Академический Документы
Профессиональный Документы
Культура Документы
Users Tracking and Roles Mining in Web-Based Applications
Загружено:
Valery DmitrushchenkovИсходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Users Tracking and Roles Mining in Web-Based Applications
Загружено:
Valery DmitrushchenkovАвторское право:
Доступные форматы
Users Tracking and Roles Mining in Web-Based Applications
Yaron Gonen
Ben-Gurion University of the Negev, Beer Sheva, Israel
yarongon@cs.bgu.ac.il
Advisor: Prof. Ehud Gudes
ehud@cs.bgu.ac.il
ABSTRACT
When a database is accessed via a web application, web-users are not connect directly to the database, but rather via the web application. From a database point of view, such a connection is always established by the same db-user (i.e. the web applications db-user) and specic data on the web-user is not available to the database. As a consequence, web-users specic data cannot be audited and ne-grained access control cannot be implemented. We propose a method that provide the ability to track the web-users in web databases. The new method can be applied to legacy web applications without requiring any changes in their existing infrastructure. Using the tracked database, we propose a method to identify logical sessions (business logic), which we will use to mine the true users-roles of the web application. Advisor: Prof. Ehud Gudes.
1.
INTRODUCTION
1.1 Users Tracking
In todays web application world, the HTTP protocol is used to connect users to application servers rather than directly to a database. This has important implications on applications security. Unfortunately, HTTP, while useful for its original purpose of static content, is stateless and is not optimal for many of todays demands. Stateless means that there is a new connection established for every request. As such, the state of individual and recurring connections cant be supported by the protocol. The stateless aspect of HTTP was solved by the application servers for client to application server communication. The solution utilizes browsers cookies and the ability of the application server to create and maintain transparent sessions and thus state for each client. However, this represents only half of the architecture. The connection from the application server to the database still remains a challenge. The application server connects to the database on the
Supported by the Lynn and William Frankel center for computer science.
users behalf. How this is done makes all the dierence for two critical reasons: security and performance. The ideal solution is to connect the users to the database using the 1:1 mapping model, i.e. every end user has a distinct database account, or schema. This is secure because the database knows who is connected and can employ its security capabilities, specically access control and auditing. In the web environment the user is almost never directly connected to the database. The user is connected to the application, and the application is connected to the database (see Figure 1.1). One might therefore conclude the application should connect each application user to a distinct database account. However, this connection model design produces problems. One problem is security. This design would require the application to know the users database password. Another problem is resource limitation. Web applications typically support many end users. To connect each user to a private database account one will have to establish a dedicated database connection for each user. This could exhaust memory and computing resources on the application server, database or both. The solution is to use a Connection pool, a pool of pre-established database connections that links the application to a database schema. The application opens, and keeps open, several physical database connections. When an incoming request is made, the application will grab a connection from the pool, issue a query, and then return the connection back to the pool. Although this solves the resource limitation, it does not exempt the application from managing a list of database users and passwords, which is a security risk. For many applications, the criterion of performance is so important that Connection pool is the only possible solution. Typically, web applications use a model of N:1 for mapping actual end users (application users) to database accounts. This all-to-one mapping means that the application connects all end users to the same database schema, while this schema has the union of all privileges for all users connected to it. This design implies several security problems: Auditing: The users identity is not supported and their individual actions are untraceable. Access Control: The principle of minimal privilege is violated. It is impossible to authorize the web application user with appropriate privileges at the database level since all application users have access to the same data. It means that roles cannot be dened and no more ne-grained access control to the database exists. Ensuring that only the right privileges are available to the user is left only to the application. Intrusion Detection: Not only that the database does not iden-
Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for prot or commercial advantage and that copies bear this notice and the full citation on the rst page. To copy otherwise, to republish, to post on servers or to redistribute to lists, requires prior specic permission and/or a fee. EDBT/ICDT PhD 2011 March 25, 2011, Uppsala, Sweden Copyright 2011 ACM 978-1-4503-0696-6/11/03 ...$10.00.
