>[id VLAN, names the channel group, and
<0-255>]] allocates an ID to each channel.
zte(cfg-nas)#iptv channel-group name <channel-group-name> rename Modify the channel group name.
<new-name>
zte(cfg-nas)#iptv channel-group {name <channel-group-name>| id-list < Enable/disable the channel group log
channel-group-list>} cdr {enable | disable} function.
zte(cfg-nas)#iptv channel-group {name <channel-group-name>| id-list Specifies the preview configuration file
<channel-group-list>}{viewfile-name <viewfile-name>| viewfile-id for the channel group.
<0-1023>}
zte(cfg-nas)#iptv port <portlist>[vlan <1-4094>] channel-group {name Allocates an access permission to the
<channel-group-name>| id-list <channel-group-list>}{deny | order | preview channel group for users.
| query}
show iptv channel-group [name <channe-groupl-name>| id Displays channel group information
<channel-group-id>] (all configuration modes) (details of one or all channel groups).
4-29
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
IPTV Configuration Example One
l Configuration Description
As shown in Figure 4-7, port 1 connects to the user and it is the order user of channel
225.1.1.1. The user vlan is 100. The multicast vlan is 4000. Router sends data stream
of multicast group 225.1.1.1. PC sends request for entering into channel 225.1.1.1.
Figure 4-7 IPTV Configuration Instance 1
l Configuration Procedure
1. Configure VLAN
zte(cfg)#set vlan 100 add port 1
zte(cfg)#set vlan 4000 add port 1, 4
zte(cfg)#set vlan 100, 4000 enable
zte(cfg)#set port 1 pvid 100
zte(cfg)#set port 4 pvid 4000
/*IGMP Snooping*/
zte(cfg)#set igmp snooping enable
zte(cfg)#set igmp snooping add vlan 100, 4000
zte(cfg)#set igmp snooping fastleave enable
2. Configure IPTV
zte(cfg)#config nas
zte(cfg-nas)#iptv control enable
zte(cfg-nas)#iptv cac-rule enable
3. Configure a rule on the port
zte(cfg-nas)#iptv channel mvlan 4000 group 225.1.1.1
name CCTV1 id 1
zte(cfg-nas)#iptv port 1 service start
zte(cfg-nas)#iptv port 1 control-mode channel
zte(cfg-nas)#iptv port 1 channel id-list 1 order
zte(cfg-nas)#iptv port 1 add mvlan 4000 uvlan 100
l Configuration Verification
Check configuration
zte(cfg-nas)#show iptv rule
MaxRuleNum:64
CurRuleNum:1
HisRuleNum:1
Id Port Vlan Mbase Mode Service Cdr Order Preview Query PkgNum
-- ---- ---- ----- ------- ------- -------- ----- ------- ----- ------
1 1 false channel in disabled 1 0 0 0
4-30
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
/*view the user online state when the user is online*/
zte(cfg-nas)#show igmp snooping vlan
Maximal group number: 1024
Current group number: 1
Num VlanId Group Last_Report PortMember
---- ------- --------------- --------------- ----------------
1 4000 225.1.1.1 192.85.1.3 1
zte(cfg-nas)#show iptv client index 0
Index :0
Rule :1 Vlan :100
Port :1 ChNum :1
Mac :00.10.94.00.00.01 Ip :192.85.1.3
Channel UserType MultiAddress ElapsedTime
------- ---------- ---------------- --------------
1 order 225.1.1.1 0:0:1:7
IPTV Configuration Example Two
l Configuration Description
As shown in Figure 4-8, port 1 connects with the user and it is the preview user of
channel 225.1.1.1. The maximum preview time is 20 seconds, the interval is at least
10 seconds and the maximum preview time is 2. The user vlan is 100. The multicast
vlan is 4000. Router sends data stream of multicast group 225.1.1.1. PC sends
request for entering into channel 225.1.1.1.
Figure 4-8 IPTV Configuration Instance 2
l Configuration Procedure
1. Configure VLAN
zte(cfg)#set vlan 100 add port 1
zte(cfg)#set vlan 4000 add port 1, 4
zte(cfg)#set vlan 100, 4000 enable
zte(cfg)#set port 1 pvid 100
zte(cfg)#set port 4 pvid 4000
/*IGMP Snooping*/
zte(cfg)#set igmp snooping enable
zte(cfg)#set igmp snooping add vlan 100, 4000
zte(cfg)#set igmp snooping fastleave enable
4-31
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
2. Configure IPTV
zte(cfg)#config nas
zte(cfg-nas)#iptv control enable
zte(cfg-nas)#iptv cac-rule enable
zte(cfg-nas)#iptv prv enable
3. Configure a rule on the port
zte(cfg-nas)#iptv channel mvlan 4000 group 225.1.1.1
name CCTV1 id 1
zte(cfg-nas)#iptv port 1 service start
zte(cfg-nas)#iptv port 1 control-mode channel
zte(cfg-nas)#iptv port 1 channel id 1 preview
4. Configure the preview template
zte(cfg-nas)#iptv view-profile name VPF1.PRF
zte(cfg-nas)#iptv view-profile name VPF1.PRF count 2
zte(cfg-nas)#iptv view-profile name VPF1.PRF blackout 10
zte(cfg-nas)#iptv view-profile name VPF1.PRF duration 20
zte(cfg-nas)#iptv channel id 1 viewfile-name VPF1.PRF
l Configuration Verification
Check configuration
/*check the configuration of preview template*/
zte(cfg-nas)#show iptv view-profile name VPF1
ViewProfile Id :1
MaxPrvCount :2
MaxPrvDuration :20
BlackoutInterval :10
/*view the user online state when the user is online*/
zte(cfg-nas)#show iptv client index 0
Index :0
Rule :1 Vlan :100
Port :1 ChNum :1
Mac :00.10.94.00.00.01 Ip :192.85.1.3
Channel UserType MultiAddress ElapsedTime
------- ---------- ---------------- --------------
1 preview 225.1.1.1 0:0:0:16
4.11 STP Configuration
STP Overview
Spanning Tree Protocol (STP) is applicable to a loop network. It blocks some redundant
paths with certain algorithms so that the loop network is pruned into a tree network without
any loop, thus avoiding the hyperplasia and infinite loop of packets in the loop network.
4-32
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Rapid Spanning Tree Protocol (RSTP) is on the basis of common STP, added with the
mechanism that the port state can be rapidly changed from Blocking to Forwarding, which
increases the topology convergence speed.
Multiple Spanning Tree Protocol (MSTP) is on the basis of RSTP and STP, added with
the forwarding processing of frames with VLAN ID. The whole network topology structure
can be planned into a Common and Internal Spanning Tree (CIST), which is divided into
Common Spanning Tree (CST) and Internal Spanning Tree (IST).
Many devices enabling MSTP construct MST area in switching network. When the devices
satisfy the following conditions, they can be considered to exist in a MST area. A switching
network can cover many MST areas. User can divide the switches into a MST area by
using MSTP commands.
l Same area name.
l Same reversion level.
l Same mapping relationship between VLAN and instance.
l Switches should be connected directly.
There are many spanning trees can be configured in each MSTP area, and they are
independent each other. Each spanning tree is Internal Spanning Tree (IST), and it can
be called as Multiple Spanning Tree Instance (MSTI). Common Spanning Tree connect
all MST areas in switching network. A MST area can be considered as a switch, CST is
a spanning tree which is generated by STP and RSTP protocol calculation. All ISTs and
CSTs are called as Common and Internal Spanning Tree (CIST). CIST is a single spanning
tree to connect all switches.
In this MSTP topology structure, an IST can serve as a single bridge (switch). In this way,
CTS can serve as an RSTP for the interaction of configuration information (BPDU). Multiple
instances can be created in an IST area and these instances are valid only in this area.
An instance is equivalent to an RSTP, except that the instance needs to perform BPDU
interaction with bridges outside this area.
MSTP topological structure is shown as Figure 4-9.
4-33
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-9 MSTP Topological Structure
Spanning Tree Protocol (STP) can calculate according to the protocol. Ports are divided
into different parts:
l Master: The port type is introduced in MSTP protocol. When the multiple different
areas exist, the main port is the minimal path cost port point to the root.
l Root: The port that has the minimal cost to root bridge and takes charge in forwarding
data to root node. When multiple ports have the same cost to the root bridge, then
the port with the lowest port priority becomes to the root port.
l Designated: The port transmits data to switch downward, and sends STP protocol
message to maintain the state of STP.
l Backup: The port receives the STP message, which proves that there exits a loop
route to the port itself.
l Alternate: The port receives excess STP protocol message from other equipment.
However, when the original link abnormally lost, the port under this state can transfer
to transmitting state and maintain the network instead of the port lapsed.
l Edged: The port is used to connect the terminal equipment, such as PC. The port
does not participate in calculation before STP is stable, and the state can be switched
fast.
According to port role, the state after the calculation being steady is shown in Table 4-1.
Table 4-1 Port Role and Port State
Port role Port state
Master Forward
Root Forward
Designated Forward
4-34
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Port role Port state
Backup Discard
Alternate Discard
Edged Forward
BPDU protect function is for the protection of margin port. The margin port will not receive
the protocol message. If there exists vicious protocol attack or Linux virtual bridge,
receiving unlawful protocol message will bring to net shocking or topology changing
abnormally. The port will be closed after using the protection. After a while, to check the
net is normal or not. If it is normal, it will recover to original state.
Root protection is function is for the protection of root switch. In the network that needs to
appoint switch as root switch, if there exists vicious protocol attack or Linux virtual bridge,
it will bring the change to the root and net abnormal. After using the root protection of
the port, if the port receives the protocol information prior to root switch, it will transfer the
port to blocking state. This port no longer transmits message, and discards the received
protocol message to protect the status of the root switch.
Loop protection function is for the protection of loop net topology. In the network where
ring exists, redundant topology will be in the state of backup, and in the state of blocking
after the port is steady. If there is no need to transfer to transmission state, it is possible
to set port to loop protect. Once the port wants to transform, it will inspire loop protection
and set the port to blocking state.
When configuring one port, only one of the three protections can be configured: BPDU
protection, root protection and loop protection.
Configuring STP
In the default configuration, the MSTP only has the instance with ins_id as 0. This instance
always exists and users cannot manually delete it. This instance is mapped with VLANs 1
to 4094.
The STP configuration includes the following commands:
Command Function
zte(cfg)#set stp {enable | disable} Enables or disables STP.
Sets the forced STP type to
zte(cfg)#set stp forceversion {mstp | rstp | stp}
MSTP/RSTP/STP.
zte(cfg)#set stp port <portlist>{enable | disable} Enables or disables port stp function.
zte(cfg)#set stp port <portlist> linktype {point-point | shared} Sets port connection type.
zte(cfg)#set stp port <portlist> packettype {IEEE | CISCO | HUAWEI |
Sets instance port packet type.
HAMMER | extend }
Checks the current STP protocol type
zte(cfg)#set stp port <portlist> pcheck
and selects the best protocol.
4-35
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables port BPDU packet
zte(cfg)#set stp port <portlist> bpdu-guard {enable | disable}
protection function.
Sets BPDU protection port link-down
zte(cfg)#set stp bpdu-interval <10-65535>
interval.
zte(cfg)#set stp trunk <trunklist>{enable | disable} Enables trunk/disables STP function.
zte(cfg)#set stp trunk <trunklist> linktype {point-point | shared} Sets trunk connection type.
zte(cfg)#set stp trunk <trunklist> packettype {IEEE | CISCO | HUAWEI | Sets trunk receiving and sending packet
HAMMER | extend } type.
zte(cfg)#set stp edge-port {add | delete} port <portlist> Adds/deletes STP edge port.
zte(cfg)#set stp {hmd5-digest | hmd5-key}{CISCO | HUAWEI}<0x00..0-0xf Sets hmd5 parameter when the device
f..f> is connected with CISCO or HUAWEI.
zte(cfg)#set stp hellotime <1-10> Sets STP notification interval.
zte(cfg)#set stp forwarddelay <4-30> Sets STP forwarding delay time.
zte(cfg)#set stp agemax <6-40> Sets STP aging time
Sets the maximum number of hop
zte(cfg)#set stp hopmax <1-40>
between any two terminals of MST.
zte(cfg)#set stp name <name> Sets the name of MSTP domain.
zte(cfg)#set stp revision <0-65535> Sets the revision level of MSTP.
Adds or deletes VLAN to/from MSTP
zte(cfg)#set stp instance <0-63>{add | delete} vlan <vlanlist>
instance.
zte(cfg)#set stp instance <0-63>{port <1-28>| trunk < trunklist >} priority Sets the priority of port/trunk in the
<0-240> instance.
zte(cfg)#set stp instance <0-63>{port <1-28>| trunk <trunklist>} cost Sets the path cost of port/trunk in the
<1-200000000> instance.
zte(cfg)#set stp instance <0-63>{port <1-28>| trunk <trunklist>} root-guard Enables or disables the root protection
{enable | disable} of port/trunk in the instance.
zte(cfg)#set stp instance <0-63>{port <1-28>| trunk <trunklist>} loop-guard Enables or disables the loop protection
{enable | disable} of port/trunk in the instance.
Sets the priority of the bridge in the
zte(cfg)#set stp instance <0-63> priority <0-61440> instance, which is used for root bridge
selection.
zte(cfg)#clear stp instance <0-63> Deletes the instance.
Sets the path cost of port/trunk in the
zte(cfg)#clear stp instance <0-63>{port <1-28>| trunk <1-15>} cost
instance as default value.
zte(cfg)#clear stp name Deletes MSTP domain name.
4-36
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Displays STP global configuration
show stp (all configuration modes)
information.
Displays the state information of the
show stp instance [<0-63>] (all configuration modes)
instance.
Displays the STP port configuration
show stp port [<portlist>] (all configuration modes)
information.
Displays STP trunk configuration
show stp trunk <trunklist> (all configuration modes)
information.
STP Configuration Instance
l Configuration Description
As shown in Figure 4-10, configure the STP function of switch 1 and switch 2 , take
switch 1 as the root bridge and block a redundant port in the loop. It realizes loop
protection and link backup between switches.
Figure 4-10 STP Configuration Instance
l Configuration Procedure
zte(cfg)#set stp enable
/*enable the stp protocol of switch1 and switch2*/
zte(cfg)#set stp forceversion stp
/*set STP forceversion as stp*/
l Configuration Verification
1. Check the STP state of switch 1 in the system view.
zte(cfg)#show stp instance
Spanning tree enabled protocol stp
RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15
Reg RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
RemainHops : 20
BridgeID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role Bound GuardStatus
--------- ------ ------- ------- ---------- ----- -----------
4-37
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
1 128.1 200000 Forward Designated SSTP None
2 128.2 200000 Forward Designated SSTP None
2. Check the STP state of switch 2 in the system view.
zte(cfg)#show stp instance
Spanning tree enabled protocol stp
RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s):15
Reg RootID:
Priority : 32768 Address : 00.d0.d0.29.52.06
RemainHops : 20
BridgeID:
Priority : 32768 Address : 00.d0.d0.29.52.06
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role Bound GuardStatus
--------- ------ ------- ------- ---------- ----- -----------
1 128.1 200000 Forward Root SSTP None
2 128.2 200000 Discard Alternate SSTP None
RSTP Configuration Instance
l Configuration Description
As shown in Figure 4-11, configure the RSTP function of switch 1 and switch 2 , take
switch 1 as the root bridge and block a redundant port in the loop. It realizes loop
protection and link backup between switches.
Figure 4-11 RSTP Configuration Instance
l Configuration Procedure
zte(cfg)#set stp enable
/*enable STP protocol of switch1 and switch2*/
zte(cfg)#set stp forceversion rstp
/*set forceversion of stp as rstp*/
l Configuration Verification
1. Check the STP state of switch 1 in the system view.
zte(cfg)#show stp instance
Spanning tree enabled protocol rstp
RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
4-38
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
ForwardDelay(s): 15
Reg RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
RemainHops : 20
BridgeID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role Bound GuardStatus
--------- ------ -------- ------- ---------- ----- -----------
1 128.1 200000 Forward Designated RSTP None
2 128.2 200000 Forward Designated RSTP None
2. Check the STP state of switch 2 in the system view.
zte(cfg)#show stp instance
Spanning tree enabled protocol rstp
RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s):15
Reg RootID:
Priority : 32768 Address : 00.d0.d0.29.52.06
RemainHops : 20
BridgeID:
Priority : 32768 Address : 00.d0.d0.29.52.06
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role Bound GuardStatus
--------- ------ --------- ------- ---------- ----- -----------
1 128.1 200000 Forward Root RSTP None
2 128.2 200000 Discard Alternate RSTP None
MSTP Configuration Instance
l Configuration Description
As shown in Figure 4-12, configure the MSTP of switch1 and switch2 (They are in the
same MST area) to realize link backup and block the loop in the net. The configuration
is as follows: establish mapping between instance 1 and service VLAN10-20; set
Name as zte, Revision as 10. Take switch1 as the root bridge in instance 1.
Figure 4-12 MSTP Configuration Instance
l Configuration Procedure
4-39
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#set stp enable
/*enable the stp protocol of switch1 and switch2*/
zte(cfg)#set stp forceversion mstp
/*set the STP forceversion as mstp*/
zte (cfg)#set stp name zte
/*set switch1 and switch2 in the same area*/
zte(cfg)#set stp revision 10
zte(cfg)#set stp instance 1 add vlan 10-20
l Configuration Verification
1. Check the STP state of switch 1 and switch 2 in the system view.
zte(cfg)#show stp
The spanning_tree protocol is enabled!
The STP ForceVersion is MSTP !
Revision: 10 Name: zte
Cisco key: 0x13ac06a62e47fd51f95d2ba243cd0346
Cisco digest: 0x00000000000000000000000000000000
Huawei key: 0x13ac06a62e47fd51f95d2ba243cd0346
Huawei digest: 0x00000000000000000000000000000000
Instance VlanMap
-------- -------------------
0 1-9,21-4094
1 10-20
2. Check the STP state of switch 1 in the system view.
zte(cfg)#show stp instance
MST00
Spanning tree enabled protocol mstp
RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15
Reg RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
RemainHops : 20
BridgeID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role Bound GuardStatus
--------- ------ ------- ------- ---------- ----- -----------
1 128.1 200000 Forward Designated MSTP None
2 128.2 200000 Forward Designated MSTP None
MST01
Spanning tree enabled protocol mstp
RootID:
Priority : 32769 Address : 00.d0.d0.02.00.54
4-40
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
HelloTime(s) : 2 MaxAge(s) : 20
ForwardDelay(s): 15 RemainHops : 20
BridgeID:
Priority : 32769 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s) : 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role GuardStatus
--------- ------ ------- ------- ---------- -----------
1 128.1 200000 Forward Designated None
2 128.2 200000 Forward Designated None
3. Check the STP state of switch 2 in the system view.
zte(cfg)#show stp instance
MST00
Spanning tree enabled protocol mstp
RootID:
Priority : 32768 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s):15
Reg RootID:
Priority : 32768 Address : 00.d0.d0.29.52.06
RemainHops : 20
BridgeID:
Priority : 32768 Address : 00.d0.d0.29.52.06
HelloTime(s) : 2 MaxAge(s): 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role Bound GuardStatus
--------- ------ ------- ------- ---------- ----- ---------
1 128.1 200000 Forward Root MSTP None
2 128.2 200000 Discard Alternate MSTP None
ST01
Spanning tree enabled protocol mstp
RootID:
Priority : 32769 Address : 00.d0.d0.02.00.54
HelloTime(s) : 2 MaxAge(s) : 20
ForwardDelay(s):15 RemainHops : 19
BridgeID:
Priority : 32769 Address : 00.d0.d0.29.52.06
HelloTime(s) : 2 MaxAge(s) : 20
ForwardDelay(s): 15 MaxHops : 20
Interface PortId Cost Status Role GuardStatus
--------- ------ ------- ------- ---------- ------------
1 128.1 200000 Forward Root None
2 128.2 200000 Discard Alternate None
4-41
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
4.12 ACL Configuration
ACL Overview
An Access Control List (ACL) is a sequential collection of permit and deny conditions that
apply to packets. When a packet is received on an interface, the switch compares the
fields in the packet against any applied ACL’s to verify that the packet has the required
permissions to be forwarded, based on the criteria specified in the access lists. It tests
packets against the conditions in an access list one by one. The first match determines
whether the switch accepts or rejects the packets because the switch stops testing
conditions after the first match. The order of conditions in the list is critical. If no conditions
match, the switch rejects the packets. If there are no restrictions, the switch forwards the
packet. otherwise, the switch drops the packet.
The ZXR10 2900E supports the following functions.
l The ZXR10 2900E provides two binding types including physical port and VLAN port.
l ACL rule can be added, deleted, sorted.
1. Rule can be added to a configured ACL. Regular ID number range is 1-500 .
2. Configured ACL can be deleted regularly. If the specified ACL instance number
or rule number hasn’t been configured, a false message will return.
3. Many rules of an ACL can be sorted and only need to specify the place where rule
number need to be moved.
l An ACL can become valid according to configured time range. After configuring
absolute or relative time range on the switch, time range can be applied to the rule of
ACL. This causes the rule to be valid according to the time range specification.
l The ZXR10 2900E provides the following five types of ACLs:
1. Basic ACL: Only match source IP address.
2. Extended ACL: Match source IP address, destination IP address, IP protocol type,
TCP source port number, TCP destination port number, UDP source port number,
UDP destination port number, ICMP type, ICMP Code and DiffServ Code Point
(DSCP).
3. L2 ingress ACL: Match source MAC address, destination MAC address, source
VLAN ID and 802. 1p priority value, Ethernet network type and DSAP/SSAP.
4. Hybrid ingress ACL: Match Source IPv4/IPv6 address, destination IPv4/IPv6
address, IP protocol type, TCP source port number, TCP destination port number,
UDP source port number, UDP destination port number, DiffServ Code Point
(DSCP), source MAC address, destination MAC address, source VLAN ID and
802. 1p priority value.
5. Global ACL: Match Source IP address, destination IP address, IP protocol type,
TCP source port number, TCP destination port number, UDP source port number,
UDP destination port number, DiffServ Code Point (DSCP), source MAC address,
destination MAC address, source VLAN ID and 802. 1p priority value.
6. Basic egress ACL: Only match source IP address.
7. Extended egress ACL: Match source IP address, destination IP address, IP
protocol type, TCP source port number, TCP destination port number, UDP
4-42
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
source port number, UDP destination port number, ICMP type, ICMP Code and
DiffServ Code Point (DSCP).
8. L2 egress ACL: Match destination MAC address, source VLAN ID and 802. 1p
priority value, Ethernet network type and DSAP/SSAP.
9. Hybrid egress ACL: Match Source IPv4/IPv6 address, destination IPv4/IPv6
address, IP protocol type, TCP source port number, TCP destination port number,
UDP source port number, UDP destination port number, DiffServ Code Point
(DSCP), source MAC address, destination MAC address, source VLAN ID and
802. 1p priority value.
l Each ACL has an access list number to identify. The access list number is a number.
The access list number ranges of different types of ACL are shown below:
1. Basic ingress ACL: 1~99
2. Extended ingress ACL: 100~199
3. L2 ingress ACL: 200~299
4. Hybrid ingress ACL: 300~399, support IPv6
5. Basic egress ACL: 400~499
6. Extended egress ACL: 500~599
7. L2 egress ACL: 600-699
8. Hybrid egress ACL:700~799, supports IPv6
9. Global ACL: 800
l Each ACL has at most 500 rules and the range is 1-500.
Configuring ACL
The ACL configuration includes the following commands:
Command Function
zte(cfg)#set port <portlist> acl mode {port | vlan} Sets port ACL binding mode.
zte(cfg)#set port <portlist> acl <1-799>{enable | disable} Binds ACL instance to the port.
zte(cfg)#set vlan <vlanlist> acl <1-399>{enable | disable} Binds ACL instance to the VLAN.
Executes an ACL action in a specific
zte(cfg)#set acl <1-799> rule <1-500> time-range <word>{enable|disable}
time range.
zte(cfg)#create acl <1-800> name <name> Creates an ACL name.
zte(cfg)#clear acl-name <1-800> Clears an ACL name.
zte(cfg)#show port <portlist> acl-mode Displays port ACL binding mode.
Creates and configures a basic ingress
zte(cfg)#config ingress-acl basic number <1-99>
ACL instance.
zte(basic-acl-group)#rule <1-500>{permit | deny}{<source-ipaddr><sip-ma
Sets a basic ingress ACL rule.
sk>| any}[fragment]
zte(cfg)#clear ingress-acl basic number <1-99> Clears a basic ingress ACL instance.
Creates and configures an extended
zte(cfg)#config ingress-acl extend number <100-199>
port ACL instance.
4-43
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(extend-acl-group)#rule <1-500>{permit | deny}<ip-protocol>{<sour Sets the rule that an extended ingress
ce-ipaddr><sip-mask>| any}{<destination-ipaddr><dip-mask>| any}[dscp ACL matches IPv4–specified protocol
<0-63>][fragment] field packet.
zte(extend-acl-group)#rule <1-500>{permit | deny} icmp
Sets the rule that an extended ingress
{<source-ipaddr><sip-mask>| any}{<destination-ipaddr><dip-mask>|
ACL is used to match ICMP packet.
any}[icmp-type <0-254><icmp-code>][dscp <0-63>][fragment]
zte(extend-acl-group)#rule <1-500>{permit | deny} ip {<source-ipaddr><sip- Sets the rule that an extended ingress
mask>| any}{<destination-ipaddr><dip-mask>| any}[dscp <0-63>][fragment] ACL is used to match IP packet.
zte(extend-acl-group)#rule <1-500>{permit | deny} tcp {<source-ipaddr
><sip-mask>| any}[source-port <0-65535><sport-mask>]{<destination-ipa Sets the rule that an extended ingress
ddr><dip-mask>| any}[dest-port <0-65535><dport-mask>][establishing | ACL is used to match TCP packet.
established][dscp <0-63>][fragment]
zte(extend-acl-group)#rule <1-500>{permit | deny} udp
{<source-ipaddr><sip-mask>| any}[source-port <0-65535><s Sets the rule that an extended ingress
port-mask>]{<destination-ipaddr><dip-mask>| any}[dest-port ACL is used to match UDP packet.
<0-65535><dport-mask>][dscp <0-63>][fragment]
zte(extend-acl-group)#rule <1-500>{permit | deny} arp {<sender-ipaddr><s Sets the rule that an extended ingress
ip-mask>| any}{<target-ipaddr><tip-mask>| any} ACL is used to match ARP packet.
zte(cfg)#clear ingress-acl extend number <100-199> Clears an extended port ACL instance.
Creates and configures a layer-2
zte(cfg)#config ingress-acl link number <200-299>
ingress ACL instance.
zte(link-acl-group)#rule <1-500>{permit | deny} ip {[cos
Sets the rule that a layer-2 ingress ACL
<0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
is used to match IP packet.
any][<dest-mac><dmac-mask>| any]}
zte(link-acl-group)#rule <1-500>{permit | deny} arp {[cos
Sets the rule that a layer-2 ingress ACL
<0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
is used to match ARP packet.
any][<dest-mac><dmac-mask>| any]}
zte(link-acl-group)#rule <1-500>{permit | deny} other {[ether-type Sets the rule that a layer-2 ingress ACL
<1501-65535>| dsap-ssap <0-65535>][cos <0-7>][<vlan-id>[<vlan-mask is used to match the packet except
>]][<source-mac><smac-mask>| any][<dest-mac><dmac-mask>| any]} IP/ARP.
zte(link-acl-group)#rule <1-500>{permit | deny} any [<vlan-id>[<vlan-mask Sets the rule that a layer-2 ingress ACL
>]][cos <0-7>][<source-mac><smac-mask>| any][<dest-mac><dmac-mask>| is used to match packets with specified
any] cos, VLAN id, smac, and dmac flags.
zte(cfg)#clear ingress-acl link number <200-299> Clears a layer-2 ingress ACL instance.
Creates and configures a hybrid ingress
zte(cfg)#config ingress-acl hybrid number <300-399>
ACL instance.
4-44
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(hybrid-acl-group)#rule <1-500>{permit | deny}<ip-protocol>{<source-ipa
Sets the rule that a hybrid ingress ACL
ddr><sip-mask>| any}{<destination-ipaddr><dip-mask>| any}[dscp <0-63>][f
matches IPv4–specified protocol field
ragment][cos <0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
packet.
any][<dest-mac><dmac-mask>| any]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} ip {<source-ipaddr><s
ip-mask>| any}{<destination-ipaddr><dip-mask>| any}[dscp <0-63>][fra Sets the rule that a hybrid ingress ACL
gment][cos <0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>| matches IPv4 packet.
any][<dest-mac><dmac-mask>| any]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} tcp {<source-ipaddr><s
ip-mask>| any}[source-port <0-65535><sport-mask>]{<destination-ipaddr
Sets the rule that a hybrid ingress ACL
><dip-mask>| any}[dest-port <0-65535><dport-mask>][dscp <0-63>][fra
matches IPv4-TCP packet.
gment][cos <0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
any][<dest-mac><dmac-mask>| any]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} udp {<source-ipaddr
><sip-mask>| any}[source-port <0-65535><sport-mask>]{<destination-ipa
Sets the rule that a hybrid ingress ACL
ddr><dip-mask>| any}[dest-port <0-65535><dport-mask>][dscp <0-63>][f
matches IPv4-UDP packet.
ragment][cos <0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
any][<dest-mac><dmac-mask>| any]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} arp {<sende
r-ipaddr><sip-mask>| any}{<target-ipaddr><tip-mask>| any}[cos Sets the rule that a hybrid ingress ACL
<0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>| is used to match ARP packet.
any][<dest-mac><dmac-mask>| any]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} any {[ether-type <1501
Sets the rule that a hybrid ingress ACL
-65535>][cos <0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
is used to match non-IPv6 packet.
any][<dest-mac><dmac-mask>| any]}
zte(hybrid-acl-group)#rule <1-500>{permit | deny} ipv6 <ip-protocol>{<s Sets the rule that a hybrid ingress
ource-ipv6addr><sipv6-mask>| any}{<destination-ipv6addr><dipv6-mask>| ACL is used to match IPv6–specified
any}[<vlan-id>] protocol field packet.
zte(hybrid-acl-group)#rule <1-500>{permit | deny} ipv6 tcp
{<source-ipv6addr><sipv6-mask>| any}[source-port <0-65535><s Sets the rule that a hybrid ingress ACL
port-mask>]{<destination-ipv6addr><dipv6-mask>| any}[dest-port is used to match IPv6-TCP packet.
<0-65535><dport-mask>][<vlan-id>]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} ipv6 udp
{<source-ipv6addr><sipv6-mask>| any}[source-port <0-65535><s Sets the rule that a hybrid ingress ACL
port-mask>]{<destination-ipv6addr><dipv6-mask>| any}[dest-port is used to match IPv6-UDP packet.
<0-65535><dport-mask>][<vlan-id>]
zte(hybrid-acl-group)#rule <1-500>{permit | deny} ipv6 any
Sets the rule that a hybrid ingress ACL
{<source-ipv6addr><sipv6-mask>| any}{<destination-ipv6addr><dipv6-mask>|
is used to match IPv6 packet.
any}[<vlan-id>]
4-45
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Sets the rule that a hybrid ingress ACL
zte(hybrid-acl-group)#rule <1-500>{permit | deny} all
is used to match any packet.
zte(cfg)#clear ingress-acl hybrid number <300-399> Clears a hybrid ingress ACL instance.
Enters and configures a global ingress
zte(cfg)#config ingress-acl global
ACL instance.
zte(global-acl-group)#rule <1-16>{permit | deny} port {<1-28>|
any}<ip-protocol>{<source-ipaddr><sip-mask>| any}{<destina Sets the rule that a global ingress ACL
tion-ipaddr><dip-mask>| any}[dscp <0-63>][fragment][cos matches IPv4–specified protocol field
<0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>| packet.
any][<dest-mac><dmac-mask>| any]
zte(global-acl-group)#rule <1-500>{permit | deny} port {<1-28>| any}
ip {<source-ipaddr><sip-mask>| any}{<destination-ipaddr><dip-mask>| Sets the rule that a global ingress ACL
any}[dscp <0-63>][fragment][cos <0-7>][<vlan-id>[<vlan-mask>]][<source- matches IPv4 packet.
mac><smac-mask>| any][<dest-mac><dmac-mask>| any]
zte(global-acl-group)#rule <1-500>{permit | deny} port {<1-
28>| any} tcp {<source-ipaddr><sip-mask>| any}[source-port
<0-65535><sport-mask>]{<destination-ipaddr><dip-mask>| Sets the rule that a global ingress ACL
any}[dest-port <0-65535><dport-mask>][dscp <0-63>][fragment][cos matches IPv4–TCP packet.
<0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
any][<dest-mac><dmac-mask>| any]
zte(global-acl-group)#rule <1-500>{permit | deny} port {<1-28>|
any} udp {<source-ipaddr><sip-mask>| any}[source-port
<0-65535><sport-mask>]{<destination-ipaddr><dip-mask>| Sets the rule that a global ingress ACL
any}[dest-port <0-65535><dport-mask>][dscp <0-63>][fragment][cos matches IPv4–UDP packet.
<0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>|
any][<dest-mac><dmac-mask>| any]
zte(global-acl-group)#rule <1-500>{permit | deny} port {<1-28>| any}
arp {<sender-ipaddr><sip-mask>| any}{<target-ipaddr><tip-mask>| Sets the rule that a global ingress ACL
any}[cos <0-7>][<vlan-id>[<vlan-mask>]][<source-mac><smac-mask>| is used to match ARP packet.
any][<dest-mac><dmac-mask>| any]
zte(global-acl-group)#rule <1-500>{permit | deny} port {<1-28>| any} any
Sets the rule that a global ingress ACL
{[ether-type <1501-65535>][cos <0-7>][<vlan-id>[<vlan-mask>]][<source-m
is used to match non IPv6 packet.
ac><smac-mask>| any][<dest-mac><dmac-mask>| any]}
Creates a basic egress ACL instance
zte(cfg)#config egress-acl basic number < 400-499>
and configures it.
zte(egress-basic-acl)#rule < 1-500>{ permit | deny}{< source-ipaddr><
Sets a basic egress ACL.
sip-mask>| any}[ fragment]
zte(cfg)#clear egress-acl basic number < 400-499> Clears a basic egress ACL instance.
4-46
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Creates an extended egress ACL
zte(cfg)#config egress-acl extend number < 500-599>
instance and configures it.
zte(egress-extend-acl)#rule < 1-500>{ permit | deny}< ip-protocol>{<
Sets an extended egress ACL which
source-ipaddr>< sip-mask>| any}{< destination-ipaddr>< dip-mask>| any}[
matches the protocol field of IPv4.
dsscp < 0-63>][ fragment]
zte(egress-extend-acl)#rule < 1-500>{ permit | deny} icmp {<
Sets an extended egress ACL which
source-ipaddr>< sip-mask>| any}{< destination-ipaddr>< dip-mask>| any}[
matches ICMP packet.
iicmp-ttype < 0-254>< icmp-code>][ dsscp < 0-63>][ fragment]
zte(egress-extend-acl)#rule < 1-500>{ permit | deny} ip {< source-ipaddr><
Sets an extended egress ACL which
sip-mask>| any}{< destination-ipaddr>< dip-mask>| any}[ dsscp < 0-63>][
matches IP packet.
fragment]
zte(egress-extend-acl)#rule < 1-500>{ permit | deny} tcp {< source-ipaddr><
sip-mask>| any}[ ssourrce-porrtt < 0-65535>< sport-mask>]{< Sets an extended egress ACL which
destination-ipaddr>< dip-mask>| any}[ desstt-porrtt < 0-65535>< matches TCP packet.
dport-mask>][ establishing | established][ dsscp < 0-63>][ fragment]
zte(egress-extend-acl)#rule < 1-500>{ permit | deny} udp {<
source-ipaddr>< sip-mask>| any}[ ssourrce-porrtt < 0-65535>< Sets an extended egress ACL which
sport-mask>]{< destination-ipaddr>< dip-mask>| any}[ desstt-porrtt < matches UDP packet.
0-65535>< dport-mask>][ dsscp < 0-63>][ fragment]
zte(egress-extend-acl)#rule < 1-500>{ permit | deny} arp {< sender-ipaddr>< Sets an extended egress ACL which
sip-mask>| any}{< target-ipaddr>< tip-mask>| any} matches ARP packet.
Clears an extended egress ACL
zte(cfg)#clear egress-acl extend number < 500-599>
instance.
