Академический Документы
Профессиональный Документы
Культура Документы
Windows OS Internal Training
Загружено:
ChandraSekharИсходное описание:
Авторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Windows OS Internal Training
Загружено:
ChandraSekharАвторское право:
Доступные форматы
Windows OS Internal Training
Index
Windows XP Overview Active Directory Directory Structure User profile (Start Menu, Desktop, My documents, App Data etc.,)
Advantage of NTFS (Sharing and Security, Encryption, Disk Quota etc.,)
Users and Groups overview System Tools (Backup, Disk Cleanup, Schedule Task, System restore etc.,)
Computer Manager(Event Viewer, Disk Management, Defrag, Device Manager etc.,)
Registry Overview ( about Hives and data types) Control Panel Overview Internal and External Commands "Run" commands
Windows OS Internal Training
Windows XP Overview The Windows eXPerience operating system is available as home and professional edition and are similar suitable for the use on standalone computers. The home edition is suitable for user which worked with Windows 9x/ME till now and don't need special network or security features in their environment. If the users have used Windows NT/2000 private, in business or both, the Professional Edition is not only with a view of the administration optimally. Microsoft already encloses 10,000 drivers on the installation media of Windows XP, about the Windows update further more 2,000 drivers are available. The Professional Edition of Windows XP has more network features than the Home Edition. An update of Windows 9 x/ME is possible, with Windows NT/2000 only the Professional Edition can be used for update. Optional FAT32 and NTFS are available as a file system for the installation partition. Windows XP (Windows version 5.1) becomes a predecessor of Windows 9x/ME as well as Windows NT/2000 and is available for 32-bits CPUs in the following versions: - Embedded - Home Edition (1 CPU) for private user (Oct. 2001)
Windows OS Internal Training
Professional Edition (2 CPU) for business user (Oct. 2001) Media Center (1 CPU) especially for multimedia devices (Nov. 2002) Tablet PC Edition especially for Tablet PCs (Nov. 2002) Server Edition (4 CPU) Advanced Server (8 CPU), also 64-bit Intel CPUs Microsoft Windows Fundamentals for Legacy PCs (July 2007)
A 64-bit version of Windows XP was announced officially of Microsoft in April 2003. The RC2 was available in February 2005. Windows XP Professional x64 was published in April 2005. At most 16 gbyte RAM are utilizably with that, the virtual address range enlarges to 16 byte. Same will be the product activation at all versions, which is needed at every new installation or extensive upgrade of the PC devices. Company customers can use can so-called corporate version by a special licensing option without this product activation. As the most visual innovation the revised Windows interface with the new design is well done, the design called Luna (as of beta 2428) can display window elements in high color. The return to the interface as of Windows 2000 is further possible. The representation and organization of the central registry is quit the same as used in Windows 2000. Standard features of Windows XP - Home and Professional Fast user switching Network assistant Remote control for the diagnosis (Remote assistant) Simplified user interface Windows Media Player Internet Explorer 6.0 Windows Movie Maker Special features of Windows XP - Professional Edition ASR - Automated System Recovery Create of offline files Backup/recovery function User guidelines (Policies) User administration (limited in Home Edition) File system encrypting (only for NTFS) Integration of the PC in a domain Integration of dynamic data storage Use as a terminal service client Use as a NetWare-Client
Windows OS Internal Training
Remote connection (desktop sharing) Use of multiple monitors EFS support in the file system Send and received Fax support SMP (use of more than one processor) The graphic device interface (GDI) in the version GDI+ can take advance of gamma correction and 3D interfaces in high color depth. Windows XP is more based on HTML than previous versions. The system control was designed complete in HTML. With the new CD-R/CD-RW software It is it is possible to create easy and simple CDs. The Windows terminal service makes the access to an shared Windows XP desktop with an terminal client like the VNC solution. With the new introduced multi-user function, user are now be able to run her applications in the background even if the user signs off and another user is logging on to Windows. If the previous user returns he can continue his work after that without having to once more start the recent documents or applications.
Active Directory What is Active Directory? Active Directory is Microsoft's trademarked directory service, an integral part of the Windows architecture. Like other directory services, such as Novell Directory Services (NDS), Active Directory is a centralized and standardized system that automates network management of user data, security and distributed resources and enables interoperation with other directories. Active Directory is designed especially for distributed networking environments. Active Directory was new to Windows 2000 Server and further enhanced for Windows Server 2003, making it an even more important part of the operating system. Windows Server 2003 Active Directory provides a single reference, called a directory service, to all the objects in a network, including users, groups, computers, printers, policies and permissions. For a user or an administrator, Active Directory provides a single hierarchical view from which to access and manage all of the network's resources.
Windows OS Internal Training
Why implement Active Directory? There are many reasons to implement Active Directory. First and foremost, Microsoft Active Directory is generally considered to be a significant improvement over Windows NT Server 4.0 domains or even standalone server networks. Active Directory has a centralized administration mechanism over the entire network. It also provides for redundancy and fault tolerance when two or more domain controllers are deployed within a domain. Active Directory automatically manages the communications between domain controllers to ensure the network remains viable. Users can access all resources on the network for which they are authorized through a single sign-on. All resources in the network are protected by a robust security mechanism that verifies the identity of users and the authorizations of resources on each access. Even with Active Directory's improved security and control over the network, most of its features are invisible to end users; therefore, migrating users to an Active Directory network will require little re-training. Active Directory offers a means of easily promoting and demoting domain controllers and member servers. Systems can be managed and secured via Group Policies. It is a flexible hierarchical organizational model that allows for easy management and detailed specific delegation of administrative responsibilities. Perhaps most importantly, however, is that Active Directory is capable of managing millions of objects within a single domain. Basic divisions of Active Directory Active Directory networks are organized using four types of divisions or container structures. These four divisions are forests, domains, organizational units and sites. Forests are not limited in geography or network topology. A single forest can contain numerous domains, each sharing a common schema. Domain members of the same forest need not even have a dedicated LAN or WAN connection between them. A single network can also be the home of multiple independent forests. In general, a single forest should be used for each corporate entity. However, additional forests may be desired for testing and research purposes outside of the production forest.
Windows OS Internal Training
Domains serve as containers for security policies and administrative assignments. All objects within a domain are subject to domain-wide Group Policies by default. Likewise, any domain administrator can manage all objects within a domain. Furthermore, each domain has its own unique accounts database. Thus, authentication is on a domain basis. Once a user account is authenticated to a domain, that user account has access to resources within that domain. Active Directory requires one or more domains in which to operate. As mentioned before, an Active Directory domain is a collection of computers that share a common set of policies, a name and a database of their members. A domain must have one or more servers that serve as domain controllers (DCs) and store the database, maintain the policies and provide the authentication of domain logons. With Windows NT, primary domain controller (PDC) and backup domain controller (BDC) were roles that could be assigned to a server in a network of computers that used a Windows operating system. Windows used the idea of a domain to manage access to a set of network resources (applications, printers and so forth) for a group of users. The user need only to log in to the domain to gain access to the resources, which may be located on a number of different servers in the network. One server, known as the primary domain controller, managed the master user database for the domain. One or more other servers were designated as backup domain controllers. The primary domain controller periodically sent copies of the database to the backup domain controllers. A backup domain controller could step in as primary domain controller if the PDC server failed and could also help balance the workload if the network was busy enough. With Windows 2000 Server, while domain controllers were retained, the PDC and BDC server roles were basically replaced by Active Directory. It is no longer necessary to create separate domains to divide administrative privileges. Within Active Directory, it is possible to delegate administrative privileges based on organizational units. Domains are no longer restricted by a 40,000-user limit. Active Directory domains can manage millions of objects.
