Академический Документы
Профессиональный Документы
Культура Документы
Attendance System Using The Fingerprint For Yemen University Staff
Загружено:
Fifi SmithОригинальное название
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Attendance System Using The Fingerprint For Yemen University Staff
Загружено:
Fifi SmithАвторское право:
Доступные форматы
Attendance System Using The Fingerprint For Yemen University Staff
Table of Contents
1.1 Problem Background.......................................................................................................................8
1.2 Problem Statement...........................................................................................................................9
1.3 Project Objective...........................................................................................................................10
1.4 Project Scope.................................................................................................................................11
1.4.1 Functionalities of Fingerprint Identification System.....................................................................12
1.4.1.1 Minutia Extractor.......................................................................................................................12
1.4.1.1.1 Preprocessing Functions.........................................................................................................12
1.4.1.1.2 Minutia Extraction Functions..................................................................................................13
1.4.1.1.3 Post-processing Functions...................................................................................................13
1.4.1.2 Minutia Matcher....................................................................................................................14
1.4.2 Functionalities of Campus Entrance Clocking System.................................................................14
1.4.3 Functionalities of Profiles & Management System.......................................................................14
1.4.3.1 User Authorization.................................................................................................................14
1.4.3.2 User Management..................................................................................................................15
1.4.3.3 Clocking Component.............................................................................................................15
1.4.3.4 Attendance Management........................................................................................................15
1.4.3.5 Leave Component..................................................................................................................16
1.4.3.6 Report Management...............................................................................................................17
1.4.3.7 Bulletin Management.............................................................................................................17
1.4.3.8 Department management.......................................................................................................18
1.5 Project Constraint..................................................................................................................18
1.5.1 Limitations.........................................................................................................................18
1.5.2. Time...................................................................................................................................18
1.5.3 Manpower..........................................................................................................................19
1.6 Project Stakeholders..............................................................................................................19
1.7 Project Framework.................................................................................................................20
1.8 Conclusion.............................................................................................................................21
2.1 Introduction...................................................................................................................................22
2.2 History of the company / Background of Company.......................................................................22
2.3 Literature Review Finding.............................................................................................................23
University Of East London 1 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Case 1 FingerFlex.................................................................................................................................23
Case 3 screen shot of SilverLiners Time Attendance Suite as follow....................................................30
2.4 Comparisons of finding.................................................................................................................32
2.5 Academic/Technology Research:...................................................................................................33
2.5.1 Fingerprint Recognition.........................................................................................................33
2.5.1.1.2 What is Fingerprint Recognition?.......................................................................................34
2.5.1.1.3 Two approaches for Fingerprint recognition.......................................................................36
2.5.1.2 System design – Fingerprint Recognition System..................................................................36
2.5.1.2.1 System Level Design..........................................................................................................36
2.5.1.2.2 Algorithm Level Design......................................................................................................38
2.5.1.3 Fingerprint Image Preprocessing:..............................................................................................39
2.5.1.3.1 Fingerprint Image Enhancement.........................................................................................39
2.5.1.3.2 Fingerprint Image Binarization...........................................................................................41
2.3.3 Fingerprint Image Segmentation...................................................................................................42
2.4.1 Fingerprint Ridge Thinning..........................................................................................................44
2.4.2 Minutia Marking...........................................................................................................................45
2.5.2 Fingerprint Scanner Research.......................................................................................................47
2.5.2.1 DigitalPersona U.are.U 4500.....................................................................................................47
2.5.3 Programming Language Research................................................................................................52
2.5.3.1 MATLAB Programming Language...........................................................................................52
2.5.3.2 Java............................................................................................................................................53
2.5.3.3 C# (C Sharp)..................................................................................................................................55
2.5.3.4 Conclusion of Programming research............................................................................................56
2.5 Target System................................................................................................................................56
2.6 Conclusion.....................................................................................................................................57
Gathering User Requirements............................................................................................................59
3.2.1 Interviews..................................................................................................................................59
3.2.2 Questionnaire............................................................................................................................65
3.3 Software Development Methodology............................................................................................66
3.4 Waterfall Model............................................................................................................................66
3.5 Spiral Methodology......................................................................................................................68
3.6 Rational Unified Process (RUP) Methodology..............................................................................69
University Of East London 2 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Six Engineering Disciplines......................................................................................................................71
3.7 Conclusion....................................................................................................................................76
4.1 Introduction...................................................................................................................................77
4.2 Types of Analysis..........................................................................................................................77
4.3 Qualitative analysis........................................................................................................................77
4.4 Quantitative Analysis.....................................................................................................................78
4.5 Summarization of the Interviews conducted..................................................................................78
4.5 Summarization of the questionnaire..............................................................................................81
4.6 Feasibility study analysis...............................................................................................................90
4.7 Operational feasibility....................................................................................................................91
4.8 Technical Feasibility......................................................................................................................91
4.9 The Cost of my project..................................................................................................................92
4.10 conclusions...................................................................................................................................94
5.1 Introduction..................................................................................................................................95
5.2 Overview of the system design......................................................................................................95
5.3 Types of design..............................................................................................................................95
5.3.1 Use Case Diagram...............................................................................................................95
5.3.2 Use Case Diagram (High Level Diagram).............................................................................96
5.3.3 Fingerprint Processing Library (Sub-diagram).......................................................................97
5.3.4 False Minutia Remover..........................................................................................................98
5.4 Design Class Diagram...................................................................................................................99
5.5 Activity Diagram.........................................................................................................................103
5.5.1 Profiles & Management System (Activity Diagram)..........................................................104
5.6 Sequences diagram......................................................................................................................105
5.7 Database Relationship Diagram...................................................................................................106
5.8 ERD.............................................................................................................................................107
5.8.1 Relation Derived for ERD...................................................................................................108
5.9 Hardware & Software..................................................................................................................110
5.10 Conclusion...................................................................................................................................111
6.1 Introduction.................................................................................................................................112
6.2 Implementation Plan...................................................................................................................113
6.3 Testing – Introduction..................................................................................................................113
University Of East London 3 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.4 Unit Testing.................................................................................................................................114
6.4.1 Test Report of Unit Testing..................................................................................................114
6.5 Functional Testing.......................................................................................................................114
6.5.1 Functional Testing (Black Box Testing................................................................................115
6.5.2 Test report of functional testing (Clocking Module)............................................................115
6.5.3 Test report of functional testing (Login module):................................................................117
6.5.3.1 Test report of functional testing (Login by Fingerprint Scanning Module)......................117
6.5.3.2 Test report of functional testing (Login by Username & Password Module)...................119
6.5.4 Test report of functional testing (Managing Users Module).................................................120
6.5.5 Report of functional testing (Managing Bulletins Module)..................................................121
6.6 Usability Testing..........................................................................................................................122
6.7 Requirement traceability matrix...................................................................................................123
6.8 Screenshots..................................................................................................................................124
6.8.1 Fingerprint Scanner Run Time Environment Installation Implementation...........................124
6.8.2 Profiles & Management GUI Implementation.....................................................................125
6.8.3 Admin Main Menu vs. HR Main Menu...............................................................................129
6.8.4 Staff Main Menu..................................................................................................................130
6.8.5 Staff Management................................................................................................................130
6.8.6 Departments Management..................................................................................................133
6.8.7 Leave Component:...............................................................................................................133
6.8.7.1 Leave Management..........................................................................................................133
6.8.8 Report Component:..............................................................................................................135
6.8.8.1 Staff Attendance Report..................................................................................................135
6.8.8.2 Staffs Current Status........................................................................................................136
6.8.8.3 Attendance Management..................................................................................................138
6.9 Conclusion...................................................................................................................................138
7.1 Introduction.................................................................................................................................139
7.2 System Strength...........................................................................................................................139
7.3 Weakness of the system...............................................................................................................140
7.4 Future Enhancement...................................................................................................................141
7.5 Conclusion...................................................................................................................................141
Books.......................................................................................................................................................143
University Of East London 4 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Articles & Whitepapers...........................................................................................................................144
Websites..................................................................................................................................................145
Appendices..............................................................................................................................................146
Gants chart...............................................................................................................................................153
APPENDIX C: Questionnaire Form (Data Gathering)............................................................................154
Questionnaire...........................................................................................................................................154
APPENDIX D: Usability Testing Questionnaire.....................................................................................156
University Of East London 5 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
List of Tables
Table 2.1 comparison of finding ……………………………………………………..……….30
Table 2.2 feature and benefit UareU …………………………………………….……………46
Table 2.3 technical specification of secuGen hamster plus…………………….…….……….49
Table 3.1 interview proceeding ………………………………………..……..……………….58
Table 3.2 comparison of methodology ……………………………………….……………….72
Table 6.1 test report of functional testing 1………….………..……………..………………114
Table 6.2 test report of functional testing 2……………..................................……………...115
Table 6.3 test report of functional testing 3……………..................................……………...117
Table 6.4 test report of functional testing 4…………….................................……………...118
Table 6.5 test report of functional testing 5……………................................……………...119
University Of East London 6 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
List of Figures
Figure 2.3.1 fingerflex clocking in…………………..…….….………………….……22
Figure 2.3.2 fingerflex attendance records………………..….………………….…….23
Figure 2.3.3 time schedule …………………………………………….….…….…….24
Figure 2.3.4 fingerflex plicy …………………………….……………………….…....25
Figure 2.3.5 fingerflex leave form ……………………………………………….…...26
Figure 2.3.6 payment main form ………………….……………………………….…27
Figure 2.3.7 silverLiner Time attendance …………………………………………….28
Figure 2.3.8 silverLiner Time attendance …..………………………………………...29
Figure 2.1.1 fingerprint image acquired …………………………………………..…..31
Figure 2.1.1.2 minutia …………………………………………………………….…..32
Figure 2.2.1 verification vs identification ………………………………………….…33
Figure 2.1.1 simplified fingerprint recognition …………………………………….…35
Figure 2.2.1 minutia extractor …………………………………………………….…..36
Figure 2.2.2 minutia matcher …………………………………………………………37
Figure 2.1.1 the original histogram ……………………………………………….......38
Figure 2.1.3 histogram enhancement …………………………………………………39
Figure 2.2.1 fingerprint image ………………………………………………………...40
Figure 3.1 waterfall diagram ………………………………………………………….65
Figure 3.2 spiral model ………………………………………………………………..66
University Of East London 7 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 3.3 Rational Unified Process image …...…………………………………..…67
Figure 5.1.1 use case diagram ………………………………...………………………94
Figure 5.1.2 use case library ……………..……..……………………………………..95
Figure 5.1.3 false minutia ………………………...…………………………………...96
Figure 5.2 design class diagram ………………………………………...…………….98
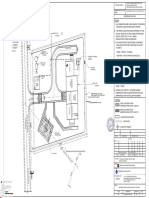
Figure 5.3.1campus entrance clocking ………………………..………………..……100
Figure 5.3.2 profile &management system …………………….……………………101
Figure 5.3.3 sequences diagram ………………………………………………….….102
Figure 4.4 database relationship diagram …………………………………………...103
Figure 5.5 ERD ………………………………………………………………..…….104
Figure 6.3.5 list of all departments ………………………………………………….130
University Of East London 8 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Abstract
Attendance system is proposed the time clack in and out of all the staff at the Yemen
university and will be run through device which is located in the entrance of the campus the
system is using the biometric technology by thumb recognition to trace the staff attendance
.so the admin can followed up with the staff attendance trough this system by being alarmed
of each staff will be using the system .the system will be calculated the business hours that
staff spends daily with ability to indicated the absent and duration that staff will be out office
.the system will be help to provide report of the staff statue during the day
University Of East London 9 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Acknowledgement
In the process of completing this project, I have received a lot of help and support from many
people in order for me to complete this project on time and to make this project a success.
First of all, I would like to thank my supervisor Ms. Kohila for the advices, help and
guidance that are provided to me throughout the process of completing the project.
The cooperation and time that Ms. Kohila had spent in guiding me had provided me with
great help and will be greatly appreciated.
I would also like to thank the my friends for their advice, support, financial helps and also
encouragement, which have motivated and kept me going in order to complete this project .
Chapter 1
University Of East London 10 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Introduction
1.1 Problem Background
The proposed automatic attendance system is using fingerprint Identification technique.
A fingerprint is captured by user interface, which are likely to be an optical, solid state or an
ultrasound sensor, or a 300DPI (Dots per Inch) or above 2D fingerprint image. Generally, there
are two approaches are used for fingerprint Identification system among them first one is
Minutiae based technique, in which minutiae is represented by ending or termination and
bifurcations. Other one is Image based method or matching pattern, which take account of global
feature of any fingerprint image.
The main aim of this system is to develop an accurate, fast and very efficient automatic
attendance system using fingerprint Identification technique for Yemen University staffs. The
system is proposed in which fingerprint identification is done by using extraction of one of the
techniques available and the system that automates the whole process of taking attendance,
Manually which is a laborious and troublesome work and waste a lot of time, with its managing
and maintaining the records for a period of time is also a burdensome task. For this purpose we
use fingerprint identification system using extraction of minutiae techniques.
First, when the user is enrolled to the system his/her fingerprint should be scanned using the
scanner and stored in the database along with his/her identity information.
There will be two modes in the system: staff mode where the staff can monitor their summarized
weekly/monthly attendance. And Admin mode where the admin can monitor all staff attendance
as well as adding, deleting, and updating staff.
1.2 Problem Statement
University Of East London 11 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
In many institutions and organizations the attendance is a very important factor for
various purposes one of the most basic needs for many universities is tracking how long staff
works. Simple time clocks can get the job done, but they don't offer much in the way of insight
into your university and they're relatively easy for staff to fool.
Modern time and attendance systems provide a couple of key benefits: by computerizing your
staff time tracking, they make it possible to integrate with payroll and HR systems and do
detailed reports on work patterns to get a better understanding of your university .
And its one of the important criteria that is to follow for staff and organization’s employees. The
current approach in which is manually taking and maintaining the attendance records is very
inconvenient task.
There are a number of problems associated with paper staff timesheets method.
Forgetfulness: Some staff forgets to complete their timesheets regularly and have to take their
best guess about when they arrived, went for lunch and left for the day. The staff or the
university may lose out.
Time Wasting: With the pen and paper method, Yemen University staffs waste time signing in
and out. Staff take more time to fill the page of the paper to mark the attendance and thereby
queue used to form for just marking the presence.
Rounding up and fraud: Other employees may routinely increase their hours by rounding up their
times. They may do this without thinking, but a few minutes each day can be equivalent to a
week or so over the course of a year. This equates to a week’s pay without the work to show for
it; and if everyone in your company does the same, there’s an impact on efficiency and profits.
Signature copy and misuse leading to fraud in the system.
Administrative headaches: Producing an accurate total for a manual employee timesheet can be
time-consuming and contentious. Employees may make mistakes, so a senior officer has to
check the figures. This officer must then explain any adjustments to the staff member in time to
meet the payroll deadline. If the employee isn’t available, the senior officer has to submit a
revised time sheet that may reduce the amount of pay the employee expects – and this is certain
to cause annoyance.
University Of East London 12 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Maintenance of records: A company must keep paper timesheets in case problems arise in the
future. You may need the sheets at a disciplinary hearing, for instance. You must therefore have
secure storage, which takes up valuable office space.
1.3 Project Objective
The main aim of this system is to develop an accurate, fast and very efficient automatic
attendance system using fingerprint identification technique for Yemen University staffs. The
system is proposed in which fingerprint identification is done by using extraction of one of the
techniques available and the system that automates the whole process of taking attendance,
Manually which is a laborious and troublesome work and waste a lot of time, with its managing
and maintaining the records for a period of time is also a burdensome task. For this purpose we
use fingerprint identification system using extraction of minutiae techniques.
First, when the user is to be enrolled to the system his/her fingerprint should be scanned using
the scanner and stored in the database along with his/her identity information.
There will be two modes in the system: staff mode where the staff can monitor their summarized
weekly/monthly attendance. And Admin mode where the admin can monitor all staff attendance
as well as adding, deleting, and updating staff.
Biometric Yemen University is an advanced staff authentication system which incorporates
biometric technology. In other words, fingerprint identification is used to authenticate the staff
arrival time and more importantly to identify the person. The following modules are included in
this project in order to address the problem mentioned in chapter 2.
Core Modules:
These are the main functionalities and the core of my project
University Of East London 13 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Image processing and enhancement such as binarization, thinning, segmentation and
down sampling.
Fingerprint(template) matching
Database module for storing the fingerprint images.
Enhanced function:
Additional to validating the authenticity of users and capturing the time, the system also aims to
include additional features to make the system more complete. Some such features include:
Generation of appropriate reports that are useful for the management to take appropriate
actions.
User profiling where the user can view their weekly or monthly summarize attendance
Staff management such as monitoring, adding, updating, deleting users.
1.4 Project Scope
Project scope of Biometric Yemen University will be defined based on the functionality
of each component.
The system Biometric Yemen University is a desktop application which offers range of
functionalities for Yemen University Staff. The core venture of this system is to deliver Time &
Attendance system using fingerprint scanner to identify the staffs. This system has been alienated
into 4 modules which include various sub modules. Below stated the three major modules allied
with Biometric Yemen University.
University Of East London 14 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
1. Fingerprint Identification System
2. Campus Entrance Clocking System
3. Profiles & Management System
1.4.1 Functionalities of Fingerprint Identification System
Fingerprint Identification system will be an independent library that is responsible for identifying
users based their fingerprint images. Fingerprint Identification System will held all processing
algorithms e.g. image enhancement (pre-processing), Minutia extraction and minutia matching.
