Академический Документы
Профессиональный Документы
Культура Документы
Info 160 Questions and Answers
Загружено:
keyshiaboateng0 оценок0% нашли этот документ полезным (0 голосов)
42 просмотров7 страницSoItware is the set oI programs that enables the computers hardware devices and application soIware to work together. A system restore point should be done,,,, Prior to installing new hardware or soIware.
Исходное описание:
Авторское право
© Attribution Non-Commercial (BY-NC)
Доступные форматы
DOCX, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документSoItware is the set oI programs that enables the computers hardware devices and application soIware to work together. A system restore point should be done,,,, Prior to installing new hardware or soIware.
Авторское право:
Attribution Non-Commercial (BY-NC)
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
42 просмотров7 страницInfo 160 Questions and Answers
Загружено:
keyshiaboatengSoItware is the set oI programs that enables the computers hardware devices and application soIware to work together. A system restore point should be done,,,, Prior to installing new hardware or soIware.
Авторское право:
Attribution Non-Commercial (BY-NC)
Доступные форматы
Скачайте в формате DOCX, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 7
1.
Setting a system restore point should be done
Prior to installing new hardware or soItware
2. What enables your computer to connect with other computers?
Network interIace card
3. Which holds the instructions the computer needs to start up?
ROM
4. Ergonomics is important only with desktop computers, not mobile devices.
False
5. Some mice include wireless USB receivers that contain Ilash memory to store your Iiles
True
6. The minimum set oI recommended standards Ior a program is known as the
System requirements
7. SoItware that is Ireely distributed but comes with conditions is
Shareware
8. Which oI the Iollowing is true about open source soItware?
The program can be changed and Ireely distributed
9. What is another name Ior SoItware as a Service (SaaS)?
Web-based application
10.To remove a program you no longer want, it`s better to delete it than uninstall it
False
11.Match the Iollowing terms to their deIinitions
a. Macro-automated sequence oI commands in productivity soItware
b. 09a-prerelease version oI commercial soItware
c. $:90-package containing multiple commercial soItware products
d. r00ar0-commercial soItware available at no charge
e. $ar0ar0-commercial soItware available Ior use Ior a limited or trial period oI time
12.The language consists oI just two digits: 0 and 1
Binary
13.Computers process data into inIormation by working exclusively with
Numbers
14. soItware is the set oI programs that enables the computer`s hardware devices and application
soItware to work together
System
15. computers are specially designed computer chips that reside inside other devices such as your car
or the electronic thermostat in your home
Embedded
16.Devices such as monitors and printers that are connected to the computer are called
Peripheral devices
17.Inkjet printers and laser printers are examples oI printers
Nonimpact
18.Restarting a computer when it is already powered on is called
A warm boot
19.The hard disk drive is a storage device, meaning that it stores data permanently
Nonvolatile
20.A(n) is where a peripheral device can attach to a computer so that data can be exchanged
between it and the operating system
Port
21.The S-video and the ports on a computer Iacilitate connecting the computer to multimedia
devices such as TVs and DVD players
DVI
22.plug into slots on the motherboard and provide additional Iunctionality Ior your computer
Expansion cards
23. is a Iorm oI permanent memory that holds all the instructions the computer needs to start up
ROM
24.RAM is considered volatile storage, which means it is
Temporary
25. is the applied science concerned with designing and arranging things that people use so that the
people and things interact most eIIiciently and saIely
Ergonomics
26.Which is true about plug-ins?
Plug-ins can present security risks
27.Which is NOT part oI a search engine?
Subject directory
28.Each time you connect to the Internet, your computer is assigned the same IP address
False
29.Match the Iollowing terms to their meaning
a. !0-tiny dot that creates an image on the computer monitor
b. 0r9-unit oI measure Ior processor speed
c. #08o:9on-the clearness or sharpness oI an image
d. !52-measurement oI printing speed
e. 5-measurement oI printer resolution
30.ocated on the Start menu, the primary purpose oI is to provide access to all the soItware
available on your computer
All programs
31.Which oI the Iollowing statements about the Windows Instant Search Ieature is FASE?