14
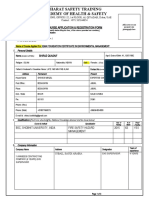
Figure 1: Typical architecture of web-applications. The users connect to the application server, and the application server uses a pooled connection to the database. tify the user who accesses it, but it is also impossible to follow SQL statements of the same user. Attackers can exploit this aw to access sensitive data, or use unauthorized functions. There exist attacks, such as business logic violations [11], which could be seen only at the session level (composed of multiple transactions), and thus could not be detected at the database level. There was an attempt to solve the problem of users identication in [11], but the proposed approach that is based on Parameterized views requires changes in both the web application and the database. Few methods for passing users identity from the web application to the database exist in latest Oracle [4] versions, but again, they require changes in legacy systems. Several third party vendors, such as Imperva [3] suggest a solution to this problem. However, there is no published technical information on how they do it and how good they are. We propose a new method and system that provides a way to link each SQL statement in the database to the end user that performed it (via the web application), thus making the web applications access to databases more traceable. Furthermore, we propose a method for ne grained access control and intrusion detection based on the tracking ability.
rights to database objects and create permission-proles of users, or in other words, roles. The challenge we are facing is mining roles from the actual webapplication usage information. Our data is the logical sessions, as tracked by the session identication method (Section 3.7). Each set of permissions used together within a logical session is a hint that these permissions should be granted as a group. The collected data holds information such as the set of permissions a user has, the set of users that access the same set of permissions, the frequency of using sets of permissions together, etc. Existing research on this subject use a user-permission assignment table gained from the database denition data. In our research we would like to take advantage of the knowledge hidden in the monitored data in order to get an accurate mapping of userspermissions needs in the application.
1.4 Motivational Example
Consider a web-application that serves a brokerage rm. The web-application manages customer accounts, executes customers trade orders, handles interactions of customers with nancial markets and updates news from the markets. Users of the web-application are divided into groups (or roles): Guest users a guest can query for security details and read market news. Customers a customer can submit trade requests on her account. Brokers a broker submits the trades to the market on the behalf of the customers. Newsmen a newsman submits market-related new. Markets the market is a group of users that actually make the transaction and updates the status of the submission. Each role has dierent permissions at the database level. For example, Newsmen have an insert permission on the News table, but all the other roles have a select permission. Customers have insert, update and delete permissions on the Trades table, Brokers have update permission and all the other roles have no permission at all. Like most web-applications today, the database maintains a Users table that holds information about the web users like user-name, password, role, etc. The connection to the database is established via a single user, the web-application user. Notice that the connection to the database is performed before any user logs in, since the authentication process needs to check the given user name and password against the Users table. From the database point of view all queries are performed by the same user. For example, all the following queries are performed by the same database user, however, it is obvious they are not performed by the same web user: s e l e c t from password insert into insert into security u s e r s where u s e r n a m e = : u s e r and = md5 ( : p a s s ) ; news ( i t e m ) v a l u e s ( : n e w s _ i t e m ) ; t r a d e s values ( : date , : action , : );
1.2 Sessions Tracking
Logical Session is a sequence of consecutive actions that could be applied on the web application in a single business oriented task. For example, in a banking web application, in order to transfer money to another account, the following actions should be taken in their presented order:
1. Request a transfer form. 2. Fill the form. 3. Submit the form. Identifying the dierent logical sessions is important because a logical sessions basically denes a role in the web application. Once discovering all the possible logical sessions (or roles), a deviation from any of them may indicate an attempt for intrusion.
We present a method to tag each query with its originating web user. Once we have done so, we can mine patterns of usage and easily track o course usage, which is probably a misuse or an intrusion.
1.5 Web Applications Frameworks
Many popular cutting-edge web applications frameworks today, such as Drupal [2], CakePHP [1] and Ruby on Rails [5], use this architecture of connecting to a database, so the need for such a tagging method is both for new and legacy systems.