Follow are two major functions of Fingerprint Identification System
1.4.1.1 Minutia Extractor
This function will be to extract minutia from a row fingerprint image. To implement a minutia
extractor, a three-stage approach is widely used by researchers. They are preprocessing, minutia
extraction and post-processing stage
1.4.1.1.1 Preprocessing Functions
Preprocessing functions are to enhance fingerprint images and perform segmentation mask, and
finally binarize the image to be ready form minutiae extraction. Overview of the preprocess
functions are as follow
GrayScale inverter
Histogram Analysis
Segmentation mask
University Of East London 15 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Image equalization
Orientation estimator
Image binarization
1.4.1.1.2 Minutia Extraction Functions
Minutia Extraction takes the final binrized image and does the following processes in order
1- Image thinning
2- Minutia Marking
1.4.1.1.3 Post-processing Functions
minutia that can be found in the previous operation are not all true minutia, here comes the post-
processing functions which is responsible for removing false minutia detected in a fingerprint
image. Filter functions to remove false minutia as stated below
Dot remover filter
Pore remover filter
Gap Remover filter
Tail Remover filter
Fragment Remover filter
Minutia Mask filter
Branch Minutia remover filter
1.4.1.2 Minutia Matcher
The minutia matcher chooses any two minutias as a reference minutia pair and then match their
associated ridges first. If the ridges match well, two fingerprint images are aligned and matching
is conducted for all remaining minutia. The three main functions are as follow
Ridge correlation to specify reference minutia pair
Align two fingerprint images
Minutia match
University Of East London 16 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
1.4.2 Functionalities of Campus Entrance Clocking System
Campus Entrance Clocking system is to be located in main entrance of the university and its
only purpose is to clock in or out staff automatically when they place their thumb on the
fingerprint scanner. This system uses Fingerprint Identification System to authenticate users. The
main functions of this system are stated below
Get fingerprint row image from the Fingerprint Scanner (Digital Persona u.are.u 4500).
Identify user based on the fingerprint collect using the Fingerprint Identification System.
Clock in or out user.
1.4.3 Functionalities of Profiles & Management System
1.4.3.1 User Authorization
This function is to authorize user either by scanning fingerprint thumb, which would give the
user his type’s full functionalities in the system, or by their username and password which will
limit some of their functionalities in the system
1.4.3.2 User Management
Admin Functions:
Add user
Edit user
Delete user
HR Functions (Biometric Login):
University Of East London 17 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Add staffs
Update staffs
Delete staffs
HR Functions (Password Login):
Update staff Info
Delete staffs
Staff Functions:
Edit his/her own basic info
1.4.3.3 Clocking Component
Admin Function:
Clocking user in/out
HR Function (Biometric Login):
Clock staff in/out
Staff Function (Biometric Login):
Clock in/out
1.4.3.4 Attendance Management
Admin Functions:
Edit user attendance record
Add new attendance record
Delete user’s attendance record
HR Functions:
Edit staff attendance record
Add new attendance record
Delete user’s attendance record
University Of East London 18 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
1.4.3.5 Leave Component
Admin Functions:
View all users leave applications
Accept users leave application
Reject users leave application
Review users leave application
Get notification with new leave application from user
HR Functions:
View staff leave application
Accept staff leave application
Reject staff leave application
Review staff leave application
Get notification with new leave application from user
Staff Functions:
Apply Leave
View his/her leave applications
Get notification when HR/Admin responded to his/her leave application.
1.4.3.6 Report Management
Admin Functions:
Generate and view users current status report
Generate and view user attendance report weekly/monthly/all.
HR Functions:
Generate and view users current status report
University Of East London 19 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Generate and view staff attendance report weekly/monthly/all.
Staff Functions:
Generate and view his/her own attendance reports weekly/monthly/all.
1.4.3.7 Bulletin Management
Admin & HR Functions:
Add new bulletin
Edit bulletin
Delete bulletin
Staff Functions:
Get notification about active bulletins
View bulletins
1.4.3.8 Department management
Admin Functions:
Add new department
Edit department
Delete department
University Of East London 20 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
1.5 Project Constraint
1.5.1 Limitations
Thus to complete the system, there are some limitations in the system as the developer will
not be attempting on:
Although this system could be implemented in a network environment, it is planned to
simulate as standalone.
In case the fingerprint scanner does not capture clear and high quality images of the
fingerprint, 2D images of fingerprint would be tested instead.
The system also assumes that fingers are undamaged which means to say that this system
is not capable of dealing with major changes that has been taken place to the finger due to
damages and/or scars.
1.5.2. Time
Time needed to develop the attendance system using the finger print for Yemen
University is defined on the Gantt chart attached to the documentation. The Project
includes many tasks that should be completed on less than three months including
analysis, design, implementation, testing evaluation and documentation. However
developing a system in short period of time is a challenging task which requires a
transaction between different project phases and concentration on the critical areas rather
consuming time on tasks that have a little impact on the system.
1.5.3 Manpower
In this project, a single person has to handle all the phases of an industrial based project in
comparatively short period of time. In real situation more than one people
University Of East London 21 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
specialized on different areas (project manager Architectural designers, server side and
client side programmers, quality assurance personnel) have to communicate in order to
deliver a quality product that meets, the usually excessive and often unrealistic client’s
requirements. However, it can be consider a great challenge for the author.
1.6 Project Stakeholders
Project Stakeholders are anyone who has an interest in the project, or whose interests
maybe affected as a result of project execution or project completion. Project Stakeholders for
This project can divide to:
Project manager: Since this is an individual work, I, the developer, will be responsible for the
development of this project from the start till the end.
User: Users will be the organization that will use the project’s product. Mainly the staff in
Yemen University whose are going to use to the product to clock in and out. An admin in
Yemen University will be responsible to manage and maintain the system.
Performing organization: IT department in Yemen University will be the responsible for
installation and maintenance of the system.
1.7 Project Framework
In the first chapter; Introduction, which will include problem background, problem
statement, project objectives, project scope, project constraints, project stakeholder, and
conclusion of the first chapter.
University Of East London 22 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
In the Second chapter; literature review will include introduction, History of the company,
finding and its comparison, target system, failure story, and conclusion.
Chapter three, Methodology which will include introduction, fact-finding methodology, system
development model, and selective of System Development Methodologies
Chapter four, Analysis will include introduction, overview of the system, types of analysis,
quantitative and qualitative analysis, interviews, manual observation, and summary.
Chapter five, Design will include introduction, overview of the system design, types of design,
use case diagram, class diagram, activity diagram, ERD, and conclusion.
Chapter six, Implementation & Testing will include introduction, system implementation
methods and plan, system testing, screenshots of data entry, and data acceptance results.
Chapter seven, Conclusion of the whole system will include introduction, system strength, and
weakness of the system, future enhancement, and critical summary
1.8 Conclusion
In this first chapter, Introduction, developer explained the problems in the current
system Yemen University is facing. Then he illustrated what will be the objectives of the new
system and scaled the scope of the project with some limitations. After that, the developer
identified who would be the stakeholders of the project. And finally a project framework which
states an overview of what each chapter will consist of.
University Of East London 23 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Chapter 2
Literature view
2.1 Introduction
This chapter starts by shading light on all what finger print for Yemen university staff is
all about. Consequently, the chapter continues with the brief history and profile of the finger
print system from the commencement till today and the establishment of the finger print system
offered good and valuable benefit to the staff in the university by using its touch. This chapter
goes on to identify the literature review and comparison of findings.
2.2 History of the company / Background of Company
The earliest dated prints of the ridged skin on human hands and feet were made about
4,000 years ago during the pyramid building era in Egypt. In addition, one small portion of palm
print, not known to be human, has been found impressed in hardened mud at a 10,000-year old
site in Egypt.
It was common practice for the Chinese to use inked fingerprints on official documents, land
sales, contracts, loans and acknowledgments of debts. The oldest existing documents so endorsed
date from the 3rd century BC, and it was still an effective practice until recent times. Even
though it is recorded that the Chinese used their fingerprints to establish identity in courts in
litigation over disputed business dealings, researchers fail to agree as to whether the Chinese
were fully aware of the uniqueness of a fingerprint or whether the physical contact with
documents had some spiritual significance.
University Of East London 24 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
2.3 Literature Review Finding
Case 1 FingerFlex
FingerFlex is a fingerprint biometric time attendance system and an add-on to
current human resource management helping them to automate data collection and process
timesheets faster designed specifically for the Malaysian market. Developer has investigated the
overall FingerFlex as it posted on their website
Functionalities in FingerFlex Time Attendance as follow
Terminal
No password or cards necessary, FingerFlex Time Attendance will identify the staff clocking in
/ out by just the finger – in a second! So practical that even most IT illiterate staff will know
how to use it.
(Figure 2.3.1; fingerflex Clocking in/out form. taken from http://www.p2digital.com/default.html)
University Of East London 25 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Records
FingerFlex Time Attendance is designed to be used by most average computer users, with no
database and programming skills required. This means, user can have access to the system
without performing any complex database queries or special commands to get the information
required.
(Figure 2.3.2; fingerflex attendance records form. taken from http://www.p2digital.com/default.html)
Schedule
Set as many as work groups and time shifts required by your company by using our intuitive
interface. FingerFlex cater to all time management requirements. User can even have different
University Of East London 26 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
working hours for different groups. The schedule management also adheres to the Malaysian
government agency work schedule requirements.
(Figure 2.3.3; Time schedule. taken from http://www.p2digital.com/default.html)
Policy
FingerFlex Time Attendance has a trigger alert system on monitoring people who are coming
late consistently. You can set your own rules for late attendance and the system will alert you
automatically.
Set rules to monitor late attendance automatically (e.g being late 3 times a month)
Print out a warning letter automatically based on the rules you set.
University Of East London 27 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
(Figure 2.3.4; fingerflex Plicy. taken from http://www.p2digital.com/default.html)
Leave
Staffs taking leave can be recorded within FingerFlex, and will show up in related reports.
University Of East London 28 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
(Figure 2.3.5; fingerflex – Leave form. taken from http://www.p2digital.com/default.html)
Case 2 PayPunch
PayPunch is a Biometric Time Clock & Attendance tracking system that replaces the typical time
clock used to track employees’ attendance. Instead of employees punching a time-card, they
simply insert their hand or a finger into the reader and enter their employee number. Screenshot
of the main menu of Paypunch illustrated below
University Of East London 29 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
(Figure 2.3.6; Paypunch - main form. taken Paypunch demo software)
Functionalities of Paypunch Lite
Manage Department
Manage Employee Info
Manage Attendance records
Leave Application
Report generations
PayPunch uses a biometric device that makes 96 discreet images of the hand and creates a
sophisticated algorithm to generate and store a unique numerical template. Each time an
employee scans his/her hand, a new number is generated and compared to the one on file. The
device accurately identifies the employee and records, their in/out transaction in the payroll
database... all in about 1-second!
University Of East London 30 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The PayPunch does not store images of your employees' hands, nor can it use any stored
information to create images of employees' hands. It does not x-ray and there is no exposure to
anything harmful whatsoever. It is an accurate measurement device for identification and
reporting purposes.
SilverLiners Time Attendance Suite 2009
SilverLiners Time Attendance System (http://www.silverliners.net/) is an application
software that help to Collect employees accurate Time in or out data using USB Fingerprint
Scanner or Keyboard, to define effective policies such as shift, Leave, OUT, Late, Absence and
Break-time policies, to create Employee Scheduling with no sweat4.Keep track of working time,
overtime, vacation days, any kind of leaves, and holidays for each employee, and to generate
various types of reports on employee time attendance data.
Case 3 screen shot of SilverLiners Time Attendance Suite as follow
(Figure 2.3.7; SilverLiner Time Attendance - attendance form. taken SilverLiner demo software)
Attendance records:
University Of East London 31 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
(Figure 2.3.8; SilverLiner Time Attendance - attendance records form. taken SilverLiner demo
software)
Functionalities of SilverLiner Time Attendance Suite 2009
Clock In/Out
Employee management
Add/update/delete Department
Add/update delete attendance records
Leave Application
Report generations
University Of East London 32 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
2.4 Comparisons of finding
Functions FingerFlex Silver Liner Paypunch ASYU
Profiles supports user support user doesn’t support Will support
profiles profiles profiles profiles
Leaves support Applying Support Leaves Doesn’t support Will support
for leave applying for leave Leave Application
Usability forms are Constant Tasks are Forms will be
consistent, common navigation grouped and constant with
tasks are made, through forms. visible, grouped functions
grouping functions Few functions Feedbacks when to easily navigate
is poor availability in a an action is taken. to, buttons and
single form. links shall be
visible, and
feedback to
inform the users
what is currently
going on or has
been done.
Attendance Attendance records Basic info Due to the many Records shall be
Record are displayed in displayed along function in the displayed in
report format and with the main frame, it report format with
have no detailed attendance record. made the detailed info of
information for Undesirable attendance each record for
each record. format of records not easily each user.
displaying record noticed and
format. visible.
Reports Reports are Generation of Detailed reports Reports are
generated easily report is done are generated generated easily
University Of East London 33 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
with fewer steps automatically with more steps with fewer steps
required to perform with detailed info. required to required to
this task however perform this perform this task.
the reports are not action. Generation of
very detailed. report is done
automatically
with detailed info.
[Figure2.3.9 finding comparison]
2.5 Academic/Technology Research:
2.5.1 Fingerprint Recognition
2.5.1.1. What is A Fingerprint?
A fingerprint is the feature pattern of one finger (Figure 1.1.1). It is believed with strong
evidences that each fingerprint is unique. Each person has his own fingerprints with the
permanent uniqueness. So fingerprints have being used for identification and forensic
investigation for a long time.
[Figure1.1.1 A fingerprint image acquired by an Optical Sensor. Taken from Handbook of
Fingerprint Recognition by Davide Maltoni, Dario Maio, Anil K. Jain, Salil Prabhakar.]
A fingerprint is composed of many ridges and furrows. These ridges and furrows present good
similarities in each small local window, like parallelism and average width.
University Of East London 34 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
However, shown by intensive research on fingerprint recognition, fingerprints are not
distinguished by their ridges and furrows, but by Minutia, which are some abnormal points on
the ridges (Figure 1.1.2). Among the variety of minutia types reported in literatures, two are
mostly significant and in heavy usage: one is called termination, which is the immediate ending
of a ridge; the other is called bifurcation, which is the point on the ridge from which two
branches derive.
[Figure 1.1.2 Minutia. (Valley is also referred as Furrow, Termination is also called Ending,
and Bifurcation is also called Branch) Taken from Handbook of Fingerprint Recognition by
Davide Maltoni, Dario Maio, Anil K. Jain, Salil Prabhakar.]
2.5.1.1.2 What is Fingerprint Recognition?
The fingerprint recognition problem can be grouped into two sub-domains: one is fingerprint
verification and the other is fingerprint identification (Figure 1.2.1). In addition, different from
the manual approach for fingerprint recognition by experts, the fingerprint recognition here is
referred as AFRS (Automatic Fingerprint Recognition System), which is program-based.
University Of East London 35 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
[Figure 1.2.1 Verification vs. Identification; Taken from Handbook of Fingerprint
Recognition by Davide Maltoni, Dario Maio, Anil K. Jain, Salil Prabhakar.]
Fingerprint verification is to verify the authenticity of one person by his fingerprint. The user
provides his fingerprint together with his identity information like his ID number. The fingerprint
verification system retrieves the fingerprint template according to the ID number and matches
the template with the real-time acquired fingerprint from the user. Usually it is the underlying
design principle of AFAS (Automatic Fingerprint Authentication System).
(Nalini Ratha Ruud Bolle, 2003 in their AFIS book) stated that Fingerprint identification is to
specify one person’s identity by his fingerprint(s). Without knowledge of the person’s identity,
the fingerprint identification system tries to match his fingerprint(s) with those in the whole
fingerprint database. It is especially useful for criminal investigation cases. And it is the design
principle of AFIS (Automatic Fingerprint Identification System).
However, all fingerprint recognition problems, either verification or identification, are
ultimately based on a well-defined representation of a fingerprint. As long as the representation
University Of East London 36 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
of fingerprints remains the uniqueness and keeps simple, the fingerprint matching, either for the
1-to-1 verification case or 1-to-m identification case, is straightforward and easy.
2.5.1.1.3 Two approaches for Fingerprint recognition
Two representation forms for fingerprints separate the two approaches for fingerprint
recognition.
The first approach, which is minutia-based, represents the fingerprint by its local features, like
terminations and bifurcations. This approach has been intensively studied, also is the backbone
of the current available fingerprint recognition products. I also concentrate on this approach in
my honors project.
The second approach, which uses image-based methods(L.C. Jain, U.Halici, I. Hayashi, S.B.
Lee and S.Tsutsui, (1999))., tries to do matching based on the global features of a whole
fingerprint image. It is an advanced and newly emerging method for fingerprint recognition. And
it is useful to solve some intractable problems of the first approach. But my project does not aim
at this method, so further study in this direction is not expanded in my thesis.
2.5.1.2 System design – Fingerprint Recognition System
2.5.1.2.1 System Level Design
A fingerprint recognition system constitutes of fingerprint acquiring device, minutia extractor
and minutia matcher [Figure 2.1.1].
University Of East London 37 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 2.1.1 Simplified Fingerprint Recognition System. Taken from Handbook of Fingerprint
Recognition by Davide Maltoni, Dario Maio, Anil K. Jain, Salil Prabhakar .
For fingerprint acquisition, optical or semi-conduct sensors are widely used. They have high
efficiency and acceptable accuracy except for some cases that the user’s finger is too dirty or dry.
Fingerprint sensor is used as will as the testing database for Biometric ASYU system is from the
available fingerprints provided by FVC2002 (Fingerprint Verification Competition 2002).
The minutia extractor and minutia matcher modules are explained in detail in the next part for
algorithm design and other subsequent sections.
University Of East London 38 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
2.5.1.2.2 Algorithm Level Design
To implement a minutia extractor, a three-stage approach is widely used by researchers. They
are preprocessing, minutia extraction and post processing stage [Figure 2.2.1].
Figure 2.2.1 Minutia Extractor; Taken from Handbook of Fingerprint Recognition by Davide
Maltoni, Dario Maio, Anil K. Jain, Salil Prabhakar.]
For the fingerprint image preprocessing stage, Histogram Equalization and Fourier
Transform are used to do image enhancement. And then the fingerprint image is binarized using
the locally adaptive threshold method (L.C. Jain, U.Halici, I. Hayashi, S.B. Lee and S.Tsutsui,
(1999)). The image segmentation task is fulfilled by a three-step approach: block direction
estimation, segmentation by direction intensity (N. Ratha, S. Chen and A.K. Jain, (1995). pp.