Windows OS Internal Training
As there are no longer PDCs and BDCs, Active Directory uses multi-master replication and all domain controllers are peers. Organizational units are much more flexible and easier overall to manage than domains. OUs grant you nearly infinite flexibility as you can move them, delete them and create new OUs as needed. However, domains are much more rigid in their existence. Domains can be deleted and new ones created, but this process is more disruptive of an environment than is the case with OUs and should be avoided whenever possible. By definition, sites are collections of IP subnets that have fast and reliable communication links between all hosts. Another way of putting this is a site contains LAN connections, but not WAN connections, with the general understanding that WAN connections are significantly slower and less reliable than LAN connections. By using sites, you can control and reduce the amount of traffic that flows over your slower WAN links. This can result in more efficient traffic flow for productivity tasks. It can also keep WAN link costs down for pay-by-the-bit services. The Infrastructure Master and Global Catalog Among the other key components within Active Directory is the Infrastructure Master. The Infrastructure Master (IM) is a domain-wide FSMO (Flexible Single Master of Operations) role responsible for an unattended process that "fixes-up" stale references, known as phantoms, within the Active Directory database. Phantoms are created on DCs that require a database cross-reference between an object within their own database and an object from another domain within the forest. This occurs, for example, when you add a user from one domain to a group within another domain in the same forest. Phantoms are deemed stale when they no longer contain up-to-date data, which occurs because of changes that have been made to the foreign object the phantom represents, e.g., when the target object is renamed, moved, migrated between domains or deleted. The Infrastructure Master is exclusively responsible for locating and fixing stale phantoms. Any changes introduced
Windows OS Internal Training
as a result of the "fix-up" process must then be replicated to all remaining DCs within the domain. The Infrastructure Master is sometimes confused with the Global Catalog (GC), which maintains a partial, read-only copy of every domain in a forest and is used for universal group storage and logon processing, among other things. Since GCs store a partial copy of all objects within the forest, they are able to create cross-domain references without the need for phantoms. Active Directory and LDAP Microsoft includes LDAP (Lightweight Directory Access Protocol) as part of Active Directory. LDAP is a software protocol for enabling anyone to locate organizations, individuals and other resources such as files and devices in a network, whether on the public Internet or on a corporate intranet. In a network, a directory tells you where in the network something is located. On TCP/IP networks (including the Internet), the domain name system (DNS) is the directory system used to relate the domain name to a specific network address (a unique location on the network). However, you may not know the domain name. LDAP allows you to search for individuals without knowing where they're located (although additional information will help with the search). An LDAP directory is organized in a simple "tree" hierarchy consisting of the following levels: An LDAP directory can be distributed among many servers. Each server can have a replicated version of the total directory that is synchronized periodically. It is important for every administrator to have an understanding of what LDAP is when searching for information in Active Directory and to be able to create LDAP queries is especially useful when looking for information stored in your Active Directory database. For this reason, many admins go to great lengths to master the LDAP search filter.
Group Policy management and Active Directory
Windows OS Internal Training
It's difficult to discuss Active Directory without mentioning Group Policy. Admins can use Group Policies in Microsoft Active Directory to define settings for users and computers throughout a network. These setting are configured and stored in what are called Group Policy Objects (GPOs), which are then associated with Active Directory objects, including domains and sites. It is the primary mechanism for applying changes to computers and users throughout a Windows environment. Through Group Policy management, administrators can globally configure desktop settings on user computers, restrict/allow access to certain files and folders within a network and more. It is important to understand how GPOs are used and applied. Group Policy Objects are applied in the following order: Local machine policies are applied first, followed by site policies, followed by domain policies, followed by policies applied to individual organizational units. A user or computer object can only belong to a single site and a single domain at any one time, so they will receive only GPOs that are linked to that site or domain. GPOs are split into two distinct parts: the Group Policy Template (GPT) and the Group Policy Container (GPC). The Group Policy Template is responsible for storing the specific settings created within the GPO and is essential to its success. It stores these settings in a large structure of folders and files. In order for the settings to apply successfully to all user and computer objects, the GPT must be replicated to all domain controllers within the domain. The Group Policy Container is the portion of a GPO stored in Active Directory that resides on each domain controller in the domain. The GPC is responsible for keeping references to Client Side Extensions (CSEs), the path to the GPT, paths to software installation packages, and other referential aspects of the GPO. The GPC does not contain a wealth of information related to its corresponding GPO, but it is essential to the functionality of Group Policy. When software installation policies are configured, the GPC helps keep the links associated within the GPO. The GPC also keeps other relational links and paths stored within the object attributes. Knowing the structure of the GPC and how to access the hidden information stored in the attributes will pay off when you need to track down an issue related to Group Policy.
Windows OS Internal Training
For Windows Server 2003, Microsoft released a Group Policy management solution as a means of unifying management of Group Policy in the form of a snap-in known as the Group Policy Management Console (GPMC). The GPMC provides a GPO-focused management interface, thus making the administration, management and location of GPOs much simpler. Through GPMC you can create new GPOs, modify and edit GPOs, cut/copy/paste GPOs, back up GPOs and perform Resultant Set of Policy modeling. Directory Structures The Windows XP installation routine makes several changes to your hard drives. Windows XP uses two different partitions to store its information: a system partition and a boot partition. These partitions can exist on a single physical partition or on two physical partitions. Unfortunately, the way these terms are used is the reverse of common sense usage. The system partition is the partition containing the initial bootstrap components and the boot menu. The boot partition is the partition hosting the Windows XP root folder and all operational drivers and files. The boot and system partition files can be located on the same partition, on different partitions, or even on different hard drives. However, the system partition must always be on the first hard drive in the system and must be an active primary partition. The boot partition can be a primary partition or a logical drive within an extended partition. System Partition Table 3.1 shows the files contained on the system partition for an x86 computer. Table 3.1 Files Located on the System Partition for an x86 Computer File NTLDR Description Controls the operating system boot selection process and hardware detection before the actual Windows XP Kernel is launched. It requires that boot.ini, ntdetect.com, bootsect.dos (if dual booting), and ntbootdd.sys (if booting on a non-BIOS enabled SCSI drive; that is, scsi() is used instead of multi() in the ARC name in boot.ini) exist in the root system partition. Contains the contents of the boot menu displayed by NTLDR. This file contains the default operating system selection, the timeout period for the selection, and an ARC name or pathname
boot.ini
Windows OS Internal Training
for each listed operating system boot selection. ntdetect.co m Detects the major components of the computer before NTLDR selects a configuration and loads the Kernel.