Creates a layer-2 egress ACL instance
zte(cfg)#config egress-acl link number < 600-699>
and configures it.
zte(egress-link-acl)#rule < 1-500>{ permit | deny} ip {[ coss < 0-7>][< Sets a layer-2 egress ACL which
vlan-id>[< vlan-mask>]][< dest-mac>< dmac-mask>| any]} matches the IP packet.
zte(egress-link-acl)#rule < 1-500>{ permit | deny} arp {[ coss < 0-7>][< Sets a layer-2 egress ACL which
vlan-id>[< vlan-mask>]][< dest-mac>< dmac-mask>| any]} matches the ARP packet.
zte(egress-link-acl)#rule < 1-500>{ permit | deny} other {[ ether-type
< 1501-65535>| dsap-ssap < 0-65535>][ coss < 0-7>][< vlan-id>[< Sets a layer-2 egress ACL which
vlan-mask>]][< source-mac>< smac-mask>| any][< dest-mac>< dmac-mask>| matches the packets except IP/ARP.
any]}
Sets the rule that a layer-2 egress ACL
zte(egress-link-acl)#rule <1-500>{permit | deny} any [<vlan-id>[<vlan-ma
is used to match packets with specified
sk>]][cos <0-7>][<dest-mac><dmac-mask>| any]
cos, VLAN id, and dmac flags.
zte(cfg)#clear egress-acl link number < 600-699> Clears a layer-2 egress ACL instance.
4-47
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Creates a hybrid egress ACL instance
zte(cfg)#config egress-acl hybrid number < 700-799>
and configures it.
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny}< ip-protocol>{<
source-ipaddr>< sip-mask>| any}{< destination-ipaddr>< dip-mask>| any}[ Sets a hybrid egress ACL which
dsscp < 0-63>][ fragment][ coss < 0-7>][< vlan-id>[< vlan-mask>]][< matches the protocol field of IPv4.
source-mac>< smac-mask>| any][< dest-mac>< dmac-mask>| any]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} ip {< source-ipaddr><
sip-mask>| any}{< destination-ipaddr>< dip-mask>| any}[ dsscp < 0-63>][ Sets a hybrid egress ACL which
fragment][ coss < 0-7>][< vlan-id>[< vlan-mask>]][< source-mac>< matches the IPv4 packet.
smac-mask>| any][< dest-mac>< dmac-mask>| any]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} tcp {< source-ipaddr><
sip-mask>| any}[ ssourrce-porrtt < 0-65535>< sport-mask>]{<
destination-ipaddr>< dip-mask>| any}[ desstt-porrtt < 0-65535>< Sets a hybrid egress ACL which
dport-mask>][ dsscp < 0-63>][ fragment][ coss < 0-7>][< vlan-id>[< matches the IPv4-TCP packet.
vlan-mask>]][< source-mac>< smac-mask>| any][< dest-mac>< dmac-mask>|
any]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} udp {< source-ipaddr><
sip-mask>| any}[ ssourrce-porrtt < 0-65535>< sport-mask>]{<
destination-ipaddr>< dip-mask>| any}[ desstt-porrtt < 0-65535>< Sets a hybrid egress ACL which
dport-mask>][ dsscp < 0-63>][ fragment][ coss < 0-7>][< vlan-id>[< matches the IPv4-UDP packet.
vlan-mask>]][< source-mac>< smac-mask>| any][< dest-mac>< dmac-mask>|
any]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} arp {< sender-ipaddr><
sip-mask>| any}{< target-ipaddr>< tip-mask>| any}[ coss < 0-7>][< vlan-id>[< Sets a hybrid egress ACL which
vlan-mask>]][< source-mac>< smac-mask>| any][< dest-mac>< dmac-mask>| matches the ARP packet.
any]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} any {[ ettherr-ttype
Sets a hybrid egress ACL which
< 1501-65535>][ coss < 0-7>][< vlan-id>[< vlan-mask>]][< source-mac><
matches the non-IPv6 packet.
smac-mask>| any][< dest-mac>< dmac-mask>| any]}
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} iipv6 < ip-protocol>{<
Sets a hybrid egress ACL which
source-ipv6addr>< sipv6-mask>| any}{< destination-ipv6addr>< dipv6-mask>|
matches the protocol field of IPv6.
any}[< vlan-id>]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} ipv6 tcp {<
source-ipv6addr>< sipv6-mask>| any}[ ssourrce-porrtt < 0-65535>< Sets a hybrid egress ACL which
sport-mask>]{< destination-ipv6addr>< dipv6-mask>| any}[ desstt-porrtt < matches the IPv6-TCP packet.
0-65535>< dport-mask>][< vlan-id>]
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} ipv6 udp {<
source-ipv6addr>< sipv6-mask>| any}[ ssourrce-porrtt < 0-65535>< Sets a hybrid egress ACL which
sport-mask>]{< destination-ipv6addr>< dipv6-mask>| any}[ desstt-porrtt < matches the IPv6-UDP packet.
0-65535>< dport-mask>][< vlan-id>]
4-48
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} ipv6 any {<
Sets a hybrid egress ACL which
source-ipv6addr>< sipv6-mask>| any}{< destination-ipv6addr>< dipv6-mask>|
matches the IPv6 packet.
any}[< vlan-id>]
Sets a hybrid egress ACL which
zte(egress-hybrid-acl)#rule < 1-500>{ permit | deny} all
matches any packet.
zte(cfg)#clear egress-acl hybrid number < 700-799> Clears a hybrid egress ACL instance.
move <1-500>{after | before}<1-500>(all ACL configuration modes) Sorts a rule in ACL instance.
clear rule <1-500>(all ACL configuration modes) Clears one rule in ACL instance.
Displays the best mask configuration
zte(cfg)#show vlan-range <vlan-range>
when VLAN ID is matched in batch.
Displays the configuration information
zte(cfg)#show acl binding {all | port [<portlist>]| vlan [<vlanlist>]}
that ACL is bound to the interface.
zte(cfg)#show acl config Displays ACL summary configuration.
zte(cfg)#show acl config [<1-800>| name <word>][ active | command | deny Displays the detailed configuration of
| passive | permit | policy | rule <1-500>| snmp | time-range ] ACL instance.
ACL Configuration Instance
l Configuration Description
As shown in Figure 4-13, configure ACL in the switch to realize the following functions.
Forbid the users to access the exterior net through the gateway from 9:00 to 18:00.
The gateway connects with the switch on port 26. The client PC connects switch on
port 1-24. All the users access the exterior network through the gateway 192.168.0.1.
Figure 4-13 ACL Configuration Instance
4-49
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l Configuration Procedure
zte(cfg)#config ingress-acl hybrid number 300
zte(ingress-hybrid-acl)#rule 1 deny ip any 192.168.0.1 255.255.255.255
zte(ingress-hybrid-acl)#rule 2 deny arp any 192.168.0.1 255.255.255.255
zte(ingress-hybrid-acl)#exit
zte(cfg)#set port 1-24 acl 300 enable
zte(cfg)#set time-range worktime range period 09:00 to 18:00 daily
zte(cfg)#set time-range worktime acl 300 rule 1 enable
zte(cfg)#set time-range worktime acl 300 rule 2 enable
4.13 QoS Configuration
QoS Overview
QoS can provide end-to-end data switching telecommunication with high quality. The
content includes the following parts:
l Port ingress rate limit
l Port egress shaping
l Port queue schedule algorithm
l Port priority mapping
l QoS profile configuration
l Flow classification
l Flow rate limit
l Flow statistics, count the packet with the special color on the base of flow rate limit.
l Flow mapping, flow redirection.
l Modify the specified field of specified packet, such as modifying DSCP field of colored
packet.
QoS includes port QoS, global QoS and flow-based QoS according to influence range.
For the data packet QoS handling method on the network edge device of access side,
there are the following conditions:
l Switch can select whether to trust the packet and which field of the packet, such as
UP or DSCP, can be trusted when receiving the packet and allocate QoS service
according to trusted field.
l When the data packet received by the switch is not trusted, QoS service is allocated
according to related QoS configuration of receiving port.
l QoS service defines the internal processing method and external processing method
of the packet. The internal processing method includes flow classification TC and so
on but external processing method includes modifying data packet 802.1p user priority
UP or DSCP domain of IP header.
For the following network core device, implement the service same as the previous service
according to 802.1p of the packet or DSCP mark. So that, a set of end-to-end QoS service
is provided. When the flow exceeds the configuration, the network device can modify QoS
service level such as dropping packets or allocating the lower level QoS service.
4-50
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
When data packet enters the port, the switch will do the QoS initial mark which mainly
includes the initialization of TC QoS.
In the direction of switch egress, QoS is used to put the packet into the suitable queue
according to marked TC and do the corresponding queue scheduling algorithm and
congestion control algorithm according to the current queue configuration and modify it
according to 802.1p User priority or IP Dscp field of data packet.
Configuring QoS
The QoS configurations on ZXR10 2900E includes global-based QoS configuration and
port-based QoS configuration. Part of QoS configuration is related to ACL. The QoS
configuration includes the following commands:
Command Function
zte(cfg)#set qos priority-mapping port <1-28> default-up <0-7> Sets the default port UP priority.
zte(cfg)#set qos priority-mapping port <1-28> trust-mode {dscp-priority |
Sets the port trusted mode.
port-profile | user-priority}
zte(cfg)#set qos priority-mapping port <1-28>{remapping-dscp | remark Sets packet UP/DSCP
{dscp-priority | user-priority}}{enable | disable} remark/remapping based on port.
Sets the mapping relation between
zte(cfg)#set qos priority-mapping qos-profile dscp-to-dscp <0-63> to <0-63>
DSCPs .
zte(cfg)#set qos priority-mapping port <1-28> port-to-profile qos-profile Sets the mapping relation between port
<0-127> and profile.
zte(cfg)#set qos priority-mapping qos-profile {up-to-profile <0-7>| Sets the mapping relation between
dscp-to-profile <0-63>} qos-profile <0-127> DSCP/UP and profile.
zte(cfg)#set qos priority-mapping qos-profile <0-127>{drop-priority {red |
yellow | green}| dscp-priority <0-63>| user-priority <0-7>| traffic-class Sets the QoS profile template.
<0-7>}
Sets 128 QoS profiles to recover default
zte(cfg)#set qos priority-mapping qos-profile default
values.
Sets the optimized queue scheduling
zte(cfg)#set qos queue-schedule enhance {disable| enable}
mode.
zte(cfg)#set qos queue-schedule mode {byte | packet} Sets the QoS queue scheduling unit.
Sets the scheduling policy of each
zte(cfg)#set qos queue-schedule port <1-28>{session <1-7>| default}
queue of the port.
zte(cfg)#set qos queue-schedule session <1-7><0-255><0-255><0-255><0-25
Sets scheduling policy template.
5><0-255><0-255><0-255><0-255>[single-wrrgroup]
Sets the speed limit mode of the global
zte(cfg)#set qos traffic-limit mode {byte|packet}
Ingress port.
4-51
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Sets 100 M port ingress rate limit, in
zte(cfg)#set qos traffic-limit fe-port <1-24>{data-rate <0-100000>| disable} which <0-100000> is the maximum of
data transmission rate.
Sets 100 M port ingress rate limit, in
zte(cfg)#set qos traffic-limit fe-port <1-24>{packet-rate
which <0-148810> is the maximum of
<0-148810>[packet-lenth <64-10240>]| disable}
packet transmission rate.
zte(cfg)#set qos traffic-limit fe-port <1-24> packet-type {broadcast | Sets the packet type that rate limit
known-uc | multicast | tcp-syn | unknown-uc}{enable | disable} function limits.
zte(cfg)#set qos traffic-limit fe-port <1-24> protect {enable|disable} Sets the port rate limiting function.
Sets the port shutdown time when the
zte(cfg)#set qos traffic-limit fe-port <1-24> protect time <1-10>
port rate limit function is enabled.
Sets 1000 M port ingress rate limit, in
zte(cfg)#set qos traffic-limit ge-port <25-28>{data-rate <0-1000000>|
which, <0-100000> is the maximum of
disable}
data transmission rate.
Sets 1000 M port ingress rate limit, in
zte(cfg)#set qos traffic-limit ge-port <25-28>{packet-rate
which, <0-148810> is the maximum of
<0-1488100>[packet-lenth <64-10240>]| disable}
packet transmission rate.
zte(cfg)#set qos traffic-limit ge-port <25-28> packet-type {broadcast | Sets the packet type that rate limit
known-uc | multicast | tcp-syn | unknown-uc}{enable | disable} function limits.
Sets the ingress rate limiting function
zte(cfg)#set qos traffic-limit ge-port <25-28> protect {enable|disable}
for the 1000 M port.
Sets the port shutdown time when the
zte(cfg)#set qos traffic-limit ge-port <25-28> protect time <1-10>
port rate limit function is enabled.
Sets the ingress rate limit for the 10000
zte(cfg)#set qos traffic-limit xge-port <2/1-2/4>{data-rate <0-10000000>|
M port, in which, <0-100000> is the
disable}
maximum of data transmission rate
Sets the ingress rate limit for the 10000
zte(cfg)#set qos traffic-limit ge-port <2/1-2/4>{packet-rate
M port, in which, <0-148810> is the
<0-14881000>[packet-lenth <64-10240>]| disable}
maximum of packet transmission rate.
zte(cfg)#set qos traffic-limit xge-port <2/1-2/4> packet-type {broadcast | Sets the message type restricted by the
known-uc | multicast | tcp-syn | unknown-uc}{enable | disable} rate limit function.
zte(cfg)#set qos traffic-shaping fe-port <1-24>{data-rate <32-100000>
Sets 100M egress shaping rate.
burst-size <8-4094>| disable}
zte(cfg)#set qos traffic-shaping fe-port <1-24> queue <1-7>{data-rate Sets 100M egress shaping rate based
<32-100000> burst-size <8-4094>| disable} on queue.
zte(cfg)#set qos traffic-shaping ge-port <25-28>{data-rate <2-1000>
Sets 1000M egress shaping rate.
burst-size <8-4094>| disable}
4-52
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#set qos traffic-shaping ge-port <25-28> queue <1-7>{data-rate Sets 1000M egress shaping rate based
<2-1000> burst-size <8-4094>| disable} on queue.
zte(cfg)#set qos traffic-shaping xge-port <2/1-2/4>{data-rate <2-10000> Sets the Egress shaping rate for the
burst-size <8-4094>| disable} 10000 M port.
zte(cfg)#set qos traffic-shaping xge-port <2/1-2/4> queue <1-7>{data-rate Sets the queue-based Egress shaping
<2-10000> burst-size <8-4094>| disable} rate for the 10000 M port.
Enables or disables the anti-DoS
zte(cfg)#set anti-DoS {enable | disable}
attacking function.
Displays priority mapping configuration
show qos priority-mapping port [<1-28>] (all configuration modes)
based on port.
show qos priority-mapping qos-profile [<0-127>| dscp-to-dscp | Displays various priority-mapping
dscp-to-profile | up-to-profile] (all configuration modes) configuration related to QoS-profile.
show qos queue-schedule mode (all configuration modes) Displays QoS queue scheduling unit.
Displays the queue scheduling policy of
show qos queue-schedule port <1-28> (all configuration modes)
each queue of the port.
Displays the configuration of scheduling
show qos queue-schedule session [<1-7>] (all configuration modes)
policy template.
Displays the egress rate limiting
show qos traffic-limit [port <1-28>] protect (all configuration modes)
configuration of the port.
show qos traffic-limit [port <1-28>] (all configuration modes) Displays ingress rate limit configuration.
show qos traffic-shaping [port <1-28>] (all configuration modes) Displays egress shaping configuration.
Displays anti-dos attacking
show anti-dos (all configuration modes)
configuration.
zte(cfg)#set qos policer <0-383> mode {aware | blind} cir <32-1048576>
cbs <20000-268435456>{ebs <20000-268435456>| pir <32-1048576> pbs Sets flow policer.
<20000-268435456>}
zte(cfg)#set qos policer <0-383> exceed-action red {no-operation | drop
Sets flow policing action.
| remark} yellow {no-operation | drop | remark}
zte(cfg)#set qos policer <0-383> exceed-action remark profile <0-127> Sets the binding and action
up {no-change | enable-modify | disable-modify} dscp { no-change | implementation mode between
enable-modify | disable-modify } flow policer and QoS profile.
zte(cfg)#set qos policer counter-mode {L1 | L2 | L3} Sets flow policer statistics mode.
Enables or disables flow policer
statistics function and configures the
zte(cfg)#set qos policer <0-383> counter <0-255>{enable | disable}
binding between flow policer and
Counter.
4-53
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables flow policer and handles the
zte(cfg)#set policy policing in acl <1-800> rule <1-500> policer <0-383>
special flow by flow policer.
zte(cfg)#set policy remark in ingress-acl <1-399,800> rule <1-500> profile Uses QoS profile to modify the specified
<0-127> up {no-change | enable-modify | disable-modify} dscp {no-change | flow UP/DSCP field that the ingress
enable-modify | disable-modify} ACL matches.
Uses QoS profile to modify the specified
zte(cfg)#set policy remark in egress-acl < 400-799> rrulle < 1-500> up {
flow UP/DSCP field that the egress
no-change |< 0-7>} dscp { no-change |< 0-63>}
ACL matches.
Sets the session between flow mapping
zte(cfg)#set mirror analyze-port session <1-3>{enable | disable}
port and port mapping .
zte(cfg)#set policy mirror in acl <1-399,800> rule <1-500>{cpu | Copies the specified data flow to the
analyze-port} monitor port.
zte(cfg)#set policy redirect in acl <1-399,800> rule <1-500>{cpu | port Redirects the specified data flow to the
<1-28>} user-specified egress port.
Implements flow statistic for the data
zte(cfg)#set policy statistics in acl <1-800> rule <1-500> counter <0-1023>
flow matching ACL rule.
zte(cfg)#set policy vlan-remark in acl <1-800> rule <1-500><1-4094>{nested Remarks the VLAN attribution of the
| replace {untagged | tagged | all}} designated flow.
zte(cfg)#set policy harddrop in acl <1-800> rule <1-500> Sets harddrop.
Clears the configuration of the specified
zte(cfg)#clear policy remark in acl <1-800> rule <1-500> flow UP/DSCP field modified by QoS
profile.
Clears the configuration that the flow
zte(cfg)#clear policy in acl <1-800> rule <1-500> policer processes the processes the
specified flow.
Clears the configuration that the
zte(cfg)#clear policy mirror in acl <1-399,800> rule <1-500> specified flow mirrors to the specified
port.
Clears the configuration that the
zte(cfg)#clear policy statistics in acl <1-800> rule <1-500> specified flow do the statistics
according to the number of the packet.
Clears the configuration that the
zte(cfg)#clear policy redirect in acl <1-399,800> rule <1-500> specified flow is redirected to the
specified port.
Clears the configuration of modifying
zte(cfg)#clear policy vlan-remark in acl <1-800> rule <1-500>
the specified flow VLAN tag.
4-54
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Clears the configuration that the
zte(cfg)#clear policy harddrop in acl <1-800> rule <1-500> specified flow implements harddrop
operation.
Clears the counter that counts the
zte(cfg)#clear qos policy-counter <counterlist>
specified flow.
zte(cfg)#clear qos policer-counter <counterlist> Clears flow policer statistics value.
zte(cfg)#clear qos policer <0-383> Clears flow policer configuration.
show qos policer [<0-383>] (all configuration modes) Displays flow policer configuration.
Displays the counter value of specified
show qos policy-counter [<0-1023>] (all configuration modes)
flow.
show qos policer-counter [<0-383>] (all configuration modes) Displays flow policer statistics value.
show policy [mirror | redirect | statistics | policing [<0-383>]| vlan-remark Displays various binding configuration
| remark | harddrop] (all configuration modes) of the specified flow.
zte(cfg)#set icmp protect {enable|disable} Sets the ICMP protection function.
QoS Configuration Instance
l Configuration Description
As show in Figure 4-14, use the 2928E as an example, set the bandwidth (both
direction) of all the user-interface as 2M. The uplink bandwidth of the switch is 20M.
The uplink port is port 26 and the client PC accesses the network through port 24.
Figure 4-14 QoS Configuration Instance
l Configuration Procedure
zte(cfg)#set qos traffic-limit fe-port 1 data-rate 2000
4-55
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#set qos traffic-limit fe-port 2 data-rate 2000
/*Omitted*/
zte(cfg)#set qos traffic-limit fe-port 24 data-rate 2000
zte(cfg)#set qos traffic-shaping ge-port 26 data-rate 20 burst-size 10
l Configuration Verification
zte(cfg)#show qos traffic-shaping port 26
Port Egress Traffic Shaping Table:
Port ID : 26
Port Shaping Rate (Kbps) : 20000 The Burst Size : 10
Queue 0 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 1 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 2 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 3 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 4 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 5 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 6 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
Queue 7 Shaping Rate (Kbps) : No-Limit The Burst Size : N/A
zte(cfg)#sho qos traffic-limit port 1
Port Ingress Traffic Limit Table:
Flags: DataRate - traffic limit rate (Kbps), BcEn - Enable Broadcast Limit
KucEn - Enable Known unicast Limit, McEn - Enable Multicast Limit
TcpSynEn - Enable TCP SYN Limit, UucEn - Enable Unknown unicast Limit
PORT DataRate(Kbps) BcEn KucEn McEn TcpSynEn UucEn
------- -------------- ----- ------ ----- --------- ------
port-1 2000 1 1 1 1 1
4.14 PVLAN Configuration
PVLAN Overview
To enhance network security, it is necessary to isolate users’ packets. A traditional solution
is to allocate a VLAN for a user. This solution has obvious limits, as described below.
1. IEEE 802.1Q standard supports 4094 VLANs at most. The number of users is limited,
which is not good for network extension.
2. Each VLAN corresponds to an IP subnet. Too many subnets bring IP address waste.
3. Too many VLANs and IP subnets make it difficult to manage networks.
The Private VLAN (PVLAN) technology solves these problems. A PVLAN divides ports
in a VLAN into isolated ports, promiscuous ports, and community ports. A promiscuous
port can communicate with any port. An isolated port can communicate only with a
promiscuous port, and it cannot communicate with other isolated ports. A community
port can communicate with a promiscuous port or another community port in the same
session. Therefore, the ports within a VLAN are separated. Users can only communicate
with their default gateways, and the network security is guaranteed.
4-56
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
The ZXR10 2900E series switches support four PVLAN sessions. Each PVLAN session
supports an unlimited number of promiscuous ports. Each PVLAN supports an unlimited
number of isolated or community ports.
Configuring PVLAN
The PVLAN configuration includes the following commands:
Command Function
zte(cfg)#set vlan pvlan session <1-4>{promise-port <portlist>|promise-tr
unk<trunklist>}{isolate-port<portlist>|isolate-trunk<trunklist>}{commu Sets the PVLAN function.
ni-port<portlist>|communi-trunk <trunklist>}
clear vlan pvlan [session<1-4>] Clears the PVLAN configuration.
show vlan pvlan [session<1-4>] (all configuration modes) Displays PVLAN configuration.
zte(cfg)#set vlan pvlan session <1-4>{promise-port <portlist>|promise-
trunk<trunklist>|isolate-port<portlist>|isolate-trunk<trunklist>|commu Configuring a kind of PVLAN port.
ni-port <portlist>| communi-trunk <trunklist>}
PVLAN Configuration Example One
l Configuration Description
As shown in Figure 4-15, add promiscuous port 26 and isolated ports 1, 2, and 3 to
session 1.
Figure 4-15 PVLAN CONFIGURATION EXAMPLE 1
l Configuration Procedure
zte(cfg)#set vlan pvlan session 1 promis-port 26 isolate-port 1-3
l Configuration Verification
zte(cfg)#show vlan pvlan
pvlan session : 1
promis-ports : 26
promis-trunks :
isolate-ports : 1-3
isolate-trunks :
4-57
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
community-ports :
community-trunks :
PVLAN Configuration Example Two
l Configuration Description
As shown in Figure 4-16, add trunk 1 and isolated port 4, 5 and 6 into session 2.
Figure 4-16 PVLAN CONFIGURATION EXAMPLE 2
l Configuration Procedure
1. Configuration of switch A:
zte(cfg)#set lacp enable
zte(cfg)#set lacp aggregator 1 add port 1-3
zte(cfg)#set lacp sggregator 1 mode dynamic
2. Configuration of switch B:
zte(cfg)#set lacp enable
zte(cfg)#set lacp aggregator 1 add port 1-3
zte(cfg)#set lacp aggregator 1 mode dynamic
zte(cfg)#set vlan pvlan session 2 promis-trunk 1 isolate-port 4-6
l Configuration Verification
zte(cfg)#show vlan pvlan
pvlan session : 1
promis-ports : 16
promis-trunks :
isolate-ports : 1-3
isolate-trunks :
community-ports :
4-58
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
community-trunks :
pvlan session : 2
promis-ports :
promis-trunks : 1
isolate-ports : 4-6
isolate-trunks :
community-ports :
community-trunks :
4.15 Layer 2 Protocol Transparent Transmission
Configuration
Layer 2 Protocol Transparent Transmission Overview
IEEE 802.1x is a Port-Based Network Access Control protocol. Port-based network
access control is a way to authenticate and authorize the users to be connected to
the LAN equipment. This type of authentication provides a point-to-pint subscriber
identification method in the LAN.
ZXR10 2900E provides 802.1x transparent transmission function which transparently
transmits 802.1x protocol packets from the client to the authentication server for
authentication.
ZXR10 2900E provides 802.1x transparent transmission function. It also provides layer-2
transparent transmission function such as STP, LACP/OAM, ZGMP,LLDP and GVRP. The
protocol range is 0x00, 0x02-0x2f.
The common layer-2 protocols are shown below.
Protocol Number Protocol
0x00 STP
0x02 LACP/OAM
0x03 802.1x
0x09 ZGMP
0x0E LLDP
0x21 GVRP
Configuring Layer 2 Protocol Transparent Transmission
The configuration of layer-2 protocol transparent transmission includes the following
commands:
4-59
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables L2pt transparent
zte(cfg)#set l2pt <protocol-list>{enable | disable | invalid}
transmission function.
Displays the configuration of L2pt
show l2pt (all configuration modes)
transparent transmission.
Layer 2 Protocol Transparent Transmission Configuration Instance
l Configuration Description
As shown in Figure 4-17, set the LACP transparent transmission function of L2pt of
Switch 1 to implement the link aggregation between Switch 2 and Switch 3. The
configuration increases the link bandwidth and realizes the redundant backup.
Figure 4-17 Layer 2 Protocol Transparent Transmission Configuration Topology
l Configuration Procedure
zte(cfg)#set lacp enable
zte(cfg)#set lacp aggregator 1 add port 1, 2
zte(cfg)#set l2pt 0x02 enable
zte(cfg)#set vlan 100 enable
zte(cfg)#set vlan 100 add port 1, 3
zte(cfg)#set port 1,3 pvid 100
zte(cfg)#set vlan 200 enable
zte(cfg)#set vlan 200 add port 2, 4
zte(cfg)#set port 2,4 pvid 200
l Configuration Verification
Display the aggregation state of Switch 2 and Switch 3:
zte(cfg)#show lacp aggregator 1
Group 1
Actor Partner
4-60
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
------------------------------- ----------------------------
Priority : 32768 32768
Mac : 00.d0.d0.02.00.54 00.d0.d0.29.52.06
Key : 258 258
Ports : 2, 1 2, 1
4.16 IPv4 Layer 3 Configuration
IPv4 Layer 3 Overview
The ZXR10 2900E provides a few IPv4 layer-3 functions for the remote configuration and
management. To realize the remote access, an IP port must be configured on the switch.
If the IP port of the remote configuration host and that of the switch are not in the same
network segment, it is also necessary to configure the static route.
Static route is a simple unicast route protocol. The next-hop address to a destination
network segment is specified by user, where next hop is also called gateway. Static route
involves destination address, destination address mask, next-hop address, and egress
interface. Destination address and destination address mask describe the destination
network information. The next-hop address and egress interface describe the way that
switch forwards destination packet.
The ZXR10 2900E allows adding and deleting the static ARP table. ARP table records
mapping relationship between IP address and MAC address of each node in same
network. When sending IP packets, switch first checks whether destination IP address
is in the same network segment. If yes, switch checks whether there is a peer end IP
address and MAC address mapping entry in the ARP table.
1. If yes, switch directly sends the IP packets to this MAC address.
2. If MAC address corresponding to peer end IP address cannot be found in ARP table,
an ARP Request broadcast packet will be sent to the network to query peer end MAC
address.
Generally, entries of the ARP table on the switch are dynamic. Static ARP table entry need
to be configured only when the connected host cannot respond the ARP Request.
Switch layer-3 configuration includes the following commands:
l Connectivity test
l Layer 3 interface related configuration
l ARP related configuration
l Static route related configuration
ZXR10 2900E series system supports hardware routing function to forward IP packets fast.
To configure the IPv4 layer-3 function, use the config router command to enter into layer-3
configuration mode first.
Configuring IPv4 Layer 3 Functions
The configuration of the IPv4 L3 functions includes the following contents:
4-61
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg)#ping <A.B.C.D>[<0-65535>[<28-65535>[<1-255>[<0-65535>[<A
Detects the network connectivity
.B.C.D>]]]]]
Router trace, which is used to determine
zte(cfg)#trace <A.B.C.D>[max-ttl <1-255>[min-ttl <1-255>[repeat
the path of IP data messages to access
<1-65535>[source <A.B.C.D>[timeout <1-60>[udp-port <1-65535>]]]]]]
the destination.
zte(cfg-router)#set ipport <0-63>{enable | disable} Enables or disables layer-3 interface.
zte(cfg-router)#set ipport <0-63> ipaddress {<A.B.C.D/M>|<A.B.C.D>< Sets IP address and submask of layer-3
A.B.C.D>} port.
zte(cfg-router)#set ipport <0-63> mac <HH.HH.HH.HH.HH.HH> Sets the MAC address of layer-3 port.
zte(cfg-router)#set ipport <0-63> vlan <1-4094> Sets the VLAN binding with layer-3 port.
zte(cfg-router)#iproute {<A.B.C.D/M>|<A.B.C.D>< A.B.C.D>}<
Adds static route.
A.B.C.D>[<1-15>]
zte(cfg-router)#arp add <A.B.C.D><HH.HH.HH.HH.HH.HH><0-63> Adds static ARP.
zte(cfg-router)#arp delete <A.B.C.D> Deletes static ARP.
Sets ARP entry aging time based on
zte(cfg-router)#arp ipport <0-63> timeout <1-1000>
layer-3 interface.
Enables the free ARP function and
zte(cfg-router)#arp gratuitous-send <5-4294967295> sets the period for sending free ARP
messages.
zte(cfg-router)#clear arp Clears dynamic ARP entry in batch.
zte(cfg-router)#clear iproute [{<A.B.C.D/M>|<A.B.C.D><A.B.C.D>}<A.B.C.
Clears static routing entry.
D>]
zte(cfg-router)#clear ipport <0-63>[mac | ipaddress | vlan ] Deletes ipport configuration.
zte(cfg-router)#clear gratuitous-send Disable the free ARP function.
Enables or disables the hardware
zte(cfg-router)#hardware-iproute {enable | disable}
routing function.
Displays the ARP table item information
zte(cfg-router)#show arp [static | dynamic | invalid | ipport <0-63>[static |
and free ARP function status according
dynamic | invalid]| ipaddress <A.B.C.D>]
to various rules.
Displays ipport layer-3 interface
show ipport [<0-63>](all configuration modes)
configuration.
show iproute(all configuration modes) Displays all routing information.
Displays hardware routing
show hardware-iproute (all configuration modes)
configuration.
IPv4 Layer 3 Configuration Instance
l Configuration Description
4-62
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
As shown in Figure 4-18, configure layer-3 ip address as 192.168.1.2 on switch. The
ip address 192.168.1.2 can ping through PC address 192.168.1.1. Bind vlan100 with
192.168.1.2. Port 1 on switch connects with PC.
Figure 4-18 Layer-3 Configuration Instance
l Configuration Procedure
zte(cfg)#set vlan 100 enable
zte(cfg)#set vlan 100 add port 1
zte(cfg)#set port 1 pvid 100
zte(cfg)#config route
zte(cfg-router)#set ipport 0 ipaddress 192.168.1.2 255.255.255.0
zte(cfg-router)#set ipport 0 vlan 100
zte(cfg-router)#set ipport 0 enable
l Configuration Verification
zte(cfg-router)#show ipport
IpPort En/Disable IpAddress Mask MacAddress VlanId
------ ---------- ------------ -------------- ----------------- ------
0 enabled 192.168.1.2 255.255.255.0 00.d0.d0.fa.29.20 100
zte(cfg-router)#exit
Use the ping command to check whether the layer-3 port is available.
zte(cfg)#ping 192.168.1.1
zte(cfg)#ping 192.168.1.1
Reply from 192.168.1.1 : bytes=28 time<1ms TTL=64
Reply from 192.168.1.1 : bytes=28 time<1ms TTL=64
Reply from 192.168.1.1 : bytes=28 time<1ms TTL=64
Reply from 192.168.1.1 : bytes=28 time<1ms TTL=64
Reply from 192.168.1.1 : bytes=28 time<1ms TTL=64
4.17 IPv6 Layer 3 Configuration
IPv6 Layer 3 Function Overview
ZXR10 2900E supports IPv6 layer-3 functions for remote configuration and management.
The Layer 3 functions are as follows:
1. IPv6 interface configuration
2. Ping v6 for checking network connectivity
3. Telnet v6 server for remote login and configuration
4-63
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Configuring IPv6 Layer 3 Functions
The configuration of IPv6 Layer 3 functions includes the following commands:
Command Function
Sets a VLAN associated with an IPv6
zte(cfg-router)#set ipv6port <0> vlan <1-4094>
Layer 3 interface.
zte(cfg-router)#set ipv6port <0> ipv6address {<ipv6Addr/M>|<ipv6Addr Sets an IPv6 address and address prefix
><wildcard>} length of an IPv6 Layer 3 interface.
Enables or disables an IPv6 Layer 3
zte(cfg-router)#set ipv6port <0>{enable | disable}
interface.
zte(cfg-router)#ipv6route default <ipv6Addr> Adds an IPv6 static route.
Clears IPv6 Layer 3 interface
zte(cfg-router)#clear ipv6port <0>[ipv6address <ipv6Addr/M>]
configuration.
zte(cfg-router)#clear ipv6route default Clears the IPv6 default route.
Displays IPv6 Layer 3 interface
show ipv6port (all configuration modes)
configuration.
show ipv6route(all configuration modes) Displays IPv6 route configuration.
Displays IPv6 device neighbor
show ipv6port <0> nd (all configuration modes) information, similar with the function of
the show arp command in IPv4.
Checks network connectivity, similar
zte(cfg)#ping6 <ipv6Addr>[<0-65535>[<48-1280>[<1-255>[<0-65535>]]]] with the function of the ping command
in IPv4.
4.18 DAI Configuration
DAI Overview
Because so many ARP middle-man-attacks happen, DAI (Dynamic ARP inspection) is
introduced in the ZXR10 2900E. DAI checks the ARP packet received by the switch. If the
packet meets the condition, it will be forwarded. Otherwise it will dropped.
DAI is related to the trusted state of the port of the switch. If ARP packet is received on
the trusted port, shield all DAI detections. If ARP packet is received on non-trusted port,
DAI validity test requires to be passed.
Configuring DAI
The DAI configuration includes the following commands:
4-64
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Enables or disables the inspection of
zte(cfg)#set arp-inspection validate {ip | dst-mac | src-mac}{enable | disable}
each field of ARP packet.
Enables or disables DAI function based
zte(cfg)#set arp-inspection vlan <vlanlist>{enable | disable}
on VLAN.
Sets a port to a trusted or untrusted
zte(cfg)#set arp-inspection port <portlist>{trust | untrust}
port.
Sets the maximum number of ARP
zte(cfg)#set arp-inspection port <portlist> limit {<1-100>| infinite}
packets in the unit time.
Displays DAI function configuration
show arp-inspection (all configuration modes)
information.
DAI Configuration Instance
l Configuration Description
As shown in Figure 4-19, when DHCP snooping is enabled, check ARP packet validity
and the corresponding relation between MAC, IP and VLAN. Illegal packet is dropped
and the rate that ARP sends to CPU of non-trusted port is limited.
Figure 4-19 DAI Configuration InstanceTopology
l Configuration Procedure
zte(cfg)#set dhcp snooping-and-option82 enable
zte(cfg)#set dhcp snooping add port 49,50
zte(cfg)#set dhcp port 49 client
zte(cfg)#set dhcp port 50 server
zte(cfg)#show dhcp snooping
DHCP snooping is enabled on the following port(s):
PortId PortType
------ --------
49 Client
50 Server
4-65
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#set arp-inspection vlan 1 enable
zte(cfg)#set arp-inspection port 49 untrust
zte(cfg)#set arp-inspection port 49 limit 15
zte(cfg)#set arp-inspection validate ip enable
zte(cfg)#set arp-inspection validate dst-mac enable
zte(cfg)#set arp-inspection validate src-mac enable
Note:
DAI detection condition: the port sent is non-trusted port, DAI function is enabled on
the VLAN. When DHCP Snooping is enabled and non-trusted port is added into DHCP
Snooping, DAI detection is valid.
l Configuration Verification
zte(cfg)#show arp-inspection
Enabled validation: ip,dst-mac,src-mac
Enabled vlanlist : 1
PortId TrustType Limit(pps)
------ --------- ----------
49 Untrust 15
50 Trust -
51 Trust -
52 Trust -
4.19 Access Service Configuration
Access Service Overview
With the rapid expansion of Ethernet construction scale, to meet the fast increase of
subscribers and requirement of diversified broadband services, Network Access Service
(NAS) is embedded on the switch to improve the authentication and management of
access subscribers and better support the billing, security, operation, and management
of the broadband network.
