Академический Документы
Профессиональный Документы
Культура Документы
InfoX SMS V300R002 System Description
Загружено:
akileshsingh125Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
InfoX SMS V300R002 System Description
Загружено:
akileshsingh125Авторское право:
Доступные форматы
infoX-SMS System Description
Table of Contents
infoX SMS V300R002 System Description (V1.00)
Huawei Technologies Co., Ltd.
All rights reserved.
Huawei Technologies Proprietary i
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Table of Contents
Table of Contents
Chapter 1 System Overview .................................................................................................... 1-1 1.1 Basic Concepts............................................................................................................. 1-1 1.2 System Overview .......................................................................................................... 1-1 1.2.1 Functions of the SMS System ............................................................................. 1-1 1.2.2 System Features................................................................................................. 1-2 1.3 infoX-SMS System in the Network................................................................................. 1-6 1.3.1 System Architecture............................................................................................ 1-6 1.3.2 Position of the SMS System in the Network......................................................... 1-9 1.4 External Interfaces ........................................................................................................ 1-9 Chapter 2 System Architecture ............................................................................................... 2-1 2.1 Design Concept of the SMS system .............................................................................. 2-1 2.2 SMS System Architecture.............................................................................................. 2-3 2.2.1 Signaling Gateway .............................................................................................. 2-4 2.2.2 MTI Server.......................................................................................................... 2-4 2.2.3 GSM MAP Server ............................................................................................... 2-5 2.2.4 CDMA MAP Server ............................................................................................. 2-5 2.2.5 SMSC................................................................................................................. 2-5 2.2.6 Dual System Management Module...................................................................... 2-7 2.2.7 MT Module.......................................................................................................... 2-9 2.2.8 Alert Server........................................................................................................2-10 2.2.9 Information Security Monitoring System .............................................................2-10 2.2.10 Report Processing System...............................................................................2-11 2.2.11 Network Management System..........................................................................2-11 2.3 Hardware Structure ......................................................................................................2-13 Chapter 3 System Functions and Implementation.................................................................. 3-1 3.1 Basic Service Supporting Functions .............................................................................. 3-1 3.1.1 SM Submission................................................................................................... 3-1 3.1.2 SM Delivery ........................................................................................................ 3-1 3.1.3 Status Report...................................................................................................... 3-1 3.1.4 Information Security Authentication ..................................................................... 3-2 3.1.5 Authentication and Charging ............................................................................... 3-2 3.1.6 Multiple Coding Schemes.................................................................................... 3-3 3.1.7 Number Conversion According to the Fields of TON, NPI, ADDRESS and PID.... 3-4 3.1.8 Authenticating Subscribers.................................................................................. 3-4 3.1.9 Delivery of Long SMs.......................................................................................... 3-5 3.1.10 Delivery of SMs to Multiple Destinations............................................................ 3-6 3.1.11 Delivery of Multiple SMs to a Destination........................................................... 3-6 3.1.12 Virtual SMC Authentication................................................................................ 3-7 3.1.13 Universal Flow of Authentication and Number Conversion................................. 3-7
Huawei Technologies Proprietary ii
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Table of Contents
3.1.14 Virtual SMC ...................................................................................................... 3-8 3.1.15 Muitiple MAP Servers Function ......................................................................... 3-8 3.1.16 Multiple Schedule Modes .................................................................................. 3-9 3.1.17 Message Exchange Between the CDMA Network and TDMA Network .............. 3-9 3.1.18 UserAck Messages ........................................................................................... 3-9 3.1.19 Distinguishing Subscriber Network Attributes According to Different Number Segments...................................................................................................................3-10 3.1.20 PUSH Messages of the WAP Service...............................................................3-10 3.1.21 PUSH Messages in the MMS Service...............................................................3-10 3.1.22 PRL Function ...................................................................................................3-11 3.1.23 IRDB................................................................................................................3-11 3.1.24 Supporting UCP 4.0 .........................................................................................3-11 3.1.25 SMs Without Calling Number ...........................................................................3-12 3.1.26 Time Zone Features.........................................................................................3-12 3.1.27 Supporting SMPP 3.3.......................................................................................3-12 3.1.28 Supporting SMPP 3.4.......................................................................................3-13 3.2 Core Scheduling Functions ..........................................................................................3-13 3.2.1 Basic Functions .................................................................................................3-13 3.2.2 Basic Scheduling Processing .............................................................................3-14 3.2.3 SM Priority Processing.......................................................................................3-15 3.2.4 Validity Period Processing..................................................................................3-17 3.2.5 Repeated SM Redelivery Processing .................................................................3-20 3.2.6 Scheduling Mode Processing .............................................................................3-21 3.2.7 Entity-Based Scheduling Processing ..................................................................3-22 3.2.8 Multidimensional Intelligent Scheduling ..............................................................3-23 3.2.9 L2CacheDaemon Processing.............................................................................3-25 3.2.10 Threshold Processing ......................................................................................3-26 3.2.11 Functions of the GSM MAP Server...................................................................3-27 3.2.12 Functions of the CDMA MAP Server ................................................................3-28 3.3 Basic Services .............................................................................................................3-29 3.3.1 MO SMs ............................................................................................................3-29 3.3.2 MT SMs .............................................................................................................3-29 3.3.3 Shortcut Messages ............................................................................................3-29 3.3.4 Twinkle SMs ......................................................................................................3-30 3.3.5 Alert Notification Service ....................................................................................3-31 3.3.6 EMS SMs...........................................................................................................3-31 3.3.7 Prepaid SMs ......................................................................................................3-31 3.4 Management Functions................................................................................................3-32 3.4.1 Logs and Alarms................................................................................................3-32 3.4.2 Bill Statistics and Browsing ................................................................................3-33 3.4.3 System Parameter Setting .................................................................................3-33 3.4.4 System Status Monitoring ..................................................................................3-33 3.4.5 Database Maintenance ......................................................................................3-33
Huawei Technologies Proprietary iii
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Table of Contents
3.4.6 Network Management ........................................................................................3-33 3.4.7 Report Statistics.................................................................................................3-33 3.5 Operation and Maintenance .........................................................................................3-34 3.5.1 Authenticating OMC Subscribers........................................................................3-34 3.5.2 Configuring SMS System Parameters ................................................................3-34 3.5.3 Pre-defined SMs ................................................................................................3-35 3.5.4 Setting Authentication and Number Conversion Parameters...............................3-35 3.5.5 SMSC Account Management .............................................................................3-36 3.5.6 Setting Route Tables..........................................................................................3-36 3.5.7 PPS Route Number Segments...........................................................................3-36 3.5.8 Other Operators Number Segment Management...............................................3-36 3.5.9 SMSC Monitoring and Tracing ...........................................................................3-37 3.5.10 SM Test ...........................................................................................................3-38 3.5.11 Exporting SMs to Files .....................................................................................3-38 3.5.12 SM Subscriber Management ............................................................................3-39 3.5.13 Multidimensional Schedule Parameter Management ........................................3-40 3.5.14 L2Cache Management.....................................................................................3-41 3.5.15 Checking the Running Status of the SMS System with MSs .............................3-41 Chapter 4 Charging Function and Implementation................................................................. 4-1 4.1 Charging for the SMS Postpaid................................................................................. 4-1 4.2 Charging for the SMS Prepaid .................................................................................. 4-1 4.2.1 PPS Authentication and Charging Flow............................................................... 4-2 4.2.2 SCP Interconnection Authentication and Charging Flow ...................................... 4-5 4.2.3 MDSP Charging Flow.......................................................................................... 4-6 4.2.4 UTIns Unicom PPS Charging Flow...................................................................... 4-6 4.3 Charging for Long SMs ................................................................................................. 4-8 4.4 Individual Number PPS Function................................................................................... 4-9 Chapter 5 Reliability and Availability Design.......................................................................... 5-1 5.1 Reliability Design .......................................................................................................... 5-1 5.1.1 Dual System Running Mode................................................................................ 5-1 5.1.2 Network Running Mode....................................................................................... 5-2 5.1.3 Flow Control ....................................................................................................... 5-3 5.1.4 Alarm Detection .................................................................................................. 5-3 5.1.5 Security Authentication ....................................................................................... 5-3 5.2 Availability Design......................................................................................................... 5-3 5.3 Extendibility Design....................................................................................................... 5-4 5.3.1 Overall Design .................................................................................................... 5-4 5.3.2 Product Upgrade Capability ................................................................................ 5-4 5.3.3 Function Extendibility .......................................................................................... 5-5 5.3.4 Performance Extendibility.................................................................................... 5-5 Chapter 6 Typical System Applications .................................................................................. 6-1 6.1 Service Networking ....................................................................................................... 6-1
Huawei Technologies Proprietary iv
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Table of Contents
6.2 Service Description ....................................................................................................... 6-2 6.3 Processing Flow............................................................................................................ 6-2 Chapter 7 Technical Indexes and Specifications.................................................................... 7-1 7.1 Hardware Specifications................................................................................................ 7-1 7.2 Performance Specifications........................................................................................... 7-2 7.3 International Standard Followed by the SMS System..................................................... 7-2
Huawei Technologies Proprietary v
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
Chapter 1 System Overview
This chapter describes the basic features of the infoX-SMS system. Taking the Global System for Mobile Communications (GSM) and Code Division Multiple Access (CDMA) networks for example, this chapter covers the position of the SMS system in the mobile network, as well as the functions and compliant specifications of the infoX-SMS system. You can learn about the features of the SMS system through reading this chapter.
1.1 Basic Concepts
The infoX-SMS system is a service processing system independent of the wireless network. It is responsible for submitting, storing, and forwarding short messages (SMs). It implements the interconnection with such networks as the public switched telephone network (PSTN), integrated services digital network (ISDN) and packet switched public data network (PSPDN) so as to transfer SMs between extended short message entities (ESMEs) and mobile stations (MSs). The basic services of the SMS system include:
l l l l
Mobile originated (MO) messages Mobile terminated (MT) messages Access through SMPP 3.3 and SMPP 3.4 SMs encoded in Unicode
1.2 System Overview
The SMS system:
l l
Implements SM exchange between the GSM and CDMA networks. Communicates with the PSTN, ISDN, and PSPDN, so as to transmit SMs from other short message entities (SMEs) such as the manual station and the automatic station. It is responsible for the SM reception, scheduling, storing, routing, backing up, forwarding, and delivering; implements the management on the SMEs connected to the SMS system.
Besides all the features of the version V300R001, the SMS system of this version is applied to the CDMA, TDMA, and GSM networks, providing the SM exchange among the CDMA, GSM and TDMA networks.
1.2.1 Functions of the SMS System
The functions of the SMS system are as follows:
l
Providing value-added services (VASs) and obtaining profits
Huawei Technologies Proprietary 1-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
As a basic telecom service of the mobile communication network, the SMS enables subscribers to transmit information through SMs and obtain such useful information as stock market, weather, sports and bank information, which greatly facilitates subscribers in getting information and gets subscribers into a better and closer relationship with operators. At the same time, operators can get direct revenue by providing VASs based on the SMS service.
l
Improving quality of service (QoS)
Mobile subscribers have high requirements for timely information transfer. In many cases such as channel busy, masking or network coverage problems, communication is difficult and information cannot be exchanged. With the SMS system, subscribers can get information at the earliest time and smooth information transmission is ensured.
1.2.2 System Features
I. High performance in handling signaling
The SMS system supports the TELLIN-USAU universal signaling access unit serving as the signaling access gateway. The TELLIN-USAU has the features as shown in Table 1-1. Table 1-1 Features of TELLIN-USAU Feature High performance in link accessing and handling Open protocol interface Description
It provides powerful signaling handling capacity for the SMS system.
It adopts the standard protocol interface which meets various networking demands of operators with the SSP, IP, and STP.
l
Modularized design and smooth expansion
The modularized superimposing structure is employed in hardware design. The expansion of processing frames in the mode of building blocks (frames are interconnected through LAN switch) meets increasing capacity requirements of subscribers. The processing capability can meet the capacity expansion requirement. The busy hour call attempt (BHCA) of the USAU reaches 39,000,000, with sufficient space for service extension, can meet the incremental service requirements of subscribers. In addition, the system supports the online smooth capacity expansion which does not influence the service running of the existing modules.
High reliability
The high reliability rests on the hot backup of components, redundancy configuration, and excellent software protection, and error tolerance, support of the congestion control of signaling and system failure test or isolation. All these factors guarantee the signaling handling capacity of the system.
Huawei Technologies Proprietary 1-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
& Note: TELLIN-USAU developed by Huawei Technologies Co., Ltd. is used as:
l l
the front end equipment for switching and accessing the signaling processing equipment of the SMS system
II. Modularized design and smooth expansion
Adopting TELLIN-USAU, the signaling gateway (SG) supports 104 links of 2 Mbps links or 1664 links of 64 Kbps. The infoX-SMS system adopts the modularized design and networking SMS system mode. The system distributes SMs among multiple MAP Servers and FCCs. Multiple SMS systems form a networking SMS system. SMs are distributed dynamically among different SMS systems, thus enhancing the reliability and fault tolerance of the whole system. The flexible networking mode enables you to choose from multiple MAP Servers networking, FCC flow distribution networking, and so on.
III. Complete integration of SMS services in the GSM, CDMA, and TDMA networks
The TELLIN-USAU connects with signaling devices of the CDMA, TDMA, and GSM networks at the same time, implementing the signaling access of SMs in the CDMA, TDMA, and GSM networks, and thus processing and scheduling SMs in the three networks uniformly. One set of the SMS system processes all the SM services of the three networks uniformly. CDMA, TDMA, and GSM SMs of the same operator do not need to be forwarded through another SMS system. Meanwhile, the SMS system can process SMs of a single network by separating signaling processing units (SPUs). It has the same functions as the Huawei-developed SMS system for the GSM, CDMA, or TDMA network, but has more powerful processing capability.
IV. Flexible scheduling modes
The SMS system provides three scheduling modes for different services, which are described in Table 1-2. Table 1-2 Description of scheduling modes Scheduling mode Description If an SM is delivered unsuccessfully, the short message scheduling center (SMSC) redelivers it until it is successfully delivered or it is time-out. The delivery interval depends on the error code returned from the NSS or the service system, and it can be set. The SM with high priority can be delivered first.
Store and Forward Message Mode
Huawei Technologies Proprietary 1-3
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
Datagram Message Mode
The SMSC returns the response message to the external entity as soon as it receives the SM submitted by the external entity. The SMSC delivers the SM only once regardless of the delivery result (success or failure). If the SMSC fails to deliver the SM due to flow control, however, the SMSC attempts to deliver it again. The SMSC immediately delivers an SM submitted by the ESME, and returns the delivery result to the ESME in the response to the submission request.
Transaction Message Mode
V. Supporting MDEST
The SMS system supports the multidimensional enhanced schedule technology (MDEST, short message Qos technology), which takes influences of different external conditions on SM transmission into consideration on the basis of basic scheduling mechanism. The feature parameters of the system environment, such as time, message flux, system kernel parameters, are regarded as factors that can affect the scheduling algorithm, and are taken into consideration of scheduling strategies. The SMS System dynamically adjusts scheduling strategies according to these parameters so as to provide different services for different subscribers.
VI. Supporting L2Cache processing
When the SMSC is busy, some SMs can be temporarily stored in the L2CacheDaemon database, and they will not be scheduled in real time. When the system load becomes lower, the SMSC reads the stored SMs from the L2CacheDaemon database to the memory of the SMSC so that the SMs can be scheduled. This method reduces the pressure of the busy SMSC, and improves the SM storing capability of the SMS System, the success rate of the SM transmission and the customer satisfaction rate.
VII. Supporting threshold processing
When the rate of a parameter value in the system over the corresponding parameter value in the License reaches the specified threshold, the system starts the threshold processing. It reduces the current SMS system load by distributing flow and indicating busy, ensuring the stability and security of the system and successful SM transmission.
VIII. Powerful service processing capability
The service processing system is a LAN system. An ordinary hub or a switched hub can be used for transmission of service data and voice data.
Huawei Technologies Proprietary 1-4
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
The stable and optimized database processing mechanism adopted by the SMS system greatly improves the SM processing performance and capability.
IX. Quick and accurate report processing capability
The SMS report system makes statistics of SM bill records, and outputs accurate and visual statistics reports. The operator thus can know various data of the SMS operation so as to perform analysis and make decisions, greatly facilitating the management on the SMS system by the operator.
X. Excellent function of bill statistics
Users can make statistics of flow information of specified SMs by configuring the counter and statistic groups, and export the information to total traffic bills, service traffic bills and delivery delay bills. It greatly helps to analyze various SM services. The SMS system supports two types of bills: charging bill and statistic bill.
l
Charging bill Charging bills include ordinary charging bills and CalledFee bills. After the creation of charging bills, the BillServer obtains charging bills from the charging bill directory periodically. And after some analysis, submits information of postpaid subscribers to the charging center for fee deduction. The information in charging bills can satisfy various charging requirements.
Statistic bill It includes nine types, namely, historical bill, MT bill, MO bill, Alert_SC bill, performance bill, information security statistic bill, total traffic bill, service traffic bill and delivery delay bill. These bills can be used by users to analyze the running condition of the SMS system.
XI. Excellent adaptability to the telecom network
Huawei-developed SMS system can interconnect with the GSM and CDMA networks of other suppliers, fully satisfying the subscribers' requirements. Meanwhile, the SMS system can realize SM exchange between different operators through the infoX-SMS GW, and realize the connection between the charging interfaces of the infoX-SMS system and the IN of Siemens.
XII. Perfect functions of maintenance, test, management and alarm
The maintenance and test (MT) system of the SMS system provides the functions of routine maintenance and test, including traffic measurement and recording, SM processing times measurement, statistics of traffic congestion, quality of service and performance and SMS test. The management of performance, maintenance, configuration and reports can be implemented through the SM manager. At the same time, the system has perfect functions of system maintenance and test, fault detecting and solving.
Huawei Technologies Proprietary 1-5
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
For the system faults of switching equipment, database, computer network and host software, hierarchical audible/visual located alarms can be provided through the alarm box, and detailed alarm information can be provided. The SMS system supports uniform remote maintenance and management through the NMS. In addition, the SMS system provides the MT console which can conduct maintenance and management on multiple SMS systems.
XIII. Comprehensive system security mechanism
l
The system's key components adopt the active/standby working mode. They can conduct switchover automatically. The system has perfect fault detecting and solving function. The system is designed with independent functional modules, and the abnormity inside a functional module cannot affect the normal running of other modules. The system can implement realtime status tracing and monitoring, and the operator responsible for system maintenance is informed in time through audible/visual multimedia alarms, thus ensuring the normal running of the system.
l l
The system performs a strict syntax check on the input man-machine operation command, rejects incorrect commands and returns prompts for errors. The user accounts of the system are uniformly allocated by the system administrator. Strict encryption and security measurements are taken on accounts to prevent the access of invalid users.
The system supports network management and monitoring through the iManager I2000 NMS.
1.3 infoX-SMS System in the Network
This section describes the architectures of the GSM, CDMA, and TDMA networks, as well as the position and functions of the infoX-SMS system in the three networks.
1.3.1 System Architecture
The system architectures of the CDMA, TDMA, and GSM networks are quite similar. Each of the three network systems is composed of the following four parts: network subsystem (NSS), base station subsystem (BSS), operation and maintenance center (OMC), and a great many mobile stations (MSs), as shown in Figure 1-1. There are interfaces between various subsystems and functional entities within the subsystems. The specifications in the CDMA, TDMA, and GSM networks stipulate standard interfaces and communication protocols through which the functional entities can implement communications coordinately. Adopting different interface specifications and protocols, the three mobile networks are independent of each other.
Huawei Technologies Proprietary 1-6
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
GSM Network
SMS
CDMA/TDMA Network
NSS
PSTN/ISDN/ PSPDN HLR/AUC/ EIR MSC/VLR
NSS
HLR/AUC/ EIR
MSC/VLR
OMC
DCN
BSC
BSS
BSS
DCN
BSC
OMC
BTS OMC Server Operation Console
BTS Operation OMC Server Console
MS
MS
SMS System: Short Message Service System HLR: Home Location Register EIR: Equipment Identity Register VLR: Visitor Location Register BSS: Base Station Subsystem BSC: Base Station Controller BTS: Base Transceiver Station MS: Mobile Station
NSS: Network SubSystem AUC: Authentication Center MSC: Mobile Switching Center PSTN: Public Switched Telephone Network ISDN: Integrated Services Digital Network PSPDN: Packet Switched Public Data Network OMC: Operation & Maintenance Center
Figure 1-1 Mobile network
I. NSS
In the mobile network, the NSS implements the switching function and database function. The database function is necessary for subscriber data management, mobility management and security management. The NSS includes the following functional entities:
l
MSC
The MSC controls calls, manages the communication service of MSs within the local network and with other networks (such as PSTN/ISDN/PSPDN, and other mobile networks), and provides the charging information. Besides, in order to set up call routes to MSs, the MSC can also function as the GMSC, that is, querying location information of MSs.
l
VLR
The visitor location register (VLR) stores the relevant information of registered subscribers in the control area, and provides the mobile subscribers with necessary conditions for call connection. It can be regarded as a dynamic database.