bootsect.dos Present only on dual-boot systems. NTLDR uses this file when the selected operating system is not Windows XP. Bootsect.dos in turn seeks out the OS-specific operating system loader file, such as io.sys for MS-DOS or os2ldr.exe for OS/2. ntbootdd.sys Used only on systems with SCSI drives that do not have onboard BIOS translation enabled. It is a copy of the device driver for your particular SCSI drive. hiberfil.sys NOTE When BOOTSECT.DOS is installed using the DOS-mode setup (for example, a Windows 98 startup disk), the file will still appear, even though it is not really a dual-boot system, meaning there is no COMMAND.com to boot into DOS. In this scenario, there is only one OS entry in the boot.ini file, and the boot selection menu does not appear. Other files can appear in the system partition on x86 dual-boot and multiboot systems. The addition of these files does not affect the function or capabilities of the required Windows XP boot files in the system partition. Installing multiple operating systems on a single computer with Windows XP Professional (or Home Edition) often requires a specific installation order or manual post-installation configuration changes. Both the Microsoft Windows XP documentation and TechNet include detailed articles on performing multiboot setups with Windows XP Professional, Windows XP Professional, Windows Server 2003, Windows 95, Windows 98, MS-DOS, and OS/2. Multi-booting Windows XP with non-Microsoft operating systems, such as Linux, often requires third-party boot and partition managers. The system partition does not include any folders. It exists as a root folder only with three or more files. Having additional folders in the system partition does not affect the operation of boot files. You might notice that the files in the system partition are among the files found on an Emergency Repair Disk (ERD). This should not be surprising Available if hibernation is enabled on the computer.
Windows OS Internal Training
because an ERD is used to restore files to the system partition if these files are corrupted, deleted, or otherwise destroyed. Boot Partition The directory structure and subsequent files installed into the boot partition are quite a bit more complex than those of the system partition. Table 3.2 describes the five folders created in the boot partition's root folder (normally the C:\ drive) during the installation of Windows XP. Table 3.2 Folders Created by Windows XP in the Boot Partition's Root Folder Directory Description
Documents This folder is used to hold the configurations for each user who accesses the system. In Windows NT, this information was and Settings stored in the \Windows\profiles folder. Program Files System Volume Information Recycler This folder is the default installation location for Windows applications. This folder stores all disk permission and security information.
This is not a true folder; instead, it is the system-controlled temporary repository for deleted files. You can access its contents by launching the Recycle Bin tool from the desktop. Note that this folder does not appear until a file is deleted. This is the main folder containing all the Windows XP system files, and the default folder for Windows XP.
Windows
The root of the boot partition is also the default location for pagefile.sys, which is the page file the Windows NT virtual memory system uses. NOTE The file and folder structure discussed in this chapter is derived from a fresh installation of Windows XP on an x86 desktop system with Service Pack 1 integrated. The typical installation method was chosen. No other applications from Microsoft or any third-party vendors were present on the system. That means no additional services or applications were installed from the
Windows OS Internal Training
Windows XP distribution CD, no hotfixes were applied, and Internet Explorer was not updated. The Program Files folder is home to 16 subfolders: Common Files. This folder contains files shared with the Microsoft applications. ComPlus Applications. This folder contains files used by ComPlus applications. If there are no ComPlus applications installed on your XP machine, this folder will be empty. COM+ builds on the Microsoft Component Object Model (COM) integrated services and features, making it easier for developers to create and use software components in any language, using any tool. Internet Explorer. This folder contains the files and executables for Internet Explorer, a Web-browsing tool. Messenger. This folder contains files and executables for the new Windows Messenger Service. This service combines features found in MSN Messenger with an improved communications infrastructure. Movie Maker. This folder contains the files and executables for the Movie Maker application. MSN. This folder contains the files and executables for MSN Explorer, the new Internet connectivity tool from Microsoft that combines Web, email services, and Internet setup services. MSN Gaming Zone. This folder contains the files and executables for the MSN Gaming Zone. NetMeeting. This folder contains all the files used by Microsoft NetMeeting. Online Services. This folder contains files used to establish Internet connectivity. These files enable you to set up Internet access through MSN or to select another available Internet service provider. Outlook Express. This folder contains all the files and executables needed by Microsoft Outlook Express, a simple e-mail application. Uninstall Information. This is a hidden folder containing files and information for uninstall services. Windows Media Player. This folder contains the Microsoft Media Player application.
Windows OS Internal Training
Windows NT. This folder contains any applications that have been ported over from other Windows operating systems (such as Pinball). This folder has empty folders in it if the ported components were not selected during installation. Windows Update. This folder contains all the files used by the Windows Update Service. Xerox. This folder contains all the files used by Xerox applications. By default, this folder is empty. The Windows root-level folder contains an extensive subfolder hierarchy but very few files. The Windows\System32 folder is the main repository of all files required to launch and operate Windows XP. The following files are among those stored in the Windows folder: Wallpaper and tiling images (.bmp)
Initialization and configuration files for backward-compatibility with various 16-bit utilities and applications (.ini) Readme, log, and documentation files (.txt, .log, and .wri) The following is a listing of the subfolders under the Windows folder: Addins. ActiveX controls files. Contains application compatibility .dlls and Appfix
AppPatch. packages.
Config. Contains configuration .idf files used by the MIDI sound system. Depending on system configuration, this folder might be empty. Connection Wizard. Files used for establishing Internet connectivity. Can be an empty folder. CSC. The Client Side Cache is where contents of mapped network drives are cached so that the contents of these drives will be available offline. By default, this folder contains empty folders. Cursors. Contains static and animated cursor files. You can use these files by configuring the Mouse applet. Debug. Contains .log files that can be used to debug network connectivity and other setup functions.
Windows OS Internal Training
Downloaded Program Files. Contains ActiveX controls and Java applets that have been downloaded from the Internet. Driver Cache. Contains a platform subdirectory and a copy of the driver.cab file so that new devices can be easily installed without needing the Windows XP CD. Might contain SP1.cab if installing an integrated copy of the operating system. Fonts. Contains all installed fonts.
Help. Contains the help files used by the Windows XP Help system and all its native utilities. Ime. Files to support the Input Method Editor. Provides language support for Windows XP. Inf. Contains the .inf (system information) files used to install software components. This is a hidden folder. Installer. The location for temporary files used by the Windows Installer program. This is a hidden folder. Java. Folder structure for Java files. Media. Contains media files (sound and video) used by sound themes.
Msagent. Microsoft agent files, which are software services that support using animated characters in the Windows interface to assist users in manipulating the operating system. Msapps. Contains files for backward-compatibility with applications that use shared components. Mui. MUI (Multilingual-User Interface) Packs give companies flexibility in making language options available to users. Offline Web Pages. Any Web pages designated as offline accessible are stored in this folder, along with any images and other files that go with it. PCHEALTH. Contains files and subfolders to support the Microsoft Help Center Service. These files support all the Windows XP Help services, including features such as Remote Desktop Assistance. Prefetch. Contains the files that XP is tracking for prefetch execution. Caching frequently used files decreases startup time for applications and optimizes XP performance.
Windows OS Internal Training
Registration. Contains files that support COM+ applications. Repair. Contains backup copies of the permanent Registry hives. The NTBackup program updates this directory with the System State option. Resources. Contains files to support the user's shell interface.