1.3 Roles Mining
Usually, in a web-application architecture such as the one described in this work, the users of the application have access rights to certain modules of the application and they do not have rights at the database objects level. Using the tracked application users activities we can learn the permissions they have in terms of access
2. PREVIOUS WORK
15
2.1 Users Tracking
Most database protection methods rely heavily on the identity of the user accessing the database [6]. Using such identity, the authorization provided by views, roles and the Grant/Revoke mechanism can be applied [10]. Much eort was invested in developing methods for detecting intrusions to databases. Various intrusion detection systems for databases that also rely on user identity have been proposed in the literature [12, 9]. Intrusion detection methods can be divided into signature-based and anomaly detection techniques. Signature-based techniques typically rely on the prior explicit knowledge of attacks patterns, which is in turn is represented by one or more signatures or rules that are stored in a database. The database is frequently updated with new signatures, based on new observations. Anomaly detection systems build models of a normal system behavior during a training phase, and then, using the models the systems attempt to detect deviations from normal behavior during a detection phase. Any deviation from normal behavior is treated as a potential attack. Few methods for session boundaries identication that rely on known user identity have been proposed [8, 15]. The session identication task involves identifying session boundaries from the log of database events. The importance of session identication is derived from the following motivations: it enables grouping all user activities within one session and can be useful for performance optimization by utilizing the prediction of future queries; such grouping basically denes a role that can be used to derive the actual access rights of a user; a deviation from such a grouping may indicate an attempt for intrusion, thus it can be used for intrusion detection. However, as explained previously, the user identity is unknown at the database level in the web environment. In spite of the importance of this problem and in spite of a lot of eorts we have found only one academic paper that deals with the problem of users tracking at the database level. In [11] Roichman and Gudes proposed a Parameterized views method that allows transferring the web user identity to the database, thus enabling the using of database built-in access control mechanisms. The drawback of the approach is that it requires changes in both, the web application and the database, thus making it unpractical for legacy systems. Latest versions of Oracle [4] support several ways of preserving user identity through the web application to the database. For users known to the database, the proxy authentication in OCI, for example, can be used. OCI enables a web application to set up, within a single database connection, a number of "lightweight" user sessions, each of which uniquely identies a connected user. The application can switch between these sessions as required to process transactions on behalf of users. But in order to support the ne-grained authorization, Oracle must maintain all the application users. Since these users are created/dropped dynamically by the web application and the number of such users may be tremendous, this solution is not practical for a typical web application. Further, in order to use this method, legacy application should be modied. Several 3rd party products that refer the problem of user identication at the database level have been proposed. Imperva [3], for example, has developed multiple methods for identication of end users regardless of how these users access the database. According to vendors, Impervas SecureSphere product supports architectures that use connection pooling to aggregate multiple user sessions into a single database connection. SecureSphere tracks end users without requiring any changes in existing databases and web applications. However, Imperva has not published any technical information on how they do it and has not produced any measurements for their success.
2.2 Roles Mining
The role mining problem was dened by Vaidya et al [14] as the problem of discovering an optimal set of roles from existing user permissions. Their denition of the problem bound the approximation produced by an inaccurate number of roles found: Given a set user users U, a set of permissions P and a user-permission assignment UPA, nd a set of roles, R, a user-to-roles assignment UA and a role-to-permissions assignment PA consistent with UPA and minimizing |R|. In most role mining researches the userpermission assignment (UPA) are the basic information given as input to any role mining algorithm. This information is taken from the actual permissions granted at the database level, and the task of the mining is to nd the optimal set of roles that can cover the UPA.
