Академический Документы
Профессиональный Документы
Культура Документы
Ijitce June 2011
Загружено:
sivalaАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Ijitce June 2011
Загружено:
sivalaАвторское право:
Доступные форматы
UK: Managing Editor
International Journal of Innovative Technology and Creative Engineering
1a park lane,
Cranford
London
TW59WA
UK
E-Mail: editor@ijitce.co.uk
Phone: +44-773-043-0249
USA: Editor
International Journal of Innovative Technology and Creative Engineering
Dr. Arumugam
Department of Chemistry
University of Georgia
GA-30602, USA.
Phone: 001-706-206-0812
Fax:001-706-542-2626
India: Editor
International Journal of Innovative Technology & Creative Engineering
Dr. Arthanariee. A. M
Finance Tracking Center India
261 Mel quarters
Labor colony,
Guindy,
Chennai -600032.
Mobile: 91-7598208700
www.ijitce.co.uk
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
IJITCE PUBLICATION
INTERNATIONAL JOURNAL OF INNOVATIVE
TECHNOLOGY & CREATIVE ENGINEERING
Vol.1 No.6
June 2011
www.ijitce.co.uk
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
From Editor's Desk
Dear Researcher,
Greetings!
Research articles in this issue discusses about Decision Tree, Braille hand glove for the blind,
Multi homed Scatter net Network, and Peristaltic pumping.
Let us observe research topics made significant progress around the world for this month, It is
nice to work with the new Windows 7 OS that has a semi-transparent interface. Scientists have
now developed a transparent battery, which could pave way for making cool gadgets. Your
mobiles and other devices can now go transparent.
LEDs save energy usage and cost. You can find that they are being used widely in many
appliances including automobile. A new technology in this is the making of three-dimensional
crystals of photons, which enhance the output of these LEDs. These 3D photon crystals can also
be used in the manufacture of solar panels.
Health wise diabetes is one of the major concerns in the world. Even children are now fallen prey
to it. It is however difficult to monitor the glucose levels in real time and administer insulin at the
required levels. A new advancement has been made in the insulin pump device that can sense
the glucose levels and control the injection of insulin into the body.
It has been an absolute pleasure to present you articles that you wish to read. We look forward
to many more new technology-related research articles from you and your friends. We are
anxiously awaiting the rich and thorough research papers that have been prepared by our
authors for the next issue.
Thanks,
Editorial Team
IJITCE
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
Editorial Members
Dr. Chee Kyun Ng Ph.D
Department of Computer and Communication Systems,
Faculty of Engineering, Universiti Putra Malaysia,UPM Serdang, 43400 Selangor,Malaysia.
Dr. Simon SEE Ph.D
Chief Technologist and Technical Director at Oracle Corporation, Associate Professor (Adjunct) at Nanyang Technological University
Professor (Adjunct) at Shangai Jiaotong University, 27 West Coast Rise #08-12,Singapore 127470
Dr. sc.agr. Horst Juergen SCHWARTZ Ph.D,
Humboldt-University of Berlin, Faculty of Agriculture and Horticulture, Asternplatz 2a, D-12203 Berlin, Germany
Dr. Marco L. Bianchini Ph.D
Italian National Research Council; IBAF-CNR, Via Salaria km 29.300, 00015 Monterotondo Scalo (RM), Italy
Dr. Nijad Kabbara Ph.D
Marine Research Centre / Remote Sensing Centre/ National Council for Scientific Research,
P. O. Box: 189 Jounieh, Lebanon
Dr. Aaron Solomon Ph.D
Department of Computer Science,
National Chi Nan University, No. 303, University Road, Puli Town, Nantou County 54561, Taiwan
Dr. Arthanariee. A. M M.Sc.,M.Phil.,M.S.,Ph.D
Director - Bharathidasan School of Computer Applications, Ellispettai, Erode, Tamil Nadu,India
Dr. Takaharu KAMEOKA, Ph.D
Professor, Laboratory of Food,
Environmental & Cultural Informatics Division of Sustainable Resource Sciences,
Graduate School of Bioresources, Mie University, 1577 Kurimamachiya-cho, Tsu, Mie, 514-8507, Japan
Mr. M. Sivakumar M.C.A.,ITIL.,PRINCE2.,ISTQB.,OCP.,ICP
Project Manager - Software, Applied Materials, 1a park lane, cranford, UK
Dr. Bulent Acma Ph.D
Anadolu University,
Department of Economics, Unit of Southeastern Anatolia Project(GAP), 26470 Eskisehir, TURKEY
Dr. Selvanathan Arumugam Ph.D
Research Scientist, Department of Chemistry, University of Georgia, GA-30602, USA.
Review Board Members
Dr. T. Christopher, Ph.D.,
Assistant Professor & Head,Department of Computer Science,Government Arts College(Autonomous),Udumalpet, India.
Dr. T. DEVI Ph.D. Engg. (Warwick, UK),
Head,Department of Computer Applications,Bharathiar University,Coimbatore-641 046, India.
Dr. Giuseppe Baldacchini
ENEA - Frascati Research Center, Via Enrico Fermi 45 - P.O. Box 65,00044 Frascati, Roma, ITALY.
Dr. Renato J. orsato
Professor at FGV-EAESP,Getulio Vargas Foundation,So Paulo Business School,Rua Itapeva, 474 (8andar) ,01332-000, So Paulo (SP),
Brazil Visiting Scholar at INSEAD,INSEAD Social Innovation Centre,Boulevard de Constance,77305 Fontainebleau - France
Y. Benal Yurtlu
Assist. Prof. Ondokuz Mayis University
Dr. Paul Koltun
Senior Research ScientistLCA and Industrial Ecology Group,Metallic & Ceramic Materials,CSIRO Process Science & Engineering Private Bag
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
33, Clayton South MDC 3169,Gate 5 Normanby Rd., Clayton Vic. 3168
Dr.Sumeer Gul
Assistant Professor,Department of Library and Information Science,University of Kashmir,India
Chutima Boonthum-Denecke, Ph.D
Department of Computer Science,Science & Technology Bldg., Rm 120,Hampton University,Hampton, VA 23688
Dr. Renato J. Orsato
Professor at FGV-EAESP,Getulio Vargas Foundation,So Paulo Business SchoolRua Itapeva, 474 (8andar), 01332-000, So Paulo (SP), Brazil
Lucy M. Brown, Ph.D.
Texas State University,601 University Drive,School of Journalism and Mass Communication,OM330B,San Marcos, TX 78666
Javad Robati
Crop Production Departement,University of Maragheh,Golshahr,Maragheh,Iran
Vinesh Sukumar (PhD, MBA)
Product Engineering Segment Manager, Imaging Products, Aptina Imaging Inc.
doc. Ing. Rostislav Choteborsk, Ph.D.
Katedra materilu a strojrensk technologie Technick fakulta,Cesk zemedelsk univerzita v Praze,Kamck 129, Praha 6, 165 21
Dr. Binod Kumar M.sc,M.C.A.,M.Phil.,ph.d,
HOD & Associate Professor, Lakshmi Narayan College of Tech.(LNCT), Kolua, Bhopal (MP) , India.
Dr. Paul Koltun
Senior Research ScientistLCA and Industrial Ecology Group,Metallic & Ceramic Materials,CSIRO Process Science & Engineering Private Bag
33, Clayton South MDC 3169,Gate 5 Normanby Rd., Clayton Vic. 3168
DR.Chutima Boonthum-Denecke, Ph.D
Department of Computer Science,Science & Technology Bldg.,Hampton University,Hampton, VA 23688
Mr. Abhishek Taneja B.sc(Electronics),M.B.E,M.C.A.,M.Phil.,
Assistant Professor in the Department of Computer Science & Applications, at Dronacharya Institute of Management and Technology,
Kurukshetra. (India).
doc. Ing. Rostislav Chotborsk,ph.d,
Katedra materilu a strojrensk technologie, Technick fakulta,esk zemdlsk univerzita v Praze,Kamck 129, Praha 6, 165 21
Dr. Amala VijayaSelvi Rajan, B.sc,Ph.d,
Faculty Information Technology Dubai Womens College Higher Colleges of Technology,P.O. Box 16062, Dubai, UAE
Naik Nitin Ashokrao B.sc,M.Sc
Lecturer in Yeshwant Mahavidyalaya Nanded University
Dr.A.Kathirvell, B.E, M.E, Ph.D,MISTE, MIACSIT, MENGG
Professor - Department of Computer Science and Engineering,Tagore Engineering College, Chennai
Dr. H. S. Fadewar B.sc,M.sc,M.Phil.,ph.d,PGDBM,B.Ed.
Associate Professor - Sinhgad Institute of Management & Computer Application, Mumbai-Banglore Westernly Express Way Narhe, Pune - 41
Dr. David Batten
Leader, Algal Pre-Feasibility Study,Transport Technologies and Sustainable Fuels,CSIRO Energy Transformed Flagship Private Bag
1,Aspendale, Vic. 3195,AUSTRALIA
Dr R C Panda
(MTech & PhD(IITM);Ex-Faculty (Curtin Univ Tech, Perth, Australia))Scientist CLRI (CSIR), Adyar, Chennai - 600 020,India
Miss Jing He
PH.D. Candidate of Georgia State University,1450 Willow Lake Dr. NE,Atlanta, GA, 30329
Dr. Wael M. G. Ibrahim
Department Head-Electronics Engineering Technology Dept.School of Engineering Technology ECPI College of Technology 5501 Greenwich
Road - Suite 100,Virginia Beach, VA 23462
Dr. Messaoud Jake Bahoura
Associate Professor-Engineering Department and Center for Materials Research Norfolk State University,700 Park avenue,Norfolk, VA 23504
Dr. V. P. Eswaramurthy M.C.A., M.Phil., Ph.D.,
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
Assistant Professor of Computer Science, Government Arts College(Autonomous), Salem-636 007, India.
Dr. P. Kamakkannan,M.C.A., Ph.D .,
Assistant Professor of Computer Science, Government Arts College(Autonomous), Salem-636 007, India.
Dr. V. Karthikeyani Ph.D.,
Assistant Professor of Computer Science, Government Arts College(Autonomous), Salem-636 008, India.
Dr. K. Thangadurai Ph.D.,
Assistant Professor, Department of Computer Science, Government Arts College ( Autonomous ), Karur - 639 005,India.
Dr. N. Maheswari Ph.D.,
Assistant Professor, Department of MCA, Faculty of Engineering and Technology, SRM University, Kattangulathur, Kanchipiram Dt - 603 203,
India.
Mr. Md. Musfique Anwar B.Sc(Engg.)
Lecturer, Computer Science & Engineering Department, Jahangirnagar University, Savar, Dhaka, Bangladesh.
Mrs. Smitha Ramachandran M.Sc(CS).,
SAP Analyst, Akzonobel, Slough, United Kingdom.
Dr. V. Vallimayil Ph.D.,
Director, Department of MCA, Vivekanandha Business School For Women, Elayampalayam, Tiruchengode - 637 205, India.
Mr. M. Rajasenathipathi M.C.A., M.Phil
Assistant professor, Department of Computer Science, Nallamuthu Gounder Mahalingam College, India.