Security. Contains subfolders and files related to security. Includes log files that define the default security applied during setup and templates for assigning new security privileges. Srchasst. Contains files and subfolders for Search Companion, the updated search assistant included with XP. Includes files to support an indexing function that improves search performance. System. Contains 16-bit versions of protected and real mode drivers and .dll files used by applications. These files are provided for backwardcompatibility with older applications. Additional 16-bit driver files can be stored in this folder. System32. Contains the core operating system files and subfolder trees. Tasks. Contains intervention. scheduled tasks that run without operator
Temp. Contains any temporary files used by the system and applications. Twain_32. Contains files to support Twain technology, enabling a scanner document to be inserted into a file. Web. Contains files and subfolders to support Internet printing and document access. WinSxS. A folder to store the shared components of side-by-side applications. These can be multiple versions of the same application or the same assembly. The System32 subfolder contains most of the files used by Windows XP. This is the primary storage location for DLLs, Control Panel applets (.cpl), device drivers (.drv), help files (.hlp and .cnt), MS-DOS utilities (.com), language support files (.nls), screensavers (.scr), setup information files (.inf), and a handful of other files used for support, configuration, or operation. The most commonly accessed described in the following list: subfolders in Windows\System32 are
Windows OS Internal Training
1025, 1028, 1031, 1033, etc. Contains locationization languages files. Most of these folders will be empty. The English language is 1033. The complete list of locale IDs can be found at http://www.microsoft.com/globaldev/reference/loclanghome.mspx. CatRoot. Contains security catalog files. CatRoot2. Contains catalog database files. Com. Contains COM object information. Config. Contains the Registry hives used during bootup and is the storage location for the System, Security, and Application log files viewed through Event Viewer. Config now contains a new folder called \systemprofile that holds a standard profile for the local system. DHCP. This is an empty folder used to hold Dynamic Host Configuration Protocol (DHCP) database files if the host becomes a DHCP server. DirectX. Contains files to support the accelerated performance features of game devices. Dllcache. Contains backup copies of the operating system files that are under the Windows File System Protection system. Drivers. Contains driver files (.sys); the \etc folder contains sample copies of the TCP/IP text-based configuration files, such as Hosts and LMHosts files. Export. This is an empty folder. IAS. If there is no Internet connection capability, this is an empty folder used to hold configuration files for the Internet Authentication Service. This service is typically found on servers. If the machine has a device capable of connecting to the Internet, the IAS folder should not be empty. It will contain two files: DNARY.MDB (used to phrase IAS log files) and IAS.MDB (used to store remote access policies). Icsxml. Contains files for Univeral Plug and Play. IME. Contains files for Input Method Editors. Intsrv. Contains files used by the World Wide Web service. This folder is empty. Macromedia. Contains a subfolder with the Shockwave Flash .ocx file.
Windows OS Internal Training
MsDTC. Contains Microsoft Distributed Transaction Coordinator files that control transaction output and message delivery between two different applications or processes. MUI. Contains Multilingual-User Interface files that are created by applications, such as Service Pack 1. Os2. Contains drivers used by the OS/2 subsystem. NPP. Contains files to support collecting network traffic from an XP PC by a Network Monitor server. Oobe. Contains "Out of Box Experience" files that prompt users to complete product activation and registration and to create a new user other than Administrator. This feature is activated only after setup. Ras. Contains the default scripts used by Dial-Up Networking. Restore. Contains a list of files to be monitored and saved to an alternative location in case of file corruption. The System Restore service takes snapshots of the XP system periodically to enable the system to be restored from a previous set of data. This folder also contains the machine GUID. Setup. Contains setup files for additional services, such as FrontPage Server Extensions and Microsoft Fax. ShellExt. By default, this folder is empty. Spool. Used by the printing system to store spooled print jobs and related files. The Printers subfolder is used to store spool files. The other folders found here vary based on printer drivers and configuration. USMT. USMT stands for User State Migration Tool. This folder contains files to support both USMT and the File and Settings Transfer Wizard. Both tools enable user files and settings to be copied to another PC. WBEM. Used by Web Based Enterprise Management to store its data and executable files and utilities. The Microsoft implementation of WBEM is the Windows Management Instrumentation (WMI) Service. With WMI, programmers can create applications that control network devices, using the same commands regardless of platform. Wins. Contains files to support the Windows Internet Name Service (WINS). This folder is empty.
Windows OS Internal Training
User Profile folders Structure Applies To: Windows Server 2003, Windows Server 2003 R2, Windows Server 2003 with SP1, Windows Server 2003 with SP2 A user profile consists of:
A registry hive. The registry is a database used to store computer- and user-specific settings. Portions of the registry can be saved as files, called hives. These hives can then be reloaded for use as necessary. User profiles take advantage of the hive feature to provide roaming profile functionality. The user profile registry hive is the NTuser.dat in file form, and is mapped to the HKEY_CURRENT_USER portion of the registry when the user logs on. The NTuser.dat hive maintains the users environment preferences when the user is logged on. It stores those settings that maintain network connections, Control Panel configurations unique to the user (such as the desktop color and mouse), and application-specific settings. The majority of the settings stored in the registry are opaque to user profiles settings are owned and maintained by individual applications and operating system components. A set of profile folders stored in the file system. User profile files are stored in the filesystem in the Documents and Settings directory, in a per user folder. The user profile folder is a container for applications and other operating system components to populate with subfolders and per-user data, such as shortcut links, desktop icons, startup applications, documents, configuration files and so forth. Windows Explorer uses the user profile folders extensively for special folders such as the users desktop, start menu and my documents folder.
Together, these two components record user-configurable settings that can migrate from computer to computer. The default location of user profiles was changed from the Windows NT 4.0 operating system to allow administrators to secure the operating system folders without adversely affecting user data. On a clean installed computer running Windows Server 2003, Windows XP or Windows 2000, profiles are stored in the %Systemdrive%\Documents and Settings folder. In contrast, on computers running Windows NT 4.0, profiles are stored inside the system directory, at %Systemroot%\profiles folder (typically WINNT\profiles).
Windows OS Internal Training
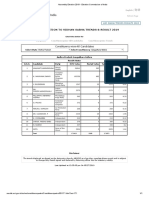
Note If you upgrade a computer from Windows NT 4.0, the profile location remains %Systemroot%\profiles. Table 1 below shows the location of user profiles for each of the possible installation scenarios:
Table 1 User Profile Locations Operating system Windows Server 2003 clean installation (no previous operating system) Windows Server 2003 upgrade of Windows 2000 Windows Server 2003 upgrade of Windows NT 4.0 Location of user profile %SYSTEMDRIVE%\Documents and Settings; for example, C:\Documents and Settings
SYSTEMDRIVE%\Documents and Settings; for example, C:\Documents and Settings %SYSTEMROOT%\Profiles; for example, C:\WinNT\Profiles
Configuration Preferences Stored in the Registry Hive The NTuser.dat file contains the following configuration settings:
Windows Explorer settings. All user-definable settings for Windows Explorer, as well as persistent network connections. Taskbar settings. Printer settings. All network printer connections. Control Panel. All user-defined settings made in the Control Panel. Accessories. All user-specific application settings affecting the Windows environment, including: Calculator, Clock, Notepad, Paint, and HyperTerminal, among others.