3. PROPOSED METHOD
Our proposed method will contain two layers, the Network Management layer, and the Users Tracking layer. The Network Management Layer will include modules which handle the acquisition and management of network packets. It will handle the TCP sessions reconstruction and HTTP and DB protocols parsing. The output of this layer is a full HTTP session between a Web Server and a user and a full session between a Web Server and a database (SQL statements). The Users Tracking layer will include algorithms which handle the Web Application users identication and mapping of users actions to SQL statements in the database. This layer is responsible for the discovering of the actions available in the Web Application, discovering of SQL statements possible in the system, and matching between the discovered actions and SQL statements. This layer can be operated in two modes: learning mode and real-time mode. In the learning mode the output of this layer is a set of actions existing in certain Web Application, a set of SQL statements usable in the database, and for each action the mapping to the set of SQL statements in the database. In the realtime mode, the output of this layer is two log les. The rst one contains a log of users actions in terms of Web Application actions. The second one contains a log of SQL statements with a username attached.
3.1 Web Application Actions Discovery
Each Web application has a way of working to accomplish its functionality and this way is represented by the ordered sequences of actions that users can perform. Users can only perform the operations available at the application interface and no other operation is available for the end-users. The main question we refer in this section is which actions are supported by any arbitrary Web Application. Typically, these actions are applied by HTTP GET or POST requests from the users browser. Let us look at the following HTTP request: GET http://my.dns/act.php?lname=Smit&fname=Jon It contains the php script name (other script-engines such as ASP may be considered) followed by the list of parameters for the script. So, if we assume that theres a dierent script to each of the actions in the Web application, we can harvest all the scripts, and compile a list of all the actions. However, let as look at the following example: http://my.dns/act.php?lname=Smit&fname=Jon&op=add http://my.dns/act.php?lname=Smit&fname=Jon&op=del We face the problem: The script is the same for both requests, but the action itself resides in a parameter, whose name is of course arbitrary. As can be guessed, the script act.php adds the input name to a list if the parameter op equal to "add", and removes the input name from the list if the parameter op equal to "del". Our approach
16
is to dene action to be a concatenation of the script name and some relevant parameters of the script. The key question is how to identify the relevant parameters. We propose a method comprising of two phases: a training phase and a pruning phase. We assume we have a Web Server log le with all HTTP requests submitted by users to certain Web Application during specied period of time (this is a task of the Network Monitoring layer of our system to create such a log). First we split this log into two parts - one for the training and one for the pruning. We assume that all the possible actions appear in the training part, and we compile a list of possible actions out of all the HTTP parameter and their values. Next, we go over the pruning part. Every time we encounter an HTTP parameter with a dierent value then in the possible action list we remove it, since the value dierence indicates this HTTP paramter is a web-application parameter.
3.2 User Name Identication
The goal of this task is to detect when a user is logging in into a Web Application and what is his/her ID (username, for example). Since the parameters name (login) varies and its applicationdependent, we can choose one of the following methods to identify the username: Keywords - to maintain a list of words that might indicate a user logging in. Manual - every Web application wished to be analyzed will have to describe the login process, so the system will be able to identify the username eld in HTTP requests.
propose the following method to achieve this goal. First of all, we dene the problem formally. Given a set of actions, supported by the Web application A = a1 , a2 , ..., ak , a set of SQL queries supported by the database Q = q1 , q2 , ..., ql , a sequence of actions performed by the web-application during some specic period of time S a = a , a , ..., a , a A and a sequence of appropriative SQL n i 1 2 queries S q = q1 , q2 , ..., qm , qi Q we should produce a subjective function f : A Q< that maps every action to a sequence of SQL queries. For example, f (a5 ) = q5 , q3 , q1 , meaning that action a5 is mapped to the sequence q5 , q3 , q1 . The algorithm for nding the map function goes as follows: for each action a S a i we know from the input web log its start time and stop time, denoted tstart (ai ) and tstop (ai ) respectively. Let S Q (a ) be the sequence i of SQL queries executed on the database between tstart and tstop . Notice that S Q (ai ) may contain queries executed by other actions then a . We construct a dataset DS Q (ai ) of all S Q (ai ) (one sequence i for each instance of action ai in S A ). For each such dataset we nd the longest frequent subsequence with a support of 1.0 using a sequence mining algorithm such as CAMLS [7]. Each such sequence represents a set of SQL queries that appropriative action ai is mapped to.