Mr. M. Moorthi M.C.A., M.Phil.,
Assistant Professor, Department of computer Applications, Kongu Arts and Science College, India
Prema Selvaraj Bsc,M.C.A,M.Phil
Assistant Professor,Department of Computer Science,KSR College of Arts and Science, Tiruchengode
Mr. V. Prabakaran M.C.A., M.Phil
Head of the Department, Department of Computer Science, Adharsh Vidhyalaya Arts And Science College For Women, India.
Mrs. S. Niraimathi. M.C.A., M.Phil
Lecturer, Department of Computer Science, Nallamuthu Gounder Mahalingam College, Pollachi, India.
Mr. G. Rajendran M.C.A., M.Phil., N.E.T., PGDBM., PGDBF.,
Assistant Professor, Department of Computer Science, Government Arts College, Salem, India.
Mr. R. Vijayamadheswaran, M.C.A.,M.Phil
Lecturer, K.S.R College of Ars & Science, India.
Ms.S.Sasikala,M.Sc.,M.Phil.,M.C.A.,PGDPM & IR.,
Assistant Professor,Department of Computer Science,KSR College of Arts & Science,Tiruchengode - 637215
Mr. V. Pradeep B.E., M.Tech
Asst. Professor, Department of Computer Science and Engineering, Tejaa Shakthi Institute of Technology for Women, Coimbatore, India.
Dr. Pradeep H Pendse B.E.,M.M.S.,Ph.d
Dean - IT,Welingkar Institute of Management Development and Research, Mumbai, India
Mr. K. Saravanakumar M.C.A.,M.Phil., M.B.A, M.Tech, PGDBA, PGDPM & IR
Asst. Professor, PG Department of Computer Applications, Alliance Business Academy, Bangalore, India.
Muhammad Javed
Centre for Next Generation Localisation, School of Computing, Dublin City University, Dublin 9, Ireland
Dr. G. GOBI
Assistant Professor-Department of Physics,Government Arts College,Salem - 636 007
Dr.S.Senthilkumar
Research Fellow,Department of Mathematics,National Institute of Technology (REC),Tiruchirappli-620 015, Tamilnadu, India.
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
Contents
1. Coefficient of Variation based Decision Tree (CvDT) .[1]
2. Use Of Braille Database For Design And Implementation Of Braille Handglove For Deafblind
People..[7]
3. Development of Reliable Multihomed Scatternet Network[13]
4. Peristaltic Pumping Of a Micropolar Fluid In An Inclined Channel.[22]
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
1
Coefficient of Variation based Decision Tree
(CvDT)
Hima Bindu K
#1
, Swarupa Rani K
#2
, Raghavendra Rao C
#3
#
Department of Computer and Information Sciences, University of Hyderabad
Hyderabad, 500046, India
1
himagopal@gmail.com,
2
swarupacs@uohyd.ernet.in,
3
crrcs@uohyd.ernet.in
Abstract Decision trees are widely used for
classification. Several approaches exist to induce
decision trees. All these methods vary in attribute
selection measures i.e., in identifying an attribute to split
at a node. This paper proposes a novel splitting criteria
based on Coefficient of Variation and it is named as
Coefficient of Variation Gain (CvGain). The decision trees
built with CvGain are compared with those built with
Entropy and Gainfix. Empirical analysis based on
standard data sets revealed that Coefficient of Variation
based decision tree (CvDT) has less computational cost
and time.
Keywords: Coefficient of Variation; CvGain; Decision
Tree; Splitting Criteria
I. INTRODUCTION
Decision trees are well known for classification [6].
Decision trees are easy to interpret and they simplify the
complex decision making process. ID3 [10], C4.5 [11],
CART [2] are few popular implementations of decision
trees. ID3 algorithm is the first decision tree
implementation. Building a decision tree follows a
greedy approach for choosing the best attribute for
splitting at a node. Splitting criteria plays a vital role in
building a decision tree. Information Gain, Gain ratio,
Gini index, Chi square statistics and Kappa index are
the well known splitting criteria. Coefficient of Variation
(Cv) [13], is a measure of consistency of a distribution
and is used in applied domain. The application of Cv for
constructing risk trees in managerial studies is
demonstrated in [3]. Cv has not attracted the
researchers of data mining as a splitting criteria till date.
Cv is a normalized measure of dispersion of a
probability distribution. This paper proposes building a
decision tree using Cv. ID3, proposed by Quinlan uses
Information gain for attribute selection, which is based
on information theory. But Information Gain is biased
towards multi-valued attributes. C4.5 is a successor of
ID3 and uses gain ratio, which is an extension of
Information gain. Gain ratio overcomes the biasing for
multi-valued attributes by applying some normalization
to Information Gain. But Gain ratio tends to prefer
unbalanced splits. The Gini index which considers a
binary split for each attribute is used by CART. But Gini
index also prefers multi-valued attributes and has a
difficulty in dealing large number of classes. The
limitations of impurity based measures like Information
gain and Gini index are given by [5]. They have
proposed a class of attribute selection measures called
C-SEP to overcome those limitations.
Reference [7] has applied ID3 on the reduced data
obtained by reduct attributes based on rough set theory
[9]. Reduct selects only predominant attributes. Thus
one can achieve dimension reduction. It is reported that
the resulting tree generates fewer classification rules
with comparable classification accuracy to ID3.
Reference [12] has built a reduct based decision tree
where the splitting attributes are selected according to
their order of presence in the reduct. To the best of our
knowledge, the latest splitting criteria used was based
on Kappa index as proposed in [4]. They proposed fixed
information gain, called as Gainfix , as the new standard
for selecting splitting attributes. Gainfix considers
relationship between condition attributes and decision
attributes in addition to Information Gain. They claimed
that the decision tree (which is named as FID3 by them)
built using Kappa achieves better performance and
simpler decision tree than ID3.
Since its inception, ID3 has been thoroughly studied
by various researchers. ID3 uses Information Gain as
the splitting criteria. But Information Gain uses
frequencies ignoring its ordinates and is based on the
Entropy which invokes logarithmic function several
times. The computation of Cv is less expensive as it
uses simple arithmetic operations and square root
function. This contrasting feature inspired the present
study to use Cv for construction of decision trees. The
tree built based on the Cv will be called as Cv based
Decision Tree, in short CvDT. As the computational
complexity of Cv is low, it is expected that Cv based
decision tree construction will take less time. This is
proved by the hypothesis test performed with paired t-
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
2
test. Hence it is suitable for agent based applications,
where a decision tree has to be built in real time.
The performance characteristics have been tabulated
using tenfold cross validation test on the proposed CvDT
as well as on ID3 and FID3 methods for evaluation
purpose.
This paper is organized as follows: Section 2
illustrates Coefficient of variation and introduces CvGain
along with computations. The CvDT algorithm is
discussed in Section 3. Section 4 illustrates CvDT
construction with a simple example. Section 5 describes
the data sets considered for validation and the adopted
validation procedure. Section 6 brings out contrasting
features of CvDT and ID3. The paper concludes with
section 7.
II. CVGAIN
A. Coefficient of Variation
Coefficient of Variation [13], [1] is the ratio of standard
deviation and mean .
Cv =
(1)
Coefficient of Variation is a dimensionless number
and hence it is suitable for comparing data in different
units or with widely different means. Cv is defined for
non zero mean. The computation of Cv is illustrated with
Table I data. This data contains two attributes: High
School GPA (called as A1) and College GPA (called as
A2).
TABLE I
GPA DATA
Student A1 A2 D
S1 3 2 2
S2 3 1 3
S3 4 3 1
S4 2 1 3
S5 3 3 2
The computations of Cv for each attribute of GPA
data are given below.
Cv(A1)=(A1)/(A1)*100 = (0.6325/3)*100 = 21.0819
Cv(A2)=(A2)/(A2) *100 = (0.8944/2)*100 = 44.7214
Cv(D)=(D)/(D) *100 = (0.7483/2.2 )*100 = 34.0151
B. CvGain
Let DT be the decision table which is preprocessed
such that Cv can be computed.
Let DT = [A1, A2, A3 An, D] where A1, A2.An are
the conditional attributes and D is the decision attribute.
Coefficient of Variation of decision attribute D is given
by
Cv(D) = 100 *
) (
) (
D
D
(2)
Coefficient of Variation of D conditioned on Ai having
v distinct values (a1, a2 av) is given by
Cv(D|Ai) = ) | (
1
j i
v
j
j
a A D Cv P =
=
(3)
Where aj is the jth possible value of Ai with chance Pj
And
CvGain ( Ai ) = Cv(D) Cv(D|Ai) (4)
Using GPA data (Table II), the detailed computations
of CvGain are given below along with the conditional
tables for Cv (D|A).
TABLE II
CONDITIONAL TABLE WITH A1 = 2
Student A1 D
S4 2 3
From Table II, Cv(D|A1 = 2) = 0/3 * 100 = 0.
TABLE III
CONDITIONAL TABLE WITH A1 = 3
Student A1 D
S1 3 2
S2 3 3
S5 3 2
From Table III, Cv(D|A1=3)= 0.4714/ 2.33*100 =
20.20
TABLE IV
CONDITIONAL TABLE WITH A1 = 4
Student A1 D
S3 4 1
From Table IV, Cv(D|A1 = 4) = 0/1 * 100 = 0
Assuming that P (Ai = aj) is the probability that
attribute Ai takes the value aj,
Cv(D|A1)=P(A1=2)*Cv(D|A1=2)+P(A1=3)*Cv(D|A1=3
) + P(A1=4)*Cv(D|A1=4)
Hence,
Cv(D|A1)=1/5*0 + 3/5*20.2031 + 1/5*0 = 12.1219
CvGain( A1 ) = 34.0151 - 12.1219 = 21.8932
With similar calculations for attribute A2,
Cv(D | A2 = 1) = 0 /3 *100 = 0
Cv(D | A2 = 2) = 0/2 *100 = 0
Cv(D | A2 = 3) = 0.5/1.5 *100 = 33.3333
Cv(D|A2) = 2/5*0 + 1/5*0 + 2/5*33.33 = 13.33
CvGain(A2) = 34.0151 - 13.3333 = 20.6818
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
3
As CvGain(A1) is large when compared with
CvGain(A2), A1 is selected as the splitting attribute.
C. Algorithm
Algorithm CvDT: Generate CvDT from the decision
table DT.
Input: Decision Table DT with attribute_list and decision
attribute D.
Output: CvDT
Method:
(1) create a node N;
(2) if Cv(D)=0 then
(3) return N as a leaf node labeled with the class
C, the class of all tuples;
(4) if attribute_list is empty then
(5) return N as a leaf node labeled with the
majority_class in D; //majority voting
(6) splitting attribute = max( CvGain ( attribute_list) )
(7) attribute_list = attribute_list splitting_ attribute;
(8) for each value j of splitting_ attribute //partition the
//tuples and grow sub trees for each partition
(9) DT
j
= { tuples in DT with splitting_ attribute = j
};
(10) if DT
j
= then
(12) create a leaf node labeled with majority
class in DT
j
and attach it to node N;
(13) else attach the node returned by
CvDT(DT
j
, attribute_ list) to node
N;
(14) end for
(15) return N;
III. ILLUSTRATION
The popular Weather data set for the concept Play Tennis
[8)] is considered for illustration purpose(Table V).