Huawei Technologies Proprietary 1-7
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
HLR
The home location register (HLR) is the central database of a mobile network. It stores the information of all mobile subscribers in the control area. The HLR stores two kinds of information: subscriber data, and location information of MSs for setting up call routes to the MSs.
l
AuC
The AuC stores authentication algorithm and encryption key, which prevent illegal subscribers from accessing the system, thus ensuring the security of the mobile subscribers' communications through the radio interface.
l
EIR
The EIR stores the International Mobile Equipment Identity (IMEI.). Generally the AuC and the EIR are integrated physically. Generally, the MSC and the VLR are integrated physically; and the AUC, EIR and HLR are integrated physically.
II. BSS
The BSS is the system equipment, which is controlled by the MSC and communicates with MSs in the specific radio coverage area. It is responsible for radio transmission and reception, and radio resource management. The BSS consists of the following two functional entities:
l
Base station controller (BSC)
The BSC is responsible for radio network resource management, cell configuration data management, power control, location and switchover. It implements powerful communication control function.
l
Base transceiver station (BTS)
The BTS is the radio interface equipment, which is controlled by the BSC. It handles the radio connection, conversion between radio signals and landline signals, radio diversity, radio channel encryption, frequency hopping, and so on.
III. OMC
The OMC is responsible for managing and controlling the whole GSM and CDMA networks.
IV. MS
The MS is the mobile subscriber's device. It consists of the following two parts:
l
Mobile terminal (MT) The MT implements such functions as voice coding, channel coding, information encryption, information modulation and demodulation, information transmission and reception.
Huawei Technologies Proprietary 1-8
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
Subscriber identity module/user identity module card (SIM/UIM card) The SIM/UIM card is an intelligent card, which keeps the subscriber identity information and the management data related to the subscriber and network. An MT with an SIM card inside can access the telecom network.
1.3.2 Position of the SMS System in the Network
The position of the SMS system in the network is as shown in the circle in Figure 1-1. The physical entities related to the SMS system are the MSC, VLR and the HLR. Their functions in the SM transmission are as follows:
l
MSC
Short messages submitted by the MS pass the BSS and reach the MSC. Then the MSC forwards them to the corresponding SMS system. After receiving the SMs delivered by the SMS system, the MSC queries the VLR and the HLR for the related routing and subscriber information, and then delivers them to subscribers through BSS.
l
VLR
The VLR stores the temporary information of a subscriber roaming in the local MSC area. The subscriber must pass the authentication through the VLR before sending an SM, and the MSC queries the route of a subscriber through the VLR before delivering an SM.
l
HLR The HLR is a database for mobile subscriber management. It stores the subscription information, position information, mobile station international ISDN number (MSISDN), and international mobile station identity (IMSI) of a subscriber. Before delivering SM, the SMS system finds which MSC the subscriber belongs to through the HLR.
1.4 External Interfaces
Figure 1-2 shows the external interfaces of the infoX-SMS system.
Huawei Technologies Proprietary 1-9
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
infoX-SMS GW
NMS SMPP interface NMS interface MT console
SMPP interface MMSC
MT interface
SMAP interface MDSP SMPP interface SMPP+ interface WAP GW infoXSMS Bill interface Bill interface SS7 interface Report system MS BOSS system SCP
SMS System: Short Message Service System SMPP: Short Message Peer-to-Peer protocol MMSC: Multimedia Messaging Service WAP GW: Wireless Application Protocol Gateway MS: Mobile Station BOSS: Business and Operation Support System SCP: Service Control Point SMAP: Service Management Access Protocol NMS: Network Management System
Figure 1-2 External interfaces of the infoX-SMS system Table 1-3 introduces the interfaces in details. Table 1-3 Interfaces with external entities Interface Description The NMS connects to and interacts with the infoX-SMS system through this interface to collect such network element information as alarm, performance and configuration, thus implementing such network management functions as topology management, performance management, fault management, and configuration management. In this way, the NMS is able to monitor, maintain and manage the infoX-SMS system. Protocol
NMS interface
MML
Huawei Technologies Proprietary 1-10
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
Interface MT interface
Description The MT console communicates with the SMS system with this interface, conducting monitoring, management, and maintenance on the SMS system. The infoX-SMS system supports the standard SMPP 3.3 and SMPP 3.4 protocols. Therefore, the infoX-SMS system can be interconnected with any service module supporting SMPP, thus expanding the service functions of the infoX-SMS system. For example:
Protocol MT protocol
SMPP interface
The SMS GW communicates with the infoX-SMS system through SMPP, providing various extended short message services for terminal users. The WAP GW communicates with the infoX-SMS system through SMPP, sending push messages to MS subscribers through the infoX-SMS system. The MMSC communicates with the infoX-SMS system, implementing the SM notification to subscribers in some MMSC service flows.
SMPP 3.3 Or SMPP 3.4
SMAP interface SMPP+ interface
The infoX-SMS system interacts with the MDSP through this interface to authenticate and computing fee for the subscribers of the SMS. The infoX-SMS system interacts with the SCP through this interface to authenticate and charge the subscribers of the SMS.
SMAP1.3
SMPP+2.0 FTP & Note: Besides, the BOSS system can also use the NETBIOS protocol in the Windows operating system, obtaining charging bills through network mapping hard disk.
Bill interface
The charging system obtains charging bills from the infoX-SMS system through this interface, and then conducts further processing. Through this interface, the report server obtains statistics bills from the infoX-SMS system, makes statistics on bill records and generates statistics report.
Huawei Technologies Proprietary 1-11
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 1 System Overview
Interface
Description It is the interface between the infoX-SMS system and MSs, which does not exist physically. The infoX-SMS system and MSs communicate through the mobile network. Therefore, the interface is the external interface of the signaling access gateway (TELLIN-USAU).
Protocol
SS7 interface
The TELLIN-USAU can access the narrowband SS7 and the IP-based broadband SS7, so it has two kinds of signaling interfaces: the TDM-based signaling interface and the IP-based signaling interface.
l
SS7
The TDM-based signaling interface adopts E1 physical interface, and it can access 64-Kbps and 2-Mbps signaling links. The IP-based signaling interface adopts the FE interface of the 10M/100M Ethernet.
Huawei Technologies Proprietary 1-12
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
Chapter 2 System Architecture
This chapter introduces the design concept and software architecture, as well as the hardware architecture of the infoX-SMS system. Reading this chapter helps you get an understanding of the working mechanism of the infoX-SMS system.
2.1 Design Concept of the SMS system
In logical functions, the SMS system can be divided into the NMS subsystem, service subsystem, access subsystem, scheduling subsystem, and charging subsystem. Figure 2-1 shows the logical structure.
Network management, MT functions, Report generation, Alarming
NMS subsystem
SS7 network
Service subsystem Scheduling subsystem
Access subsystem
Charging subsystem infoX-SMS
Service network
BOSS system
Figure 2-1 SMS system architecture The functions of each subsystem are as follows:
I. Access subsystem
The access subsystem accesses the SMS system to external systems, which include:
l l l
SS7 network through the signaling access gateway Service network through the SMPP 3.3 or SMPP 3.4 protocol Charging network through SMAP 1.3, SMPP 2.0, files and internal protocols
Huawei Technologies Proprietary 2-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
Physically, the access subsystem includes:
l
Signaling processing module composed of the access gateway (such as USAU), MTI Server, and MAP Server SMSC Interfaces adopting different protocols (such as SMPP interface)
II. Scheduling subsystem
The scheduling subsystem realizes the function of SM scheduling, which includes the SM storing, forwarding, backup, and routing management and so on. Physically, the scheduling subsystem is composed of the SMSC, L2CacheDaemon, historical database, DBDaemon, and so on.
III. Service subsystem
The service subsystem implements the service functions such as SM forwarding and enhanced status report provided by the SMS system. Physically, the service subsystem is composed of the SMSC, CCM, UserProxy, the ICCWebServer, and so on.
IV. Charging subsystem
The charging subsystem conducts charging related functions such as bill creation and pre-deduction of PPS subscribers. Physically, charging subsystem is composed of the BillCreater, PPS processing module of the SMSC, and UTIns.
V. NMS subsystem
The NMS subsystem implements such functions as network management, maintenance and test, statistics, report generation, and alarming. Physically, the NMS subsystem is composed of the MT console, MT Server, I2000, AlertServer, alarm console, reporting system, and so on.
& Note: For detailed description of the modules of the subsystem, refer to section 2.2 SMS System Architecture.
Huawei Technologies Proprietary 2-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
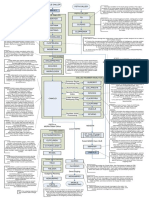
2.2 SMS System Architecture
The SMS system is designed with the modularized concept. This system can be divided into several parts according to different functional categories, which can be selected during the construction of the system depending on the actual needs so as to provide services of different levels. The system architecture is shown in Figure 2-2.
WWW Client SP MT terminal /NMC MT Server Alert Server infoX SMS GW service database UserProxy
ICCWebServer
SMCAPP Report BillCreater Information security module
Backup Daemon
GSM MAP Server
ClusterMng
MTI Server
DBDaemon
CDMA MAP Server
FileMirror TELLIN-USAU
L2Cache Daemon
ServerSelector To another node of dual system
No.7 Mobile network SMC database
MS
MT Server: Maintenance and Test Server MAP Server: Mobile Application Part Server MTI Server: Message Transfer Interface Server CCM: Customer Care Module ICC: Intellectual Control Center which is the infoX-SM Assistant system Alert Server: connected with various modules of the SMS system Huawei Technologies Proprietary 2-3
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
infoX: infoX-SMS GW
FCC: Flow Control Center
Figure 2-2 infoX-SMS system architecture
& Note: In Figure 2-2 the CCM 1 is connected with the SMCAPP to process called-related services. The CCM 2 is connected with the infoX-SMS GW to handle calling-related services. In addition, the CCM can be directly connected with the SMCPP to handle calling-related services. For detailed information, refer to section . In this figure, the modules in the dotted line box are the service modules of the SMS system; the modules out of the dotted line box are peripheral modules connecting with the SMS system.
Functions of the modules are detailed in the following sections.
2.2.1 Signaling Gateway
The TELLIN-USAU can be used as the SG of the SMS system. The TELLIN-USAU is located between the signaling network and the internal processing module of the SMS system. As the SG, the TELLIN-USAU implements the signaling interaction between the SMS system and the MSC and the HLR, and accomplishes signaling access and conversion necessary for the information interaction between the MS and the SMS system.
2.2.2 MTI Server
The MTI Server is the interface layer between the MAP layer and the TCAP layer in the signaling system number 7 (SS7). The main functions are as follows:
l
Processing the conversion between signaling at the TCAP layer and that at the MAP layer Processing basic dialogs processes, including dialog creation, release, and maintenance, at the MAP layer Distributing signaling at the MAP layer among the application modules, including the MAP Server, USSD Gateway and so on, of the MAP layer Connecting the application modules at the MAP layer, and distributing messages according to the AC_NAME and SSN of messages
As the server, the MTI Server connects the MAP Server, USSD Gateway, and the signaling access gateway. When receiving the MAP dialog request at the TCAP layer from the wireless network, the MTI Server sends the request to the corresponding MAP processing module. For
Huawei Technologies Proprietary 2-4
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
dialog requests initiated from the modules of the MAP layer, the MTI Server distributes them to the corresponding signaling access gateway according to a proportion.
2.2.3 GSM MAP Server
The GSM MAP Server is the GSM G/IW gateway of the SMS system. It processes the MAP signaling of the SMS system, converts the MAP signaling into the message of internal format, and then forwards it to SMSC. The GSM MAP Server connects with the MTI Server as the client, processing the MAP signaling. Meanwhile, the GSM MAP Server connects with the SMSC as the server, implementing the conversion between the MAP signaling and the message of internal format.
2.2.4 CDMA MAP Server
The CDMA MAP Server is a part of the SMS system. It converts the signaling between layers TCAP and CDMA MAP, and converts CDMA MAP signaling into messages of the internal format and forwards them to the SMSC. The CDMA MAP Server, as a client, connects with the CTI Server directly; or as the server, connects with the USAU directly; and as the superior level of the signaling access gateway, processes the CDMA MAP signaling. At the same time, the CDMA MAP Server, as the server, is connected with the SMSC, implementing the conversion between the CDMA MAP signaling and messages of the internal format.
2.2.5 SMSC
The SMSC is responsible for scheduling, storing and forwarding SMs in the SMS system. Its basic functions include submission, delivery, and scheduling of SMs, maintenance of SM subscriber data, subscriber authentication, system flow control, management of external interfaces, generation of SM historical records, generation of realtime SMS bills and provision of external standard interfaces (such as SMPP 3.3 and SMPP 3.4 interface). As the kernel module of the SMS system, the SMSC provides system interfaces for modules such as the CDMA MAP Server, GSM MAP Server. The interface between the SMSC and the GSM MAP Server complies with the protocol ETSI GSM 03.40 Version 4.8.1: European digital cellular telecommunications system (Phase 2); Technical realization of the Short Message Service (SMS) Point to Point (PP). The interface between the SMSC and the CDMA MAP Server complies with the protocol EIA/TIA IS637A protocol and the EIA/TIA IS637B. The interfaces between the SMSC and the service modules comply with the standard SMPP protocol.
Huawei Technologies Proprietary 2-5
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
The SMSC consists of five modules, SMCAPP, BillCreater, DBDaemon, BackupDaemon, and L2CacheDaemon. The SMCAPP and other modules access data of each other through memory sharing. Their functions are as follows:
I. SMCAPP
The SMCAPP module is responsible for receiving, scheduling and delivering SMs, managing all the SMEs connected to the SMS system and providing the interface for the maintenance and test of the SMSC operation.
II. BILLCreater
The BILLCreater module is responsible for generating realtime SMS bills which are used for the query and statistics by the charging system and report system.
III. DBDaemon
The DBDaemon module is responsible for backing up and restoring the memory data in the SMSC, such as the management on subscriber data, historical data and predefined SMs.
IV. BackupDaemon
The BackupDaemon module implements the backup and restoration of the memory data in the SMSC. The BackupDaemon backs up SMs in the memory of SMCAPP in real time. When the SMCAPP is restarted by ClusterMng after abnormal exist, it reads back SMs from the BackupDaemon, recovering SMs during the abnormity of the SMCAPP. In the dual system mode, the BackupDaemon module has the functions of backing up and restoring data of the active and standby hosts. The BackupDaemon of the standby host backs up SMs from that of the active host, ensuring the consistency of SM data in the memories of the active host and standby host. When switchover happens, the original standby host changes into the active host, while the SMCAPP of the original standby host turns into the Master status. Meanwhile, the SMCAPP of the current active host reads back messages from the BackupDaemon, ensuring the consistency of SM data in the memories of the two hosts. At the startup of an SMS system, it first loads pre-defined SMs and subscriber information into the memory of the SMSC through DBDaemon, and then recovers the SMs from the BackupDaemon.
V. L2CacheDaemon
During the peak hour, some of the SMs are saved into the L2CacheDaemon. Temporarily, these SMs are not scheduled in real time.
Huawei Technologies Proprietary 2-6
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
When the system load is lower, the SMCAPP, together with the L2CacheDaemon, reads back the SMs into the memory of the SMSC for rescheduling.
2.2.6 Dual System Management Module
The dual system management module provides dual system management functions for key system components, enhancing the system stability and security.
I. ClusterMng
ClusterMng is responsible for monitoring and maintaining specific application modules of the SMS system, such as SMCAPP.
l
Dual system management in the Linux operating system In the Linux operating system, the ClusterMng implements the dual system functions of the SMS system together with the VCS management software. The VCS manages and switches the floating IP address and VGs. Meanwhile, the VCS software on the active host is responsible for monitoring the running of each process of the Oracle database (DB2 database), and the ClusterMng. The ClusterMng is responsible for monitoring and maintaining the running of each application module of the SMS system. For example, the running of the scheduling process. If the VCS software on the active host finds that the network running is abnormal, the Oracle database (DB2 database) is abnormal, or the ClusterMng process is abnormal and fails to be restarted, the VCS performs a switchover automatically. If the ClusterMng finds that an exception occurs on a module, it tries to restart the module for several times. When the exception cannot be removed, the ClusterMng decides whether to perform a switchover according to the configuration.
Dual system management in the Windows system Under the Windows operating system, ClusterMng and Serverselector accomplishes dual system functions of the SMS system. ClusterMng takes the server where the floating IP is as the active server, and it is responsible for monitoring and maintaining the running status of specific application modules of SMs, such as the running status of the SMCAPP module. The ClusterMng tries to start a module for many times if it finds that the module works abnormally. If the abnormity persists, it determines whether to conduct dual system switchover according to the configuration.
Huawei Technologies Proprietary 2-7
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
II. FileMirror
According to the configuration, the FileMirror conducts the synchronization of the configuration files of the dual system, ensuring the consistency of data at the active and standby hosts. In this case, the data on the two hosts are consistent after the switchover. Such configuration files as account files, route files, the configuration file of the MAP Server, the configuration file of the MTI Server need synchronization. The FileMirror can detect the change of configuration files on the active host, and synchronize the file after change into the standby host, ensuring the data consistency on the two nodes of the dual system. In this case, when switchover occurs, the standby host is switched over to the active host, and the data configuration on it is consistent with that of the original active host before the switchover. Currently, the FileMirror supports only synchronization of a single file or that of files in the same directory.
Huawei Technologies Proprietary 2-8
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
2.2.7 MT Module
The MT modules of the SMS system include the Maintenance and Test Server (MT Server) and the Maintenance and Test Console (MT console), as shown in Figure 2-3. Through them, you can perform the maintenance, management, and test operations on the SMS system.
MT Console
MT Server
SMSC
MAP Server
MTI Server
MAP Server SMSC MT Server MTI Server MT Console
Mobile Application Part Server Short Message Scheduling Center Maintenance and Test Server Message Transfer Interface Server Maintenance and Test Console
Figure 2-3 Networking of the MT modules The maintenance and test (MT) system consists of the MT console and MT Server.
I. MT Server
The MT Server is an intermediate service layer for the interaction of the MT console and the maintained modules. It has such functions as authentication, MT user management, message distribution, and status monitoring. The MT Server has the following features:
l l l
Running in the dual system mode with high stability and reliability Supporting NM alarms. Supporting report of alarms to the Alert Server through TCP/IP
The functions of the MT Server are as follows:
l l l
Implementing the authentication for maintenance and test. Ensuring the connection with the service module. Providing the message transmission between the service module and the MT console. Providing the operations on the accounts of MT users.
Huawei Technologies Proprietary 2-9
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
l l
Notifying the MT console of the connection status with the service module. Notifying the service module of the abnormality in connection with the MT console. Providing the interface with the iManager I2000 network management system (NMS). Authenticating the IP addresses of the devices (such as the network management system, MT console, SMCAPP) that request for connection to the MT Server.
Monitoring and recording the MT operations implemented by MT subscribers for later query.
II. MT Console
The MT console is an indispensable part of the SMS system. As the maintenance management terminal of the SMS system, it is responsible for the operation, maintenance and management of the system. It is also the interface between the whole system and subscribers, providing friendly graphical user interface (GUI) and easy operations. Subscribers can query the status, configure data, and performs monitoring and tracing respectively on the SMSC, GSM MAP Server, CDMA MAP Server, and MTI Server through the MT console.
2.2.8 Alert Server
As the local alert server of the SMS system, the Alert Server communicates with the alarm source modules (such as SMCAPP) through the Inner Message of TCP/IP. It receives alarms from alarm source modules and prompts alarms through the sound box and audio/visual alarm console of the alarm subsystem. The Alert Server receives alarms from each module of the SMS system. Then it reports the alarms to the NMS through the MT Server. On the Web operation platform of the Alert Server, you can query the historical alarms, clear alarms, filter alarms, set validity period, and so on.
2.2.9 Information Security Monitoring System
The information security monitoring system obtains bills from the SMS system, implements the analysis and statistics of the bill files, notifies relevant personnel of questionable subscribers and SPs, gives alarms and records them into the database. Operators can, according to those data, restrict questionable subscribers (or SPs) to normalize the SM-related behaviors of SM subscribers (or SPs). For details of the information security monitoring system, refer to corresponding Online Help.
Huawei Technologies Proprietary 2-10
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
& Note: Information security monitor differs from information security authentication. Information security authentication means filtering SMs submitted to the SMS system in real time for security regards and rejecting the SMs which do not meet requirements. Information security monitor means monitoring and normalizing the SM-related actions of subscribers or SPs through after-the-fact statistics.