3.6 Users Tracking in Terms of the Database
Given a mapping function f : A Q< , a tagged sequence of actions S = au1 , au2 , ..., auo and a sequence of SQL queries n A 1 2 S q = q1 , q2 , ..., qm we can produce a tagged sequence of SQL u1 u2 queries S q = q1 , q2 , ..., quo . n
3.3 Users Tracking in Terms of Web Application
After user login event has been detected, the goal of Users tracking task is to attach the user ID to all the actions user performs with Web application. This can be achieved by associating the user ID with HTTP session ID, which typically generated and sent from a web server to a client to identify the current interaction session. The client usually stores and sends the session ID as an HTTP cookie and/or sends it as a parameter in GET or POST queries. This approach will allow us to track all user activity in terms of Web application actions.
3.7 Finding Logical Sessions
A logical session is a sequence of consecutive web actions that are applied in a single business oriented task. For example, in a banking web application, in order to transfer money to another account, the following task should be performed in that specic order: 1. Select an account. 2. Request a transfer form. 3. Submit the form. The logical session identication task involves identifying session boundaries from the web-application log. We introduce a concept of Execution Tree. An Execution Tree represents all possible ways of working (business logic) for a given web application. We build this tree as follows: rst, we create the root of the tree, which is the login action. Next, we create the set A f that contains all the actions in A that appear rst right after the login action, and add them all as children of the root. We now go over the web log, and for each action traverse the tree, adding children nodes as needed. Every time we encounter an action ai such that ai A f we start a new traverse path at the root of the tree (this can happen when a user starts a new logical session without logging o).
3.4 SQL Statements Identication
Our goal in this section is to nd a set of SQL statements possible in certain Web database, given a log of SQL statements for some time period. Our approach is to learn the structure of each SQL statement possible in the system and to ngerprint that structure. There are a large number of such possible statements, but most of them dier only in constants that represent the users (or Web Application) inputs. If we replace the constants in each statement with variables, we get some high level representation of the SQL sentence called the ngerprint. In order to do so we rst use an SQL lexical analyzer to create the parse-tree. Since the SQL statements in the real database log do not contain "?" as parameters, but the values themselves, we need a schema-description in order to dierentiate schema objects from parameters. Using such schema-description given by the user/ extracted from the database, we automatically extract the parameters from the statement and create a ngerprint.
3.8 Roles Mining
The input we get from the logical sessions identied consists of a set of tuples (one for each session), containing a session number, a user id and a set of permissions used in that session. From that input we construct a Permission Usage Lattice (PUL). A node in the lattice represents a role and consists of the permissions of the role and the users who had used these permissions in the same session. A node n in the lattice is a sub-node of another node m if S etO f Permissions(n) S etO f Permissions(m). The cardinality of a node n is dened by the size of S etO f Permissions(n). Constructing the lattice from the input is rather strait forward: tuples
3.5 Mapping from Actions to SQL Queries
Our main goal is to attach the username to each SQL query performed by the Web application on the database. So far we are able to attach the username to each action in terms of the Web application. All we need in order to complete the task is to know the mapping function from the Web application action to actual queries in the database for each action existing in the Web application. We
17
having identical set of permission are represented by a single node containing all the dierent users. Keeping in mind that a node in the lattice represent a role, preserving all sets of permissions that appeared in the input may result with a large number of initial role candidates. In the worst case it may lead to 2n nodes, where n in the total number of permissions. However, aiming at a signicantly smaller number of roles, we wish to reduce the number of roles by applying the following steps: 1. Removing role n whose set of permissions is contained in a more general role m, and all users in n also appear in m. This way we do not grant the users additional permissions. 2. Constructing a mechanism for an optimal score where both keeping a role and giving a user permissions results in bad scoring.