NAS uses the 802.1x protocol and RADIUS protocol to realize the authentication and
management of access subscribers. It is highly efficient, safe, and easy to operate.
IEEE 802.1x is called port-based network access control protocol. Its protocol system
includes three key parts: client system, authentication system, and authentication server.
l The client system is generally a user terminal system installed with the client software.
A subscriber originates the IEEE802.1x protocol authentication process through this
client software. To support the port-based network access control, the client system
must support the Extensible Authentication Protocol Over LAN (EAPOL).
4-66
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
l The authentication system is generally network equipment that supports the
IEEE802.1x protocol, for example, the switch. Corresponding to the ports of different
subscribers (the ports could be physical ports or MAC address, VLAN, or IP address
of the user equipment), the authentication system has two logical ports: controlled
port and uncontrolled port.
1. The uncontrolled port is always in the state that the bidirectional connections are
available. It is used to transfer the EAPOL frames and can ensure that the client
can always send or receive the authentication.
2. The control port is enabled only when the authentication is passed. It is used to
transfer the network resource and services. The controlled port can be configured
as bidirectional controlled or input controlled to meet the requirement of different
applications. If the subscriber authentication is not passed, this subscriber cannot
visit the services provided by the authentication system.
3. The controlled port and uncontrolled port in the IEEE 802.1x protocol are logical
ports. There are no such physical ports on the equipment. The IEEE 802.1x
protocol sets up a local authentication for each subscriber that other subscribers
cannot use. Thus, there will not be such a problem that the port is used by other
subscribers after the port is enabled.
l The authentication server is generally a RADIUS server. This server can store a
lot of subscriber information, such as VLAN that the subscriber belongs to, CAR
parameters, priority, subscriber access control list, and so on. After the authentication
of a subscriber is passed, the authentication server will pass the information of
this subscriber to the authentication system, which will create a dynamic access
control list. The subsequent flow of the subscriber will be monitored by the above
parameters. The authentication system communicates with the RADIUS server
through the RADIUS protocol.
RADIUS is a protocol standard used for the authentication, authorization, and exchange
of configuration data between the Radius server and Radius client.
RADIUS adopts the Client/Server mode. The Client runs on the NAS. It is responsible
for sending the subscriber information to the specified Radius server and carrying out
operations according to the result returned by the server.
The Radius Authentication Server is responsible for receiving the subscriber connection
request, verifying the subscriber identity, and returning the configuration information
required by the customer. A Radius Authentication Server can serve as a RADIUS
customer proxy to connect to another Radius Authentication Server.
The Radius Accounting Server is responsible for receiving the subscriber billing start
request and subscriber billing stop request, and completing the billing function.
The NAS communicates with the Radius Server through RADIUS packets. Attributes in the
RADIUS packets are used to transfer the detailed authentication, authorization, and billing
information. The attributes used by this switch are primarily standard attributes defined in
the rfc2865, rfc2866, and rfc2869.
The EAP protocol is used between the switch and the subscriber. Three types of identity
authentication methods are provided between the RADIUS servers: PAP, CHAP, and
4-67
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
EAP-MD5. Any of the methods can be used according to different service operation
requirements.
l PAP (Password Authentication Protocol)
PAP is a simple plain text authentication mode. NAS requires the subscriber to
provide the username and password and the subscriber returns the subscriber
information in the form of plain text. The server checks whether this subscriber
is available and whether the password is correct according to the subscriber
configuration and returns different responses. This authentication mode features
poor security and the username and password transferred may be easily stolen.
Figure 4-20 shows the process of using the PAP mode for identity authentication.
Figure 4-20 USING PAP MODE FOR IDENTITY AUTHENTICATION
l CHAP (Challenge Handshake Authentication Protocol)
CHAP is an encrypted authentication mode and avoids the transmission of the user’s
real password upon the setup of connection. NAS sends a randomly generated
Challenge string to the user. The user encrypts the Challenge string by using the own
password and MD5 algorithm and returns the username and encrypted Challenge
string (encrypted password).
The server uses the user password it stores and the MD5 algorithm to encrypt the
Challenge string. Then it compares this Challenge string with the encrypted password
of the server and returns a response accordingly.
Figure 4-21 shows the process of using the CHAP mode for identity authentication.
4-68
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-21 USING CHAP MODE FOR IDENTITY AUTHENTICATION
l EAP-MD5 (Extensible Authentication Protocol - Message Digest 5)
EAP is a kind of authentication mode of transmitting EAP message transparently
including EAP-MD5 and PEAP. The following example is about EAP-MD5 description.
EAP-MD5 is a CHAP identity authentication mechanism used in the EAP framework
structure. Figure 4-22 shows the process of using the EAP-MD5 mode for identity
authentication.
Figure 4-22 USING EAP MODE FOR IDENTITY AUTHENTICATION
Configuring Access Service
The access service configuration includes the following commands:
Command Function
zte(cfg)#set port <portlist> vlanjump {enable [defaultauthvlan <1-4094>]| Enables or disables the vlan jump after
disable]} user 802.1x authentication.
4-69
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables re-authentication
zte(cfg-nas)#dot1x re-authenticate {enable | disable}
function.
Sets the time interval of
zte(cfg-nas)#dot1x re-authenticate period <1-4294967295>
re-authentication.
zte(cfg-nas)#dot1x quiet-period <0-65535> Sets quiet period of authentication.
Sets the time that the authentication
system needs to wait before it can
zte(cfg-nas)#dot1x tx-period <1-65535> retransmit the EAPOL data packet
because it does not receive the
response from the client.
Sets the time-out time for the
authentication system to receive the
zte(cfg-nas)#dot1x supplicant-timeout <1-65535>
data packets from the authentication
client system.
Sets the time-out time for the
authentication system to receive the
zte(cfg-nas)#dot1x server-timeout <1-65535>
data packets from the authentication
server.
Sets the maximum times of request
retransmitting when the timer expires
zte(cfg-nas)#dot1x max-request <1-10> before the authentication system
receives the Challenge response from
the client.
Sets the private MAC address that
zte(cfg-nas)#dot1x add vlan <1-4094>[mac <HH.HH.HH.HH.HH.HH>]
DOT1X protocol can use.
Deletes the private MAC address that
zte(cfg-nas)#dot1x delete vlan <1-4094>
DOT1X protocol can use.
zte(cfg-nas)#clear client Deletes all clients.
zte(cfg-nas)#clear client index <0-255> Clears the specified client.
Deletes the client end user of specified
zte(cfg-nas)#clear client {port <portlist>| vlan <vlanlist>}
port/VLAN.
Displays 802.1x configuration
show dot1x (all configuration modes)
information.
Displays the information of all access
show client (all configuration modes)
users.
Displays the information of an accessing
show client index <0-255> (all configuration modes)
users
4-70
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Displays the user accessing information
show client mac <HH.HH.HH.HH.HH.HH> (all configuration modes)
of a MAC address.
Displays the user accessing information
show client port <portlist> (all configuration modes)
of a port.
Enables or disables port 802.1x access
zte(cfg-nas)#aaa-control port <portlist> dot1x {enable | disable}
authentication function.
zte(cfg-nas)#aaa-control port <portlist> port-mode {auto | Sets the authentication control mode of
force-unauthorized | force-authorized} the port.
Sets the authentication mode of the
zte(cfg-nas)#aaa-control port <portlist> protocol {pap | chap | eap }
port.
Enables or disables port accounting
zte(cfg-nas)#aaa-control port <portlist> accounting {enable | disable}
function.
This allows or prohibits multi-subscriber
zte(cfg-nas)#aaa-control port <portlist> multiple-hosts {enable | disable}
access of the port.
Sets the maximum number of
zte(cfg-nas)#aaa-control port <portlist> max-hosts <0-256>
subscribers connected through the port.
Enables or disables the abnormal
zte(cfg-nas)#aaa-control port <portlist> keepalive {enable | disable} off-line detection mechanism of the
port.
Sets the abnormal off-line detection
zte(cfg-nas)#aaa-control port <portlist> keepalive period <1-3600>
period of the port.
zte(cfg-nas)#aaa-control port <portlist> keepalive antiproxy {add |
delete}{character-detect | ip-modified | multi-card | multi-ipaddress | Enables or disables port anti-deception
packet-analyse | port-detect | service-detect | tcp-session <1-65535>| rule.
udp-session <1-65535>}
zte(cfg-nas)#aaa-control port <portlist> keepalive antidhcp {enable | Enables or disables port
disable} anti-DHCP-deception rule.
Enables or disables the function of
zte(cfg-nas)#aaa-control port <portlist> keepalive client-ip {enable | disable}
acquiring user IP address.
Displays port AAAconfiguration
show aaa-control port [<portlist>] (all configuration modes)
information.
zte(cfg-nas)#radius isp <ispname>{enable | disable} Adds or deletes one ISP domain.
zte(cfg-nas)#radius isp <ispname>{add | delete}accounting Adds or deletes accounting server in
<A.B.C.D>[<0-65535>] ISP.
zte(cfg-nas)#radius isp <ispname>{add | delete} authenticate Adds or deletes authentication server
<A.B.C.D>[<0-65535>] in ISP.
4-71
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg-nas)#radius isp <ispname> client <A.B.C.D> Sets RADIUS client end address.
Sets the shared password of ISP
zte(cfg-nas)#radius isp <ispname> sharedsecret <string>
domain (public key).
Sets or deletes the full account of the
zte(cfg-nas)#radius isp <ispname> fullaccount {enable | disable}
domain.
zte(cfg-nas)#radius isp <ispname> defaultisp {enable | disable} This specifies a default domain.
zte(cfg-nas)#radius isp <ispname> description <string> Sets the domain description.
zte(cfg-nas)#radius nasname <nasname> Sets the NAS server name.
Sets Radius authentication domain
zte(cfg-nas)#radius delimiter <ispdelimiter>
name delimiter.
Sets keep time of radius accounting
zte(cfg-nas)#radius keep-time <0-4294967295>
breaking packet.
zte(cfg-nas)#radius timeout <1-255> Sets the server response time-out time.
Sets the number of retransmissions
zte(cfg-nas)#radius retransmit <1-255>
upon server response time-out.
zte(cfg-nas)#clear accounting-stop {session-id <session-id>| user-name Deletes the radius accounting-stop
<user-name>| isp-name <isp-name>| server-ip <A.B.C.D>} packet which is failed to send.
Displays radius configuration
show radius [ispname <ispname>] (all configuration modes)
information.
show radius accounting-stop [{ session-id <session-id>| user-name
Displays the RADIUS accounting
<user-name>| isp-name <isp-name>| server-ip <A.B.C.D>}] (all
packet which fails to be sent.
configuration modes)
Access Service Configuration Instance
l Configuration Description
As shown in Figure 4-23, the user installs radius client terminal in PC. The switch
connects the radius server and the user’s PC through the network cable. The user
can log in to the switch through the console port and configure the access server, and
then enable client software on user PC to originate authentication request.
4-72
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-23 Access Authentication Configuration Instance
l Configuration Procedure
1. Configure layer-3 interface commands
zte(cfg-router)#set ipport 0 ip 10.40.89.106/24
zte(cfg-router)#set ipport 0 vlan 1
zte(cfg-router)#set ipport 0 enable
2. Configure 802.1X commands
zte(cfg)#set port 2 security enable
zte(cfg)#config nas
zte(cfg-nas)#aaa port 2 dot1x enable
zte(cfg-nas)#aaa port 2 keepalive enable
zte(cfg-nas)#aaa port 2 accounting enable
3. Configure radius commands
zte(zte)#config nas
zte(cfg-nas)#radius isp zte enable
zte(cfg-nas)#radius isp zte defaultisp enable
zte(cfg-nas)#radius isp zte sharedsecret 1234
zte(cfg-nas)#radius isp zte client 10.40.89.106
zte(cfg-nas)#radius isp zte add accounting 10.40.89.78
zte(cfg-nas)#radius isp zte add authentication 10.40.89.106
4. Enable radius client software on PC and input correct username and password.
Then the authentication request is launched.
Note:
Disable the security proxy such as Sygate before the user PC sending authentication
request.
l Configuration Verification
When the authentication request succeeds, view the user information by using the
command show client.
4-73
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#show client
MaxClients : 256 HistoryAccessClientsTotal : 1
OnlineClients: 1 HistoryFailureClientsTotal: 0
Flags:I-Index,Au-Authorized,P-PortId,US-UpSpeed,DS-DownSpeed,Y-yes,N-no
I UserName Au P Vlan MacAddress US DS ElapsedTime
--- ------------- -- ---- ---- ----------------- ------ ------ ------------
0 liushujie Y 2 1 00.19.e0.1a.97.dd 0 0 0:0:0:22
4.20 MAC Authentication Configuration
MAC Authentication Overview
On current networks, many devices (such as IP phones and printers) do not support
authentication client. When connected to networks, the devices cannot initiate D0T1X
authentication.
MAC authentication means that, with a MAC address segment configured on a device,
when the device detects that a MAC address belongs to the address segment, a switch
agent initiates authentication. The user's MAC address is used as a username and
password. If a RADIUS server returns a message indicating that the authentication
succeeded, the device can access the network.
Configuring MAC Authentication
The MAC authentication configuration includes the following commands:
Command Function
Enables or disables the MAC
zte(cfg-nas)#aaa-control mac-authentication {enable | disable }
authentication function.
zte(cfg-nas)#aaa-control mac-authentication session <1-3> range Adds the range of MAC addresses that
<HH.HH.HH.HH.HH.HH><HH.HH.HH.HH.HH.HH> need authentication in unit of session.
Clears the range of MAC addresses in
zte(cfg-nas)#clear mac-authentication session <1-3>
unit of session.
Clears all clients with authenticated
zte(cfg-nas)#clear mac-authentication client
MAC addresses.
Clears a specific MAC authentication
zte(cfg-nas)#clear mac-authentication client mac <HH.HH.HH.HH.HH.HH>
client.
zte(cfg-nas)#clear mac-authentication client {port <portlist>| vlan Clears clients on a specific port or in a
<vlanlist>} specific VLAN.
Displays MAC authentication
show aaa mac-authentication (all configuration modes)
configuration information.
Displays information of all MAC
show aaa mac-authentication client (all configuration modes)
authentication clients.
4-74
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
4.21 QinQ Configuration
QinQ Overview
QinQ is the IEEE 802.1Q tunneling protocol and is also called VLAN stacking. QinQ
technology is the addition of one more VLAN tag (outer tag) to the original VLAN tag (inner
tag). The outer tag can shield the inner tag.
QinQ does not need the protocol support. The simple Layer 2 Virtual Private Network
(L2VPN) can be realized through QinQ. The QinQ is especially suitable for the small-size
LAN that takes the layer-3 switch as its backbone.
Figure 4-24 shows the typical networking of the QinQ technology. The port connected to
the user network is called Customer port. The port connected to the ISP network is called
Uplink port. The edge access equipment of the ISP network is called Provider Edge (PE).
Figure 4-24 TYPICAL QINQ NETWORKING
The user network is generally connected to the PE through the Trunk VLAN mode. The
internal Uplink ports of the ISP network are symmetrically connected through the Trunk
VLAN mode.
1. When a packet is sent form user network 1 to the customer port of switch A, because
the PORTBASE VLAN-based customer port does not identify the tag when receiving
the packet, the customer port processes the packet as an untagged packet no matter
whether this data packet is attached with the VLAN tag or not. The packet is forwarded
by the VLAN 10, which is determined by the PVID.
2. The uplink port of switch A inserts the outer tag (VLAN ID: 10) when forwarding the
data packet received from the customer port. The tpid of this tag can be configured
on the switch. Inside the ISP network, the packet is broadcast along the port of VLAN
10 until it reaches the switch B.
3. Switch B finds out that the port connected to user network 2 is a customer port. Thus, it
removes the outer tag in compliance with the conventional 802.1Q protocol to recover
the original packet and sends the packet to user network 2.
4. In this way, data between user network 1 and user network 2 can be transmitted
transparently. The VLAN ID of the user network can be planned regardless of the
conflict with the VLAN ID in the ISP network.
Configuring QinQ
The QinQ configuration includes the following commands:
4-75
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(cfg)#set vlan qinq customer port <portlist>{enable | disable} Adds or deletes a customer port.
zte(cfg)#set vlan qinq uplink port <portlist>{enable | disable} Adds or deletes an uplink port.
zte(cfg)#set vlan egress-tpid session <1-7> tpid-value <0xHHHH> Sets an egress TPID template.
Sets the binding between port and
zte(cfg)#set port <portlist> egress-tpid {default | session <1-7>}
template.
Displays the egress-tpid value of each
show vlan egress-tpid (all configuration modes)
template.
show vlan qinq (all configuration modes) Displays customer/uplink port of QinQ.
QinQ Configuration Instance
l Configuration Description
As shown in Figure 4-25, encapsulate an exterior label in SW1 (ZXR10 2952E) for the
packet from SW2. The VLAN number is 100. The port connecting upstream BRAS
in SW1 is port 24. The port connecting downstream SW2 is port 1. The NM vlan of
SW1 is 999 and the management IP address is 192.168.0.1/24.
Figure 4-25 QinQ Configuration Instance
l Configuration Procedure
/*set qinq, the outer label is 100*/
zte(cfg)#set vlan 100 enable
zte(cfg)#set vlan 100 add port 1 untag
zte(cfg)#set vlan 100 add port 24 tag
zte(cfg)#set port 1 pvid 100
zte(cfg)#set vlan qinq customer port 1 enable
zte(cfg)#set vlan qinq uplink port 24 enable
zte(cfg)#set vlan 999 enable
zte(cfg)#config router
zte(cfg-router)#set ipport 1 ipaddress 192.168.0.1/24
zte(cfg-router)#set ipport 1 vlan 999
4-76
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zte(cfg-router)#set ipport 1 enable
zte(cfg-router)#exit
4.22 Syslog Configuration
Syslog Overview
Syslog is an important part of Ethernet switch and is the information junction center of
system software module. Syslog manages most of important information output and
classifies in detail , which filters the information effectively and provides the strong support
for network administrator and development staff to monitor network running status and
diagnose network fault.
Syslog is classified by information source and information is filtered by function module,
which satisfies user customized demand.
As shown in Table 4-2, syslog can classify the log information from the top down into eight
levels according to importance. Information filters from low level to high level.
Table 4-2 Syslog Log Information
Severity Level Description
Emergencies crucial fault
Alerts the fault that must be corrected quickly
Critical key fault
Errors the fault need to be noticed but not important
Warnings warn , maybe a mistake exists
Notifications the information that needs to be noticed
Informational general prompt information
Debugging debug information
Configuring Syslog
The Syslog configuration includes the following commands:
Command Function
zte(cfg)#set syslog module {all | arp-inspection | commandlog | dhcp| radius
Enables or disables syslog module.
| AAA}{enable | disable}
zte(cfg)#set syslog level {emergencies | alerts | critical | errors | warnings |
Defines syslog information level.
notifications | informational | debugging }
zte(cfg)#set syslog add server <1-5 > ipaddress <A.B.C.D>[name
Sets syslog server.
<name>][<0-65535>]
zte(cfg)#set syslog delete server <1-5> Deletes syslog server .
4-77
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables syslog function at
zte(cfg)#set syslog {enable | disable}
the global mode.
show syslog status (all configuration modes) Displays configuration of syslog.
Syslog Configuration Instance
l Configuration Description
Suppose that syslog function of switch is enabled , information level is informational,
all function modules are enabled, server IP address is 192.168.1.1, name is Srv1.
l Configuration Procedure
zte(cfg)#set syslog enable
zte(cfg)#set syslog level informational
zte(cfg)#set syslog module all disable
zte(cfg)#set syslog module radius enable
zte(cfg)#set syslog module aaa enable
zte(cfg)#set syslog module commandlog enable
zte(cfg)#set syslog add server 1 ipaddress 192.168.1.1 name server1
l Configuration Verification
zte(cfg)#show syslog status
Syslog status: enable
Syslog level: informational
Syslog enabled modules:
commandlog AAA radius
Syslog disabled modules:
all-others
Syslog server IP UDP port Name
1 192.168.1.1 514 server1
4.23 NTP Configuration
NTP Overview
NTP is the protocol used to synchronize the clocks between network devices. ZXR10
2900E provides NTP client function and synchronizes the clock with other NTP servers.
Configuring NTP
The NTP configuration includes the following commands:
Command Function
zte(cfg)#set ntp add authentication-key <1-255> md5 <string> Sets NTP authentication-key.
zte(cfg)#set ntp delete authentication-key <1-255> Deletes NTP authentication-key.
4-78
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#set ntp {add | delete} trusted-key <1-255> Adds or deletes NTP trusted-key.
Enables or disables NTP authentication
zte(cfg)#set ntp authenticate {enable | disable}
function.
zte(cfg)#set ntp server <A.B.C.D>[version <1,2,3>| key <1-255>] Sets NTP server.
Sets the source IP address that is used
zte(cfg)#set ntp source <A.B.C.D>
for switch to send NTP packet.
zte(cfg)#set ntp clock-period <5-2147483647> Sets the period of NTP synchronization.
zte(cfg)#set ntp timezone <(-12)-(+13)> Sets NTP time-zone.
zte(cfg)#set ntp {enable | disable} Enables or disables NTP.
Sets the ID of the udp port through
zte(cfg)#set ntp src-udp-port {123 | 1000}
which NTP messages are sent.
show ntp (all configuration modes) Displays NTP configuration.
NTP Configuration Instance
l Configuration Description
Suppose that switch and NTP server (IP address is 202.10.10.10) implement
time synchronization. Make sure that switch and NTP server can ping each other
successfully. The NTP module is configured as follows:
l Configuration Procedure
zte(cfg)#set ntp server 202.10.10.10
zte(cfg)#set ntp enable
l Configuration Verification
zte(cfg)#show ntp
ntp protocol is enable
ntp server address : 202.10.10.10
ntp source address : None
ntp source udp port : 1000
ntp is_synchronized : No
ntp rcv stratum : 16
no reference clock.
ntp time zone : 0
In the viewed information, ntp is-synchronized means if the current switch is
synchronized with server.
4-79
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
4.24 GARP/GVRP Configuration
GARP/GVRP Overview
GARP is a kind of generic attribute registration protocol, which distributes VLAN and
multicast MAC address dynamically to the member in the same switching network by
applying the different application protocols.
GVRP(GARP VLAN Registration Protocol)is a kind of application protocol defined by
GARP, which maintains VLAN information in switch dynamically based on GARP protocol
mechanism. All switches supporting GVRP can receive the VLAN registration information
from other switches and update local VLAN registration information dynamically including
the current VLAN on this switch and the ports in this VLAN. Also all switches supporting
GVRP can broadcast the local VLAN registration information to other switches, so that,
the VLAN configurations of all devices with GVRP in the same switching network have
the consistent interworking according to demand.
Configuring GARP/GVRP
The GARP/GVRP configuration includes the following commands:
Command Function
zte(cfg)#set vlan <vlanlist>{permit | forbid}{port <portlist>| trunk Permits or forbids adding/deleting
<trunklist>} port/trunk in the specified VLAN.
zte(cfg)#set garp {enable | disable} Enables or disables GARP function.
zte(cfg)#set garp timer {hold | join | leave | learvall}<timer_value> Sets various GARP timers.
show garp (all configuration modes) Displays GARP configuration
zte(cfg)#set gvrp {enable | disable} Enables or disables GVRP .
Enables or disables GVRP on port/trunk
zte(cfg)#set gvrp {port <portlist>| trunk <trunklist>}{enable | disable}
.
zte(cfg)#set gvrp {port <portlist>| trunk <trunklist>} registration {normal | Sets GVRP registration type on Trunk
fixed | forbidden} port.
show gvrp (all configuration modes) Displays GVRP configuration and state.
Note:
1. Only GARP is enabled first, can GVRP be enabled.
2. Generally, GARP timer uses default value. If it is modified, the configuration in the
network must be same.
3. GVRP port registration type uses default normal value. If it is modified, VLAN learning
cannot be implemented.
4-80
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
GARP/GVRP Configuration Instance
l Configuration Description
As shown in Figure 4-26, switch A connects with switch B through port 1. By
configuring GVRP, the two switches can register each other and refresh their VLAN
table.
Figure 4-26 GVRP Configuration Instance
l Configuration Procedure
1. Configuration of switch A:
zte(cfg)#set garp en
zte(cfg)#set gvrp en
zte(cfg)#set gvrp port 1 en
zte(cfg)#set vlan 10-20 en
zte(cfg)#set vlan 10-20 add port 1
2. Configuration of switch B:
zte(cfg)#set garp en
zte(cfg)#set gvrp en
zte(cfg)#set gvrp port 1 en
zte(cfg)#set vlan 30-40 en
zte(cfg)#set vlan 30-40 add port 1
Note:
1. Garp function should be enabled first before Gvrp function is enabled.
2. Enabling GVRP can enable up to 256 vlans.
3. Timer of Garp generally uses the default value. If it is modified, the value must be
the same as the one configured in the network.
4. Gvrp port registration type uses default Normal value. If it is modified to other
types, vlan learning can’t be done.
l Configuration Verification
SwitchA(cfg)#show garp /*View GARP configuration*/
GARP is enabled!
GARP Timers:
Hold Timeout :100 milliseconds
Join Timeout :200 milliseconds
Leave Timeout :600 milliseconds
LeaveAll Timeout :10000 milliseconds
4-81
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
SwitchA(cfg)#show gvrp /*View GV RP configuration*/
GVRP is enabled!
PortId Status Registration LastPduOrigin
------ -------- ------------ -----------------
1 Enabled Normal 00.d0.d0.f2.51.24
SwitchA(cfg)#show port 1 vlan
PortId : 1
Tagged in vlan : 30-40
Untagged in vlan : 1, 10-20
SwitchB(cfg)#show port 1 vlan
PortId : 1
Tagged in vlan : 10-20
Untagged in vlan : 1, 30-40
SwitchA(cfg)#show vlan 30
VlanId : 30 VlanStatus: enabled
VlanName:
VlanMode: Dynamic
Tagged ports : 1
Untagged ports :
Forbidden ports :
SwitchB(cfg)#show vlan 10
VlanId : 10 VlanStatus: enabled
VlanName:
VlanMode: Dynamic
Tagged ports :1
Untagged ports :
Forbidden ports :
4.25 DHCP Configuration
DHCP Overview
The DHCP (Dynamic Host Configuration Protocol) enables the host to apply dynamic
addresses from server.
The ZXR10 2900E DHCP function includes the following contents:
DHCP snooping function prevents bogus DHCP server from being laid in network, and in
this case, the port connecting to DHCP server must be set to trusted port. What’s more,
dynamic ARP inspection technology can be used together to prevent illegal IP and MAC
address binding, thus ensuring normal assignment of IP addresses by DHCP server.
DHCP Snooping and Option82 are designed to solve these safety problems. DHCP
Snooping, namely DHCP packet filtering, is to detect legality of DHCP packets based on
some special rules and filter illegal packets. Use Option82 technique to provide more
additional information, and then strengthen the network safety ability.
4-82
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
In the DHCP service system, ZXR10 2900E series switches are provided with a lot of
automatically deployed functions. For details, refer to “Downloading Software Version
Automatically”.
Configuring DHCP
The DHCP configuration includes the following commands:
Command Function
Enables or disables DHCP snooping
zte(cfg)#set dhcp snooping-and-option82 {enable | disable}
and Option82 at the global mode.
Enables or disables DHCP Snooping
zte(cfg)#set dhcp snooping {add | delete}{port <portlist>| trunk <trunklist>}
function based on port/trunk.
zte(cfg)#set dhcp port <1-28>{server | cascade | client} Sets DHCP attribute of port.
zte(cfg)#set dhcp trunk <trunklist>{server | default} Sets trunk attribute in DHCP snooping.
Enables or disables port
zte(cfg)#set dhcp ip-source-guard {add | delete} port <portlist>
ip-source-guard function.
zte(cfg)#set dhcp snooping bind-entry mac <HH.HH.HH.HH.HH.HH> ip Adds static user information binding
<A.B.C.D> vlan <1-4094> port <1-28> entry.
Sets the binding mode of port dynamic
zte(cfg)#set dhcp snooping bind-entry mode port <portlist>{hold | drop}
user information binding entry.
Enables or disables DHCP Option82
zte(cfg)#set dhcp option82 {add | delete}{port <portlist>| trunk <trunklist>}
function based on port/trunk.
zte(cfg)#set dhcp option82 sub-option device { ani< string >| remote-ID Configures the device information of
{cisco | manual < string >}} Switch.
zte(cfg)#set dhcp option82 sub-option port <1-28>{circuit-ID {on {cisco
| china-tel | dsl-forum| henan-rtf}| off}| subscriber-ID {on <string>| off}| Sets option82 sub-option.
reserve {on tag <1-255> value <string>| off}}
zte(cfg)#set dhcp option82 mode port <1-52>{default | drop | modify | Sets the mode of port dynamic user
append} information association.
zte(cfg)#clear dhcp snp-bind-entry {mac <HH.HH.HH.HH.HH.HH>| port
Clears DHCP binding entry.
<1-28>| all}
zte(cfg)#clear dhcp option82 sub-option device ani Deletes device identifier information.
Displays the configuration of DHCP
show dhcp (all configuration modes) snooping-and-option82 and DHCP
client.
Displays DHCP snooping global
show dhcp snooping (all configuration modes)
configuration information.
Displays DHCP snooping entry
show dhcp snooping binding[port <1-28>] (all configuration modes)
information.
4-83
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Displays port ip-source-guard
show dhcp ip-source-guard (all configuration modes)
configuration.
Displays DHCP option82 configuration
show dhcp option82 (all configuration modes)
information.
Displays the configuration information
show dhcp option82 port (all configuration modes)
of DHCP option82.
Displays the configuration information
show dhcp option82 device (all configuration modes)
of device.
Enables or disables DHCP client
zte(cfg)#set dhcp client {enable | disable}
function.
Sets whether the packet that DHCP
zte(cfg)#set dhcp client broadcast-flag {enable | disable}
server returns is broadcast packet.
Displays DHCP client configuration
show dhcp client (all configuration modes)
information.
Sets the IP address of layer-3 interface
zte(cfg-router)#set ipport <0-63> ipaddress dhcp
acquired by DHCP protocol.
Releases or renews layer-3 interface IP
zte(cfg-router)#set ipport <0-63> ipaddress dhcp {release | renew}
address.
zte(cfg-router)#set ipport <0-63> dhcp client {class-id {characters <string>|
Sets the sending message when DHCP
hex-numbers <hex-string>}| client-id mac | hostname <string>| lease
client interacts with server.
{<0-365><0-23><0-59>| infinite}}
zte(cfg-router)#set ipport <0-63> dhcp client request {dns-server | Sets message type sent by server when
domain-name | route | static-route | tftp-server-name} DHCP client interacts with server.
zte(cfg-router)#clear ipport < 0-63> dhcp client { class-id | client-id | Clears DHCP client optional sending
hostname | lease } information configuration.
Clears the configuration requesting
zte(cfg-router)#clear ipport <0-63> dhcp client request {dns-server |
DHCP server to return various
domain-name | route | static-route | tftp-server-name}
information.
zte(cfg)#set dhcp snooping bind-entry database read Reads DHCP binding entry from flash.
Recovers binding entry from flash after
zte(cfg)#set dhcp snooping bind-entry database recovery{ disable | enable }
restarted.
zte(cfg)#set dhcp snooping bind-entry database time-write {disable | enable Writes DHCP binding entry into flash at
| time <30-65535>} regular time.
zte(cfg)#set dhcp snooping bind-entry database write Writes DHCP binding entry into flash.
Displays configuration related to DHCP
show dhcp snooping database (all configuration modes)
database.
4-84
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Enables/Disables DHCP udp-check
zte(cfg)#set dhcp special udp-light-check {enable | disable}
function globally.
Enables/Disables snooping function of
zte(cfg)#set dhcp snooping vlan <vlanlist>{ disable | enable }
a VLAN globally.
Configuring DHCP snooping/Option82
l Configuration Description
As shown in Figure 4-27, PC can get IP address from specified DHCP server and
prevent other illegal DHCP servers from affecting hosts in the network.
Figure 4-27 DHCP Snooping/Option82 Configuration InstanceTopology
l Configuration Procedure
zte(cfg)#set dhcp snooping-and-option82 enable
zte(cfg)#set dhcp snooping add port 49,50
zte(cfg)#set dhcp port 49 client
zte(cfg)#set dhcp port 50 server
zte(cfg)#set dhcp ip-source-guard add port 49
zte(cfg)#set dhcp option82 add port 49,50
l Configuration Verification
zte(cfg)#show dhcp snooping
DHCP snooping is enabled on the following port(s):
PortId PortType
------ --------
49 Client
50 Server
DHCP snooping disabled vlan: none
zte(cfg)#show dhcp option82
4-85
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
DHCP option82 is enabled on the following port(s):
PortId PortType
------ --------
49 Client
50 Server
zte(cfg)#show dhcp
DHCP download flag is disabled, config file is found.
DHCP download will not startup, when system reboot.
DHCP config file(option-67) *.dat will be translated to ZXR10_2952E.dat.
DHCP snooping-and-option82 is enabled.
PortId PortType Snooping Option82
------ -------- -------- --------
49 Client Enabled Enabled
50 Server Enabled Enabled
51 Client Disabled Disabled
52 Client Disabled Disabled
DHCP client is disabled.
zte(cfg)#show dhcp ip-source-guard
Ip source guard is configured on the following port(s):
49
Configuring DHCP Client
l Configuration Description
As shown in Figure 4-28, PC can get IP address from specified DHCP server.
Figure 4-28 DHCP Client Configuration InstanceTopology
l Configuration Procedure
zte(cfg)#set dhcp client enable
zte(cfg)#set vlan 10 add port 49 untag
zte(cfg)#set vlan 10 enable
4-86
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zte(cfg)#set port 49 pvid 10
zte(cfg)#config router
zte(cfg-router)#set ipport 0 vlan 10
zte(cfg-router)#set ipport 0 ipaddress dhcp
zte(cfg-router)#set ipport 0 enable
l Configuration Verification
zte(cfg-router)#show ipport
IpPort Status IpAddress Mask MacAddress VlanId IpMode
------ ------ ---------- ------------ ----------------- ------ ------
0 up 100.1.1.5 255.255.0.0 00.00.00.00.00.02 10 dhcp
4.26 DHCPv6 Configuration
DHCPv6 Overview
Dynamic Host Configuration Protocol of IPv6 (DHCPv6) is used by a network host to
dynamically apply for host configuration from a server.
ZXR10 2900E series system supports the following DHCPv6 functions:
1. DHCPv6 snooping function. DHCPv6 servers and clients do not support authentication
mechanism. DHCPv6 servers created illegally and privately bring confusion to address
allocation, gateway and DNS parameters of some hosts. As a result, these hosts
cannot connect to external networks properly. In addition, there are problems such
as IP spoofing, MAC address spoofing and user ID spoofing from illegal clients, and
DHCPv6 server address exhaustion. On the basis of DHCPv6 snooping, the Option82
technology can solve these security problems effectively.
2. IP source guard function. By listening to the DHCPv6 interaction procedure between
a client and a server, the system records the IP address allocated to the client by the
server. The system filters out packets with other source IP addresses on ports, thus
preventing spoofing.
Configuring DHCPv6
The DHCPv6 configuration includes the following commands:
Command Function
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 snooping {enable | disable}
snooping function globally.
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 snooping {add | delete} port <portlist>
snooping function on a port.
Sets the attribute of a port in the
zte(cfg)#set dhcpv6 port <1-28>{server | cascade | client}
DHCPv6 snooping function.
Enables or disables the ip-source-guard
zte(cfg)#set dhcpv6 ip-source-guard {add | delete} port <portlist>
function on a port.
4-87
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 option18 {enable | disable}
Option18 function globally.
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 option18 {add | delete} port <portlist>
Option18 function on a port.
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 option37 {enable | disable}
snooping function globally.
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 option37{add | delete} port <portlist>
Option37 function on a port.
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 option82 {enable | disable}
Option82 function globally.
Enables or disables the DHCPv6
zte(cfg)#set dhcpv6 option82 {add | delete} port <portlist>
Option18 function on a port.