2.2.10 Report Processing System
The SMS report system, through the statistics of the SM bills, outputs accurate and visual statistics reports for subscribers, thus facilitating operators in the management of the SMS system. The SMS report system consists of the pre-statistics system and the report system.
l
The pre-statistics system is responsible for the resolution and statistics of original bill records according to the user-defined rules. Then it generates the statistics table, and writes the statistics table into the report database for the report system and the network management.
The report system is responsible for generating, displaying and outputting SMS reports. It takes the statistics table generated by the pre-statistics system from the report database, and generates service reports using the user-defined templates.
For specific contents of SMS reports, refer to Report System User Manual and Prestatistics System User Manual
2.2.11 Network Management System
The HUAWEI iManager I2000 Intelligent network management system interacts with the MT Server of the SMS system through MML, implementing the network monitor of the SMS system. The iManager I2000 provides the following functions:
l
Topology management: The system reflects in topological views the configurations of SM equipments, the network architecture of the SMS system, and the topological connection between the SM equipments in the local network and that in other networks.
Configuration management: The system searches and selects configuration information related to the SM equipments within the local network, functional entities staying on the equipments and the online SMS services. When configuration information is changed, the network management system will obtain information about configuration changes and mark them. In addition, the system manages the automatic update of the information.
Huawei Technologies Proprietary 2-11
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
Fault (Alarm) management: In the network management system, the fault daemon receives in real time alarms of the SM equipments, such as the SMSC, MAP Server, MTI Server and MT server. The alarm foreground displays in real time the alarms.
Performance management: The SMSC performance management part provides such performance analyses as CPU occupation statistics, memory occupation statistics, hard-disk operation statistics, mobile termination (MT) failure statistics, mobile origination (MO) failure statistics, flow statistics, Service Report Table A statistics, Service Report Table B statistics and Service Report Table B statistics.
Security management: The system controls the network management user authority.
For specific contents of the network management, refer to iManager I2000 Intelligent Network Management System User Manual.
Huawei Technologies Proprietary 2-12
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
2.3 Hardware Structure
Different hardware structures are adopted by the SMS system according to the different SM service flows.
I. A Single SMS system installed together with the database
When the SM service flow and number of subscribers are small, a single dual system serves as the hardware platform for the kernel programs and database of the SMS system, as shown in Figure 2-4.
APP Oracle
APP Oracle
SMC Node1
Disk array
SMC Node2
Figure 2-4 SMS system installed together with the database In this mode, all programs and database of the SMS system run on the two nodes of the dual system. Subscriber data, historical SMs are stored on the shared disk array. The active node of the dual system provides services externally. When error occurs on the active node, ClusterMng notifies all programs of switchover. The original standby node provides services externally, ensuring the normal running of services.
II. A single SMS system installed separately with the database
When the SM service flow and number of subscribers are large, two dual systems are adopted. One serves as the hardware platform for the kernel programs, and the other as the hardware platform for database, as shown in Figure 2-5.
APP
APP
SMC Node1
Disk array
SMC Node2
Oracle
Oracle
Disk array Database Server1 Database Server2
Figure 2-5 SMS system installed separately with the database
Huawei Technologies Proprietary 2-13
PDF "pdfFactory Pro" d www.fineprint.cn
infoX-SMS System Description
Chapter 2 System Architecture
In this mode, all programs of the SMS system run on the two nodes of the dual system. Bill data are stored in the shared array of the dual system. Database runs on the two nodes of the dual system. Subscriber data, historical SMs are saved in the shared disk array of the dual system. The active host provides services externally. When error occurs on the active node, ClusterMng notifies all programs of switchover. The original standby node provides services externally, ensuring the normal running of services.
III. Multiple SMSCs with Multiple MAP Servers
When the SM service flow is large, the network of multiple MAP Servers is adopted.
STP1
STP2
USAU1
USAU2
MTI Server1
MTI Server2
MTI Server3
MTI Server4
MAP Server1
MAP Server2
MAP Server3
MAP Server4
SMSC2 SMSC1
SMSC3 SMSC4
Figure 2-6 Multiple MAP Servers In the mode of multiple MAP Servers, the MAP Server and MTI Server of each SMSC can be installed together with the SMSC or can be installed independently. The MAP Servers and MTI Servers of the multiple sets of SMS systems form a crossover network with the SMSC.
Huawei Technologies Proprietary 2-14
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Chapter 3 System Functions and Implementation
This chapter introduces the scheduling processing functions of the SMSC, as well as the basic service functions, system management functions, and system maintenance functions of the infoX-SMS system. Reading this chapter enables you to get an understanding of the functions and features of the infoX-SMS system.
3.1 Basic Service Supporting Functions
The basic service supporting functions support the basic services of the infoX-SMS system. This chapter covers the basic service supporting functions.
3.1.1 SM Submission
The infoX-SMS system supports the submission of SMs by mobile subscribers and ESMEs.
l
After an SM is submitted to the SMS system and is confirmed as valid, it is inserted into the short message queue and an acknowledgment message is sent back to the originator.
If the SM is invalid or cannot be processed by the SMS system temporarily, the SMS system sends to the originator a message indicating submission failure.
3.1.2 SM Delivery
The infoX-SMS system delivers SMs submitted to it. The SMS system automatically adjusts the delivery frequency according to the number of SMs waiting to be delivered, regularly takes out the SM that must be delivered, and ensures that only one SM is sent to one MS at one time.
l
If the SM is successfully delivered, it is moved to the historical information database for query and bill statistics. If the SM fails to be delivered, the SMSC adopts specific scheduling strategy and performs subsequent scheduling on the SM according to the error code returned and the current scheduling mode of the SMSC.
If the SM has not been delivered successfully yet after its life cycle ends, it is moved to the historical information database with the failure cause recorded.
3.1.3 Status Report
The subscriber can obtain the status of an SM he or she sends through the report returned by the system.
Huawei Technologies Proprietary 3-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
The infoX-SMS system generates status report according to the configuration (whether status report is needed), and notifies the subscriber of the submission result of the SM. The message status includes the following:
l l
Forwarding notification (forwarding success) Forwarding failure notification (permanent failure)
In addition, the MS can select the requirement for the enhanced status report. The SMS System returns an SM indicating the SM transfer status to the MS. The system needs the ICC to manage and support the service of the enhanced status report.
3.1.4 Information Security Authentication
The information security authentication means filtering the SMs submitted to the SMS system in real time for information security and refusing those SMs not satisfying the requirements. 1) 2) After receiving an SM, the infoX-SMS system forwards it to the information security module. The information security module authenticates the SM, for example, it checks whether the SM contains sensitive words or whether it is a junk SM, and then returns the authentication result to the infoX-SMS system. 3) The infoX-SMS system processes the SM if it passes the authentication. Otherwise, it rejects the SM.
3.1.5 Authentication and Charging
The SMS system supports the authentication of PPS service subscribers and Mobile Virtual Private Network (MVPN) service subscribers.
l
When a PPS subscriber sends or receives an SM, the infoX-SMS system sends the information of the PPS subscriber to the IN SCP for authentication and charging according to the PPS routing information. The infoX-SMS system supports roaming charging of PPS subscribers. When the SMS system performs PPS authentication and fee deduction on a PPS subscriber who sends or receives an SM, it sends the authentication message with the MOMSC address to the SCP. The SCP determines the charging rate of an SM according to the MOMSC address (the SCP checks whether the MOMSC address indicates a local MSC), and charges roaming PPS subscribers and non-roaming PPS subscribers differently. The PPS roaming charging supports charging rollback.
MVPN is a special mobile virtual private network, and allows VPN subscribers to send and receive SMs using short numbers. When processing this type of SMs, the SMS system needs to convert the short number to the actual MSISDN,
Huawei Technologies Proprietary 3-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
therefore, it needs to obtain the actual MSISDN corresponding to the short number from the IN network. The authentication mode and route for the number segments of the local PPS service and local MVPN service should be flexibly set according to the actual requirements.
3.1.6 Multiple Coding Schemes
The infoX-SMS system supports multiple coding schemes, thus supporting multiple languages.
I. GSM coding schemes that the system supports
l l l
7-bit compressed coding 8-bit coding Unicode coding (16bit)
II. CDMA coding schemes that the system supports
The system supports the following five coding schemes of the CDMA network: 00000, 00010, 00011, 00100, and 01001. Table 3-1 shows the coding schemes that the CDMA network defines. Table 3-1 Coding schemes that the CDMA network defines CHARi Encoding Type Octet,unspecified Extended Protocol Message [21] 7-bit ASCII [25] IA5 (Table 11 OF [31]) UNICODE [29] Shift-JIS [30] Korean [33]
iii ii i
MSG_ENCODING Field 00000 00001 00010 00011 00100 00101 00110 00111 01000 01001 8
Length of CHARi (bits)
(see iv) 7 7 16 8 or 16 8 or 16 8 8 7
Latain/Hebrew [28] Latain [27] GSM 7-bit default alphabet [37] All other values are reserved
Huawei Technologies Proprietary 3-3
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
III. TDMA coding schemes that the system supports
The system supports the following three coding schemes of the TDMA network: 00001, 00010, and 00100. Table 3-2 shows the coding schemes that the TDMA network defines. Table 3-2 Coding schemes that the TDMA network defines Value 00001 00010 00011 00100 00101 IRA User spccific Latain 1, as specified in ISO-8859-1 BMP, as specified in ISO-10646 Hebrew, as specified in ISO-8859-8 Function
All other values are reserved
3.1.7 Number Conversion According to the Fields of TON, NPI, ADDRESS and PID
The system supports three number conversion points: number conversion before NP authentication, number conversion before PPS authentication and number conversion before delivery. At each number conversion point, the number conversion strategies are configurable, thus meeting the requirements of related service flows. At each number conversion point, the system converts the calling and called numbers according to their attributes, including the PID before number conversion, TON before number conversion, NPI before number conversion, referential number and number conversion strategies. The converted number is used for routing.
3.1.8 Authenticating Subscribers
For MO service, the SMSC conducts calling and called number authentications. There are two types of authentication: subscriber authentication and number segment authentication.
l
Subscriber authentication According to all the SMs submitted from an interface, the system checks whether the calling party or the called party is a registered subscriber of the SMSC. If not, the SM is rejected.
Number segment authentication According to all the SMs submitted from an interface, the system checks whether the calling party or the called party meets the authentication requirements of the number segment defined in the account attributes or SMC address.
Huawei Technologies Proprietary 3-4
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
For details of number authentication, refer to section 3.1.13 Universal Flow of Authentication and Number Conversion. The following shows the authentication flow of the SMs submitted by the CDMA/TDMA subscribers (Number segments of the CDMA/TDMA subscribers are configurable):
l
Calling number authentication: If the calling number is registered in the local SMS system, it passes the authentication. The system processes the SM as the one submitted by the local subscriber. If the calling number is not registered, the system authenticates the SM according to the authentication data corresponding to the gateway accounts for the CDMA or TDMA network or that corresponding to the virtual SMC address for the CDMA/TDMA networks. If it passes the authentication, the system processes the SM as the one submitted by the local subscriber. Otherwise, the system regards that the SM is forwarded from another SMS system. If it is configured in the SMS system that calling number authentication is conducted on the forwarded SM, the system checks the calling number of the SM in the home SMS system list. If the number is found in the list, it is an authorized forwarded SM. Otherwise, the SM is rejected.
Called number authentication: The system first checks the called number in the home SMS system list. If the called number is found in the list, it indicates that the called party belongs to another SMS system. The SM is then forwarded according to the forwarding mode configured in the table. If the called number is not found in the list, it is authenticated in the local SMS system. If the called number is registered in the local SMS system, it passes the authentication, and the system processes the SM as the one delivered to the local subscriber. If the called number is not registered in the local SMS system and it is a subscriber in the CDMA/TDMA networks, the system checks whether the called number is a local number by referring to the calling authentication number segment corresponding to the CDMA/TDMA gateway accounts or virtual SMC address. If yes, the SM is delivered directly. If no, the SM is forwarded. If the called number is the GSM subscriber, called number authentication is conducted according to the authentication data corresponding to gateway accounts for the CDMA/TDMA networks or that corresponding to virtual SMC address. If the called number does not pass the authentication, the SM is rejected.
3.1.9 Delivery of Long SMs
The following lists the lengths of ordinary SMs when different coding schemes are adopted:
Huawei Technologies Proprietary 3-5
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
l l l
Unicode coding: 70 characters 8-bit coding: 140 characters 7-bit coding: 160 characters
The SMs with the length larger than the maximum length are defined as long SMs. When the MS and the SMS G/IW MSC support Phase 2, the SMS system supports the delivery of the long SMs which can be 35,700 bytes long at most (the SM length after coding includes the additional information). After receiving long SMs, the infoX-SMS system segments them to several packets and sends them to subscribers.
& Note: To enable the GSM network to forward long SMs, the MS and the radio network must support the PHASE2 protocol.
3.1.10 Delivery of SMs to Multiple Destinations
The SMS system supports the sending of an SM to multiple destinations. 1) 2) The ESME submits a Submit_multi message to the infoX-SMS system through the SMPP 3.4 interface. After receiving the Submit_multi message, the infoX-SMS system creates SMs according to the attributes of the Submit_multi message (SM content, number of destination addresses, and destination address list). The system creates one SM for each destination address. 3) The infoX-SMS system delivers the SMs according to the system scheduling strategies.
3.1.11 Delivery of Multiple SMs to a Destination
When the network supports Phase 2, the SMS system can deliver multiple SMs to a subscriber simultaneously (in this case, the GMSC obtains the routing information from the HLR only once, and the session with the MSC is maintained during the delivery). In this way, the load of the SS7 network can be greatly alleviated.
& Note: To enable the GSM network to forward multiple SMs, the MS and the radio network must support PHASE2.
Huawei Technologies Proprietary 3-6
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
When the infoX-SMS system delivers multiple SMs to one subscriber, the GMSC obtains routing information from the HLR only once, and the SMS system keeps interacting with the MSC until the SMs are successfully sent or a fault occurs.
3.1.12 Virtual SMC Authentication
When an MS submits an SM to the SMS system, the SMS system judges whether the SMS system address of the SM is the virtual address of the SMS system and decides whether the subscriber can use the SM services provided by the SMS system. If a subscriber who is not in the service range of the SMS system submits an SM to the SMS system, the SMS system rejects the SM.
3.1.13 Universal Flow of Authentication and Number Conversion
The SMS system supports the universal flow of authentication and number conversion. That is, subscribers can set suitable rules, authentication and number conversion data, and customize proper policies of authentication and number conversion as required.
I. Number conversion flow
The SMS system has three number conversion points: Before NP, Before SCP and Before Deliver. These four points are distributed in the following MO flow and MT flow:
l l l l
Before NP: converts the number before querying the attribute of NP. Before SCP: converts the number before querying the attribute of the subscriber. Before Deliver: converts the number by the end of MT process. Change Deliver: converts the number when SM is delivering.
Number conversion in the change deliver point is effective to ordinary SMs and status reports. At each point, the rule of number conversion can be configured as Not Convert Number, Number Head Conversion and Number Tail Conversion. The number conversion strategies are configurable, thus meeting the requirements of related service flows. The number conversion at each point includes the number conversion according to accounts and SMC addresses. The number conversion according to accounts precedes the number conversion according to SMC addresses. The relationship between the two types can be configured.
l
Number conversion according to accounts: converting numbers according to the account name; numbers to be converted; the attribute of the calling or called number; PID value, TON value and NPI value of the number before conversion; and number conversion policies. The converted number is used for routing.
Number conversion according to SMC addresses: converting numbers according to the SMC address; numbers to be converted; the attribute of the
Huawei Technologies Proprietary 3-7
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
calling or called number; PID value, TON value and NPI value of the number before number conversion; and number conversion policies. The converted number is used for routing.
II. Authentication flow
The SMS system authenticates the calling or called SMs after all number conversions are finished. It checks whether the calling or called parties are valid subscribers and decides whether to provide SM services for them. The SMS system supports blacklist authentication and whitelist authentication.
l
Blacklist authentication: If a number is not in the configured authentication data, it passes the authentication. If the number is in the configured authentication data, it is authenticated according to the found authentication data.
Whitelist authentication: If a number is not in the configured authentication data, it fails the authentication. If the number is in the configured authentication data, it is authenticated according to the found authentication data.
3.1.14 Virtual SMC
The SMS system supports virtual SMC. One SMS system can provide SMS for 16 local mobile networks. The SMS system can configure multiple SMC numbers. Each SMC number is corresponding to a local mobile network. The physical SMS system entity occupies multiple logical SMC numbers, and the specific numbers are subject to the actual situation of the local network.
& Note: Currently, only the GSM part of the SMS system supports the virtual SMC function.
3.1.15 Muitiple MAP Servers Function
The SMS system supports multiple MAPs networking by connecting multiple SMSCs through MAP Servers, thus realizes the even distribution of SMs and increases the reliability and disaster-tolerance capability of the system. MO submits SMs to the MAP Server. And then, the MAP Server distributes SMs to different SMSCs according to ending digits of called number, calling number segment and percentage. If links between MAP Servers and SMSCs are abnormal, or the SMSCs are overloaded, the MAP Server can send SMs to FCC (Provided that links is set up with FCC) or other SMSCs. This mechanism ensures that the system is not affected by abnormal MAP Server or SMSC.
Huawei Technologies Proprietary 3-8
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
The multiple MAP networking is a typical mode using FCC for load distribution. In this networking mode, if connection between the MAP Server and the SMSC is fine, and the SMSC is overloaded, the distribution function of MAP Server is enabled. The FCC can distribute SMs evenly according to the current SM processing capability of the MAP Server and the SMSC. The FCC can also adjust the License of SMSC dynamically, thus realize the SMs traffic distribution between multiple SMS systems in the network SM mode.
3.1.16 Multiple Schedule Modes
The system supports the following three schedule modes required in standards:
l l l
Store and forward mode Datagram mode Transaction mode
For detailed description of the schedule modes, refer to section 1.2.2 System Features.
3.1.17 Message Exchange Between the CDMA Network and TDMA Network
The system supports the function that the home SMS system of the called party delivers SMs to the destination MS. If the calling party and called party of the SM do not belong to the same SMS system, the home SMS system of the calling party forwards the SM to the home SMS system of the called party. In the CDMA network, the home SMS system of the called party, after sending the SM to the destination MS, sends a status confirmation message to the home SMS system of the calling party, notifying the delivery result, thus ensuring the charging accuracy.
& Note: The status confirmation flow complies with the CDMA network only. If the SMS systems of other manufacturers do not support the preceding specifications, the SMS system of the calling number forwards the SM to the home SMS system of the called number. There is no status acknowledgement flow.
3.1.18 UserAck Messages
The originating CDMA/TDMA MS may apply for the UserAck message when sending an SM. Then a piece of UserAck message is returned to the SMS system of the originating MS when the target MS reads the SM. The SMS system then forwards the SM to the calling party.
Huawei Technologies Proprietary 3-9
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
& Note: This function applies to the CDMA/TDMA network only. According to the protocol, the function is developed in the SMS system of this version. This function needs the support of the MS. Currently, there is no application in the network.
3.1.19 Distinguishing Subscriber Network Attributes According to Different Number Segments
The SMS system supports number heads for the GSM, CDMA, and TDMA networks. If the subscriber belongs to the non-target network (Subscriber attributes can be distinguished by number segment), the SMS system distinguishes the subscriber network type according to the configured number head of the subscriber, and adopts corresponding scheduling strategy and coding scheme for the successful delivery of the SM. For detailed scheduling strategy, refer to section 3.2.8 Multidimensional Intelligent Scheduling.
3.1.20 PUSH Messages of the WAP Service
The SMS system supports PUSH messages of the WAP service. The MS has a very strict limit for the content of WAP PUSH messages. The value of SMS_TELESERVICEID (a parameter of the MAP layer in the CDMA network, which is used to identify special SM services) varies with different WAP services. The SP identifies the service type of the PUSH message through the ServiceType parameter in the SMPP message. The SMS system can flexibly convert ServiceType into SMS_TELESERVICEID needed by the MS, and code the SM content. Then the MS can receive the SM. The push flow of the WAP service is thus implemented.
& Note: This service is only supported in the CDMA network.
3.1.21 PUSH Messages in the MMS Service
The SMS system supports PUSH messages in the MMS service. The PUSH messages in the MMS service of the CDMA network conforms to the WDP259 protocol. The SMS system adds a special message head before the SM content and then delivers it to the MS. The value of SMS_TELESERVICEID is specially set for the PUSH messages in the MMS service. The SMS system converts ServiceType at the
Huawei Technologies Proprietary 3-10
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
SMPP interface into SMS_TELESERVICEID needed by the MS, and codes the SM content. Then the MS can receive the SM. The push flow of the MMS service is thus implemented.
& Note: This function is only supported in the CDMA network. In the GSM network, the PUSH messages in the MMS service are transferred transparently by the SMS system.
3.1.22 PRL Function
The SMS system supports the preferred roaming list (PRL) service. The PRL service provides the refreshment service of operators for roaming CDMA MSs. A PRL delivery tool is used together with the SMS system. The delivery tool loads PRL information list from files and then sends the messages to the CDMA MSs as the flow specified by ANSI IS683.