Windows OS Internal Training
Application Settings. Many applications store some per user settings in the users registry hive (HKEY_CURRENT_USER). An example of these types of settings would be Microsoft Word 2000s toolbar settings.
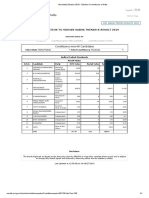
Configuration Preferences Stored in Profile Directories Figure 1 below shows the structure of the user profile.
Figure 1: User Profile.
Each users profile contains the following folders:
Application data*. Application-specific data, such as a custom dictionary for a word processing program. Application vendors decide what data to store in this directory. Cookies. Internet Explorer cookies.
Windows OS Internal Training
Desktop. Desktop items, including files and shortcuts. Favorites. Internet Explorer favorites Local Settings*. Application settings and data that do not roam with the profile. Usually either machine specific, or too large to roam effectively.
Application data. Computer specific application data. History. Internet Explorer history. Temp. Temporary files. Temporary Internet Files. Internet Explorer offline cache.
My Documents. The new default location for any documents that the user creates. Applications should be written to save files here by default.
My Pictures. Default location for users pictures. My Music. Default location for users music.
NetHood*. Shortcuts to My Network Places items. PrintHood*. Shortcuts to printer folder items. Recent. Shortcuts to the most recently used documents. SendTo. Shortcuts to document storage locations and applications. Start Menu. Shortcuts to program items. Templates*. Shortcuts to template items.
* These directories are hidden by default. To see these directories, change the View Options. The Folder Redirection feature of IntelliMirror allows an administrator to redirect the location of certain folders in the user profile to a network location. When these redirected folders are accessed either by the operating system or by applications, the operating system automatically redirects to the location on a network share specified by the administrator. From a user perspective, this is similar to the roaming scenario because users have the same settings regardless of which computers they use. However unlike roaming, these settings actually remain on the network share. Folder
Windows OS Internal Training
redirection can be used with all types of user profiles: local, roaming, or mandatory. Using Folder Redirection with local profiles can provide some of the benefits of roaming profiles (such as having a users data available at any computer or maintaining data on the server) without the need to implement roaming profiles. Remember though, using Folder Redirection with a local profile would only result in the users documents and files being available from all computers. To have settings and configurations move with the user, you would need to use roaming profiles. Combining Folder Redirection with roaming profiles gives the benefit of roaming profiles, while minimizing network traffic caused by synchronization of the profile. Folder redirection is accomplished using Group Policy. The use of Folder Redirection with roaming profiles is discussed later in this article. Table 2 below lists the folders that roam with the profile by default and indicates whether they can be redirected using Group Policy.
Table 2 Folders that Roam with the Profile Roams with profile by default Yes Redirect with Group Policy Yes
Folder Name Application Data
Description Per-user roaming application data.
Windows OS Internal Training
Cookies Users Internet Explorer cookies. Desktop items, including files and shortcuts. Users Internet Explorer favorites. Temporary files and peruser non-roaming application data. Users documents. Shortcuts to My Network Places items. Shortcuts to printer folder items. Shortcuts to recently used documents Shortcuts to document storage locations and applications. Yes No
Desktop
Yes
Yes
Favorites
Yes
No
Local Settings
No
No
My Documents NetHood
Yes Yes
Yes No
PrintHood
Yes
No
Recent
Yes
No
Send To
Yes
No
Start Menu Templates
Users personal start menu. Yes Per-user customized templates. Yes
Yes No
Non-Roaming Folders The default behavior of roaming user profiles in Windows NT 4.0 is to include all the folders in the user profile directory. Thus when a user first logs on, all
Windows OS Internal Training
folders within the profile folder are copied from the server to the client at logon and copied back at logoff, Windows 2000 introduced a per-user local settings folder into the user profile that is not copied during log on or logoff. This folder is intended for the storage of operating system components and other applications can store non-roaming per-user data. A typical example of the usage of this folder is for Microsoft Internet Explorer to store a users Favorites in the roaming portion of the user profile but store the Temporary Internet Files in the local (non-roaming) portion of the user profile. This will allow a user to retain access to their favorite URLs, but will save copying of temporary cache files at logon and logoff. On computers running Windows Server 2003, Windows XP or Windows 2000, the History, Local Settings, Temp and Temporary Internet Files folders do not roam by default. Other Non-Roaming Folders are configured using the Group Policy Object Editor. The path for this setting in the Group Policy name space is: User Configuration\Administrative Templates\System\User Profiles\Exclude directories in roaming profile Once enabled this allows multiple folder names to be defined, all relative to the root of the users profile. Once included in the policy these folders will not be copied to the local machine at logon, nor copied back to the server at logoff. This setting is likely to result in decreased time taken for a user to logon, by restricting the amount of data within a user profile that really does roam with the user. How Do Users Get Their Profile? The way in which users get their profiles depends on the type of profile they're configured to use. This section describes this process. Local Profile - New User 1. The user logs on. 2. The operating system checks the list of user profiles located in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersi on\ProfileList to determine if a local profile exists for the user.
3. Because this is a new user, no local profile is found. If the computer is
part of a domain, the operating system checks if a domain wide default profile exists in a folder named Default User on the domain controllers NETLOGON share.
Windows OS Internal Training
If a domain wide profile exists, it is copied to a subfolder on the local computer with the user name under %SYSTEMDRIVE %\Documents and Settings\. For example, a new user with the user name JDoe would have a profile created in %SYSTEMDRIVE %\Documents and Settings\JDoe. If a default domain profile does not exist, then the local default profile is copied from the %Systemdrive%\Documents and Settings\Default User folder to a subfolder on the local computer with a user name under %Systemdrive%\Documents and Settings\.
4. If the computer is not part of a domain, the local default profile is copied from the %Systemdrive%\Documents and Settings\Default User folder to a subfolder on the local computer with a user name under %Systemdrive%\Documents and Settings\. 5. The users registry hive (NTUSER.DAT) is mapped to the HKEY_CURRENT_USER portion of the registry. 6. The users %userprofile% environment variable is updated with the value of the local profile folder 7. When the user logs off, a profile is saved to the local hard disk of the computer. Local Profile - Existing User 1. The user logs on. 2. Windows checks the list of user profiles located in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersi on\ProfileList to get the path to the users profile. 3. The users registry hive (NTUSER.DAT) is mapped to the HKEY_CURRENT_USER portion of the registry. 4. The users %userprofile% environment variable is updated with the value of the local profile folder. 5. When the user logs off, the profile is saved to the local hard disk of the computer. Roaming Profile - New User 1. The user logs on.
Windows OS Internal Training
2. The path to the users roaming profile is retrieved from the user object on the Domain Controller. 3. Windows checks to see if a profile exists in the roaming path, if no profile exists a folder is created. 4. Windows checks the list of user profiles located in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersi on\ProfileList to determine if a cached copy of the profile exists. If a local copy of the profile is not found, and the computer is part of a domain, Windows checks to determine if a domain wide default profile exists in the Default User folder on the domain controllers NETLOGON share.