The Search Ieature is located by accessing the Start menu and clicking the Accessories Iolder
32.The is the top level oI a computer`s hard drive Iilling structure
C: drive
33.Select the choice that lists the terms in order Irom smallest to largest
Byte, kilobyte, megabyte, gigabyte
34.Data that has been organized or presented in a meaningIul Iashion is called
InIormation
35.SoItware reIers to a set oI instructions that tells the computer what to do. These instruction sets are
called
Programs
36.Predesigned Iorms that provide the basic structure Ior a particular kind oI document are known as
Templates
37.Which Iile Iormat enables users to share, view and print any Iile as long as they have the appropriate
program installed?
38.A(n) soItware installation allows you to decide which Ieatures you want to install on the hard
drive
Custom
39.When available, the best way to remove an unwanted soItware application is to
Use the application`s uninstall program
40.Match the Iollowing terms to their meanings:
a. :890r8-smallest segments within disk sectors
b. %rack8-concentric circles on the hard drive
c. $0c9or8-pie-shaped wedges on the hard drive
d. !a990r8-round, thin plates oI metal that make up a hard drive
41.Match the Iollowing terms to their meanings:
a. %a8k 2anag0r-displays perIormance measures Ior processes
b. $8902 r089or0-brings system back to a previously stable state
c. 8k c0an:5-removes unnecessary Iiles Irom the hard drive
d. 8k d01rag20n90r-regroups related pieces oI Iiles on the hard disk
e. rror c0ckng-checks the hard drive Ior damaged Iiles
42.Which oI the Iollowing is a program that appears to be something useIul or desirable but does something
malicious in the background?
A Trojan horse
43. Iloods a computer with requests until it shuts down and reIuses to answer any requests Ior
inIormation
A DDoS attack
44. is an unwanted piggyback program that usually downloads with soItware you are installing Irom
the Internet
Spyware
45.Spyware programs that monitor keystrokes with the intent oI stealing passwords, login IDs or credit card
inIormation are reIerred to as
Keystroke loggers
46.A(n) virus runs a program that searches Ior common data Iiles, compresses them and makes them
unusable
Encryption
47.Social is any technique that uses social skills to generate human interaction that entices
individual to reveal sensitive inIormation
Engineering
48.Which oI the Iollowing operating systems is used primarily with mainIrames as a network operating
system?
UNIX
49.MicrosoIt Windows and Mac OS use a interIace
Graphical user
50.The contains all oI the diIIerent conIigurations used by the OS and by other applications
Registry
51.BeIore upgrading your OS, you should back up your
Data Iiles
52.The OS allows you to organize the contents oI your computer in a hierarchical structure oI
Directories
53.The location oI a Iile is speciIied by its
File path
54.C:\Documents\Spring2012\CIS101\TermPaper\ComputerTechnology is an example oI a
File path
55.The process oI replacing repeated patterns oI letters in a Iile with a shorter placeholder is called
File compression
56.You can use the Windows to check on a nonresponsive program
Task Manager
57.Which oI the Iollowing ways oI connecting a device to your computer does NOT need a cable?
Bluetooth
58.Which statement about USB ports is TRUE?
One port can connect diIIerent types oI devices
59.Match the Iollowing views to their descriptions:
a. 89 v0-view the maximum number oI Iolders or Iiles at one time
b. $2a con8 v0-displays additional inIormation in ScreenTips when pointed to
c. %08 v0-displays icons with Iile name, application and Iile size
d. 09a8 v0-displays in list Iorm with additional inIormation displayed in columns
60.The concept oI the Internet developed Irom
The Cold War crisis
61.Web 2.0 describes
A trend oI new Web applications that combine the Iunctionality oI multiple applications
62.RSS stands Ior
Really Simple Syndiction
63.Webcasts diIIer Irom podcasts in that webcasts
Are not updated automatically
64.Adobe Reader, Flash Player and Quicktime player are all examples oI special soItware programs
called
Plug-ins
65.E-commerce that involved business buying and selling goods and services to other businesses is
called
B2B
66.The 's in https stands Ior
Secure socket layer
67.The text version oI a Web site`s Internet address is called the
UniIorm Resource ocator (UR)
68.HTTP is the abbreviation Ior
Hypertext transIer protocol
69.In the UR http://www.prenhall.com, the portion labeled http is the
Protocol
70.In the UR http://www.prenhall.com, the portion labeled .com is the
Top-level domain
71.Search engines have which three parts?