& Note: This function is applied in the CDMA network only and is applied in the current network.
3.1.23 IRDB
The SMS system supports the IRDB service. The IRDB service provides the refreshment service of operator list for roaming TDMA MSs. An IRDB delivery tool is installed together with the SMS system. The delivery tool loads IRDB information list from files and then sends the messages to the TDMA MSs as the flow specified by EIA/TIA 136-730.
& Note: This function is applied in the TDMA network only and is applied in the current network.
3.1.24 Supporting UCP 4.0
Connecting with the UCPGateWay, the SMS system processes ESME messages which support the UCP protocol in the X.25 network or TCP network. The SMPP 3.4
Huawei Technologies Proprietary 3-11
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
protocol is adopted between the UPT and SMSC, and the UCP 4.0 protocol is adopted between the UCPGateWay and ESME. The protocol contains the following commands:
l l l l l l l l l
Session management: sending connection request SMs Multiple address call input: sending SMs in batches Submit Short Message: submitting SMs Delivery Short Message: sending SMs Delivery notification: status notification SMs Modify Short Message: replacing SMs Inquiry message: querying SMs Delete message: deleting SMs MT alert: status notification SMs
3.1.25 SMs Without Calling Number
Some devices do not carry a calling number when submitting the submit_sm message through the SMPP interface. The SMS system can process the SM by adding a called number according to the configuration.
3.1.26 Time Zone Features
The SMS system can process information of different time zones.
l
The SMS system can deliver SMs with time zone information, which guarantees that the time information in the SMs received by roaming subscribers is correct. The SMS system can process MO SMs with time zone information.
3.1.27 Supporting SMPP 3.3
The SMS system is compatible with the SMPP 3.3 interface protocol. Table 3-3 shows commands of the SMPP 3.3 protocol supported by the SMS system. Table 3-3 SMPP 3.3 protocol supported by the SMS system Command BIND_RECEIVER_SM SUBMIT_SM DELIVER_SM QUERY_SM CANCEL_SM REPLACE_SM REPLACE_SM_EX QUERY_SMS Description Applies to connect with the SMS system Submits SMs Sends SMs Queries SMs Deletes SMs Replaces SMs Replaces SM extensions Queries SMs
Huawei Technologies Proprietary 3-12
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Command QUERY_SM_DETAILS ADD_SUB DEL_SUB MOD_SUB ENQUIRE_SUB ENQUIRE_LINK
Description Queries the details of special SMs Adds users Deletes users Modifies users Queries subscriber Information Handshake messages
3.1.28 Supporting SMPP 3.4
The SMS system is not completely compatible with SMPP 3.4 interface protocol. For the functions provided by the system, refer to the SMPP v3.4 Protocol
Implementation Conformance Statement (PICS) Proforma.
3.2 Core Scheduling Functions
The SMSC is the core processing module of the infoX-SMS system. This section introduces the basic functions of the SMSC and its scheduling mechanism. The SM scheduling mechanism that the SMSC adopts includes basic scheduling processing, SM priority processing, validity period processing, repeated SM redelivery processing, scheduling mode processing, entity-based scheduling processing, multidimensional intelligent scheduling processing, L2Cache processing and threshold processing.
3.2.1 Basic Functions
The SMSC is responsible for scheduling, storing and forwarding SMs in the SMS system. Its basic functions include the submission, delivery, and scheduling of SMs, maintenance of SM subscriber data, subscriber authentication, system flow control, generation of SM historical records, management of external interfaces, provision of external standard interfaces, such as the SMPP interface. Short message flow is as shown in Table 3-4. Table 3-4 Short message flow SM type SM flow The MS submits an SM to the SMSC through the MAP Server. The SMSC schedules the SM according to the scheduling strategy and delivers it through the MAP Server at an appropriate time. If the SM fails to be delivered before its life cycle is reached, it will be moved to the SM historical database.
MS-to-MS SM
Huawei Technologies Proprietary 3-13
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
SM type
SM flow The ESME sends an SM to the SMS system through the SMPP interface. The SMSC schedules the SM according to the scheduling strategy and delivers it through the MAP Server at an appropriate time. If the SM fails to be delivered before its life cycle is reached, it will be moved to the SM historical database. Through the MAP Server, the MS submits the SM to the SMSC, which schedules the SM according to the scheduling strategy and then delivers it to ESME through the SMPP protocols. The SM will be interpreted by the ESME. This method is adopted when the MS sends the information service request to the SM information platform.
ESME-to-MS SM
MS-to-ESME SM
3.2.2 Basic Scheduling Processing
I. Feature description
The scheduling strategy of the SMSC involves the submission, storage and forwarding of SMs, priority and life cycle of SMs, redelivery of SMs, status report, subscriber authentication, predefinition of SMs, and so on.
II. Implementation principles
The basic process is as shown in Table 3-5. Table 3-5 Basic Scheduling Processing Serial No. Processes When an SM is submitted to the SMSC, the SMSC inserts it in the short message queue if confirming that the message is valid, and returns confirmation information to the originator. If the message is illegal or the SMSC cannot process it, the SMSC will return submission failure and failure cause to the originator. According to the load of the system, the priority, the planned delivery time and the delivery failure delay strategy of messages, the SMSC sorts out the messages to be transmitted, and ensures delivering only one SM to one MS at one moment. After an SM is successfully delivered, it is moved to the historical information database for query and bill statistics. If the SM fails to be delivered, the SMSC adopts specific scheduling strategy and performs subsequent scheduling on the SM according to the retuned error code and the current scheduling mode of the SMSC. If the SM fails to be delivered continuously, the SMSC moves it to the historical information database after the life cycle of the SM ends.
Huawei Technologies Proprietary 3-14
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.2.3 SM Priority Processing
I. Feature description
The SMS system supports the setting of the SM priority, including high priority and ordinary priority.
l
For an SM of high priority, the SMSC delivers it forcibly (that is, the SMSC attempts to deliver it once even if the MS is temporarily absent or has no more storage capacity).
When delivering to the recipient, the SMSC delivers SMs of high priority first. For an SM of ordinary priority, the SMSC first decides if the MS is reachable and if it has enough storage capacity. If not, the SMSC does not deliver the SM to the recipient any longer until it receives the Alert_SC message from the network or its redelivery mechanism is started.
In the multidimensional scheduling, the SMSC subdivides the priority of SMs into five levels: Common, Important 2, Important 2, VIP 2 and VIP 1. The operation for each level of the SM varies.
II. Implementation principles
In the multidimensional scheduling, the priority of the SM is decided together by the priority of the number (segm0ent) and the priority strategy table. When an SM is submitted, the SMSC determines the priorities of the calling number and called number and then determines the priority of the SM according to the calling number (segment) priority and called number (segment) priority and thus delivers the SM to a message queue of the called entity. Table 3-6 introduces how the priority of a number and that of an SM are determined. Table 3-6 Determining the priority of an SM Serial No. Processes Determining the priority of a number: To determine the priority of a number, the system first judges whether the subscriber corresponding to this number is a registered subscriber. If yes, the priority of the number is the priority of the registered subscriber. Otherwise, the priority of the number is the priority of its corresponding number segment. If the subscriber corresponding to this number is not a registered subscriber and this number is not in the number segment priority table, the system regards it as common subscriber by default and the priority of the number is the priority of the common subscriber.
Huawei Technologies Proprietary 3-15
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Serial No.
Processes Determining the priority of an SM
l
Priority of ordinary SMs The system determines the priorities of the calling number and called number according to the above-mentioned method, obtains the priority of the SM according to the priority strategy table, and delivers the SM to the priority queue corresponding to the called for scheduling. For the following two types of SMs: l The SM with high priority which is submitted to the SMSC by service subscriber. l The pointed-to-point SM submitted to the SMSC by MS subscriber when the SMSC starts the quick deliver function. l The SMSC obtains the priority of the SM according to the preceding method, and then delivers the SM to the queue of one-level higher in priority for scheduling. If the priority of the SM is already the highest priority (VIP1), its current priority does not need to be upgraded. & Note: If the priority strategy table does not exist or the corresponding SM priority of the calling number and called number priorities is not configured in the priority strategy table, the higher one of the priorities of the calling number and called number is used as the priority of an SM. l Priority of status report When the called party of an SM is an ordered entity, the priority of the status report is normal. When the called party of an SM is a free entity, the priority level of status report is the same as that of the SM. l Priority of SMs that are datagram message mode and transaction message mode For SMs in the datagram message mode and transaction message mode, the priority is VIP1. Their scheduling strategy is the first priority even when other SMs with VIP1 priority are in the SM queue.
Huawei Technologies Proprietary 3-16
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
& Note:
l
You can query the SM priority in historical bills, charging bills, MO bills, historical database and memory of the SMS system. The SM priority is the combination of original priority and scheduling priority of the SM. The original priority, which is set value in bit4, takes the first four bits. The scheduling priority, which is set value of in bit0, bit1 and bit2, takes the next four bits. The value of the SM priority in the query result may be from 0 to 4 and from 16 to 20. The 0 to 4 corresponds to original priority 0, and corresponds to schedule priority that is from 0 to 4. The 16 to 20 corresponds to original priority 1, and corresponds to schedule priority that is from 0 to 4.
The SM priority in MT bills is of two values. The value 0 indicates normal priority, and 1 indicates high priority.
3.2.4 Validity Period Processing
I. Feature description
When an SM is sent, the originator should set the validity period for the redelivery. If it is not set, the SMSC may set an appropriate default value. When the validity period expires, the SMSC will move this SM to the historical information database, stating that the cause for the completion is timeout, and selectively generate a status report as required by the originator.
II. Implementation principles
1) After an SM is delivered to the SMS system, the SMS system confirms the validity period of the SM according to the processing flow shown in Figure 3-1. Refer to Table 3-7 for detail description.
Huawei Technologies Proprietary 3-17
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Start
(1)Status report?
Yes
Default validity period
No (2)SM service type specifies validity period? No (3)Service schedule strategy table specifies validity period? No Yes Get validity period Yes Get validity period Yes Get validity period Change to the maximum validity period Yes
(7)Longer than the maximum validity period? No Validity period is not changed
(4)SM specifies validity period?
No (5)Service attribute table specifies validity period? No Get validity period Yes Get validity period
(6)Calling party is registered?
Yes
No Default validity period
Figure 3-1 Judging validity period flow Table 3-7 Description of judging validity period Serial No. 1 2 Description The validity period of the status report is the default value of the system. If the SM is not a status report, the SMS system judges whether the validity period of the SM service type is configured. If yes, the SMS system adopts the validity period. If not, it proceeds to the next step. The SMS system obtains the validity period of the SM through the service schedule strategy table. If not, it proceeds to the next step. The SMS system judges whether the validity period is contained in the SM. If yes, the SMS system adopts the validity period. If not, it proceeds to the next step. The SMS system obtains the validity period of the SM through the service attribute table. If not, it proceeds to the next step.
Huawei Technologies Proprietary 3-18
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Serial No. 6
Description The SMS system judges whether the calling party is registered. If yes, the SMS system adopts the validity period in the registered information. If not, the SMS system adopts the validity period by default. The validity period is adopted after step 1 to 6. The SMS system judges whether the validity period is longer than the maximum validity period of the system. If yes, the validity period is changed to the maximum validity period of the system. If not, the validity period is unchanged.
2) 3)
The infoX-SMS system schedules and delivers the SM. The infoX-SMS system determines the timeout deletion mode of the SM according to the MT error code returned by the wireless network when the SM delivery fails, and accordingly judges whether the SM meets the conditions for timeout deletion. The following are the timeout deletion modes. Each MT error code corresponds to a deletion mode.
Deletion before timeout When a called entity receives a response to delivery of an SM or a delivery failure occurs, the SMSC views whether any SM will time out. If the result of the current time plus the time interval for next delivery is larger than the SM validity time, this SM will time out. The SMSC deletes it immediately whether the SMSC ever delivered it or not.
Deletion after timeout After the SMSC delivers an SM of a called entity, if there is a new SM submission which triggers the delivery of SMs in the called entity in non-work status or the time for redelivering an SM is up in non-work status, the SMSC views whether any SM is time out. If there is, the SMSC deletes it.
& Note: If the validity period is equal to the timeout period, the SMS system recognizes the SM as not timed out, and continues to schedule the SM.
4)
The infoX-SMS system deletes the SM if it meets the conditions for timeout deletion, and then records it into the historical information database.
Huawei Technologies Proprietary 3-19
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Caution:
l
For non point-to-point SMs, their validity period, deletion before timeout and deletion after timeout are carried out strictly according to the methods described in the preceding.
For all point-to-point SMs, if they fail to be delivered, the SMS system cannot delete the SM in ten minutes during the redelivery interval. If the validity period is less than ten minutes or the redelivery interval configured, the SMS system reconfigures the validity period of the SM to one hour.
3.2.5 Repeated SM Redelivery Processing
I. Feature description
The infoX-SMS system attempts to redeliver SMs that are not delivered successfully repeatedly.
II. Implementation principles
The system provides three redelivery mechanisms as shown in Table 3-8. Table 3-8 Redelivery mechanisms Mechanism Processing When an SM is delivered, if the HLR detects that the SM cannot be received because the MS is switched off or the storage area is full, the delivery of this SM fails and the cause is registered in the HLR. Alert_SC triggering SMs When the HLR detects that the failure cause is eliminated (that is, the MS is switched on, or the memory of the MS is available, and so on), it sends the Alert_SC command to the SMS system. The SMS system redelivers the SM after a waiting time. You can set the waiting time in TimeOut of [AlertSC] in the smscconfig.ini file. Setting waiting time is to avoid redelivery failure that led by long power-on time of MSs. If an SM fails to be delivered, the SMS system adopts specific scheduling strategy and performs subsequent scheduling on the SM according to the error code returned after the delivery failure. You can set the scheduling strategy to Redeliver, Delete, or Write into L2Cache according to actual requirements. If Redeliver is adopted, the SMS system attempts to redeliver the SM according to the set redelivery strategy. The SMS system triggers the SM that has the requirement of timed delivery at a specified time.
Periodically redelivering SMs
Triggering SMs at a specified time
Huawei Technologies Proprietary 3-20
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.2.6 Scheduling Mode Processing
I. Feature description
Besides the store and forward message mode, other scheduling modes are also required in the current applications. In light of the requirements, the Huawei-developed SMS system provides the following scheduling modes as shown in Table 3-9. Table 3-9 Scheduling modes Scheduling mode Store and Forward Message Mode Processing If an SM is delivered unsuccessfully, the SMSC redelivers it until it is successfully delivered or it is time-out. The delivery interval depends on the error code returned from the NSS, and it can be set. The SM with high priority can be delivered first. The SMSC delivers an SM only once regardless of the delivery result (success or failure). Datagram Message Mode For example, in the GPS application, after an SM fails to be delivered for the first time, it does not need to be stored. In this application, no reliability is required for the SM scheduling. Instead, it is time sensitive. The SMSC immediately delivers an SM submitted by the ESME, and returns the delivery result to the ESME in the response to the submission request. For example, such services as the MS bank and mobile stock require the delivery result to be known in the response to the submission of an SM, and it is not required that the SM must be delivered successfully.
Transaction Message Mode
II. Implementation principles
1) After receiving an SM, the infoX-SMS system decides which scheduling mode to adopt by using the following methods. The infoX-SMS system can adopt one of the following scheduling modes:
l l
A: scheduling mode specified by the SP when the SM is submitted B: scheduling mode specified in the attributes of the account through whose interface the SM is submitted C: scheduling mode specified in the registration information of the calling party of the SM
Table 3-10 introduces how the SM scheduling mode is determined:
Huawei Technologies Proprietary 3-21
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Table 3-10 SM scheduling mode Serial No. 1 Description The default scheduling mode, that is, the store and forward mode, is used as the scheduling mode of an SM submitted by an MS through the Gateway (MAP Server) interface. For an SM submitted by a service, if factor A or factor B specifies the default scheduling mode (store and forward), the infoX-SMS system adopts the scheduling mode specified by the other factor. If different scheduling modes are specified by factor A and factor B, and that neither factor A nor factor B specifies the default scheduling mode (store and forward), the infoX-SMS system adopts the default scheduling mode. In case that the scheduling mode cannot be determined by using the preceding methods, the scheduling mode is determined by factor C. In case that the scheduling mode cannot be determined by using the preceding methods, the default scheduling mode is adopted (store and forward).
2)
The infoX-SMS system schedules and delivers an SM according to its scheduling mode.
3.2.7 Entity-Based Scheduling Processing
I. Feature description
In the infoX-SMS system, short message entities (SMEs) include free entities and ordered entities. The system creates free entities or ordered entities according to the attribute of the called party. For SMs corresponding to different SME type, the system adopts different scheduling modes.
II. Implementation principles
Table 3-11 shows the entity-based scheduling processes.
Huawei Technologies Proprietary 3-22
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Table 3-11 Entity-based scheduling processes Serial No. Description After receiving SMs, the SMS system adopts the following methods to create SMEs:
l
The SMS system creates ordered entities by default if the called numbers are MS numbers. Because the SMS system can only delivers an SM to the MS at a same time, the MSISDN cannot be a free entity. If the called numbers are configured in the service attribute table, the SMS system creates free entities or ordered entities according to the specified delivery mode (free delivery or ordered delivery) in the service attribute table of the called numbers. The SMS system creates free entities by default if the called numbers are not registered service numbers, that is, if the called numbers are neither in the service attribute table nor registered numbers or MS numbers. If the number of free entities in the memory exceeds the maximum value set in the License file, the SMS system creates ordered service entities.
For SMs corresponding to different SME type, the SMS system adopts different scheduling strategies in delivering SMs.
l
For SMs sent to ordered entities, The SMS system sequences the SMs according to their priority and submission time, and then put them into the same message queue for scheduling. The system delivers an SM at one time, and delivers the next SM after the delivery of the first one is finished (on receiving the ACK message or timeout message). The SMS system creates ordered entities for MS numbers by default because only one SM can be sent to mobile subscriber at one time. For SMs sent to free entities, The SMs are delivered independently and concurrently. The system does not wait for sending the next message after the delivery of the first one.
3.2.8 Multidimensional Intelligent Scheduling
I. Feature description
The SMSC can distinguish the priorities of SMs according to the subscriber priority, the service priority and the number segment priority. For SMs of different priorities, different multidimensional scheduling strategies can be adopted. Multidimensional scheduling strategies are divided into four types: common mode, busy-hour mode, idle-hour mode and festival mode. The multidimensional parameter of each scheduling strategy can be customized according to actual requirements. With the multidimensional scheduling, SMs can be scheduled differently according to different subscriber, service and number segment priorities. Multidimensional scheduling strategies define the processing mechanism for SMs failed to be delivered. In different scheduling modes, that is, common mode,
Huawei Technologies Proprietary 3-23
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
busy-hour mode, idle-hour mode, and festival mode, the system administrator can set different scheduling strategies (Redeliver, Write into L2Cache, Delete, Delete all, and Redeliver SM of high priority) for SMs with different MT error codes. Therefore, the SMSC adopts different scheduling strategies for SMs failed to be delivered for different reasons. For each MT error code, the SMS system can configure SM processing strategies of up to 20 levels (Level 1 - level 20). If the SM fails to be delivered after being processed by the processing strategy of the current level, and the system returns the same MT error code, the system adopts the processing strategy of the next level. The SM is deleted from the memory if it is not delivered successfully after being processed by processing strategies of 20 levels.
II. Implementation principles
Table 3-12 shows multidimensional intelligent scheduling. Table 3-12 Multidimensional intelligent scheduling Procedure Description After receiving SMs, the infoX-SMS system decides which multidimensional scheduling strategy to adopt by using the following methods:
l
The system selects the multidimensional scheduling strategy for SMs according to the service scheduling strategy table. l If there are no matched multidimensional scheduling strategies in the service scheduling strategy table, the system decides the multidimensional scheduling strategy according to the priority queue scheduling decision table and the priority of SMs. l The system adopts the default multidimensional scheduling strategy if no matched multidimensional scheduling strategy is found after the preceding methods are used. & Note: It is configurable whether the system adopts the service scheduling strategy table first or the priority queue scheduling decision table first to decide the multidimensional scheduling strategy.
The infoX-SMS system schedules and delivers the SMs. If the delivery fails, the infoX-SMS system determines the scheduling strategy of the SMs according to the current running mode (common mode, busy-hour mode, or festival mode) of the system, the MT error codes returned by the system and the multidimensional strategy of the SMs.
l
4
l
If the delivery fails again and the system returns the same MT codes, the system adopts the processing strategy of the next level in the next delivery. If the SMs still cannot be delivered successfully after being processed by the processing strategies of 20 levels, the system deletes them from the memory. If the system returns different MT error codes, adopt a different scheduling strategy as instructed in step 3.
If the delivery is still unsuccessful, repeat step 4.