TABLE V
DECISION TABLE FOR THE CONCEPT PLAY TENNIS
Outlook Temperature humidity Windy Class
Overcast Hot high False N
Overcast Mild high True N
Overcast Hot normal False N
Overcast Cool normal True N
Rain Mild high False N
Rain Mild high True P
Rain Cool normal False N
Rain Mild normal False N
Rain Cool normal True P
Sunny Hot high False P
Sunny Mild high False P
Sunny Hot high True P
Sunny Cool normal False N
Sunny Mild normal True N
To compute Cv, the mean value need to be non zero.
Hence the data need to be pre-processed in such a way
that avoids mean to be zero. A simple pre processing
which assigns positive integers is used here for
illustration. In fact any pre processing technique which
gives non zero mean is applicable. Table VI shows the
pre-processed data and Table VII shows the CvGain
values.
TABLE VI
PREPROCESSED DECISION TABLE
Outlook Temperature humidity windy Class
2 3 2 1 2
2 2 2 2 2
2 3 1 1 2
2 1 1 2 2
1 2 2 1 2
1 2 2 2 1
1 1 1 1 2
1 2 1 1 2
1 1 1 2 1
3 3 2 1 1
3 2 2 1 1
3 3 2 2 1
3 1 1 1 2
3 2 1 2 2
TABLE VII
CVGAIN VALUES
Attribute CvGain
Outlook 5.73
Temperature 0.45
Humidity 2.42
Windy 0.74
From the Table VII, Outlook has maximum CvGain;
hence the attribute Outlook is selected as splitting
attribute at root node. Hence the data will be split into
three sub tables based on the Outlook values. For
Outlook = 1, 2 and 3 the decision tables are shown in
VIII, IX and X respectively.
TABLE VIII
DECISION TABLE FOR OUTLOOK = 1
Temperature humidity Windy class
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
4
2 2 1 2
2 2 2 1
1 1 1 2
2 1 1 2
1 1 2 1
TABLE IX
DECISION TABLE FOR OUTLOOK = 2
Temperature Humidity windy Class
3 2 1 2
2 2 2 2
3 1 1 2
1 1 2 2
TABLE X
DECISION TABLE FOR OUTLOOK = 3
Temperature humidity windy class
3 2 1 1
2 2 1 1
3 2 2 1
1 1 1 2
2 1 2 2
The corresponding building component of the decision
tree is as shown in figure 1:
Fig. 1. Decision tree with Outlook as splitting criteria at root node.
With similar computations on tables VIII,IX and X, the
decision tree is obtained as shown in figure 2 with
preprocessed codes replaced with their original values.
Fig. 1. Final Decision tree.
IV. EXPERIMENT
To examine the effectiveness of our splitting criteria
on decision tree construction, we collected ten datasets
from UCI machine learning repository, shown in Table
XI.
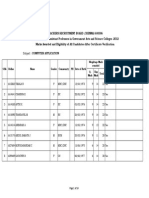
TABLE XI
CHARACTERISTICS OF DATA SETS
S.No Data set Number of
Objects
Number of
Attributes
1 Iris 150 4
2 Wine 178 13
3 Breast cancer 699 10
4 Blood
Transfusion
748 4
5 Abalone 4177 8
6 Ecoli 336 7
7 Yeast 1484 8
8 Page-blocks 5473 10
9 Wine red 1599 11
10 Pima-Indians 768 8
We built decision trees with three different splitting
criteria: Information Gain of ID3, Gainfix of FID3 and
CvGain proposed in this paper. The data sets with
continuous values are discritized. When the data set is
nominal integer codes are used. The data sets are
randomly permuted and tenfold cross validation is
administered. Each time the same partitions of the data
sets are used for building and testing the decision trees.
The philosophy of constructing decision tree algorithm is
the same for all the three trees, only with difference in
the selection criteria. Information Gain, GainFix and
CvGain are used as the attribute selection criteria for
ID3, FID3 and CvDT respectively. We computed the
classification performance and the times taken for
training the decision trees as well as for testing them.
We performed t-test to verify the statistical significance
of our results (we used a standard significance level of
0.05). The characteristics of the datasets are shown in
the table XI. The datasets collected contain 150 tuples
NTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-8711)
VOL.1 NO.6 JUNE 2011
5
as the least and 5473 tuples as the highest. The least
number of attributes taken is 4 while the highest is 13.
The results are shown in table XII.
The advantage of CvGain is revealed in the times
taken for decision tree generation. The generation times
of CvDT are statistically significantly low when
compared to the other two methods. In the case of the
larger datasets considered in this experiment like
Abalone and Page-blocks, the reduction of time is more
clearly visible. With Abalone, 338 and 1672 milliseconds
of time is saved when compared with ID3 and FID3
respectively. Similarly with Page-blocks they are 118
and 2726 milliseconds. Hence it is expected that CvGain
TABLE XII
COMPARISON OF ACCURACY, TIMES FOR CVDT, ID3 AND FID3
Data Classification
Performance
Generation Time in ms Testing Time in ms
CvDT ID3 FID3 CvDT ID3 FID3 CvDT ID3 FID3
Iris 97.33 97.33 97.33 20.25 23.30 43.85 0.06 0.05 0.05
Wine 95.56 97.22 96.67 50.71 76.91 226.08 0.07 0.06 0.06
Breast
cancer
99.43 99.86 99.71 68.39 92.77 280.32 0.24 0.22 0.23
Blood
Transfusion
81.81 81.67 81.81 131.06 153.24 264.64 0.34 0.33 0.33
Abalone 85.80 85.76 85.76 1586.44 1924.62 3258.47 18.01 18.26 21.10
Ecoli 95.88 95.00 95.29 123.71 168.67 319.79 0.13 0.13 0.13
Yeast 92.16 92.30 92.50 792.69 1002.69 1975.08 5.41 5.31 5.27
Page-
blocks
97.15 97.28 97.44 785.26 903.79 3511.66 18.95 18.80 18.30
Wine red 95.63 95.19 95.31 756.97 1071.02 2741.15 5.39 5.51 5.07
Pima-
Indians
95.97 96.23 96.36 265.04 355.26 840.57 2.34 2.33 2.33
is suitable for applications which require the decision
trees to be built in real time.
The Classification Performances are more or less
equal for all the three trees. The observations based on
the experiment are as follows:
1. Basically all the three trees are working on the
same partitions of the data in each the ten folds
used in the experiment.
2. The same procedure is used to build the
decision tree, with the variation in the splitting
criteria.
3. The gain values of the attributes are different
values with CvGain, Information Gain and
GainFix. But the attribute with maximum gain
value is the same with all the three methods for
some of data sets. It is different for some of the
data sets also.
4. It is possible that more than one attribute can
have the maximum Gain value, and one of them
is selected arbitrarily.
5. When the decision trees are verified, the
decision trees built are the same for few data
sets ( Tom Mitchell, Iris, Blood Transfusion, ) but
different with all the other data sets. For some
of the data sets even though the decision trees
are different, it is observed that some sub trees
are being the same. And few Attributes have
interchangeable behavior in terms of selection
for splitting.
The algorithm of the FID3 paper is also
implemented in Matlab environment, to make the
readings comparable. Thus the Classification
Performances reported in the table XII are not the same
as reported in [4]. The time taken for testing the CvDT is
also same as ID3 and FID3. But the time taken for
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
6
generating decision tree using CvDT is significantly less
when compared to ID3 and FID3. The paired t-test on
generation times reveals statistical significance,
indicating that CvDT construction time is significantly
lower than ID3 and FID3. In fact CvDT is outperforming
the other two methods in terms of generation time when
the data sets are large in size. The following figure 3
with the data sets along the X-axes with increasing sizes
reveals this.
Fig. 3. Comparison of Times taken for generating(TG) the three
decision trees
X. CONCLUSION
The criterion for splitting a node in a decision tree
decides the efficiency of a decision tree. So far
Information Gain, Gain ratio, Gini index, Chi square
statistic and Kappa index are used as the splitting
criteria. CvGain is proposed and demonstrated as
another splitting criteria in this paper. Coefficient of
Variation (Cv), which is a measure of consistency of a
distribution is used to compute CvGain. It has been
observed that decision tree based on CvGain has the
same performance as ID3 and FID3, but at less
computational cost.
ACKNOWLEDGMENT
We thank Dr. Rajeev Wankar and P.S.V.S Sai Prasad
of University of Hyderabad, for their thoughtful
comments and support.
REFERENCES
[1] Blake Ian F, (1979). An Introduction to Applied Probability, John
Wiley & Sons.
[2] Breiman L., Friedman J., Olshen R., and Stone C (1984)..
Classification and Regression Trees.Wadsworth International
Group.
[3] Damghani K.Khalili, Taghavifard M.T., Moghaddam R. Tavakkoli
(2009), Decision Making Under Uncertain and Risky situations,
2009 ERM Symposium, www.ermsymposium.org/2009/pdf/2009-
damghani-decision.pdf
[4] Baoshi, Zheng Yongqing, Zang Shaoyu (2009), A New Decision
Tree Algorithm Based on Rough Set Theory, IEEE, 2009 Asia-
Pacific Conference on Information Processing.
[5] Fayyad U. M. and Irani K. B.( 1992), The attribute selection
problem in decision tree generation. In Proc. 1992 National
Conference on Artificial Intelligence (AAAI92), pages 104110,
AAAI/MITPress.
[6] Han Jiawei and Kamber Micheline (2006), Data mining
Concepts and Techniques, 2nd edition, Morgan Kauffman
Publishers.
[7] Minz Sonajharia and Jain Rajni (2003), Rough Set based
Decision Tree Model for Classification, LNCS 2737 Springer.
[8] Mitchell Tom (1997), Machine Learning. McGraw-Hill.
[9] Pawlak Nsjn Zdzislaw (1991), Rough Sets Theoretical Aspects
and Reasoning about Data, Kluwer Academic Publications.
[10] Quinlan R. (1986),Induction of decision trees, Machine
Learning, Vol. 1, No. 1, pp.81-106.
[11] Quinlan R. (1993),C4.5: Programs for Machine
Learning,Morgan Kaufmann Publishers.
[12] Ramadevi Y, Rao C.R. (2008), Reduct based Decision Tree
(RDT), IJCSES International Journal of Computer Sciences and
Engineering Systems, Vol.2,No.4
[13] Snedecor George W., Cochran William G, (1989), Statistical
Methods, Eighth Edition, Iowa State University Press.
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
7
Use Of Braille Database For Design And
Implementation Of Braille Handglove For
Deafblind People
M.Rajasenathipathi , Arthanariee A. M, and M.Sivakumar
Assistant professor in Computer Science , N.G.M. College-642001, Tamilnadu, India
Director,Bharathidasan School of Computer Applications,Ellispettai-638116, Tamilnadu, India
Doctoral Research Scholar, Anna University, Coimbatore, Tamilnadu , India
Abstract : Braille hand glove is one of the communication
methods for the deaf blind. The Braille hand glove produces
the vibration on the six position of the right hand of deaf blind.
These six positions are matched to six values of Braille code.
Here the user input is translated into Braille code by a
conversion algorithm and the same is sent to hand glove to
operate the corresponding vibration motors inside the glove.
So instead of touching the raised dots in Braille sheet, this
Braille hand glove produces vibration based on English
character value. The hand glove vibration method sees to be
most suitable medium for real-time communication for the
benefit of deaf and blind people, who prefer to work in
computer environment.