Sets the device identifier of a switch
zte(cfg)#set dhcpv6 option82 ani <string>
node.
zte(cfg)#set dhcpv6 option82 sub-option port <1-28>{circuit-ID {on {cisco
| china-tel | dsl-forum}| off}| subscriber-ID {on <string>| off}| reserve {on Sets Option82 sub-option.
tag <1-255> value <string>| off}}
zte(cfg)#clear dhcpv6 snp-bind-entry {mac <HH.HH.HH.HH.HH.HH>| port
Clears ip-source-guard entities.
<1-28>| all}
zte(cfg)#clear dhcpv6 option82 ani Clears device identifiers.
Displays DHCPv6 snooping and option
show dhcpv6 (all configuration modes)
configuration.
Displays global DHCPv6 snooping
show dhcpv6 snooping (all configuration modes)
configuration information.
show dhcpv6 snooping [port <1-28>] (all configuration modes) Displays DHCPv6 snooping entities.
Displays port ip-source-guard
show dhcpv6 ip-source-guard (all configuration modes)
configuration.
Displays DHCPv6 Option82
show dhcpv6 option82 (all configuration modes)
configuration information.
Displays DHCPv6 Option82
show dhcpv6 option82 port (all configuration modes)
configuration information on ports.
show dhcpv6 option82 ani (all configuration modes) Displays device identifiers.
Displays DHCPv6 Option18
show dhcpv6 option18 (all configuration modes)
configuration information.
Displays DHCPv6 Option37
show dhcpv6 option37 (all configuration modes)
configuration information.
4-88
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
DHCPv6 Configuration Instance
l Configuration Description
This configuration example describes how to configure DHCPv6 snooping/Option82.
As shown in Figure 4-29, the PCs can obtain IP addresses from the DHCP server.
Option82 is used to improve the security performance. It is required to prevent illegal
DHCP server from affecting the PCs on the network.
Figure 4-29 DHCPv6 Snooping/Option82 Configuration Instance
l Configuration Procedure
zte(cfg)#set dhcpv6 snooping enable
zte(cfg)#set dhcpv6 snooping add port 49,50
zte(cfg)#set dhcpv6 port 49 client
zte(cfg)#set dhcpv6 port 50 server
zte(cfg)#set dhcpv6 ip-source-guard add port 49
zte(cfg)#set dhcpv6 option82 enable
zte(cfg)#set dhcpv6 option82 add port 49,50
l Configuration Verification
zte(cfg)#show dhcpv6 snooping
DHCP v6 snooping is enabled on the following port(s):
PortId PortType
------ --------
49 Client
50 Server
zte(cfg)#show dhcpv6 option82
DHCP v6 option82 is enabled on the following port(s):
PortId PortType
------ --------
49 Client
50 Server
zte(cfg)#show dhcpv6 ip-source-guard
4-89
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Ip source guard is configured on the following port(s):
49
4.27 VBAS Configuration
VBAS Overview
VBAS is not physical equipment but a protocol standard, which is developed by
Guangdong Institute of China Telecom. VBAS is to solve the problem of wide-band
user identifier. When BAS gets user identifier by inquiring corresponding relationship
between MAC of users dialing to the switch and port, then sends user name, password
and identifier information to RADIUS, it can judge the position of the user.
Layer 2 communication mode is implemented between BAS and switches, that is,
information query and response data packets of VBAS are encapsulated into Ethernet
data frames of layer-2 directly, and use protocol number 0x8200 to identify.
Caution!
Only trust ports can receive VBAS packets and VBAS response packets only can be sent
from trust ports.
Port connecting to user network is called cascade port and port connecting to BAS server
is called trust port. Typical network of VBAS is shown in Figure 4-30.
Figure 4-30 VBAS Typical Network
Configuring VBAS
The VBAS configuration includes the following commands:
4-90
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Enables or disables global VBAS
zte(cfg)#set vbas trust-port <portlist>{enable | disable}
trust-port.
Enables or disables cascade port VBAS
zte(cfg)#set vbas cascade-port <portlist>{enable | disable}
function.
Enables or disables global VBAS
zte(cfg)#set vbas {enable | disable}
function.
show vbas (all configuration modes) Displays VBAS configuration.
VBAS Configuration Instance
l Configuration Description
As shown in Figure 4-31, this example describes how to set trust port of switch A as
port 1, cascade port as port 2, trust port of switch B as port 1.
Figure 4-31 VBAS Configuration InstanceTopology
l Configuration Procedure
1. Configuration of switch A:
zte(cfg)#set vbas enable
zte(cfg)#set vbas trust-port 1 enable
zte(cfg)#set vbas cascade-port 2 enable
2. Configuration of switch B:
zte(cfg)#set vbas enable
zte(cfg)#set vbas trust-port 1 enable
3. Configuration Verification
Check switch A
zte(cfg)#show vbas
vbas: enabled
trust port : 1
cascade port : 2
4-91
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Check switch B
zte(cfg)#show vbas
vbas: enabled
trust port : 1
cascade port : none
4.28 PPPoE-PLUS Configuration
PPPoE-PLUS Overview
The typical user location technology has PPPoE-PLUS(PPPoE+) besides VBAS and
DHCP OPTION82. PPPOE+ technology inserts user location information in PADI/PADR
message by monitoring the PAD packet interacting procedure between PC and BAS
server. PPPoE+ is divided into three types based on the format of the inserted user
information, China Telecom format, DSL BBS format, and CISCO format. ZXR10 2900E
also supports user-defined formats.
Configuring PPPoE-PLUS
The configuration of PPPoE-PLUS(PPPoE+) includes the following contents:
Command Function
zte(cfg)#set pppoe-plus {enable | disable} Enables or disables PPPoE+ function.
zte(cfg)#set pppoe-plus tag-format port <1-28>{dsl-forum | cisco | china-tel
Sets PPPoE+ location message format.
| manual <string>}
zte(cfg)#set pppoe-plus rid <1-28>[<string>] Adds or deletes port rid information.
show pppoe-plus (all configuration modes) Displays PPPoE+ global configuration.
show pppoe-plus port <1-28> (all configuration modes) Displays port rid configuration.
Sets the mode for dynamic user
zte(cfg)#set pppoe-plus mode port <1-28>{default | drop | modify }
information processing at the port.
PPPoE-PLUS Configuration Instance
l Configuration Description
As shown in Figure 4-32, configure the user information format of switch A as DSL
forum format.
Figure 4-32 PPPOE-PLUS Configuration InstanceTopology
4-92
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
l Configuration Procedure
Configure switch A
zte(cfg)#set pppoe-plus enable
zte(cfg)#set pppoe-plus tag-format port 1 dsl-forum
l Configuration Verification
zte(cfg)#show pppoe-plus
PPPoE plus is enabled.
zte(cfg)#show pppoe-plus port 1
PPPoE Vendor-Specific Tag format on port 1:DSL-Forum
PPPoE-PLUS option mode information on port 1: Default
PPPoE VST remote ID on port 1 has not been set.
4.29 ZESR Configuration
ZESR Overview
With the integration of data, voice, video and IP, the demand for network reliability and
network fault convergence time are raised in the recent years. To shorten the time of
network fault convergence, ZTE provides ZESR (ZTE Ethernet Smart Ring).
ZESR is based on EAPS (RFC 3619) and improved on it. ZESR checks if the ring is proper
and ensures that there is only one logical link between any two nodes, which effectively
prevents the broadcast storm caused by data loop. When there is a fault on link or device
of Ethernet ring, logic route will be switched quickly to ensure the service recover soon.
ZESR protocol is more simple than STP protocol and the topology convergence speed is
more fast.
ZESR Related Concepts
l ZESR Ring: A ZESR ring physically corresponds to an Ethernet ring topology. A
ZESR area consists of multiple ZESR rings. One ring is the major-level, others are
the segment linking with the major-level. If there is only one ring in ZESR area, then
it is the main-level.
l ZESR Control VLAN: Each ZESR area has a control VLAN. The ZESR protocol
message is transmitted in the control VLAN.
l ZESR Protected VLAN: Each ZESR area has multiple protect VLANs. The users’
service is transmitted in the protect VLAN. Realize the service traffic protection in
layer-2 by the link switch of ZESR Protected Vlan.
l Master Node: Master node is the primary control node. The primary ring and the
segment of each level have a node respectively (It can be combined to one, master
edge-port). It takes charge in the control of the primary ring and the segment of each
level.
l Transmission Node: The nodes except the master node in ZESR ring are transmission
node. It mainly assists the master to do loop inspection and service switching.
4-93
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l Edge Node: The node connects with more than 2 levels in ZESR ring is called edge
node. The edge node can be transmission node (contains 2 ports), master node
(contains 2 ports) or assistant port (contains 1 port).
l Assistant Node: The assistant port is also edge port. It is the transmission node that
has only one port in the relative segment. It mainly assists the master node to achieve
service switching for the segment. As shown in “ZESR Multi-ring Multi-domain Design
Figure”, major ring is composed of S1, S2, S3 and S4. Of which S1 is master node,
others are transmission node. Level 1 segment 1 is composed of S3, S4, S5 and S6.
Of which S3 and S4 are assistant nodes, S5 is master node, S6 is transmission node.
Level 1 segment 2 is composed of S3, S4 and S7. Of which S3 and S4 are assistant
nodes, S7 is master node.
l Smart-link node: The smart-link is a simple expansion for the former ZESR function
and realizes the protection for key service link. As shown in “SMART-LINK”, when
the link goes wrong, it can switch automatically and carry out malfunction response in
time.
Introduction to ZESR Function
l Single-Ring Single-Domain ZESR
à ZESR Domain
ZESR domain is an example of ZESR protocol. It is in an Ethernet ring and
consists of master node, transit node and control VLAN.
Figure 4-33 ZESR running state when the ring is “complete state”
As shown in Figure 4-33, each node is ZXR10 2900E switch. All the nodes form
a ring. The MASTER switch is the master node. ZESR Domain sets a control
VLAN composed of all the ports in the ring. The protected VLAN must contain
all the above ports. ZESR Domain sets a master and multi transit nodes. Each
node connects with the ring with two ports: primary port and secondary port.
4-94
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
à ZESR Loop Detection Mode
Master of ZESR Domain sends HEALTH packet from the primary port in cycle.
If the loop link is complete state (the loop is connected), then HEALTH packet
is received by the secondary port, if the secondary port does not receive the
HEALTH packet, then the link state is link failure.
When there is malfunction somewhere, the adjacent node detects the malfunction
and informs the master. The loop is link failure.
As shown in Figure 4-33, the two interfaces of master are: primary and secondary.
The loop port is blocked when master initializes. The secondary port is blocked
when the master detects the normal link. If master detects the disconnection of
the link, then it forwards the secondary port. The loop port is blocked when the
transit initializes.
When the loop is link failure, as shown in Figure 4-34, master opens the
secondary port to make the data transit through secondary port.
Figure 4-34 ZESR running state when the ring is “link failure”
When the loop is link restore, as shown in Figure 4-35, master detects the link
recovery, blocks the secondary port and sets lop as complete state.
4-95
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-35 ZESR running state when the ring is “link restore”
l Multi-Ring Multi-Domain ZESR
à Principle of Multi-Ring Multi-Domain ZESR
ZESR domain consists of many switches, which are configured with the
same domain ID, control VLAN and protection VLAN. These switches are
interconnected. One or more EAPS domains exist on a physical loop. Each
EAPS domain defines its master node, transmission node and assistant node.
Figure 4-36 Multi-Ring Multi-Domain
4-96
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-37 ZESR Multi-Ring Multi-Domain Design Figure
à Basic Operation Principle of Non Level 0 Segment Link
Hierarchical ZESR technology is brought into the complex network. The running
of ZESR protocol on segment link of one level is based on that the upper level
primary ring or segment link is not down.
As shown in Figure 4-38, S3~S6 compose the segment links of level 1 segment
1, where S3 and S4 are assistant nodes and S5 is the master node. S3 and S4
can always intercommunicate with each other via primary ring. If all links where
S3, S4, S5 and S6 locate on segment 1 of level 1 are up, master node S5 will
block its secondary port, and if the states of some links are Down, the secondary
port of the master node will be enabled.
Figure 4-38 Non level 0 Segment Link
4-97
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-39 SMART-LINK
à The Function of Master Node on Primary Ring
One master node exists on primary ring of one ZESR domain. As shown in Figure
4-37, such as master node S1 is both the initiator of detection of ring network state
and the decision-maker for operation after topology changing of primary ring.
à The Function of Transit Node
Transit node is used to monitor the state of direct-connect ZESR link and notify
the link change to master node, who will make decision for processing.
à The Function of Assistant Node
Assistant node is also the border node, and transit node with only one port
on corresponding segment link. It is mainly used to monitor the state of
direct-connect ZESR, notify the link change to master node and meanwhile
monitor the state of master node on segment link.
à The Function of Multi-Domain
Multiple domains are supported on one segment of link, realizing traffic sharing.
l ZESR Tangent Ring
For the reason that ZESR edge-node has heavy burden, ZESR tangent ring adopts
the design of using multi ctrl vlans to protect the same group of protected vlans.
4-98
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-40 Tangent Ring Design Figure
As shown in Figure 4-40, the ring composed by S1, S2, S3 and the ring composed by
S3, S4, S5 are tangent at S3. The two rings belong to different areas, but they protect
the same protected vlans.
l ZESR Linkhello Function
The ZESR protocol of ZXR10 2900E adds the Linkhello interacting protocol between
adjacent nodes. It is used to detect the link faults such as link monologue and link
across transmission equipment. Linkhello interaction is only used for adjacent nodes
and has nothing to do with ZESR node type and network form.
When Linkhello mechanism is added, there are two ways to detect link state: one
is to detect the physical state of link, another is to send Linkhello frame detection
between the two adjacent nodes of the loop. Only when both state are up, the link is
up. Otherwise the link is down.
4-99
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Note:
à No more than 4 areas in one node
à No more than 3 layers in one node
à No more than 3 layers in one area
à No more than 4 lower layer access ports in one node
à No more than 8 ZESR ports in one node
à When the protocol port of ZESR node is enabled and configured (including
master and slave port, edge port, access port), other services, such as adding
aggregation port group, enabling port security, port rate limit and enabling loop
detection cannot be configured on this protocol port.
Configuring ZESR
The ZESR configuration includes the following commands:
Command Function
Adds or deletes ZESR domain control
zte(cfg)#set zesr domain <1-4>{add | delete} control-vlan <vlanId>
VLAN.
Adds or deletes the MSTP instance that
zte(cfg)#set zesr domain <1-4>{add | delete} protect-instance <1-15>
ZESR requires to protect.
zte(cfg)#set zesr domain <1-4>{add | delete}{primary-port <1-28>|
Adds or deletes primary/secondary
primary-trunk <1-15>| secondary-port <1-28>| secondary-trunk
port/trunk on each node.
<1-15>}
zte(cfg)#set zesr domain <1-4>{add | delete}{access-port <1-28>| Adds or deletes SMART-LINK access
access-trunk <1-15>} port/trunk on the ZESR ring node.
zte(cfg)#set zesr domain <1-4> mode smart-link Sets node type as SMART-LINK.
zte(cfg)#set zesr domain<1-4> major-level mode {master | transit |
Sets the node attribute of major-level.
edge-master | edge-transit}
zte(cfg)#set zesr domain <1-4> major-level preforward-timer <3-600> Sets preforward-timer, preup-timer and
preup-timer <0-500> linkdown-failtimer <8-500> linkdown-failtimer on the primary ring.
zte(cfg)#set zesr domain <1-4> level <1-2> segment<1-4> mode {master | Sets the node attribute of secondary
transit | edge-master | edge-transit} ring.
zte(cfg)#set zesr domain <1-4> level <1-2> segment <1-4>{add | Adds or deletes the edge port of the
delete}{edge-port <1-28>| edge-trunk <1-15>}[notmaster | master] secondary ring.
zte(cfg)#set zesr domain <1-4> level <1-2> segment <1-4>
Sets preforward-timer, preup-timer and
preforward-timer <3-600> preup-timer <0-500> linkdown-failtimer
linkdown-failtimer of the secondary ring.
<8-500>
4-100
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#set zesr domain <1-4> linkhello {add | delete} port <1-28> Adds or deletes linkhello port.
zte(cfg)#set zesr domain <1-4> linkhello-timer <1-3> linkhello-failtimer Sets linkhello packet sending interval
<3-9> and linkhello mechanism timeout.
Enables or disables linkhello
zte(cfg)#set zesr domain <1-4> linkhello {enable | disable}
mechanism.
zte(cfg)#set zesr domain <1-4>{enable | disable} Enables or disables ZESR domain.
Sets the attribute of a node on the
zte(cfg)#set zesr domain <domainId> major-level mode {zess-master|zess-tr
major-level ring on a cross-device
ansit|zess-edge-master |zess-edge-transit}
smart-link.
Sets the attributes of the nodes on the
zte(cfg)#set zesr domain <domainId> level <levelId> segment <segId>
slavery device ring under cross-device
mode {zess-master|zess-transit| zess-edge-master|zess-edge-transit}
smart-link.
Sets the mode to send TCN in a ZESR
zte(cfg)#set zesr domain <domainId> tcn {cancel-sending|sending}
domain.
Enables or disables a port to send TCN
zte(cfg)#set zesr tcn-sending port <portlist>{enable|disable}
packets.
Enables or disables a trunk port to send
zte(cfg)#set zesr tcn-sending trunk <trunklist>{enable|disable}
TCN packets.
zte(cfg)#set zesr protocol-mac {normal|special} Sets the ZESR protocol MAC mode.
zte(cfg)#clear zesr domain <1-4> Deletes ZESR domain.
show zesr domain [<1-4>] (all configuration modes) Displays ZESR configuration.
ZESR Single Ring Networking Example
l Configuration Description
As shown in Figure 4-41, S1 is Master node, P1 is Primary Port, P2 is Secondary
Port. S2~S4 are Transit nodes. The protect instance in the ring is 1, the protected
data VLAN is 100 and the protocol control VLAN is 4000.
4-101
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-41 ZESR Single Ring Networking
l Configuration Procedure
1. S1 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2 untag
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode master
zxr10(cfg)#set zesr domain 1 enable
2. S2–S4 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
4-102
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zxr10(cfg)#set zesr domain 1 major-level mode transit
zxr10(cfg)#set zesr domain 1 enable
Note:
1. ZESR port in control VLAN must be configured as tag port.
2. Before enabling ZESR function, STP function must be enabled.
3. The primary port and the secondary port in master node are different on function.
Normally, the primary port is set as forwarding status, but the secondary port is
set as blocking status.
4. The primary port and the secondary port in transit node are the same on function.
Normally, they are both set as forwarding status.
ZESR Multi-Ring Networking Example
l Configuration Description
As shown in Figure 4-42, the multi ring networking composed of 6 switches is shown
above. There are one ZESR primary ring and two hierarchical rings.
1. The primary ring is composed of nodes S1~S4. S1 is Master, P1 is the Primary
Port, P2 is the Secondary Port, S2 is the Transit node, S3~S4 are Edge-Transit
node, P3 and P4 are the edge-port of the two hierarchical rings.
2. The link 1 of hierarchical ring is composed of S6, S3 and S4. S6 is the Master, P1
is the Primary Port, P2 is the Secondary Port, S3 and S4 are the assisting nodes.
3. The link 2 of hierarchical ring 1 is composed of S5, S3 and S4. S5 is the Master,
P1 is the Primary Port, P2 is the Secondary Port, S3 and S4 are the assisting
nodes.
The protect instance in the ring is 1, the protected data is VLAN 100 and the protocol
VLAN is VLAN 4000.
4-103
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-42 ZESR Multi-Ring Networking Topology
l Configuration Procedure
1. S1 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode master
zxr10(cfg)#set zesr domain 1 enable
2. S2 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
4-104
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode transit
zxr10(cfg)#set zesr domain 1 enable
3. S3 and S4 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1-4
zxr10(cfg)#set vlan 4000 add port 1-4 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1-4 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode edge-transit
zxr10(cfg)#set zesr domain 1 level 1 segment 1 add edge-port 3
notmaster
zxr10(cfg)#set zesr domain 1 level 1 segment 2 add edge-port 4
notmaster
zxr10(cfg)#set zesr domain 1 enable
4. S5 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
4-105
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 level 1 segment 2 mode master
zxr10(cfg)#set zesr domain 1 enable
5. S6 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 level 1 segment 1 mode master
zxr10(cfg)#set zesr domain 1 enable
Note:
1. The intersecting node of the primary ring and the hierarchical ring must be
Edge-Port or Edge-Transit.
2. The port connecting the primary ring and the hierarchical ring must be Edge-Port.
3. The edge-port has two attributes: not Master and Master. The attribute not Master
is used in the condition that the master of the hierarchical ring exists. Master is
used in the condition that the master does not exist and the edge-port master
serves as the master.
4. The edge-port with Master attribute must be set on edge-master.
ZESR Smart Link Networking Example
l Configuration Description
This example describes how to configure ZESR smart link networking domain. The
smart link networking composed of 5 switches is shown in Figure 4-43. There are one
ZESR primary ring and one smart link node.
1. The primary ring is composed of nodes S1~S4. S1 is Master, P1 is the
PrimaryPort, P2 is the SecondaryPort, S2 is the Transit node, S3~S4 are
Edge-Transit node, P3 is the Access port using for Smart Link.
2. S5 is the Smart Link node. P1 is the PrimaryPort. P2 is the SecondaryPort.
The protect instance in the ring is 1, the protected data is VLAN 100 and the protocol
VLAN is VLAN 4000.
4-106
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-43 Smart Link Networking
l Configuration Procedure
1. S1 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode master
zxr10(cfg)#set zesr domain 1 enable
2. S2 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
4-107
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode transit
zxr10(cfg)#set zesr domain 1 enable
3. S3 and S4 nodes
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1-3
zxr10(cfg)#set vlan 4000 add port 1-3 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1-3 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode edge-transit
zxr10(cfg)#set zesr domain 1 add access-port 3
zxr10(cfg)#set zesr domain 1 enable
4. S5 node
/*VLAN*/
zxr10(cfg)#set vlan 100 add port 1, 2
zxr10(cfg)#set vlan 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
zxr10(cfg)#set port 1, 2 pvid 100
/*STP*/
zxr10(cfg)#set stp instance 1 add vlan 100
zxr10(cfg)#set stp enable
/*ZESR*/
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 mode smart-link
zxr10(cfg)#set zesr domain 1 enable
4-108
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Note:
1. The intersecting node of the primary ring and the Smart Link node must set as
Edge-Master or Edge-Transit.
2. The port connecting the primary port and Smart Link must set as Access-Port.
3. The Smart Link can be used with the hierarchical ring at the same time.
Cross-Device TCN Sending Example
l Configuration Description
As shown in Figure 4-44, configure ZESS on the ZTE devices from SW-1 or SW-6.
The devices are connected to devices of another vender. It is required to enable STP.
When the link is changed over, SW-1 is responsible for sending TCN to inform the
uplink devices to clear the MAC entities.
4-109
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-44 Cross-Device TCN Sending Example
l Configuration Procedure
Configuration on SW-1:
VLAN:
zxr10(cfg)#set vlan 100, 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
STP:
zxr10(cfg)#set stp enable
zxr10(cfg)#set stp instance 1 add vlan 100
ZESS:
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
4-110
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zxr10(cfg)#set zesr domain 1 major-level mode zess-master
zxr10(cfg)#set zesr domain 1 enable
zxr10(cfg)#set zesr tcn-sending port 1 enable
zxr10(cfg)#set zesr tcn-sending port 2 enable
zxr10(cfg)#set zesr domain 1 tcn sending
The configurations on devices from SW-2 to SW-6:
VLAN:
zxr10(cfg)#set vlan 100, 4000 add port 1, 2 tag
zxr10(cfg)#set vlan 100, 4000 enable
STP:
zxr10(cfg)#set stp enable
zxr10(cfg)#set stp instance 1 add vlan 100
ZESS:
zxr10(cfg)#set zesr domain 1 add control-vlan 4000
zxr10(cfg)#set zesr domain 1 add protect-instance 1
zxr10(cfg)#set zesr domain 1 add primary-port 1
zxr10(cfg)#set zesr domain 1 add secondary-port 2
zxr10(cfg)#set zesr domain 1 major-level mode zess-transit
zxr10(cfg)#set zesr domain 1 enable
4.30 OAM Configuration
OAM Overview
With the rapid development of Ethernet technology, Ethernet networking proportion
gradually increases in network structure . Ethernet devices replacing ATM network
devices and other devices are widely used in access, convergence layer and backbone
network. Due to the great application, Operation Administration Maintenance (OAM)
function of Ethernet devices receive much concern. The main Ethernet OAM protocols
are shown below.
l IEEE 802.3ah (Operations, Administration, and Maintenance-OAM)
l IEEE 802.1ag (Connectivity Fault Management) (Draft)
l ITU-Y 1731 (OAM functions and mechanisms for Ethernet based networks ) (Draft)
IEEE 802.3ah operations, administration and maintenance standard is the formal standard,
which aims at the management of link level. It monitors and troubleshoots the point to
point (virtual point to point) Ethernet link. It has the important meaning for connection
management of Last One Mile. The faults take place constantly on Last One Mile.
ZXR10 2900E series switch supports IEEE 802.3ah.
Ethernet OAM Main Function
4-111
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l OAM Discovery Function: After enabling Ethernet OAM function, ZXR10 2900E series
switch can detect the remote DTE device which has OAM function. After coordinating
with the peer OAM, enter normal Ethernet OAM interaction process .
l Remote Link Event Alarm: OAM function inspects the events of remote link, and
adopts the corresponding responding methods. When the fault takes place on re-
mote link, OAM defines the event and announces it to remote OAM client. The de-
tailed events announcement packet is also provided.
OAM defines the following link events.
1. Link Failure: The physical layer locates the failure that take place on receiving
direction of local DTE.
2. Emergency Failure: The local failure event has happened, and this failure can not
be recovered.
3. Emergency Events: The un-defined emergency event happens.
l OAM Remote Loopback: ZXR10 2900E series switch provides optional data link
layer frame level loopback mode by OAM function. OAM remote loopback is used to
locate failure and examine the link performance. When remote DTE is on the OAM
remote loopback mode, the statistic data of local and remote DTE can be inquired
and compared at any time. Meanwhile, OAM loopback frame can be analyzed to
obtain the additional information of link health (frame discard due to the link failure).
l Link Monitoring: ZXR10 2900E series switch monitors and examines the link state,
and announces the specified frame events by OAM function. The specified frame
events can be classified into four types: error symbol period event, error frame event
and error frame period event, error frame-second statistic event. After inspecting the
error, OAM will respond and alarm the peer device by announcement mechanism.
Configuring OAM
The OAM configuration includes the following commands:
Command Function
Enables or disables global OAM
zte(cfg)#set ethernet-oam {enable | disable}
function.
Enables or disables OAM function on
zte(cfg)#set ethernet-oam port <portlist>{enable | disable}
port.
zte(cfg)#set ethernet-oam port <portlist> period <1-10> timeout <2-20> Enables or disables OAM function on
mode {active | passive} port.
Sets remote-loopback timeout value on
zte(cfg)#set ethernet-oam remote-loopback timeout <1-10>
port.
Starts or stops OAM remote-loopback
zte(cfg)#set ethernet-oam remote-loopback port <portlist>{start | stop}
function on port.
zte(cfg)#set ethernet-oam org-specific {oui <XX-XX-XX>| time-stamp Sets the specified content in OAMPDU
<1-10>} packet.
4-112
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Enables or disables link monitor
zte(cfg)#set ethernet-oam port <portlist> link-monitor {enable | disable}
function.
zte(cfg)#set ethernet-oam port <portlist> link-monitor symbol-period Sets the symbol period event which is
threshold <1-65535> window <1-65535> used for link monitor.
zte(cfg)#set ethernet-oam port <portlist> link-monitor frame threshold
Sets the error frame.
<1-65535> window <1-60>
zte(cfg)#set ethernet-oam port <portlist> link-monitor frame-period
Sets the period of error frame.
threshold <1-65535> window <1-600000>
zte(cfg)#set ethernet-oam port <portlist> link-monitor frame-seconds
Sets error frame summary.
threshold <1-900> window <10-900>
Displays OAM global configuration
show ethernet-oam (all configuration modes)
information.
Displays OAM port summary
show ethernet-oam port (all configuration modes)
information.
show ethernet-oam port <portlist> discovery (all configuration modes) Displays port OAM discovery state.
Displays port OAM statistics
show ethernet-oam port <portlist> statistics (all configuration modes)
information.
Displays port OAM link event
show ethernet-oam port <portlist> link-monitor (all configuration modes)
configuration and state.
OAM Remote Loopback Configuration Instance
l Configuration Description
OAM monitor function can notify the abnormal frame of link receiver to the local. The
function is based on OAM discovery. As shown in Figure 4-45,The user logs in to
the switch through console port and configures OAM. Enable OAM and the port link
monitor of the other end. Then the error frame and the error symbol can be detected
and notify local switch.
Figure 4-45 Remote Loop Network
l Configuration Procedure
1. Configuration of switch A:
zte(cfg)#set ethernet-oam en
zte(cfg)#set ethernet-oam port 1 en
2. Configuration of switch B:
4-113
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#set ethernet-oam enable
zte(cfg)#set ethernet-oam port 2 enable
zte(cfg)#show Ethernet-oam port 2 discovery
PortId 2: ethernet oam enabled
Local DTE /*the local device information*/
-----------
Config:
Mode : active
/*the port mode must be active, or the discovery is failure*/
Period : 10*100(ms)
Link TimeOut : 5(s)
Unidirection : nonsupport
PDU max size : 1518
Status:
Parser : forward
Multiplexer : forward
Stable : yes
/*yes represents that discovery succeeds. no represents discovery fails.*/
Discovery : done
/*discovery succeeds. “undone”represents that discovery fails*/
Loopback : off
PDU Revision : 92
Remote DTE /*the remote device information*/
-----------
Config:
Mode : active
Link Monitor : support
Unidirection : nonsupport
Remote Loopback : support
Mib Retrieval : nonsupport
PDU max size : 1518
Status:
Parser : forward
Multiplexer : forward
Stable : yes
Mac Address : 00.d0.d0.29.28.02
/*the system MAC of the remote device.
The MAC address is 00.00.00.00.00.00 when discovery fails.*/
PDU Revision : 967
zte(cfg)#set ethernet-oam remote-loopback port 2 start
zte(cfg)#show ethernet-oam port 2 discovery
PortId 2: ethernet oam enabled
Local DTE
-----------
4-114
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Config:
Mode : active
Period : 10*100(ms)
Link TimeOut : 5(s)
Unidirection : nonsupport
PDU max size : 1518
Status:
Parser : discard /*the parser state is discard*/
Multiplexer : forward
Stable : yes
Discovery : done
Loopback : on(Master)
/*the local is the active originator (Master).
The other end displays as slave.*/
PDU Revision : 1431
Remote DTE
-----------
Config:
Mode : active
Link Monitor : support
Unidirection : nonsupport
Remote Loopback : support
Mib Retrieval : nonsupport
PDU max size : 1518
Status:
Parser : loopback /*the parser state is loopback*/
Multiplexer : discard /*the multiplexer state is discard*/
Stable : yes
Mac Address : 00.d0.d0.29.28.02
PDU Revision : 28
zte(cfg)#set ethernet-oam remote-loopback port 2 stop
/*disable OAM remote-loopback on port2.
The switch replies OAM discovery success.*/
The key points of configuration:
The switch gives the following prompts when OAM discovery failure occurs, or starting
and stopping remote loopback.
OAM discovery is completed successfully on port 2, the following information appears.
SAT JUL 03 23:30:00 2004 ETH-OAM port 2's discovery process is successful.
Disconnect the network cable between switches, the following information appears.
SAT JUL 03 23:33:00 2004 ETH-OAM port 2 deteced
a fault in the local receive direction.
4-115
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
OAM Link Control Event Configuration Instance
l Configuration Description
OAM monitor function can notify the abnormal frame of the link receiver to the local.
The function is based on OAM discovery. As shown in Figure 4-46,The user logs in to
the switch through console port and configures OAM. Enable OAM and the port link
monitor of the other end. Then the error frame and the error symbol can be detected
and announced to local switch.
Figure 4-46 Link Control Network
l Configuration Procedure
1. Configuration of switch A:
zte(cfg)#set ethernet-oam enable
zte(cfg)#set ethernet-oam port 2 enable
2. Configuration of switch B:
zte(cfg)#set ethernet-oam enable
zte(cfg)#set ethernet-oam port 1 enable
zte(cfg)#set ethernet-oam port 1 link-monitor enable
zte(cfg)#set ethernet-oam port 1 lin symbol-period threshold 10 window 10
zte(cfg)#set ethernet-oam port 1 lin frame threshold 10 window 20
zte(cfg)#set ethernet-oam port 1 link-monitor frame-period threshold 5
window 1000
zte(cfg)#set ethernet-oam port 1 link-monitor frame-seconds threshold 10
window 30
zte(cfg)#show eth port 1 link-monitor
Link Monitoring of Port: 1
Errored Symbol Period Event:
Symbol Window : 10(million symbols)
Errored Symbol Threshold : 10
Total Errored Symbols : 0
Local Total Errored Events : 0
Remote Total Errored Events : 0
Errored Frame Event:
Period Window : 20(s)
Errored Frame Threshold : 10
Total Errored Frames : 0
Local Total Errored Events : 0
Remote Total Errored Events : 0
4-116
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Errored Frame Period Event:
Frame Window : 1000(ten thousand frames)
Errored Frame Threshold : 5
Total Errored Frames : 0
Local Total Errored Events : 0
Remote Total Errored Events : 0
Errored Frame Seconds Event:
Errored Seconds Window : 30(s)
Errored Seconds Threshold : 10(s)
Total Errored Frame Seconds : 0(s)
Local Total Errored Frame Seconds Events : 0
Remote Total Errored Frame Seconds Events : 0
Key of configuration:
The link monitoring events are classified into four types: error symbol monitor event,
error frame monitor event, error frame-period monitor event and error frame-second
statistic monitor event. When the link monitoring information is viewed, the related
error symbol, the statistic of error frame and the statistic of local and peer link events
will be shown on each event.
4.31 SQinQ Configuration
SQinQ Overview
SQinQ is a kind of VLAN tunnel technology. It provides multi-point to multi-point VLAN
transparent transportation service and simple Layer 2 VPN tunnel by means of adding a
VLAN tag outside original 802.1Q tag and getting rid of outside VLAN tag when the packet
is transported to edge switch.
SQinQ has the function of providing SPVLAN tag according to traffic, which is different
from that ordinary QinQ adds SPVLAN tag based on ports. That is, in the same Customer
port, according to difference between traffic carried CVLAN tags, provide corresponding
SPVLAN tag based on user demands.
Configuring SQinQ
The SQinQ configuration includes the following commands:
4-117
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables SVLAN function.
When the SQinQ function is enabled,
the uplink traffic is normally forwarded
in SPVLAN. The downlink traffic
zte(cfg)#set vlan sqinq session <1-400> customer-port <port-id>
is normally forwarded in SPVLAN.
customer-vlan <vlan-list> uplink-vlan <vlan-id>
Because the UNI port belongs to
SPVLAN in untagged mode, the
SPVLAN tag of downlink packets will
be removed.
zte(cfg)#clear vlan sqinq Deletes all SQinQ sessions.
zte(cfg)#clear vlan sqinq session <1-400> Deletes the specified SQinQ session.
show vlan sqinq (all configuration modes) Displays all SQinQ sessions.
show vlan sqinq session <1-400> (all configuration modes) Displays the specified SQinQ session.
SQinQ Configuration Instance
l Configuration Description
Port 1 is a customer port, and port 2 is an uplink port. When CVLAN is 10 and 12, the
packet from port 1 SPVLAN is 997 and 998 respectively.
l Configuration Procedure
Configure the SVLAN instance.
zte(cfg)#set vlan 10,12 add port 1 tag
zte(cfg)#set vlan 997,998 add port 1 untag
zte(cfg)#set vlan 997,998 add port 2 tag
zte(cfg)#set vlan 10,12,997,998 enable
zte(cfg)#set vlan sqinq session 1 customer-port 1 customer-vlan 10 uplink-vlan 997
zte(cfg)#set vlan sqinq session 2 customer-port 1 customer-vlan 12 uplink-vlan 998
l Configuration Verification
The following example shows how to show the SVLAN instance.
zte(cfg)#show vlan sqinq
Session number : 1
Customer Port : 1
Customer Vlan List : 10
Uplink Vlan : 997
Session number : 2
Customer Port : 1
Customer Vlan List : 12
Uplink Vlan : 998
4-118
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
4.32 VLAN Mapping Configuration
VLAN Mapping Overview
VLAN Mapping, namely N to One VLAN mapping, implements the VLAN convergence
function by establishing mapping between customer VLAN and service provider VLAN by
replacing the outer VLAN tags in the data frames. This way, customer services can be
transmitted according to operator’s network planning.