Huawei Technologies Proprietary 3-24
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.2.9 L2CacheDaemon Processing
I. Feature description
With the memory database technology, the SMSC schedules SMs through the memory database. Messages of lower priority in the memory database are saved into the L2Cache Daemon database when the SMSC is heavy loaded. The SMs are read back to the memory for schedule and delivery when the load of the SMSC is lower. This method can reduce the load on the SMSC during peak hours of traffic. In this case, the undelivered SMs are replaced timely instead of occupying the memory for a long time, hence ensuring the system stability in peak hours.
II. Implementation principles
The L2Cache features include writing SMs into L2CacheDaemon database and reading SMs from L2CacheDaemon database.
l
Writing SMs into the L2CacheDaemon database When the writing conditions are met, the SMSC notifies the L2CacheDeamon to write SMs in the non-work status that meet writing conditions into the L2CacheDaemon database. Table 3-13 lists the conditions on which the SMs are written into the L2CacheDaemon database.
Table 3-13 Modes of writing SMs into L2CacheDaemon database Mode Processing If the SM delivery fails, and the scheduling strategy is Write into L2Cache according to the multidimensional scheduling strategy and the MT error code returned by the system, the SMSC writes the SM into the L2CacheDaemon database. Conduct the operation of Export SMs in memory on the MT console of the infoX-SMS system. Then, the system writes the SMs waiting in the memory because of delivery failure and scheduled time into the L2CacheDaemon database. The system adopts the corresponding threshold processing strategy when the ratio between the actual value of a parameter (for example, MO Speed, MT Speed, or Memory SM number) in the system and that specified in the License file reaches the threshold. If the threshold processing strategy is Write into L2Cache, the SMs that meet the condition are written into the LaCacheDaemon database.
Huawei Technologies Proprietary 3-25
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
& Note: When the function of writing SMs into the L2CacheDaemon database is triggered, only SMs whose priorities are lower than or equal to Message Queue of Highest Priority in L2Cache are written into the L2CacheDaemon database. The highest priority of SMs that are written into the L2CacheDaemon database is configurable.
Reading back SMs from the LaCacheDaemon database
Table 3-14 lists the three conditions on which SMs are read back from the L2CacheDaemon database. Table 3-14 Modes of reading back SMs from the L2CacheDaemon database Mode Processing The SMSC periodically judges whether SMs in the L2CacheDaemon database can be read back. When the read-back conditions are met, the SMSC initiatively notifies the L2CacheDaemon, and then the L2CacheDaemon reads back the SMs from the L2CacheDaemon database. The SMSC then creates the SM in the memory and schedules it according to a certain scheduling strategy. When the SMSC receives the ALERT_SC message (the MS is activated or is capable of receiving SMs), the L2CacheDaemon reads back the corresponding SM from the L2CacheDaemon database. If SMs in the L2CacheDaemon database expire, they are forwarded to the expiry partition, read back and then deleted in ten minutes.
3.2.10 Threshold Processing
I. Feature description
The SMSC supports License management. The hardware and software of the system determine the license of the SMSC. When relevant values of the system reach the certain range of the specified value in the graded scheduling strategies, the system starts the threshold processing. Therefore, the stability and reliability of the system is ensured. The scheduling strategies in the threshold processing can be set according to actual situations.
II. Implementation principles
Table 3-15 shows the threshold processing.
Huawei Technologies Proprietary 3-26
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Table 3-15 Threshold processing Procedure Description The system adopts a specific threshold processing strategy, for example, distributing flow and indicating busy, rejecting new MO SMs, and writing messages into the L2Cache, when the ratio between the actual value of a parameter (MO Speed, MT Speed, or Memory SM number) in the system and that specified in the License file reaches the threshold. The system stops using the threshold processing strategy when the ratio between the actual value of a parameter in the system and that specified in the License file decreases and reaches the threshold value for stopping the processing strategy.
3.2.11 Functions of the GSM MAP Server
I. Feature description
1) 2) 3) 4) 5) 6) 7) 8) 9) Supporting multiple-module processing Supporting Phase 1, Phase 2 and Phase 2+ SM signaling Supporting the identification of MAP session version in the GSM network Implementing the signaling flow of submitting SMs from GSM MSs, and transferring the submitted SMs to the SMSC Implementing the signaling flow of delivering SMs from the GSM SMS system, and returning the delivery results to the SMSC Implementing the ALERT_SC signaling flow from the HLR to the SMS system, and sending the corresponding information to the SMSC Supporting the function of sending multiple SMs so as to improve the network efficiency Version number of MAP signaling being configurable Monitoring the running status of the system
10) Monitoring resources of the MAP Server 11) Providing the function of querying the location of an MS 12) Monitoring the message exchange between the MAP Server and SMS system, MTI Server and MAP Server 13) Supporting 2M signaling link 14) Supporting SIGTRAN signaling 15) Signaling the feature of multiple signaling points 16) Supporting obtaining delivery routes from different HLRs according to different number segments 17) Receiving SRI messages and Forward MT messages by simulating HLR and MSC 18) Supporting SM interception
Huawei Technologies Proprietary 3-27
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
19) Supporting networking of multiple MAP Servers, and message distribution by percentage, by calling number segment, and by the ending digits of the called number 20) Supporting testing the normal running of the SMS system in the networking of multiple MAP Servers
II. Implementation principles
The GSM MAP Server completes the relevant SM signaling to the SMS system after the interaction with the PLMN. It converts the SM application protocol in the MAP protocol into to the internal protocol, and sends it to the SMS system for the realization of scheduling. SM interception: cooperating with HUAWEI SPS, the GSM MAP Server intercepts an SM sent by a subscriber roaming to the local area and sends it to the SMS system for information security authentication. In this way, the SMS system provides corresponding services to the subscribers roaming to the area. Flow distribution: in different flow distribution modes, the MAP Server distributes SMs to different SMS systems respectively by the ending digits of the called number, calling number segments, or percentage.
3.2.12 Functions of the CDMA MAP Server
I. Feature description
1) 2) 3) 4) 5) 6) 7) 8) 9) Supporting SM signaling in the CDMA network. Supporting the signaling flow of CDMA MSs submitting SMs to the MAP Server, and forwarding the submitted SMs to the SMSC. Supporting the signaling flow of the SMSC delivering SMs in the CDMA network to the MAP Server, and returning delivery results to the SMSC. Supporting the signaling flow the HLR sending the Alert_SC message to the SMSC, and supporting sending the message to the SMSC. Supporting the message forwarding flow among SMS systems for the CDMA network. Supporting delivering multiple SMs in batches to increase the network efficiency. Supporting monitoring the running status of the system. Supporting monitoring the resources of the CDMA MAP Server. Supporting to query the MS location. SMSC, and between the MTI Server and the MAP Server. 11) Supporting 2M signaling link. 12) Supporting the SIGTRAN signaling. 13) Supporting multiple signaling points (SPs).
10) Supporting monitoring the message exchange between the MAP Server and the
Huawei Technologies Proprietary 3-28
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
II. Implementation principles
The CDMA MAP Server completes the relevant SM signaling to the SMS system after the interaction with the PLMN. It converts the SM application protocol in the MAP protocol into to the internal protocol, and sends it to the SMS system for the realization of scheduling.
3.3 Basic Services
3.3.1 MO SMs
The MO refers to the process that the MS submits an SM to the SMS system, and then receives an acknowledgement message from the SMS system.
3.3.2 MT SMs
The MT refers to the process that the SMS system sends an SM to the objective MS according to the schedule, and then receives an acknowledgement message from the MS.
3.3.3 Shortcut Messages
& Note: Only the SMS system of the GSM network supports the shortcut messages.
The shortcut message is a kind of SM. After a shortcut message is received, it is displayed on the screen of the MS immediately, while an ordinary short message is displayed only after the subscriber chooses to read it. After the subscriber reads the shortcut message, he can choose whether to save it. If he chooses not to save it, the next SM will overwrite this one. For example, the data coding scheme (DCS) of the UCS2 coding shortcut SM is 24, which is different from the ordinary SM. If the MS supports the shortcut message service, it checks the DCS value after receiving an SM. If the value is 24, the SM is displayed on the screen of the MS immediately. If the MS does not support the shortcut message service, it processes the received SM as an ordinary SM.
& Note: Only the SMS system of the GSM network supports the twinkle messages.
Huawei Technologies Proprietary 3-29
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
l l l
If the DCS of an SM is 16, the SM is a shortcut SM of 7bit coding. If the DDS of an SM is 20, the SM is a shortcut SM of 8bit coding. If the DDS of an SM is 24, the SM is a shortcut SM of USC2 coding.
The SMS system supports changing the ordinary SMs into shortcut SMs. The subscriber can set calling numbers and time segments as conditions for changing SMs (to be received) into shortcut SMs. For SMs that meet the conditions, the SMS system changes the DCS value of SM attribute, thus changes ordinary SMs into shortcut SMs, and then sends the shortcut SMs to the subscriber.
3.3.4 Twinkle SMs
The twinkle SM service is similar to the shortcut message service, which needs the support of the MS. When a short message is received, the MS first judges whether there are special control characters (for example, the NOKIA MS takes 1 of ASCII character as the special control character). If there are, the contents within the control characters are displayed in the twinkling mode.
Huawei Technologies Proprietary 3-30
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
& Note: NOKIA MS is the product of the NOKIA Corporation. For details of the product, refer to relevant technical materials of the NOKIA Corporation. The NOKIA Corporation reserves all rights of the trade marks and copyrights of its company name, product names and documentation mentioned in this manual.
3.3.5 Alert Notification Service
As an SMPP 3.4 message, the Alert Notification cooperates with the set_dpf field of Data_sm to transparently transmit the Alert_SC message. When the MS is switched on, or the memory is released due to such operations as deleting SMs when the memory is used up, the HLR sends an Alert_SC message to the SMS system. If an ESME fails to send an SM to the subscriber with the Data_sm command and a delivery pending flag has been successfully set for the SM, the SMS system sends the Alert_Notification message to the ESME, indicating that the SM function of the subscriber is available. The service enables the SMS system to instruct the ESME to send subscribers messages. For example, the WAP proxy server can rely on this function to send data to subscribers.
3.3.6 EMS SMs
ETSI GSM Specifications 03.40 (4.9.1): European Digital Cellular Communications System; Point-to-Point Short Message Service Technique Implementation. The SMS system can identify user data header indicator (UDHI). For an SM whose UDHI is 1, the SMS system checks the user data header (UDH). If the UDH is illegal, the SMS system refuses to send the SM.
& Note:
l l
If the UDHI of an SM is 1, the SM has a special SM head. It is an EMS SM. If UDHI is 0, the SM is an ordinary SM.
3.3.7 Prepaid SMs
The SMS system supports interconnection with the intelligent network (IN), thus realizes authentication and charging function of prepaid subscribers.
Huawei Technologies Proprietary 3-31
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
After the SMS system receives SMs submitted by the prepaid subscribers, the SMS system sends charging petitions to the SCP, and then carries out the processes according to the charging results. For the SMs charged successfully but failed to be delivered, the SMS system notifies the SCP to reimburse the subscriber for the undelivered SMs. The inform modes fall into instant inform and reimbursement bill inform. They are reliable.
3.4 Management Functions
3.4.1 Logs and Alarms
The SMSC provides the log and alarm functions for operations and the abnormity that affects the normal system operation. Through the alarm box, audio/visual alarms can be generated. The alarms of different levels can be given off for the abnormities of different levels. The information about abnormities is recorded for analyzing and checking problems. The SMSC generates logs and alarms for the abnormities or operations described in Table 3-16. Table 3-16 Abnormities or operations Serial No. 1 2 3 4 5 Description Log records for all the operations of the SMSC configuration and modification Alarms for the lack of application resources Log records for the connection of key services and alarms for abnormities Log records for the database connection and alarms for abnormities Alarms for other abnormities
The SMS system supports alarms for system resources. For the Windows and UNIX operating systems, the alarms are described in Table 3-17. Table 3-17 Alarms for system resources Serial No. 1 2 3 4 5 Description Alarm monitoring of CPU occupation of the whole system Alarm monitoring of CPU occupation of single process Alarm monitoring of the memory occupation Alarm monitoring of the disk occupation Alarm monitoring of the system disk and the network card failures
Huawei Technologies Proprietary 3-32
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.4.2 Bill Statistics and Browsing
The system can generate standard bills, perform classified statistics of bills, browse and print bills, and dump overdue bills. Charging information can be transferred to the billing center in accordance with the FTP or FTAM procedures, or processed off line with the tape drive.
3.4.3 System Parameter Setting
All parameters of the system can be set in the infoX-SMS system. The parameter configuration includes: setting network parameters of the software modules, setting operation parameters of the SMS system (such as communication waiting time, size of the SM cache, and event logs), and editing predefined SMs.
3.4.4 System Status Monitoring
The infoX-SMS system can monitor the CPU usage, memory usage, number of SMs, and number of entities, as well as display the contents of all SMs stored in the memory and database.
3.4.5 Database Maintenance
The SMS system starts the database maintenance program on schedule (at night in general) to check the database consistency, and handle illegal information in time.
3.4.6 Network Management
The Huawei-developed mobile short message subsystem of iManager I2000 NMS features powerful service provisioning capability, simple and convenient NM means. The mobile short message subsystem of iManager I2000 NMS manages SM equipments through the MT server. It provides perfect management function for the SMSC and basic configuration management function for the MAP Server and the MTI Server, and provides all the functions except the service performance management function for the SM information service platform. The SM NMS uses iManager 12000 NMS to manage the SM system data uniformly. The service modules provide parameters and alarm information of the SM system, and then submit them to the iManager I2000 NMS. The iManager I2000 NMS processes the data according to the requests.
3.4.7 Report Statistics
The SMS report system makes the statistics of the SM bill records, and outputs accurate and visual statistics reports. Thus the subscribers can know various data of
Huawei Technologies Proprietary 3-33
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
the SMS system the operation so as to perform analysis and make decisions, greatly facilitating the management on the SMS system by the operator.
3.5 Operation and Maintenance
The SMS system MT console provides comprehensive maintenance, monitor, and test functions. With the MT console, you can maintain multiple SMSCs in a centralized way, compare and synchronize data of different SMSCs. In addition, the SMS system also provides data importing and exporting, facilitating data maintenance.
3.5.1 Authenticating OMC Subscribers
This function is used to maintain and manage the authority of the OMC users, restrict OMC users that do not have the authority, and forbid them to perform any operation on the SMS system beyond their authority.
3.5.2 Configuring SMS System Parameters
The function enables you to set system parameters of the SMSC, including environment parameters and deletion modes. The function also enables you to compare default values of environment parameters with values of environment parameters of a specified SMSC, and synchronize them. In addition, you can compare and synchronize system parameter settings of different SMSCs. The system parameters of the SMSC you can set are described in Table 3-18. Table 3-18 Description of system parameters Parameter Country code Flow time control retry Description For example, the country code of China is 86. Time interval of the SMSC redelivering SMs failed to be delivered due to flow control Maximum number of SMs which can be submitted or stored simultaneously by each MS SME Maximum number of SMs which can be delivered or stored simultaneously by each MS SME Default life cycle adopted when no life cycle is defined for the SM Adding digits for the number of the SMSC according to the users digit adding plan. Time-out duration of the SMSC waiting for the ACK returned from the MAP Server or the service interface.
Maximum submission number Maximum number delivery
Default SM life cycle Digit adding plan Time-out duration of waiting for ACK
Huawei Technologies Proprietary 3-34
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Parameter
Description Including deletion before timeout and deletion after timeout.
l
Deletion mode
l
Deletion before timeout When a called entity receives a response to delivery of an SM or a delivery failure occurs, SMSC views whether any SM will time out. If the result of the current time plus the time interval for next delivery is larger than the SM validity time, this SM will time out. SMSC deletes it immediately whether SMSC ever delivered it or not. Deletion after timeout After the SMSC delivers an SM of a called entity, if there is a new SM submission which triggers the delivery of SMs in the called entity in non-work status or the time for redelivering an SM is up in non-work status, SMSC views whether any SM is time out. If there is, SMSC deletes it.
IP address of the alarm server PID of each module Mask bit of the alarm function of each module
IP address of the alarm server Process identification of each module It indicates whether to mask the alarm of the corresponding module.
3.5.3 Pre-defined SMs
Pre-defined SM means that the SP uses predefined sentences to replace sentences used normally. Portability variables of pre-defined SMs If the SM ID (sm_default_msg_id) is set by default, when ESME is submitting an SM, the SMS system uses an SM that is combined from content of pre-defined SM template and content of pre-defined SM, to replace the SM content submitted by the ESME. Managing SM pre-definition includes adding, modifying and deleting pre-defined SMs.
3.5.4 Setting Authentication and Number Conversion Parameters
Parameters related to the authentication and number conversion include:
l l l
Authentication mode: blacklist or whitelist Whether to convert numbers on a specific number conversion point Number conversion mode: number head conversion or number tail conversion
You can set the calling and called authentication number segments for different SMC addresses and accounts, and the number conversion data on different number conversion points in the infoX-SMS system.
Huawei Technologies Proprietary 3-35
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.5.5 SMSC Account Management
An SMSC account is used to manage the connection between the SMSC and other modules like ESME and MAP Server. A valid account is required for the SMSC to authenticate the validity of the connection between a module such as the ESME or MAP Server and the SMSC. The account stores such data as interface authority, authentication property, basic flow control information. The SMS system account management includes querying accounts, adding accounts, deleting accounts, modifying accounts, comparing accounts, synchronizing accounts, importing accounts, exporting accounts, adding interfaces, deleting interfaces, modifying interfaces, blocking interfaces and unblocking interfaces
3.5.6 Setting Route Tables
This function is used to manage SM route tables of the accounts on the SMSC. With this setting, route definition can be performed for all SM data, that is, the processing module of a certain SM data can be specified. Route table settings include querying route tables, adding route tables, deleting route tables, adding sub-items in the route table, deleting sub-items in the route table, changing route in batch, comparing routing information, synchronizing routing information and testing routing information.
3.5.7 PPS Route Number Segments
This function is used to manage the number segments of the PPS service and Mobile Virtual Private Network (MVPN) service. The authentication mode and route for the number segments of the local PPS service and local MVPN service should be flexibly set according to the actual requirements. The PPS route management is used to add, delete, import and export, test, query, and save PPS routes, as well as modify PPS authentication type. Meanwhile, you can compare and synchronize PPS routes of different SMS systems.
3.5.8 Other Operators Number Segment Management
This function is used to manage and set other operators' number segments (that do not need to be charged in the SMSC). The management of other operators number segments includes adding, deleting, importing and exporting, querying, and saving other operators number segments, as well as comparing and synchronizing other operators number segments of different SMS systems.
Huawei Technologies Proprietary 3-36
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.5.9 SMSC Monitoring and Tracing
This function is used to monitor the running status of the SMSC and query SMs in the memory and database, providing methods for determining whether the system is running normally and the basis for system expansion. The SMSC monitoring and tracing includes:
l
Monitoring System resource This function is used to monitor the system resources shown in Table 3-19.
Table 3-19 Monitored system resources Monitored resource CPU Rate Occupancy Description CUP usage of the server where the SMSC is located Memory usage of the server where the SMSC is located Number of running threads of the SMSC servers can be displayed in real time so that the operation information of the SMSC can be known Number of running processes of the SMSC servers can be displayed in real time so that the operation information of the SMSC can be known Number of SMs in L2Cache currently Number of SMs that the SMSC sent to the L2Cache Number of SMs in the memory of the SMSC currently Number of subscribers registered in the SMSC Number of SMEs in the memory of the SMSC currently. Number of SM entities
l
Memory Usage Thread count
Process count Number of SMs in L2Cache Number of SMs sent to L2Cache Number of SMs in the memory Number of registered subscribers
An SME is a dynamic object created during the running of the SMSC. The dynamic relationship between SMs and registered SM subscribers is stored on SME.
Monitoring SMs This function is used for subscribers to observe the specific SM status of a specified number in the SMSC and SMEs and SMs on SMEs in the memory. This function includes querying specified subscribers and MO SMs in specified time segment, querying specified subscribers and MT SMs in specified time segment, querying specified subscribers MO SMs in the memory, and querying specified subscribers MT SMs in the memory.
Huawei Technologies Proprietary 3-37
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.5.10 SM Test
This function is used to test the SM transmission, completely set various attributes of the SM, edit the SM contents in the hex system, and display the transmission status and error codes. With the function of SM test, all parameters for transmitting an SM can be set. The parameters include:
l l l l l l l l l l l l l l l l l l l l l l
MSC Address SC Address Dispatching Mode Original Address Original Address Numbering Type Original Address Numbering Plan Destination Address Destination Address Numbering Type Destination Address Numbering Plan Priority RD RP UDHI SR Message Index PID DCS Default SM UDL Periodical Duration Timeout Duration SM Content
This function opens all SM parameters and provides the open SM test function.