Keywords: Braille, Glove, Vibration, Cell
I INTRDUCTION
People who have both sight
and hearing impairments are known as deaf blind.
Because of their impairments they face many problems
in their normal daily life. It is particularly difficult for
totally deaf and blind people to acquire vital and
sufficient information necessary for daily living,
compared with sighted hearing people. To obtain
information for living, Braille glove vibration method is
one de`vice for the benefit of deaf-blind people, who
work in computer environment. There are several
communication methods that involve tactile sensation,
such as finger Braille, manual alphabets and the print
on palm method. However, some problems arise in
such conversion, such as lack of privacy for deaf blind
people and not suitable for computer environment.
Therefore focus has been on vibration in six different
positions which matches to Braille code.
II THE BRAILLE SYSTEM
The Braille code was adapted by Louis Braille
in the early part of the nineteenth century from a military
system which used raised dots to send messages at
night. After competition with other raised systems
earlier this century, it has become the main system for
the majority of those blind people who read and
write using tactile means, and can be found in many
countries around the world. Braille uses the raised dots
in groups of six which are arranged in three rows of two
and which are numbered from 1 to 6.
Fig 1. Braille cell Fig 2. letter M value
These six positions which can be raised or flat, are
used in combination to give just 64 different Braille
characters. This clearly means that there cannot be one
to one correspondence between Braille characters and
text Braille code.
1 4
2 5
3 6
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
8
As mentioned earlier Braille generally consists of cells
of six raised dots arranged in a grid of two dots
horizontally by three dots vertically. The dots are
conventionally numbered 1,2 and 3 from the top of the
left column and 4,5 and 6 from the top of the right
column. The presence or absence of dots given the
coding for the symbol. English Braille is used to code
the letters, punctuation symbol, some double letter
signs and word signs directly but capital letters and
numbers are dealt with by using a prefix symbol as
follows
III BRAILLE CODE TRANSLATION
The steps which are followed when any English text is
converted to Braille code are as follows
1. Read the input value up to the enter key
2. Separate the words on the basis of blank space
3. Break the corresponding word into corresponding
letter
4. Access the Braille database based on the following
major condition
(i) Input value is between a to z
(ii) Input value is between A to Z
(iii) Input value is between 0 to 9
(iv) Input value is in special symbol list
(v) If character matches, then print
corresponding Braille code as it is
(vi) Repeat steps 4 and 5 until all the
characters of input values are matched
with database. If match does not occur
then appropriate error messages are
generated.
By following the above mentioned steps, we will be able
to convert English to Braille code. This conversion is
totally based on one to one matching. The flowchart for
the same is as follows
.
Fig 3: Braille Alphabet
Flow chart for conversion of English text to Braille code
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
9
If str[i]
betwee
n
If str[i]
Betwee
If str[i]
Betwee
If str[i]
In symbol
Print
lowercas
e Braille
code
Print
uppercas
e Braille
code
Print
digits
Braille
code
Print
symbols
Braille
code
No
Yes Yes Yes Yes
No
No
No
No
Yes
Assign
L = 1
Read Input
values in Str
Access
character
Str[i]
L=L+1
End
start
Print
error
message
If
str[i]==
NULL
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
10
IV SOFTWARE IMPLEMENTATION
In standard Braille, all sixty four cells will correspond
to a letter of the roman alphabet. When we convert
English text to Braille code then the above conversion
chart is used as the database and the input text is
matched for the corresponding Braille representation,
Braille is displayed. Input and output window will look
like as in fig no.
Fig 4 : Screen layout for Braille code conversion
V DESIGN OF BRAILLE HAND GLOVE
Fig 5: Hand glove with six positions
Braille hand glove principle is based on six dots. The
six dots forming the cell permit sixty three different
patterns of dot arrangements. It is matched with
lphabets, numbers and special symbols of the English
language. The Braille glove contains six vibration
motors. These are fixed in five fingers and center
palm. The basic technique used in the hand glove is
based on the ASCII value of English letter from the
user typed input in the keyboard. It is converted into
Braille value and it activates the corresponding
motors. So based on the position of vibration the blind
person can understand the value of the letter. For
example if the user types the letter r, it is converted
to Braille value as 1,2,3,5 and this value activates the
corresponding motors in Braille hand glove. This
conversion program is written in hi tech C language
and it is recorded in micro controller of the hand
glove. Any blind person can wear this glove in right
hand, and understand the English letters through
vibration instead of touching the Braille sheet.
Similarly the whole word or sentence is converted into
Braille vibration and send to blind person. Based on
this method the visible person and deaf and blind
person can communicate effectively.
VI THE DESIGN CONCEPT
The Braille Hand glove comprises the following key
components
1. 89C51 Micro controller
2. RS 232 C
3. Relay Driver and Relay
4. power supplies
5. Vibrator motor in hand glove
Fig. 6 Block
diagram of Braille hand glove
89C51
PC
Relay
driver- 6
Relay - 6
Vibrator -
6
RS 232 C
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
11
Table 1 ASCII and Binary value for Braille
VII HARDWARE IMPLEMENTATION
The main component in Braille glove is vibration
motor. it is configured in coin type motor, is a simple
brush motor with a traditional axial design. The
eccentric movement of the weight attached to the
rotor provides vibration during operation. The amount
of vibration is directly proportional to the voltage
applied to the motor. Cylinder motors are
manufactured in high volumes and are fairly
inexpensive. An electrical current applied to the coil in
the direction of the arrow generates upward force on
the left side of the coil and downward force on the
right side, causing the coil to revolve clockwise.
The basic technique used in the hand glove based is
based on the ASCII value of English letter from the
user typed in input box of the editor. After clicking the
serial or parallel mode in the editor, the input English
characters are converted into Braille value and
activate the corresponding motors. So based on the
position of vibration the blind person can understand
the value of English letter. Any blind person can wear
this glove in right hand, and can understand the
English letters through vibration
.Fig 7: Hardware prototype
VIII TESTING OF THE SYSTEM
Both hardware and software Translation programs
were written in an incremental fashion, testing and
verifying each section of code. This starts with
reading the rules from a text file, separating them into
fields and matching each field and applying the rule.
Consequently debugging and corrections were made
to the code at all steps of development. Both
programs work well and have not had any fatal errors.
The execution time of the programs in software part
and vibrations in hardware are done under a few
seconds making it acceptable for the Blind people to
use.
For the testing of the system we have translated
English newspapers heading into the corresponding
Braille text and Braille vibrations. We found that it is
with 100% accuracy for Braille text conversion and
Braille glove is working with 100% accuracy in
vibration for corresponding position. Also every
conversion is done automatically. The
ASCII
Value
ASCII
Chara
cter
Braille
Chara
cter
Binary
Representati
on
D
6
D
5
D
4
D
3
D
2
D
1
32
(space
)
0 0 0 0 0 0
33 ! ! 1 0 1 1 1 0
34 " 0 1 0 0 0 0
35 # # 1 1 1 1 0 0
36 $ $ 1 0 1 0 1 1
37 % % 1 0 1 0 0 1
38 & & 1 0 1 1 1 1
39 ' 0 0 0 1 0 0
40 ( ( 1 1 0 1 1 1
41 ) ) 1 1 1 1 1 0
42 * * 1 0 0 0 0 1
82 R R 0 1 0 1 1 1
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
12
Translation of English text to Braille vibration is shown
in the table 2.
Table 2 : Two modes in Braille Vibration
The little poor accuracy of the translation in serial
mode was mainly due to mixing of digits and
alphabets. It can be rectified by increasing the buffer
size and by decreasing the speed of vibration in hand
glove .
IX CONCLUSION AND FURTHER WORK
SUGGESTED
The development of low cost Braille hand glove is
necessary for visually impaired community. The
same Translation technique can be used in various
languages like Bengali, Hindi, Tamil ,French, etc.,
Also it proposes a new approach to blind persons to
know about computer oriented technologies. The
feedback from visually impaired community is that
Braille hand gloves are the best kit for two way
communication . This technology if upgraded can
prove to be a boon for the visually impaired
community so that they can perform better and on par
with the visible people
The reverse engineering process for the same
problem which produces Braille signal to English text,
if constructed can prove to be an effective two way
communication tool in online chatting and new
effective teaching methodology for physically
impaired people.
X REFERENCES
[1] Pradip k Das and Atal Chaudhuri, A computerized Braille
Tran scripter for the Visually handicapped ,IEEE-EMBS 1995
[2] Kenneth R Ingham, Braille, the language, its machine
Translation and Display, IEEE Transactions and Man Machine
systems 1998.
[3]. c. Moore and I Murray, An Electronic design of a low cost
Braille type writer , International Conference, Perth, western
Australia, 18-21 November 2001
[4] Paul Blenkhorn, A system for converting print into Braille,
IEEE on Rehabilitation Engineering. Vol5 No2 ,June 1997
[5] Paul blenkhorn and Gareth evans, Automated Braille
production from word processed documents, IEEE transactions on
neural systems and rehabilitation engineering,Vol9 No1, March
2001
[6] Murray and T Dias, A portable device for optically recognizing
Braille, International Conference, Perth, western Australia,18-21 ,
November 2001
[7] F.E.Sandne and Y.P.huand, C hord level error correction for
portable Braille devices, Electronics letters , vol 42,No 2 January
2002
[8] Gael Dias and Bruno conde, Towards web browsing for
Visually impaired people, International Conference of information
Technology (ITNG,07)- 2007
[9] Gael Dias and Bruno conde, Towards web browsing for
Visually impaired people, International Conference of information
Technology (ITNG,07),IEEE,UK,2007
[10] Myung-chul cho and Hoo-gon choi, Pair of Braille based
chord gloves, IEEE computer soci ety, 2002
[11] Yasuhrio Matsuda and Isomura, Finger Braille Recognition
system for people who communicate with deaf, Proceeding of
IEEE international conference on 2008
[12] Anupam Basu and soumitro Banerjee, A Pc based Braille
library system for the sightless, IEEE Transactions on
Rehabilitation Engineering vol 6 no1 March 1998
[13] Makoto Tanaka and Hideaki Goto, Text Tracking wearable
camera system for visually impaired people, IEEE 2008
[14] Mu chun su and Yu chine wang, Portable communication aid
for deaf-blind people, Computing and control Engineering journal
February 2001
[15] David A Fisher and C.Bond, A single handed Braille chord
system for computer Keyboard input, IEEE 1992
[16] Paul blenkhron, A system for converting Braille into print
IEEE Transactions on rehabilitation Engineering vol3 no 2 June
1995[17] Lgmo Koo and Ryel Choi, Wearable Fingertip Tactile
Display,SICE International Conference , Korea, 2006
[18] Manip and Akria, Analysis of prosody in finger Braille using
electromyography, IEEE EMBS International Conference, US Aug
30 sep 3 ,2006
MODE
Total
number of
words
Percentage of words
translated correctly
software Hardware
Serial mode 876 99.62 99.12
Parallel
mode
992 100 100
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
13
Development of Reliable Multihomed
Scatternet Network
R.Dhaya, Dr.V.Sadasivam, Dr.R.Kanthavel
Lecturer, National Engineering College, Kovilpatti, Tamilnadu ,India.