Due to the limited VLAN resource, the VLANs of service provider network and customer
network are planned separately. The “customer VLAN” mentioned in this chapter refers to
CVLAN used in customer network, while the “service provider VLAN” is the SVLAN used
in service provider’s network.
Different services of home users (Internet, IPTV, VoIP) are generally transferred through
different VLANs in the access networks of MAN, as shown in Figure 4-47. As there are
limited VLANs in operator’s network, the VLAN convergence function needs to be fulfilled in
the switches in access layer to transmit the same service, which is transferred by different
users in different VLANs, through one VLAN.
4-119
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-47 VLAN Mapping Networking Diagram
Mapping Modes:
Uplink: replace the CVLAN with SVLAN based on “Interface+customer VLAN”.
Downlink: replace the SVLAN in the outermost layer with CVLAN based on “SVLAN +
Destination MAC address”.
The whole system supports 400 sessions, up to 400 CVLANs can be supported.
4-120
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Configuring VLAN Mapping
The VLAN mapping configuration includes the following commands:
Command Function
Sets the VLAN Mapping function.
When the VLAN Mapping is enabled,
the uplink traffic is normally forwarded
zte(cfg)#set vlan mapping session <session_id> customer-port <<port-id>
in SPVLAN. The downlink traffic is
customer-vlan <vlan-list> uplink-vlan <vlan-id>
normally forwarded in SPVLAN. When
reaching the user port, it is transformed
to the corresponding CVLAN tag.
zte(cfg)#clear vlan mapping Deletes all VLAN Mapping sessions.
Deletes the specified VLAN Mapping
zte(cfg)#clear vlan mapping session <1-400>
session.
Deletes the user information of all VLAN
zte(cfg)#clear vlan mapping user
Mapping sessions.
Deletes the user information of the
zte(cfg)#clear vlan mapping user session <1-400>
specified VLAN Mapping session.
show vlan mapping (all configuration modes) Displays all VLAN Mapping sessions.
Displays the specified VLAN Mapping
show vlan mapping session <1-400> (all configuration modes)
session.
Displays the user information of all
show vlan mapping user-table (all configuration modes)
VLAN Mapping sessions.
Displays the user information of the
show vlan mapping user-table session <1-400> (all configuration modes)
specified VLAN Mapping session.
VLAN Mapping Configuration Instance
l Configuration Description
The port 1 is on customer network, and the port 24 is on service provider network, as
shown in Figure 4-48. Map the packets received from port 1, and whose CVLANs are
between 1-100, to SPVLAN 1000.
4-121
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-48 VLAN Mapping Configuration Instance
SW1 and SW2 are configured in the same way. Take SW1 as example.
l Configuration Procedure
The following example shows how to configure the VLAN Mapping instance.
zte(cfg)#set vlan 1-100,1000 add port 1,24 tag
zte(cfg)#set vlan 1-100,1000 enable
zte(cfg)#set vlan mapping session 1 customer-port 1 customer-vlan 1-100
uplink-vlan 1000
l Configuration Verification
The following example shows how to show the SVLAN instance.
zte(cfg)#show vlan mapping
Session number : 1
Customer Port : 1
Customer Vlan List : 1-100
Uplink Vlan : 1000
4.33 sFlow Configuration
The sFlow configuration includes the following commands:
Command Function
zte(cfg)#set sflow agent-address <A.B.C.D>[udp-port <1-65535>] Sets the IP address of an sFlow agent.
4-122
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Sets the IP address of an sFlow
zte(cfg)#set sflow collector-address <A.B.C.D>[udp-port <1-65535>]
collector.
Sets the format version of sFlow
zte(cfg)#set sflow version <number>
sampling packets.
Enables or disables the sFlow function
zte(cfg)#set sflow {ingress | egress}{enable | disable}
on an ingress or an egress.
Sets the reloading mode on an sFlow
zte(cfg)#set sflow {ingress | egress} reload-mode { continue | cpu}
ingress or egress.
Sets the sampling mode on an sFlow
zte(cfg)#set sflow ingress sample-mode {all | forward}
ingress or egress.
zte(cfg)#set sflow {ingress | egress} port <portlist> packet-sample off Disables port-based sFlow sampling.
zte(cfg)#set sflow {ingress | egress} port <portlist> packet-sample on Enables port-based sFlow sampling or
frequency <2-16000000>[time-range <word>] associates with a time range.
zte(cfg)#clear sflow config [{agent | collector}] Clears sFlow configuration on ports.
zte(cfg)#clear sflow statistic Clears statistics information on ports.
show sflow (all configuration modes) Displays all sFlow configuration.
4.34 PP Configuration
PP Overview
Protocol Protect (PP) maintains and monitors the rate of packets forwarded to the CPU,
thus preventing viruses or spiteful attacks to the switch. In this way, the switch provides
self-protection ability and ensures network security.
PP takes the following measures: limiting the rates of related services, filtering unsuitable
packets, sending alarms when there are packets sent at an abnormal rate, and reminding
NMS that there may be packets attacking the CPU.
To enhance flexibility and compatibility of the switch, PP provides the function of configuring
priority users for the protocol packets sent by the switch.
Configuring PP
The PP configuration includes the following commands:
Command Function
zte(cfg)#create protocol-protect mac-drop rule <1-128> src-mac
Create a mac drop rule.
<HH.HH.HH.HH.HH.HH> mask <HH.HH.HH.HH.HH.HH>
4-123
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables or disables the PP alarm
zte(cfg)#set protocol-protect alarm port <portlist>{enable | disable}
function on a port.
zte(cfg)#set protocol-protect alarm port <portlist>{protocol-name}<0-180 Sets PP 30 second-protocol alarm
00> threshold.
Sets the rate limit of sending packets
zte(cfg)#set protocol-protect limit {group-name}<0-800>
to the CPU.
zte(cfg)#set protocol-protect priority{protocol-name|all}{<0-7>|default} Sets PP protocol priority.
zte(cfg)#set protocol-protect mac-drop {disable | enable} Enables the mac drop function.
zte(cfg)#set protocol-protect mac-drop rule <1-128> bind port <portlist> Binds the mac drop rule with the port.
Clears the number of messages
zte(cfg)#clear protocol-protect mac-drop counter [port <portlist>]
dropped by the mac drop function.
Clears the mac drop rules for specified
zte(cfg)#clear protocol-protect mac-drop port <portlist>[rule <1-128>]
or all ports.
zte(cfg)#clear protocol-protect mac-drop rule [<1-128>] Clears specified mac drop rules.
Displays statistics information of
show protocol-protect statistic [port <portlist>] (all configuration modes)
protocol packet alarms on a PP port.
show protocol-protect limit (all configuration modes) Displays PP rate limit information.
Displays packet priority configuration
show protocol-protect priority (all configuration modes)
information.
show protocol-protect mac-drop port [<portlist>](all configuration modes) Displays the rules and statistics bound
with a specified port.
show protocol-protect mac-drop rule [<1-128>](all configuration modes) Displays specified mac drop rules.
PP Configuration Instance
l Configuration Description
As shown in Figure 4-49, Host 1 sends DHCP attack packets. Users can view
the device operating status and alarm information. Users also can view IGMP
operating status under DHCP packet attacks. The router sends IGMP query packets
periodically.
4-124
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-49 PP Configuration Instance
l Configuration Procedure
zte(cfg)#set igmp snooping enable
zte(cfg)#set igmp snooping add vlan 1
zte(cfg)#set dhcp snooping-option enable
zte(cfg)#set dhcp snooping add port 1-3
l Configuration Verification
Use Host1 to send DHCP Discover packets. View alarm information on the switch.
Thu Jul 1 17:53:18 2004 Receive too many packets of 'dhcp' from port 1
Use Host2 to apply for joining the multicast group 225.0.0.1. View the multicast entity
on the device.
zte(cfg)#show igmp snooping vlan
Maximal group number: 1024
Current group number: 1
Num VlanId Group Last_Report PortMember
---- ------- --------------- --------------- -------------------
1 1 225.0.0.1 10.40.1.10 2-3
4.35 LLDP Configuration
LLDP Overview
The Link Layer Discovery Protocol (LLDP) is a new protocol defined in the 802.1ab. This
protocol allows neighboring devices to send messages to each other to update physical
topology information and establish Management Information Bases (MIBs). The LLDP
workflow is described below:
1. The local device sends its link and management information to a neighbor device.
2. The local device receives the network management information of a neighbor device.
4-125
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
3. The MIB of the local device stores the network management information of all
neighbor devices, and a network management program can query layer-2 connection
information in the MIB.
The LLDP is not a configuration protocol of the remote system or a signaling control
protocol used between two ports. The LLDP discovers layer-2 protocol configuration
conflicts between neighbor devices, but it only reports the problem to an upper-layer
network management device, without providing any mechanism to solve the problem.
The LLDP is simply a neighbor discovery protocol that defines a standard for network
devices (such as switches, routers, and WLAN access points) in the Ethernet to advertise
their identities to other nodes in the network and store discovery information of all neighbor
devices. For example, device configuration and device IDs can be advertised by the LLDP.
The LLDP defines a universal advertisement information set, a protocol for sending
the advertisement information, and a method for storing the received advertisement
information. The device that wants to advertise its information can place multiple pieces
of advertisement information into a Link Layer Discovery Protocol Data Unit (LLDPDU).
The LLDPDU contains a variable-length message unit (called TLVs), which are described
below:
l Type: indicates the type of the message to be sent.
l Length: indicates the number of bytes in the message.
l Value: indicates the contents to be sent.
Each LLDPDU contains four mandatory TLVs and one optional TLV:
l Chassis ID TLV and Port ID TLV: identify the sender.
l TLL TLV: notifies the receiver of the storage period of a message. If the receiver does
not receive any update message within the specified period, the receiver discards all
the related messages. A recommended update frequency is defined by the IEEE, that
is, to send messages at 30-second intervals.
l Optional TLVs: include a basic management TLV set (such as port description TLV), a
special TLV set defined by IEEE 802.1, and a special TLV set defined by IEEE 802.3.
l End of LLDPDU TLV: indicates the end of an LLDPDU.
Configuring LLDP
The LLDP configuration includes the following commands:
Command Function
Sets the interval for sending LLDP
zte(cfg)#lldp hellotime <5-32768>
neighbor discovery messages.
zte(cfg)#lldp holdtime <2-10> Sets the LLDP neighbor holding time.
Sets the maximum number of neighbors
zte(cfg)#lldp max-neighbor <1-31>
that can be discovered by LLDP.
Enables or disables all LLDP functions
zte(cfg)#lldp {port <portlist>| trunk <trunklist>}{enable | disable}
on a specific port.
4-126
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
Enables or disables the LLDP sending
zte(cfg)#lldp {port <portlist>| trunk <trunklist>}{txenable | txdisable}
function on a specific port.
Enables or disables the LLDP receiving
zte(cfg)#lldp {port <portlist>| trunk <trunklist>}{rxenable | rxdisable}
function on a specific port.
Sets the optional MED TLV type sent
zte(cfg)#lldp port <portlist> med-tlv-select <tlv type>{enable | disable}
on a port.
Sets the maximum number of neighbors
zte(cfg)#lldp {port <portlist>| trunk <trunklist>} max-neighbor <1-8> that can be discovered on a specific
LLDP port.
Clears LLDP neighbors with who
zte(cfg)#clear lldp neighbor [{port <portlist>| trunk <trunklist>}] neighbor relationships have been
established.
Clears statistics information of LLDP
zte(cfg)#clear lldp statistic [{port <portlist>| trunk <trunklist>}]
neighbors.
show lldp config [{port <portlist>| trunk <trunklist>}] (all configuration Displays LLDP configuration
modes) information.
show lldp neighbor [{port <portlist>| trunk <trunklist>}] (all configuration Displays summary information of LLDP
modes) neighbors.
show lldp entry [{port <portlist>| trunk <trunklist>}] (all configuration Displays detailed information of LLDP
modes) neighbors.
show lldp statistic [{port <portlist>| trunk <trunklist>}] (all configuration Displays statistics information of LLDP
modes) neighbors.
LLDP Configuration Instance
l Configuration Description
As shown in Figure 4-50, two switches are connected to each other through a
twisted-pair. By default, the LLDP function is enabled, and all parameters use the
default values. Use the show command to view neighbor establishment information.
Figure 4-50 LLDP Configuration Instance
l Configuration Verification
zte(cfg)#show lldp neighbor
Capability Codes:
P-Repeater, B-Bridge, W-WLAN Access Point, R-Router, T-Telephone
C-DOCSIS Cable Device, s-Station, S-Switch, O-Other
Interface DeviceID Holdtime Capability Platform PortID NetworkPolicy
4-127
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
--------------------------------------------------------------------------------
port-19 00d0d0092918 110 B S ZXR10 2918E-PS port-9 Unknown
Version V2.05..
zte(cfg)#show lldp entry
--------------------------------------------------------
Local Port:port-19
Chassis ID:00d0d0092918 (MAC Address)
Port ID :port-9 (Interface Name)
TTL ID :100 (Time to live)
Port Description :port-9 status is up,media-type is 100BaseT,pvid is 1.
System Name :zte
System Description:ZXR10 2918E-PS Version V2.05.10.B10
System Capability :Bridge Switch
4.36 Single Port Loop Detection Configuration
Single Port Loop Detection Overview
Single port loop detection is to check whether a loop exists in the ports of the switch. If such
a loop exists, it may result in errors in learning MAC addresses and may easily cause a
broadcast storm. In severe case, switch and network may be down. Starting the single port
loop detection and disabling the port with loop can efficiently avoid the influence caused
by port loop.
The switch sends a test packet through a port. If this test packet is received through the
port without any change (or only a tag is attached), it indicates that a loop exists in this
port.
The test packet sent by the switch includes the following three parameters:
l Source MAC address: It indicates the MAC address of the switch. The MAC address
of each switch is unique.
l Port Number: Port numbers correspond to the numbers of the ports on the switch one
by one.
l Discrimination Field: For each switch, the digital signature of each port is different.
When three parameters in the receiving and sending test packets are same, the loop
definitely exists on this port.
Configuring Single Port Loop Detection
The configuration of single port loop detection includes the following contents:
Command Function
Sets the interval for sending loop
zte(cfg)#set loopdetect sendpktinterval <5-60>
detection packet.
4-128
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#set loopdetect blockdelay <1-1080> Sets interval for blocking port with loop.
Enables or disables loop detection on
zte(cfg)#set loopdetect port <portlist>{enable|disable}
a port.
Enables or disables loop detection on a
zte(cfg)#set loopdetect port <portlist> vlan <vlanlist>{enable|disable}
port in a specific VLAN.
Enables or disables port protection
zte(cfg)#set loopdetect port <portlist> protect {enable | disable}
when a loop occurs on a port.
Enables or disables cross-device loop
zte(cfg)#set loopdetect extend port <portlist>{enable | disable}
detection on a port.
Enables or disables loop detection on a
zte(cfg)#set loopdetect trunk <trunklist>{enable|disable}
trunk port.
Enables or disables loop detection on a
zte(cfg)#set loopdetect trunk <trunklist> vlan <vlanlist>{enable|disable}
trunk port in a specific VLAN.
Enables or disables trunk port protection
zte(cfg)#set loopdetect trunk <trunklist> protect {enable | disable}
when a loop occurs on a trunk port.
Enables or disables cross-device loop
zte(cfg)#set loopdetect extend trunk <trunklist>{enable | disable}
detection on a trunk port.
show loopdetect (all configuration modes) Displays loop detection information.
Displays port information of loop
show loopdetect port [<portlist>] (all configuration modes)
detection.
Displays trunk information of loop
show loopdetect trunk [<trunklist>] (all configuration modes)
detection.
Clears loop detection configuration
zte(cfg)#clear loopdetect
information.
Single Port Loop Detection Configuration Instance
l Configuration Description
As shown in Figure 4-51, configure the single port loop detection function so that Port
1 on Switch 1 can detect the loop on Switch 2 and block Port 1.
4-129
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-51 Single Port Loop Detection Configuration Topology
l Configuration Procedure
zte(cfg)#set loopdetect port 1 enable
l Configuration Verification
Check the loop detection state of Switch 2:
zte(cfg)#show loopdetect
The block-delay of loopdetect : 5 (min)
The packet interval of loopdetect : 15 (sec)
PortId isUp isStp isProtect isExtend loopVlanNum loopType
------ ---- ----- --------- -------- ----------- ---------
1 Up No Yes No 1 Port
zte(cfg)#show loopdetect port 1
PortId : 1
VlanId isLoop isBlock
------ ------ -------
1 Yes Yes
Double Ports Loop Detection Configuration Instance
l Configuration Description
As shown in Figure 4-52, configure the double ports loop detection function of
loop-detect of switch2 to suppressing broadcast storm of network under switch2.
Figure 4-52 Double Ports Loop Detection Configuration Topology
l Configuration Procedure
Switch2(cfg)#set loopdetect port 1,2 enable
Switch2(cfg)#set loopdetect extend port 1 enable
l Configuration Verification
Check the loop detection state of switch2
4-130
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Switch2(cfg)#show loopdetect
The block-delay of loopdetect : 5 (min)
The packet interval of loopdetect : 15 (sec)
PortId isUp isStp isProtect isExtend loopVlanNum loopType
------ ---- ----- --------- -------- ----------- ---------
1 Up No Yes Yes 1 Port
2 Up No Yes No 0 Port
4.37 UDLD Configuration
UDLD Overview
UniDirectional Link Detection (UDLD) is a Layer 2 logical link detection protocol. It can
detect logical connectivity of Ethernet links and verify physical connectivity. Different from
physical connectivity detection, UDLD is neighbor-based detection. Layer 1 devices are
transparent for UDLD.
UDLD needs to establish neighbor relationship between Layer 2 devices first. When the
UDLD function is enabled on an Ethernet port whose status is up, the port sends a Probe
message inviting a neighbor device to join. The port on which the UDLD function is enabled
on the neighbor device receives the Probe message and sends an Echo message. If the
port receives the Echo message, the connection between the devices works properly in
both directions in the view of the local device. Neighbor relationship is established with
the peer device on the local device. The local devices sends an Echo message. After the
peer device receives the Echo message, the neighbor relationship is established between
the devices.
After neighbor relationship is established, the devices send Hello messages periodically
to detect whether the link is operating properly. When receiving a Hello message from the
neighbor, a device updates the neighbor information saved locally and resets the time-out
period of the neighbor. If the device does not receives a Hello message when the time-out
period expires, it is considered that the a fault occurs to the neighbor and the neighbor is
aged. If the last neighbor is deleted due to aging, it is considered that the link is not in
normal operating state. It is necessary to handle the problem according to working mode.
There are two UDLD working modes: normal mode and aggressive mode.
l In normal mode, only when the device receives a protocol message confirming that
the link is connected incorrectly will the port be shut down. If the device does not
receive the related message or cannot confirm that the link is working properly in one
direction, the device does not operates the port.
l In aggressive mode, if the device cannot confirm that the link is working properly in
both directions (such as the link is connected incorrectly, the link is working properly
only in one direction or the link is a self-loop), the port is shut down. It is necessary to
use the reset or recovery command to recover the communication ability of the port.
Generally, UDLD shuts down a port in the following situations.
4-131
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l In both modes, when an Echo message is sent, the device detects that the neighbor
of the peer port is not the device itself during the final neighbor detection.
l In aggressive mode, the status becomes PROBE because the last neighbor is aged,
and multiple Probe messages are sent continuously without any response.
l In aggressive mode, the port receives the UDLD message sent by itself and there is
a self-loop.
To prevent a neighbor from being aged by mistake, a local device sends Flush messages
on its own initiative to the port on which the UDLD function is enabled in the following
situations.
l The port is down administratively.
l UDLD is down on the port.
l The device is restarted.
Configuring UDLD
The UDLD configuration includes the following commands:
Command Function
zte(cfg)#udld port <portlist>{enable|disable} Enables or disables UDLD on a port.
zte(cfg)#udld port <portlist> mode {aggressive | normal} Sets the mode of a port in UDLD.
Sets the interval of sending messages
zte(cfg)#udld port <portlist> message timer <7-90> after UDLD enters the BiDirectional
status and the port is steady.
Enables or disables the UDLD recovery
zte(cfg)#udld port <portlist> recovery {enable | disable}
function.
zte(cfg)#udld port <portlist> recovery timer <10-600> Sets the recovery interval.
Recovers link establishment function on
zte(cfg)#udld port <portlist> reset
a port manually.
Enables or disables the forced
zte(cfg)#udld force-check {enable | disable}
monologue detection function.
Sets the forced monologue detection
zte(cfg)#udld force-check timer <15-600>
period.
Displays UDLD configuration on all
show udld (all configuration modes)
ports.
Displays port configuration, status and
show udld port [<portlist>] (all configuration modes)
detailed neighbor information.
UDLD Configuration Instance
l Configuration Description
As shown in Figure 4-53, it is required that the switch can detect the connection error,
send alarm information and shut down the ports.
4-132
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-53 UDLD Configuration Instance
l Configuration Procedure
zteA(cfg)#udld port 17,18 enable
zteB(cfg)#udld port 17,18 enable
l Configuration Verification
Thu Jul 1 16:07:09 2004 Udld Port : 17 link failure
Thu Jul 1 16:07:09 2004 Udld Port : 18 link failure
Thu Jul 1 16:07:10 2004 Port : 17 linkdown
Thu Jul 1 16:07:10 2004 Host Topology changed
Thu Jul 1 16:07:10 2004 Port : 18 linkdown
Thu Jul 1 16:07:10 2004 Host Topology changed
zteA(cfg)#show udld port 17
Port 17
Administrative configuration: Enable
Port mode: Aggressive(Aggr)
Current state: Unidirectional - Detected link failure
Recovery configuration: Disable
Recovery time interval: 30s
Message time interval: 15s
Force check configuration: Disable
Force check time: 30s, Remaining: 0s
No neighbour information stored
4.38 TACACS+ Configuration
TACACS+ Overview
Terminal Access Controller Access-Control System Plus (TACACS+) is developed from
TACACS and XTACACS. It is the latest version of TACACS (not compatible with the
previous two versions). It is a popular AAA protocol at present.
4-133
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
TACACS+ supports separate authentication, authorization, and accounting. Different
TACACS+ servers can act respectively as the authentication, authorization, and
accounting servers.
Configuring TACACS+
The TACACS+ configuration includes the following commands:
Command Function
Enables or disables a server
zte(cfg-nas)#tacacs-plus group <group-name>{enable|disable}
group.
zte(cfg-nas)#tacacs-plus group <group-name>{add|delete} host Adds or deletes a server in a
<A.B.C.D>[<49,1025-65535>|<4-180>|<string>] TACACS+ server group.
Sets the default TACACS+ login
zte(cfg-nas)#tacacs-plus loginauthen default group <group-name>
authentication server group.
Sets the default server group
zte(cfg-nas)#tacacs-plus loginauthor default group <group-name>
authorized for TACACS+ login.
Sets the default server group
zte(cfg-nas)#tacacs-plus adminauthen default group <group-name> authenticated for TACACS+
management.
Sets the default server group for
zte(cfg-nas)#tacacs-plus accounting commands default group <group-name>
TACACS+ MML accounting.
Sets the default server group for
zte(cfg-nas)#tacacs-plus accounting exec default group <group-name>
TACACS+ user accounting.
Sets the refresh period for
zte(cfg-nas)#tacacs-plus accounting update period <1-2147483647>
TACACS+ user accounting.
Clears the default TACACS+ login
zte(cfg-nas)#clear tacacs-plus loginauthen default
authentication server group.
Clears the default TACACS+ login
zte(cfg-nas)#clear tacacs-plus loginauthor default
authorization server group.
Clears the default server group
zte(cfg-nas)#clear tacacs-plus adminauthen default authenticated for TACACS+
management.
Clears the default server group for
zte(cfg-nas)#clear tacacs-plus accounting commands default
TACACS+ MML accounting.
Clears the default server group for
zte(cfg-nas)#clear tacacs-plus accounting exec default
TACACS+ user accounting.
Clears the refresh period for
zte(cfg-nas)#clear tacacs-plus accounting update
TACACS+ user accounting.
Displays TACACS+ configuration
show tacacs-plus (all configuration modes)
information.
4-134
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
TACACS+ Configuration Instance
l Configuration Description
As shown in Figure 4-54, the switch works as a TACACS+ client and its IP address is
192.168.1.1/24. The Windows server works as a TACACS+ server and its IP address
is 192.168.1.100/24.
Figure 4-54 TACACS+ Configuration Instance
l Configuration Procedure
zte(cfg)#set loginauth tacacs-plus+local
zte(cfg)#set adminauth tacacs-plus+local
zte(cfg)#config router
zte(cfg-router)#set ipport 1 ipaddress 192.168.1.1 255.255.255.0
zte(cfg-router)#set ipport 1 vlan 1
zte(cfg-router)#set ipport 1 enable
zte(cfg-router)#exit
zte(cfg)#config nas
zte(cfg-nas)#tacacs-plus group zte enable
zte(cfg-nas)#tacacs-plus group zte add host 192.168.1.100
zte(cfg-nas)#tacacs-plus loginauthen default group zte
zte(cfg-nas)#tacacs-plus loginauthor default group zte
zte(cfg-nas)#tacacs-plus adminauthen default group zte
zte(cfg-nas)#tacacs-plus accounting commands default group zte
zte(cfg-nas)#tacacs-plus accounting exec default group zte
zte(cfg-nas)#tacacs-plus accounting update period 10
4.39 Time Range Configuration
Time Range Overview
There are several conditions in the time range configuration.
4-135
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l Configure a time range for each day: Specify the exact start time and end time. If the
start time and the end time are not configured, the time range is a full day.
l Configure a period: Specify the period to be a certain day of a week.
l Configure a date range: Specify the start date and end date. If the start date and the
end date are not configured, the start date is the day when the configuration takes
effect and the end date is the day when the configuration is invalid.
Configuring a Time Range
The time range configuration includes the following commands:
Command Function
zte(cfg)#set time-range <word> period <hh:mm> to <hh:mm>{daily |
day-off | day-working | monday | tuesday | wednesday | thursday | friday Sets a periodic time range.
| saturday | sunday}
zte(cfg)#set time-range <word> absolute <hh:mm><yyyy-mm-dd>[to
Sets an absolute time range.
<hh:mm><yyyy-mm-dd>]
zte(cfg)#clear time-range <word> Clears time range configuration.
show time-range [<word>] (all configuration modes) Displays time range configuration.
4.40 Voice VLAN Configuration
Voice VLAN Overview
The Voice VLAN is a VLAN specially allocated for voice data of users. It provides a voice
VLAN and adds interfaces of voice devices to the voice VLAN. The user can configure
the CoS and DSCP for voice data to increase the priority of voice data transmission and
ensure the call quality.
Voice data can be added to the voice VLAN in two modes: dynamic mode and manual
mode.
In dynamic mode, if the interface fails to be added to or removed from the voice VLAN, the
system will send an alarm to notify the user.
To prevent common service packets from occupying the bandwidth of the voice VLAN and
ensure the quality of voice communication, the voice VLAN provides the security mode.
The security mode is classified into the strict security mode and non-strict security mode.
Configuring a Voice VLAN
The voice VLAN configuration includes the following commands:
Command Function
zte(cfg)#set vlan voice-vlan port <1-18> ingress-vlan <vlanlist>
Sets the voice VLAN function on a port.
voice-vlan <1-4094>
4-136
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#set vlan voice-vlan port <1-18> oui-id <1-32> mac-addr
Adds an OUI to a port.
<HH.HH.HH.HH.HH.HH> mac-mask <HH.HH.HH.HH.HH.HH>
zte(cfg)#set vlan voice-vlan <1-4094> qos-profile <0-127> modify Sets to modify either up or dscp or
{up|dscp|all} both.
Disables the association between a
zte(cfg)#set vlan voice-vlan <1-4094> qos-profile disable
QoS profile and a voice VLAN.
Clears all voice VLAN information
zte(cfg)#clear vlan voice-vlan port <1-18>
configured on a port.
zte(cfg)#clear vlan voice-vlan port <1-18> oui-id Clears all OUIs configured on a port.
Clears a specific OUI configured on a
zte(cfg)#clear vlan voice-vlan port <1-18> oui-id <1-32>
port.
Displays voice configuration on all
show vlan voice-vlan (all configuration modes)
ports.
show vlan voice-vlan port <1-18> (all configuration modes) Displays voice configuration on a port.
show vlan voice-vlan default-oui (all configuration modes) Displays the default OUI of a device.
show vlan voice-vlan user-table port <1-18> (all configuration modes) Displays the user table on a port.
show vlan voice-vlan <vlanlist> qos (all configuration modes) Displays voice VLAN QoS configuration.
Voice VLAN Configuration Instance
l Configuration Description
As shown in Figure 4-55, the two IP Phones are in VLAN 10 and VLAN 20,
respectively. The voice VLAN is VLAN 100.
Figure 4-55 Voice VLAN Configuration Instance
l Configuration Procedure
zte(cfg)#set vlan 10,20,100 add port 1-3 tag
zte(cfg)#set vlan 10,20,100 enable
zte(cfg)#set vlan voice-vlan port 1 oui-id 1 mac-addr 00.00.01.00.00.01
mac-mask FF.FF.FF. FF.FF.FF
4-137
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#set vlan voice-vlan port 2 oui-id 1 mac-addr 00.00.01.00.00.02
mac-mask FF.FF.FF. FF.FF.FF
zte(cfg)#set vlan voice-vlan port 1 ingress-vlan 10 voice-vlan 100
zte(cfg)#set vlan voice-vlan port 2 ingress-vlan 20 voice-vlan 100
l Configuration Verification
zte(cfg)#show vlan voice-vlan
Port Id: 1
Customer Vlan List: 10
Voice-vlan : 100
Oui configed :
oui-id: 1 mac: 00.00.01.00.00.01 mask: FF.FF.FF.FF.FF.FF
Port Id: 2
Customer Vlan List: 20
Voice-vlan : 100
Oui configed :
oui-id: 1 mac: 00.00.01.00.00.02 mask: FF.FF.FF.FF.FF.FF
4.41 802.1AG Configuration
802.1AG Overview
For IEEE802.1ag, the CFM (Connectivity Fault Management) function checks, separates
and reports connectivity faults of the virtual bridge LAN. It is used in operators’ network
and also valid for the C-VLAN (Customer VLAN) network.
The network manager performs planning on network services and levels for the
management and maintenance purposes. The entire network is divided into multiple
Management Domain (MD)s. For a single management domain, refer to Figure 4-56.
Figure 4-56 Single Management Domain
4-138
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
In the domain shown in Figure 4-56, a series ports are defined on peripheral and internal
devices. The grey ports on the peripheral devices are service ports connected to the
external devices and therefore are named Maintenance association End Point (MEP). The
other black ports (including those on intermediate devices) connect internal devices and
therefore are named Maintenance Domain Intermediate Point (MIP). The management
function is implemented through the defined MEP and MIP.
As shown in Figure 4-57, a network is divided into a customer domain, provider domain,
and operator domain. A level between 0-7 is designated for each domain. The domain
level determines the inclusion relation between domains. A domain with a higher level can
include domains with lower levels but not vice versa. The domains with the same level
cannot include each other. This means that all domains can be tangential (internally or
externally) and inclusive but cannot be intersecting.
Figure 4-57 Domains in the Network
The message types defined in the CFM protocol include:
l Continuity Check Message (CCM): A multicast CFM protocol data unit. It is
periodically sent by an MEP to confirm the connectivity of MEP in the same MA. An
MEP receiving a CCM message does not reply to this message.
l Link Trace Message (LTM): A multicast CFM protocol data unit. It is sent by an MEP
to trace the path from the MEP to the MP. Each MP along the path generates an LRT
as a response. This ends until the message reaches the destination or cannot be
further forwarded.
l Link Trace Reply (LTR): A unicast CFM protocol data unit. It is sent by the MP receiving
an LTM to reply to the LTM.
4-139
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
l Loopback Message (LBM): A unicast CFM protocol data unit. It is sent to a specified
MP from an MEP, expected to receive an LBR message.
l Loopback Reply (LBR): A unicast CFM protocol data unit. It is sent by the MP receiving
an LBM as the reply to the LBM.
With the five protocol messages listed above, CFM implements the following functions:
l Detecting faults: MEP detects network connectivity faults by periodically sending
and receiving CCM messages. The faults include connection failure and unwelcome
connection (error connection).
l Notifying faults: After MEP detects a connectivity fault, it sends a proper alarm to the
specified management system, for example, trap messages of SNMP.
l Locating a path: MEP locates and traces a path from an MEP to another MP (including
MEP and MIP) by using LTM/LTR messages.
l Confirming and separating a fault: This is an administrative function. The network
manager confirms the fault through LBM/LBR messages and separates the fault.
Configuring a 802.1AG Command
802.1AG configuration includes the following commands:
Command Function
zte(cfg)#cfm {disable|enable} Enables/disables the CFM function.
Creates a CFM md
zte(cfg)#create cfm md-session <1-16> name <string> level <0-7>
zte(cfg)#create cfm md-session <1-16> ma-session <1-32> name <string> Creates a CFM ma
zte(cfg)#create cfm md-session <1-16> ma-session <1-32> mep-session Creates a CFM local mep
<1-64> mep-id <1-8191> direction {down|up}
zte(cfg)#create cfm md-session <1-16> ma-session <1-32> mip-session Creates a CFM mip
<1-64> name <string>
zte(cfg)#create cfm md-session <1-16> ma-session <1-32> rmep-session Creates a CFM remote mep
<1-64> rmep-id <1-8191> remote-mac <hh.hh.hh.hh.hh.hh>
zte(cfg)#cfm md-session <1-16> ma-session <1-32> primary-vlan Sets the primary VLAN within cfm ma
<1-4094>
zte(cfg)#cfm md-session <1-16> ma-session <1-32> ccm time-interval Sets the interval that ccm packets of
<4-7> mep within cfm ma are sent.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> ccm md-name {absent Sets the way to fill in the MEG ID field
| disable | present} in a cfm ccm messages.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the status of the cfm mep protocol.
state {disable|enable}
4-140
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the status of cfm mep ccm sending
ccm-send {disable|enable} packets of .
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the status of cfm mep ccm
ccm-receive {disable|enable} receiving packets.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the priority of packets sent by cfm
priority <0-7> mep ccm.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the lowest alarm priority of cfm
alarm-lowest-pri <1-5> mep.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Allocates a port or aggregation port for
assign {delete | port <portid>| trunk <trunkid>} mep.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mip-session <1-64> Allocates port or aggregation port for
assign {delete | port <portid>| trunk <trunkid>} mip.
zte(cfg)#clear cfm md-session [<1-16>] Clears all configuration of cfm md.
zte(cfg)#clear cfm md-session <1-16> ma-session [<1-32>] Clears all configuration of cfm ma.
zte(cfg)#clear cfm md-session <1-16> ma-session <1-32>{mep-id Clears all configuration of cfm mep.
[<1-8191>]| mep-session [<1-64>]}
zte(cfg)#clear cfm md-session <1-16> ma-session <1-32> mip-session Clears all configuration of cfm mip.
[<1-64>]
show cfm md-session [<1-16>](all confiuration modes) Displays all configuration of cfm md.
show cfm md-session <1-16> ma-session [<1-32>](all confiuration modes) Displays all configuration of cfm ma.
show cfm md-session <1-16> ma-session <1-32> mp-session [<1-64>](all Displays all configuration of cfm mp.
confiuration modes)
show cfm(all confiuration modes) Displays global protocol status of cfm.
zte(cfg)#cfm lbm md-session <1-16> ma-session <1-32> smep-id Detects lbm.
<1-8191>{dmep-id <1-8191>| dmep-mac <hh.hh.hh.hh.hh.hh>| dmip-mac
<hh.hh.hh.hh.hh.hh>}[repeat <1-200>[size <0-400>[timeout <1-10>]]]
zte(cfg)#cfm ltm md-session <1-16> ma-session <1-32> smep-id Detects ltm.
<1-8191>{dmep-id <1-8191>| dmep-mac <hh.hh.hh.hh.hh.hh>| dmip-mac
<hh.hh.hh.hh.hh.hh>}[ttl <1-64>[timeout <5-10>]]
zte(cfg)#cfm read trans-id <1-4294967295> Reads the ltm path tree.
Network Configuration Without MIP
l Configuration Description
The network configuration without MIP refers to the connected devices as shown
inFigure 4-58.
4-141
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-58 Single-Domain CFM Network Without MIP
l Configuration Procedure
Configuration on S1:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 1
direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 assign port 1
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 2
remote-mac 00.d0.d0.c0.00.02
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
Configuration on S2:
zte(cfg)# cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 2
direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 assign port 2
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 1
remote-mac 00.d0.d0.c0.00.01
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
Network Configuration With MIP
l Configuration Description
The network configuration with MIP refers to the connected devices as shown inFigure
4-59.