1657-1672) and Region of Interest extraction by Morphological operations. Most methods used
in the preprocessing stage are developed by other researchers but they form a brand new
combination in this project through trial and error.
For minutia extraction stage, three thinning algorithms (L.C. Jain, U.Halici, I. Hayashi, S.B.
Lee and S.Tsutsui, (1999); D.Maio and D. Maltoni, (1997). 19(1):27-40) are tested and the
Morphological thinning operation is finally bid out with high efficiency and pretty good thinning
quality. The minutia marking is a simple task as most literatures reported but one special case is
University Of East London 39 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
found during my implementation and an additional check mechanism is enforced to avoid such
kind of oversight.
For the post processing stage, a more rigorous algorithm is developed to remove false minutia
based on (Lin Hong, (1998); L.C. Jain, U.Halici, I. Hayashi, S.B. Lee and S.Tsutsui, (1999)).
Also a novel representation for bifurcations is proposed to unify terminations and bifurcations.
Figure2.2.2 Minutia Matcher; Taken from Handbook of Fingerprint Recognition by Davide Maltoni,
Dario Maio, Anil K. Jain, Salil Prabhakar.
The minutia matcher chooses any two n match well, two fingerprint images are aligned and
matching is conducted for all remaining minutia [Figure 2.2.2].
2.5.1.3 Fingerprint Image Preprocessing:
2.5.1.3.1 Fingerprint Image Enhancement
Fingerprint Image enhancement is to make the image clearer for easy further operations.
Since the fingerprint images acquired from sensors or other Medias are not assured with perfect
quality, those enhancement methods, for increasing the contrast between ridges and furrows and
for connecting the false broken points of ridges due to insufficient amount of ink, are very useful
for keep a higher accuracy to fingerprint recognition.
University Of East London 40 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Two Methods are adopted in this project: the first one is Histogram Equalization; the next
one is Fourier Transform.
2.5.1.3.1.1 Histogram Equalization:
Histogram equalization is to expand the pixel value distribution of an image so as to increase
the perceptional information. The original histogram of a fingerprint image has the bimodal type
[Figure 3.1.1.1], the histogram after the histogram equalization occupies all the range from 0 to
255 and the visualization effect is enhanced [Figure 3.1.1.2].
Figure 3.1.1 the Original histogram Figure 3.1.2 Histogram after the
of a fingerprint image Histogram Equalization
The right side of the following figure [Figure 2.1.1.3] is the output after the histogram
equalization.
University Of East London 41 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 2.1.3: Histogram Enhancement; Original Image (Left). Enhanced image (Right)
Taken from Handbook of Fingerprint Recognition by Davide Maltoni, Dario Maio, Anil K. Jain, Salil
Prabhakar.
2.5.1.3.2 Fingerprint Image Binarization
Fingerprint Image Binarization is to transform the 8-bit Gray fingerprint image to a 1-bit image
with 0-value for ridges and 1-value for furrows. After the operation, ridges in the fingerprint are
highlighted with black color while furrows are white.
A locally adaptive binarization method is performed to binarize the fingerprint image. Such a
named method comes from the mechanism of transforming a pixel value to 1 if the value is
larger than the mean intensity value of the current block (16x16) to which the pixel belongs
Figure 3.2.1.
University Of East London 42 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 3.2.1 the Fingerprint image after adaptive binarization; Binarized image(left), Enhanced gray
image(right); Taken from Handbook of Fingerprint Recognition by Davide Maltoni, Dario Maio, Anil K. Jain,
Salil Prabhakar.
2.3.3 Fingerprint Image Segmentation
In general, only a Region of Interest (ROI) is useful to be recognized for each fingerprint
image. The image area without effective ridges and furrows is first discarded since it only holds
background information. Then the bound of the remaining effective area is sketched out since the
minutias in the bound region are confusing with those spurious minutias that are generated when
the ridges are out of the sensor.
To extract the ROI, a two-step method is used. The first step is block direction estimation and
direction variety check (N. Ratha, S. Chen and A.K. Jain, (1995). pp. 1657-1672), while the
The direction map is shown in the following diagram. We assume there is only one fingerprint in
each image.
University Of East London 43 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 3.3.1.1 Direction map. Binarized fingerprint (left), Direction map (right);
Taken from Handbook of Fingerprint Recognition by Davide Maltoni, Dario Maio, Anil K. Jain, Salil
Prabhakar.
1. ROI extraction by Morphological operations
Two Morphological operations called ‘OPEN’ and ‘CLOSE’ are adopted. The ‘OPEN’
operation can expand images and remove peaks introduced by background noise The ‘CLOSE’
operation can shrink images and eliminate small cavities.
University Of East London 44 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 2.3.3After OPEN operation Figure 2.3.4 ROI + Bound
They show the interest fingerprint image area and it’s bound. The bound is the
subtraction of the closed area from the opened area. Then the algorithm throws away those
leftmost, rightmost, uppermost and bottommost blocks out of the bound so as to get the tightly
bounded region just containing the bound and inner area.
2.4.1 Fingerprint Ridge Thinning
Ridge Thinning is to eliminate the redundant pixels of ridges till the ridges are just one
pixel wide. (L.C. Jain, U.Halici, I. Hayashi, S.B. Lee and S.Tsutsui, 1999) uses an iterative,
parallel thinning algorithm. In each scan of the full fingerprint image, the algorithm marks down
redundant pixels in each small image window (3x3). And finally removes all those marked pixels
after several scans. (D.Maio and D. Maltoni, (1997). IEEE 19(1):27-40) uses a one-in-all method
to extract thinned ridges from gray-level fingerprint images directly. Their method traces along
the ridges having maximum gray intensity value. However, binarization is implicitly enforced
since only pixels with maximum gray intensity value are remained.
University Of East London 45 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The thinned ridge map is then filtered by other three Morphological operation to remove
some H breaks, isolated points and spikes.
2.4.2 Minutia Marking
After the fingerprint ridge thinning, marking minutia points is relatively easy. But it is
still not a trivial task as most literatures declared because at least one special case evokes my
caution during the minutia marking stage.
In general, for each 3x3 window, if the central pixel is 1 and has exactly 3 one-value neighbors,
then the central pixel is a ridge branch [Figure 4.2.1]. If the central pixel is 1 and has only 1 one-
value neighbor, then the central pixel is a ridge ending [Figure3.2.5].
0 1 0 0 0 0 0 1 0
0 1 0 0 1 0 0 1 1
1 0 1 0 0 1 1 0 0
Figure 4.2. Bifurcation Figure 4.2.2 Termination Figure 4.2.3 Triple counting
branch
Taken from Handbook of Fingerprint Recognition by Davide Maltoni, Dario Maio, Anil K. Jain, Salil
Prabhakar.
Figure 4.2.3 illustrates a special case that a genuine branch is triple counted. Suppose both the
uppermost pixel with value 1 and the rightmost pixel with value 1 have another neighbor outside
the 3x3 window, so the two pixels will be marked as branches too. But actually, only one branch
is located in the small region. So a check routine requiring that none of the neighbors of a branch
are branches is added.
University Of East London 46 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Also the average inter-ridge width D is estimated at this stage. The average inter-ridge width
refers to the average distance between two neighboring ridges. The way to approximate the D
value is simple. Scan a row of the thinned ridge image and sum up all pixels in the row whose
value is one. Then divide the row length with the above summation to get an inter-ridge width.
For more accuracy, such kind of row scan is performed upon several other rows and column
scans are also conducted, finally all the inter-ridge widths are averaged to get the D.
Together with the minutia marking, all thinned ridges in the fingerprint image are labeled with a
unique ID for further operation. The labeling operation is realized by using the Morphological
operation.
University Of East London 47 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
2.5.2 Fingerprint Scanner Research
The developer of Biometric ASYU system stated that the fingerprint image would be
acquired using a fingerprint sensor/scanner. Research has been conducted to find the suitable
affordable Fingerprint scanner for the system.
Developer has narrowed down the choices to two sensors from two different companies, Digital
Persona U.are.U 4500 and SecuGen Hamster Plus.
2.5.2.1 DigitalPersona U.are.U 4500
The DigitalPersona U.are.U 4500 Fingerprint Reader is
an optical USB 2.0 fingerprint scanner suitable for most users
in common or shared computer environments. The reader is
easy to install and use. U.are.U 4500 accommodates the widest
range of fingerprint and skin conditions.
The U.are.U 4500 Reader is a USB fingerprint reader featuring
an elegant, sleek design with a soft, blue glow and the unsurpassed performance DigitalPersona
is known for. Made for power-users and shared environments, the 4500 is the natural choice for
those that want and need the very best. Here’s a look at just some of its features and benefits:
Blue LED Soft, cool blue glow fits into any environment. Provides a
pleasing presence; does not compete in low light environments,
such as restaurants, or conflict with alarm condition colors, such
as in healthcare.
Small form factor Conserves valuable desk space.
Rugged construction High-quality metal casing weighted to resist unintentional
movement.
University Of East London 48 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Special undercoating Stays where you put it because of a special undercoating.
Rotation invariant Touch it from any direction, it still provides a high quality image
and matching performance, perfect for shared environments.
Excellent image High-quality optics ensure best image every time.
quality
Works well with dry, Reliable performance over the widest population of users. Reads
moist, or rough even the most difficult fingerprints.
fingerprints
Table 2.1Features & benefits of DigitalPersona u.are.u 4500 ]
4500HD - High-Durability Model
(DigitalPersona, Inc. website) The 4500HD was specifically designed for business critical
applications that require a high-level of durability from fingerprint readers but still need a high
degree of accuracy. When deployed in a shared environment, fingerprint readers are commonly
subjected to harsh use and outright vandalism that can significantly reduce their performance or
break the device. To counter this, the 4500HD Reader has a super tough coating that stands up to
physical and chemical abuse while delivering unequaled accuracy and performance for hard-to-
read fingerprints.
The U.are.U 4500 and 4500HD fingerprint readers are designed for use with Digital Persona's
full range of software: Digital Persona Pro for Active Directory and Digital Personal SDKs for
your own applications.
Easy-to-use
To use, simply place a finger on the reader window and the reader quickly and automatically
captures and encrypts the fingerprint image before sending it to the Digital Persona ID entity
Engine for verification.
University Of East London 49 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Specifications of the Reader
Device name U.are.U 4500 Reader
Manufacturer DigitalPersona, Inc.
Device connection USB 2.0
Supported OS (1) Microsoft Windows (32bit)
Sensor resolution 512 dpi
Image capture area
15 x 18 mm (0.6" x 0.7")
(Platen size)
Sensor type Optical
Illumination Blue LEDs
Device size 65 x 36 x 16 mm (2.6" x 1.4" x 0.6")
Operating temperature 0°C ~ +40°C
Operating humidity 20-80 % (non-condensing)
Table 2.2 Features & benefits of DigitalPersona u.are.u 4500, (Biometric Supply, 2009)]
SDK (Software Development Kit)
SDK/API is very important to invoke the functionalities of the reader. SDK comes with
simple fingerprint verification algorithm but Biometric ASYU system requires Fingerprint
Identification and the scanner SDK/API would be used only to get a row image of the
fingerprint, and then the system itself will do its job buy processing the image, extract the
features and store the template in the database.
The product supports the following operating environments:
Windows 7 (32/64-bit), Vista (32/64-bit), XP (32/64-bit), XP Embedded (32-bit)
and Server 2003/2008 (32/64-bit)
Citrix Presentation Client/Server
Windows Terminal Services including RDP
Microsoft .NET
Java
University Of East London 50 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
2.5.5.2.1 SecuGen Hamster Plus
SecuGen Hamster Plus is the improved version of SecuGen's popular and
versatile fingerprint reader product line, with Auto-On™ and Smart
Capture™. Packaged in a comfortable, ergonomic design, the Hamster
Plus features the industry's most rugged and advanced optical sensor
using patented SEIR fingerprint biometric technology.
Auto-On™ is an Automatic Finger Placement Detection technology that
automatically checks for the presence of a finger. When used with Auto-
On-compatible software, the Hamster Plus will turn on and scan user
finger as soon as the user touches the sensor - all without having to prompt the system.
SecuGen Hamster Plus can be used for authentication, identification and verification functions
that let your fingerprints act like digital passwords that cannot be lost, forgotten or stolen. Check
with your software provider to ensure that the software works with Auto-On.
Features
SecuGen Hamster Plus
- High-performance, maintenance-free optical fingerprint sensor
- Sensor resistant to scratches, impact, vibration and electrostatic shock
- Auto-On™ (Automatic Finger Placement Detection)*
- Smart Capture™ (Self-Adjusting Fingerprint Brightness)
- USB connection
- Removable weighted stand
- Compact, lightweight and portable
- Integrated finger guide
- Readily accessible for any finger
- Driver CD included
- Three year limited warranty
Technical Specifications
University Of East London 51 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Fingerprint Sensor SecuGen USB Sensor
Dimensions (w/o stand) 1.1" x 1.6" x 2.9" (27 x 40 x 73 mm)
Weight (w/o stand) 3.5 oz. (100 g)
Resolution 500 dpi + 0.2%
Verification Time Less than 1 second
Operating Temperature 32° to 104°F (0° to 40°C)
Operating Humidity < 90% relative, non-condensing
Interface USB 1.1, 2.0
Supported Operating Systems Windows 7 / Vista / Server 2003 / XP / 2000 / Me / 98
Certifications FCC, CE, RoHS
[Technical Specification of SecuGen Hamster Plus]
SDK (Software Development Kit)
SDK/API is very important to invoke the functionalities of the reader. SDK comes with
simple fingerprint verification algorithm but Biometric ASYU system requires Fingerprint
Identification and the scanner SDK/API would be used only to get a row image of the
fingerprint, and then the system itself will do its job buy processing the image, extract the
features and store the template in the database.
Following are some features and requirement that would be related to the development of
Biometric ASYU system.
Requirements
Windows 7 / Vista / Server 2003 / XP / 2000 / ME / 98SE
Pentium processor or later
Installation of BioAPI framework
Includes
University Of East London 52 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Runtime modules
INI file
Skin modules
BioAPI sample application
User Manual
2.5.3 Programming Language Research
The most popular programming language in design such Biometric ASYU system are
Java, C#, Visual Basic, and MATLAB. Since C# and Visual Basic share the same .Net
framework, the developer decided to compared one of the mentioned .NET programming
language, Java, and MATLAB.
2.5.3.1 MATLAB Programming Language
MATLAB is a high-level technical computing language and interactive environment for
algorithm development, data visualization, data analysis, and numeric computation (Giora
Maymon, (2008). P. 305). Using the MATLAB product, programmers can solve technical
computing problems faster than with traditional programming languages, such as C, C++, and
Fortran.
Programmers can use MATLAB in a wide range of applications, including signal and image
processing, communications, control design, test and measurement, financial modeling and
analysis, and computational biology. Add-on toolboxes (collections of special-purpose
MATLAB functions, available separately) extend the MATLAB environment to solve particular
classes of problems in these application areas.
University Of East London 53 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
MATLAB provides a number of features for documenting and sharing programmer’s work.
MATLAB code can be integrated with other languages and applications, and distribute
MATLAB algorithms and applications.
Key Features
High-level language for technical computing
Development environment for managing code, files, and data
Interactive tools for iterative exploration, design, and problem solving
Mathematical functions for linear algebra, statistics, Fourier analysis, filtering,
optimization, and numerical integration
2-D and 3-D graphics functions for visualizing data
Tools for building custom graphical user interfaces
Functions for integrating MATLAB based algorithms with external applications and
languages, such as C, C++, Fortran, Java, COM, and Microsoft Excel
2.5.3.2 Java
Java is a programming language originally developed by James Gosling at Sun
Microsystems (which is now a subsidiary of Oracle Corporation) and released in 1995 as a core
component of Sun Microsystems' Java platform. The language derives much of its syntax from C
and C++ but has a simpler object model and fewer low-level facilities (Jon Byous, (1998). Sun
Developer Network). Java applications are typically compiled to byte code (class file) that can
run on any Java Virtual Machine (JVM) regardless of computer architecture.
Java has Java Advanced Imaging which would be very useful in design such at Biometric
ASYU system that has extensive image processing programming. Sun Developer Network SDN
states that “The Java Advanced Imaging API broadens the reach of the Java platform to allow
sophisticated, high performance image processing functionality to be incorporated into Java
applets and applications”.
Java Advanced Imaging API offers unique advantages for imaging professionals
University Of East London 54 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Reduce Time-to-Market:
Its easy-to-use programming model simplifies the tasks required to creating imaging
software, therefore, reducing the time to develop applications.
Network-Centric:
Because it is built on the network-centric Java Platform, developers can use this to build
collaborative applications for high-end image processing and visualization over the
network.
Imaging Standard for the Future:
It offers the first Java based open-specification, cross platform, extensible imaging API,
and enabling developers to focus on creating the right applications regardless of the
disparate computing platforms.
Programs written in Java have a reputation for being slower and requiring more memory
than those written in C. (Jelovic, Dejan, "Why Java Will Always Be Slower than C++")
However, Java programs' execution speed improved significantly with the introduction of Just-
in-time compilation in 1997/1998 for Java 1.1, (Andy Patrizio (2006)) the addition of language
features supporting better code analysis (such as inner classes, StringBuffer class, optional
assertions, etc.), and optimizations in the Java Virtual Machine itself, such as HotSpot becoming
the default for Sun's JVM in 2000.
2.5.3.3 C# (C Sharp)
C# is an object-oriented programming language developed by Microsoft Corporation as
part of their .NET initiative in response to the success of Sun Microsystems' Java programming
language. C# source code—as well as those of other .NET languages—is compiled into an
intermediate byte code called MSIL (Microsoft Intermediate Language). C# is primarily derived
University Of East London 55 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
from the C, C++, and Java programming languages with some features of Microsoft's Visual
Basic in the mix.