4.
EVALUATION
In order to evaluate our system we need a comprehensive environment with thousands of users working in. We have decided to simulate it using a log generator that will generate HTTP sessions between a Web Server and a user and sessions between a Web Server and a database (SQL statements) from the network trafc. This generator will be based on the industry-standard TPC-E Benchmark [13]. TPC-E is an On-Line Transaction Processing (OLTP) workload. It is a mixture of intensive transactions that simulate the activities found in complex OLTP application environments. The database schema, data population, transactions, and implementation rules have been designed to be broadly representative of modern OLTP systems. The TPC-E emulator, which the log generator is based upon, models the activity of a brokerage rm that manages customer accounts, execute customer trade orders, and be responsible for the interactions of customers with nancial markets. We omit here the database design and the transaction ow of the business model. TPC-E generates all the events in the system and passes them to our log generator which creates a web log record and a series of SQL statements. Since we generated the logs ourselves we know: The user of each web-action. Which web-action generated which SQL statements. The true roles of the web-application. An evaluation for success can easily be set by comparing the results of our methods with the expected ones.
[8] K. Gupta, B. Nath, and K. Ramamohanarao. User session modeling for eective application intrusion detection. volume 278 of IFIP International Federation for Information Processing, pages 269284. Springer Boston, 2008. [9] W. G. J. Halfond and A. Orso. Preventing sql injection attacks using amnesia. In Proceedings of the 28th international conference on Software engineering, ICSE 06, pages 795798, New York, NY, USA, 2006. ACM. [10] R. Ramakrishnan and J. Gehrke. Database Management Systems. McGraw-Hill, Inc., New York, NY, USA, 2nd edition, 1999. [11] A. Roichman and E. Gudes. Fine-grained access control to web databases. In Proceedings of the 12th ACM symposium on Access control models and technologies, SACMAT 07, pages 3140, New York, NY, USA, 2007. ACM. [12] A. Roichman and E. Gudes. Diweda - detecting intrusions in web databases. In V. Atluri, editor, Data and Applications Security XXII, volume 5094 of Lecture Notes in Computer Science, pages 313329. Springer Berlin / Heidelberg, 2008. [13] TPC. Tpc-e. http://www.tpc.org/tpce/. [14] J. Vaidya, V. Atluri, and Q. Guo. The role mining problem: nding a minimal descriptive set of roles. In Proceedings of the 12th ACM symposium on Access control models and technologies, SACMAT 07, pages 175184, New York, NY, USA, 2007. ACM. [15] Q. Yao, A. An, and X. Huang. Finding and analyzing database user sessions. In L. Zhou, B. C. Ooi, and X. Meng, editors, Database Systems for Advanced Applications, volume 3453 of Lecture Notes in Computer Science, pages 851862. Springer Berlin / Heidelberg, 2005.
5.
[1] [2] [3] [4] [5] [6]
REFERENCES
Cakephp. http://cakephp.org/. Drupal. http://drupal.org/. Imperva. http://www.imperva.com. Oracle. http://www.oracle.com/. Ruby on rails. www.rubyonrails.org. E. Bertino, P. Samarati, and S. Jajodia. An extended authorization model for relational databases. Knowledge and Data Engineering, IEEE Transactions on, 9(1):85 101, January 1997. [7] Y. Gonen, N. Gal-Oz, R. Yahalom, and E. Gudes. Camls: A constraint-based apriori algorithm for mining long sequences. In DASFAA (1), pages 6377, 2010.