4-142
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Figure 4-59 Single-Domain CFM Network With MIP
l Configuration Procedure
Configuration on S1:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 1
direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 assign port 1
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 2
remote-mac 00.d0.d0.c0.00.03
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
Configuration on S2:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mip-session 1 name zte_mip_1
zte(cfg)#cfm md-session 1 ma-session 2 mip-session 1 assign port 2
zte(cfg)#create cfm md-session 1 ma-session 1 mip-session 2 name zte_mip_1
zte(cfg)#cfm md-session 1 ma-session 2 mip-session 2 assign port 3
Configuration on S3:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 2
direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
4-143
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 assign port 4
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 1
remote-mac 00.d0.d0.c0.00.01
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
4.42 Y.1731 Configuration
Y.1731 Overview
The Y.1731 protocol complements the 802.1ag protocol. It defines a series of extensions
in which CFM (Connection Fault Management) is used to measure the network link status
and performance.
The Y.1731 protocol is used in:
l The error management OAM: AIS (Alarm Indication Signal), LCK (Locked), RDI
(Remote Defect Indication) and functions mentioned in 802.1ag (CCM, LB, LT).
l The performance management OAM: LM (Loss Measurement), and DM (Delay
Measurement).
Y.1731 Configuration
Y.1731 configuration includes the following commands:
Command Function
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191>
Enables the LM function at one end.
one-lm {enable | disable}
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Enables the LM function at both ends.
two-lm {enable | disable}
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Enables the DM function in both
two-dm {enable | disable} directions.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Enables the AIS function.
ais {enable | disable}
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Enables the LCK function.
lck {enable | disable}
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the level that sending the AIS/LCK
client-level <0-7> function to outer layers.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Sets the remote MEP related to local
relate-to rmep-id <1-8191> MEP.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Starts LM detection at one end.
one-lm send-packet [continue-time <60-600> interval <1-60>]
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Stops LM detection at one end.
one-lm send-packet stop
4-144
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
Command Function
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191> Starts DM detection at both ends.
two-dm send-packet [continue-time <60-600> interval <1-60>]
Stops DM detection at both ends.
zte(cfg)#cfm md-session <1-16> ma-session <1-32> mep-id <1-8191>
two-dm send-packet stop
Clears the results of LM detection at
zte(cfg)#clear cfm md-session <1-16> ma-session <1-32> mep-id one end and at both ends, as well
<1-8191>{ one-lm | two-lm | two-dm } as the result of DM detection in both
directions.
zte(cfg)#clear cfm md-session <1-16> ma-session <1-32> mep-id Clears the related remote MEP.
<1-8191> relate-rmep
LM Network Configuration
l Configuration Description
The network configuration is illustrated by using the network instance shown in Figure
4-60.
Figure 4-60 LM Network Configuration Instance
l Configuration Procedure
Configuration on S1:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 1 direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 assign port 1
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 2 remote-mac
00.d0.d0.c0.00.02
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
4-145
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 relate-to rmep-id 2
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 one-lm (two-lm) enable
Configuration on S2:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 2 direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 assign port 4
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 1 remote-mac
00.d0.d0.c0.00.01
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 relate-to rmep-id 1
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 one-lm (two-lm) enable
l Configuration Verification
LM on both ends is automatically performed based on the CCM configuration. While
LM on one end is performed after manually triggering on S1 or S2:
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 (2) one-lm send-packet
View the measurement result by using the command for displaying MEP information
that is provided by 802.1ag.
DM Network Configuration
l Configuration Description
The network configuration is illustrated by using the network instance shown in Figure
4-61.
Figure 4-61 DM Network Configuration Instance
l Configuration Procedure
Configuration on S1:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
4-146
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 1 direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 assign port 1
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 2 remote-mac
00.d0.d0.c0.00.02
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 relate-to rmep-id 2
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 two-dm enable
Configuration on S2:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 2 direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 assign port 4
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 1 remote-mac
00.d0.d0.c0.00.01
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 relate-to rmep-id 1
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 two-dm enable
l Configuration Verification
Manually trigger the test on S1 or S2:
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 (2) one-lm send-packet
View the measurement result by using the command for displaying MEP information
that is provided by 802.1ag.
AIS/LCK Network Configuration
l Configuration Description
The network configuration is illustrated by using the network instance shown in Figure
4-62.
4-147
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-62 AIS/LCK Network Configuration Instance
l Configuration Procedure
Configuration on S1:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 1 direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 assign port 1
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 2 remote-mac
00.d0.d0.c0.00.04
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ais (lck) enable
Configuration on S2:
zte(cfg)# cfm enable
zte(cfg)#create cfm md-session 10 name zte level 4
zte(cfg)#create cfm md-session 10 ma-session 10 name zte_zte
zte(cfg)#cfm md-session 10 ma-session 10 primary-vlan 100
zte(cfg)#create cfm md-session 10 ma-session 10 mep-session 10 mep-id 10 direction down
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 state enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 ccm-send enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 ccm-receive enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 assign port 3
zte(cfg)#create cfm md-session 10 ma-session 10 rmep-session 20 rmep-id 20 remote-mac
00.d0.d0.c0.00.03
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 ccm-receive enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 ais (lck) enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 client-level 5
Configuration on S3:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 10 name zte4 level 4
zte(cfg)#create cfm md-session 10 ma-session 10 name zte_zte
zte(cfg)#cfm md-session 10 ma-session 10 primary-vlan 100
zte(cfg)#create cfm md-session 10 ma-session 10 mep-session 20 mep-id 20 direction down
4-148
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 state enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 ccm-send enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 ccm-receive enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 assign port 5
zte(cfg)#create cfm md-session 10 ma-session 10 rmep-session 10 rmep-id 10 remote-mac
00.d0.d0.c0.00.02
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 10 ccm-receive enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 ais (lck) enable
zte(cfg)#cfm md-session 10 ma-session 10 mep-id 20 client-level 5
Configuration on S4:
zte(cfg)#cfm enable
zte(cfg)#create cfm md-session 1 name zte_1 level 5
zte(cfg)#create cfm md-session 1 ma-session 1 name zte_zte_1
zte(cfg)#cfm md-session 1 ma-session 1 primary-vlan 100
zte(cfg)#create cfm md-session 1 ma-session 1 mep-session 1 mep-id 2 direction down
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 state enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-send enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 2 assign port 6
zte(cfg)#create cfm md-session 1 ma-session 1 rmep-session 2 rmep-id 1 remote-mac
00.d0.d0.c0.00.01
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ccm-receive enable
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 ais (lck) enable
l Configuration Verification
Disconnect the link between S2 and S3. After that, alarms occur on only S2 and S3,
and unrelated alarms on S1 and S4 are restricted due to the AIS function.
zte(cfg)#cfm md-session 1 ma-session 1 mep-id 1 (2) one-lm send-packet
View the measurement result by using the command for displaying MEP information
that is provided by 802.1ag.
4.43 MAC-based VLAN Command Configuration
MAC-based VLAN Overview
MAC-based VLAN decides the VLAN for forwarding an untagged frame based on the
source MAC address of the frame. This technology allows packets to be transmitted in
different VLANs and provides different services to different users.
Configuring MAC-based VLAN
MAC-based VLAN configuration includes the following commands:
4-149
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
zte(mac-based-vlan)#rule <1-1024> mac-address <HH.HH.HH.HH.HH.H Sets a rule for MAC-based VLAN.
H>mac-mask <HH.HH.HH.HH.HH.HH> vlan <1-4094>
zte(mac-based-vlan)#clear rule <1-1024> Clears a rule for MAC-based VLAN.
Sets the binding relation between
zte(cfg)#set vlan mac-based {global |port <portlist>} session
global/port and sessions of MAC-based
<1-64>{bind|unbind}
VLAN.
Displays all rules of all or one session
show vlan mac-based session [<1-64>]
configured for an MAC-based VLAN.
Displays the binding relations between
show vlan mac-based session [<1-64>] bind a port and all or one session configured
for an MAC-based VLAN.
mac based VLAN Configuration Instance
l Configuration Description
Set the following MAC-based VLAN rule for port 1: Assign the VLAN "vlan100"
to all untagged frames whose source MAC address is 00.00.00.00.00.01 and
assign the VLAN "vlan200" to all untagged frames whose source MAC address is
00.d0.d0.00.00.00.
l Configuration Procedure
Configure an MAC-based VLAN instance:
zte(cfg)#set vlan 100,200 enable
zte(cfg)#set vlan 100,200 add port 1 untag
zte(cfg)#set vlan 10,12 add port 1 tag
zte(cfg)#config mac-based-vlan session 1
zte(mac-based-vlan)#rule 1 mac-address 00.00.00.00.00.01 mac-mask ff.ff.ff.ff.ff.ff vlan 100
zte(mac-based-vlan)#rule 2 mac-address 00.d0.d0.00.00.00 mac-mask ff.ff.ff.00.00.00 vlan 200
zte(cfg)#set vlan mac-based port 1 session 1 bind
4.44 DHCP Relay Configuration
DHCP Relay Overview
DHCP Relay interacts with both the Client and Server, acting different roles. From the
view of the DHCP Client, DHCP Relay Agent can be considered as its DHCP Server and
DHCP Relay implements the response to the IP address requests from the Client. For this,
DHCP Relay Agent needs to intercept on the interception port of the DHCP Server. From
the view of the DHCP Server, DHCP Relay Agent can be considered as its DHCP Client
and DHCP Relay initiates IP address requests. For this, the IP address of the interface
through which messages are received must be filled in the Relay Agent field of the DHCP
request messages forwarded by DHCP Relay. The DHCP Server checks the validity of
4-150
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
the Relay Agent domain and allocates an IP address to the DHCP Client that is in the
same subnet as the IP address in accordance with the domain value. This means that
the allocated IP address and the IP address of the interface through which Relay receives
request messages are in the same network segment. At the same time, DHCP Relay
implements the forwarding of the responses from the DHCP Server to the Client.
Configuring the DHCP Relay
DHCP relay configuration includes the following commands:
Command Function
Globally enables/disables the DHCP
zte(cfg)#set dhcp relay{enable | disable}
relay function.
Globally enables/disables the DHCP
zte(cfg)#set dhcp relay option82{enable | disable}
relay option82 function.
zte(cfg)#set dhcp relay option82 sub-option device { ani< string >| remote-ID Sets the switch node device ID.
{cisco | manual < string >}}
zte(cfg)#set dhcp relay option82 sub-option port <1-28> circuit-ID {on Sets the relay option82 suboption.
{cisco | china-tel | dsl-forum| henan-rtf| manual < string >}| off}
Sets the mode in binding the dynamic
set dhcp relay option82 mode port <1-52>{default | drop | modify | append} user information binding table options
for the port.
Sets the DHCP Relay mode, sets the
zte(cfg)#set dhcp relay server mode {ipport | vclass-id} DHCP server depending on ipport or
vclass-id.
Sets the DHCP Relay retry, that is,
zte(cfg)#set dhcp relay server retry <5-1000> the number of times that message
resending to the server is tried.
Sets the server IP address
zte(cfg)#set dhcp relay vclass-id {characters <string>| hex-numbers <
corresponding to the class-id domain of
hex-string>} server <A.B.C.D>
the server.
zte(cfg)#clear dhcp relay vclass-id {characters <string>{ server A.B.C.D}| Clears the configured dhcp relay
hex-numbers <hex-string>{ server A.B.C.D}} vclass-id.
clear dhcp relay option82 sub-option device ani Clears the device ID information.
show dhcp relay Displays the DHCP relay configuration.
Displays the DHCP Relay option60
show dhcp vclass-id
configuration.
zte(cfg)#clear dhcp option82 sub-option device ani Clears the device ID information.
show dhcp relay binding [port <1-28>| trunk <1-15>](all configuration Displays the DHCP relay binding
modes) information.
4-151
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Displays the DHCP relay option82
show dhcp relay option82 port<1-28>(all configuration modes)
configuration of the port.
Displays device-related information,
show dhcp relay option82 device(all configuration modes)
including ANI and remote-ID.
Sets the DHCP relay information of
zte(cfg-router)#set ipport <0-63> dhcp relay {agent | server <A.B.C.D>}
ipport.
Clears the DHCP relay information of
zte(cfg-router)#clear ipport <0-63> dhcp relay {agent | server <A.B.C.D>}
ipport.
DHCP Configuration Instance
l Configuration Description
As shown in Figure 4-63, switch port 1 is connected to the DHCP client, and switch
port 2 is connected to the DHCP server of the IP network.
Figure 4-63 DHCP Relay Configuration Instance
Note:
The DHCP client and the DHCP server are in different network segments.
l Configuration Procedure
1. Assign a specified VLAN to the port:
set vlan 1000 add port 2 tag
set vlan 1000 enable
2. Configure the DHCP relay by using the following commands:
zte(cfg)#set dhcp relay enable
4-152
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 4 Service Configuration
zte(cfg-router)#set ipport 0 ipaddress 169.1.15.1 255.255.0.0
zte(cfg-router)#set ipport 0 vlan 1
zte(cfg-router)#set ipport 0 enable
zte(cfg-router)#set ipport 0 dhcp relay agent
zte(cfg-router)#set ipport 0 dhcp relay server 10.230.72.2
zte(cfg-router)#set ipport 63 ipaddress 10.230.72.1 255.255.255.0
zte(cfg-router)#set ipport 63 vlan 1000
zte(cfg-router)#set ipport 63 enable
l Configuration Verification
zte(cfg)#show dhcp relay
DHCP relay status : enable
DHCP server mode : ipport
DHCP server retry : 10
DHCP relay option82: disable
zte(cfg)#show dhcp relay option82 port 1
DHCP option82 sub-option information on port 1:
Circuit-ID: Disabled
Remote-ID: Enabled
Format: Cisco
DHCP option82 mode information on port 1: Default
zte(cfg)#show ipport 0
Status : up IpAddress : 169.1.15.1
VlanId : 1 Mask : 255.255.0.0
ArpProxy : disabled MacAddress: 00.00.00.11.22.33
Timeout : 600(s) IpMode : static
En/Disable: enabled
Dhcp client configuration as follows:
Class-id : -
Client-id : -
Hostname : -
Lease : -
Clear request: -
Dhcp relay configuration as follows:
Relay agent : enable
Server IP : 10.230.72.2
4-153
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
This page intentionally left blank.
4-154
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5
Management
Table of Contents
REMOTE-ACCESS ....................................................................................................5-1
SSH ...........................................................................................................................5-3
PRIVILEGE ................................................................................................................5-6
SNMP Overview.........................................................................................................5-7
RMON Overview ......................................................................................................5-12
ZGMP ......................................................................................................................5-15
sFlow .......................................................................................................................5-22
WEB.........................................................................................................................5-23
M_Button..................................................................................................................5-43
Telnet .......................................................................................................................5-45
5.1 REMOTE-ACCESS
Remote-Access Overview
Remote-Access is a restrictive mechanism used for network management users to log in
through Telnet, SSH, SNMP and Web, that is, it is used to restrict the access. This function
is to enhance the security of the network management system.
After this function is enabled, specify a network management user to access the switch
only from a specified IP address , the user cannot access the switch from other IP
addresses. When this function is disabled, the network management user can access the
switch through Telnet, SSH, SNMP and Web from any IP address.
Configuring REMOTE-ACCESS
The REMOTE-ACCESS configuration includes the following commands:
Command Function
Enables or disable remote access
zte(cfg)#set remote-access {any | specific}
control function.
zte(cfg)#set remote-access ipaddress <A.B.C.D>[<A.B.C.D>][{snmp Permits or denies the login mode
| telnet | ssh | web}{permit | deny}] of IP address.
Deletes all IP address
zte(cfg)#clear remote-access all
configuration.
5-1
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Deletes the configuration of
zte(cfg)#clear remote-access ipaddress <A.B.C.D>[<A.B.C.D>] specified IP address and segment
address.
Displays the configuration
show remote-access (all configuration modes)
information of REMOTE-ACCESS.
REMOTE-ACCESS Configuration Instance1
l Configuration Description
Only allow the network management user to access the switch from 192.168.1.0/24
through Telnet SSH SNMP Web.
l Configuration Procedure
zte(cfg)#set remote-access specific
zte(cfg)#set remote-access ipaddress 192.168.1.0 255.255.255.0
zte(cfg)#show remote-access
Whether check remote manage address: YES
Allowable remote manage address(es) and application(s):
192.168.1.0/255.255.255.0 snmp, telnet, ssh, web
REMOTE-ACCESS Configuration Instance2
l Configuration Description
Only allow the network management user to access the switch from 192.168.1.1
through Telnet SSH SNMP Web.
l Configuration Procedure
zte(cfg)#set remote-access specific
zte(cfg)#set remote-access ipaddress 192.168.1.1
zte(cfg)#show remote-access
Whether check remote manage address: YES
Allowable remote manage address(es) and application(s):
192.168.1.1/255.255.255.255 snmp, telnet, ssh, web
REMOTE-ACCESS Configuration Instance3
l Configuration Description
Allow the network management user to access the switch from 192.168.1.1 through
Telnet/SSH.
l Configuration Procedure
zte(cfg)#set remote-access specific
zte(cfg)#set remote-access ipaddress 192.168.1.1
zte(cfg)#show remote-access
Whether check remote manage address: YES
Allowable remote manage address(es) and application(s):
5-2
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
192.168.1.1/255.255.255.255 snmp, telnet, ssh, web
zte(cfg)#set remote-access ipaddress 192.168.1.1 255.255.255.255 snmp deny
zte(cfg)#set remote-access ipaddress 192.168.1.1 255.255.255.255 web deny
zte(cfg)#show remote-access
Whether check remote manage address: YES
Allowable remote manage address(es) and application(s):
192.168.1.1/255.255.255.255 telnet,ssh
5.2 SSH
SSH Overview
The secure shell (SSH) is a protocol created by Network Working Group of the IETF, which
is used to offer secure remote access and other secure network services over an insecure
network.
The purpose of the SSH protocol is to solve the security problems in interconnected
networks, and to offer a securer substitute for Telnet and Rlogin (Although the present
development of the SSH protocol has far exceeded the remote access function scope),
therefore, the SSH connection protocol shall support interactive session.
The SSH can be used to encrypt all transmitted data. Even if these data is intercepted, no
useful information can be obtained.
At present, the SSH protocol has two incompatible versions: SSH v1.x and SSH v2.x.
This switch only supports SSH v2.0 and uses the password authentication mode. The
SSH uses port 22.
Configuring SSH
The SSH configuration includes the following commands:
Command Function
zte(cfg)#set ssh {enable | disable} Enables or disables SSH.
zte(cfg)#set ssh regenerate Generates a new SSH key.
Displays the SSH configuration
show ssh (all configuration modes)
and status.
SSH Configuration Instance
l Configuration Description
As shown in Figure 5-1, one host attempts to access the switch through SSH. The
switch is configured with a layer-3 port. The IP address of the port is 192.1.1.1/24,
and the IP address of the host is 192.1.1.100/24.
5-3
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-1 SSH CONFIGURATION EXAMPLE
l Configuration Procedure
1. The specific configuration of the switch is as follows:
zte(cfg)#set ssh enable
zte(cfg)#show ssh
SSH is enabled.
There's no ssh user logging in this system.
2. The client end setting of host:
The client end of SSH v2.0 can use the free software Putty developed by Simon
Tatham . The current version provides client end support of Putty0.54 version.
The required settings when using Putty to log in to switch are as follows.
a. Set the IP address and port number of the SSH Server, as shown in Figure
5-2.
Figure 5-2 SETTING IP ADDRESS AND PORT NUMBER OF THE SSH
SERVER
5-4
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
b. Set the SSH version number, as shown in Figure 5-3.
Figure 5-3 SETTING SSH VERSION NUMBER
c. For the first time to log in, the user confirmation is needed, as shown in Figure
5-4.
Figure 5-4 USER CONFIRMATION REQUIRED IN THE FIRST LOGIN
d. The SSH login result is shown in Figure 5-5.
5-5
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-5 SSH LOGIN RESULT
5.3 PRIVILEGE
PRIVILEGE Overview
The command level function, or the privilege function, refers to leveling the command lines
available for the switches and granting different permissions. With this function, users
of different levels can access the commands of different scopes. This protects switch
configuration from being modified by any user with any permission.
PRIVILEGE Configuration
PRIVILEGE configuration includes the following commands:
Command Function
Enables/disables the command
zte(cfg)#privilege {enable | disable}
level function.
zte(cfg)#privilege <0-15> session <1-1024>{all | Sets the command permission.
part}<mode><key1-string>[<key2-string>[... <key10-string>]]
Clears a specified command
zte(cfg)#clear privilege session [<1-1024>]
permission rule.
show privilege {default | level [<0-15>]| session [<1-1024>]} (for Displays a specified command
all configuration modes) permission rule.
PRIVILEGE Configuration Instance
l Configuration Description
Users can perform this configuration only when logging in to the switch with the highest
permission (Level 15).
5-6
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
l Configuration Procedure
Configure the switch:
/*Enable privilege function*/
zte(cfg)#privilege enable
/*Grant Level-12 permission to all functions of the set node*/
zte(cfg)#privilege 12 session 1 part cfg set
l Verifying the Configuration
1. Execute the following command to verify the command permission rule.
zte(cfg)#show privilege session
State: Enable
User level: 15
Session Level Type Mode Key
------- ----- ---- ------------- -----------------
1 12 part cfg set
2. Log in to the switch and use the related set command as a user with a lower
permission (for example, Level 11).
Execute the zte(cfg)#set stp enable command. The system will prompt that the
user is not allowed to use the command.
The user privilege(level 11) is less than command privilege(level 12 rule 1).
% Command cannot be performed because of insufficient privilege. (0x40000aab)
Log in to the switch as a user with a permission higher than or equal to the
permission (for example, Level 13) and use the same command. The command
can be properly executed, without the prompt mentioned above occurring.
5.4 SNMP Overview
SNMP
SNMP is the most popular network management protocol currently. It involves a series of
protocol and specifications:
l MIB: Management Information Base
l SMI: Structure of Management Information
l SNMP: Simple Network Management Protocol
They offer the means to collect network management information from network devices.
SNMP also enables devices to report problems and errors to network management
stations. Any network administrator can use SNMP to manage switches. ZXR10 2900E
supports SNMPv1, v2c and v3(v3 strengthens SNMP management security based on v1
and v2c).
SNMP adopts the “Management process—Agent process” model to monitor and control
all types of managed network devices. The SNMP network management needs three key
elements:
5-7
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
1. Managed devices, which can communicate over the Internet. Each device contains
an agent.
2. NMS, The network management process shall be able to communicate over the
Internet.
3. The protocol used for the exchange of management information between the switching
agent process and the NMS, that is, SNMP.
An NMS collects data by polling the agents that reside in the managed devices. The agents
in the managed devices can report errors to NMSs at any time before the NMSs poll them.
These errors are called traps. When a trap occurs to a device, the NMS can be used to
query the device (suppose it is reachable) and obtain more information. Snmp v2c and
v3 also support inform (a SNMPv2 Trap that need response) to inform abnormal events to
NMS. If receives inform message NMS will send a acknowledgement packet to switch. If
switch hasn’t received acknowledgement packet from NMS in a period time it will resend
the original inform message twice.
All variables in the network are stored in the MIB. SNMP monitors network device status
by querying the related object values in the agent MIB. ZXR10 2900E implements the
standard MIB and private MIB defined in rfc2233, rfc1493, rfc2665 and rfc2819.
Configuring SNMP
The SNMP configuration includes the following commands:
Command Function
zte(cfg-snmp)#set engineID Sets device SNMP engine ID.
Sets the number of SNMP packets
zte(cfg-snmp)#set recvpacket <0-100> that SNMP protocol stack can
handle.
Creates a community name, sets
zte(cfg-snmp)#create community <string>{public | the access authority, and binds a
private}[ingress-acl-basic-number <1-99>] basic acl ID with the community
name.
Creates a view name. The default
zte(cfg-snmp)#create view < string >[{include | exclude}<mib-oid>] setting is include, which includes
mib subtree.
Sets specific community name
zte(cfg-snmp)#set community <string> view <string>
that the view contains.
zte(cfg-snmp)#set community <string> ingress-acl-basic-nu Sets the basic ACL number bound
mber <1-99> to the specified community.
zte(cfg-snmp)#clear community <string> ingress-acl-basic-num Deletes the basic ACL number
ber bound to the specified community.
Enables or disables 1493
zte(cfg-snmp)#set mib1493compatible {enable | disable}
compatible mode.
5-8
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Command Function
Sets IP address, group name,
zte(cfg-snmp)#set host <A.B.C.D> trap {v1 <string>| v2c <string>|
username and version of trap host
v3 <string>{auth | noauth | priv}}
and inform host.
zte(cfg-snmp)#set host <A.B.C.D> inform { v2c <string>| v3 Sets host IP address, group name,
<string>{auth | noauth | priv}} username and version of inform.
zte(cfg-snmp)#set trap {linkdown | linkup | authenticationfail Enables/disables the function to
| coldstart | warmstart | topologychange | memberupdown trap link connection/disconnection,
| portloopdetect | trunkloopdetect | linkMonitorStatus | authentication failure, cool/hot
remoteLinkStatus | dyingGaspStatus | remoteDiscovery | start/topology change, trunk
powerDown | dhcpCharCheck | cpuUserationThreshold | member UP/DOWN, loopback
memUserationThreshold | fanStatusCheck | macNotification | detected at port/Trunk, MAC
udldUnidirectional | protocolProtect | dismanpingnotifications| number exceeding the threshold,
adminPasswordNoChange | arpOverload | bootfileLost link monitor event alarms, remote
| cfmFaultAlarm | fanSpeed | fileTransfer | ipConflict | link event alarms, event detection
MacOverload | poe | StpBridgeRoleChange | StpPortStateChange alarms, MAC list variation
| temperature | all}{enable | disable} notification, and ping notification.
zte(cfg-snmp)#set group <string> v3 {auth | noauth | priv}[read Sets the SNMP V3 group name
<string>[write <string>[notify <string>]]] and group security level.
zte(cfg-snmp)#set user <string><string> v3 [md5-auth <string>| Sets SNMP v3 user name,
sha-auth <string>[des56-priv <string>]] authentication mode and password
Enables or disables MAC change
zte(cfg-snmp)#set trap macnotification {port<1-51>|
notification function on a specific
trunk<1-15>}{enable|disable}
port or trunk.
zte(cfg-snmp)#set trap macnotification {history-size<1-256>| Sets the number and interval of
interval<1-3600>} MAC change notifications.
zte(cfg-snmp)#clear host <A.B.C.D>{trap | inform}<string> Clears a host configuration.
zte(cfg-snmp)#clear community <string> Clears a community name.
zte(cfg-snmp)#clear view <string> Clears a view.
zte(cfg-snmp)#clear group <string> v3 {auth | noauth | priv} Clears a group.
zte(cfg-snmp)#clear user <string> v3 Clears a user.
Clears SNMP engine identifier and
zte(cfg-snmp)#clear engineID
recovers default value.
Displays all SNMP configuration
show snmp (all configuration modes)
information.
show snmp {community | engineID | group | host | trap | user | Displays each element of SNMP
view} (all configuration modes) V1, V2C and V3.
5-9
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
SNMP Configuration Instance1
l Configuration Description
Suppose that the IP address of the network management server is 10.40.92.105,
the switch has a layer-3 port with the IP address of 10.40.92.200, and the switch
is managed through the network management server.
Create a community named “zte” with the read/write authority and the view named
“vvv”, and then associate the community “zte” with the view “vvv”. Specify the IP
address of the host receiving traps as 10.40.92.105, and the community as “zte”.
l Network
DTU device is directly connected with network management server PC.
l Configuration Procedure
zte(cfg)#config router
zte(cfg-router)#set ipport 0 ipaddress 10.40.92.200 255.255.255.0
zte(cfg-router)#set ipport 0 vlan 2
zte(cfg-router)#set ipport 0 enable
zte(cfg-router)#exit
zte(cfg)#config snmp
zte(cfg-snmp)#create community zte private
zte(cfg-snmp)#create view vvv
zte(cfg-snmp)#set community zte view vvv
zte(cfg-snmp)#set host 10.40.92.105 trap v2 zte
zte(cfg-snmp)#show snmp community
CommunityName Level ViewName Acl
-------------- ------- ------------ ---
zte private vvv -
zte(cfg-snmp)#show snmp view
ViewName Exc/Inc MibFamily
--------- -------- ------------------------
vvv Include 1.3.6.1
zte(cfg-snmp)#show snmp host
HostIpAddress Comm/User Version type SecurityLevel
-------------- ---------- ------- ------ -------------
10.40.92.105 zte Ver.2c Trap
SNMP Configuration Instance2
l Configuration Description
5-10
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Suppose that the IP address of the network management server is 10.40.92.77, the
switch has a layer-3 port with the IP address of 10.40.92.11, and the switch is managed
through the network management server.
Create a user named “zteuser” and the group named “ztegroup”, the security level of
this group is private ( that is authentication and encryption ). Specify the IP address
of the host receiving trap or inform as 10.40.92.77, and the user is“zteuser”.
l Switch Configuration
zte(cfg)#config router
zte(cfg-router)#set ipport 1 ipaddress 10.40.92.11/24
zte(cfg-router)#set ipport 1 vlan 1
zte(cfg-router)#set ipport 1 enable
zte(cfg-router)#exit
zte(cfg)#config snmp
zte(cfg-snmp)#set group ztegroup v3 priv
zte(cfg-snmp)#set user zteuser ztegroup v3 md5-auth zte des56-priv zte
zte(cfg-snmp)#set host 10.40.92.77 inform v3 zteuser priv
zte(cfg-snmp)#show snmp group
groupName: ztegroup
secModel : v3 readView : zteView
secLevel : AuthAndPriv writeView : zteView
rowStatus: Active notifyView: zteView
zte(cfg-snmp)#show snmp user
UserName : zteuser
GroupName : ztegroup(v3)
EngineID : 830900020300010289d64401
AuthType : Md5 StorageType: NonVolatile
EncryptType: Des_Cbc RowStatus : Active
zte(cfg-snmp)#show snmp host
HostIpAddress Comm/User Version type SecurityLevel
---------------- ----------- ------- ------ -------------
10.40.92.77 zteuser Ver.3 Inform AuthAndPriv
l Configuration Result
When the configuration is completed, use mibbrowser software to login.
SNMP Configuration Instance3
l Configuration Description
This example describes how to configure the MAC change advertisement function.
As shown in Figure 5-6, configure SNMP first so that the switch can be managed
through the network management server. Configure the MAC advertisement function
5-11
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
so that the MAC change information on Port 1 can be reported to the network
management system. The report condition is: The number of changed MAC entities
reaches 50, or the time is one minute (that is, 60 seconds).
Figure 5-6 MAC Change Advertisement Configuration Instance
l Configuration Procedure
zte(cfg-snmp)#set trap macnotification enable
zte(cfg-snmp)#set trap macnotification port 1 enable
zte(cfg-snmp)#set trap macnotification history-size 50
zte(cfg-snmp)#set trap macnotification interval 60
l Configuration Verification
If the number of changed MAC entities reaches 50 within one minute, the switch
sends trap information when the number reaches 50 instead of waiting until one
minute. The number of entities sent is 50. If the number of changed MAC entities
does not reach 50 within one minute, the switch sends trap information after when one
minute expires. The number of entities sent is less than or equal to 50. By default,
the MAC change advertisement function is disabled. Therefore, if the MAC change
advertisement function is enabled globally but it is not enabled on a related port, the
network management system cannot receive trap information. In this example, if the
MAC entities change on another port instead of Port 1, trap information is not sent.
5.5 RMON Overview
RMON
The Remote Monitoring (RMON) defines standard network monitoring function and the
communication interface between the management console and the remote monitor.
RMON offers an efficient and high availability method to monitor the behaviors of subnets
in case of reducing the load of other agents and management stations.
RMON specifications refer to the definition of RMON MIB. ZXR10 2900E supports four
groups of RMON MIB.
l History: records the periodic statistics sample of the information that can be obtained
from the statistics group.
l Statistics: maintains the basic application and error statistics of each subnet that the
agent monitors.
l Event: it is a table related to all events generated by RMON agents.
l Alarm: allows operators of the management console to set sampling interval and
alarm threshold for any count or integer recorded by RMON agents.
5-12
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
All these groups are used to store the data collected by the monitor and the derived data
and statistics. The alarm group is based on the implementation of the event group. These
data can be obtained through the MIB browser.
The RMON control information can be configured through the MIB browser, and a
HyperTerminal or remote Telnet command line. The RMON sampling information and
statistics are obtained through the MIB browser.
Configuring RMON
The RMON configuration includes the following commands:
Command Function
Enables or disables RMON
zte(cfg-snmp)#set rmon {enable | disable}
function.
zte(cfg-snmp)#set statistics <1-65535>{datasource <1-28>|
owner <name>| status {valid | underCreation | createRequest Sets statistics group.
| invalid}}
zte(cfg-snmp)#set alarm <1-65535>{interval <1-65535>| variable
<mib-oid>| sampletype {absolute | delta}| startup {rising | falling
| both}| threshold <1-65535> eventindex <1-65535>{rising Sets alarm group.
| falling}| owner <name>| status {valid | underCreation |
createRequest | invalid}}
zte(cfg-snmp)#set event <1-65535>{description <string>| type
{none | log | snmptrap | logandtrap}| owner <name>| community Sets event group.
<name>| status {valid | underCreation | createRequest | invalid}}
zte(cfg-snmp)#set history <1-65535>{datasource <1-28>|
bucketRequested <1-65535>| owner <name>| interval Sets history group.
<1-3600>| status {valid | underCreation | createRequest | invalid}}
Displays RMON global
show rmon (all configuration modes)
configuration.
Displays the configuration
show statistics [<1-65535>] (all configuration modes)
information of statistics group.
Displays the configuration
show alarm [<1-65535>] (all configuration modes)
information of alarm group.
Displays the configuration
show event [<1-65535>] ( all configuration modes)
information of event group.
Displays the configuration
show history [<1-65535>] (all configuration modes)
information of history group.
RMON Configuration Instance
l Configuration Description
5-13
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
The following examples describe how to set event 2, history 2, alarm 2 and statistics
1 respectively.
l Network
DUT device is directly connected with network management server PC.
l Switch Configuration
zte(cfg-snmp)#set event 2 description It'sJustForTest!!
zte(cfg-snmp)#set event 2 type logandtrap
zte(cfg-snmp)#set event 2 community public
zte(cfg-snmp)#set event 2 owner zteNj
zte(cfg-snmp)#set event 2 status valid
zte(cfg-snmp)#set history 2 datasource 16
zte(cfg-snmp)#set history 2 bucket 3
zte(cfg-snmp)#set history 2 interval 10
zte(cfg-snmp)#set history 2 owner zteNj
zte(cfg-snmp)#set history 2 status valid
zte(cfg-snmp)#set rmon enable
zte(cfg-snmp)#set alarm 2 interval 10
zte(cfg-snmp)#set alarm 2 variable 1.3.6.1.2.1.16.2.2.1.6.2.1
zte(cfg-snmp)#set alarm 2 sample absolute
zte(cfg-snmp)#set alarm 2 startup rising
zte(cfg-snmp)#set alarm 2 threshold 8 eventindex 2 rising
zte(cfg-snmp)#set alarm 2 threshold 15 eventindex 2 falling
zte(cfg-snmp)#set alarm 2 owner zteNj
zte(cfg-snmp)#set alarm 2 status valid
zte(cfg-snmp)#set statistics 1 datasource 16
zte(cfg-snmp)#set statistics 1 owner zteNj
zte(cfg-snmp)#set statistics 1 status valid
l Configuration Verification
1. View configuration information about event 2:
zte(cfg-snmp)#show event 2
EventIndex : 2 Type : log-and-trap
Community : public Status : valid
Owner : zteNj
Description :It'sJustForTest!!
2. View configuration information about history 2:
zte(cfg-snmp)#show history 2
ControlIndex : 2 BucketsRequest: 3
Interval : 10 BucketsGranted: 3
ControlStatus: valid ControlOwner : zteNj
DataSource : 1.3.6.1.2.1.2.2.1.1.16
5-14
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
3. View configuration information about alarm 2:
zte(cfg-snmp)#show alarm 2
AlarmIndex : 2 SampleType: absolute
Interval : 10 Value : 16
Threshold(R) : 8 Startup : risingAlarm
Threshold(F) : 15 Status : valid
EventIndex(R): 2 Variable : 1.3.6.1.2.1.16.2.2.1.6.2.1
EventIndex(F): 2 Owner : zteNj
4. View configuration information about statistics 1:
zte(cfg-snmp)#show statistics 1
StatsIndex: 1
DropEvents : 0 BroadcastPkts : 0
Octets : 0 MulticastPkts : 0
Pkts : 0 Pkts64Octets : 0
Fragments : 0 Pkts65to127Octets : 0
Jabbers : 0 Pkts128to255Octets : 0
Collisions :0 Pkts256to511Octets : 0
CRCAlignErrors :0 Pkts512to1023Octets : 0
UndersizePkts :0 Pkts1024to1518Octets: 0
OversizePkts :0 DataSource(port) : 1.3.6.1.2.1.2.2.1.1.16
Status : valid Owner : zteNj
l Configuration Result
After the above configuration, when the number of etherHistoryPkts of the first bucket
of port 16 rises over 8 or the number falls below 15, the event with the index of 2 is
triggered. The event with the index of 2 sends a trap to the management station.