C# is used to develop applications for the Microsoft .NET environment. .NET offers an
alternative to Java development. Microsoft's Visual Studio .NET development environment
incorporates several different languages including ASP.NET, C#, C++, and J# (Microsoft Java
for .NET), all of which compile to the Common Language Runtime.
Working with Images in the .NET Framework:
Biometric ASYU system require extensive of image processing methods. .Net Framework has
The System.Drawing.Imaging Namespace that allows the programmer to interact with
images. .Net framework support different image format. all the image formats that the .NET
Framework supports. BMP is the standard image format used by Windows to store images.
Additionally, you can set the number of colors a BMP image can support. The number of bits
used to store each pixel determines the total number of possible colors that could be assigned to
that pixel and subsequently the color map of the image itself. The number of bits per pixel for
BMP files is specified in the file header and can vary from 1 to 64. Commonly used values are 1,
4, 8, and 24. BMP files are usually not compressed and therefore are not well-suited for transfer
across the Internet
C# is a language in itself. It can perform mathematical and logical operation, variable
assignment and other expected traits of a programming language. This in itself is not flexible
enough for more complex applications. At some stage, the developer will want to interact with
the host system whether it be reading files or downloading content from the internet.
The .NET framework is a toolset developed for the Windows platform to allow the developer to
interact with the host system or any external entity whether it be another process, or another
computer. The .NET platform is a Windows platform specific implementation. Other operating
systems have their own implementations due to the differences in the operating systems I/O
management, security models and interfaces.
University Of East London 56 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
2.5.3.4 Conclusion of Programming research
Matlab would be the best in implementing complex mathematical algorithms but when it
comes to GUI and database connection it is not helpful as the other two. Due to mostly the
familiarity developer chose C# programming language. Detailed analysis of the chosen
programming language is in analysis chapter
2.5 Target System
The comparison made for the pros and cons between two online ordering/purchase systems as
aforementioned, has provided a clearer understanding and concept in constructing the new
system proposed in this project.
Below are the specifications for the new system,
1. Profiles
Each user of the system will have a profile where they can monitor and track their
attendance summary and clock in/out.
2. Leaves
Leave function will be supported to allow the user to apply for leave and the
administration & HR will be notified to response to the leave application requested by the
user.
3. Usability
Forms will be constant with grouped functions to easily navigate from one form/function
to another, buttons and links shall be visible, and feedback to inform the users what is
currently going on or has been done.
University Of East London 57 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
4. Reports
Attendance record reports will be generated for all users or each user of the system and a
report of the current status of all users.
2.6 Conclusion
In summary, after done the background and history of the company and the literature
review and the comparison of the sample system. Structure for the new system is planed base
on the idea, concept which gathered in this chapter. A new technology fingerflex is able to
improve the features and user interface of this system and it might include in the future
enhancement.
Chapter 3
Methodology
3.1 Introduction
University Of East London 58 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Methodology is defined as the analysis of the principles of methods, rules, and postulates
employed by a discipline and it’s includes the following concepts as they related to a particular
discipline or field of inquiry.
A collection of theories, concepts or ideas;
Comparative study of different approaches; and
Critique of the individual methods
3.2 Fact Findings Methodology
Fact finding is the process of using research, interviews, questionnaires, samplings and
Other techniques to collect information about systems, requirements and preferences. It is also
known as information gathering or data collection.
Fact finding is important in system planning and system analysis phases because it is during
these phases that the analyst learns about the vocabulary, problems, opportunities, constraints,
requirements, and priorities of a system.
There are seven common fact-finding techniques as below
Sampling of existing documentation, forms, and databases.
Research and site visits
Observation
Questionnaires
Interview
(General Information on Fact-Finding. Colorado University. Accessed 17 November 2008)
Gathering User Requirements
A good set of user requirements are needed for any project, especially computer system
projects, to be successful. This is where many projects fail, in that they do not specify correctly
what the system should do. In fact many systems have just been given a deadline for delivery, a
budget to spend, and a vague notion of what it should do.
The root of this problem is:
University Of East London 59 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Computer systems developers rarely have as good an idea of how a business runs and
should run, compared with a business user,
Business users have little idea of what a computer system could achieve for them.
As a result paralysis sets in and business management time is concentrated on meeting timescales
and budgets, rather than what is going to be delivered.
3.2.1 Interviews
Goals are important information that can be gleaned from interviewing. The Facts that the
developer obtain from hard data may explain past performance, but goals project the
organization’s future. Developer may not be able to determine goals through any other data-
gathering methods.
In doing qualitative research there is often the need to conduct interviews for the purpose of data
collection.
Developer had a good understanding of the context of the situation before beginning the
interview. While both interviews conducted with YEMENI UNIVERSITY staff, the developer as
the analyst had to understand the organization and its industry setting and a clear understanding
of the objectives and aims of the research project.
Interview
The interview used a general guide and a list of topics and question. This type of interview has
the advantage of allowing an interviewer (developer) to concentrate on specific topics and issues
regarding the current staff time and attendance system.
Interview
University Of East London 60 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Interview Proceeding: No 1
Interviewer Mr. Raed mohammed Mubarak
Interviewee Mr. mohammed Adnana
Position Yemen University Human Resource Manager
Location Yemen University level ground
Date & Time
Objective To understand the current work environment, the flows
prevailing in the currents systems and which would be the
possible remedies expected by the staffs.
Table 3.1 interview proceeding table
Mr. Mohammed Adnan Yemen University Human Resource Manager.
Type of the interview is semi-structured interview.
The purpose of this interview is to have fully understanding of YEMENI UNIVERSITY
operations and issues of the current system they are using in taking the attendance. And also to
get other features the management would like to have in a new system.
[Question -> Question asked to interviewee, Answer->answer given by the interviewee,
Reason-> Reason behind the question, Conclusion scrutiny of the answer]
Those are the questions that will be asked in Interview 1 below:
Question: What is the current method the staffs use to clock in and out? Briefly describe.
Question: How the management track staffs attendance?
University Of East London 61 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Question: What is the college policy in dealing with a staff who forgets to sign in or out from
the system?
Question: what are the procedures taken by the management if a staff clock in 10 minutes late or
clock out before the time he or she suppose to leave?
Question: Is the starting and ending time or work different from department to another?
Question: is there an overtime work for the staff?
The list of questions were asked and their answers are in next chapter in the analysis section
Survey
The main objective of this survey it to gather information which will be used for the
development of Attendance System using Fingerprint for Yemen University staff
Question
Personal Information:
1) Your job position: ________________________.
2) Department : _______________________.
3) What is your age range?
Below 18
18-27
28-37
University Of East London 62 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
38-55
Above 55
4) Your working days: (Pick the days you are working on)
Mon Tue Wed Thu Fri Sat Sun
5) Your working time:
Fixed; Start at: ______ AM/PM End at: _________ AM/PM.
Variable
Question
In your opinion the current staff attendance system (paper-based) in Yemen University is:
Excellent
Good
Satisfactory
Average
Poor
Question
What is the approximate time taken to sign in and off to record your attendance?
___________Minute(s).
Question
“Buddy punching” in manually attendance system is when somebody signs for somebody
in his/her absence. Do you agree these problems happen in the real world in such
attendance systems?
Yes No
Question
In your opinion if the “buddy punching” problem is really happening, what is the best
strategy to overcome these problems?
University Of East London 63 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Using a biometric system, such as fingerprint so that the person would be validated
based on the biological structure of the finger rather than any type.
Using Card swipe, to avoid “buddy punching” an additional staff is needed to be
employed to make sure nobody misuses the system.
Using the same manual system, employ additional staff to make sure that nobody
misuses the system
Question
What do you like about the current staff attendance system? Please state two
1- _________________________________________
2- _________________________________________
Question
What do you dislike about the current system? Please state two
1-_________________________________________
2-_________________________________________
Question
Do you have any experience with any biometric user authenticating system?
Yes No
Question
Would you encourage using Fingerprint Identification staff time & attendance?
Yes No I don’t know
University Of East London 64 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Question
(In the proposed system, each staff would be able to not only clock-in and out to record
the time but also to log in and to view his/her profile and report)
What would you like to see in your profile other than your attendance summary?
The purpose of this survey is to identify the requirement of the system and more specifically to
get advice on the technical aspects from the system.
The list of questions were asked and their answers are in section next chapter in the analysis
section
3.2.2 Questionnaire
Questionnaires are an inexpensive way to gather data from a potentially large number of
respondents (Bell, J (1998)). Often they are the only feasible way to reach a number of reviewers
large enough to allow statistically analysis of the results. A well-designed questionnaire was
distributed among the staff of YEMENI UNIVERSITY to gather information on both the overall
performance of the current system as well as information for the system being developed.
Although questionnaires may be cheap to administer compared to other data collection
methods, they are every bit as expensive in terms of design time and interpretation. (Denial,
2006)
The questionnaire conducted and its answers are in next chapter analysis chapter.
University Of East London 65 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
University Of East London 66 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
3.3 Software Development Methodology
Software engineering is the practice of using selected process techniques to improve the
quality of a software development effort. This is based on the assumption, subject to endless
debate and supported by patient experience, that a methodical approach to software development
results in fewer defects and, therefore, ultimately provides shorter delivery times and better value
(James R, 2004).The documented collection of policies, processes and procedures used by a
development team or organization to practice software engineering is called its software
development methodology (SDM) or system development life cycle (SDLC).
3.4 Waterfall Model
Rather than try to give an all-encompassing definition for methodologies that should be
classified as waterfall approaches, it easier to describe just some common
characteristics. Primarily, a waterfall methodology structures a project into distinct phases with
defined deliverables from each phase. The phases are always named something different,
depending on which company is trying to differentiate its own particular flavor, but the basic
idea is that the first phase tries to capture What the system will do its requirements, the second
determines How it will be designed, in the middle is the actual programming, the fourth phase is
the full system Testing, and the final phase is focused on Implementation tasks such as go-live,
training, and documentation.
University Of East London 67 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 3.1.: Steps in a typical waterfall development method life cycle (Leonid information-
systems image, 2009)
A project schedule with 20-40% of the time budgeted for the first two phases, 30-40% of
the time to the programming, and the rest allocated to testing and implementation time. The
actual project organization tends to be highly structured. Most medium to large size projects will
include a rigidly detailed set of procedures and controls to cover everything from the types of
communications to use in various situations, to authorizing and tracking change orders, to the
specific ways that defects are logged, communicated, resolved, and re-tested.
University Of East London 68 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
3.5 Spiral Methodology
While the waterfall methodology offers an orderly structure for software development,
demands for reduced time-to-market make its series steps inappropriate. The next evolutionary
step from the waterfall is where the various steps are staged for multiple deliveries or handoffs.
The ultimate evolution from the water fall is the spiral, taking advantage of the fact that
development projects work best when they are both incremental and iterative, where the team is
able to start small and benefit from enlightened trial and error along the way.
(Behl, “Information Tech For Mgmt”, P. 467) mentions that the spiral methodology
reflects the relationship of tasks with rapid prototyping, increased parallelism, and concurrency
in design and builds activities. The spiral method should still be planned methodically, with tasks
and deliverables identified for each step in the spiral.
Figure 3.2. : Spiral model (Leonid information-systems image, 2009)
University Of East London 69 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
3.6 Rational Unified Process (RUP) Methodology
(Figure 3.3: Rational Unified Process image taken from IBM RUP website)
The Rational Unified Process attempts to capture many of modern software
development's best practices in a form suitable for a wide range of projects and organizations
(Philippe, Kruchtenm (2004). The Rational Unified Process). This process recognizes that the
traditional waterfall approach can be inefficient because it idles key team members for extended
periods of time. Many feel that the waterfall approach also introduces a lot of risk because it
defers testing and integration until the end of the project lifecycle. Problems found at this stage
are very expense to fix.
University Of East London 70 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Six Engineering Disciplines
Business Modeling Discipline
Business modeling explains how to describe a vision of the organization in which the
system will be deployed and how to then use this vision as a basis to outline the process,
roles and responsibilities
Requirements Discipline
Requirements explain how to elicit stakeholder requests and transform them into a set of
requirements work products that scope the system to be built and provide detailed
requirements for what the system must do.
Analysis and Design Discipline
The goal of analysis and design is to show how the system will be realized. The aim is to
build a system that:
Performs — in a specific implementation environment — the tasks and functions
specified in the use-case descriptions.
Fulfills all its requirements.
Is easy to change when functional requirements change.
Designs results into a design model and analysis optionally into an analysis model. The
design model serves as an abstraction of the source code; that is, the design model acts as
a 'blueprint' of how the source code is structured and written. The design model consists
of design classes structured into packages and subsystems with well-defined interfaces,
representing what will become components in the implementation.
Implementation Discipline
University Of East London 71 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The purposes of implementation are:
To define the organization of the code in terms of implementation subsystems that
are organized in layers.
To implement classes and objects in terms of components (source files, binaries,
executables, and others).
To test the developed components as units
Test Discipline
The purposes of test are:
To verify the interaction between objects.
To verify the proper integration of all components of the software.
To verify that all requirements have been correctly implemented.
To identify and ensure that defects are addressed prior to the deployment of the
software
Deployment Discipline
The purpose of deployment is to successfully produce product releases, and to deliver the
software to its end users. It covers a wide range of activities including producing external
releases of the software
University Of East London 72 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
After analyzing the methodologies, there were reasons for not choosing or choosing a
particular methodology. Waterfall methodology is not suitable to be used for the project because
it requires the requirements of the project to be stated at an early stage. The project requirements
cannot be stated early as there is no experience in developing this kind of project and the project
is not about modifying an existing system but building a new one. Thus if the methodology is
followed, it will be a trouble if any new requirement that are found in the middle of the project as
waterfall methodology does not allow reverse back mechanism. Besides that a poor design
choice will not discovered until the final phase of testing or implementation and If mistakes are
made in the main design, it will not be discovered until the project reaches the programming
stage.
Meanwhile, since the spiral model is best to be implemented for large projects where risk
assessment expertise is highly required, it no essential of the adoption of this methodology for
the project as this is not a large project. In the other hand, the risks that might occur in the project
will not as complicated as large projects and even if a risk occurs, it can be handled.
The desktop application Biometric for attendance system for Yemen University has a
number of key criteria that a methodology must support in order for it to meet its objectives.
However, after analyzing all the methodologies it is found that RUP offers more plus points than
the other two methodologies. With the assistance of RUP it is able to effectively structure and
manage the development of Desktop applications such as Biometric attendance system for
Yemen University, focusing on the vital areas of image processing, HCI and user involvement.
However, because RUP allows for the flexible integration of other techniques, the benefits of
other methods will be used to complement it at various stages in its lifecycle.
Criteria Waterfall Spiral RUP
Cover All the aspect of SDLC *** ** ***
Provides support for date modeling - * ***
University Of East London 73 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Able to define technical problem * *** **
Involves user in development - ** ***
Provides support for project management control ** *** ***
Figure 3.5 [Comparison of Methodologies Table ]
The table showed above underlines the fact that RUP is the closest match to Desktop
application requirement. Besides that one important aspect of RUP is that it allows much
flexibility in the changing of requirement anytime unlike the waterfall methodology, as it is
impossible to identify all project requirements. RUP can be used effectively during the
Organizational Analysis stage to identify individual stakeholder requirements, and given that the
UML diagram types support the modeling of complex actor-system interaction, they will be used
during the Information Analysis stage. In addition, RUP’s entity modeling technique can be
employed during the Technical design stage to develop Biometric attendance system for Yemen
University desktop application’s underlying database and to design the user interfaces during the
HCI stage.
Another important feature of this methodology is that each iteration leads to an executable
release of the project hence there will be evidence on the progress of the project.
RUP has many advantages witch help in developing a sturdy desktop application over other
system development methodologies which are
1- Develop system iteratively
An iterative approach helps the developer increasing understanding of the problems of Biometric
attendance system for Yemen University through successive refinement, and to incrementally
grow an effective solution over multiple iterations. This will help the developer in mitigating the
risk at early stages of system development. At any stage of the development process it is easy to
University Of East London 74 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
manage changes in system. This mode of development provides a higher level of reusability and
better overall quality as well.
2 - Manage requirements
Managing requirements is the primary goal of system developing process. With the help of
notions of use case and scenarios proscribed in RUP it is possible to capture functional
requirement of Biometric attendance system for Yemen University and to ensure that these drive
of the design, implementation and testing of software, making it more likely that the final system
fulfills the end user needs.
3 - User component-based architectures
The Rational Unified Process supports component-base development. Components are not-trivial
modules, subsystems that fulfill a clear function. Biometric attendance system for Yemen
University is alienated into two main components which are Campus Entrance Clocking and
User Profiling Clocking.
4 - Visually model software
Making use of industry-standard Unified Modeling Language (UML) it would be possible to
visually model Biometric attendance system for Yemen University to capture the structure and
behavior of architectures and component. This help to maintain consistency between a design
and its implementation; and prompt unambiguous communication.
5 - Verify software quality
Poor application performance and poor reliability are common factors which dramatically inhibit
the acceptability of today’s system. With the aid of RUP it would be easy to plan, design,
implement, execute, and evaluate Biometric attendance system for Yemen University and can
make it a reliable system.
University Of East London 75 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
3.7 Conclusion
In Conclusion, the developer decided to choose an iterative development methodology for
Biometric attendance system for Yemen University staff system using fingerprint since iterative
development can critically manage the risk at each iteration. Based on this fact Waterfall
methodology is evaded because it is an incremental methodology (not iterative) and from Spiral
and RUP which are iterative methodologies, Rational Unified Process (RUP) has been chosen as
the development methodology for the application prototype. This is mainly because it allows
iterative development witch then help the project to e managed well and phases to be revisited.
In addition to that RUP offers significant and critical risk management at each iteration. Besides
that, there are several reasons/factors that lead the developer to settle on using RUP as the
software development methodology for Biometric for Yemen University staff.
University Of East London 76 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Chapter 4
Analysis
4.1 Introduction
The major objective of Analysis phase of this chapter is to analyze the various researches
done by the developer and to state the finding developer acquired from it. This section includes
the discussion and analysis of the finding of the primary research conducted. The details are then
justified with the analysis of secondary research carried out by the developer including the
reasonable explanations.