If a domain wide profile exists, it is copied to a subfolder on the local computer with their user name under %Systemdrive %\Documents and Settings\. If a default domain profile does not exist, then the local default profile is copied from the %Systemdrive%\Documents and Settings\Default User folder to a subfolder on the local computer with their user name under %Systemdrive%\Documents and Settings\.
5. The users registry hive (NTUSER.DAT) is mapped to the HKEY_CURRENT_USER portion of the registry. 6. The users %userprofile% environment variable is updated with the value of the local profile folder 7. The user can then run applications and edit documents as normal. When the user logs off, their local profile is copied to the path configured by the administrator. If a profile already exists on the server, the local profile is merged with the server copy (see merge algorithm later in this paper for more details). Roaming Profile - Existing User 1. The user logs on. 2. The path to the users roaming profile is retrieved from the user object on the Domain Controller. 3. Windows checks to see if a profile exists in the roaming path, if no profile exists a folder is created.
Windows OS Internal Training
4. Windows checks the list of user profiles located in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersi on\ProfileList to get the path to the users cached profile if it exists. 5. The contents of the local cached profile are compared with the copy of the profile on the server, and the two profiles are merged. (See the new merge algorithm later in this paper for more details). 6. The users registry hive (NTUSER.DAT) is mapped to the HKEY_CURRENT_USER portion of the registry. 7. The users %userprofile% environment variable is updated with the value of the local profile folder 8. The user can then run applications and edit documents as normal. When the user logs off, the local profile is copied to the path configured by the administrator. If a profile already exists on the server, the local profile is merged with the server copy.
File Systems You can use FAT16, FAT32, NTFS, or a combination of file systems on a single computer, but each volume can have only one file system installed. When choosing which file system to use, you need to determine the following:
How the computer is used (dedicated to Windows XP or multiple-boot). The number and size of locally installed hard disks. Security considerations. Interest in using advanced file system features.
Windows OS Internal Training
Important It is recommended that you format all Windows XP volumes with NTFS except on computers with certain multiple-boot configurations. For more information about NTFS, see NTFS File System later in this chapter. Certain file systems have limitations regarding the minimum and maximum size of volumes that they can format. Additionally, the cluster size of each file system, which depends on the size of the volume and the maximum number of clusters the file system can manage, can affect the choice of file systems. The version of NTFS included with Windows XP can take advantage of many advanced features not available by using other file systems. As such, using NTFS wherever possible is recommended to gain the maximum benefits from Windows XP. The following are some file system size limitations that should also be considered:
FAT volumes smaller than 16 megabytes (MB) are formatted as FAT12. FAT16 volumes larger than 2 gigabytes (GB) are not accessible from computers running MS-DOS, Windows 95, Windows 98, and many other operating systems.
While FAT32 volumes can theoretically be as large as 2 terabytes, Windows XP limits the maximum size FAT32 volume that it can format to 32 GB. However, Windows XP can read and write to larger FAT32 volumes formatted by other operating systems.
The implementation of FAT32 in Windows XP limits the maximum number of clusters on a FAT32 volume that can be mounted by Windows XP to 4,177,918. This is the maximum number of clusters on a FAT32 volume that can be formatted by Windows 98.
NTFS volumes can theoretically be as large as 16 exabytes (EB), but the practical limit is 2 terabytes.
The user can specify the cluster size when an NTFS volume is formatted. However, NTFS compression is not supported for cluster sizes larger than 4 kilobytes (KB).
Windows OS Internal Training
Advantages of NTFS Formatting Windows XP volumes with NTFS instead of FAT allows you to use advanced features that are available only on NTFS, including the following:
NTFS is a recoverable file system. A user seldom needs to run a disk repair program on an NTFS volume. NTFS guarantees the consistency of the volume by using standard transaction logging and recovery techniques. In the event of a system failure, NTFS uses its log file and checkpoint information to automatically restore the consistency of the file system. NTFS supports compression on volumes, folders, and files. Files that are compressed on an NTFS volume can be read and written by any Windows-based application without first being decompressed by another program; decompression happens automatically during the file read. The file is compressed again when it is closed or saved. NTFS supports all Windows XP file system features. NTFS does not restrict the number of entries in the root folder. Windows XP can format volumes up to 2 terabytes with NTFS. NTFS manages disk space more efficiently than FAT, using smaller clusters (4 KB for volumes up to 2 terabytes). The boot sector is backed up to a sector at the end of the volume. NTFS minimizes the number of disk accesses required to find a file. On NTFS volumes, you can set permissions on shares, folders, and files that specify which groups and users have access, and what level of access is permitted. NTFS file and folder permissions apply to users working on the local computer and to users accessing the file over the network from a shared folder. You can also set share permissions that operate on network shares in combination with file and folder permissions. NTFS supports a native encryption system, EFS, that uses symmetric key encryption in conjunction with public key technology to prevent unauthorized access to file contents.
Reparse points enable new features such as volume mount points. Disk quotas can be set to limit the amount of space users can consume.
Windows OS Internal Training
NTFS uses a change journal to track changes made to files. NTFS supports distributed link tracking to maintain the integrity of shortcuts and OLE links.
NTFS supports sparse files so that very large files can be written to disk while requiring only a small amount of storage space.
Disadvantages of NTFS While NTFS is recommended for most Windows XP users, it is not appropriate in all circumstances. Disadvantages of NTFS include:
NTFS volumes are not accessible from MS-DOS, Windows 95, or Windows 98. The advanced features of the version of NTFS included with Windows XP are not available in Windows NT. For very small volumes that contain mostly small files, the overhead of managing NTFS can cause a slight performance drop in comparison to FAT.
A former disadvantage of NTFS was accessing the NTFS-formatted system volume when corrupted or deleted system files prevented the computer from starting. In the past, it was a common requirement that Windows NT be installed to a second, separate folder to access the NTFS system volume of the first installation. Windows XP resolves this problem by offering a pair of new troubleshooting tools. The first tool, known as Safe Mode, allows Windows XP to be started with only the basic set of device drivers and system services loaded. Safe Mode allows a system that cannot start, due to system corruption or the installation of incompatible drivers or system services, to bypass those blocking issues, enabling the local administrator to resolve the problem. If the damage to the operating system files is severe enough that the computer cannot start even in Safe Mode, you can start the computer from either the Windows XP operating system CD or Setup floppy disks by using the Recovery Console. The Recovery Console is a special command-line environment that enables the administrator to copy system files from the operating system CD, fix disk errors, and otherwise troubleshoot system problems without installing a second copy of the operating system. What are the advantages of NTFS over FAT32?
Is the native file system for WinNT/2k/XP
Windows OS Internal Training
Allows indexing which improves file searching (mostly, faster); causes slight performance hit (can turn off). Has better security -- such as file-wise encryption (not supported by WinXP home) and per-user access rules (you can stop your wife from seeing the porn folder!) Supports user quotas (prevent the tykes from downloading too many mp3s) Has file-wise compression. Is journaled, decreasing data loss (ScanDisk at start up unnecessary). Uses Unicode (allows foreign and extended character) file names and natively supports long file names. Supports larger files than FAT (greater than 4GB). Allows larger volume sizes (greater than 1TB) There is talk about a theoretical limit of 16 Exabytes, and up to 2 Terabytes. Supported format on dynamic disks (no dynamic disks on WinXP Home). Works well with large cache (greater than 96MB systems). Performs better on volumes ~20GB and more. Is more space-efficient on large volumes (greater than 8GB). Resistant to fragmentation.