18
Вам также может понравиться
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- RYA-MCA Coastal Skipper-Yachtmaster Offshore Shorebased 2008 AnswersДокумент28 страницRYA-MCA Coastal Skipper-Yachtmaster Offshore Shorebased 2008 AnswersSerban Sebe100% (4)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- Pindyck TestBank 7eДокумент17 страницPindyck TestBank 7eVictor Firmana100% (5)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- CHAPTER 3 Social Responsibility and EthicsДокумент54 страницыCHAPTER 3 Social Responsibility and EthicsSantiya Subramaniam100% (4)
- State Immunity Cases With Case DigestsДокумент37 страницState Immunity Cases With Case DigestsStephanie Dawn Sibi Gok-ong100% (4)
- BST Candidate Registration FormДокумент3 страницыBST Candidate Registration FormshirazОценок пока нет
- Audit On ERP Implementation UN PWCДокумент28 страницAudit On ERP Implementation UN PWCSamina InkandellaОценок пока нет
- Kaitlyn LabrecqueДокумент15 страницKaitlyn LabrecqueAmanda SimpsonОценок пока нет
- Dry Canyon Artillery RangeДокумент133 страницыDry Canyon Artillery RangeCAP History LibraryОценок пока нет
- Proceedings of SpieДокумент7 страницProceedings of SpieNintoku82Оценок пока нет
- Bajaj Allianz InsuranceДокумент93 страницыBajaj Allianz InsuranceswatiОценок пока нет
- Ajp Project (1) MergedДокумент22 страницыAjp Project (1) MergedRohit GhoshtekarОценок пока нет
- Hayashi Q Econometica 82Документ16 страницHayashi Q Econometica 82Franco VenesiaОценок пока нет
- Transparency Documentation EN 2019Документ23 страницыTransparency Documentation EN 2019shani ChahalОценок пока нет
- Urun Katalogu 4Документ112 страницUrun Katalogu 4Jose Luis AcevedoОценок пока нет
- Ss 7 Unit 2 and 3 French and British in North AmericaДокумент147 страницSs 7 Unit 2 and 3 French and British in North Americaapi-530453982Оценок пока нет
- General Field Definitions PlusДокумент9 страницGeneral Field Definitions PlusOscar Alberto ZambranoОценок пока нет
- Digital LiteracyДокумент19 страницDigital Literacynagasms100% (1)
- Anaphylaxis Wallchart 2022Документ1 страницаAnaphylaxis Wallchart 2022Aymane El KandoussiОценок пока нет
- Form Three Physics Handbook-1Документ94 страницыForm Three Physics Handbook-1Kisaka G100% (1)
- Expense Tracking - How Do I Spend My MoneyДокумент2 страницыExpense Tracking - How Do I Spend My MoneyRenata SánchezОценок пока нет
- Daraman vs. DENRДокумент2 страницыDaraman vs. DENRJeng GacalОценок пока нет
- Online Learning Interactions During The Level I Covid-19 Pandemic Community Activity Restriction: What Are The Important Determinants and Complaints?Документ16 страницOnline Learning Interactions During The Level I Covid-19 Pandemic Community Activity Restriction: What Are The Important Determinants and Complaints?Maulana Adhi Setyo NugrohoОценок пока нет
- Final ExamSOMFinal 2016 FinalДокумент11 страницFinal ExamSOMFinal 2016 Finalkhalil alhatabОценок пока нет
- Brochure Ref 670Документ4 страницыBrochure Ref 670veerabossОценок пока нет
- 1934 PARIS AIRSHOW REPORT - Part1 PDFДокумент11 страниц1934 PARIS AIRSHOW REPORT - Part1 PDFstarsalingsoul8000Оценок пока нет
- Sustainable Urban Mobility Final ReportДокумент141 страницаSustainable Urban Mobility Final ReportMaria ClapaОценок пока нет
- Innovations in Land AdministrationДокумент66 страницInnovations in Land AdministrationSanjawe KbОценок пока нет
- Shahroz Khan CVДокумент5 страницShahroz Khan CVsid202pkОценок пока нет
- Epidemiologi DialipidemiaДокумент5 страницEpidemiologi DialipidemianurfitrizuhurhurОценок пока нет
- Ces Presentation 08 23 23Документ13 страницCes Presentation 08 23 23api-317062486Оценок пока нет