4.2 Types of Analysis
There are two different but similar types of data analysis; these are Qualitative analysis
and Quantitative Analysis, below are the details of the two different types of analysis.
4.3 Qualitative analysis
Quantitative Analysis provides data-driven analytical services for a range of business
challenges, specializing in statistical models for site selection decisions. Qualitative Analysis
Mean is securities analysis that uses subjective judgment based on no quantifiable information,
such as management expertise, industry cycles, strength of research and development, and labor
relations. This type of analysis technique is different than quantitative analysis, which focuses on
numbers. The two techniques, however, will often be used together.
University Of East London 77 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
4.4 Quantitative Analysis
The process of determining the value of a security by examining its numerical, measurable
characteristics such as revenues, earnings, margins, and market share.
Quantitative analysis is a process that involves measurement of results such as quantities of
substances produced, not just the nature of the reactions that produce them
4.5 Summarization of the Interviews conducted
In order to learn the prospects of the problems facing by Yemen University staffs, the developer
conducted interview with Mr. Mohammed Adnana Human Resource Manager in Yemen
University. The purpose of this interview is to mainly understand their current work
environment, the flows prevailing in the currents systems and which would be the possible
remedies expected by the staffs. The interview proceeding along with the reason and conclusion
of each question is stated below.
Interview Proceeding: No 1
Interviewer Mr. Raed Mohammed Mubarak
Interviewee Mr. Mohammed Adnana
Position Yemen University - Human Resource Manager
Location Yemen University level ground
Date & Time
Objective To understand the current work environment, the flows
prevailing in the currents systems and which would be the
possible remedies expected by the staffs.
*[Question -> Question asked to interviewee, Answer->answer given by the interviewee,
Reason-> Reason behind the question, Conclusion ->scrutiny of the answer]
Question: What is the current method the staffs use to clock in and out? Briefly describe.
University Of East London 78 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Reason: to get the idea in general of the current system flows.
Answer: “Presently we just record it manually on a paper. Staffs sign in and out on a paper
which placed in a relevant point.”
Conclusion: when staffs come or leave college, they have to sign in and out on the attendance
paper manually. That attendance paper is located in a relevant place.
Question: How the management track staffs attendance?
Reason: to know the current staffs attendance tracking and study that for the new developing
system.
Answer: “We rely on that attendance paper, the information that is collected by end of the day or
week from each department. And then we discuss that. That use to track staff attendance”
Conclusion: the staff attendance records can be viewed in the new system. Tracking the
attendance will be automatic operation instead of manually.
Question: What is the college policy in dealing with a staff who forgets to sign in or out from
the system?
Reason: to implement in the new system what action should be taken if staff does not sign in or
out.
Answer: “Usually if somebody forgot to sign in or out, we have sometime flexibility. Staffs
sometimes come and tell us they have forgotten to sign in or out previous day. We know that
staff is telling the truth because he/she attended classes and/or was around. So, normally we warn
him/her not to do that again”
Conclusion: staff attendance records to be managed by Admin or HR to add or edit records.
Question: Is the starting and ending time or work different from department to another?
University Of East London 79 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Reason: to know if the all departments have the same work starting and ending time so when
implementing the new system all departments will have fixed starting and ending time.
Answer: “It may vary from department to another. If a lecturer has part time classes for example
from 6:45 to 9:45 let’s say a lecturer has classes from. Every lecturer has to come by ‘core hours’
9:30am to 5pm even though if they don’t have classes in the morning”
Conclusion: while all departments do not have fixed time, each department’s times will be set
independently.
Question: is there an overtime work for the staff?
Reason: because the new system is going to be automatic, overtime work attendance would be
independent or integrated to the official work hours.
Answer: “Yes, some staffs work overtime and some teach classes part time at night. They fill up
the overtime log book. The staff has to verify that from Anthony’s office, when it’s signed off,
payment would be approved”
4.5 Summarization of the questionnaire
Questions
Personal Information:
5) Your job position: ________________________.
6) Department : _______________________.
7) What is your age range?
Below 18
18-27
28-37
38-55
University Of East London 80 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Above 55
8) Your working days: (Pick the days you are working on)
Mon Tue Wed Thu Fri Sat Sun
Reason To know which department they are working in and days of work. And to analyze
Whether each a specific department has a specific working days
Analysis
Age Range
50.00%
45.00%
40.00%
35.00%
30.00%
25.00% Age Range
20.00%
15.00%
10.00%
5.00%
0.00%
Below 18
18-27
28-37
38-55
Above 55
Department are noted to the following next question
Question
Your working time:
Fixed; Start at: ______ AM/PM End at: _________ AM/PM.
Variable
Reason To know if all staff in a specific department has a fixed working time.
That would help the developer to set a fixed time for each department when
registering in the system
University Of East London 81 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Analysis
Sales
80.00%
60.00% Sales
76.67%
40.00%
20.00%
0.00% 23.33%
Fixed Working Time
Variable Working Time
4.35%
100.00%
13.04%
80.00% 4.35%
4.35% 8:00am-12:00pm
8:00am-5:00pm
60.00% 8:00am-7:00pm
9:00am-6:00pm
8:30am-6:00pm
40.00%
73.91%
20.00%
0.00%
Fixed Working Time
Majority of the staffs work fixed time. analysis is done to see whether each
department have a fixed time but it turned out that staffs work time may vary even if
they are in the same department. Of all the staffs responded to the questionnaire and
fixed working time, 73.91% of them start work at 8:30am and end at 6:00pm.
Question In your opinion the current staff attendance system (paper-based) in Yemen
University is:
University Of East London 82 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Excellent
Good
Satisfactory
Average
Poor
Reason This question would help the developer to analyze whether the staffs are happy with
the current system, in this case, the good features in the current system to be studied
and applied in the new system
Analysis
100.00% 13.33%
90.00%
80.00%
70.00% 16.67%
Poor
60.00% Average
13.33%
50.00% Good
13.33% Excellent
40.00%
Satisfactory
30.00%
20.00%
43.33%
10.00%
0.00%
43.33% of the staffs who participated and responded to the questionnaire are
satisfied with the current system. the current system is to be carefully revised for
features that could be implemented in the new system
Question What is the approximate time taken to sign in and off to record your
attendance?
___________Minute(s).
Reason To know the average time taken for a staff to clock in and out, the result to be
compare with the result of the time taken in the new system.
Analysis The average result: 2.30 minutes the time taken to clock in or out.
University Of East London 83 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Question “Buddy punching” in manually attendance system is when somebody signs
for somebody in his/her absence. Do you agree these problems happen in
the real world in such attendance systems?
Yes No
Reason
Analysis
"Buddy Punching" problem exist in such
current attendance system
100
80
60 83.33%
40
20
0 16.67%
Yes
No
83.33% of the respondents think the “Buddy Punching” problem do exist in such
the current attendance system. needs for upgrade would be favorable to avoid such
a problem.
Question In your opinion if the “buddy punching” problem is really happening, what
is the best strategy to overcome these problems?
Using a biometric system, such as fingerprint so that the person would
be validated based on the biological structure of the finger rather than any
type.
Using Card swipe, to avoid “buddy punching” an additional staff is
needed to be employed to make sure nobody misuses the system.
Using the same manual system, employ additional staff to make sure
that nobody misuses the system
Reason This question is to the staff who think “buddy punching” problem do exist in the
University Of East London 84 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
previous question. This question is to know which of these three selected options
the best in eliminating such a problem.
Analysis
Biometric
80.00%
70.00%
60.00%
50.00%
40.00% 73.33%
30.00%
20.00%
10.00% 23.33%
0.00%
Biometric 3.33%
Swipe Card
Paper-based
73.33% of the respondents think that Biometric authentication is the best solution to
the problem.
Question What do you like about the current staff attendance system? Please state two
3- _________________________________________
4- _________________________________________
Reason To note the best the staff like about the current system, so that, it can be studied and
applied in the new system if within the scope of the project.
Analysis The abstract of the features they like is the following:
Getting evaluation from other staff
Easy and fast
Simple
Flexibility
Other staff can sign in for me
Need an ID to access
Flexibility
Convenient
Easy
Require signature of staff
“buddy punching”
University Of East London 85 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Some of the above features like; easy and fast, simple, flexible, and convenient are
within the requirement of the project.
“Require signature of staff” feature will be upgraded to Biometric authentication.
Question What do you dislike about the current system? Please state two
1-_________________________________________
2-_________________________________________
Reason To note what the staff do not like about the current system, so that, it can be avoided in the
new system.
Analysis The abstract of the ….
Anybody can punch for others
Staff my sign in at different time
Manual and slow
Not accurate
Sign in time not constant
Writing manually
Not accurate
Can be misused
Can’t sign in if nobody at the counter
Not systematic
Manual
Waste time/time consuming
Not safe
Wasting Paper
Sometime my name is not there/rewrite
University Of East London 86 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Question Do you have any experience with any biometric user authenticating system?
Yes No
Reason To study the staff’s experience in interacting with biometric system.
That would identify the training time required to train the staffs for the new
system.
Analysis
Have experience with Biometric
system before?
60.00%
50.00%
40.00% Have experience with
Biometric system
before?
30.00% 60.00%
20.00% 40.00%
10.00%
0.00%
No
Yes
While majority of them do not have previous experience in working with
biometric system before, help within the system and a manual help will be
provided.
Question Would you encourage using Fingerprint Identification staff time &
attendance?
Yes No I don’t know
University Of East London 87 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Reason to see whether the staff would prefer to use biometric attendance system
Analysis
Encourage Biometric Attendance System?
80
70
60 Have experience with
50 Biometric system before?
40
73.33%
30
20
10
6.67% 20.00%
0
No
Yes
I don't ...
73.33% of the respondents encourage to use a biometric attendance system.
Question
(In the proposed system, each staff would be able to not only clock-in and
out to record the time but also to log in and to view his/her profile and
report)
What would you like to see in your profile other than your attendance
summary?
__________________________________________________________
Reason To get what the staff would like to see in their profile other than their attendance
summary so they can be studied and applied to the new system if within the scope
of the project
Analysis The abstract of the ….
The overall weekly work with some notes from my boss
Who is on leave for the day
Reason for absence e.g. MC, personal reason
University Of East London 88 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Photo ID for identification
Whole records of any issues during morning time.
Leave status
Overtime calculation
My record whether I’m early or late for work
Most of the likes above are to be studied and applied in the new system.
4.6 Feasibility study analysis
In practice, the meaning of the feasibility studies, in assumption are not necessarily
straight appropriate. In creative writing the terms costs and means on one hand and qualities and
objectives on the other are very closely related to feasibility.
However, in the framework of project, the terms rational and achievable are more related to the
term project feasibility. Project feasibility can be defined as the overall feasibility of a creation
project; therefore, base on these definitions, I conclude that it is important to the development of
the proposed Attendance system. And there is a need for assessment as result of the high-risk
involved in the project. Hence, I will discuss three types of feasibility that need to be put into
reflection
4.7 Operational feasibility
In conditions of the proposal of operational feasibility, it is submitted that the
apprehension with the current events as well as the individual skills can be implicit to be
sufficient enough in order to function the proposed system or if there are additionally procedures
and skills that are required to be obtained. Operational feasibility is reliant of human resource
that is available for this project and it encompasses making a projection as to whether the system
would be able to operate and be properly used. Herewith a discussion of some operational areas
and indicate the level of performance.
University Of East London 89 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
4.8 Technical Feasibility
The term technical feasibility establishes that the product or service can operate in the desired
behavior. Technical feasibility means “achievable” (Whitten&Jeffrey, 2001).
I feel that this has to be confirmed without building the system. The proof is defining a complete
number of technical options that are feasible within known and demanded resources and
requirements. At such, I will use a standardize questions according to Shelly Cashman in his
book entitled” System Analysis and Design" in order to will help determine the state of technical
feasibility
In terms of technology availability and requirement for the development of the proposed system,
it is very feasible as it is widely available, reasonably cheap and has very low maintenance cost
requirements. The technology to be used is not a very sophisticated one. Hence, it is going to be
in consideration of the level of technical expertness among the target users which are time
attendance.
Hence, training will be required. And on the author’s part, the system will be produce in such
way that even a lay man could understand easily in view of achieving technical feasibility.
4.9 The Cost of my project
Hardware cost
Product Quantity Price Total
Computer 10 RM 3,000 RM 24,000
Are U are Scanner 10 RM 350 RM 3,500
Printer 2 RM 1,000 RM 2,000
University Of East London 90 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Photo copy machine 1 RM 7,000 RM 7,000
Laptop 5 RM 3,500 RM 17,500
Servers 1 RM 35,000 RM 35,000
Total RM 89.000
Hardware total cost = RM 90,500
5.6 Software cost
Product Quantity Price Total
Microsoft Visual Studio 15 RM 400 RM 6,000
VB.NET
Microsoft SQL 2008 15 RM750 RM 11,250
Standard Edition
Monitoring software ( PC 15 RM 400 RM 6,000
Anywhere 12.1 Remote
and Host )
Antivirus software 15 RM 200 RM 3,000
Total RM 26,250
Software total cost = RM 26,250
5.7 Other cost
Object Quantity Price Total
Advertisements 15 days RM 1,550 RM 23,250
Meeting and other 2 years RM 100,000 RM 100,000
University Of East London 91 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
miscellaneous
expenses
Total RM 123,250
Other cost total = RM 123,250
Project total estimation cost in3 months:
Subject of Cost Cost
Interview total cost RM 5274.5
Hardware Cost RM 89.000
Software Cost RM 26,250
Other Cost RM 123,250
Total RM 1.337.046.5
4.10 conclusions
I have analyzed by different types such as the Questionnaire, interview and as well as the
different kind of studies areas such as Quantitative analysis Qualitative analysis
To conclude this Chapter, It is considered very important steps to be studied before start
the design stage to build that whatever will be designed should be in the right way. This
means that the system must be designed in a way that is as user friendly as probable and
that the crossing point of the use be kept simple and efficient so as to avoid
understanding.
University Of East London 92 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Chapter 5
Design
5.1 Introduction
In system design the process architecture, component, models interface and data will be
discussed furthermore all the requirement will be analyzed and documented in the form of details
such as use case, class diagram, activity diagram that can be used for strong communication. It
describes all important aspect of a system. Also it represents the system with structural and
behavioral language models and those designing modeling include the architectural mechanical
and detailed design and there is also be an entity relationship to describe the data requirement
and assumption in the system.
5.2 Overview of the system design
UML design methods are becoming the most widely used methods for computer system design.
The UML has become the standard language used in Object-oriented analysis and design it is
widely used for modeling software systems and is increasingly used for high designing non-
software systems and organizations
5.3 Types of design
5.3.1 Use Case Diagram
Use case presents a graphical overview of the functionality provided by a system in terms of
actors, their goals and any dependencies between those use cases.
University Of East London 93 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The main purpose of a use case diagram for my system is to show what system functions are
performed for which actor. Roles of the actors in the system can be depicted.
5.3.2 Use Case Diagram (High Level Diagram)
Attendance system using fingerprint for Yemen University
Staff
Campus Entrance Clocking
«uses»
Clock In Time Checking
«uses»
«extends»
Clock Out
«extends»
Fingerprint Processing Library
process
Fingerprint Image
Staff Fingerprint Processor
Profiles & Management
«uses»
Clock In
Time Checking «extends»
«uses»
Clock out
«uses»
Login Password
Verification
«uses»
All
View Attendance
Record Fingerprint
identification
HR
View Staffs Report
View HR report
Manage Staff
Attendance
Manage HR
Attendance
Admin
Figure 5.1.1 Use Case Diagram (High Level Diagram
University Of East London 94 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.3.3 Fingerprint Processing Library (Sub-diagram)
Fingerprint Processing Library
Invert Gray Scale «extends»
Enhance Image
«extends»
Divide Image into
blocks «extends» «extends»
«extends»
Analyze Histogram
«extends» Generate Template
«extends»
«extends»
Equalize Image
«extends»
«extends»
Compute orientation Exctract Minutia
Fingerprint
Processor
Binarize Image
«extends»
get probe Template
Thin Image «extends» «uses»
«uses»
Match Templates
Detect Minutia
«uses»
Remove False Get all users'
Scan Fingerprint
Minutia templates
Figure 5.1.2 use case Library (Sub-diagram
University Of East London 95 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.3.4 False Minutia Remover
False Minutia Remover (Sub-Diagram)
Remove branch Detect Minutia
Minutia
«uses»
«extends»
«uses»
Mask Minutia «extends»
«uses»
«extends» Remove False
Remove fregments Minutia
«uses» «extends»
«extends»
Remove Tails
«uses»
«extends»
Remove Gaps «extends» Fingerprint
«uses» Processor
Remove pores
«uses»
Remove Dots
Figure 5.1.3 False Minutia Remover
University Of East London 96 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.4 Design Class Diagram
Class diagram in the Unified Modeling Language (UML) is a type of static structure diagram
that describes the structure of my system by showing the system's classes, their attributes, and
the relationships between the classes.
University Of East London 97 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Figure 5.2 Design Class Diagram
University Of East London 98 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
University Of East London 99 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.5 Activity Diagram
The main reason to use activity diagrams is to model the workflow behind the system being
designed. Activity Diagrams are also useful for: analyzing a use case by describing what actions
need to take place and when they should occur; describing a complicated sequential algorithm;
and modeling applications with parallel processes (Martin Fowler, Kendall Scott: UML Distilled
Addison-Wesley 2000).