Professor, M.S.University, Tirunelveli, Tamilnadu, India.
Teaching Research Associate, Govt. College of Engineering, Tirunelveli, Tamilnadu, India.
Abstract Since wireless networks are movable and
flexible, the conventional protocols are standing behind
fault tolerance problems. A new Stream control
transmission protocol (SCTP) is a transport layer protocol
which is reliable, message-oriented data transport
protocol that supports multiple streams to prevent
head-of-line blocking and multihoming for end-to-
end network fault-tolerance. A host is multihomed if
it can be addressed by multiple IP addresses. SCTP
multihoming allows connections, or associations to
remain alive even when an endpoints IP address
become unreachable. In a multihomed host there will be
at least two IP addresses. SCTP uses one IP for a primary
path and the other IP for secondary path. Initially, SCTP
uses the primary path for transmission of data. If the
primary path fails then the secondary path is chosen
for further transmission. Similarly if the secondary path
fails then the primary path is chosen for further
transmission. On the other hand Bluetooth Scatternet
refers to a collection of Bluetooth piconets. The proposed
Bluetooth Scatternet system uses the multihoming
concept of SCTP for effective fault tolerance during data
transmission.
Keywords: Multihoming, Scatternets,
Piconets,Bluetooth.
I. INTRODUCTION
Bluetooth is a wireless protocol for exchanging data
over short distances from fixed and mobile devices,
creating personal area networks (PANs). It can connect
several devices, overcoming problems of
synchronization. Bluetooth uses a radio technology
called frequency-hopping spread spectrum, which chops
up the data being sent and transmits chunks of it on up
to 79 frequencies. It can achieve a gross data rate of 1
Mb/s [2]. Bluetooth provides a way to connect and
exchange information between devices such as mobile
phones, telephones, laptops, personal computers,
printers, Global Positioning System (GPS) receivers and
digital cameras.
Bluetooth protocols assume that a small number of
units will participate in communications at any given
time. These small groups are called piconets, and they
consist of one master unit and up to seven active slave
units. The master is the unit that initiates transmissions,
and the slaves are the responding units[13].
As with piconets, where multiple Bluetooth devices
are able to connect with each other in an ad-hoc
manner, so too can multiple piconets join together to
form a larger network known as a scatternet [12].
Bluetooth devices must have point-to-multipoint
capability in order to engage in scatternet
communication, and several piconets can be connected
to each other through one scatternet [4]. Furthermore, a
single Bluetooth device may participate as a slave in
several piconets, but can only be a master in one
piconet.
II. PROPOSED SOLUTION
The main objective of this paper is to perform the
simulation of SCTP in Bluetooth Scatternets which of
course, is a wireless network. A Bluetooth Scatternet
consisting of two piconets is established. Each piconet
has one master and one slave. The slave called Slave-
bridge connects the two piconets. Connects here
means that this slave-bridge acts as the medium
through which data transmission will take place between
the two Masters. This suggests that whenever there is a
path breakage, SCTP will automatically detect the path
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
14
failure and an alternate path can be used by means of
heartbeat signals.
A. DEVICE DETECTION
In mobile ad hoc environments, devices initially
have no information about their surrounding
environment or the devices that operate within their
range. There is no centralized instance to query about
the environment. Therefore, a protocol must exist that
provides means for detecting devices and enables
devices to set up a connection, Bluetooth uses the Base
band protocol for this task . Two procedures are used in
the device discovery procedure; inquiry and page.
B. PROXIMITY PROCESS
In order to set up a connection, a device must
detect what other devices are in range. This is the goal
of the inquiry procedure. The process is initiated by the
unit that wishes to collect device information or create a
connection. To conserve power and coexist with other
link activity, inquiry is always initiated by higher level
control protocols. The inquiry procedure must overcome
the initial frequency discrepancy between devices.
Therefore, inquiry only uses 32 of the 79 hop
frequencies [3]. Typically a device enters inquiry mode
periodically. Similarly, a device that wishes to be visible
to inquiring units enters inquiry scan in certain intervals.
In order to find each other, one device must be in Inquiry
state and one (or more) device must be in Inquiry Scan
sub-state simultaneously.
C. CONNECTION ESTABLISHMENT
In Bluetooth the connection establishment is
handled by the page process. The page process
requires knowledge of the BD_ADDR of the device with
which the connection is to be established. Furthermore
the device being paged must be in Page Scan sub-state,
i.e. listening for page messages. At the end of the page
process a connection has been set up, the paging
device becomes the master and the paged device
becomes the slave. As with inquiry a device typically
enters Page state periodically and a device that wishes
to be able to connect to paging units enters page scan in
certain intervals.
D. SCATTERNET USERCASE
In this scenario the mobile phone functions as both a
master and a slave . In order for this to work, regardless
of data speed, an effective scatternet implementation is
required.
E. PICONET VS SCATTERNET:
A piconet is the type of connection that is formed
between two or more Bluetooth-enabled devices.
However, when a piconet is formed between two or
more devices, one device is dynamically elected to take
the role of 'master', and all other devices assume a
'slave' role for synchronization reasons. Piconets have a
3-bit address space, which limits the maximum size of a
piconet to 8 devices (2
3
= 8), i.e. 1 master and 7 slaves
[3]. A piconet allows one master device to interconnect
with up to seven active slave devices (because a three-
bit MAC address is used). Up to 255 further slave
devices can be inactive, which the master device can
bring into active status at any time. A piconet typically
has a range of about 10 m and a transfer rate between
about 400 and 700 kbit/s depending on whether
synchronous or asynchronous connection is used.
A scatternet is a type of ad-hoc computer network
consisting of two or more piconets. A scatternet is a
number of interconnected piconets that supports
communication between more than 8 devices .
Scatternets can be formed when a member of one
piconet (either the master or one of the slaves) elects to
participate as a slave in a second, separate piconet. The
device participating in both piconets is known as slave-
bridge which can relay data between members of both
ad-hoc networks. Using this approach, it is possible to
join together numerous piconets into a large scatternet,
and to expand the physical size of the network beyond
Bluetooth's limited range.
III. EXISTING PROBLEM
Besides all the explanations mentioned above,
SCTP still has some existing shortfalls. The existing
problem is, however not involved with fixed network with
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
15
fixed hosts i.e., the normal connections that involves
connections using cables. The existing problem is
mainly with the manipulation of data transmission in
fixed network with mobile hosts and with wireless
networks [10].
Presently TCP is mainly used in wireless networks.
But TCP does not support multihoming. It supports only
one IP per host that greatly reduces the fault tolerance
level of the connection. Also there is a great possibility
for congestion to occur[11]. The same problem occurs
when we use UDP as the transmission protocol.
Introduction
IV. STREAM CONTROL TRANSMISSION PROTOCOL
Stream Control Transmission Protocol (SCTP) is an
end-to-end transport protocol that provides services
heretofore unavailable from either of the workhorse
transport protocols[9].
A. NEED FOR SCTP
TCP has performed immense service as the primary
means of reliable data transfer in IP networks. However,
an increasing number of recent applications have found
TCP too limiting, and have incorporated their own
reliable data transfer protocol on top of UDP [8]. The
limitations which users have wished to bypass include
the following:
TCP provides both reliable data transfer and
strict order-of transmission delivery of data.
Some applications need reliable transfer without
sequence maintenance, while others would be
satisfied with partial ordering of the data [5]. In
both of these cases the head-of-line blocking
offered by TCP causes unnecessary delay.
The stream-oriented nature of TCP is often an
inconvenience. Applications must add their own
record marking to delineate their messages, and
must make explicit use of the push facility to
ensure that a complete message is transferred
in a reasonable time.
The limited scope of TCP sockets complicates
the task of providing highly-available data
transfer capability using multihomed hosts.
TCP is relatively vulnerable to denial of service
attacks, such as SYN attacks. Transport of
PSTN signalling across the IP network is an
application for which all of these limitations of
TCP are relevant[6] .
Two key problems surfaced in the use of TCP:
Head-of-line blocking - a problem where
sending independent messages over an order-
preserving TCP connection causes delivery of
messages sent later to be delayed within a
receivers transport layer buffers until an earlier
lost message is retransmitted and arrives thus
resulting in undesirable call setup failure[5].
Multihoming - where a host with multiple points
for redundancy purposes, does not want to wait
for a routing convergence to communicate
critical messages to its peer communication
endpoint. For call control signalling, such delay
is unacceptable when an alternate available
path exists[1]. A TCP connection only binds a
single point of attachment at either end point.
TABLE 1: COMPARISON OF SCTP SERVICES AND FEATURES
WITH THOSE OF TCP AND UDP.
SERVICES/FEATURES SCTP TCP
UDP
Connection oriented Yes Yes No
Full Duplex Yes Yes Yes
Reliable Data Transfer Yes Yes No
Partial Reliable Data
Transfer
Optional No No
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
16
Flow control Yes Yes No
TCP Friendly Congestion
Control
Yes Yes No
ECN Capable Yes Yes No
Ordered data delivery Yes Yes No
Unordered data delivery Yes No Yes
Path MTU discovery Yes Yes No
Message fragmentation Yes Yes No
Message bundling Yes Yes No
Multistreaming Yes No No
Multihoming Yes No No
Reachability check Yes Yes No
SCTP monitors the paths of the association using a
built-in heartbeat [7] as shown in Table 1; upon
detecting a path failure, the protocol sends traffic over
the alternate path. It's not even necessary for the
applications to know that a failover recovery occurred.
V. EXPERIMENTAL WORKS :BASIC STRUCTURE
OF THE PROPOSED SYSTEM
The experiment consists of:-
Two Piconets, each with a Master and a Slave
First Piconet consists of Master1 with two IP
addresses: IP 0.1 and IP 0.2
Second Piconet consists of Master2 with two IP
addresses: IP 6.1 and IP 6.2
Slave Bridge connects both the Piconets
Primary path is (if node 1 is to be failed)
o Master1 IP 0.1 Slave Bridge
IP 6.1 Master2
Alternate path is
o Master1 IP 0.2 Slave Bridge
IP 6.1 Master2
Path for acknowledgement is
o Master2 IP 6.2 Slave Bridge
IP 0.2 Master1
A. WORKING OF THE PROPOSED SYSTEM
The main working of this paper is as stated above.
According to the node selected, the primary path is
assigned. For example, if we select node 1 to fail, the
path 01346 will be selected as the primary path.
If we select node 5 to fail, the path 02356 will
be selected as the primary path. Similarly, the heartbeat
also depends on the node to be failed. When we select
the node to be failed, the heartbeat will start flowing
through its complementary IP address of the
corresponding host. For example, if node 1 is selected
then heartbeat signals will flow through 32 and 20
(Node 2 is the complementary IP address for node 1).
Example 1:If node 1 fails, then the Primary path
(01346) will fail. This means that no data
transmission can occur through the primary path. Now
stop the heartbeat signals through 32 and 20. As
soon as the heartbeat signals stop, data transmission
will continue through the secondary path
(02346). Note here that only the IP address of
the failure node is replaced with its complementary IP
address (1 is replaced with 2), but not necessarily for the
other host (4 is not replaced with 5). After all data
transmissions are over, acknowledgement signals will
be started from the Receiver (Master2) to the Sender
(Master1) via Slave-bridge (65320).