3.5.11 Exporting SMs to Files
SMs in the SMSC memory can be exported to a file. This function is usually used to export SMs in the memory of one or more SMSCs into files and submit them into the memory of another SMSC for delivery through Short Message Broadcaster. For details of the Short Message Broadcaster, refer to Short Message Broadcaster Online Help. The operations of exporting SMs to file include:
l
Starting exporting SMs into files This operation is to export SMs in the memory of the SMSC into files. The SMs of one or more types shown in Table 3-20 can be exported simultaneously.
Huawei Technologies Proprietary 3-38
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Table 3-20 SM types to be exported SM type Point to point Point to service Point to operators other Description SMs sent between mobile subscribers of a same network. SMs sent from local mobile subscribers to SPs. SMs sent from mobile subscribers of one operator to those of other operators. SMs sent from SPs to local mobile subscribers. SMs sent from mobile subscribers of other operators to those of one operator.
Service to point Other operator to point
Stopping exporting SMs into the files This operation is to stop exporting SMs into the files.
3.5.12 SM Subscriber Management
This function is used to browse and trace subscribers of the SMSC, and manage the subscriber definition and deletion.
l
Browsing and tracing SM subscribers This function is used to query and browse the registered SM subscribers in the SMSC, and trace their states (such as "idle", "wait due to delivery failure", "wait due to timed messages", wait due to flow control).
Defining SM subscribers There are three ways to define SM subscribers: defining a single subscriber, defining subscribers in batch, and read from files.
Deleting SM subscribers This function is used to delete subscribers whose numbers are out of service. Modifying subscriber information This function is used to modify the registered information of subscribers with the changes in the subscriber information.
& Note: In addition to SM subscriber management on the MT console, the subscribers can also open accounts, deregister accounts, and change attributes through SMs and website.
Huawei Technologies Proprietary 3-39
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
3.5.13 Multidimensional Schedule Parameter Management
The SMSC can adopt multidimensional strategies for SMs of different priorities according to the subscriber priority, the service priority and the number segment priority. This function is used to manage various multidimensional schedule parameters at the MT console.
l
Configuring the service attribute table The service attribute table is used to configure the delivery mode (Deliver freely or Deliver orderly), maximum number of submission and delivery and calling validity period for service subscribers.
Managing the group number segments The group number segment means to define a group name, collect one or more number segments and put it/them into the defined group. In this case, the group number segments can be used conveniently in the management of the service schedule decisions, route and the PPS route.
Managing multidimensional scheduling strategies This functions is used to manage the processing mechanism of SMs that are delivered unsuccessfully.
Configuring parameters of authentication and number conversion This function is used to configure rules of authentication and number conversion, set the data of number conversion and authentication, and test rules of authentication and number conversion.
Managing the priority strategies It is used to manage the SM priority strategies that are used to determine the SM priority according to the calling and called number priorities.
Managing the number segment priority It is used to manage the number segment priority. The number segment priority table determines the number priority of subscribers who have not registered in the SMSC.
Managing service schedule decisions It is used to manage the service schedule decision table. The table determines the scheduling strategy of the specified calling service for called number segments and enhances the quality disparity among different services.
Managing the priority queue schedule decisions This function is used to manage default scheduling strategies for different priority queues.
Configuring festival parameters This function is used to configure the time points of each festival (maximum ten festivals), so that the SMSC can schedule the SMs accordingly.
Configuring parameters for busy hour of each week This function can be used to configure the busy hour on each day of a week so that the SMSC can schedule the SMs accordingly.
Huawei Technologies Proprietary 3-40
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
Configuring idle parameters of each week This function is used to configure the time segments of each week during which flow is light. In these time segments, the SMS system schedules SMs according to the schedule strategy of the idle mode. A maximum of two idle time segments can be configured each day.
Configuring multidimensional schedule parameters It is used to configure parameters for multidimensional scheduling on the SMS system.
Configuring global parameters of the counters This function is to configure basic parameters required by counters. These basic parameters are valid for all counters. Global parameters of the counters include: attributes of the counters, rules of adjusting MO or MT success rate, MO or MT error code, and groups whose delivery delay needs to be counted.
Managing statistic groups This function is to configure information of statistic groups for counters. Managing counters This function is used to configure counters and counter condition for sorting and counting SMs.
3.5.14 L2Cache Management
The L2Cache features enhance the SMSC performance. When the SMSC is busy, it writes the SMs that cannot be processed immediately into the L2Cache database; when the SMSC becomes idle, it reads the SMs from the L2Cache database and processes them. The L2Cache can be managed through the MT console.
l
Configuring L2Cache parameters
You can configure relevant parameters for the SMSC to read SMs from the L2Cache database. In addition, you can compare and synchronize L2Cache parameters of different SMS systems.
l
Importing SMs from the L2Cache file to the database
You can read the L2Cache file in the remote loading directory of the L2Cache module to the memory of the L2Cache module, and then write them from the L2Cache module to the L2Cache database.
l
Exporting SMs from the memory
You can export SMs from the memory of the SMS system to the L2Cache.
l l
Stopping exporting SMs from the memory You can stop SMs from the memory of the SMS system to the L2Cache.
3.5.15 Checking the Running Status of the SMS System with MSs
The maintenance personnel can use an MS to send a test SM to a called number. When receiving the SM, the GSM MAP Server sends it to the specified SMS system
Huawei Technologies Proprietary 3-41
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 3 System Functions and Implementation
according to the called number. After receiving the test SM, the SMS system returns a message to the calling party, indicating that the SMS system is running normally.
Huawei Technologies Proprietary 3-42
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
Chapter 4 Charging Function and Implementation
This chapter introduces the charging function of the SMS system, including the charging of prepaid and postpaid subscribers for the SMS, as well as the charging for long SMs. By reading this chapter, you can have an idea about the charging function and implementation of the SMS.
4.1 Charging for the SMS Postpaid
After a postpaid subscriber sends an SM, the SMSC writes a charging bill instead of charging him in real time. 1) 2) After the SM is successfully submitted to the SMSC of the SMS system, the SMSC schedules and delivers the SM. After the SM is delivered successfully or unsuccessfully, the SMSC deletes it from the memory and writes a charging bill. Information in the charging bill can satisfy various charging requirements. 3) The charging system obtains the charging bill from the bill directory, and then conducts charging according to the charging bill and specific charging policy.
4.2 Charging for the SMS Prepaid
The SMSC communicates with the SCP through the SMPP+ protocol, thus realizing the authentication and charging of PPS subscribers sending or receiving SMs. You can flexibly set the authenticated and charged objects to calling numbers, called numbers, or charged numbers. Figure 4-1 shows the networking of the SMSC and the SCP.
SCP1 SMPP+
SCP3
SMSC
SCP2
Figure 4-1 Connection between the SMSC and the SCP
Huawei Technologies Proprietary 4-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
1)
For the duration of the MO authentication of an SM, the SMSC forwards authentication and charging requests to the SCP of the corresponding PPS number segment based on the PPS number segment table.
2)
If the SCP returns a message indicating the success of the authentication and charging, the SMSC continues to handle and deliver the SM. Otherwise, the SMSC declines the submission of the SM.
& Note: If the SCP authentication fails and an error code is returned, the SMSC determines whether the calling or the called party passes the authentication according to the configurations in session SCP Code Map in smscppsconfig.ini.
3)
After the delivery of the SM, the SMSC, based on the requirements of the SCP, identifies whether to notify the SCP of the delivery result. If the SMSC forwards the result to the SCP, the SCP identifies whether the pre-deduction in the authentication procedure is valid based on the delivery result. For an invalid deduction, the pre-deduction fee is returned to the subscriber.
4.2.1 PPS Authentication and Charging Flow
The following introduces the PPS authentication and charging flow in the case that the SMSC is directly connected with the SCP where the data of the authenticated subscriber is located.
& Note: The PPS authentication and charging flows of point-to-point, point-to-service, and service-to-point SMs are the same, but their submission and delivery procedures are different from each other. Here the PPS authentication and charging flow of a point-to-point SM is introduced as an example.
Figure 4-2 shows the basic PPS authentication and charging flow.
Huawei Technologies Proprietary 4-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
MSC 1
SMS_IWMSC
SMSC
SCP
HLR
MSC 2
Forward_SM Message Transfer PPS_USER_CHECK PPS_USER_ CHECK_RESP Message Transfer Send_Routing _Info_For_sm Send_Routing_In fo_For_sm_Ack Forward_SM Delivery Report Delivery Report PPS_CHARGE _NOTIFY PPS_CHARGE_ NOTIFY_RESP
Figure 4-2 PPS authentication and charging flow The flow is described as follows: 1) 2) 3) After the MS submits the SM to the MSC 1, the MSC 1 forwards it to the interworking MSC for short message service (SMS-IWMSC). The SMS-IWMSC submits the SM to the SMSC (Message Transfer). The SMSC identifies whether to authenticate the called party, calling party or charge party based on the route table of the PPS number segment. If no, the handling operation continues. Otherwise, the authentication request message is sent to the corresponding SCP (PPS_USER_CHECK).
& Note: For each object to be authenticated, the SMSC sends an authentication request message (PPS_USER_CHECK) to the SCP. For example, the SMSC queries the PPS number segment table. If it determines that both the calling party and the called party of an SM must be authenticated, it sends two authentication request messages to the SCP for authenticating them respectively.
4)
The SCP identifies whether the subscriber is valid (including such factors as whether it is in the activated status and whether the balance is enough). The SCP then conducts the pre-deduction and returns the authentication response
Huawei Technologies Proprietary 4-3
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
message (PPS_USER_CHECK_RESP, including the authentication result and notification mode) to the SMSC.
l
Authentication result The value 0 is returned with a successful authentication; otherwise, the error code indicating the failure cause is returned.
Notification mode indicates whether to notify the SCP of the delivery result after an SM is delivered from the SMSC. It can happen in the following four cases: Notifying the SCP no matter the sending of the SM succeeds or not. Notifying the SCP if the sending of the SM fails. Notifying the SCP if the sending of the SM succeeds. Not notifying the SCP no matter the sending of the SM succeeds or not.
5)
The SMSC analyzes the PPS_USER_CHECK_RESP message indicating the authentication result. If the authentication fails, the SMSC declines the submission of the SM. Otherwise, the SMSC continues to handle the SM and submits the message transfer request to the gateway MSC for short message service (SMS-GMSC).
6) 7) 8) 9)
The SMS-GMSC queries the routing information for sending the SM from the HLR (Send_Routing_Info_For_SM) The HLR sends the routing information for sending the SM to the SMS-GMSC (Send_Routing_Info_For_SM_Ack). The SMS-GMSC forwards the SM to the MSC2 where the subscriber is located (Forward_SM) After delivering the SM to the subscriber, the MSC2 returns the delivery report to the SMS-GMSC (Delivery report)
10) The SMS-GMSC forwards the delivery report to the SMSC (Delivery report) 11) Based on the SCP-required notification mode and delivery result, the SMSC identifies whether to forward the short message result notification request message to the SCP. If yes, the SMSC forwards the short message result notification request message to the SCP (PPS_CHARGE_NOTIFY).
& Note: The SMSC writes the reimbursement bill if an exception of the interface between the SMSC and the SCP leads to the failure in the SMSC sending the short message result notification request message.
12) The SCP identifies whether the deduction in the authentication procedure is valid based on the delivery result. If no, the pre-deduction fee is returned to the subscriber. The SCP then forwards the short message result notification response message to the SMSC (PPS_CHARGE_NOTIFY_RESP).
Huawei Technologies Proprietary 4-4
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
4.2.2 SCP Interconnection Authentication and Charging Flow
If the SMSC is not directly connected to the SCP where the data of the authenticated subscriber is located, the SMSC conducts the authentication and charging through the SCP directly connected to itself. Figure 4-3 shows the SCP interconnection authentication flow. SCP1 is directly connected to the SMSC. The data of the authenticated subscriber (For example, subscriber A) is located at SCP2. In addition, SCP2 is connected with SCP1.
SMSC
PPS_USER_CHECK PPS_USER_CHECK PPS_USER_CHECK_RESP PPS_USER_CHECK_RESP PPS_CHARGE_NOTIFY PPS_CHARGE_NOTIFY PPS_CHARGE_NOTIFY_RESP PPS_CHARGE_NOTIFY_RESP
SCP1
SCP2
Figure 4-3 SCP interconnection authentication and charging flow The flow is described as follows: 1) Based on the PPS number segment route table, the SMSC determines that the SCP has to authenticate Subscriber A. Because the SMSC is not directly connected to SCP2 where Subscriber A is located, the SMSC forwards authentication request message to the SCP directly connected with the SMSC (PPS_USER_CHECK). 2) Based on the MSISDN of Subscriber A, SCP1 finds that the SCP where Subscriber A is located is SCP2 and forwards authentication request message to SCP2 (PPS_USER_CHECK). 3) SCP2 identifies whether Subscriber A is valid (including such factors as whether it is in the activated status and whether the payment amount is enough). The SCP then conducts the pre-deduction and returns the authentication response message (PPS_USER_CHECK_RESP, including authentication results and notification modes) to SCP1. 4) 5) SCP1 forwards the authentication response message to the SMSC. (PPS_USER_CHECK_RESP). The SMSC sends the SM. Based on the SCP1-required notification mode and delivery result, the SMSC identifies whether to forward short message result notification request message to SCP1. If yes, the SMSC forwards the short
Huawei Technologies Proprietary 4-5
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
message result notification request message to SCP1 (PPS_CHARGE_NOTIFY). 6) 7) SCP1 then forwards the short message result notification request message to SCP2 (PPS_CHARGE_NOTIFY). SCP2 identifies whether the deduction in the authentication procedure is valid based on the delivery result. If no, the pre-deduction fee is returned to the subscriber. SCP2 then forwards the short message result notification response message to SCP1 (PPS_CHARGE_NOTIFY_RESP). 8) SCP1 then forwards the short message result notification response message to the SMSC (PPS_CHARGE_NOTIFY_RESP).
4.2.3 MDSP Charging Flow
The SMCAPP cannot judge whether a subscriber is a PPS subscriber through his MSISDN. Therefore, the SMCAPP needs to be connected to the mobile data service platform (MDSP), which is responsible for judging whether a subscriber is an authorized PPS subscriber.
& Note: The infoX-MDSP is a data service product that is developed by Huawei and has the full intelligent right. It is a platform used for implementing integrated management and uniform access of the data service on the basis of the mobile communications network.
The SMSC connects to the MDSP through the SMPP+1.0 or SMPP+2.0 protocol. It transmits all point-to-point messages to the MDSP which judges whether a subscriber is a prepaid service or postpaid service subscriber.
l
If the subscriber is a prepaid service subscriber, the MDSP sends a charging request directly to the SCP. If the subscriber is a postpaid service subscriber, the MDSP notifies the SMSC of that, and then the SMSC marks the message as a PPS message in the charging bill, so as to facilitate the charging system to sort the bills required to be charged.
4.2.4 UTIns Unicom PPS Charging Flow
The SMSC provides an interface for the Unicom PPS. It connects to the Siemens payment platform (PP) through the UTIns for the PPS implementation. Figure 4-4 shows the connection among the UTIns, SMSC, and short message gateway (SMG).
Huawei Technologies Proprietary 4-6
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
SMG1...n
CM PP
UTIns/conversion module HTTP PP
SMSC1...n
PP SM
Figure 4-4 Connection between the SMSC and the Siemens payment platform
I. UTIns external interfaces The external interfaces of the UTIns include:
1) 2) 3) 4) 5) can be connected to up to ten SMSCs. can be connected to up to ten SMGs. adopt SMPP+ protocols when connected to SMSCs. adopt CMPP 1.1 when connected to SMGs. adopt HTTP 1.0 when connected to the payment platform.
II. The charging flow from the SMSC to the HTTP payment platform through UTIns
The processing flow is as shown in Figure 4-5.
SMSC UTIns PP
(1) Authentication request (2) Charging request (3) Charging ACK (4) Authentication ACK (5) Result Notification (6) Reimbursement request (7) Reimbursement ACK (8) Result Notification ACK
Figure 4-5 Unicom PPS flow for the SMSC 1) Upon receiving SMPP messages from the SMSC, the UTIns converts them into HTTP 1.0 messages, and delivers them to the payment platform.
Huawei Technologies Proprietary 4-7
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
2)
Upon receiving HTTP 1.0 messages from the payment platform, the UTIns converts them into SMPP messages, and sends them to the SMSC.
III. The charging flow from the SMG to the HTTP payment platform through UTIns
The processing flow is as shown in Figure 4-6.
SMG CMPP (1) sm-chg-req UTIns HTTP PP
(2) Charging request (3) Charging ACK (4) sm-chg-rsp (5) sm-cnfm-req (6) Reimbursement request (7) Reimbursement ACK (8) sm-cnfm-rsp
Figure 4-6 Unicom PPS flow for the SMG 1) 2) Upon receiving CMPP messages from the SMG, the UTIns converts them into HTTP 1.0 messages, and delivers them to the payment platform. Upon receiving HTTP 1.0 messages from the payment platform, the UTIns converts them into CMPP messages, and sends them to the SMG.
& Note: There are two types of messages: charging and reimbursement.
4.3 Charging for Long SMs
The infoX-SMS system charges for unsegmented long SMs that are submitted to the SMSC only once. For those segmented long SMs that are submitted to the SMSC, the infoX-SMS system supports two charging modes:
Huawei Technologies Proprietary 4-8
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 4 Charging Function and Implementation
I. Charging for each packet of a long SM
l
For postpaid subscribers The infoX-SMS system generates a charging bill for each packet of a long SM. The charging system charges the postpaid subscriber according to the charging bills and specific charging policy.
For prepaid subscribers The infoX-SMS system sends the authentication and charging message to the SCP for each packet of a long SM. The SCP authenticates and charges the prepaid subscriber in real time.
II. Charging for a long SM only once
l
For postpaid subscribers The infoX-SMS system generates a charging bill only for the first packet of a long SM. That is to say, it regards that all subsequent packets of the long SM are free. The charging system charges the postpaid subscriber according to the charging bill and specific charging policy.
For prepaid subscribers The infoX-SMS system sends the authentication and charging message to the SCP only for the first packet of a long SM. For all subsequent packets of the long SM, the infoX-SMS system does not send authentication and charging messages to the SCP. That is to say, it regards that all subsequent packets are free. The SCP authenticates and charges the prepaid subscriber in real time.
4.4 Individual Number PPS Function
The CDMA network is the destination network. All subscribers can dynamically update the payment types of their own. The infoX-SMS system judges PPS numbers according to the PPS route table. In addition, it checks whether a single MSISDN is a PPS number according to registration information. The authentication attributes in registration information must be identical with those in the PPS route table. Therefore, the PPS attributes of registered subscribers must include Authenticate the caller, Authenticate the called, and so on. The PPS attribute in registration information has higher priority than the PPS route table. When they conflict with each other, the former prevails. When the individual number PPS function is enabled, it is difficult to configure authentication routes in the PPS route table. Therefore, you need to add the default authentication account in the configuration file. If no route is found in the PPS route table, authentication messages are delivered from the default authentication account.
Huawei Technologies Proprietary 4-9
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 5 Reliability and Availability Design
Chapter 5 Reliability and Availability Design
This chapter introduces the design principles in the reliability, availability, and extendibility of the infoX-SMS system. By reading this chapter, you can have an idea about the measures and processing mechanism adopted for the reliability, availability, and extendibility of the infoX-SMS system. With this information, you can better manage and maintain the infoX-SMS system.
5.1 Reliability Design
The reliability design of the infoX-SMS system is embodied in several aspects. The following sections give details.
5.1.1 Dual System Running Mode
The infoX-SMS system adopts the dual system as the running platform, as shown in Figure 5-1.
Application system Monitor process of the application system Monitor script of the dual system Dual system software Unaccessible Standby host OS
Active host
Accessible
Database is locked or shared
Figure 5-1 Software composition of the dual system In the dual system running mode, kernel components of the system can be backed up. When the active host is faulty, the system automatically switches to the standby host. The data in the stabdby host are consistent with those on the active host before the fault. The dual system running mode costs less than others and does not need a special operating system. You only need to install the corresponding dual system software in an ordinary operating system. Both nodes of the dual system can still run independently. This mode affects the performance of applications at a lower degree, and it can be used more flexibly.
Huawei Technologies Proprietary 5-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 5 Reliability and Availability Design
5.1.2 Network Running Mode
The infoX-SMS system supports the networked SMS networking mode. A MAP Server can distribute MO messages to multiple SMSCs, and an SMSC can distribute MT messages to multiple MAP Servers. Figure 5-2 shows a common networking diagram.
LSTP1
LSTP2
SG1
SG2
SG3
MAP Server1
MAP Server2
MAP Server3
Ba
ck up
Back
up
SMSC1
SMSC2 SMPP
SMSC3
infoX-SMS GW
SG Signaling Gateway LSTP Low Level signaling Transfer Point SMPP Short Message Peer to Peer Real line: indicates direct connection. Dotted line between an MAP Server and an SG: indicates non-direct connection. Real line between an MAP Server and an SMSC: indicates that the SMSC is the active one. Dotted line between an MAP Server and an SMSC: indicates that the SMSC is the standby one.