Sharing and Security How to Share and Set Permissions for Folders and Files Using Windows XP File and Printer Sharing for Microsoft Networks The File and Printer Sharing for Microsoft Networks component allows computers on a network to access resources on other computers using a Microsoft network. This component is installed and enabled by default. It is enabled per connection using TCP/IP and is necessary to share local folders. The File and Printer Sharing for Microsoft Networks component is the equivalent of the Server service in Windows NT 4.0. To share folders with other users on your network 1. Open My Documents in Windows Explorer. Click Start, point to All Programs, point to Accessories, and then click Windows Explorer. 2. Click the folder you want to share. 3. Click Share this folder in File and Folder Tasks.
Windows OS Internal Training
4. In the Properties dialog box select the radio button Share this folder to share the folder with other users on your network, as shown in Figure 1 below.
Figure 1. Sharing a folder on a network
5. To change the name of the folder on the network, type a new name for the folder in the Share name text box. This will not change the name of the folder on your computer. Note The Sharing option is not available for the Documents and Settings, Program Files, and Windows system folders. In addition, you cannot share folders in other users profiles. To set, view, change, or remove file and folder permissions 1. Open Windows Explorer, and then locate the file or folder for which you want to set permissions. To open Windows Explore click Start, point to All Programs, point to Accessories, and then click Windows Explorer. 2. Right-click the file or folder, click Properties, and then click the Security tab as shown in Figure 2 below.
Windows OS Internal Training
Figure 2. Setting file and folder permissions
3. To set permissions for a group or user that does not appear in the Group or user names box, click Add. Type the name of the group or user you want to set permissions for and then click OK, as shown in Figure 3 below.
Windows OS Internal Training
Figure 3. Adding new group or user permissions 4. To change or remove permissions from an existing group or user, click the name of the group or user and do one of the following, as shown in Figure 2 above:
To allow or deny a permission, in the Permissions for...box, select the Allow or Deny check box. To remove the group or user from the Group or user names box, click Remove.
Notes
In Windows XP Professional, the Everyone group no longer includes Anonymous Logon. You can set file and folder permissions only on drives formatted to use NTFS. To change permissions you must be the owner, or have been granted permission to do so by the owner. Groups or users granted Full Control for a folder can delete files and subfolders within that folder regardless of the permissions protecting the files and subfolders. If the check boxes under Permissions for user or group are shaded or if the Remove button is unavailable, then the file or folder has inherited permissions from the parent folder. When adding a new user or group, by default, this user or group will have Read & Execute, List Folder Contents, and Read permissions.
Windows OS Internal Training
User profiles overview A user profile defines customized desktop environments, such as individual display, and network and printer connections settings. You or your system administrator can define your desktop environment. Types of user profiles include: A local user profile, which is created the first time you log on to a computer and is stored on the computer's local hard disk Any changes made to your local user profile are specific to the computer on which the changes are made. A roaming user profile, which is created by your system administrator and is stored on a server This profile is available every time you log on to any computer on the network. Any changes made to your roaming user profile will be updated on the server. A mandatory user profile, which is a roaming profile that can be used to specify particular settings for individuals or an entire group of users. Only system administrators can make changes to mandatory user profiles. Local Users and Groups overview Local Users and Groups is a tool you can use to manage local users and groups. It is available on the following operating systems: Windows 2000 Professional Windows XP Professional Member servers running Windows 2000 Server A local user or group is an account that can be granted permissions and rights from your computer. Domain or global users and groups are managed by your network administrator. You can add local users, global users, and global groups to local groups. However, you cannot add local users and groups to global groups Local Users and Groups is an important security feature because you can limit the ability of users and groups to perform certain actions by assigning them rights and permissions. A right authorizes a user to perform certain actions on a computer, such as backing up files and folders or shutting down a computer. A permission is a rule associated with an object (usually a file,
Windows OS Internal Training
folder, or printer) and it regulates which users can have access to the object and in what manner. Local Users and Groups is not available on domain controllers. Use Active Directory Users and Computers to manage global users and groups. Groups overview Groups displays all built-in groups as well as groups you create. The built-in groups are created automatically when you install Windows 2000 or Windows XP. Belonging to a group gives a user rights and abilities to perform various tasks on the computer. Administrators Members of the Administrators group have the largest amount of default permissions and the ability to change their own permissions. Backup Operators Members of the Backup Operators group can back up and restore files on the computer, regardless of any permissions that protect those files. They can also log on to and shut down the computer, but they cannot change security settings. Power Users Members of the Power Users group can create user accounts, but can modify and delete only those accounts they create. They can create local groups and remove users from local groups they have created. They can also remove users from the Power Users, Users, and Guests groups. They cannot modify the Administrators or Backup Operators groups, nor can they take ownership of files, back up or restore directories, load or unload device drivers, or manage the security and auditing logs. Users Members of the Users group can perform most common tasks, such as running applications, using local and network printers, and shutting down and locking the workstation. Users can create local groups, but can modify only the local groups that they created. Users cannot share directories or create local printers. Guests The Guests group allows occasional or one-time users to log on to a workstation's built-in Guest account and be granted limited abilities.
Windows OS Internal Training
Members of the Guests group can also shut down the system on a workstation. Replicator The Replicator group supports directory replication functions. The only member of the Replicator group should be a domain user account used to log on the Replicator services of the domain controller. Do not add the user accounts of actual users to this group. Users overview Users displays the two built-in user accounts, Administrator and Guest, as well as any user accounts you create. The built-in user accounts are created automatically when you install Windows 2000 or Windows XP. Administrator account The Administrator account is the one you use when you first set up a workstation or member server. You use this account before you create an account for yourself. The Administrator account is a member of the Administrators group on the workstation or member server. The Administrator account can never be deleted, disabled, or removed from the Administrators local group, ensuring that you never lock yourself out of the computer by deleting or disabling all the administrative accounts. This feature sets the Administrator account apart from other members of the Administrators local group. Guest account The Guest account is used by people who do not have an actual account on the computer. A user whose account is disabled (but not deleted) can also use the Guest account. The Guest account does not require a password. The Guest account is disabled by default, but you can enable it. You can set rights and permissions for the Guest account just like any user account. By default, the Guest account is a member of the built-in Guests group, which allows a user to log on to a workstation or member server. Additional rights, as well as any permissions, must be granted to the Guests group by a member of the Administrators group.
System Tools Disk Cleanup
Windows OS Internal Training
The Disk Cleanup tool helps you free up space on your hard disk by searching your disk for files that you can safely delete. You can choose to delete some or all of the files. Use Disk Cleanup to perform any of the following tasks to free up space on your hard disk:
Remove temporary Internet files. Remove downloaded program files. For example, ActiveX controls and Java applets that are downloaded from the Internet. Empty the Recycle Bin. Remove Windows temporary files. Remove optional Windows components that you are not using. Remove installed programs that you no longer use.