Example 2:If node 2 fails, then the Primary path
(02356) will fail. This means that no data
transmission can occur through the primary path. Now
stop the heartbeat signals through 31 and 10. As
soon as the heartbeat signals stop, data transmission
will continue through the secondary path
(01356). Note here also that only the IP
address of the host that fails is replaced with its
complementary IP address (2 is replaced with 1), but not
necessarily for the other host (5 is not replaced with 5).
After all data transmissions are over, acknowledgement
signals will be sent from the Receiver (Master2) to the
Sender (Master1) via Slave-bridge (65320).
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
17
Fig 1: Proposed Bluetooth Scatternet with two piconets
Figure 1 shows our proposed network having
two piconets. Node-0 and node-6 are the masters in
each piconet. As we can see, the slave-bridge lies in the
intersection of the two piconets. This means that it lies
within the data transmission range of Master1 as well as
Master 2. Note that from the piconets, Master1 and
Master 2 are not in each others range for data
transmission.Node-1 and node-2 are the IP addresses
of Master1, node-4 and node-5 are the IP addresses of
Master 2. Thus we have justified that both Master1 and
Master 2 are multihomed. Data transmission takes place
through one of the IP addresses of Master1, passes
through the slave-bridge, and then reaches Master2
through one of its IP addresses. This is referred to as
the Primary path. When path breakage occurs, data
transmission will take place by replacing the failed IP
address with its complementary IP address of the
corresponding host.
This is illustrated in the following algorithm proposed in
figure 2:-
Fig 2: Proposed algorithm
V. EXPERIMENTAL RESULTS
A. INITIALIZATION
Node 0 checks for other nodes which are within its
range and is illustrated in Fig 3. Here Node 1, Node 2
and Node 3 are within the range of Node 0. So Node 0
can transmit data to these three nodes.
Fig 3: Node 0 inquires its neighbouring nodes
B. DATA TRANSFER THROUGH PRIMARY PATH
Step 1: Initialize the Bluetooth Scatternet.
Step 2: Start Data transfer through Primary Path.
Step 3: Start Heartbeat signals through alternate
path.
Step 4: If Primary path fails-
Stop Data transfer through
Primary path.
Search for alternate path using
Heartbeat signals.
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
18
After initialisation the data starts transferring
from the sender to the receiver through the Primary
Path. Here the Primary Path is 01346 as shown
in the Figure 4. Here the Primary Path is 01346
because the node to be failed is selected as Node 1.
Fig 4: Data transfer through Primary Path
C. HEARTBEAT SIGNALS THROUGH 32 AND 20
After data starts transferring through the Primary
Path the Heartbeat signals are sent through the paths
32 and 20 which is shown in Figure 5. The
heartbeats check whether these two paths are alive or
not. This is done because when the Primary Path fails
these two paths will serve as the alternate path.
Fig 5: Heartbeat signals through alternate path
D. PATH FAILURE DUE TO NODE 1 (PACKET
LOSS)
When data transfers through the Primary Path,
there occurs a path failure due to Node 1 which results
in Packet Loss in Node 1 and which is shown in Figure
6. Data can no longer transfer through the Primary Path.
Fig 6: Path failure due to node 1
E. DATA TRANSFER THROUGH SECONDARY
PATH
Due to the Primary Path failure, we cannot
transfer any data through it. So we use the Secondary
Path as shown in Figure 7 for transferring the remaining
data.The Secondary Path transfers all the remaining
data from the sender to the receiver. Here the
Secondary path is taken as 02346.
Fig 7: Data transfer through Secondary Path
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
19
F. ACKNOWLEDGEMENT FROM RECEIVER TO
SENDER
After all the data transmissions are over, we send the
acknowledgements through a separate path. This is
illustrated in Figure 8. Here the path 65320 is
used for transferring acknowledgements from receiver to
sender.
IV. GE
Fig 8: Acknowledgement from Receiver to Sender
G. X-GRAPH : NODE VS TRANSMISSION TIME
(PRIMARY AND SECONDARY PATH)
The Figure 9 graph compares the efficiency of
data transfer through Primary and Secondary path.
Fig 9 : Node Vs Transmission Time (Primary and Secondary path)
TABLE 2: NODE VS TRANSMISSION TIME (PRIMARY PATH)
X-AXIS
(NODE)
Y-AXIS
(TRANSMISSION TIME)
0 0.221539
1 0.456455
3 0.556162
4 0.682935
6 0.691748
In Table 2, Node(N) is taken in X-axis and
Transmission Time is taken in the Y-axis. Node(N)
specifies the nodes forming the Primary Path.
Transmission time specifies the time at which every
node receives a particular packet that is sent from
sender to receiver. Here the time taken by Primary Path
to send a single packet from sender to receiver is
around 0.46.
TABLE 3: NODE VS TRANSMISSION TIME (SECONDARY PATH)
X-AXIS
(NODE)
Y-AXIS
(TRANSMISSION TIME)
0 3.086787
2 3.111769
3 3.190826
4 3.262293
6 3.273045
In the above Table 3, Node(N) is taken in X-axis and
Transmission Time is taken in the Y-axis. Node(N)
specifies the nodes forming the Secondary Path.
Transmission time specifies the time at which every
node receives a particular packet that is sent from
sender to receiver. Here the time taken by Secondary
Path to send a single packet from sender to receiver is
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
20
around 0.20. So from the tables we can find that
Secondary Path is more efficient than Primary Path.
H. 5.8.2 NODE VS TRANSMISSION TIME (PATH
FAILURE)
This Figure 10 shows the path failure due to
node 4. In x-axis we take the nodes forming the primary
path. In y-axis, we take the transmission time from
sender to receiver. As we can see from the graph, when
node 4 fails the transmission through the Primary path is
ended.
Fig 10: Node Vs Transmission Time (Path failure)
TABLE 4: NODE VS TRANSMISSION TIME (PATH FAILURE)
X-AXIS
(NODE)
Y-AXIS
(TRANSMISSION TIME)
0 1.91539
1 2.156455
3 2.356162
4 2.8023
6 ---------
In the above Table 4, we take Node (N) in X-
axis and Transmission Time is taken in the Y-axis. Node
(N) specifies the nodes forming the Primary Path
01346. Data starts transferring through the
Primary path. It reaches Node 4 at the time 2.8023. At
the meantime, Node 4 fails due to packet loss. So no
more data can be transferred through Node 4.Hence the
data does not reaches Node 6. This is the reason why
Node 6 has no transmission time.
VI. CONCLUSION
A Bluetooth Scatternet has been established.
Multi-homing facility of SCTP has been implemented in
the established Bluetooth Scatternet. Hence congestion
is avoided in our Proposed System. From the
experimental result it is seen that secondary path is
more efficient than Primary path. Secondary path
transfers data two times faster than the Primary path. So
even if Primary path fails, data transmission through
Secondary path will be very efficient and reliable. SCTP
thus increases the fault tolerance level during data
transmission in Bluetooth Scatternets. Increased ACK
traffic due to large amount of data transmission can be
avoided by providing separate path for ACK. In our
Proposed System, we provided a separate path for
ACK. Hence ACK traffic has been avoided.
In our proposed system we have two IP
addresses per host. But we can increase the number of
IP addresses more than two for each host so as to
obtain more than two paths for data transmission in
order to increase the fault tolerance level.
REFERENCES
[1] Abd EI AI ,Saadawi, and M. Lee., LS_SCTP: A Bandwidth
Aggregation Technique For Stream Control Transmission Protocol.
Computer Communication, Vol 27, No 10, pp 1012-1024,2004.
[2] Baatz, M. Frank, C. Khl, P. Martini and C. Scholz, Bluetooth
Scatternets: An Enhanced Adaptive Scheduling Scheme, Proc. IEEE
INFOCOM02,pp 789-790, 2005.
[3] Basagni, Bruno and Petrioli, A Performance Comparison of
Scatternet Formation Protocols for Networks of Bluetooth Devices,
Proc. IEEE International Conference on Pervasive Computing and
Communications (PerCom) Texas, pp 93-103, 2005.
[4] Bhagwat and Segall A, A routing vector (RVM) for routing in
Bluetooth scatternets, Proc. IEEE Int. Workshop on Mobile Multimedia
Communications MoMuC,pp 375-379, 1999.
[5] caro A, Amer P ,Iyengar J and R Stewart, Retransmission policies
with transport layer multihoming In IEEE ICON 2003, pp 255-260,
2003.
[6] Daoud K. , Guillouard, K., Herbelin, P. and Crespi, N, A Network-
Controlled Architecture for SCTP Hard Handover,IEEE Conference on
Vehicular Technology, pp 1-5,2010.
[7] Iyengar J , shah K,Amer P, and Stewart Concurrent multipath
transfer using SCTP multihoming. In SPECTS 2004, San
Jose.Califonia,pp 74-81, 2004.
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
21
8] Iyengar J, Amer P and Stewart R, Concurrent multipath transfer
using transport layer multihoming: performance under varying band
width proportions. In Milcom Vol 1,pp 238-244, 2003.
9] Jinsuk Baek Fisher, P.S. Minho Jo and Hsiao-Hwa Chen, A
Lightweight SCTP for Partially Reliable Overlay Video Multicast
Service for Mobile Terminals , IEEE Transactions on Multimedia,
Vol 12,No 7,pp 754 - 766 ,2010.
[10] Riccione, RG-SCTP: Using the relay gateway approach for
applying SCTP in vehicular networks,The IEEE symposium on
Computers and Communications, pp 234-239,2010.
[11] UC Berkeley, LBL,USC/ISI, AND Xerox parc.ns2 documentation
and software, version 21b8,2001,
[12] Wang Y , Stojmenovic I and LI X Y, Bluetooth Scatternet
Formation for Single-hop Ad Hoc Networks Based on Virtual Positions,
in Proc. 9th IEEE Symposium on Computers and Communications
ISCC2004,pp 1-17 , 2006.
[13] Wang Y , Stojmenovic I and LI X Y, Partial Delaunay,
Triangulation and Degree Limited Localized Bluetooth Multihop,
Scatternet Formation, IEEE Transactions on Parallel and Distributed,
Systems, Vol 15, No 4, pp 350-361, 2006.
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
22
Peristaltic Pumping Of a Micropolar Fluid In
An Inclined Channel
*R.Hemadri Reddy, *A.Kavitha, **S.Sreenadh, **P.Hariprabakran
*School of Advanced Sciences, VIT University, Vellore- 632014,T.N, INDIA.
**Department of Mathematics, Sri Venkateswara University, Tirupati- 517502.A.P.INDIA.
Abstract-Peristaltic pumping of a non-Newtinian
micropolar fluid in an inclined channel is studied.
The analysis has been carried out in the wave frame
of reference with long wavelength and zero
Reynolds number assumptions. The velocity
distribution and stream functions are obtained. The
pressure rise (drop) over one wavelength is
obtained. The velocity field, the stream function, ,
the volume flux and the pressure rise over one cycle
of the wave and frictional force are obtained and on
the flow quantities are discussed graphically.
Keywords: Peristaltic transport; micropolar fluid; volume
flow rate; pressure rise.
I. INTRODUCTION
Peristaltic pumping is a form of fluid transport,
generally from a region of lower to higher pressure, by
means of a progressive wave of area contraction or
expansion which propagates along the length of a tube-
like structure. Peristalsis occurs naturally as a means of
pumping biofluids from one place of the body to another.