Figure 5-2 Networked SMS networking diagram This networking mode associates all infoX-SMS systems within a certain range. It distributes partial flow of heavy-loaded infoX-SMS systems to infoX-SMS systems with lower load for processing, thus sharing resources, reducing the load of the infoX-SMS system overloaded, and enhancing the disaster tolerance capability.
Huawei Technologies Proprietary 5-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 5 Reliability and Availability Design
5.1.3 Flow Control
The infoX-SMS system can conduct comprehensive flow control for the SMS to avoid the impact of traffic in peak hours on the system.
l
The system conducts flow control at the interface and account levels. It limits the number of submitted SMs but it does not limit that of delivered SMs. The system monitors the actual values of such parameters as the number of SMs, number of SMEs, MO speed, and MT speed in real time. Once the actual value of one of the parameters exceeds the threshold for starting the threshold processing strategy, the corresponding threshold processing strategy is triggered. When the actual value is lower than the threshold value for terminating the threshold processing, the system automatically stops using the threshold processing strategy.
5.1.4 Alarm Detection
Devices of the infoX-SMS system support the alarm detection function. The system generates an alarm message of hardware or software when an exception affecting the system running occurs. It also generates an audio and visual alarm through the alarm box. With the audio and visual alarm function, alarms of different kinds and levels are reported differently. Software alarm messages are generated when process exceptions occur on both the active and standby hosts. In addition, the infoX-SMS system reports alarms to the NMS. It also provides detailed alarm information, including alarm causes, location information, and recovery suggestions, which help maintenance personnel adopt proper recovery measures in time, thus ensuring the normal running of the system.
5.1.5 Security Authentication
A comprehensive authentication system is the prerequisite of a reliable system. All MT terminals of the infoX-SMS system adopt the password login mode, and the passwords are encrypted. The system administrator uniformly allocates user accounts of the system. Strict encryption and security measurements are taken to prevent unauthorized access. In addition, the infoX-SMS system backs up messages in real time, monitors processes, and conducts fault tolerance processing on submitted messages.
5.2 Availability Design
The infoX-SMS system provides friendly, convenient, and safe MT terminals. The system provides two maintenance modes:
l
I2000 maintenance mode that supports remote centralized operations In this mode, the I2000 NMS can manage and monitor all network devices in the
Huawei Technologies Proprietary 5-3
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 5 Reliability and Availability Design
remote centralized way, and connect with superior NMS devices through SNMP. Besides common configuration operations, this mode supports the realtime collection of alarm information and statistics data. Alarm information helps users to know the current running status of the system. By analyzing statistics data, users can have an idea about the submission and delivery of SMs.
l
MT console maintenance mode that supports short-distance maintenance In this mode, you can quickly conduct query and setting operations, for example, creating accounts and routes. The modification to configuration information takes effect immediately without the restart of programs. In addition, the batch processing function is provided for some primary operations to increase the operation efficiency.
5.3 Extendibility Design
The extendibility of the infoX-SMS system is reflected in the product upgrade capability, function extendibility, and performance extendibility.
5.3.1 Overall Design
The SMS system is designed with the concept of separating services from switching. The system is divided into three layers, service switching layer, service supporting layer, and service implementing layer. In the three layers, the changes of services do not affect the running of the service switching layer and the service supporting layer. The adjacent layers communicate through protocols or encapsulated application programming interfaces (APIs). As a result, each layer is relatively independent. Being the specific service system, the service implementing layer features changeability and flexibility. Being the access and service supporting system, the service switching layer and service supporting layer feature stability and normalization. In the 3-layer encapsulation mode, changes of the service implementing layer do not affect the stability of the service switching layer and service supporting layer. After the service switching layer and service supporting layer are optimized and expanded in a normative way, all applications of the service implementing layer can be expanded in the aspect of service functions.
5.3.2 Product Upgrade Capability
The infoX-SMS system supports various operating systems such as Windows 2003 and SuSE Linux. Besides, it supports the Oracle database and DB2 database. The features of multiple MAP Servers and networked SMS support software expandability. In a single office, multiple SMS systems ensure the capability and performance. Among different offices, fault tolerance networking can be implemented
Huawei Technologies Proprietary 5-4
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 5 Reliability and Availability Design
through the networked SMS system function. For details, refer to section 5.1.2 Network Running Mode. The advanced telecom application environment (ATAE) architecture of hardware provides powerful expandability. The SMS system can run on a single board. You can add SMS systems by adding boards.
5.3.3 Function Extendibility
I. Modularized design and smooth expansion
In the infoX-SMS system, the TELLIN-USAU serves as the SG. With flexible configuration, various SGs have good extendibility. For example, the number of modules and links can be smoothly increased, and the system can be flexibly expanded to obtain the required capacity.
II. Convenient service extendibility
The SMS system provides various SMEs with open service interfaces. The system supports the short message peer to peer (SMPP) interface. This facilitates the access of other data sources and diversifies the functions of the service system. It also provides the user with graphical service creation environment (SCE), universal API, building blocks of the component object model/distribution component object model (COM/DCOM) and the service template technology, thus providing multiple flexible and convenient practical tools and technologies for the system extendability.
5.3.4 Performance Extendibility
When the configuration and processing capability of a single node in the system cannot satisfy the requirements of the service running, you can adopt the networked SMS system networking mode that is based on the Smart networked SMS system technology to implement the multiple node service processing mode. This networking mode enhances the reliability and processing capability of the system. Assume that an infoX-SMS system supports the processing capability of 800 SMs each second. In this case, you can use two (or four) infoX-SMS systems to compose the networked SMS system to satisfy the performance requirement of 1500 SMs each second (or 3000 SMs each second). It is obvious that the increase of the number of infoX-SMS systems and the performance improvement of the networked SMS system are in the direct proportion, and the increase of the number of infoX-SMS systems satisfies the expansion requirement. Meanwhile, the link capacity can be expanded through the increase of the number of modules because of the modularized design of the SG; therefore, the SG is not the bottleneck of the performance expansion.
Huawei Technologies Proprietary 5-5
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
Chapter 6 Typical System Applications
This chapter describes the solutions and signaling flows of SM exchanges among the CDMA, GSM, and TDMA networks. By reading this chapter, you can know the networking of the infoX-SMS system in the signaling network and the signaling flow of SM exchange between the CDMA and GSM networks.
6.1 Service Networking
Similar to the TDMA network, both the GSM and CDMA systems consist of four parts, the network subsystem (NSS), base station subsystem (BSS), operation and maintenance center (OMC) and mobile stations (MSs), as shown in Figure 1-1. Figure 6-1 shows the networking mode for the SMS system accessing the mobile network.
Figure 6-1 Networking mode for the SMS system accessing the mobile network
Huawei Technologies Proprietary 6-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
6.2 Service Description
The infoX-SMS system is a service processing system independent of the GSM, CDMA, and TDMA networks. It is responsible for submitting, storing, and forwarding SMs. The infoX-SMS system is responsible for the SM exchange among the GSM, TDMA, and CDMA networks. It is also responsible for the interworking among the PSTN, ISDN, and PSPDN so as to forward SMs from external short message entities (ESMEs). The SMS system can handle the SMS service of a single network, GSM, CDMA, or TDMA network, or forward short messages among the GSM, CDMA, and TDMA networks.
6.3 Processing Flow
I. MO and MT flows in the GSM network
Figure 6-2 shows the MO flow.
SMC SMC|WMSC HLR MSC VLR MS (1) Access request and possible authentication (2) Message Transfer (3) Forward_ ShortMessage
(4) Message Transfer (5) Ack
(6) Ack (7) Ack
Figure 6-2 MO signaling flow in the GSM network The flow is described as follows: 1) 2) 3) 4) The MS submits an access request and possible authentication message to the VLR. The MS submits an SM to the MSC. The MSC forwards the SM to the SMS-IWMSC (IWMSC: interworking MSC, responsible for processing SMs submitted by an MS). The SMS-IWMSC transfers the SM to the SMS system.
Huawei Technologies Proprietary 6-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
5) 6) 7)
The SMS system sends an acknowledgement (success or error) back to the SMS-IWMSC. The SMS-IWMSC sends the acknowledgement back to the MSC. The MSC sends the acknowledgement back to the MS.
Figure 6-3 shows the MT flow.
SMC SMSGMSC (2) SendRoutingI nfo_for_short message HLR MSC VLR MS
(1) Message transfer
(3) Forward_ ShortMessage (4) SendInfoFor_ MT_SMS (5) Message Transfer (7) Forward_ ShortMessage_ACK (6) ACK
(8) ACK
Figure 6-3 MT signaling flow in the GSM network The flow is described as follows: 1) 2) 3) 4) The SMS system submits the message transfer request to the SMS-GMSC (GMSC: Gateway MSC, responsible for processing delivered SMs). The SMS-GMSC queries from the HLR about the routing information for sending. The SMS-GMSC forwards the SM to the MSC. The MSC queries from the VLR about the routing information for sending, and from the HLR gets back the international mobile subscriber identity (IMSI) of the subscriber and the number of the MSC where the current subscriber is located. 5) 6) 7) 8) The MSC transfers the SM to the MS. The MS sends the acknowledgement back to the MSC. The MSC sends the forwarding report back to the SMS-GMSC. The SMS-GMSC sends the acknowledgement back to the SMS system.
II. MO and MT flows in the CDMA network
Figure 6-4 illustrates the MO and MT flows in the CDMA network.
Huawei Technologies Proprietary 6-3
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
Destination MS (1) system access
MSC BS
VLR
HLR
MC
Originator SME
(2) REGNOT
(3) REGNOT (4) regnot
(5) regnot
(6) SMDPP (7) smdpp
(10) SMSREQ (11) smsreq
(9) SMSREQ
(8) SMSREQ
(12) smsreq
(13) smsreq (14) SMDPP
(15) SMD-REQ (16) SMD-ACK (17) smdpp
Figure 6-4 MO and MT signaling flows in the CDMA or TDMA network The flow is described as follows: 1) 2) 3) 4) The destination MS makes itself recognized by other MSCs through registration or other system access. The MSC sends the REGNOT message to the VLR to notify it of the MS location. The VLR forwards the REGNOT message to the HLR to which the MS belongs. The HLR records the SM destination address of the MS, and returns the REGNOT message to the VLR. The attribute information of the MS is contained in the message. 5) 6) The VLR forwards the REGNOT message to the MSC. The originator MS submits an SM through the SMDPP operation to the SMS system, that is, the MS initiates an MO operation.
Huawei Technologies Proprietary 6-4
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
7) 8)
The SMS system returns the smdpp positive acknowledgement message to the originator MS. If the SMS system does not have the temporary SM routing address of the destination MS, it conducts step 8 to step 13. The SMS system sends the SMSREQ message containing the information of the MS whose route is to be queried to the HLR to which the MS belongs.
9)
The SMS system conducts step 9 to step 12 if the HLR does not have the temporary SM routing address of the destination MS. The HLR forwards the SMSREQ message to the VLR that provides services for the MS.
10) The VLR forwards the SMSREQ message to the MSC providing services for the destination MS. 11) The MSC sends the smsreq message containing the temporary SM routing address of the destination MS to the VLR. 12) The VLR forwards the smsreq message to the HLR. 13) The HLR forwards the smsreq message to the SMS system. 14) The SMS system uses the temporary SM routing address of the destination MS to send the SM through the SMDPP operation to the MSC of the destination MS. 15) The MSC and base station (BS) send the SMD-REQUEST message to the destination MS through an air interface. 16) The destination MS sends the SMD-ACK message to the MSC and the BS, indicating that it receives SMD-REQUEST. 17) The MSC converts SMD-ACK into the smdpp positive acknowledge message, and then sends it to the SMS system.
III. Flow of a GSM subscriber sending an SM to a CDMA subscriber
After a GSM subscriber sends an SM to a CDMA subscriber, the SM is first submitted to the SMS system for the GSM network. The SMS system for the GSM network adopts the flow of delivering SMs by obtaining routes. It is required that the SMS system for the GSM and CDMA networks can receive route obtaining information by simulating the GSM-HLR, return the response to the route obtaining (set the MSC number in the response message to the SMC number), and receive MT messages from the SMS system for the GSM network. Figure 6-5 shows the flow.
Huawei Technologies Proprietary 6-5
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
GSM-SC (1) SRI
ITP/STP
CDMA-SMS
CDMA-HLR
CDMA-MSC
(2) SRI (3) SRI_RESP (4) SRI_RESP (5) FOWORD_MT (6) FOWORD_MT (7) SMS_REQ (8) SMS_REQ_RESP (9) SMDPP (10) SMDPP_RESP (11) FOWORD_RESP
(12) FOWORD_RESP
Figure 6-5 Flow of a GSM subscriber sending an SM to a CDMA subscriber The flow is described as follows: 1) After the GSM-SC receives the SM from the calling party, the SM is processed according to the normal flow. Then, the GSM-SC obtains the route for the CDMA subscriber, and sends the SRI message to the signaling gateway, that is, ITP or STP. 2) 3) The signaling gateway forwards the SRI message to the CDMA-SMS. The CDMA-SMS processes the SRI message by simulating the GSM-HLR, uses the SMC number for the CDMA network, and returns the SRI_RESP message to the signaling gateway. 4) 5) 6) 7) The signaling gateway returns the SRI_RESP message to the GSM-SC. The GSM-SC delivers the MT message to the signaling gateway because it has obtained the CDMA-SC number. The signaling gateway forwards the MT message to the CDMA-SMS. The CDMA-SMS delivers the MT message, and the message is processed according to the normal flow. Then, the CDMA-SMS sends the SMS-REQ message to the CDMA-HLR for obtaining the route. 8) 9) The CDMA-HLR returns the SMS-REQ-RESP message, which contains MSC information. The CDMA-SMS delivers the SM to the CDMA-MSC, and the latter delivers the SM to the mobile phone. 10) The CDMA-MSC returns the SMDPP_RESP message.
Huawei Technologies Proprietary 6-6
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
11) The CDMA-SMS returns the FORWARDMESSAGE_RESP message to the signaling gateway according to the delivery result. 12) The signaling gateway forwards the FORWARDMESSAGE_RESP message to the GSM-SC.
IV. Flow of forwarding SMs between SMS systems for the GSM network
Figure 6-6 shows the flow.
Home SMS system of the Calling party calling party (1) MO-FowardSM (2) MO-FowardSM _Resp Home SMS system of the called party
HLR
Called party
(3) Query the home SMC of the called party
(4) MO-FowardSM (5) MO-FowardSM _Resp
(6) sendRouting InfoforSM (6) sendRouting InfoforSM_Resp (7) MT-FowardSM
(10) Send the status report message (11)Receives the status report response message (13) Forward the status report message (14 )Receive the status report response message (12)Write the charging bill according to the status report
(8) MT-FowardSM _Resp
Figure 6-6 Flow of forwarding SMs between SMS systems for the GSM network The flow is described as follows: 1) 2) 3) Subscriber A (calling party) sends an SM to subscriber B (called party). The message is submitted to the SMS system. The home SMS system of the calling party returns the Mo-ForwardSM-resp message. After finding that subscriber B does not belong to the local SMS system, the SMS system queries the home SMC address of the called party, and starts the SM forwarding flow. If the SMS system cannot find the home SMC address of the
Huawei Technologies Proprietary 6-7
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
called party in the configuration file, it delivers the SM according to the traditional delivery mode of home SMS system of the calling party. 4) 5) The home SMS system of the calling party forwards the SM to the home SMS system of the called party by sending the Mo-ForwardSM message. Upon receiving the SM forwarded by the home SMS system of the calling party, the home SMS system of the called party checks whether the opposite SMS system is an authentication SMS system. If not, it rejects the SM. Upon receiving the SM, the home SMS system of the called party returns the Mo-ForwardSM-resp message. 6) The home SMS system of the called party queries route information of the called party from the HLR of the called party by sending the sendRoutingInfoForSM message. 7) 8) 9) The HLR of the called party returns route information of the called party to the home SMS system of the called party. The home SMS system of the called party delivers the Mt-ForwardSM message to subscriber B. Subscriber B returns the Mt-ForwardSM-resp to the home SMS system of the called party. 10) After the forwarded SM is delivered successfully or unsuccessfully, for example, the SM has not been delivered successfully yet after its life cycle ends, the home SMS system of the called party generates a final status report and forwards it to the home SMS system of the calling party by sending the MT-ForwardSM message. 11) The home SMS system of the calling party obtains the final delivery status of the SM from the received final status report. 12) The home SMS system of the calling party records the charging bills of SMs according to the status report. 13) The home SMS system of the calling party forwards the status report to the calling party if required. 14) The called party returns a response upon receiving the status report.
V. Flow of a CDMA subscriber sending an SM to a GSM subscriber
l
After a CDMA subscriber sends an SM to a GSM subscriber, the SM is first submitted to the SMS system for the CDMA network. Two subsequent flows are available: The CDMA-SMS directly obtains the route from the GSM-HLR by simulating the SMS system for the GSM network, and delivers the SM through the GSM-MSC. In this case, the CDMA-SMS does not exchange messages with the GSM-SC.
The CDMA-SMS delivers an MO message to the GSM-SC by simulating the GSM-MSC, and the GSM-SC delivers the SM.
The following describes these two flows respectively.
Huawei Technologies Proprietary 6-8
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
Figure 6-7 illustrates the flow of a CDMA subscriber sending an SM to a GSM subscriber.
GSM-MSC GSM-HLR (2) SRI (3) SRI_RESP (4) SRI_RESP (5) ForwardMessge(MT) ITP/STP (1) SRI CDMA-MC
(6) ForwardMessage(MT) (7) FordwardMessage_ Resp(MTACK)
(8) FordwardMessage_ Resp(MTACK)
Figure 6-7 Flow of a CDMA subscriber sending an SM to a GSM subscriber The flow is described as follows: 1) After the CDMA-SMS receives the SM from the calling party, the SM is processed according to the normal flow of processing GSM SMs. Then, the CDMA-SMS obtains the route for the GSM subscriber, and sends the SRI message to the signaling gateway, that is, ITP or STP. 2) 3) 4) 5) 6) 7) 8) The signaling gateway forwards the SRI message to the GSM-HLR. The GSM-HLR returns the SRI-RESP message, which contains the current serving MSC number of the called party. The signaling gateway forwards the SRI_RESP message to the CDMA-SMS. The CDMA-SMS sends the MT message to the signaling gateway according to the obtained route. The signaling gateway sends the MT message to the GSM-MSC. The GSM-MSC sends the message to the called party through the wireless network, and returns the MTACK message to the signaling gateway. The signaling gateway forwards the MTACK message to the CDMA-SMS.
VI. Flow of the CDMA signaling processing module of the SMS system submitting the MO message to the SMS system for the GSM network by simulating the GSM-MSC
Figure 6-8 illustrates the message flow.
Huawei Technologies Proprietary 6-9
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
GSM-MSC
GSM-HLR
GSM-SC
ITP/STP
(2) ForwardMessage (MO) (3) ForwardMessage _Resp (MOACK) (5) SRI (6) SRI_Resp (7) ForwardMessage (MT) (8) ForwardMessage _Resp (MTACK)
CDMA-MC (1) ForwardMessage (MO)
(4) ForwardMessage _Resp (MOACK)
Figure 6-8 Flow of the CDMA signaling processing module of the SMS system submitting the MO message to the SMS system for the GSM network by simulating the GSM-MSC The flow is described as follows: 1) Upon receiving the SM submitted by the calling party, the CDMA-SMS sends an MO message to the signaling gateway, that is, ITP or STP by simulating the GSM-SMC. 2) 3) 4) 5) 6) 7) 8) The signaling gateway forwards the MO message to the GSM-SC. Upon receiving the MO message, the GSM-SC returns the MOACK message to the signaling gateway. The signaling gateway forwards the MOACK message to the CDMA-SMS. The GSM-SC processes the SM according to the normal delivery flow, and obtains the route from the GSM-HLR. The GSM-HLR returns route information to the GSM-SC. The GSM-SC sends the SM to the GSM-MSC according to the MSC number. The GSM-MSC delivers the SM to the destination GSM mobile phone through the wireless network, and returns the MTACK message to the GSM-SC. You can flexibly select one of the preceding-mentioned schemes of sending SMs from the CDMA network to the GSM network according to actual situations.
& Note: You can replace the CDMA network with the TDMA network in the preceding description because the signaling flow on the MAP layer in the CDMA network is the same as that in the TDMA network.
Huawei Technologies Proprietary 6-10
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
VII. Flow of forwarding SMs between SMS systems for the CDMA network
Figure 6-9 shows the flow.