5.6 ZGMP
ZGMP Overview
ZGMP is ZTE Group Manage Protocol. A cluster is a combination consisting of a set of
switches in a specific broadcast domain. This set of switches forms a unified management
domain, providing an external public network IP address and management interface, as
well as the ability to manage and access each member in the cluster.
The management switch which is configured with a public network IP address is called a
command switch. Other switches serve as member switches. In normal cases, a member
switch is not configured with a public network IP address. A private address is allocated
to each member switch through the class DHCP function of the command switch. The
command switch and member switches form a cluster (private network).
In general, the broadcast domain where a cluster is located consists of switches in these
roles: Command switch, member switches, candidate switches and independent switches.
One cluster has only one command switch. The command switch can automatically collect
the device topology and set up a cluster. After a cluster is set up, the command switch
5-15
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
provides a cluster management channel to manage member switches. Member switches
serve as candidate switches before they join the cluster. The switches that do not support
cluster management are called independent switches.
It is recommended that you isolate the broadcast domain between the public network
and the private network on the command switch and shield direct access to the private
address. The command switch provides an external management and maintenance
channel to manage the cluster in a centralized manner.
Figure 5-7 shows the cluster management networking.
Figure 5-7 CLUSTER MANAGEMENT NETWORKING
Figure 5-8 shows the changeover rule of the four roles of switches within a cluster.
5-16
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-8 Switch Character Switch Rule
Configuring ZGMP
The ZGMP configuration includes the following commands:
Command Function
zte(cfg-group)#set zdp {enable | disable} Enables or disables ZDP function.
zte(cfg-group)#set zdp {port <portlist>| trunk <trunklist>}{enable | Enables or disables the ZDP
disable} function based on port/trunk.
Sets the time interval for sending
zte(cfg-group)#set zdp timer <5-255>
ZDP packets.
zte(cfg-group)#set zdp holdtime <10-255> Sets ZDP holdtime.
show zdp (all configuration modes) Displays ZDP global configuration.
Displays ZDP neighbor
show zdp neighbour (all configuration modes)
information.
Displays ZDP neighbor detailed
show zdp neighbour detail (all configuration modes)
information.
Enables or disables the global
zte(cfg-group)#set ztp {enable | disable}
ZTP function.
zte(cfg-group)#set ztp {port <portlist>| trunk <trunklist>}{enable | Enables or disables the ZTP
disable} function based on port/trunk.
Sets a VLAN for collecting
zte(cfg-group)#set ztp vlan <1-4094>
topology information.
Sets the range (hop count) of
zte(cfg-group)#set ztp hop <1-128>
collecting topology information.
Sets time interval for collecting
zte(cfg-group)#set ztp timer
topology information periodically
5-17
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Sets the port delay for forwarding
zte(cfg-group)#set ztp portdelay <1-100>
topology requests.
Sets the hop delay for forwarding
zte(cfg-group)#set ztp hopdelay <1-1000>
topology requests.
Starts collecting topology
zte(cfg-group)#ztp start
information.
show ztp (all configuration modes) Displays ZTP configuration.
Displays the configuration
show ztp device [<idlist>](all configuration modes) information of ZTP according to
the device ID.
Displays network topology by
show ztp topology (all configuration modes)
simple graph.
Displays detail information of
show ztp mac <HH.HH.HH.HH.HH.HH> (all configuration modes) specified device according to MAC
address.
Sets a command switch, specifies
zte(cfg-group)#set group commander ipport <0-63>[ip-pool a layer-3 port number for cluster
<A.B.C.D/M>] management and sets IP address
pool for user cluster management.
zte(cfg-group)#set group candidate Sets a switch as candidate switch.
Sets a switch as independent
zte(cfg-group)#set group independent
switch.
zte(cfg-group)#set group add {mac <HH.HH.HH.HH.HH.HH>[<1- Adds a device with specified
255>]| device <idlist>} member ID from cluster.
Deletes a device with specified
zte(cfg-group)#set group delete member <idlist>
member ID from cluster.
Sets a time interval for handshake
zte(cfg-group)#set group handtime <1-300> between command switch and
member switch.
Sets effective holding time of
zte(cfg-group)#set group holdtime <1-300> information about switches in
cluster.
zte(cfg-group)#set group name <name> Sets cluster name.
Sets the protocol broadcast
zte(cfg-group)#set group mac-mode {standard | extend [mac
address mode of cluster
<HH.HH.HH.HH.HH.HH>]}
management as standard mode.
Sets IP address of internal public
zte(cfg-group)#set group syslogsvr <A.B.C.D>
SYSLOG Server of cluster.
5-18
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Command Function
Sets IP address of internal public
zte(cfg-group)#set group tftpsvr <A.B.C.D>
TFTP Server of cluster.
Displays cluster configuration
show group (all configuration modes)
information.
Displays candidate switches
show group candidate (all configuration modes)
information.
Displays cluster member switches
show group member [<1-255>] (all configuration modes)
information.
Saves configuration of specified
zte(cfg-group)#save member {<idlist>| all}
member switch.
Deletes configuration of specified
zte(cfg-group)#erase member {<idlist>| all}
member switch.
Restarts a specified member
zte(cfg-group)#reboot member {<idlist>| all}
switch.
rlogin {commander | member <1-255>}(all configuration modes) Remotely logs in to cluster device.
ZGMP Configuration Instance
l Configuration Description
As shown in Figure 5-9, the initial configuration of the switches is the default
configuration. Here, set the VLAN where the public network IP address of the
command switch in the cluster is located to 2525, the IP address to 100.1.1.10/24,
the gateway address to 100.1.1.1, the cluster management VLAN to 4000, the private
address pool to 192.168.1.0/24, and the IP address of the TFTP Server of the whole
cluster to 110.1.1.2.
5-19
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-9 CLUSTER MANAGEMENT NETWORKING
l Configuration Procedure
1. Configure the public network IP address of the command switch and the gateway.
zte(cfg)#set vlan 2525 enable
zte(cfg)#set vlan 2525 add port 1-24 tag
zte(cfg)#config router
zte(cfg-router)#set ipport 25 ipaddress 100.1.1.10/24
zte(cfg-router)#set ipport 25 vlan 2525
zte(cfg-router)#set ipport 25 enable
zte(cfg-router)#iproute 0.0.0.0/0 100.1.1.1
2. Create a cluster on layer-3 port 1 of the command switch and VLAN 1 (default
VLAN).
zte(cfg)#config group
zte(cfg-group)#set group commander ipport 1
Cmdr.zte(cfg-group)#ztp start
5-20
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Cmdr.zte(cfg-group)#show ztp device
Last collection vlan : 1
Last collection time : 210 ms
Id MacAddress Hop Role HostName Platform
-- ------------------ ---- ------ --------- ---------------
0 00.00.00.00.00.01 0 cmdr Cmdr.zte ZXR10 2928E
1 00.0d.0d.f1.e2.00 1 candi zte ZXR10 2918E
2 00.50.43.3c.3b.5d 1 candi zte ZXR10 2910E-PS
3 00.00.00.00.33.33 2 candi zte ZXR10 2918E
Cmdr.zte(cfg-group)#set group add device 1-3
Adding device id : 1 ... Successed to add member!
Adding device id : 2 ... Successed to add member!
Adding device id : 3 ... Successed to add member!
Cmdr.zte(cfg-group)#show group member
Id MacAddress IpAddress HostName State
-- ------------------ --------------- --------- -----
1 00.0d.0d.f1.e2.00 192.168.1.2/24 Mem1.zte Up
2 00.50.43.3c.3b.5d 192.168.1.3/24 Mem2.zte Up
3 00.00.00.00.33.33 192.168.1.4/24 Mem3.zte Up
3. Switch to each member switch and add all ports to VLAN 4000 (taking member 4
as an example).
Cmdr.zte(cfg)#set vlan 4000 enable
Cmdr.zte(cfg)#set vlan 4000 add port 1-16 tag
Cmdr.zte(cfg)#rlogin member 1
Trying ...Open
Connecting ...
Mem1.zte>
Mem1.zte>enable
password:
Mem1.zte (cfg)#set vlan 4000 enable
Mem1.zte (cfg)#set vlan 4000 add port 1-16 tag
4. Delete the cluster created on VLAN 1.
Cmdr.ZTE(cfg-group)#set group delete member 1-3
Deleting member id : 1 ... Successed to del member!
Deleting member id : 2 ... Successed to del member!
Deleting member id : 3 ... Successed to del member!
Cmdr.zte(cfg-group)#set group candidate
zte(cfg-group)#
5. Create a cluster on VLAN 4000.
zte(cfg-group)#set ztp vlan 4000
zte(cfg-group)#set group commander ipport 1
Cmdr.zte(cfg-group)#ztp start
Cmdr.zte(cfg-group)#show ztp device
Last collection vlan : 4000
Last collection time : 230 ms
5-21
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Id MacAddress Hop Role HostName Platform
-- ------------------ ---- ------ --------- --------------
0 00.00.00.00.00.01 0 cmdr Cmdr.zte ZXR10 2928E
1 00.0d.0d.f1.e2.00 1 candi zte ZXR10 2918E
2 00.50.43.3c.3b.5d 1 candi zte ZXR10 2910E-PS
3 00.00.00.00.33.33 2 candi zte ZXR10 2918E
Cmdr.zte(cfg-group)#set group add device 1-3
Adding device id : 1 ... Successed to add member!
Adding device id : 2 ... Successed to add member!
Adding device id : 3 ... Successed to add member!
Cmdr.zte(cfg-group)#show group member
Id MacAddress IpAddress HostName State
-- ------------------ --------------- --------- -----
1 00.0d.0d.f1.e2.00 192.168.1.2/24 Mem1.zte Up
2 00.50.43.3c.3b.5d 192.168.1.3/24 Mem2.zte Up
3 00.00.00.00.33.33 192.168.1.4/24 Mem3.zte Up
6. Set the IP address of the TFTP Server in the cluster to 110.1.1.2.
Cmdr.zte(cfg-group)#set group tftpsvr 110.1.1.2
7. Set the IP address of the SYSLOG Server in the cluster to 110.1.1.2.
Cmdr.zte(cfg-group)#set group syslogsvr 110.1.1.2
8. Download version zImage on member 1.
Mem1.zte(cfg-tffs)#tftp commander download zImage
5.7 sFlow
sFlow Overview
sFlow Overview is a technique to monitor high speed data transmission network. It uses
sFlow proxy embedded in network equipments to send the sampled data packets to the
sFlow collectors.
sFlow implements the following functions:
l Provide the correct statistics about client flow.
l Monitor intrusion and police violation to make the network more safer.
l Monitor the network traffic and application visually.
l Provide the correct data suitable for capacity deployment.
l Ensure the priority of traffic across core network.
l Recognize the network application flow from the remote site to ensure the effect on
server.
Configuring sFlow
The sFlow configuration includes the following commands:
Command Function
zte(cfg)#set sFlow agent-address <A.B.C.D> Sets proxy IP address of sFlow.
5-22
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Command Function
zte(cfg)#set sFlow collector-address <A.B.C.D> Sets IP address of sFlow collector.
Enables or disables ingress/egress
zte(cfg)#set sFlow {ingress | egress}{enable | disable}
sFlow function.
Sets sampling mode on
zte(cfg)#set sFlow {ingress | egress} reload-mode {continue | cpu}
ingress/egress direction.
Sets sampling rate on
zte(cfg)#set sFlow {ingress | egress} port <portlist> packet-sample
ingress/egress direction of
{off | frequency <2-16000000>}
gigabit port.
Sets the packet range on ingress
zte(cfg)#set sFlow ingress sample-mode {all | forward}
direction.
Clears all sFlow configuration and
zte(cfg)#clear sFlow config
recovers as default state.
Clears sFlow port sampling
zte(cfg)#clear sFlow statistic
statistics.
Displays sFlow configuration
show sFlow (all configuration modes)
information.
5.8 WEB
WEB Management Overview
ZXR10 2900E provides an embedded Web server stored in flash memory, which allows
user to use a standard Web browser (it is recommended to use IE6.0 above and 1024×768
resolution) for managing remote switch.
Configuring System Login
On the condition that WEB connection has been configured on the switch .
1. Open Microsoft Internet Explore.
2. Enter the IP address of the switch in the address bar (this address is that switch can
connect) to open the system login interface, as shown in Figure 5-10.
5-23
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-10 System Login Interface
3. Enter legal username and password, and select user privilege. Admin user needs to
enter login password and management password. Guest users only need to enter
login password. Click Login to login in to the system main interface, as shown in
Figure 5-11.
Figure 5-11 System Main Interface
WEB Configuration Management
l WEB Configuration Management
System Information Check
Click directory tree on the left of system main page, Configuration > System, open
system information page (by default, Configuration directory is expansive), as shown
in Figure 5-12.
5-24
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-12 System Information Page
This page displays the following system information:
Parameter Description
VersionNumber version number
SwitchType switch type
VersionMakeTime version making time
MacAddress switch hardware address
HostName system name
SysLocation system location
SysUpTime the running time after the system is started
Both “HostName” and “SysLocation” can be configured. After configuration, click
the Apply button to submit to complete the configuration.
l Port Management
Port State Information Check
Click directory tree on the left of system main page, Configuration > Port > Port
State, open port state information page as shown in Figure 5-13 .
5-25
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-13 Port State Information Page
This page displays the following information of port:
Parameter Description
PortClass port class
LinkState port linkup|linkdown state
Duplex duplex working state of port
Speed working speed of port
Note:
Linkdown of port means that port hasn’t physical connection. The displaying values
of “Duplex” and “Speed” are meaningless.
Port Configuration Information Check
Click directory tree on the left of main page, Configuration > Port > Port Parameter,
open port configuration information page, as shown in Figure 5-14.
5-26
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-14 Port Configuration Information Page
This page displays the following information of port:
Parameter Description
MediaType port media type
Name port name
AdminStaus port enable
AutoNeg port working mode, that is , working speed and
duplex mode
PVID port default VLAN ID
FlowControl port flow control enable
MultiFilter port multicast filter enable
MacLimit port Mac address learning limit
Security port security enable
SpeedAdvertise port speed advertisement
Single Port Configuration
Single port configuration: click the Config button in the line of port to be configured
in port configuration information page list to open configuration page of this port, as
shown in Figure 5-15.
5-27
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-15 Single Port Configuration Page
Configure the attribute of the selected port in this page, after configuration, click the
Apply button to complete the configuration.
Note:
“Security” and “MacLimit” are conflicting. Therefore the two attributes can’t be
configured enabled at the same time.
Caution!
Note: If the port connects the network management host is shutdown network
management will be interrupted.
Bulk port configuration
Bulk port configuration: select multiple ports in port configuration information page
list (select Select All to select all ports), and then click Apply to open bulk port
configuration page, as shown in Figure 5-16.
5-28
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-16 Bulk Port Configuration Page
Click the check box before attribute to select the attribute to be configured in this page,
and then click Apply to submit to complete the configuration.
l VLAN Management
VLAN Information Check
Click directory tree on the left of main page, Configuration > VLAN > Vlan
Overview, open VLAN information page to display the VLAN information which
is operated currently. If the VLAN hasn't been operated the default VLAN will be
displayed. Refer to Figure 5-17.
Figure 5-17 VLAN Information Page
When VLAN entry to be displayed is more than 20, it will be displayed by page and
page number will prompted at bottom right corner of page. When the number of page
is more than one page, click previous or next to switch page or select page number
in GO drop-down box.
5-29
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
The Description of Information Displayed
Parameter Description
VlanName VLAN name
AdminStatus VLAN enable
Tag Ports port with tag in VLAN
UntagPorts port without tag in VLAN
TagTrunks trunk with tag in VLAN
UntagTrunks trunk without tag in VLAN
Checking the Specified VLAN Information
View specific VLAN information: select [Input] in VLAN information page, and then
enter VLAN number in the following text box, such as "1,3-5" or select [All]. Click
[Apply] to submit to get the corresponding VLAN information.
1. Click directory tree Configuration > VLAN > Vlan Configure on the left of main
page, open VLAN number entering page, as shown in Figure 5-18.
Figure 5-18 VLAN Number Entering Page
2. Enter VLAN number in VLAN number page( such as "1, 3-5"), click Apply to
enter single VLAN configuration or bulk VLAN configuration page, respective
description are as follows:
à Figure 5-19 shows the single VLAN configuration interface.
5-30
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-19 Single VLAN Configuration Page
After setting some attributes of VLAN in this page, click Apply to complete
the configuration.
Note:
When configuring port/Trunk in VLAN, enter port/Trunk number in the
following text box, the format is as "1,3-5". Also can select the corresponding
check box to add them into VLAN.
à Figure 5-20 shows bulk VLAN configuration.
Figure 5-20 Bulk VLAN Configuration Page
Admin of Select items is used to enable VLAN. Port is ordinary port of bulk
VLAN configuration. Trunk is Trunk group of bulk VLAN configuration.
5-31
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
After setting some attributes of VLAN in this page, click Apply to complete
the configuration.
l PLAN Management
PVLAN Information Check
Click directory tree Configuration > PVLAN > Pvlan Overview on the left of main
page, open PVLAN information page, as shown in Figure 5-21.
Figure 5-21 PVLAN Information Page
The Description of Information Displayed:
Parameter Description
Pvlan Session PVLAN instance
Promiscuous Port Promiscuous physical port
Promiscuous Trunk Promiscuous trunk port
Isolated Port Isolated physical port
Isolated Trunk Isolated trunk port
Community Port Community physical port
Community Trunk Community trunk port
PVLAN Configuration
Click directory tree Configuration > PVLAN > Pvlan Configure on the left of main
page, open PVLAN configuration page, as shown in Figure 5-22.
5-32
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-22 PVLAN Configuration Page
PVALN Attribute Overview:
Parameter Description
Pvlan Session PVLAN instance
Promiscuous Port Promiscuous physical port
Promiscuous Trunk Promiscuous trunk port
Isolated Port Isolated physical port
Isolated Trunk Isolated trunk port
Community Port Community physical port
Community Trunk Community trunk port
This page also can set attributes. After setting, click Apply to submit. When system
is configured successfully, the configured information page will be displayed.
l Port Mirroring Management
Port Mirroring Information Check
Click directory tree Configuration > MIRROR > Mirror Overview on the left of main
page, open Mirror information page, refer to Figure 5-23.
5-33
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-23 Mirror Information Page
The Description of Information Displayed:
Parameter Description
Source port mirroring source port
Destination port mirroring destination port
Ingress Mirroring Configuration
Click Configuration > MIRROR > Mirror Configure on the left of main page to
configure mirroring port. Refer to Figure 5-24.
Figure 5-24 Mirroring Port Configuration Page
The source port and destination port can be configured in this page. After setting,
click Apply to submit to complete the configuration.
l LACP Management
5-34
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
LACP Basic Information Check
Click directory tree Configuration > Lacp > Lacp Port on the left of main page, open
LACP basic information page, as shown in Figure 5-25.
Figure 5-25 LACP Basic Attribute Page
The Description of Information Displayed:
Parameter Description
AdminStatus LACP enable
LacpPriority LACP priority
Aggregation Port Information Overview:
Parameter Description
GroupNum aggregation group number that aggregation
port belongs to
GroupMode aggregation group aggregation mode that port
belongs to
LacpTime aggregation port timeout mode
LacpActive aggregation port active/passive mode
set basic attributes of "AdminStatus" and "LacpPriority" in this page and set attributes
of "LacpTime" and "LacpActive" of aggregation port. After setting, click Apply to
submit to complete the configuration.
When setting same configuration of bulk aggregation port attribute , click the
corresponding check box to select multiple aggregation ports (select Select All to
select all ports), and then click Set to open configuration page of bulk aggregation
port, as shown in Figure 5-26.
5-35
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-26 Bulk Aggregation Port Configuration Page
After setting attributes of aggregation port in this page, click Apply to submit.
Aggregation Group Information Check
Click directory tree Configuration > Lacp > Lacp State on the left of main page, open
aggregation group information page, as shown in Figure 5-27.
Figure 5-27 Aggregation Group Information Page
The Description of Information Displayed:
Parameter Description
Attached Ports attached ports in aggregation group
Active Ports active ports in aggregation group
GroupMode aggregation mode of aggregation group
5-36
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Click Config of the right column to open the corresponding aggregation group
configuration page, as shown in Figure 5-28.
Figure 5-28 Aggregation Group Configuration Page
Configure "Aggretator Mode" attribute of aggregation group in this page , bind port
with aggregation group (select port in optional port column, clic ) and release port
from aggregation group (select port in aggregation port column, click ).
Note:
Only the ports with same attribute can be bound into the same aggregation group.
Each aggregation group can bind up to 8 ports.
Caution!
Avoid binding the port connects the network management host with aggregation
group, or the network management will be interrupted.
Monitoring Information
l Terminal Log Check
Click directory tree Monitoring > Terminal Log on the left of main page, open terminal
log information page, as shown in Figure 5-29.
5-37
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-29 Terminal Log Information Page
Click Refresh button to update terminal log information.
l Port Statistics Information Check
Click directory tree Monitoring > Port Statistics on the left of main page, open port
statistics information page, as shown in Figure 5-30.
Figure 5-30 Port Statistics Information Page
Click Refresh button to update port statistics information.
Select port in PortNumber drop-down box to get the port statistics. statistics includes:
l Statistics Data Overview
Parameter Description
ReceivedBytes Received bytes
ReceivedFrames Received frames
5-38
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Parameter Description
ReceivedBroadcastFrames Received broadcast frames
ReceivedMulticastFrames Received multicast frames
OversizeFrames Oversize frames
UndersizeFrames undersize frames
CrcError number of CRC error
SendBytes sending bytes
SendFrames sending frames
SendBroadcastFrames sending broadcast frames
SendMulticastFrames sending multicast frames
l Configuration Information Check
Click directory tree Monitoring > Running config on the left of main page, open
configuration information page, as shown in Figure 5-31. This page displays
configuration information of switch.
Figure 5-31 Configuration Information Page
This page displays configuration information of switch.
System Maintenance
l Configuration Saving Page
Click directory tree Maintenance > Save on the left of main page, open saving
configuration information page, as shown in Figure 5-32.
5-39
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-32 Saving Configuration Page
Click Ok to save configuration or click Cancel to cancel configuration.
Caution!
Saving configuration will cover the original configuration file. Make sure that the
configuration need to be covered before clicking Ok.
l Configuring Reboot
Click directory tree Maintenance > Reboot on the left of main page, open reboot
function page, as shown in Figure 5-33.
Figure 5-33 Reboot Function Page
Click Ok to reboot the switch or click Cancel to cancel reboot.
5-40
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
l Uploading File
à Click directory tree Maintenance > Upload on the left of main page, open file
upload page, as shown in Figure 5-34.
Figure 5-34 File Upload Page
à Click Browse..., browse and select the file to be uploaded, as shown in Figure
5-35, and then click Ok to upload file.
Figure 5-35 Browse and Select the File
Note:
For safety and application, only allow “zImage”, “bootrom.bin”, “startrun.dat”
and “to_permmac.dat” to be uploaded.
5-41
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Caution!
Make sure the legality and validity of file to be uploaded. The uploaded file will cover
the original file. If the operation is not correct switch can't work. Unprofessional
personnel are not recommended to use this function.
l User Management
Click directory tree Maintenance > User Manager on the left of main page, open user
management page, as shown in Figure 5-36.
Figure 5-36 User Management Page
By default, the Modify tab is displayed. Modify the login password and management
password, and then click Apply to submit.
l Adding User
Click add button in user management page, open Adding User page, as shown in
Figure 5-37
5-42
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Figure 5-37 Adding User Page
Enter the information about the user to be added, and then click Apply to submit.
l Deleting User
Click Delete button in user management page, open Deleting User page, as shown
in Figure 5-38.
Figure 5-38 Deleting User Page
Select the user to be deleted, and then click Apply to submit.
5.9 M_Button
Introduction to the M_Button Function
The M_button function is used to display the key statistics data and indicate the key events
through the panel indicators, which facilitates device maintenance.
5-43
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
The M_button function includes the following modes:
1. LINK mode (LINK): In this mode, a port indicator displays the LINK/ACT status of a
port. If the port is in link status, the green indicator is lit. If there is traffic, the green
indicator is flashing. If the port is not in link status, the indicator is not lit.
2. SPD mode (SPD): In this mode, a port indicator displays the current speed of a port.
If the port speed is the same as the default port speed, the green indicator is lit. If not,
the yellow indicator is lit.
3. DUPLEX mode (DUP): In this mode, a port indicator displays the duplex status. If the
port is in full-duplex mode, the green indicator is lit. If the port is in half-duplex mode,
the yellow indicator is lit.
4. STA mode (STAT): In this mode, a port indicator displays the STP status. If the STP
status of the port is Forward, the green indicator is lit. If the STP status of the port is
Disable, the indicator is not lit. In other statuses, the yellow indicator is lit. The STA
status is the status of the port in Instance 0.
5. CPU usage mode (CUP%): In this mode, a port indicator displays the current CPU
usage. For the 2910E-PS, the first 8 ports display the current usage, each of which
represents 12.5%. For other devices, the first 10 ports display the current usage, each
of which represents 10%.
6. Memory usage mode (MEM%): In this mode, a port indicator displays the current
memory usage. For the 2910E-PS, the first 8 ports display the current usage, each
of which represents 12.5%. For other devices, the first 10 ports display the current
usage, each of which represents 10%.
7. Uplink port outbound bandwidth occupation rate mode (↑BW%): In this mode, a port
indicator displays the current occupation rate of uplink port outbound bandwidth. The
current speed on the uplink interface is used as the base. For the 2910E-PS, the first
8 ports display the current occupation rate, each of which represents 12.5%. For other
devices, the first 10 ports display the current occupation rate, each of which represents
10%.
8. Uplink port inbound bandwidth occupation rate mode (↓BW%): In this mode, a port
indicator displays the current occupation rate of uplink port inbound bandwidth. The
current speed on the uplink interface is used as the base. For the 2910E-PS, the first
8 ports display the current occupation rate, each of which represents 12.5%. For other
devices, the first 10 ports display the current occupation rate, each of which represents
10%.
9. PING network management center mode (PING): In this mode, use the first five port
indicators. A device sends 5 ICMP packets to the network management center. For an
ICMP packet, if the correct reply is received, the corresponding indicator turns green.
If the correct reply is not received, the corresponding indicator turns yellow. When the
five indicators are all lit, and then they are not lit. After 20 seconds, the next PING flow
will start. If the network management address is not configured, the five indicators turn
yellow at the same time and then they are not lit. After 20 seconds, the next PING flow
will start.
5-44
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
10. CRC port display mode (CRC): In this mode, a port indicator displays the CRC errors.
If there is a CRC error frame on the port, the yellow indicator is lit. If there is no CRC
error frame on the port, the indicator is not lit.
11. STORM port display mode (STORM): In this mode, a port indicator indicates a storm
port. If the port is a storm port, the yellow indicator is lit. If the port is not a storm port,
the indicator is not lit.
12. NoMAC port display mode (NoMAC): In this mode, a port indicator indicates whether a
MAC address is learnt. If the port does not learn a MAC address, the yellow indicator
is lit. If the port learns a MAC address, the indicator is not lit. This mode supports
trunk. If a trunk port learns a MAC address, the indicators of the active ports in the
trunk are not lit.
13. PoE mode: In this mode, a port indicator indicates the PoE status. If PoE is normal,
the green indicator is lit. If a PoE exception occurs, the yellow indicator is lit. If there
is no power, the indicator is not lit. Only 2910E-PS and 2918E-PS support this mode.
M_Button Function Mode Switch
1. There is a mode button on the panel. Press it once, and then the indicator for the
next mode (the sequence in which the modes described in the previous topic) begins
flashing for 2 seconds. If the button is not pressed in 2 seconds, the mode indicator is
off. The device enters this mode and executes the function of this mode. If the button
is pressed in 2 seconds, the device enters the next mode. The next mode indicator
begins flashing. The previous process is repeated.
2. In a mode, if the mode button is not pressed in 3 minutes, the device exits from this
mode automatically to the LINK mode. If the button is pressed, the device enters the
next mode. The corresponding mode indicator begins flashing, which is as described
in 1.
3. In the PING mode, a ping packet is sent once per 20 seconds. In other modes, the
statuses are updated in real time.
5.10 Telnet
Telnet Overview
As a member of the TCP/IP protocol family, the Telnet protocol is the standard protocol for
the remote Internet login service. With this protocol, users can perform operations on a
remote switch through the local PC.
A ZTE switch can be used as both a Telnet client and a Telnet server.
Telnet Configuration
Telnet configuration includes:
5-45
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Command Function
Enables/disables the Telnet server
zte(cfg)#set Telnet server {enable | disable}
function, which is enabled by default.
Displays the Telnet configuration and
show Telnet (for all configuration modes)
status.
Telnet Configuration Instance
l Configuration Description
See Figure 5-39, a switch has a layer-3 port with the IP address 192.168.1.1/24, and
the host IP address is 192.168.1.100/24. The host remotely logs in to the switch
through Telnet.
Figure 5-39 Telnet Login Instance
l Configuration Procedure
1. Configure the switch
By default, the Telnet server function is enabled. You can use the following
command to make sure that the function is enabled.
zte(cfg)#show Telnet
Telnet server is enable
2. Configure the PC
Note:
Windows 2000 provides the Telnet client and server programs. Telnet.exe
is the client program and tlntsvr.exe is the server program. In addition,
Windows 2000 provides the Telnet server management program tlntadmn.exe.
By default, the Telnet service is installed in Windows 2000.
5-46
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 5 Management
Execute the Telnet command on the PC, see Figure 5-40.
Figure 5-40 Execute the Telnet Command on the PC
For the Telnet login result, see Figure 5-41.
Figure 5-41 Telnet Login Result
5-47
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
This page intentionally left blank.
5-48
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 6
Maintenance
Table of Contents
Routine Maintenance .................................................................................................6-1
Virtual Line Detection .................................................................................................6-2
Common Fault Handling.............................................................................................6-3
6.1 Routine Maintenance
Daily Maintenance Items
1. Check the running state of the switch
a. Check whether the back-end terminal interface can be normally operated.
b. Check whether each indicator state of the switch is normal.
c. Check whether the fan of switch runs normally.
d. Check whether the temperature of switch is normal and whether there is abnormal
smell in the equipment room.
e. Check the system alarm information.
2. Check the state of telecommunication between switch and each device connected.
Log in to the switch by HyperTerminal or Telnet. Use the ping command to test the
various network segments for connectivity check.
3. Check whether the related services of switch is normal.
4. Record the today's operation and phenomenon.
The today’s operation means the operation which is done on the switch. The
phenomenon includes switch state and equipment room environment.
Monthly Maintenance Items
1. Sum up the everyday operation every month
a. Sum up the routine problem. If necessary, discuss with ZTE maintenance
personnel.
b. Sum up and accumulate the maintenance experience in the routine maintenance
for more efficient maintenance.
2. Clean the equipment room environment
a. Note the cleaning of the air-conditioner and check the performance of
air-conditioner timely.
6-1
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
b. Note the chute and whether the related wire is loosen. If it is loose, adjust it.
3. Clean the switch
Note the cloth should not be too wet and the operation cannot affect the interface.
4. The backup of the alarm information, the backup of statistics information, the backup
of configuration information
Maintenance Period
The maintenance period of Ethernet switch is shown as Table 6-1.
Table 6-1 Maintenance Period of Ethernet Switch
No. Maintenance Test Item Test Period
1 Switch running state Day
Equipment room temperature and humidity check
2 Day
and power check
The telecommunication state between switch and
3 Day
the device
Whether the related service is normally
4 Day
implemented
5 Ordinary problem monthly summary Month
Ordinary maintenance experience monthly
6 Month
summary
7 Equipment room cleaning Month
8 Switch cleaning Month
9 Yearly summary Year
Monitoring room device full maintenance and
10 Year
check
6.2 Virtual Line Detection
VCT applies TDR to realize the diagnosis of the line. It can diagnose the fault state of the
line, such as Open, Short, Impedance Mismatch and Good termination. Also it can use
the experience formula to calculate the location of the fault line.
Use the show vct port <1-28> command to check the VCT detection result of the specified
port.
Example 1
zte(cfg)#show vct port 1
Cable Test Result for Port 1
6-2
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 6 Maintenance
RX PAIR :
Cable Test Passed. No problem found.
Cable Length is unknown.
TX PAIR :
Cable Test Passed. No problem found.
Cable Length is unknown.
Example 2
zte(cfg)#show vct port 8
Cable Test Result for Port 8
RX PAIR :
Cable Test Passed. Cable is open.
Approximately 7 meters from the tested port.
TX PAIR :
Cable Test Passed. Cable is open.
Approximately 6 meters from the tested port.
6.3 Common Fault Handling
6.3.1 Introduction to Common Fault
Fault includes hardware fault and software fault. For hardware fault, if we can correctly
locate, this kind of fault is removed by changing hardware. For software and the fault of
the configuration, the correct operation can be used to resolve the problem.
During the process of handling fault, according to the previous chapter, check whether the
configuration of the device is correct, the cable of the device is correct and the environment
of the device is satisfying.
6.3.2 The Configuration by Console Port Fails
Fault Phenomenon
The configuration by console port fails.
Related Component Check
Configuration cable, HyperTerminal serial port, switch Console port
Fault Analysis and Location
1. The configuration cable connection is not correct.
2. HyperTerminal serial port attribute configuration is wrong, terminal serial port has fault.
3. The console port of the switch has fault.
6-3
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Fault Handling
1. Use the correct configuration cable.
2. Check the attribute of serial port of hyperterminal, the correct configuration : Bits per
Second (baud rate) is set to 9600, data bit is set to 8, Parity check is set to “None”, data
flow control is set to “None”. Check whether the hyperterminal serial port is normal and
change the configuration terminal.
3. Check whether the Console port of the switch is normal.
6.3.3 Failed Telnet Connection
Fault Phenomenon
Failed Telnet connection
Fault Analysis and Location
1. The PVID configuration of the port is wrong.
2. The port is disabled.
3. The VLAN that IP port binds is disabled.
4. Switch does not configure valid IP address, subnet mask and default gateway.
5. The IP address of switch has conflict with the IP address of other devices.
6. The wrong switch REMOTE ACCESS configuration causes that IP address is filtered.
Fault Handling
1. Modify all PVIDs of ports and make them same as the VLAN ID to which the port
belongs.
2. Enable all the ports used.
3. Enable the VLAN that IP port binds.
4. Configure valid IP address, subnet mask and default gateway.
5. Modify the IP address of the switch or the IP or other devices to remove the IP address
conflict.
6. Configure REMOTE ACCESS as any, permit any host mode.
6.3.4 WEB Management Cannot be Connected
Fault Phenomenon
When WEB browser is opened, WEB management page cannot be opened.
Fault Analysis and Location
1. The browser version is too low.
2. The wrong address and port number are inputted on the browser address column.
3. The communication fault between host and device.
4. Switch does not configure management port or correct IP address.
6-4
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 6 Maintenance
5. Switch does not enable WEB management function.
Fault Handling
1. Upgrade the browser version of host to at least IE6.0.
2. Check the switch configuration and acquire correct IP address and port number.
3. Check the line between host and device to ensure that the communication between
host and device is normal.
4. Configure the correct management interface for the switch and configure the correct
IP address at the same time.
5. Enable WEB management function of the switch and configure port number.
6.3.5 Losing the Login Username or Password
Fault Phenomenon
When users input the username and login password, they cannot log in to the switch.
Fault Analysis and Location
The username or password is wrong.
Fault Handling
At first, ensure whether administrator can find the original username and password. If
cannot, reboot the switch and delete the configuration file. The operation procedure is as
follows:
1. Reboot the switch and enter any key at the hyperterminal to enter boot state.
ZXR10 2928E BootRom Version v1.15
Compiled May 21 2012 08:57:22
Copyright (c) 2010 by ZTE Corporation.
boot location [0:Net,1:Flash] : 1
actport : 1
serverip : 10.40.89.78
netmask : 255.255.255.0
ipaddr : 10.40.89.79
bootfile : /img/zImage.B10
username : ZXR10
password : ZXR10
MAC : 00:d0:d0:29:28:01
Press any key to stop autoboot: 2
[ZXR10 Boot]:
2. In [ZXR10 Boot] state, input [ZXR10 Boot]:zte, enter [BootManager] of switch, input
<?> for command help.