A spider, an indexer, and search engine soItware
72.The large scale networking (SN) project is
A U.S government Internet research project
73.The Internet and the World Wide Web are the same thing
False
74.The Internet protocol used to upload and download Iiles is HTTP
False
75.A subject directory is a set oI programs that searches the Web Ior speciIic keywords you wish to query
and returns to a list oI Web sites on which these keywords are Iound.
False
76.A(n) organizes the data in search engine programs into a large database
Indexer
77.A(n) actually searches other search engines rather than individual Web sites
Metasearch engine
78.A is a structured outline oI Web sites organized by topics and subtopics
Subject directory
79.The individual words you search Ior when using a search engine are reIerred to as
Keywords
80.A(n) is the part oI the search engine responsible Ior collecting data on the Web
Spider
81.Photocopiers do not present any vulnerability Ior potential hackers
False
82.VCU oIIers students server space Ior personal websites at ramsites.net
True
83.What is the Iree antivirus soItware all VCU students can use?
Sophos
84.Even a properly installed surge protector may Iail to protect a computer Irom all power surges
True
85.Antivirus soItware segregates inIected Iiles to prevent Iurther spread in a process known as
Quarantine
86.Match the Iollowing terms to their meanings:
a. :08nar1ng-exploiting a Ilaw in the Bluetooth access soItware with malicious intent
b. !r0909ng-creating a scenario that sounds legitimate enough that someone will trust you
c. ook0-a text Iile Ior storing personal preIerences pertaining to Web sites
d. o9n09-programs that run on a large number oI zombie computers
e. ogca 5or9-virtual communication gateway Ior a speciIic service, such as HTTP or FTP
87.Match the Iollowing terms to their deIinitions:
a. $cr59 kdd0-a teenage hacker who reuses hacking tools written by someone else
b. ack-a9 ack0r-an unethical hacker
c. !8ng-sending an e-mail containing Ialse inIormation to obtain personal inIormation
d. $oca 0ngn00rng-techniques used to manipulate people into perIorming actions or divulging
conIidential inIormation
e. 90-a9 ack0r-an 'ethical hacker
88.Match the Iollowing terms to their deIinitions:
a. !ack09 190rng-method Ior selectively allowing certain requests to access ports
b. ! addr088-a computer`s identity on the Internet
c. r0a-hardware or soItware Ior protecting computers Irom hackers
d. 09ork addr088 9ran8a9on-the technique oI assigning hidden internal IP addresses protected
Irom hackers
89.Which is the correct order oI the boot process?