MS(A) (1) SMDPP
MC(A)
MC(B)
MS(B)
(2) smdpp
(3) SMDPP
(4) smdpp
(5) SMDPP (6) smdpp
(7) SMDPP
(8) smdpp
Figure 6-9 Flow of forwarding SMs between SMS systems for the CDMA network The flow is described as follows: 1) 2) 3) 4) 5) 6) 7) 8) Subscriber A submits an SM to SMS system A. SMS system A sends an smdpp message to subscriber A, indicating submission success. The destination subscriber B does not belong to SMS system A, so SMS system A sends the SM to SMS system B through the SMDPP operation. SMS system B sends an smdpp message to SMS system A, indicating forwarding success. SMS system B sends the SM to subscriber B. Subscriber B sends an smdpp message to SMS system B, indicating delivery success. SMS system B sends the SM delivery status notification to SMS system A through the SMDPP operation. SMS system A sends an smdpp message to SMS system B, responding to the SM delivery status notification.
Huawei Technologies Proprietary 6-11
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 6 Typical System Applications
VIII. SM exchange between SMS systems
There are four types of SM exchange between SMS systems: For SM exchange between SMS systems for the GSM network, refer to part 4 Flow of forwarding SMs between SMS systems for the GSM network in this section. For SM exchange between SMS systems for the CDMA network, refer to part 2 MO and MT flows in the CDMA network in this section. For SM sending from SMS systems for the GSM network to those for the CDMA network, refer to part 3 Flow of a GSM subscriber sending an SM to a CDMA subscriber in this section. For SM sending from SMS systems for the CDMA network to those for the GSM network, refer to part 5 Flow of a CDMA subscriber sending an SM to a GSM subscriber in this section.
Huawei Technologies Proprietary 6-12
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 7 Technical Indexes and Specifications
Chapter 7 Technical Indexes and Specifications
This chapter introduces the performance indexes of the infoX-SMS system and specifications this system abides by. By reading this chapter, you can know technical indexes and specifications of the infoX-SMS system.
7.1 Hardware Specifications
The SMS system uses N610-22 cabinets. The N610-22 assembly cabinet holds networking parts of the relative product, including server, KVM switcher, memory device, LAN switch, firewall and so on. The outer sizes of the N610-22 assembly cabinet are as follows:
l l l
High: 2200 mm Width: 600 mm Depth: 1000 mm
The inner sizes of the N610-22 assembly cabinet are as follows:
l l l
High: 46U (1U=44.45 mm, 46U=2044.70 mm) Width: 19 inch (1 inch=25.4 mm, 19 inch=482.6 mm) Depth: 750 mm
N610-22 assembly cabinet uses -48V DC power, and working power input ranges between -40V and -57V. The cabinet has working grounding, protection grounding and lightning protection grounding. The host cabinet and standby cabinet use power supply of double load sharing mode. Power consumption is 4230w when N610-22 assembly cabinet in full configuration. Table 7-1 shows the consumption of respective equipment. Table 7-1 Description of equipment consumption Device Power distribution box Fan module frame LAN Switch KVM Switcher ATCA frame CPCI frame 20 60 2 x 30 180 130 2800 600 Power consumption (W)
Huawei Technologies Proprietary 7-1
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 7 Technical Indexes and Specifications
Device Memory device Tape drive (optional) Total consumption 480 500 4830
Power consumption (W)
7.2 Performance Specifications
Table 7-2 shows performance indexes of the SMS system. Table 7-2 Performance indexes description System configuration Main performance indexes in the case of the GSM network Maximum MO rate: 800 pieces per second Windows 2003/ATAE, 2 x 2.8GHz CPU, 4GB memory. The SMSC and the database are installed on different computers. Maximum MT rate: 800 pieces per second Number of SMs in the memory: 400000 Number of entities in the memory: 400000 Number of SMPP ports: 30 Maximum MO rate: 800 pieces per second SuSE Linux 9+SP2/ATAE, 2 x 2.8GHz CPU, 4GB memory. The SMSC and the database are installed on different computers. Maximum MT rate: 800 pieces per second Number of SMs in the memory: 400000 Number of entities in the memory: 400000 Number of SMPP ports: 30 Same as the GSM network. Same as the GSM network. Main performance indexes in the case of the CDMA or TDMA network
7.3 International Standard Followed by the SMS System
Huawei-developed infoX-SMS system is designed based on the following standards:
l
YD/T 1039-2000 900/1800MHz TDMA Digital Cellular Mobile Communications Network Short Message Center Equipment Specifications, Volume I Point-to-Point Short Message Service
YD/T 1040-2000 900/1800MHz TDMA Digital Cellular Mobile Communications Network Short Message Center Equipment Test Specifications, Volume I Point-to-Point Short Message Service
Huawei Technologies Proprietary 7-2
PDF "pdfFactory Pro" www.fineprint.cn
infoX-SMS System Description
Chapter 7 Technical Indexes and Specifications
YD/T 1094-2000 900/1800MHz TDMA Digital Cellular Mobile Communications Network, Interface Protocols for the Connection of External Short Message Entities (ESMEs) to Short Message Centers (SMCs)
Part I GB 13000.1-93 Information Technology Universal 8-BIT Coding Character Set (UCS): Architecture And Multi-Language Plane YD/T 910.4-1997 Technical Specifications for 900/1800MHz TDMA Digital Cellular Mobile Communications Network Mobile Application Part (MAP) Phase II
ETSI GSM Specifications 03.38 (5.2.0): European Digital Cellular Communications System; Character and Specific Language Information ETSI GSM Specifications 03.40 (4.9.1): European Digital Cellular Communications System; Point-to-Point Short Message Service Technique Implementation
ETSI GSM Specifications 04.11 (4.8.0): European Digital Cellular Communications System; Support of Point-to-Point Short Message Service at the Radio Interface
ETSI GSM Specifications 03.47(5.0.0): European Digital Cellular Communications System; Example of Protocol Stack for Interoperability Between the Service Center and Mobile Switching Center
ETSI GSM Specifications 09.02(6.3.0): ETSI GSM 09.02 Version 6.3.0: Mobile Application Part Specification (Phase 2+) 800 MHz CDMA Digital Cellular Mobile Communications Network, Interface Protocols for the Connection of External Short Message Entities (ESMEs) to Short Message Centers (SMCs)
800 MHz CDMA Digital Cellular Mobile Communications Network Short Message Center Equipment Specifications, Point-to-Point Short Message Service
YD/T 1031-1999 800 MHz CDMA Digital Cellular Mobile Communications Network, Technical Specification for Signaling System Mobile Application Part (MAP)
ANSI T1.114-1988 Signaling System Number7 (SS7)-Transaction Capabilities Application Part (TCAP) Short Message Service for Spread Spectrum Systems (ANSI/TIA/EIA-637-A) ANSI/TIA/EIA-41-D-1997, Cellular Radio telecommunications Intersystem Operations ANSI/TIA/EIA-841, TIA/EIA-41-D Based Network Enhancements for MDN Based Message Centers IS824 CDMA Cell Broadcast Short Message Service Specifications
l l
Huawei Technologies Proprietary 7-3
PDF "pdfFactory Pro" www.fineprint.cn
Вам также может понравиться
- Triple Play: Building the converged network for IP, VoIP and IPTVОт EverandTriple Play: Building the converged network for IP, VoIP and IPTVОценок пока нет
- ZXIN10 SACP IMP Platform Installation GuideДокумент55 страницZXIN10 SACP IMP Platform Installation GuideAhmed Hamed BadrОценок пока нет
- Technical Manual TELLIN-USAU Universal Signaling Access UnitДокумент86 страницTechnical Manual TELLIN-USAU Universal Signaling Access Unitrobins rajОценок пока нет
- SCP Service Control Point 032010 enДокумент4 страницыSCP Service Control Point 032010 enGökhan TunaОценок пока нет
- Huawei OCSДокумент114 страницHuawei OCSeilou linОценок пока нет
- OWG000203 MSOFTX3000 Local Office Data Configuration ISSUE 1.2Документ45 страницOWG000203 MSOFTX3000 Local Office Data Configuration ISSUE 1.2Hoàng Quốc VươngОценок пока нет
- 01-07 Configuring Trunk DataДокумент141 страница01-07 Configuring Trunk DatarajboothОценок пока нет
- SMSC Integration PlanДокумент15 страницSMSC Integration PlanmathewmitОценок пока нет
- SMS Procedures and Trouble ShootingДокумент59 страницSMS Procedures and Trouble ShootingRandyОценок пока нет
- ZXIN10 System Network Architecture 0Документ25 страницZXIN10 System Network Architecture 0Ahmed Hamed Badr100% (1)
- Gprs Asn1 CDRДокумент65 страницGprs Asn1 CDRJackson MwambopoОценок пока нет
- 32.1.3.12 CN - PD - 12 ZXUN TAS Product DescriptionДокумент70 страниц32.1.3.12 CN - PD - 12 ZXUN TAS Product DescriptionRajesh PorwalОценок пока нет
- OWG000204 Interworking With HLR Data Configuration (IP) - Issue1.1Документ32 страницыOWG000204 Interworking With HLR Data Configuration (IP) - Issue1.1Kumaraguru Sathiyaseelan100% (1)
- NGN Fault Analysis SoftX3000Документ73 страницыNGN Fault Analysis SoftX3000samba5113100% (2)
- Challenges in Online Charging System VirtualizationДокумент45 страницChallenges in Online Charging System VirtualizationMagnus Abrahamsson100% (3)
- GSM R Hlr9820Документ0 страницGSM R Hlr9820futronoОценок пока нет
- 4WG001102 MSOFTX3000 Hardware Structure ISSUE 1.0Документ68 страниц4WG001102 MSOFTX3000 Hardware Structure ISSUE 1.0Mohamed H. GooniОценок пока нет
- 05-Chapter 5 SIGTRAN PDFДокумент112 страниц05-Chapter 5 SIGTRAN PDFMarouane Elmoatadid BillahОценок пока нет
- NGN ZteДокумент20 страницNGN ZteAnouar Aleya100% (3)
- Application Server ProvisioningДокумент78 страницApplication Server ProvisioningevildesirezОценок пока нет
- Descritivo Tecnico Do ProdutoДокумент88 страницDescritivo Tecnico Do Produtofreddy novalОценок пока нет
- Technical Manual - System Description HUAWEI HLR9820 Home Location RegisterДокумент45 страницTechnical Manual - System Description HUAWEI HLR9820 Home Location RegisterRaufrmzОценок пока нет
- HUAWEI CG9812 V300R001 Product DescriptionДокумент26 страницHUAWEI CG9812 V300R001 Product Descriptionrosan.sapkota0% (2)
- SMSC MT Console HuaweiДокумент40 страницSMSC MT Console Huaweia2zzmanОценок пока нет
- 8DG43091JAAA - V1 - 1350 OMS OIS TMF814 CORBA Interface Specification, 12.3, Issue 1Документ552 страницы8DG43091JAAA - V1 - 1350 OMS OIS TMF814 CORBA Interface Specification, 12.3, Issue 1Yves MarianoОценок пока нет
- OWD090700 (Slide) GGSN9811 V900R007C02 Product Overview-20090928-B-V1.0Документ44 страницыOWD090700 (Slide) GGSN9811 V900R007C02 Product Overview-20090928-B-V1.0elmanzanedaОценок пока нет
- Msoftx3000 v1r7c01 Guide To Embedded MGCFДокумент28 страницMsoftx3000 v1r7c01 Guide To Embedded MGCFAriel MendozaОценок пока нет
- In Product Advanced Training On USAU OveДокумент52 страницыIn Product Advanced Training On USAU OveInam KhosaОценок пока нет
- MSOFTX3000 RNC ConfigurationДокумент17 страницMSOFTX3000 RNC ConfigurationAmro GoneimОценок пока нет
- Diameter Interfaces and 3GPP SpecificationsДокумент5 страницDiameter Interfaces and 3GPP Specificationsariful_islam_20067643100% (1)
- UGW9811 V900R009 Product DescriptionДокумент55 страницUGW9811 V900R009 Product DescriptionEnrique Zegarra100% (1)
- Huawei Umg8900-TrainingДокумент69 страницHuawei Umg8900-TrainingduyckОценок пока нет
- Huawei InfoX USSD-GwДокумент37 страницHuawei InfoX USSD-Gwariful_islam_2006764350% (2)
- MSOFTX3000 ATCA Platform Data Configuration of Hardware and Module Groups-20090622-B-1.0Документ51 страницаMSOFTX3000 ATCA Platform Data Configuration of Hardware and Module Groups-20090622-B-1.0hanedОценок пока нет
- ASN.1 Tags Used in The Call Data Records For UMTS R3 / GSM R10, ETSI and Japanese MarketsДокумент57 страницASN.1 Tags Used in The Call Data Records For UMTS R3 / GSM R10, ETSI and Japanese MarketsmagelasilvaОценок пока нет
- SJ-20100630164932-055-ZXSS10 SS1b (V2.0.1.07) SoftSwitch Control Equipment PC Server Telnet Configuration - 278953Документ17 страницSJ-20100630164932-055-ZXSS10 SS1b (V2.0.1.07) SoftSwitch Control Equipment PC Server Telnet Configuration - 278953منصورالمغربيОценок пока нет
- IMS Service Centralization and Continuity Guidelines 9 May 2012Документ14 страницIMS Service Centralization and Continuity Guidelines 9 May 2012eru5Оценок пока нет
- 01 - Initial Configuration - (V300R010C03 - 02) PDFДокумент571 страница01 - Initial Configuration - (V300R010C03 - 02) PDFPulsmade MalawiОценок пока нет
- SoftX3000 Technical Manual-Signaling&ProtocolsДокумент487 страницSoftX3000 Technical Manual-Signaling&ProtocolspmilyutinОценок пока нет
- OAX000200 SoftX3000 Data Configuration For h.323 Sip Terminal ISSUE2.0-20041018-AДокумент21 страницаOAX000200 SoftX3000 Data Configuration For h.323 Sip Terminal ISSUE2.0-20041018-ARandyОценок пока нет
- Online Charging System Design Document 2Документ13 страницOnline Charging System Design Document 2Jean NkuruОценок пока нет
- Fe MGWДокумент34 страницыFe MGWAmin100Оценок пока нет
- Number AnalysisДокумент11 страницNumber Analysissamba5113Оценок пока нет
- Number Analysis Huawei - MSCДокумент4 страницыNumber Analysis Huawei - MSCLuis Fernando EspinoОценок пока нет
- DSP RevisionДокумент1 страницаDSP RevisionGaurav Singh ThakurОценок пока нет
- Electronic Communications Committee (ECC) Within The European Conference of Postal and Telecommunications Administrations (CEPT)Документ13 страницElectronic Communications Committee (ECC) Within The European Conference of Postal and Telecommunications Administrations (CEPT)Nagendra BadamОценок пока нет
- 1 OAS025101 SG7000 System Overview ISSUE1.00Документ54 страницы1 OAS025101 SG7000 System Overview ISSUE1.00oscaanzcОценок пока нет
- 2015CustomerTrainingCatalog CourseDescriptions (CN USC)Документ56 страниц2015CustomerTrainingCatalog CourseDescriptions (CN USC)gobinathОценок пока нет
- SG7000 Configuration Examples (V200R005C02 - 02)Документ73 страницыSG7000 Configuration Examples (V200R005C02 - 02)Catherine HiginoОценок пока нет
- 3 MSOFTX3000 Operation Manual Data ConfigurationДокумент424 страницы3 MSOFTX3000 Operation Manual Data ConfigurationOsama Haider100% (7)
- Media Gateway SoftswitchДокумент10 страницMedia Gateway SoftswitchMahmoud Karimi0% (1)
- SE2900 Product Documentation V500R018C10 - 02 20191030150129Документ7 страницSE2900 Product Documentation V500R018C10 - 02 20191030150129hernanОценок пока нет
- HUAWEI SAE-HSS9820 归属用户服务器: IPLOOK NetworksДокумент12 страницHUAWEI SAE-HSS9820 归属用户服务器: IPLOOK NetworksIPLOOK TechnologiesОценок пока нет
- Alarm Description: HUAWEI SE2900 Session Border ControllerДокумент32 страницыAlarm Description: HUAWEI SE2900 Session Border ControllerAbraham KraОценок пока нет
- HUAWEI UGW9811 Unified Gateway V900R011C00 Product DescriptionДокумент65 страницHUAWEI UGW9811 Unified Gateway V900R011C00 Product Descriptionalbraa80100% (1)
- 13.MSOFTX3000 Number Analysis Configuration ISSUE1.00Документ45 страниц13.MSOFTX3000 Number Analysis Configuration ISSUE1.00wessОценок пока нет
- International Roaming GuideДокумент76 страницInternational Roaming Guidevijrag_bit100% (1)
- Customer Training Catalog Course Descriptions: HUAWEI Learning ServiceДокумент45 страницCustomer Training Catalog Course Descriptions: HUAWEI Learning ServicegobinathОценок пока нет
- Drive Test Training Material - Huawei-14032019Документ48 страницDrive Test Training Material - Huawei-14032019Clive Mangwiro86% (7)
- FDD TDD New LayeringДокумент8 страницFDD TDD New LayeringMuhammad Arif Wibowo100% (1)
- DatДокумент7 страницDatSerhat MorsümbülОценок пока нет
- 802.11ac Wireless Access Point Model WAC104: User ManualДокумент79 страниц802.11ac Wireless Access Point Model WAC104: User ManualAjiputrapandhawaОценок пока нет
- Unit 4: Multiplexing and Multi-User AccessДокумент44 страницыUnit 4: Multiplexing and Multi-User AccessdfbbvcxОценок пока нет
- Chapter 6 IctДокумент37 страницChapter 6 IctJood ObeidatОценок пока нет
- 802 11ah Overview Comm Soc r1Документ15 страниц802 11ah Overview Comm Soc r1l386543Оценок пока нет
- 2960 XДокумент3 страницы2960 Xblackmamba etti jeanОценок пока нет
- Dell EMCNetworking MX9116 N Spec SheetДокумент4 страницыDell EMCNetworking MX9116 N Spec SheetmarvinreneОценок пока нет
- CNS 200W en StudentManual v03Документ388 страницCNS 200W en StudentManual v03Luciano FilhoОценок пока нет
- WWW Finetopix ComДокумент3 страницыWWW Finetopix ComBouziane BeldjilaliОценок пока нет
- OEB538110 LTE eRAN15.1 VoLTE Service MonitoringДокумент43 страницыOEB538110 LTE eRAN15.1 VoLTE Service MonitoringRespati Rangga50% (2)
- Assignment Wireless CommunicationДокумент13 страницAssignment Wireless CommunicationSmarika ShresthaОценок пока нет
- Tor PDFДокумент19 страницTor PDFsesogeОценок пока нет
- WiMAX TutorialДокумент45 страницWiMAX TutorialHAMOUD80Оценок пока нет
- Simulation of Bluetooth Modulation in Simulink: Experiment 4Документ4 страницыSimulation of Bluetooth Modulation in Simulink: Experiment 4tiam037Оценок пока нет
- UTM Firewalls: AR3050S and AR4050SДокумент8 страницUTM Firewalls: AR3050S and AR4050SChristian Javier Lopez DuranОценок пока нет
- Marconi OMS 1200 DatasheetДокумент4 страницыMarconi OMS 1200 DatasheethamidОценок пока нет
- De DupeДокумент96 страницDe Dupemrudula rangateОценок пока нет
- Nimbra 390Документ2 страницыNimbra 390Karyadi DjayaОценок пока нет
- Midterm Exam II With Solutions PDFДокумент7 страницMidterm Exam II With Solutions PDFKiruba KaranОценок пока нет
- Eigrp QuizДокумент5 страницEigrp QuizJohn Paul SorianoОценок пока нет
- 61FIT2CNE Tutorial 13 - Dynamic IPv6 Routing Configuration With Ospfv3 (Multiarea)Документ13 страниц61FIT2CNE Tutorial 13 - Dynamic IPv6 Routing Configuration With Ospfv3 (Multiarea)Tùng VũОценок пока нет
- DSLAMДокумент21 страницаDSLAMFaizanAshraf100% (1)
- Chapter 2: Technology Infrastructure: The Internet and The World Wide WebДокумент4 страницыChapter 2: Technology Infrastructure: The Internet and The World Wide WebMuzamil HaqmalОценок пока нет
- Management Information System CHAPTER 4Документ2 страницыManagement Information System CHAPTER 4gut78Оценок пока нет
- Airtel Acquires Warid UgandaДокумент2 страницыAirtel Acquires Warid UgandaThe New VisionОценок пока нет
- ICT2103 - Assignment - August2015 (Group 2 Tan Yih Wei) BVДокумент10 страницICT2103 - Assignment - August2015 (Group 2 Tan Yih Wei) BVHoh Jia HengОценок пока нет
- Key Performance Indicators For Juniper Devices Version 2 2Документ92 страницыKey Performance Indicators For Juniper Devices Version 2 2Anonymous GsZPoVeОценок пока нет
- Nexus VPC and OTVДокумент22 страницыNexus VPC and OTVAsad Hussain ShahОценок пока нет