5Campus Entrance clocking activity diagram
Scan Staff Thumb
Retrieve all users' templetes Process Fingerprint Image
Identify Staff
[ Not Identified ] [ Staff Identified ]
Display "Unidentified" Check Last Action taken by the staff
[ Clocked out ] [ Clocked in ]
Clock in Staff Clock out Staff
* *
Confirm Clocking to Staff
Fi
gure 5.3.15Campus Entrance clocking
University Of East London 100 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.5.1 Profiles & Management System (Activity Diagram)
[HR | Staff] [Admin]
A
Autherize User
UserName & Password Scan Thumb
Verify User Identfy User
[HR | Admin]
[Staff]
[HR]
[Staff]
Show Main Menu [Limited] Show Main Menu
[Logged by Password]
Log out Edit My Info Clock In/out
Apply Leave
View Attendance Report
[Logged by Biometric]
University Of East London 101 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.6 Sequences diagram
: Staff : Finger process : HR : Admin
image
Sign in
Send login into
Tap thumb
Process time check in
Check in
Process time check out
Sign manage HR report
Send send log into manage HR attendance
Check in
View Staff Report
Manage Staff Attendance
Manage Staff
University Of East London 102 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.8 ERD
An entity-relationship (ER) diagram is a specialized graphic that illustrates the interrelationships
between entities in a database. ER diagrams often use symbols to represent three different types
of information. Boxes are commonly used to represent entities. Diamonds are normally used to
represent relationships and ovals are used to represent attributes.
Fp_id image template type Fp_id image template type Admin_id Name
id
Admin
Fingerprint Admin
Fingerprint deptName
User_id
m
password startTime
1
Has m Has
firstName
endTime
1 Contains
LastName m 1 Department
User id
Status
1
isNew
Active 1
Associated
to
1 Notification
date
Gender 1
Has
Tel_no 1 Has Has isStaffView
m
dob m 1
Attendance Bulletin Leave
address
id
photo
Status type date dateTo dateFrom
Att_id type date classificatin
status note id title text date target Target_id active
Figure 5.5 ERD diagram
University Of East London 103 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5.8.1 Relation Derived for ERD
1. TABLE: User [For storing user information]
Attributes Name Type
Primary Key user_id varchar(15)
Foreign Key dept_id Int
Attribute password varchar(30)
lname varchar(20)
fname varchar(20)
status Bit
active Bit
gender varchar(15)
tel_no varchar(20)
dob varchar(20)
address Text
city varchar(20)
state varchar(20)
county varchar(20)
photo Binary
2. TABLE: Department [For storing Department data]
Attribute Name Type
Primay Key dept_id Int
Foreign Key - -
Attribute dept_name varchar(50)
start_time Smalldatetime
end_time Smalldatetime
3. TABLE: Fingerprint [For Storing Fingerprint data]
Attribute Name Type
Primary Key fingerprint_id Int
Foreign Key user_id varchar(15)
image Binary
template Binary
FingeType varchar(10)
4. TABLE: Leave [For Storing leaves data]
University Of East London 104 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Attribute Name Type
Primary Key Leave_id Int
Foreign Key user_id varchar(15)
request_FromDate Smalldatetime
request_ToDate Smalldatetime
date Smalldatetime
type varchar(20)
status varchar(15)
note Text
5. TABLE: Notification [For storing new Notifications been made by a user]
Attribute Name Type
Primary Key notification_id Int
Foreign Key Leave_id Int
Foreign Key user_id varchar(15)
date Smalldatetime
isNew Bit
isStaffView Bit
6. TABLE: Bulletin [For storing bulletin added by HR or Admin]
Attribute Name Type
Primary Key bulletin_id Int
Foreign Key - -
date Smalldatetime
title varchar(100)
text Text
target varchar(30)
target_id Text
active Bit
University Of East London 105 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
7. TABLE: Attendance [For storing attendance records of Staffs & HRs]
Attribute Name Type
Primary Key att_id Int
Foreign Key user_id varchar(15)
type varchar(5)
date Smalldatetime
time Smalldatetime
status Bit
classification varchar(50)
note varchar(MAX)
8. TABLE: Admin [For storing Admin data]
Attribute Name Type
Primary Key admin_id varchar(20)
Foreign Key - -
name varchar(30)
9. TABLE: AdminFingerprint [For storing Admin fingerprints data]
Attribute Name Type
Primary Key AdminFP_id Int
Foreign Key admin_id varchar(20)
image Binary
template Binary
FingerType varchar(10)
5.9 Hardware & Software
The hardware and software required during the development period.
University Of East London 106 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
A standard PC running Window NT or later is required during the development period
Microsoft® Visual Studio 2008 or later with .Net framework 3.5 or later
Microsoft® Developer Network (MSDN) libraries
Microsoft® SQL Server
Microsoft® Office 2007 or later
The Fingerprint Scanner API (Application Programming Interface) /SDK (Software
Development Kit) for capturing a raw image
5.10 Conclusion
There are different software design model that exit today and all these different development
model have their own advantages and disadvantages .however in this present day the
combination of all these methodologies is integrated .timing is very essential in development and
if the days happened the at the moment could be taken over by the competitors diagrams
University Of East London 107 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Chapter 6
Implementation and testing
6.1 Introduction
The function of organization Implementation can be summarized as follows: building the
new system accessible to a geared up set of user and position on-going support and maintenance
of the system within the performing organization. At a finer level of detail, deploying the system
consists of executing all steps necessary to educate the consumers on the use of the new system,
placing the newly developed system into production, confirming that all data required at the start
of operations is available and accurate, and validating that business function that interact with the
system are functioning properly. A key difference between System Implementation and all other
phase of the lifecycle is that all project activities up to this point have been performed in safe,
protected, and secure environment, where project issues that arise have little or no impact on
day-to-day business operation. After system implementation, system testing is taking places and
it is the point in the lifecycle at which every aspect of the application being developed, along
with any supporting data conversion routines and system utilities, are thoroughly validated by the
customer representatives prior to proceeding with system implementation. The entire testing
phase is centered on gaining sufficient evidence of the systems Accuracy and functionality to be
able to proceed to System Implementation with the highest level of confidence possible in the
success of the system. This phase differs from system construction in that acceptance testing is
the final opportunity to establish that the system performs as expected.
6.2 Implementation Plan
University Of East London 108 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The purpose of Implementation plan is to take all possible steps to guarantee that the
Future system deployment and alteration occurs well, efficiently, and perfectly. The sequencing
of operation activities is just as important as it was with earlier Activities. This sequence of
proceedings should be encompass in the deployment and alteration plan part of the technical
requirement, and will address and prioritize any necessary training activities, setup activities
needed to prepare the production setting (PC/Server, are U are device , etc), and data conversion
and rationale activities. This implementation plan will define the steps for physically migrate the
system and any associated utilities to production, and for validating the accuracy and wholeness
of this migration after these steps have been performed. Proper planning and sequencing of the
Deployment can help to reduce the chance of any missteps that could result in having to restart
the deployment process, or lengthen the implementation schedule.
6.3 Testing – Introduction
Testing is the process of used to evaluate software qualities such as reliability, usability,
maintainability and level of performance. Test results are used to compare the actual properties
of the software to those specified in the requirement document.
(Ilene Burnstein, 2002)
The definition of testing offered by Ilene Burnstein (2002) specified that it is a practice
concerned with achieving a high quality product, whether or not the product is a software
program. In the perspective of Biometric ASYU, quality of the desktop application will be a
quantifiable measure of how well the system meets the initial requirements, how well the system
performs functionally and finally, the level of user acceptance with regards to usability and
robustness to utilize. The various testing methods selected to evaluate Biometric ASYU are Unit
Testing, Functional Testing, Cognitive Walkthrough, Usability Testing and Compatibility
Testing. Below given the brief explanation of each testing method conducted, proposed for
Biometric ASYU
University Of East London 109 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.4 Unit Testing
Unit testing is not a formal process and it has been completed during the development phase of
each modules of Biometric ASYU. With the short-term goal of testing concerning the detection
of defects, this method was effective as it led to the minor errors regarding data inputs and
validation. Since the problems found out during unit testing and the solution for that are depicted
previously in the Implementation only the model of the report, designed of unit testing is stated
below.
6.4.1 Test Report of Unit Testing
UNIT TESTING – Unit Name
Test Date: -
Duration -
Test Objective -
Test Date Expected Result Actual Result Remark
- - - -
6.5 Functional Testing
Functional Testing of Biometric ASYU is tested together with reliability testing to ensure that
the process of each module is functioning as expected and can meet the user requirement
efficiently. This method was also successful to find out that is the modules of the system are
reliable enough for publishing and maintaining delicate information. The testers chosen for
University Of East London 110 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
functional testing were individuals without any knowledge of the inner workings, structure or
language of the module being tested. The test reports, of the modules which found tainted during
the functional testing process is stated below.
6.5.1 Functional Testing (Black Box Testing
Tester Type Tester Name Modules Tested
Student
Administration
Staff
6.5.2 Test report of functional testing (Clocking Module)
Test Module: Clocking Module
Test Date:
Duration:
Test Objective To clock a user in and out.
(1st Testing) Capture user’s fingerprint image, input obligations
process it, and then build a template
Expected Result -Identify the user fingerprint template User Fingerprint image
against all the templates stored in the captured using the
database (1-to-Many). fingerprint sensor, then
processed, and build
- Check the status of the user; if the
temporary template for
status was clocked in, then clock out
identification.
the user and vice versa.
- Clocking in or out; gets the current
University Of East London 111 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
date and time and store a new
attendance record in the database.
Actual Result Run time error -
Remark The user had no attendance record so -
it could not check her status (Clocked
in or out)
(2nd Testing) Capture user’s fingerprint image, input obligations
process it, and then convert it to a
template
Expected Result -Identify the user fingerprint template User Fingerprint image
against all the templates stored in the captured using the
database (1-to-Many). fingerprint sensor, then
processed, and build
- Check the status of the user; if the
temporary template for
status was clocked in, then clock out
identification.
the user and vice versa.
- Clocking in or out; gets the current
date and time and store a new
attendance record in the database.
Actual Result Identical to the expected result -
Remark if the user is new, has no record, the -
default first action set to be “Clock
IN”
Figure 6.1 Test report of functional testing
6.5.3 Test report of functional testing (Login module):
6.5.3.1 Test report of functional testing (Login by Fingerprint Scanning Module)
University Of East London 112 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Test Module: Login By Fingerprint Scanning Module
Test Date:
Duration:
Testers Involved Arsalan Shahbaz
Awlaqi
Zeshan
Test Objective To identify users based on their fingerprint
(1st Testing) Capture user’s fingerprint image, input obligations
process it, and then convert it to a
template
Expected Result Identify the user fingerprint template User Fingerprint image
against the templates stored in the captured using the fingerprint
database. Login process successful. sensor, then processed and
converted to a template.
Actual Result Login failed -
Remark The default threshold of template
matching is high (30)
First Testing Capture user’s fingerprint image, input obligations
process it, and then convert it to a
template
Expected Result Identify the user fingerprint template User Fingerprint image
against the templates stored in the captured using the fingerprint
database. Login process successful. sensor, then processed and
converted to a template.
Actual Result Identical to the expected result The user successfully logged
into the system
Remark the threshold of template matching was
reduced to 10
Figure 6.2 Test report of functional testing
University Of East London 113 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.5.3.2 Test report of functional testing (Login by Username & Password Module)
Test Module: Login By Username & Password Module
Test Date:
Duration:
Testers Involved Arsalan Shahbaz
Awlaqi
Zeshan
Test Objective To verify username and password in the database
1st Testing Valid username and password invoke input field obligations
“Login” Button
Expected Result Verifying the user’s username and Invalid inputs are not allowed,
password in the database and display the display error message and
appropriate menu/profile the user profile login process unsuccessful
with the “Login By Username & Password”
limited functionalities.
Actual Result Login was successful but HR user has all invalid input are allowed and
the functionalities that are provided to him error message is not displayed
if he login using his fingerprint.
Remark There was an error in the connection string The textbox validation criteria
University Of East London 114 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
declared which resulted in a server error have been changed and tested
2nd Testing Valid username and password invoke input field obligations
“Login” Button
Expected Result Verifying the user’s username and Invalid inputs are not allowed,
password in the database and display the display error message and
appropriate menu/profile the user profile login process unsuccessful
with the “Login By Username & Password”
limited functionalities.
Actual Result Identical to the expected result The user successfully logged
into the system
Remark Programmatically: the “LoginMethod” was -Nil-
not verified. When it was verified, HR user
had the appropriate limited functionalities.
Figure 6.3 Test report of functional testing
6.5.4 Test report of functional testing (Managing Users Module)
Test Module: Managing Users Module
Test Date:
Duration:
Testers Arsalan Shahbaz
Involved Awlaqi
Zeshan
Test To add, delete, and update users successfully
Objective
1st Testing Add new user Update existing user Delete existing user
Expected -Scan the new user’s -Retrieve existing user’s -Confirm deletion
Result fingerprint then build a detail
-Delete all data
University Of East London 115 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
template. - (optional) scan new associated with the
fingerprint for update. user.
-The user’s fingerprint
template should not be -if new fingerprint was
already enrolled with an scanned, template should
existing user overwrite the user’s
existing templates
-Enforce filling the
required field -Validate all fields before
submit.
-Validate all fields.
-Update user
-Enroll the new user
Actual Result Identical to the expected Identical to the expected Identical to the
result result expected result
Remark - - -
Figure 6.4 Test report of functional testing
6.5.5 Report of functional testing (Managing Bulletins Module)
Test Module: Managing Bulletins Module
Test Date:
Duration:
Testers Arsalan Shahbaz
Involved Awlaqi
Zeshan
Test To add, delete, and update bulletins.
Objective
1st Testing Add new Bulletin Update Bulletin Delete Bulletin
(“Save” button invoke) (“Save” button invoke) (“Delete” invoke)
University Of East London 116 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Expected -Validate all fields -Retrieve existing -Confirm deletion
Result bulletin’s detail
-Store the new bulletin in -Delete the bulletin
the database for the -Validate all fields before from the database
selected target(all, a submitting changes.
department, or selective
-Update bulletin in the
users)
database for the selected
-selected target should be target(all, a department, or
notified with the bulletin selective users)
Actual Result Identical to the expected Identical to the expected Identical to the
result result expected result
Remark - - -
Figure 6.5 Report of functional testing
6.6 Usability Testing
Usability testing was conducted to evaluate and ensure that the users are able to use the
system without any confusion and find it useful to them. Then volunteers from different
background were tested the system in order to determine the desktop application’s usability
strengths and weaknesses. A questionnaire was used to present the task to the users, who then be
asked to score each task accordingly. The questionnaire mainly covers four major sections of
usability testing which are system compatibility, consistency, flexibility, and minimal actions. Its
contains the sample questionnaire supplied to the ten volunteer’s from different background.
6.7 Requirement traceability matrix
Requirement traceability matrix is used to recognize and bond the system functionalities
to the original requirement specification, in form of the user case diagram. The matrix depicted
University Of East London 117 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
below confirms that the entire original requirements are absolutely implemented in the Desktop
application Biometric ASYU.
ID User requirement Forward traceability Status
U1 Extract true Minutia from a fingerprint s1 Success
U2 Match fingerprint template s1 Success
U3 Identify user by their fingerprint image s1 Success
U4 Clock in/out a user by just scanning s1,s2 Success
his/her thumb
U5 Manage user; add, edit, and delete s3, s1 Success
U6 Generate user attendance report s3 Success
U7 Leave component; apply & manage s3 Success
U8 Bulletin management; add, edit, and s3 Success
delete
U9 Mange Department s3 Success
ID Functional Requirement Backward traceability Status
s1 Fingerprint Identification System U1, U2, U3, U4, U5 Success
s2 Campus Entrance System U4 Success
s3 Profiles & Management System U5, U6, U7, U8, U9 Success
6.8 Screenshots
University Of East London 118 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.8.1 Fingerprint Scanner Run Time Environment Installation Implementation
To use the fingerprint sensor, Digital Persona Run Time Environment must be installed in
the system. To make it easier to the other end to run the system, installation of the Fingerprint
scanner RTE is done programmatically within the system. In Visual Studio 2008, a folder was
created to hold the silent setup files of the sensor RTE. In the final installed system, a folder
automatically created to hold the sensor RTE to be installed if it is not already installed. It has
setup files for 64bits and 32bits machines which would be installed automatically and silently.
Below are figures of the RTE locations in Visual Studio and the installed system (if the user
installs it)
After the path of silent install batch is stored, now it’s time to run that batch.
System.Dignostic.Process class is used to run the selected batch file. Because it’s going to install
the RTE silently, a dialog pops up as feedback to the user that installation is under processing.
Show the dialog below:
6.8.2 Profiles &
Management GUI
Implementation
In this form,
two panels were
created; first is to hold
the user type
prompt selection and
the second the
appropriate menu based
on the user selection. The first panel looks as follow:
University Of East London 119 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
When one of the three login buttons is click, the above panel will disappear and the second
panel, which has the appropriate user menu, will appear. If the user clicks on Admin Login,
Admin Login panel will show up which look as follow
University Of East London 120 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
As shown above, the admin can login by scanner his/her fingerprint using the fingerprint scanner
or by locating his/her fingerprint image (for testing purpose only).
When running the system from Visual Studio, Admin registered fingerprint images can be found
under {Project Directory}\Fingerprint Image\Admin Fingerprint. When running it from installed
release in Program File, Admin registered fingerprint images can be found in {Program
Files}\Biometric ASYU\Admin Fingerprint Images\.
HR and Staff Login cannot browse their fingerprint image, they have to scan their thumb using
the scanner or login using username and password, which has limited functionalities. HR and
Staff Menus look as follow
University Of East London 121 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
In Admin case, When Admin fingerprint image scanned or located or in HR or Staff case, when
a fingerprint is scanned or username & password were provided, the system will create an object
of the abstract base class Users Abstract and depend on the user type the object will be initialize.
6.8.3 Admin Main Menu vs. HR Main Menu
University Of East London 122 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Admin, as assumed, has all the functionalities of the system. HR users, on the other hand, have
all except they are not allowed to manage department or any other function related to other HR
users or Admin users. Admin and HR main menu looks like the following figure except that the
top menu strip of HR main menu has limited functions
If the HR user login using his/her username & password, clocking users in or out, in the main
menu will be not available.
6.8.4 Staff Main Menu
University Of East London 123 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Staffs Main Menu shows user basic information, Clocking in or out button would be
available only if the staff login in by scanning his fingerprint. Main menu is shows below
Staff can edit their information, view weekly, monthly, or all their attendance reports. They also
can apply for leave and browse Bulletins or notifications sent by HR or admin.