[BootManager]: ?
6-5
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
? - alias for 'help'
cd - change current path
exit - exit from BootManager mode
format - format flash
ftp - get/put file from/to FTP server
help - print online help
load - load zImage
ls - list files in current directory
mv - change [source] name to [destination] name
poever - get poe firmware version
reboot - perform REBOOT of the CPU
rm - remove file
setBOOTpassword - set password for BOOT mode
setPtype- set packaged type
show - show board information
update - update boot or firmware
[BootManager]:
3. Implement the rm command, delete startrun.dat configuration file and reboot the
switch.
[bootManager]:cd cfg
[bootManager]: ls
/cfg/
startrun.dat 671
to_permmac.dat 98304
[bootManager]: rm startrun.dat
[bootManager]: ls
/cfg/
to_permmac.dat 98304
[bootManager]:
4. After the switch is rebooted, use default username and password for login.
6.3.6 Losing Enable Enable Password
Fault Phenomenon
When users log in to the switch and input the password, they cannot enter global
configuration mode.
Fault Analysis and Location
Use the wrong password when users enter global configuration mode.
6-6
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 6 Maintenance
Fault Handling
The handling method refers to “Losing the Login Username or Password”.
Note
Before the switch is rebooted, record the current configuration for reconfiguration.
6.3.7 The Two Devices Cannot Interconnect in The Same VLAN
Fault Phenomenon
The two devices cannot interconnect in the same VLAN.
Fault Analysis and Location
1. The port PVID configuration is wrong.
2. The port is disabled.
3. The VLAN used by the port is disabled.
4. When the port is added in the VLAN, select the tag.
5. Device does not configure IP address or the IP addresses configured are not in the
same network segment.
Fault Handling
1. Modify all PVIDs of ports and make them same as the VLAN ID to which the port
belongs.
2. Enable all the ports used.
3. Enable VLAN used.
4. Add the port used into VLAN again, select untag when it is added.
5. Configure the correct IP address for device.
6.3.8 The Solution to Authentication Timeout Fault in Campus
Network
Fault Phenomenon
There are six buildings in the student dormitory of A school. If students want to access
the internet, the hosts must pass the authentication and accounting system. The Radius
server software of the authentication and accounting system and Bras hardware device
are provided by company B. The access layer device ZXR10 2900E must enable DOT1X
function and work with authentication and accounting server to provide the authentication
and accounting service of student area.
Company B completes the debug of Radius accounting server and Bras device and
allocates the authentication and accounting client end to each building by electrical
campus network for installation. Most students complete the registration and activation of
account number. When the preparation is completed, our company enables DOT1X port
6-7
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
authentication function on the access layer device of six buildings of student area in the
specified time. The configuration of ZXR10 2900E is as follows:
The two devices connected with the two ports in the same VLAN cannot ping each other.
set port 1-24 security enable
config nas
radius isp test defaultisp enable
radius isp test sharedsecret amtium
/*The sharing key negotiated with company B */
radius isp test add accounting 10.150.12.101
/*Company B authentication and accounting server address*/
radius isp test add authentication 10.150.12.101
/*Company B authentication and accounting server address*/
radius isp test client 172.16.0.181
/*Configure ISP name and the IP address of access switch*/
aaa-control port 1-24 dot1x enable
aaa-control port 1-24 accounting enable
aaa-control port 1-24 port-mode auto
When the configuration is completed, some hosts of B1, B2 and B3 three building have
“authentication timeout” problem.
Fault Analysis and Location
When the student account number and password are checked, the internal network
authentication still cannot be passed. After checking all the related configuration of
ZXR10 2900E in detail, the problem still exists. Also, change one new ZXR10 2900E, the
problem still exists. The diagnosis result is that the problem is interconnection between
the two devices.
By the packet sniffing, we find that ZXR10 2900E sends Access Request of radius protocol
to accounting server of company B but the later response message is not received. In
normal circumstance, the radius protocol message receiving and sending procedure is as
follows:
Access switch sends Access Request message
Server returns Access Challenge message
Switch sends Access Request message again
Server returns Access Accept message
Switch sends Accounting Request message
Server returns Accounting Response message
Because the procedures of authentication data packets sniffed from the two same ZXR10
2900Es are not same, the diagnosis result is company B accounting server configuration
problem. The engineer of company B checks the alarm information of their server, find
that the alarm of AP not support user auth type exists, that is, the authentication types
6-8
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Chapter 6 Maintenance
of server and switch are not same. When the back-end configuration of accounting and
authentication server is checked, it is found that the shared key configuration of access
layer switch of B1–B3 is wrong, the original key “amtium” is configured as “antium” now,
which causes the unsuccessful authentication negotiation of two devices and that user
authentication failure.
Solution
When the engineer of company B changes the password as “amtium” and have checked
for two days, the fault such as “authentication timeout”does not appear. The problem is
resolved completely.
6.3.9 The Solution to ARP Attack in Campus Network
Fault Phenomenon
The 11 access layer switches ZXR10 2900E of the same VLAN in the student dormitory
building cannot connect the network. It causes that forty percent of users of the building
cannot access the network.
Fault Analysis and Location
Check the network management system, find that the eleven switches are disconnected
and fail to be pinged through. The maintenance personnel arrives at the weak electricity
well, accesses one of the switch by HyperTerminal, the IP address is 172.168.0.123.
The CPU utilization reaches 93%~100%. Check the alarm information and configuration
information, the abnormality is not found. Access the convergence layer switch T40G,
find the alarm that “port 4 receives more ARP broadcast packets”. Check the traffic
information of this port by command, find that about one hundred thousand broadcast
packets are added every ten seconds.
Analyze the access switch ZXR10 2900E of this port and find the following conditions:
1. There is loop on the user side.
2. User host has the virus and sends broadcast packet continuously.
3. User host installs the ARP attack software and sends ARP attack packet continuously.
Check that the IP address of the ZXR10 2900E connected with this port of the convergence
layer switch is 172.168.0.111. The user connects the switch by the network cable and does
the packet sniffing and find that the host with the MAC address “00:19:e0:a9:5a:fc” sends
the ARP broadcast packet continuously. According to the label of the network cable, find
that the host is from 2606 dormitory. Pull out the network cable of the host, the eleven
switches recover normal and CPU utilization is no more than 5%.
Solution
1. Filter the MAC address of this PC with fault on the access layer switch and prohibit the
PC from accessing the internet, which prevents it from influencing the other users
6-9
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
2. Notice the school center equipment room, prohibit the host from logging in to the
network before that the hardware of the host is not formatted and the system is installed
again.
3. The PCs of the whole network install ARP dedicated check and kill tool.
6-10
SJ-20120409144109-002|2012-07-02(R1.0) ZTE Proprietary and Confidential
Downloaded from www.Manualslib.com manuals search engine
Figures
Figure 2-1 ZXR10 2900E CONFIGURATION MODES .............................................. 2-1
Figure 2-2 Starting HyperTerminal ............................................................................ 2-2
Figure 2-3 Location Information Dialog Box .............................................................. 2-2
Figure 2-4 Connection Description Dialog Box .......................................................... 2-3
Figure 2-5 Connect To Dialog Box ............................................................................ 2-3
Figure 2-6 COM1 Properties Dialog Box ................................................................... 2-4
Figure 2-7 Run Telnet ............................................................................................... 2-5
Figure 2-8 Telnet Window ......................................................................................... 2-5
Figure 3-1 TFTPD Server ......................................................................................... 3-4
Figure 3-2 Tftpd Settings Dialog Box......................................................................... 3-4
Figure 3-3 Connect to Server Dialog Box .................................................................. 3-5
Figure 3-4 FileZilla Server Window ........................................................................... 3-5
Figure 3-5 Users Dialog Box ..................................................................................... 3-6
Figure 3-6 Directory Setting Area.............................................................................. 3-6
Figure 3-7 Network Architecture of Automatic Configuration File
Downloading......................................................................................... 3-10
Figure 3-8 Network Structure of Automatic Configuration File Uploading ................ 3-11
Figure 4-1 PoE Application ....................................................................................... 4-7
Figure 4-2 Port Mirroring Configuration Instance ..................................................... 4-11
Figure 4-3 VLAN Transparent Transmission Configuration InstanceNetwork
Topology ............................................................................................... 4-14
Figure 4-4 LACP Configuration Instance ................................................................. 4-19
Figure 4-5 Network Topology of IGMP Snooping Configuration Instance................. 4-23
Figure 4-6 MLD Snooping Configuration Instance ................................................... 4-25
Figure 4-7 IPTV Configuration Instance 1 ............................................................... 4-30
Figure 4-8 IPTV Configuration Instance 2 ............................................................... 4-31
Figure 4-9 MSTP Topological Structure................................................................... 4-34
Figure 4-10 STP Configuration Instance ................................................................. 4-37
Figure 4-11 RSTP Configuration Instance ............................................................... 4-38
Figure 4-12 MSTP Configuration Instance .............................................................. 4-39
Figure 4-13 ACL Configuration Instance ................................................................. 4-49
Figure 4-14 QoS Configuration Instance ................................................................. 4-55
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 4-15 PVLAN CONFIGURATION EXAMPLE 1 .............................................. 4-57
Figure 4-16 PVLAN CONFIGURATION EXAMPLE 2 .............................................. 4-58
Figure 4-17 Layer 2 Protocol Transparent Transmission Configuration
Topology ............................................................................................... 4-60
Figure 4-18 Layer-3 Configuration Instance ............................................................ 4-63
Figure 4-19 DAI Configuration InstanceTopology .................................................... 4-65
Figure 4-20 USING PAP MODE FOR IDENTITY AUTHENTICATION ..................... 4-68
Figure 4-21 USING CHAP MODE FOR IDENTITY AUTHENTICATION .................. 4-69
Figure 4-22 USING EAP MODE FOR IDENTITY AUTHENTICATION..................... 4-69
Figure 4-23 Access Authentication Configuration Instance...................................... 4-73
Figure 4-24 TYPICAL QINQ NETWORKING........................................................... 4-75
Figure 4-25 QinQ Configuration Instance ................................................................ 4-76
Figure 4-26 GVRP Configuration Instance .............................................................. 4-81
Figure 4-27 DHCP Snooping/Option82 Configuration InstanceTopology ................. 4-85
Figure 4-28 DHCP Client Configuration InstanceTopology ...................................... 4-86
Figure 4-29 DHCPv6 Snooping/Option82 Configuration Instance............................ 4-89
Figure 4-30 VBAS Typical Network ........................................................................ 4-90
Figure 4-31 VBAS Configuration InstanceTopology................................................. 4-91
Figure 4-32 PPPOE-PLUS Configuration InstanceTopology.................................... 4-92
Figure 4-33 ZESR running state when the ring is “complete state” .......................... 4-94
Figure 4-34 ZESR running state when the ring is “link failure” ................................. 4-95
Figure 4-35 ZESR running state when the ring is “link restore”................................ 4-96
Figure 4-36 Multi-Ring Multi-Domain....................................................................... 4-96
Figure 4-37 ZESR Multi-Ring Multi-Domain Design Figure...................................... 4-97
Figure 4-38 Non level 0 Segment Link .................................................................... 4-97
Figure 4-39 SMART-LINK ....................................................................................... 4-98
Figure 4-40 Tangent Ring Design Figure................................................................. 4-99
Figure 4-41 ZESR Single Ring Networking ........................................................... 4-102
Figure 4-42 ZESR Multi-Ring Networking Topology............................................... 4-104
Figure 4-43 Smart Link Networking ....................................................................... 4-107
Figure 4-44 Cross-Device TCN Sending Example................................................. 4-110
Figure 4-45 Remote Loop Network ....................................................................... 4-113
Figure 4-46 Link Control Network.......................................................................... 4-116
Figure 4-47 VLAN Mapping Networking Diagram .................................................. 4-120
Figure 4-48 VLAN Mapping Configuration Instance............................................... 4-122
Figure 4-49 PP Configuration Instance ................................................................. 4-125
II
Downloaded from www.Manualslib.com manuals search engine
Figures
Figure 4-50 LLDP Configuration Instance ............................................................. 4-127
Figure 4-51 Single Port Loop Detection Configuration Topology............................ 4-130
Figure 4-52 Double Ports Loop Detection Configuration Topology......................... 4-130
Figure 4-53 UDLD Configuration Instance............................................................. 4-133
Figure 4-54 TACACS+ Configuration Instance ...................................................... 4-135
Figure 4-55 Voice VLAN Configuration Instance ................................................... 4-137
Figure 4-56 Single Management Domain .............................................................. 4-138
Figure 4-57 Domains in the Network ..................................................................... 4-139
Figure 4-58 Single-Domain CFM Network Without MIP......................................... 4-142
Figure 4-59 Single-Domain CFM Network With MIP.............................................. 4-143
Figure 4-60 LM Network Configuration Instance ................................................... 4-145
Figure 4-61 DM Network Configuration Instance ................................................... 4-146
Figure 4-62 AIS/LCK Network Configuration Instance ........................................... 4-148
Figure 4-63 DHCP Relay Configuration Instance .................................................. 4-152
Figure 5-1 SSH CONFIGURATION EXAMPLE ......................................................... 5-4
Figure 5-2 SETTING IP ADDRESS AND PORT NUMBER OF THE SSH
SERVER................................................................................................. 5-4
Figure 5-3 SETTING SSH VERSION NUMBER........................................................ 5-5
Figure 5-4 USER CONFIRMATION REQUIRED IN THE FIRST LOGIN.................... 5-5
Figure 5-5 SSH LOGIN RESULT .............................................................................. 5-6
Figure 5-6 MAC Change Advertisement Configuration Instance.............................. 5-12
Figure 5-7 CLUSTER MANAGEMENT NETWORKING........................................... 5-16
Figure 5-8 Switch Character Switch Rule ................................................................ 5-17
Figure 5-9 CLUSTER MANAGEMENT NETWORKING........................................... 5-20
Figure 5-10 System Login Interface ........................................................................ 5-24
Figure 5-11 System Main Interface.......................................................................... 5-24
Figure 5-12 System Information Page..................................................................... 5-25
Figure 5-13 Port State Information Page ................................................................. 5-26
Figure 5-14 Port Configuration Information Page .................................................... 5-27
Figure 5-15 Single Port Configuration Page ............................................................ 5-28
Figure 5-16 Bulk Port Configuration Page ............................................................... 5-29
Figure 5-17 VLAN Information Page ....................................................................... 5-29
Figure 5-18 VLAN Number Entering Page .............................................................. 5-30
Figure 5-19 Single VLAN Configuration Page ......................................................... 5-31
Figure 5-20 Bulk VLAN Configuration Page ............................................................ 5-31
Figure 5-21 PVLAN Information Page ..................................................................... 5-32
III
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
Figure 5-22 PVLAN Configuration Page.................................................................. 5-33
Figure 5-23 Mirror Information Page ....................................................................... 5-34
Figure 5-24 Mirroring Port Configuration Page ........................................................ 5-34
Figure 5-25 LACP Basic Attribute Page .................................................................. 5-35
Figure 5-26 Bulk Aggregation Port Configuration Page ........................................... 5-36
Figure 5-27 Aggregation Group Information Page ................................................... 5-36
Figure 5-28 Aggregation Group Configuration Page................................................ 5-37
Figure 5-29 Terminal Log Information Page ............................................................ 5-38
Figure 5-30 Port Statistics Information Page ........................................................... 5-38
Figure 5-31 Configuration Information Page............................................................ 5-39
Figure 5-32 Saving Configuration Page .................................................................. 5-40
Figure 5-33 Reboot Function Page ......................................................................... 5-40
Figure 5-34 File Upload Page ................................................................................. 5-41
Figure 5-35 Browse and Select the File .................................................................. 5-41
Figure 5-36 User Management Page ...................................................................... 5-42
Figure 5-37 Adding User Page................................................................................ 5-43
Figure 5-38 Deleting User Page.............................................................................. 5-43
Figure 5-39 Telnet Login Instance ........................................................................... 5-46
Figure 5-40 Execute the Telnet Command on the PC.............................................. 5-47
Figure 5-41 Telnet Login Result .............................................................................. 5-47
IV
Downloaded from www.Manualslib.com manuals search engine
Tables
Table 2-1 Common Command Parameters ............................................................. 2-12
Table 2-2 Functional Keys Descriptions .................................................................. 2-14
Table 4-1 Port Role and Port State.......................................................................... 4-34
Table 4-2 Syslog Log Information............................................................................ 4-77
Table 6-1 Maintenance Period of Ethernet Switch ..................................................... 6-2
Downloaded from www.Manualslib.com manuals search engine
Tables
This page intentionally left blank.
Downloaded from www.Manualslib.com manuals search engine
Glossary
ACL
- Access Control List
ARP
- Address Resolution Protocol
CoS
- Class of Service
DHCP
- Dynamic Host Configuration Protocol
DSCP
- Differentiated Services Code Point
GARP
- Generic Attribute Registration Protocol
IP
- Internet Protocol
IPTV
- Internet Protocol Television
LACP
- Link Aggregation Control Protocol
LLDP
- Link Layer Discovery Protocol
MLD
- Multicast Listener Discovery
MPU
- Management Process Unit
MSTP
- Multiple Spanning Tree Protocol
NTP
- Network Time Protocol
OAM
- Operation, Administration and Maintenance
PPPoE
- Point to Point Protocol over Ethernet
PVLAN
- Private Virtual Local Area Network
VII
Downloaded from www.Manualslib.com manuals search engine
ZXR10 2900E Series Configuration Guide
PoE
- Power over Ethernet
QoS
- Quality of Service
RADIUS
- Remote Authentication Dial In User Service
RMON
- Remote Monitoring
RSTP
- Rapid Spanning Tree Protocol
SNMP
- Simple Network Management Protocol
SSH
- Secure Shell
STP
- Spanning Tree Protocol
TACACS+
- Terminal Access Controller Access-Control System Plus
TCP
- Transfer Control Protocol
TFTP
- Trivial File Transfer Protocol
UDLD
- UniDirectional Link Detection
UDP
- User Datagram Protocol
VBAS
- Virtual Broadband Access Server
VLAN
- Virtual Local Area Network
VPN
- Virtual Private Network
ZESR
- ZTE Ethernet Switch Ring
VIII
Downloaded from www.Manualslib.com manuals search engine
Вам также может понравиться
- ZXR10 2900E Series: Configuration GuideДокумент266 страницZXR10 2900E Series: Configuration Guidejoko handoyoОценок пока нет
- SJ-20130731155059-002-ZXR10 2900E Series (V2.05.11) Easy-Maintenance Secure Switch Configuration Guide - 540668Документ307 страницSJ-20130731155059-002-ZXR10 2900E Series (V2.05.11) Easy-Maintenance Secure Switch Configuration Guide - 540668shujath_ali_1Оценок пока нет
- SJ-20150112110821-002-ZXR10 2900E Series (V2.05.12) Easy-Maintenance Secure Switch Configuration Guide - 676543Документ321 страницаSJ-20150112110821-002-ZXR10 2900E Series (V2.05.12) Easy-Maintenance Secure Switch Configuration Guide - 676543Yuniar Mita RuswandiОценок пока нет
- zxr10 2900e SeriesДокумент750 страницzxr10 2900e SeriesThae Myat Khaing LwinОценок пока нет
- SJ-20130329092338-003-ZXR10 5250-H Series (V2.05.10) All Gigabit Intelligent Switch Command ReferenceДокумент706 страницSJ-20130329092338-003-ZXR10 5250-H Series (V2.05.10) All Gigabit Intelligent Switch Command Referencemarco100% (1)
- ZXR10 5900E Configuration Guide (Basic Configuration)Документ174 страницыZXR10 5900E Configuration Guide (Basic Configuration)HectorОценок пока нет
- Zte ConfigurationДокумент192 страницыZte Configurationmgraj7100% (1)
- ZXUN USPP (V4.13.20) Universal Subscriber Profile Platform Software Installation GuideДокумент177 страницZXUN USPP (V4.13.20) Universal Subscriber Profile Platform Software Installation GuideEm KaaPeeM100% (1)
- SJ-20121213142710-016-ZXR10 8900E (V3.01.01) Series Core Switch Configuration Guide (Reliablity) - 548073Документ217 страницSJ-20121213142710-016-ZXR10 8900E (V3.01.01) Series Core Switch Configuration Guide (Reliablity) - 548073Frans RapetsoaОценок пока нет
- SJ-20140617195408-005-ZXA10 C320 (V2.0.1) Optical Access Convergence Equipment Configuration Manual (CLI)Документ181 страницаSJ-20140617195408-005-ZXA10 C320 (V2.0.1) Optical Access Convergence Equipment Configuration Manual (CLI)Zhie Al MuhajirinОценок пока нет
- SJ-20111107090012-009 ZXR10 M6000 (V1.00.60) Carrier-Class Router Configuration Guide (Basic Configuration)Документ102 страницыSJ-20111107090012-009 ZXR10 M6000 (V1.00.60) Carrier-Class Router Configuration Guide (Basic Configuration)Nishchal AgarwalОценок пока нет
- SJ-20160119164028-003-ZXR10 5960 Series (V3.02.20) All 10-Gigabit Data Center Switch Configuration Guide (Basic Configuration)Документ172 страницыSJ-20160119164028-003-ZXR10 5960 Series (V3.02.20) All 10-Gigabit Data Center Switch Configuration Guide (Basic Configuration)leandro de sousaОценок пока нет
- SJ-20121213142710-009-ZXR10 8900E (V3.01.01) Series Core Switch Configuration Guide (Link Layer) - 566375Документ162 страницыSJ-20121213142710-009-ZXR10 8900E (V3.01.01) Series Core Switch Configuration Guide (Link Layer) - 566375Frans RapetsoaОценок пока нет
- SJ-20140402111402-005-ZXMW NR8250 (V2 03 03) Configuration GuideДокумент219 страницSJ-20140402111402-005-ZXMW NR8250 (V2 03 03) Configuration GuideMumbi NjorogeОценок пока нет
- SJ-20110624091725-012 ZXR10 8900&8900E (V3.00.01) Series Switch Configuration Guide (QoS)Документ49 страницSJ-20110624091725-012 ZXR10 8900&8900E (V3.00.01) Series Switch Configuration Guide (QoS)Nishchal AgarwalОценок пока нет
- Switch Zte 2Документ185 страницSwitch Zte 2Ruben MataОценок пока нет
- SJ-20130205142913-019-ZXR10 M6000 (V1.00.60) Carrier-Class Router Configuration Guide (Reliability) PDFДокумент147 страницSJ-20130205142913-019-ZXR10 M6000 (V1.00.60) Carrier-Class Router Configuration Guide (Reliability) PDFHarjanto Handi KusumoОценок пока нет
- Zxr10 5960 SwitchДокумент208 страницZxr10 5960 SwitchEdivaldoVianaОценок пока нет
- SJ-20130408140048-003-ZXUR 9000 GSM (V6.50.103) Product DescriptionДокумент47 страницSJ-20130408140048-003-ZXUR 9000 GSM (V6.50.103) Product DescriptionnazilaОценок пока нет
- ZXHN H268A: Maintenance Management Manual (EXETEL)Документ80 страницZXHN H268A: Maintenance Management Manual (EXETEL)ElvisОценок пока нет
- SJ-20160119164028-015-ZXR10 5960 Series (V3.02.20) All 10-Gigabit Data Center Switch Configuration Guide (IDC)Документ127 страницSJ-20160119164028-015-ZXR10 5960 Series (V3.02.20) All 10-Gigabit Data Center Switch Configuration Guide (IDC)keslleyОценок пока нет
- SJ-20140721105958-012-ZXCTN 9000-E (V3.00.10) Carrier Class Multi-Service Packet-Based Platform Configuration Guide (MPLS)Документ410 страницSJ-20140721105958-012-ZXCTN 9000-E (V3.00.10) Carrier Class Multi-Service Packet-Based Platform Configuration Guide (MPLS)Loi Nguyen ThoОценок пока нет
- ZXR10 8900 Series: User Manual (FW Volume)Документ147 страницZXR10 8900 Series: User Manual (FW Volume)JoseОценок пока нет
- ZXR10 8900 Series: User Manual (Basic Configuration Volume)Документ186 страницZXR10 8900 Series: User Manual (Basic Configuration Volume)Douglas Da Silva BeneditoОценок пока нет
- SJ-20141021142133-002-ZXHN F660 (V5.2) GPON ONT Maintenance Management Guide (JAZZTEL) PDFДокумент113 страницSJ-20141021142133-002-ZXHN F660 (V5.2) GPON ONT Maintenance Management Guide (JAZZTEL) PDFcrashpunkОценок пока нет
- ZXR10 5900E Series (V2.8.23.B2) Easy-Maintenance MPLS Routing Switch User Manual (IPv4 Routing Volume)Документ150 страницZXR10 5900E Series (V2.8.23.B2) Easy-Maintenance MPLS Routing Switch User Manual (IPv4 Routing Volume)M J (TheTycza)Оценок пока нет
- SJ-20110624091725-007 ZXR10 8900&8900E (V3.00.01) Series Switch Debugging GuideДокумент65 страницSJ-20110624091725-007 ZXR10 8900&8900E (V3.00.01) Series Switch Debugging GuideNishchal AgarwalОценок пока нет
- ZXMW PR10 S400&S500 Digital Microwave System Configuration GuideДокумент83 страницыZXMW PR10 S400&S500 Digital Microwave System Configuration GuideLarba SawadogoОценок пока нет
- sjzl20092702 OperationGuide - TrafficControlДокумент236 страницsjzl20092702 OperationGuide - TrafficControlfouad_hassan2010Оценок пока нет
- ZXA10 C300: Optical Access Convergence EquipmentДокумент75 страницZXA10 C300: Optical Access Convergence EquipmentPeblo StantsОценок пока нет
- ZXR10 M6000 (V1.00.30) Carrier-Class Router Configuration Guide (IPv4 Routing) PDFДокумент237 страницZXR10 M6000 (V1.00.30) Carrier-Class Router Configuration Guide (IPv4 Routing) PDFcristopherОценок пока нет
- CSU New ManualДокумент95 страницCSU New Manualmo7amedmoh100% (1)
- SJ-20130205142913-017-ZXR10 M6000 (V1.00.60) Carrier-Class Router Configuration Guide (QoS)Документ91 страницаSJ-20130205142913-017-ZXR10 M6000 (V1.00.60) Carrier-Class Router Configuration Guide (QoS)Harjanto Handi KusumoОценок пока нет
- NetNumen U31 R10 V12.14.30 Unified Element Management System Product Description 595609Документ59 страницNetNumen U31 R10 V12.14.30 Unified Element Management System Product Description 595609Sammy Ulali100% (1)
- SJ-20100908091007-005-ZXC10 BSCB (V8.0.3.002) Controller Technical Manual PDFДокумент124 страницыSJ-20100908091007-005-ZXC10 BSCB (V8.0.3.002) Controller Technical Manual PDFengrSadiqueОценок пока нет
- SJ-20130930111159-002-ZXMW NR8250 (V2.03.02) System DescriptionДокумент103 страницыSJ-20130930111159-002-ZXMW NR8250 (V2.03.02) System DescriptionkmadОценок пока нет
- SJ-20121213161606-015-ZXWR RNC (V3.12.10) Initial Configuration GuideДокумент47 страницSJ-20121213161606-015-ZXWR RNC (V3.12.10) Initial Configuration GuideAmirpasha FatemiОценок пока нет
- SJ-20140214110341-001-Unitrans ZXMP S385 (V3.30) Product DescriptionДокумент153 страницыSJ-20140214110341-001-Unitrans ZXMP S385 (V3.30) Product DescriptionDavood SalehiОценок пока нет
- NetNumen Unified Element Management System Operation Guide PDFДокумент487 страницNetNumen Unified Element Management System Operation Guide PDFDanny Njoman50% (2)
- SJ-20140724091740-009-NetNumen U31 R18 (V12.13.50) Maintenance Management Operation GuideДокумент107 страницSJ-20140724091740-009-NetNumen U31 R18 (V12.13.50) Maintenance Management Operation GuidenazilaОценок пока нет
- SJ-20151105160201-002-ZXMW NR8950 (V2.04.02) System DescriptionДокумент75 страницSJ-20151105160201-002-ZXMW NR8950 (V2.04.02) System DescriptionSergio Arroyo100% (1)
- ZXHN+F670+V1 0+PON+ONT+Maintenance+Management PDFДокумент186 страницZXHN+F670+V1 0+PON+ONT+Maintenance+Management PDFAnonymous u8XKgo878% (9)
- ZXHN F670 V1 0 PON ONT Maintenance Management PDFДокумент186 страницZXHN F670 V1 0 PON ONT Maintenance Management PDFmarsudi.kisworo7533Оценок пока нет
- zxv10 w300Документ89 страницzxv10 w300FRANKLIN NAVARROОценок пока нет
- SJ-20110624091725-013 ZXR10 8900&8900E (V3.00.01) Series Switch Configuration Guide (VPN)Документ117 страницSJ-20110624091725-013 ZXR10 8900&8900E (V3.00.01) Series Switch Configuration Guide (VPN)Nishchal AgarwalОценок пока нет
- SJ-20160328171815-028-ZXUR 9000 UMTS (V4.15.10.20) Configuration Tool Operation GuideДокумент61 страницаSJ-20160328171815-028-ZXUR 9000 UMTS (V4.15.10.20) Configuration Tool Operation GuideKhải Khà KhàОценок пока нет
- ZXDU CSU501B User GuideДокумент124 страницыZXDU CSU501B User GuideColour BlindОценок пока нет
- SUMMARY SJ-20120313111345-002-ZXUR 9000 GSM (V6.50.10) Product Description - 415955Документ43 страницыSUMMARY SJ-20120313111345-002-ZXUR 9000 GSM (V6.50.10) Product Description - 415955fahadmalik890% (1)
- SJ-20161220134736-010-ZXA10 C300&C350&C320 (V2.1.0) Optical Access Convergence Equipment Configuration Management - PDF - 805260 PDFДокумент232 страницыSJ-20161220134736-010-ZXA10 C300&C350&C320 (V2.1.0) Optical Access Convergence Equipment Configuration Management - PDF - 805260 PDFRonaldo YoupLoadОценок пока нет
- TD-OLT ZTE-ZXA10 C300 Product DescriptionДокумент81 страницаTD-OLT ZTE-ZXA10 C300 Product Descriptiontest oneОценок пока нет
- SJ-20111215100134-001 ZXR10 5900E Series (V2.8.23.C) Easy-Maintenance MPLS Routing Switch Hardware Manual - 399469Документ59 страницSJ-20111215100134-001 ZXR10 5900E Series (V2.8.23.C) Easy-Maintenance MPLS Routing Switch Hardware Manual - 399469M J (TheTycza)Оценок пока нет
- ZXA10 C220: Configuration Manual (CLI)Документ190 страницZXA10 C220: Configuration Manual (CLI)Teerapong NakkaraОценок пока нет
- Manual Edimax br-6224nДокумент131 страницаManual Edimax br-6224nReca BogdanОценок пока нет
- Microsoft Windows Server 2008 R2 Administrator's Reference: The Administrator's Essential ReferenceОт EverandMicrosoft Windows Server 2008 R2 Administrator's Reference: The Administrator's Essential ReferenceРейтинг: 4.5 из 5 звезд4.5/5 (3)
- Deploying QoS for Cisco IP and Next Generation Networks: The Definitive GuideОт EverandDeploying QoS for Cisco IP and Next Generation Networks: The Definitive GuideРейтинг: 5 из 5 звезд5/5 (2)
- Network Processors: Architecture, Programming, and ImplementationОт EverandNetwork Processors: Architecture, Programming, and ImplementationОценок пока нет
- Cisco CCNA/CCENT Exam 640-802, 640-822, 640-816 Preparation KitОт EverandCisco CCNA/CCENT Exam 640-802, 640-822, 640-816 Preparation KitРейтинг: 2.5 из 5 звезд2.5/5 (8)
- The Theory of "Efficient Breach": A Jewish Law Perspective: R Onald W ArburgДокумент21 страницаThe Theory of "Efficient Breach": A Jewish Law Perspective: R Onald W Arburgoutdash2Оценок пока нет
- 2015 Queensland Tide TablesДокумент123 страницы2015 Queensland Tide TablesNanda AnnisaОценок пока нет
- Mga Ibat Ibang Tawag Sa Mga RapistДокумент7 страницMga Ibat Ibang Tawag Sa Mga RapistkikayОценок пока нет
- 2020 - ProspectusДокумент675 страниц2020 - ProspectusJohny DoeОценок пока нет
- Guidelines in The Issuance of Cetificate of Competency For Fire Volunteers, Members of Fire Brigades and Safety PractitionersДокумент5 страницGuidelines in The Issuance of Cetificate of Competency For Fire Volunteers, Members of Fire Brigades and Safety PractitionersMacabebe Fire Station33% (3)
- Chapter 6 Bank Recon Practice QHДокумент3 страницыChapter 6 Bank Recon Practice QHSuy Yanghear100% (1)
- A Critical Study On Hostile WitnessesДокумент7 страницA Critical Study On Hostile WitnessesSME894Оценок пока нет
- Department of Education: Republic of The PhilippinesДокумент2 страницыDepartment of Education: Republic of The PhilippinesAileen VillagraciaОценок пока нет
- Penggunaan Rasio Keuangan Untuk Mengukur Kinerja Keuangan Perusahaan (Studi Pada PT. Astra Otoparts, TBK Dan PT. Goodyer Indonesia, TBK YangДокумент10 страницPenggunaan Rasio Keuangan Untuk Mengukur Kinerja Keuangan Perusahaan (Studi Pada PT. Astra Otoparts, TBK Dan PT. Goodyer Indonesia, TBK YangAris SetiawanОценок пока нет
- Estate of Vda V. DizonДокумент3 страницыEstate of Vda V. DizonSy Kristine Frances A.Оценок пока нет
- ia-2021.01.20-16.22-NTI Commercial Motor Claim FormДокумент4 страницыia-2021.01.20-16.22-NTI Commercial Motor Claim FormJennifer McPhersonОценок пока нет
- FXTM Partners - Introducing Partnership AgreeementДокумент19 страницFXTM Partners - Introducing Partnership AgreeementPhạmm Thịi Hồngg NhunggОценок пока нет
- Answer (Yek-146)Документ8 страницAnswer (Yek-146)Ilmioamore InfermiereОценок пока нет
- Principles of Macroeconomics July 16, 2016: A. Three Most Common Barriers To TradeДокумент8 страницPrinciples of Macroeconomics July 16, 2016: A. Three Most Common Barriers To TradeAllie ContrerasОценок пока нет
- Vicoy Vs People, 383 SCRA 707, G.R. No. 138203, July 3, 2002Документ7 страницVicoy Vs People, 383 SCRA 707, G.R. No. 138203, July 3, 2002Gi NoОценок пока нет
- Stages of Civil Suit ByAbdullah ZahidДокумент11 страницStages of Civil Suit ByAbdullah ZahidAbdullah Zahid100% (1)
- Modern Work Plan Comparison - EnterpriseДокумент9 страницModern Work Plan Comparison - EnterpriseferОценок пока нет
- Uniform CPA Examination Questions May 1980 To November 1981Документ260 страницUniform CPA Examination Questions May 1980 To November 1981Adrienne GonzalezОценок пока нет
- Class Program Grade 1 (2022-2023)Документ7 страницClass Program Grade 1 (2022-2023)Rose Mae Cagampang PawayОценок пока нет
- Global Visas - Client Care LetterДокумент7 страницGlobal Visas - Client Care Letterbalus1430% (1)
- Wedding ScriptДокумент11 страницWedding ScriptJevon Lorenzo Advincula100% (1)
- Tenant Construction Guide Rev1docxДокумент12 страницTenant Construction Guide Rev1docxBer Salazar JrОценок пока нет
- Duty List of The Month of Octber 2023Документ5 страницDuty List of The Month of Octber 2023acadprokmcОценок пока нет
- The Conduct of The Earl of CaithnessДокумент15 страницThe Conduct of The Earl of CaithnessBren-RОценок пока нет
- Preamble of The Indian ConstitutionДокумент4 страницыPreamble of The Indian ConstitutionSupriyaОценок пока нет
- Apostles in The New TestamentДокумент13 страницApostles in The New TestamentMarvin John YpilОценок пока нет
- MCQ PDFДокумент7 страницMCQ PDFshaan76Оценок пока нет
- Test Bank For Organizational Change An Action-Oriented Toolkit, 4th Edition, Gene Deszca Cynthia Ingols Tupper F. CawseyДокумент36 страницTest Bank For Organizational Change An Action-Oriented Toolkit, 4th Edition, Gene Deszca Cynthia Ingols Tupper F. Cawseymarkalantinkhwukc100% (20)
- Invoice 20072010-19082010 (Aug' 10)Документ3 страницыInvoice 20072010-19082010 (Aug' 10)scribd_lostandfoundОценок пока нет
- 1733VGДокумент18 страниц1733VGTERASAT SAОценок пока нет