This mechanism occurs in the gastrointestinal, urinary
and reproductive tracts and many other glandular ducts
in the living body. The early reviews of Ramachandra
Rao and Usha [1] , Jaffrin and Shapiro[2] , Manton [3],
Brasseur et al. [4], Srivastava and Srivastava [5],
Provost and Schwarz [6], Shukla and Gupta [7], Misra
and Pandey [8] ,Rao and Rajagopal [9],Kavitha et.al[10]
Vajravelu et al. [11-15], Subba Reddy[16&17], Srinivas
[18,19] deal with the peristaltic transport of viscous
fluids through tubes and channels having impermeable
flexible walls.
In classical continuum theory a body is assumed to
be a dense collection of point masses in which there is
no internal structure. In the motion of a volume element
v it is assumed that the individual motions of material
points coincide with the motion of centre of mass of the
volume element v . In this case the density of the
volume element v is independent of the size of v
and independent on its location in space and the time t.
Eringen [20] reported that this is not true
as v 0 .The density shows an increasing
dependence on the size of the v , when v is less
than a critical value v* . Classical continuum theory
cannot explain the mechanical behavior of rheologically
complex fluids, such as liquid crystals, colloidal fluids
and blood. Due to this fact a new approach was
necessitated. There are several approaches to the
formulation of microcontinuum theories of fluids such as
simple deformable directed fluids, dipolar fluids, polar
fluids, simple micro-fluids, micropolar fluids, etc. All
these consider the existence of couple stresses and
body couples.
Eringen [20,21] reported the theory of micropolar
fluids in which the fluid micro elements undergo
rotations without stretching. Micropolar fluids are
superior to the Navier-Stokes fluids and they can sustain
stresses and body couples. Here the micro particles in
the volume v rotate with an angular velocity about
the centre of gravity of the volume in an average
sense and is described by the micro rotation vector
. The micropolar fluids can support stress and body
couples and find their applications in a special case of
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
23
fluid in which micro rotational motions are important.
Airman and Cakmak [22] discussed three basic viscous
flows of micropolar fluids. They are Couette and
Poiseuille flows between two parallel plates and the
problem of a rotating fluid with a free surface. The
results obtained are compared with the results of the
classical fluid mechanics. Srinivasacharya et al.[23]
made a study on the peristaltic pumping of a micro polar
fluid in a tube. The gravitational effects are also
important in peristaltic pumping. In view of this, we have
considered the peristaltic pumping of a micropolar fluid
in an inclined channel. This mathematical model may
be useful to have a better understanding of the
physiological systems such as blood vessels. The
velocity field, the stream function, the volume flow rate
and the pressure rise are obtained and results are
discussed through graphs.
II.MATHEMATICAL FORMULATION and SOLUTION
Consider the peristaltic pumping of a micropolar fluid
in an inclined channel of half-width a. A longitudinal
train of progressive sinusoidal waves takes place on the
upper and lower walls of the channel. For simplicity we
restrict our discussion to the half-width of the channel
as shown in figure. (1)
The wall deformation is given by
( ) ( )
2
H X, t a bsin X ct
= +
(1)
Where b is the amplitude, is the wavelength and c is
the wave speed.
Figure 1. Physical model
EQUATIONS of MOTION
Under the assumption that the channel length is
an integral multiple of the wavelength and the
pressure difference across the ends of the channel is a
constant, the flow becomes steady in the wave frame
( ) x, y
moving with velocity c away from the fixed
(laboratory) frame
( ) X, Y
. The transformation between
these two frames is given by
X= X-ct; y= Y; u(x, y)=U(X-ct,Y); v(x,y)=V(X-ct,Y) (2)
Where U and V are velocity components in the
laboratory frame and u, v are velocity components in the
wave frame. In many physiological situations it is
proved experimentally that the Reynolds number of the
flow is very small. So, we assume that the flow is
inertia-free. Further, we assume that the wavelength is
infinite.
USING the NON-DIMENSIONAL QUANTITIES.
2
u x y pa a H
u ; x ; y ; p ; ; h
c a c c a
= = = = = =
The non-dimensional form of equations
governing the motion (dropping the bars) is
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
24
( )
2
2
u p
N 1 N sin 0
y y x
+ + =
(3)
2
2 2
2 N u
2 0
m y y
=
(4)
Where
k
N
k
=
+
is coupling number
is the micro rotation velocity
u is the velocity
is the viscosity of the fluid
k is the micropolar viscosity
m is the micropolar parameter
p is the fluid pressure
The non-dimensional boundary conditions are
u
0
y
at y = 0 (5)
0
y
at y = 0 (6)
u = -1 at y= h(x) (7)
0 = at y= h(x) (8)
SOLUTION
The general solution of (3) and (4) is given by
N
u
m
= ( )
( )
( )
1
2 3 4 2
2
1 N P sin 2A
A sinhmy A coshmy y A
2 N m
y
+ + + +
(9)
Where
p
P
x
( )
( )
1
2 3 2
1 N p sin A
Acoshmy A sinhmy y
2 N m
= +
(10)
using the boundary conditions (5) to (8) in
(9) and (10),we obtain the velocity of the fluid and
micro rotation velocity as
( )
( )
2
1 2
1 Np sin N
u Ssinhmy coshmy y S 1
2 N m
= + +
(11)
where
1
1 2
3
2N D
S
m S
=
2 1 1
2
2 2
3 3
D 2ND 2N sinhmh h Ncoshmh
S h
m S S m m m
= + +
3
S 2cosh mh N =
1
D mh sinh mh =
( )
( )
1
2 3 2
1 N P sin A
A coshmy A sinhmy y
2 N m
= +
(12)
where
( ) [ ]
( )( )
1
mN 1 N P sin mh sinhmh
A
2 N 2coshmh N
=
( ) [ ]
( )( )
2
2 1 N P sin mh sinhmh
A
m 2 N 2coshmh N
=
( )
( )
3
1 N P sin
A
2 N m
=
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
25
Integrating the equation (11) and using the condition
0 = at y 0 = , we get the stream function as
( )
( )
3
1
2
1 N p sin Scoshmy Nsinhmy y
Sy y
2 N m m m 3
= + +
(13)
The volume flux q through each cross-section in
the wave frame is given by
h
0
q u dy =
(14)
where
1
1 2
3
2N D
S
m S
=
( )
( )
3
1
2
1 NP sin
q
2 N
Scoshmh Nsinhmh h
Sh h
m m m 3
=
+ +
2 1 1
2
2 2
3 3
D 2ND 2N sinhmh h Ncoshmh
S h
m S S m m m
= + +
3
S 2cosh mh N =
1
D mh sinh mh =
The pressure gradient is obtained from equation (14)
( )( )
( )
3
1 2
q h 2 N dp 1
sin
coshmh Nsinhmh h dx 1 N
S Sh
m m m 3
+
= +
+ +
(15)
The time averaged flow rate is
Q q 1 = + (16)
THE PUMPING CHARACTERISTICS
Integrating the equation (15) with respect to x
over one wavelength, we get the pressure rise (drop)
over one cycle of the wave as
( )( )
( )
1
0
3
1 2
Q 1 h 2 N
p dx sin
1 N
1
coshmh Nsinhmh h
S Sh
m m m 3
+
= +
| |
]
]
]
+ +
]
\
(17)
The pressure rise required to produce zero
average flow rate is denoted by
0
P . Hence
0
P is
given by
( )( )
( )
1
0
0
3
1 2
h 1 2 N
p dx sin
1 N
1
coshmh Nsinhmh h
S Sh
m m m 3
= +
| }
]
]
]
+ +
]
\ .
(18)
The dimensionless frictional force F at the wall across
one wavelength in the inclined channel is given by
1
0
dp
F h dx
dx
=
( )( )
( )
1
0
3
1 2
h 1 2 N
h dx sin
1 N
1
coshmh Nsinhmh h
S Sh
m m m 3
= +
| }
]
]
]
+ +
]
\ .
(19)
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
26
III. DISCUSSION OF The RESULTS
From equation (17), we have calculated the
pressure difference as a function of Q for different
values of coupling number N with a 0.4, = m=2,
2 =
and for different )
2
,
4
, 0 . (
= e i and is
shown in figure (2-4). In figure( 3) It is observed that for
chosen parameters the pumping curves intersect at a
point in the first quadrant closure to
Q 0 .1 8 .
This
may be due to the inclination of the channel is
horizontal. For
Q 0.18 <
we observed that the
pressure rise increases with the coupling number N.
The behavior is otherwise when Q > 0.18. For free
pumping the Q decreases with the increasing N. For
free pumping we observe that the flux Q increases
with increasing
0
2
< <
. The same behavior
is observed for the pressure difference p when
Q 0. =
The variation of pressure rise with time
averaged flow rate is calculated from equation (17) for
different values of micropolar parameter m, and is
shown in figures (5) to (7) for fixed
a 0.4, =
n 0.2, = 2 = .It is observed that the pumping
curves that the pumping curves meet at a point
between
Q 0. 1 =
and
Q 0 . 2 =
, this value is
estimated as Q 0.12 = , when
Q 0 . 1 2 <
the
pressure rise decreases with increasing m. The
opposite behavior is noticed for
Q 0 . 1 2 >
. For free
pumping we observe that the flux Q increases with
increasing inclination of the channel
0
2
.
From equation (17), we have calculated
pressure rise as a function of Q for different values of
0
2
and is shown in figure (8) for fixed
n 0.2, = 2 = , m 2 = and
a 0.4, =
. It is observed
that for an inclined channel, the peristaltic wave passing
over the channel wall pumps against more pressure rise
compared to a horizontal channel
( ) 0 =
. For free
pumping the flux Q increases with increasing angle of
inclination between 0 and
2
.
The variation of frictional force with time
averaged flow rate is calculated from equation (19) for
different values of N, m, for a fixed a = 0.4 and is
shown in figure (9) to (13) it is observed that the
frictional force F has the opposite behavior compared
to pressure rise. For horizontal channel it is observed
that the given N, the frictional force increases with the
flux Q.
Figure 2.The variation of p with Q for different values
of N with a 0.4, = m=2, 2 = , =0
Figure 3. The variation of p with Qfor different values
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
27
of N with a 0.4, = m=2, 2 = ,
4
=
Figure 4. The variation of p with Q for different values
of N with a 0.4, = m 2 = , 2 = , =
2
Figure 5. The variation of p with Q for different values
of m with a 0.4, = n=0.2, 2 = , =0
Figure 6.The variation of p with Q for different values
of m with a 0.4, = n=0.2, 2 = , =Pi/4
Figure 7.The variation of p with Q for different values
of m with a 0.4, = n=0.2, 2 = , =Pi/2
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
28
Figure 8.The variation of p with Q for different values
of with a 0.4, = m=2, 2 = , n=0.2
Figure 9.The variation of F with Q for different values
of N with a 0.4, = m=2, 2 = ,
4
=
Figure 10.The variation of F with Q for different values
of N with a 0.4, = m=2, 2 = , =Pi/2
Figure11.The variation of F with Q for different values
of N with a 0.4, = m=2, 2 = , =0
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
29
Figure 12.The variation of p with Q for different values
of with a 0.4, = m=2, 2 = , n=0.2
Figure 13. The variation of F with Q for different values
of m with a 0.4, = n=0.2, 2 = , =Pi/2
REFERENCES
[1] Ramachandra Rao, A., and Usha, S. Peristaltic transport of two
immiscible viscous fluid in a circular tube, J. Fluid Mech.,
298(1995), 271-285.