6.8.5 Staff Management
Admin user is allowed to manage all users of the system; HRs and staffs. Whereas an HR user, if
logged in using his/her fingerprint, can only manage staffs. If HR users logged in using their
username & password, they will not be allowed to add new staff or update staffs’ fingerprints
templates.
The Staff Management Menu created with three containers. See the figure below
University Of East London 124 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The left panel has the user functions to manage users. The left panel shows all users categorized
by department and represented using TreeView (Light Green color is department name; white is
the user name, dark green is the currently selected user). The panel on the right shows users
abstract information.
Add user: When “Add user” link label is clicked, Edit Staff Information dialog shows up as
follow;
University Of East London 125 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Staff Detail Tab: filling new user Fingerprint tab: three sample to be
information; captured using the fingerprint sensor
Edit User: function can be clicked either by double clicking on the user on the right panel or
double clicking on the user on the middle panel (TreeView) or on the left panel by clicking on
the “Edit user” link label. If the user performs one of the mentioned above way for edit, Edit
Staff Form shows up filled with selected user information to be updated.
Delete User: when user click on “Delete User” link label on the left panel, system will ask for
user confirmation. See figure below
6.8.6 Departments Management
University Of East London 126 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
The Admin only is the one who can mange departments by adding, deleting or updating a
department. When adding or updating a department, Admin has to set the Starting and Ending
work time for that department.
Figure 6.3.5: left: list of all department. Right: adding or updating department Dialog
6.8.7 Leave Component:
6.8.7.1 Leave Management
Leave applications are managed by admin. HR can manage staff leave applications only. If there
is an application request from a user, a button pops up when the HR or Admin login to the
system. See an example below
University Of East London 127 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
HR & Admin main menu checks for notifications when it starts by checking if there are new
notifications. Each notification has leave_id relationship.
Leave Application Form display leave depend on the user type. If Admin, all leaves would be
display; if HR, only staff Leave would be displayed. Staff can also view they own leave
applications. Leave Application form will display leave application depending on the user type.
HR and Admin can decide what to response to the leave applications; by accept, reject or review
the leave application. See the figure below
University Of East London 128 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.8.8 Report
Component:
6.8.8.1 Staff Attendance
Report
Staff attendance report
can be viewed by Admin and HR
users. This report shows all
users grouped by departments.
Each user name is underline which allows navigation to another report that displays the selected
user attendance report. And in the user attendance report it displays the number of leaves the user
has and the limit of leave which is 15. An example for Staff Attendance Report, which shows all
users and the drill through report are show in below
University Of East London 129 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
All user categorized by department]
6.8.8.2 Staffs Current Status
Staff current status report can also be viewed by Admin and HR users. It displays all users who
are currently online (clocked in) and offline (clocked out). See an example of this below
University Of East London 130 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
University Of East London 131 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.8.8.3 Attendance Management
Admin and HR manage the staff attendance record; add new, edit, and delete. For adding new
record, the staffs, who Admin or HR wants to add new record to, should be clocked out. Form
developer for managing attendance record is shown below
University Of East London 132 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6.9 Conclusion
In the end of this chapter, it can be seen obviously that the system is working as we expected
after several rounds of testing and training to the users.
Even though we been through some of the errors that come up during the first round of that
testing after the implementation stage, but we tried to solve the it and perform another round
until we make sure that all the functions are working efficiency.
Implementing such a project required a lot of time consumed and must get to know all the
weaknesses to be avoid of having a sudden problem in the future.
University Of East London 133 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
University Of East London 134 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Chapter 7
Conclusion
7.1 Introduction
The fingerprints of different students were successfully process the attendance
and added to the database. The fingerprints were further verified and several dry runs
were made that confirmed matches and mismatches for different samples. Apart from
that, the attendance system was used to demonstrate the various functions and processing
methods used in image processing of the fingerprint. The outputs for all the trial runs and
process demonstration were recorded. During the overall phases, most of the time has
been spent on learning the visual studio coding and also My SQI which is the main
development tools for database in this project. In Order to develop a quality system, the
analysis and design phase is most important of all. The project was interesting as
experience but not as enjoyable as it was expected to be. Lack of The knowledge on
visual studio programming language and never experience in dealing with developed
System was connected to Microsoft Access database server caused sometimes in
searching the Solution and testing process. However, despite the problems experienced
during the project and the system satisfies most of its objectives and can be extended in
the future to be more functional and available.
7.2 System Strength
To determine the degree of success of the system, the developer finds it important to
answer this question, which would give the developer a whole overview of the success of
the system.
What are the reasons to conclude that Biometric ASYU is successful?
University Of East London 135 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Fingerprint Identification system is the main objective of this proposed system; thus, it
successfully identify users based on their scanned fingerprints, using Digital Persona
fingerprint scanner, with satisfied response time.
Identification of project challenges and selection of proper methods for meeting
these challenges: The challenges that the developer would be facing were successfully
identified at the preliminary stage of the project. Due to this, the developer was
successfully able to meet these challenges with solutions before it grew out to become a
major problem. Hence, the developer was able to ensure the successful creation of
Biometric ASYU by being prepared to face the challenges of the system.
Effective research work: research had been done effectively which help the user to
study and compare different algorithms in use today to implement fingerprint
identification system. and affective research to help the system as a whole.
Response from the end user; response from the end user were satisfied and that
demonstrate their satisfactory with the system.
7.3 Weakness of the system
These skills will benefit me in my future undertakings. The main air of a project for the
developer is to gain experience which will help him in future in the development of potential
software products. Although the developer has had many hurls to cross and encountered
many problems, he gained valuable skills. Success of a project also can be considered in
terms of the knowledge gained by developing the project. The project assisted the developer
in gaining immense knowledge in different areas, mainly being:
Implementing a systems which require Fingerprint identification as an authorization
module.
Understanding the concept of image processing algorithms and how to apply them
Developing a system musing a relevant software methodology and adequate database
architecture.
Improvement in my programming skills, especially in .Net programming languages.
To get more familiar with the programming language C#.
University Of East London 136 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Understanding more about the human computer interaction factor that could affect the
usability of my syste
7.4 Future Enhancement
Integration with Payroll system; in the future this system could be integrated with the
payroll system.
Upgrade to run on network environment
More efficient algorithms may be applied
In the future this system will be changed and improve to become an expert system which
is capable I doing various type of decision making.
7.5 Conclusion
The common notion that an IT project (whether programming-intensive or research-intensive) is
an individual effort can be easily dismissed, in the developer’s point of view. Such projects are
rarely, if ever, the work of one individual. Any IT project requires vast amount of research, fact-
finding, observation, and subsequently, analysis and design. For the developer, the past 32
weeks, the span of the project development lifecycle, have been an eye-opening, yet learning
experience. The developer feels that on completion of this project, he is better able to undertake
future challenges of such nature.
Most importantly, as explained earlier sections, the project has helped the developer to build up a
broader perception of how project are developed in an industrial ambiance. Meeting deadlines,
conduction interviews, analyzing observations and every other skill picked up during the period
of the itinerary as a student in YEMEN UNIVERSITY, has been successfully un-doubtfully
added value to the developer’s professional and academic proficiency & knowledge. The
developer has learnt the value of research & development and how it can be applied for real life
problems.
University Of East London 137 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Approaching the subject of development of a massive image processing and fingerprint
identification methods, the developer commenced the project with absolutely no clue on how to
proceed with such a task. Moving on to the development part, it was painful experience and
some might say a big mistake for a beginner to attempt something of this scale. Understanding
the whole concept of Fingerprint identification in itself was the main challenge. Picking up
programming skills and also conducting the research on the system at the same time has been a
strenuous job for the developer
Generally speaking, after the completion of the project, the developer realized that it was an
indispensable experience before finally stepping off the train that is a college education onto the
platform entitled the Real World.
References & Bibliography
Books
P. Krutchen, The Rational Unified Process (Boston: Addison-Wesley, 2000), p. 23.
S. . R. Schach, Object-Oriented and Classical Software Engineering (Boston: McGraw-
Hill,2002), p. 71.
Philippe Kruchten, A Rational Development Process, CrossTalk, 9 (7), STSC, Hill AFB,
UT, pp.11-16.
Philippe Kruchten, A Rational Development Process, CrossTalk, 9 (7), STSC, Hill AFB,
UT, pp.11-16.
Gonzalez, R., & Woods, R. (2008). Digital Image Processing. San Francisco: Ignatius
Press.
University Of East London 138 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
K. Beck, “Embracing Change with Extreme Programming,” IEEE Computer, 32
(October1999), pp. 70–77.
P. C. Patton, “The Development of the Idea of Computer Programming,” QMCS White
Paper 2003.3, St. Thomas University, June
J. Rumbaugh, I. Jacobson, G. Booch, The Uniform Modeling Language (Boston:
Addison-Wesley, 1998).
K. Nandakumar and A. K. Jain “Local correlation-based fingerprint matching”, In Indian
Conference on Computer Vision, Graphics and Image Processing, pages 503–508, 2004.
A. Ross, J. Reisman, and A. K. Jain, “Fingerprint matching using feature space
correlation,” in Proc. Post-ECCV Workshop on Biometric Authentication, pp 48-57,
Copenhagen,Denmark, June 1, 2002.
Fayyaz A. Afsar, M. Arif and M. Hussain “Fingerprint Identification and Verification
using Minutiae Matching”, in proc. National Conference on Emerging Technologies,
Karachi, Pakistan, 2004.
A. Cockburn, Writing Effective Use Cases (Boston: Addison-Wesley, 2001).
Wilhelm Burger and Mark J. Burge (2007). Digital Image Processing: An Algorithmic
Approach Using Java.
Articles & Whitepapers
A. K. Jain, L. Hong, and R. Bolle “On-line fingerprint verification” IEEE Trans. Pattern
Anal. Machine Intell., 19(4):302–314, 1997.
B. W. Boehm, “A Spiral Model of Software Development and Enhancement,” IEEE
Computer, 21 (May 1988), pp. 61–72.
Chitresh Saraswat, Amit Kumar “An Efficient Automatic Attendance System using
Fingerprint Verification Technique” IEEE Computer Science and EngineeringVol. 02,
No. 02, 2010, 264-269
B.G. Sherlock. D.M. Monro. K. Millard., “Fingerprint enhancement by directional
Fourier filtering,” IEE hoc.-Vis. Image Signal Processing, Vol. 141, No. 2, April 1994.
University Of East London 139 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
E. Hastings, “A Survey of Thinning Methodologies,” Pattern analysis and Machine
Intelligence, IEEE Transactions, vol. 4, Issue 9, pp. 869 885, 1992.
Wei Wang, Jianwei Li, Feifei Huang, “Design and implementation of Log-Gabor filter in
fingerprint image enhancement”, Pattern Recognition Letters, Volume 29, Issue 3, 1
February 2008, Pages 301-308.
Lin Wang, “An effective method for extracting singular points in fingerprint images”,
AEU - International Journal of Electronics and Communications, Volume 60, Issue 9, 2
October 2006, Pages 671-676.
Rodrigo de Luis-García, “Biometric identification systems”,Signal Processing, Volume
83, Issue 12, December 2003, Pages 2539-2557.
Xuejun Tan and Bir Bhanu, “A robust two step approach for fingerprint
identification”,Pattern Recognition Letters, Volume 24, Issue 13, September 2003, Pages
2127-2134.
Partha Bhowmick, Bhargab B. Bhattacharya, “Removal of digitization errors in
fingerprint ridgelines using B-splines”,Pattern Recognition, In Press, Accepted
Manuscript, Available online 19 March 2008.
Websites
Salil Prabhakar, Anil Jain, “Fingerprint Identification” [online] march 2010, Available at:
http://www.cse.msu.edu/biometrics/fingerprint.html
MathWorks, “Perform image processing, analysis, and algorithm development”, [online]
march 2010, available at : http://www.mathworks.com/products/image/
Wiki, “Image processing”, [online] available at :
http://en.wikipedia.org/wiki/Image_processing
Keith Price's Annotated Computer Vision Bibliography
Andrew Kirillov, “Image Processing Lab in C#”, [online], july 2010, available at
http://www.codeproject.com/KB/GDI-plus/Image_Processing_Lab.aspx
University Of East London 140 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Appendices
Proposal
Attendance system using fingerprint for Yemen University
Project background.
The proposed automatic attendance system using fingerprint verification techniq1ue. A
fingerprint is captured by user interface, which are likely to be an optical, solid state or an
ultrasound sensor, or a 300DPI (Dots Per Inch) or above 2D fingerprint image. Generally, there
are two approaches are used for fingerprint verification system among them first one is Minutiae
based technique, in which minutiae is represented by ending or termination and bifurcations.
University Of East London 141 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Other one is Image based method or matching pattern, which take account of global feature of
any fingerprint image.
The main aim of this system is to develop an accurate, fast and very efficient automatic
attendance system using fingerprint verification technique for Yemen’s university staff. The
system is proposed in which fingerprint verification is done by using extraction of one of the
techniques available and the system that automates the whole process of taking attendance,
Manually which is a laborious and troublesome work and waste a lot of time, with its managing
and maintaining the records for a period of time is also a burdensome task. For this purpose we
use fingerprint verification system using extraction of minutiae techniques.
First, when the user is to be enrolled to the system his/her fingerprint should be scanned using
the scanner and stored in the database along with his/her identity information.
There will be two modes in the system: staff mode where the staff can monitor their summarized
weekly/monthly attendance. And Admin mode where the admin can monitor all staff attendance
as well as adding, deleting, and updating staff.
Problem statements:
In many institutions and organization the attendance is a very important factor for various
purposes and its one of the important criteria that is to follow for students and organization
employees. The previous approach in which manually taking and maintains the attendance
records was very inconvenient task.
There are a number of problems associated with paper staff timesheets.
Forgetfulness : Some employees forget to complete their timesheets regularly and have to take
their best guess about when they arrived, went for lunch and left for the day. The employees or
the company may lose out.
University Of East London 142 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Time Wasting. With the pen and paper method, Yemen’s university staff suffers from the
wastage of time. Staff take more time to fill the page of the paper to mark the attendance and
thereby queue used to form for just marking the presence.
Rounding up and fraud . Other employees may routinely increase their hours by rounding up
their times. They may do this without thinking, but a few minutes each day can be equivalent to a
week or so over the course of a year. This equates to a week’s pay without the work to show for
it; and if everyone in your company does the same, there’s an impact on efficiency and
profits.Signature copy and misuse leading to fraud.
Administrative headaches . Producing an accurate total for a manual employee timesheet can be
time-consuming and contentious. Employees may make mistakes, so a senior officer has to
check the figures. This officer must then explain any adjustments to the staff member in time to
meet the payroll deadline. If the employee isn’t available, the senior officer has to submit a
revised time sheet that may reduce the amount of pay the employee expects – and this is certain
to cause annoyance.
Maintenance of records. A company must keep paper timesheets in case problems arise in the
future. You may need the sheets at a disciplinary hearing, for instance. You must therefore have
secure storage, which takes up valuable office space.
Rationale:
Biometric ASYU the automated time and attendance system can solve these problems. The
hardware provides a point at which each staff must clock on and off; the timesheet software turns
the information into a simple record of attendance.
The fingerprint verification can be defined as the system that confirm the authenticity of one
person by comparing his captured fingerprint templates against the stored templates in database.
The following tangible and intangible benefits are anticipated
Extreme high level of security against employee in time clocking.
Reduction of payroll error and eliminate hours of payroll calculations
Can be linked to payroll system automatically and easily
University Of East London 143 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Productivity and social ties among staff will increase due to improved employee morale
and motivation from the procedural justice within the proposed system and elimination of
unethical and misconduct facilitated from the current system.
Staff won’t have to waste their precious working time only to fill the hand book and they
do not need to stand in the long queue for marking the attendance.
Due to the use of biometric technology and that each user’s fingerprint is unique,
signature copying and “buddy-punching” is impossible.
Nature of the challenge:
The main challenge in developing this system is implementing fingerprint verification process.
The system must get user’s fingerprint image, acquire it, process it, extract the features from it,
and create/match templates. I have to understand how image processing works and how to apply
it, writing and understanding different complex algorithms in image processing and manipulating
and understanding them to make a complete Fingerprint recognition system. The system must be
able to match a person’s fingerprint correctly and consistently. The techniques and algorithms
involved require extensive research and data gathering to be done to understand fully how the
process of verification are done and the best tools that are required to develop the system.
Finding the appropriate Fingerprint scanner device and integrate it with the system is challenging
process.
Project objectives & Scope of proposal and deliverables
Biometric ASYU is an advanced staff authentication system which incorporates biometric
technology. In other words, fingerprint verification is used to authenticate the staff arrival time
and more importantly to identify the person. The following modules are included in this project
in order to address the problem mentioned in previously
Core Modules:
These are the main functionalities and the core of my project
Image processing and enhancement such as binarization, thinning, segmentation and
down sampling.
University Of East London 144 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Fingerprint(template) matching
Database module for storing the fingerprint images.
Enhanced function:
Additional to validating the authenticity of users and capturing the time, the system also aims to
include additional features to make the system more complete. Some such features include:
Generation of appropriate reports that are useful for the management to take appropriate
actions.
User profiling where the user can view their weekly or monthly summarize attendance
Staff management such as monitoring, adding, updating, deleting users.
Special Features:
Based on my research and if I have the time, these are the advanced features the developer is
going to develop the system that could be implement in a network environment.
Assumptions and scope limitation:
Thus to complete the system, there are some limitation in the system as I will not be attempting
on:
Although this system could be implemented in a network environment, it is planned to
simulate as standalone.
In case the fingerprint scanner does not capture clear and high quality images of the
fingerprint, 2D images of fingerprint would be tested instead.
The system also assumes that fingers are undamaged which means to say that this system
is not capable of dealing with major changes that has been taken place to the finger due to
damages and/or scars.
University Of East London 145 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Learning objectives
The main learning objective of this project is to research various methods of extracting features
and template matching methods in use today. This includes two broad categories: minutiae-based
and correlation based.