Activate BIOS, conduct POST, load OS into RAM, check settings
90.You can determine the location oI a Iile by its
Path
91.The term that deIines excessive swapping oI Iiles between RAM and virtual memory is:
Thrashing
Вам также может понравиться
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- PainterДокумент5 страницPainterYantaru CornerОценок пока нет
- Python Pandas Tutorial PDFДокумент13 страницPython Pandas Tutorial PDFjuhiqueyoomОценок пока нет
- Personal Info:: Abdelfatah Atef Moustafa 593, 19 Street, El Mokattam, Cairo (+2) 01123029426Документ5 страницPersonal Info:: Abdelfatah Atef Moustafa 593, 19 Street, El Mokattam, Cairo (+2) 01123029426Ahmed TawfikОценок пока нет
- Research ProposalДокумент2 страницыResearch ProposalDonesa Rucci BenliОценок пока нет
- Access Control Software User Manual ZK SoftwareДокумент93 страницыAccess Control Software User Manual ZK SoftwareJovany SalazarОценок пока нет
- 2000 Why and Where - A Characterization of Data ProvenanceДокумент15 страниц2000 Why and Where - A Characterization of Data ProvenanceYingmin LIОценок пока нет
- Adobe Acrobat Reader DC Install For All Versions: About 5.270.000.000 Results (0,61 Seconds)Документ4 страницыAdobe Acrobat Reader DC Install For All Versions: About 5.270.000.000 Results (0,61 Seconds)Er SejОценок пока нет
- HW3 DB/Sudoku: Part A - DatabaseДокумент13 страницHW3 DB/Sudoku: Part A - DatabaseShubham GoyalОценок пока нет
- Evaluation of Business Performance (CIS412) : Lecture NotesДокумент5 страницEvaluation of Business Performance (CIS412) : Lecture NotesRodney Jack SandovalОценок пока нет
- Text Formatting Tags - A Simple Guide To HTMLДокумент3 страницыText Formatting Tags - A Simple Guide To HTMLJoynalIslamKabirОценок пока нет
- Hadoop and Java Ques - AnsДокумент222 страницыHadoop and Java Ques - AnsraviОценок пока нет
- FileIO in O/SДокумент28 страницFileIO in O/Snofiya yousufОценок пока нет
- Manik Mahajan: Curriculum VitaeДокумент5 страницManik Mahajan: Curriculum Vitaemanik mahajanОценок пока нет
- How Configure Wifi Proxy Settings in SmartphonesДокумент10 страницHow Configure Wifi Proxy Settings in Smartphonesch kishore kumarОценок пока нет
- EC5377u-872 Quick StartДокумент24 страницыEC5377u-872 Quick StartWaqas AhmedОценок пока нет
- View & Index: BY Sonal Pandey NITTTR, ChandigarhДокумент12 страницView & Index: BY Sonal Pandey NITTTR, ChandigarhsonalОценок пока нет
- Learn JPA & Hibernate - BaeldungДокумент6 страницLearn JPA & Hibernate - BaeldungTomás Patricio Izquierdo KairúzОценок пока нет
- VUMT ManualДокумент15 страницVUMT ManualTonyОценок пока нет
- MRP LIVE PROCESS Document V 1.0Документ18 страницMRP LIVE PROCESS Document V 1.0rahul shendage100% (1)
- Life and Legend of Saint ClareДокумент227 страницLife and Legend of Saint ClareClaudia StanОценок пока нет
- Msbi Developer Resume FresherДокумент3 страницыMsbi Developer Resume FreshersravanОценок пока нет
- Module 1 Getting Started With Windows PowerShellДокумент44 страницыModule 1 Getting Started With Windows PowerShellJunior CamargoОценок пока нет
- COMPRO Plug-In For Abaqus User 'S GuideДокумент14 страницCOMPRO Plug-In For Abaqus User 'S GuideMuhammad LutfiОценок пока нет
- Icecream Screen Recorder Pro 6 Crack With Serial Key 2020 Download PDFДокумент4 страницыIcecream Screen Recorder Pro 6 Crack With Serial Key 2020 Download PDFHildidОценок пока нет
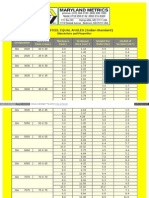
- Rolled Steel Equal Angles (Indian Standard)Документ4 страницыRolled Steel Equal Angles (Indian Standard)sandeepricky3dОценок пока нет
- One-TimePasswordAuthentication UACPДокумент114 страницOne-TimePasswordAuthentication UACPalvin bautistaОценок пока нет
- RESTful Web ServicesДокумент13 страницRESTful Web ServicessplokbovОценок пока нет
- Power BI Data Analysis and VisualizationДокумент289 страницPower BI Data Analysis and VisualizationMike100% (2)
- Instructions For Taking The ITEP Practice Test 22DEC16 1Документ3 страницыInstructions For Taking The ITEP Practice Test 22DEC16 1Tony Espinosa AtocheОценок пока нет
- 2.2 Json PDFДокумент15 страниц2.2 Json PDFKh MitraОценок пока нет