[2] Jaffrin, M.Y. and Shapiro, A.H. Peristaltic Pumping, Ann. Rev.
Fluid Mech., 3(1971), 13-36.
[3] Manton, M.J. Long-Wave length peristaltic pumping at low
Reynolds number, J. Fluid Mech. 68(1975), 467-476.
[4] Brasseur, J.G., Corrsin, S. and LU, Nan Q. The influence of a
peripheral layer of different viscosity on peristaltic pumping with
Newtonian fluids, J. Fluid Mech., 174(1987), 495-519.
[5] Srivastava, L.M. and Srivastava, V.P, Peristaltic transport of
blood: Casson model II, J. Biomech, 17(1984), 821-829.
[6] Provost, A.M. and Schwarz, W.H. A theoretical study of viscous
effects in peristaltic pumping, J. Fluid Mech., 279(1994), 177-195.
[7] Shukla, J.B. & Gupta, S.P. Peristaltic transport of a power-law
fluid with variable viscosity. Trans. ASME. J. Biomech. Engg.
104, (1982) 182-186.
[8] Misra, J.C. and Pandey, S.K. Peristaltic transport of a non-
Newtonian fluid with a peripheral layer, Int. J. Engg Sci.,
37(1999), 1841-1858
[9] Rao, I.R. & Rajagopal, K.R., 1999, Some simple flows of a
Johnson- Segalman fluid, Acta Mech.132,209-219.
[10] Kavitha. A, Hemadri Reddy. R, Sreenadh. S, Saravana. R,
Srinivas. A. N .S. Peristaltic flow of a micropolar fluid in a vertical
channel with longwave length approximation, Advances in
Applied Science Research, 2011, 2 (1): 269-279
[11] Vajravelu, K. Sreenadh, S. and Ramesh Babu, V.Peristaltic
pumping of a Herschel-Bulkley fluid in a channel, Appl. Math. And
Computation, 169(2005a),726-735.
[12] Vajravelu, K. Sreenadh, S. and Ramesh Babu, V.Peristaltic
pumping of a Herschel-Bulkley fluid in an inclined tube, Int. J.
Non-linear Mech. 40(2005b), 83-90.
[13] Vajravelu, K. Sreenadh, S. and Ramesh Babu, V.Peristaltic
pumping of a Herschel-Bulkley fluid in contact with a Newtonian
fluid, Quarterly of Appl. Math.64, (2006) No.4,593-604.
[14] Vajravelu. K, Sreenadh. S, Hemadri Reddy. R, and
Murugeshan.K, Peristaltic Transport of a Casson fluid in contact
with a Newtonian Fluid in a Circular Tube with permeable wall,
International Journal of luid Mechanics Research, 36 (3), (2009),
244-254.
[15] Vajravelu, K. Sreenadh,S. Lakshmi Narayana, P. The
influence of heat transfer on peristaltic transport of a Jeffrey fluid
in a vertical porous stratum, (accepted) Communications in
Nonlinear Science and Numerical Simulation (2010),
[16] Subbareddy, M.V. Manoranjan Mishra, Sreenadh, S. and
Ramachandra Rao, A. Influence of lateral walls on peristaltic
flow in a Rectangular ducts, Journal of Fluids Engineering, 127
(2005), 824-827.
[17] subba Reddy.M.V, A.Ramachandra Rao and S.Sreenadh,
Peristaltic motion of a power-law fluid in an asymmetric channel,
International Journal of Nonlinear Mechanics, 42, 1153-1161,
2006.
[18] Srinivas, S. & Kothandapani, M., 2009 The influence of heat and
mass transfer on MHD peristaltic flow through a porous space
with complaint wall, Appl. Math. Comput. 213, 197-208.
[19] Srinivas, S., Gayathri, R. & Kothandapani, M., 2009 The
influence of slip conditions, wall properties and heat transfer on
MHD peristaltic transport, Computer Physics Communications
180, 2115-2122.
[20] Eringen, A.C. Theory of Micropolar fluid ONR Report.1965
[21] Eringen, A.C. Theory of micropolar fluids, J.Math. Mech.,16
No.1(1966), 1-18.
[22] Ariman. T and Cakmak. A.S., Some Basic viscous flows in
Micropolar fluids, Rheologica Acta, Band 7, Heft 3 (1968),
236-242.
[23] Srinivasacharya, D., Mishra, M. and Ramachandra Rao
.A.Peristaltic pumping of a micropolar fluid in a tube, Acta
Mechanica, 161(2003), 165-178.
INTERNATIONAL JOURNAL OF INNOVATIVE TECHNOLOGY & CREATIVE ENGINEERING (ISSN:2045-711)
VOL.1 NO.6 JUNE
30
Вам также может понравиться
- JoinToGrow Chess Notation SheetДокумент2 страницыJoinToGrow Chess Notation SheetsivalaОценок пока нет
- A Simplified NMEA Sentence Generator For The Simulation of GPS TrackingДокумент8 страницA Simplified NMEA Sentence Generator For The Simulation of GPS TrackingsivalaОценок пока нет
- June 2018 Ijitce - Co.uk International Journal of Innovative Technology and Creative EngineeringДокумент27 страницJune 2018 Ijitce - Co.uk International Journal of Innovative Technology and Creative EngineeringsivalaОценок пока нет
- Enhanced Banking Framework For Improved Transaction SecurityДокумент15 страницEnhanced Banking Framework For Improved Transaction SecuritysivalaОценок пока нет
- Efficient Spatial Averaging Filter For High Quality Compressed Wireless Image TransmissioДокумент5 страницEfficient Spatial Averaging Filter For High Quality Compressed Wireless Image TransmissiosivalaОценок пока нет
- FICCI E-Commerce Conference TeamДокумент5 страницFICCI E-Commerce Conference TeamsivalaОценок пока нет
- IEC 2018 Ver 3Документ4 страницыIEC 2018 Ver 3sivalaОценок пока нет
- Borewell Pump Details 40 CharactersДокумент1 страницаBorewell Pump Details 40 CharacterssivalaОценок пока нет
- Cattle Feed PDFДокумент6 страницCattle Feed PDFRangasamyОценок пока нет
- Computer Application PDFДокумент14 страницComputer Application PDFsivalaОценок пока нет
- Ijitce NovДокумент52 страницыIjitce NovsivalaОценок пока нет
- IJITCE June 2011Документ1 страницаIJITCE June 2011sivalaОценок пока нет
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- Cetscale in RomaniaДокумент17 страницCetscale in RomaniaCristina RaiciuОценок пока нет
- Future Hopes and Plans - Be Going To - Present Continuous - Will - Be AbleДокумент31 страницаFuture Hopes and Plans - Be Going To - Present Continuous - Will - Be AbleDouglasm o Troncos RiosОценок пока нет
- 7 HR Data Sets for People Analytics Under 40 CharactersДокумент14 страниц7 HR Data Sets for People Analytics Under 40 CharactersTaha Ahmed100% (1)
- Problem Solving Cases in Microsoft Access and Excel 13th Edition Monk Solutions ManualДокумент24 страницыProblem Solving Cases in Microsoft Access and Excel 13th Edition Monk Solutions ManualJosephWilliamssjgdxОценок пока нет
- Cspu 620 Fieldwork Hours Log - Summary SheetДокумент2 страницыCspu 620 Fieldwork Hours Log - Summary Sheetapi-553045669Оценок пока нет
- WVTC Prospectus STG5Документ13 страницWVTC Prospectus STG5Vamuyan Adam SesayОценок пока нет
- Jncip EntДокумент4 страницыJncip Entreal_mc0% (2)
- 7C.3 Particles and ForcesДокумент19 страниц7C.3 Particles and Forcesharold hargridОценок пока нет
- My Daily Journal ReflectionДокумент4 страницыMy Daily Journal Reflectionapi-315648941Оценок пока нет
- The 4 Parenting StylesДокумент4 страницыThe 4 Parenting StylesJeff Moon100% (3)
- DepEd nursing proceduresДокумент8 страницDepEd nursing proceduresMary Anne TusiОценок пока нет
- Jenifer Romualdo Lee ResumeДокумент2 страницыJenifer Romualdo Lee ResumeLorilla AlvinОценок пока нет
- Philosophy BrochureДокумент2 страницыPhilosophy Brochureapi-512190037Оценок пока нет
- Overhead Crane Operator HandbookДокумент42 страницыOverhead Crane Operator HandbookMaey Akim100% (1)
- First Year Course RequirementsДокумент17 страницFirst Year Course RequirementsJOLLY RAY F. BEDERICOОценок пока нет
- San Antonio Elementary School 3-Day Encampment ScheduleДокумент2 страницыSan Antonio Elementary School 3-Day Encampment ScheduleJONALYN EVANGELISTA100% (1)
- Six Principles of Special EducationДокумент36 страницSix Principles of Special EducationIsabella Marie GalpoОценок пока нет
- A Presentation of Gabriel Tarde and The End of SocialДокумент6 страницA Presentation of Gabriel Tarde and The End of SocialHenrique Alcantara E SilvaОценок пока нет
- Semisupervised Neural Networks For Efficient Hyperspectral Image ClassificationДокумент12 страницSemisupervised Neural Networks For Efficient Hyperspectral Image ClassificationVishal PoonachaОценок пока нет
- Collaboration and Feeling of Flow With An Online Interactive H5P Video Experiment On Viscosity.Документ11 страницCollaboration and Feeling of Flow With An Online Interactive H5P Video Experiment On Viscosity.Victoria Brendha Pereira FelixОценок пока нет
- Guideline, Research WritingДокумент70 страницGuideline, Research WritingBilal Kemal89% (18)
- Research 2: First Quarter - Week 5 and 6Документ20 страницResearch 2: First Quarter - Week 5 and 6Rutchel100% (2)
- Erasmus Module CatalogueДокумент9 страницErasmus Module Catalogueelblaco87Оценок пока нет
- pr1-module-week-5-6-i-what-is-a-research-title1-1-the-most-important-element-that-defines-theДокумент28 страницpr1-module-week-5-6-i-what-is-a-research-title1-1-the-most-important-element-that-defines-theJerelyn MalacasteОценок пока нет
- Agenda Setting Syllabus 2010Документ2 страницыAgenda Setting Syllabus 2010Arta Novita HarlanОценок пока нет
- Icpap Membership FormДокумент4 страницыIcpap Membership FormMuhammad Ammar IftikharОценок пока нет
- Job Description: Preferably An MBA/PGDBM in HRДокумент2 страницыJob Description: Preferably An MBA/PGDBM in HRsaarika_saini1017Оценок пока нет
- Conceptual Framework: Dr. Fariza KhalidДокумент23 страницыConceptual Framework: Dr. Fariza KhalidrameshОценок пока нет
- Predloga Venture DesignДокумент9 страницPredloga Venture DesignĐorđe KlisuraОценок пока нет
- Weekly Report, Literature Meeting 2Документ2 страницыWeekly Report, Literature Meeting 2Suzy NadiaОценок пока нет