Therefore I need to research various algorithms used to implements the mentioned methods.
Furthermore, I also need to compare and contrast these algorithms and identify the best suited
algorithm for the selected choices
Apart from this, it is also a learning objective to study image processing methods and algorithms
such as binarization, thinning, segmentation and down sampling.
In order to implement the system, an object oriented programming languages is necessary. For
this reason I mush master one of them, I chose C#. I have to master C# in processing images,
interacting with the SDK component that comes with the fingerprint scanner in order to invoke
the functionality such as capturing image from the scanner.
Hardware, software components, access to information / expertise, user involvement
Hardware & Software
The hardware and software required during the development period.
A standard PC running Window NT or later is required during the development period
Microsoft® Visual Studio 2008 or later with .Net framework 3.5 or later
Microsoft® Developer Network (MSDN) libraries
Microsoft® SQL Server
Microsoft® Office 2007 or later
The Fingerprint Scanner API (Application Programming Interface) /SDK (Software
Development Kit) for capturing a raw image
University Of East London 146 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Access to information/expertise
The main source of information for doing this system will be conducting interviews,
questionnaires, books, journals, whitepapers, and research papers. These resources will be
offering the necessary information to develop the system.
Besides that, various websites will also help to accomplish my goal of developing a consistent
and precise system.
Forums also assist me in accessing the information by posting questions to other members in the
forum and it is essential for knowledge exchanging among other members who are keen in
biometric and image processing. Also, the website of the scanner’s company would probably
have its own forum where users exchange their knowledge with interacting with the sensor.
List of users to be interviewed for user requirement
Interview with staff of Yemen’s University
Interview with one of the Human Resource Department
Interview with one of the Research & Development Executive, Yemen university.
University Of East London 147 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Gants chart
University Of East London 148 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
APPENDIX C: Questionnaire Form (Data Gathering)
Biometric ASYU(Attendance system for Yemen University Staff )
Questionnaire
Thank you for participating in Biometric ASYU Data Gathering. Biometric ASYU is my
proposed Project as a final year project. It is proposed as a replacement to the current staff
attendance system. In the proposed system staffs would be able to clock-in and out by placing
their thumb on a fingerprint scanner instead of the current method. Besides, it allows the users to
login to the system and check their attendance and time summery reports. If you have any
questions regarding the completion of this questionnaire please contact Raed Mohammed by
phone 019-3709185 or email
raed_alawliqi@diplomats.com
This questionnaire is to be completed anonymously and you will not be identified as an
individual participant. Please answer truthfully.
Section A: Personal Information
9) Your job position: ________________________.
10) Department : _______________________.
11) What is your age range?
Below 18
18-27
28-37
38-55
Above 55
12) Your working days: (Pick the days you are working on)
Mon Tue Wed Thu Fri Sat Sun
University Of East London 149 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
6) Your working time:
Fixed; Start at: ______ AM/PM End at: _________ AM/PM.
Variable
Section B: Existing System Information
1) In your opinion the current staff attendance system (paper-based) in Yemen University is:
Excellent
Good
Satisfactory
Average
Poor
2) What is the approximate time taken to sign in and off to record your attendance?
___________Minute(s).
3) “Buddy punching” in manually attendance system is when somebody signs for somebody
in his/her absence. Do you agree these problems happen in the real world in such
attendance systems?
Yes No
4) In your opinion if the “buddy punching” problem is really happening, what is the best
strategy to overcome these problems?
Using a biometric system, such as fingerprint so that the person would be validated
based on the biological structure of the finger rather than any type.
Using Card swipe, to avoid “buddy punching” an additional staff is needed to be
employed to make sure nobody misuses the system.
Using the same manual system, employ additional staff to make sure that nobody
misuses the system
5) What do you like about the current staff attendance system? Please state two
University Of East London 150 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
5- _________________________________________
6- _________________________________________
6) What do you dislike about the current system? Please state two
1- __________________________________________
2- __________________________________________
Section C: About the new Biometric ASYU (YEMEN UNIVERSITY Staff Time &
Attendance) system
1) Do you have any experience with any biometric user authenticating system?
Yes No
2) Would you encourage using Fingerprint Verification staff time & attendance?
Yes No I don’t know
3) (In the proposed system, each staff would be able to not only clock-in and out to record
the time but also to log in and to view his/her profile)
What would you like to see in your profile other than your attendance summary?
APPENDIX D: Usability Testing Questionnaire
I would like to know your outlook subsequent to the testing of Biometric ASYU
Note: These details will be treated as private and confidential
Questions Poor Good Excellent
Compatibility
- Could you predict on the action that the buttons can
perform?
- Is the wording familiar?
- Is the controls matched to user skill?
University Of East London 151 U0749623
Attendance System Using The Fingerprint For Yemen University Staff
Consistency
is the assignment of color codes conventional?
is the coding consistent across display, menu options?
is the display format consistent?
are symbols for graphic data standard?
are the user actions required consistent?
is the format within date fields consistent?
Does the confirmation feedback find consistent?
Flexibility
is the design for data entry flexible?
are the menu options dependent on context?
does it provide flexible sequence control?
If mistake were done, do you think that the system help you
to recover from it?
Minimal Actions
Does it provide default values?
Is the shifting among windows easy?
Does it require minimal steps in sequential menu selection?
does it require minimal user control actions
Is the return to general menu required only one simple key
action?
Name:…………..
Designation:………………
Signature:……………
Thank you for your time and cooperation!!!
University Of East London 152 U0749623
Вам также может понравиться
- PCNG ManualДокумент323 страницыPCNG ManualAlan Lira100% (1)
- Chapter 1: What Is Simulation? .......................................................................................... 1Документ8 страницChapter 1: What Is Simulation? .......................................................................................... 1Ayrton Barriga AguilarОценок пока нет
- IndexДокумент103 страницыIndexFernando Calderon AyalaОценок пока нет
- AT1007E Application Notes Smoke Value MeasurementДокумент98 страницAT1007E Application Notes Smoke Value MeasurementViktor DilberОценок пока нет
- TE 002222 MOP 002 OMS Operation ManualДокумент97 страницTE 002222 MOP 002 OMS Operation ManualGerman ParraОценок пока нет
- Online Tailoring Management System Ch1-2Документ21 страницаOnline Tailoring Management System Ch1-2Simegnew TizazuОценок пока нет
- Teleca - OSS For Network Operators - Mentions Service Robots - Apr02Документ52 страницыTeleca - OSS For Network Operators - Mentions Service Robots - Apr02Amit ZoharОценок пока нет
- Apache Unomi 1.X - DocumentationДокумент53 страницыApache Unomi 1.X - Documentationkuldeep singhОценок пока нет
- RCST Pro - HTMLДокумент55 страницRCST Pro - HTMLDavid LaduОценок пока нет
- TptmshandbookДокумент134 страницыTptmshandbookDinithi LakshikaОценок пока нет
- Final Project Online Broker Management Systemfull DocumentationДокумент124 страницыFinal Project Online Broker Management Systemfull DocumentationAmanuel Nigussu0% (1)
- JUnit 5 User GuideДокумент90 страницJUnit 5 User GuideaawaakОценок пока нет
- eBook-Explicit Analysis RADIOSS 230824 125223Документ387 страницeBook-Explicit Analysis RADIOSS 230824 125223zacheu35Оценок пока нет
- Ambo University Awaro Campus Online Student Union Voting System1244Документ59 страницAmbo University Awaro Campus Online Student Union Voting System1244wanofi israelОценок пока нет
- Visual TD Developer ReferenceДокумент159 страницVisual TD Developer ReferenceBairon AlviraОценок пока нет
- Machine LearningДокумент87 страницMachine LearninghiphoplistenerОценок пока нет
- Comment - EEP Procurement Manual - Mgmt-Aa - RevisedДокумент150 страницComment - EEP Procurement Manual - Mgmt-Aa - RevisedBelay TadesseОценок пока нет
- WRU Project Guideline For StudentsДокумент40 страницWRU Project Guideline For StudentsAdugna BayisaОценок пока нет
- Reactive SpringДокумент421 страницаReactive SpringfranceteОценок пока нет
- Open Sim Users Guide 04042012Документ258 страницOpen Sim Users Guide 04042012manishpaliОценок пока нет
- Part 20Документ152 страницыPart 20k516517Оценок пока нет
- Road Safety Audit Spec 220829Документ37 страницRoad Safety Audit Spec 220829Anup Kumar HalderОценок пока нет
- Reactive SpringДокумент378 страницReactive SpringMihai PistruiОценок пока нет
- MEI SCR Integration ToolkitДокумент72 страницыMEI SCR Integration ToolkitlasercrazerОценок пока нет
- An Introduction To Tkinter (Fredrik Lundh)Документ211 страницAn Introduction To Tkinter (Fredrik Lundh)Hernando CortezОценок пока нет
- Mockito Programming CookbookДокумент74 страницыMockito Programming CookbookAndrei Lucian Mircioagă100% (1)
- E100M002 15 GuideD'utilisationFibroScan EN-GBДокумент82 страницыE100M002 15 GuideD'utilisationFibroScan EN-GBE.D.V.Оценок пока нет
- Assignment: Human Computer Interaction and DesignДокумент56 страницAssignment: Human Computer Interaction and DesignLong LongОценок пока нет
- Openclinic Technical DocumentationДокумент21 страницаOpenclinic Technical DocumentationtiescoОценок пока нет
- SampleManager User GuideДокумент164 страницыSampleManager User GuideLuis Muchaki100% (3)
- Manual NIAflow Software (En)Документ172 страницыManual NIAflow Software (En)Vladimir Illich PinzonОценок пока нет
- Sam61us Manual PDFДокумент158 страницSam61us Manual PDFByron UchupantaОценок пока нет
- Junit5 User Guide PDFДокумент93 страницыJunit5 User Guide PDFripudsudanОценок пока нет
- Junit User Guide 5.10.2Документ179 страницJunit User Guide 5.10.2Sunitha RekhaОценок пока нет
- MANUAL DEALER EN Ver.2.6Документ77 страницMANUAL DEALER EN Ver.2.6Renato SanchezОценок пока нет
- FLR4537 - Module 2Документ62 страницыFLR4537 - Module 2Tofael Uddin Ahmed MajmadarОценок пока нет
- En - User Manual Proslide 32b - Reva - 2016-04Документ78 страницEn - User Manual Proslide 32b - Reva - 2016-04顾小艾Оценок пока нет
- Mobile Application Development BikilaДокумент67 страницMobile Application Development BikilaKidus AsfawosenОценок пока нет
- Sigtran Openss7Документ150 страницSigtran Openss7Jesus Bazan100% (1)
- C Control Pro Eng PDFДокумент240 страницC Control Pro Eng PDFszabo gabrielОценок пока нет
- Wind Power Development ToolkitДокумент200 страницWind Power Development Toolkitsebascian100% (1)
- Reactive Spring by Josh LongДокумент378 страницReactive Spring by Josh Longloverof liuyifeiОценок пока нет
- CGP-01900-011 BBL N en 2010-10-01Документ101 страницаCGP-01900-011 BBL N en 2010-10-01qualidade gdbrОценок пока нет
- visDesBook PDFДокумент158 страницvisDesBook PDFnoahkrpgОценок пока нет
- The System NotesДокумент36 страницThe System Notesasdad92% (13)
- Otto2 1 4Документ56 страницOtto2 1 4previzsla66Оценок пока нет
- CSIS Manual v2019.Документ111 страницCSIS Manual v2019.nurse2012100% (1)
- Reliability Engineering - A Life Cycle ApproachДокумент439 страницReliability Engineering - A Life Cycle ApproachrobertoОценок пока нет
- Indonesia Refrigerator Market Study - FINALДокумент76 страницIndonesia Refrigerator Market Study - FINALreauhan100% (1)
- Case Engineering - ManuelДокумент172 страницыCase Engineering - ManueljmОценок пока нет
- ISPE Guide: Science and Risk-Based Approach For The Delivery of Facilities, Systems, and EquipmentДокумент3 страницыISPE Guide: Science and Risk-Based Approach For The Delivery of Facilities, Systems, and EquipmentLuis Gerardo Rendón BeltránОценок пока нет
- ADAPT-Floor Pro 20 User ManualДокумент262 страницыADAPT-Floor Pro 20 User ManualMarisol SanchezОценок пока нет
- s192 - The Open Group Agile Architecture FrameworkДокумент118 страницs192 - The Open Group Agile Architecture FrameworkFaqih ZulfikarОценок пока нет
- MicroStation Student ManualДокумент53 страницыMicroStation Student ManualAlok NahakОценок пока нет
- XFlow2019x Refresh2 UserGuideДокумент325 страницXFlow2019x Refresh2 UserGuideIsrael OluwagbemiОценок пока нет
- Pegasus Users GuideДокумент102 страницыPegasus Users GuideOmarH.Morales0% (1)
- 2022-06-10 - List Revisi DRPPLN Green Book 2022Документ7 страниц2022-06-10 - List Revisi DRPPLN Green Book 2022Maulana FamilyОценок пока нет
- NAA Standard For The Storage of Archival RecordsДокумент17 страницNAA Standard For The Storage of Archival RecordsickoОценок пока нет
- M580 HSBY System Planning GuideДокумент217 страницM580 HSBY System Planning GuideISLAMIC LECTURESОценок пока нет
- HDM Method PDFДокумент117 страницHDM Method PDFBonagiri DheerajОценок пока нет
- GE TVSS Specification Data Sheet (TME 65ka - 100ka - Wall Monut)Документ3 страницыGE TVSS Specification Data Sheet (TME 65ka - 100ka - Wall Monut)Angela TienОценок пока нет
- STAT 344 SyllabusДокумент7 страницSTAT 344 SyllabusnoОценок пока нет
- SWFP66D Series Fine-Grinding Hammer Mill: Operation ManualДокумент65 страницSWFP66D Series Fine-Grinding Hammer Mill: Operation ManualDanielDeFrancescoОценок пока нет
- Assignment 4 Forward KinematicsДокумент2 страницыAssignment 4 Forward KinematicsVaibhav KulkarniОценок пока нет
- Multi DIALOG MDM - MDT. MDM 10-20kVA Single - Single-Phase and Three - Single-Phase MDT 10-80kVA Three - Three-Phase NETWORK RANGEДокумент8 страницMulti DIALOG MDM - MDT. MDM 10-20kVA Single - Single-Phase and Three - Single-Phase MDT 10-80kVA Three - Three-Phase NETWORK RANGEMARCOS LARA ROMERO DE AVILAОценок пока нет
- Lecture-13 Indexing and Its Types: Subject: DBMS Subject Code: BCA-S301T Faculty: Saurabh JhaДокумент16 страницLecture-13 Indexing and Its Types: Subject: DBMS Subject Code: BCA-S301T Faculty: Saurabh JhaShivam KushwahaОценок пока нет
- Fractional Fourier TransformДокумент12 страницFractional Fourier Transformvolly666Оценок пока нет
- Soil Classification and Crop Recommendation SystemДокумент4 страницыSoil Classification and Crop Recommendation SystemInternational Journal of Innovative Science and Research TechnologyОценок пока нет
- Infografia Línea Del Tiempo Historia de La Computadoras en InglesДокумент1 страницаInfografia Línea Del Tiempo Historia de La Computadoras en InglesGEORGEGAMER MCОценок пока нет
- Function: Maintenance & Repair at Operational LevelДокумент2 страницыFunction: Maintenance & Repair at Operational LevelSHUSHEELОценок пока нет
- Sop SampleДокумент2 страницыSop Samplearshpreet bhatiaОценок пока нет
- PD2083-EL-HAZ-A1-004.pdf HAZARDOUS AREA CLASSIFICATION SV STATION-3Документ1 страницаPD2083-EL-HAZ-A1-004.pdf HAZARDOUS AREA CLASSIFICATION SV STATION-3Alla Naveen KumarОценок пока нет
- Purposive Communication AssignmentДокумент2 страницыPurposive Communication AssignmentJohn Warren MestiolaОценок пока нет
- First Order Logic: Artificial Intelligence COSC-3112 Ms. Humaira AnwerДокумент24 страницыFirst Order Logic: Artificial Intelligence COSC-3112 Ms. Humaira AnwerKhizrah RafiqueОценок пока нет
- OpenTxt VIM TablesДокумент20 страницOpenTxt VIM Tablesmanasb27Оценок пока нет
- An Inflection Point For The Data-Driven Enterprise: Pulse SurveyДокумент20 страницAn Inflection Point For The Data-Driven Enterprise: Pulse SurveyAndy BaneОценок пока нет
- Getting Started With PIC18F4550 and MPLABX IDE - PIC ControllersДокумент11 страницGetting Started With PIC18F4550 and MPLABX IDE - PIC ControllersKrishanu Modak100% (1)
- Java Lab RecordДокумент29 страницJava Lab RecordCyberDootОценок пока нет
- ZTE H3601 OverviewДокумент2 страницыZTE H3601 OverviewAnonymous dzjg5bTEОценок пока нет
- Selva Kumar: Ocean Operations, Global Business Operations, Health & Safety & OM ImportsДокумент3 страницыSelva Kumar: Ocean Operations, Global Business Operations, Health & Safety & OM ImportssenisagoodboyОценок пока нет
- Gen Set Controller GC 1f 2Документ13 страницGen Set Controller GC 1f 2Luis Campagnoli100% (2)
- FB156Документ14 страницFB156Hoangvinh DuongОценок пока нет
- SGV Series: Storage Filling PumpДокумент2 страницыSGV Series: Storage Filling PumpAnupam MehraОценок пока нет
- ECIL Technical Officer Recruitment 2023 NotificationДокумент3 страницыECIL Technical Officer Recruitment 2023 NotificationLucasОценок пока нет
- OM Appendix 3D Diamond DA40NG Flight Operations ManualДокумент123 страницыOM Appendix 3D Diamond DA40NG Flight Operations ManualBekhzod ArtygaliyevОценок пока нет
- Cat 320 Next Gen Excavator BrochureДокумент16 страницCat 320 Next Gen Excavator BrochureKeron TrotzОценок пока нет