You can start Disk Cleanup, by doing any of the following:
Click Start, and then click Run. In the Open box, type cleanmgr, and then click OK. -orClick Start, point to All Programs, point to Accessories, point to System Tools, and then click Disk Cleanup. -orIn Windows Explorer or My Computer, right-click the disk in which you want to free up space, click Properties, click the General tab, and then click Disk Cleanup.
Remove Files Stored on Your Hard Disk To remove files stored on your hard disk that you no longer use, follow these steps:
1. Click Start, and then click My Computer. 2. Right-click the disk in which you want to free up space, and then click
Properties. 3. Click the General tab, and then click Disk Cleanup. 4. Click the Disk Cleanup tab (if it is not already selected), click to select the check boxes next to the files that you want to remove, and then click OK. 5. Click Yes to the proceed with this action, and then click OK. Remove Windows Components To remove Windows components that you are not using, follow these steps:
1. Click Start, and then click My Computer. 2. Right-click the disk in which you want to free up space, and then click
Properties.
Windows OS Internal Training
3. Click the General tab, and then click Disk Cleanup. 4. Click the More Options tab, and then under Windows components,
click Clean up. The Windows Components Wizard starts. 5. In the Components list, click to clear the check box next to the component(s) that you want to remove. o A shaded check box next to a component indicates that only some of its subcomponents are installed. If you want to remove a subcomponent, click Details, click to clear the check box next to the subcomponent(s) that you want to remove, and then click OK. 6. Click Next. 7. In the Completing the Windows Components Wizard page, click Finish. 8. Click OK, click Yes to proceed with this action, and then click OK. Remove Installed Programs To remove programs that you no longer use, follow these steps:
1. Click Start, and then click My Computer. 2. Right-click the disk in which you want to free up space, and then click
Properties. 3. Click the General tab, and then click Disk Cleanup. 4. Click the More Options tab, and then under Installed programs, click Clean up. The Add or Remove Programs dialog box is displayed.
5. In the Currently installed programs list, click the program that you
want to remove, and then click Remove (or Change/Remove).
6. If you receive a prompt to confirm the removal of the program, click
Yes.
7. Repeat step 5 and 6 to remove other programs that you no longer use,
and then click Close.
8. Click OK, click Yes to proceed with this action, and then click OK.
Remove Restore Points To remove all restore points except the most recent restore point, follow these steps:
1. Click Start, and then click My Computer. 2. Right-click the disk in which you want to free up space, and then click
Properties. 3. Click the General tab, and then click Disk Cleanup.
Windows OS Internal Training
4. Click the More Options tab, and then under System Restore, click
Clean up.
5. Click Yes to remove all but the most recent restore point. 6. Click OK, click Yes to proceed with this action, and then click OK.
Administrative tools Component Services Used by system administrators to deploy and administer COM+ programs from a graphical user interface, or to automate administrative tasks using a scripting or programming language. Software developers can use Component Services to visually configure routine component and program behavior, such as security and participation in transactions, and to integrate components into COM+ programs. For more information, see Using Component Services Computer Management Used to manage local or remote computers from a single, consolidated desktop utility. Computer Management combines several Windows XP administrative tools into a single console tree, providing easy access to a specific computer's administrative properties. For more information, see Using Computer Management Data Sources (ODBC) Open Database Connectivity (ODBC) is a programming interface that enables programs to access data in database management systems that use Structured Query Language (SQL) as a data access standard. For more information, see Using Data Sources (ODBC) Event Viewer Used to view and manage logs of system, program, and security events on your computer. Event Viewer gathers information about hardware and software problems, and monitors security events. For more information, see Using Event Viewer Local Security policy Used to configure security settings for the local computer. These settings include the Password policy, Account Lockout policy, Audit policy, IP Security policy, user rights assignments, recovery agents for encrypted data, and other security options. Local Security Policy is only available on computers
Windows OS Internal Training
that are not domain controllers. If the computer is a member of a domain, these settings may be overridden by policies received from the domain. Performance Used to collect and view real-time data about memory, disk, processor, network, and other activity in a graph, histogram, or report form. For more information, see Using Performance Services Used to manage the services on your computer, set recovery actions to take place if a service fails, and create custom names and descriptions for services so that you can easily identify them. For more information, see Using Services Note Administrative Tools can also be opened from Microsoft Management Console, or by clicking Start, clicking Control Panel, clicking Performance and Maintenance, and then clicking Administrative Tools. Task Scheduler overview Applies To: Windows Server 2003, Windows Server 2003 R2, Windows Server 2003 with SP1, Windows Server 2003 with SP2 Task Scheduler overview Using Task Scheduler, you can schedule any script, program, or document to run at a time that is most convenient for you. When you first install your Windows Server 2003 family operating system, the Task Scheduler service is enabled. By default, you must be a member of the Administrators, Backup Operators, or Server Operators group on the local computer, to view, add, edit, or delete scheduled tasks, or to disable, pause, or restart the Task Scheduler service. For more information, see Task Scheduler and Security. With Task Scheduler, you can:
Schedule a task to run daily, weekly, monthly, or at certain times (such as system startup). Change the schedule for a task. Stop a scheduled task.
Windows OS Internal Training
Customize how a task runs at a scheduled time.
Each scheduled task you create is stored as a .job file in the \Windows\Tasks folder. The .job file contains the properties and configuration information for the task. You can create a scheduled task on your computer and then drag the .job object over to a remote computer. After you drag a task from one computer to another, you must update the account information for the task before it will run. Removing a scheduled task removes only the .job file from the schedule. The program file the task runs is not removed from the hard disk.
Windows XP System Restore Microsoft OSs have typically included utilities that help you recover systems that become unstable or crash, but Windows XP's System Restore goes much further. System Restore reinstates the registry, local profiles, the COM+ database, the Windows File Protection (WFP) cache (wfp.dll), the Windows Management Instrumentation (WMI) database, the Microsoft IIS metabase, and files that the utility copies by default into a Restore archive. You can't specify what to restore: it's all or nothing. Understanding System Restore Creating a Restore Point Restoring a System Troubleshooting
Understanding System Restore System Restore's purpose is to return your system to a workable state without requiring a complete reinstallation and without compromising your data files. The utility runs in the background and automatically creates a restore point when a trigger event occurs. Trigger events include application installations, AutoUpdate installations, Microsoft Backup Utility recoveries, unsigned- driver installations, and manual creations of restore points. The utility also creates restore points once a day by default. System Restore requires 200MB of free hard disk space, which the utility uses to create a data store. If you don't have 200MB of free space, System Restore remains disabled until the space becomes available, at which point the utility enables itself. System Restore uses a first in/first out (FIFO) storage scheme: The utility purges old archives to make room for new ones when the data store reaches a set limit.
Windows OS Internal Training
The file types that System Restore monitors are many but include most of the extensions that you typically see when you install new software (e.g., .cat, .com, .dll, .exe, .inf, .ini, .msi, .ole, .sys). Note that only application installations that use a System Restore restorept.api-compliant installer will trigger the creation of a restore point. Typically, system recoveries are easiest when you know *or think you know* what caused the problem (e.g., a recently installed device driver). In some cases, System Restore might not be the best choice for correcting a problem you're experiencing. System Restore changes many different files and registry entries, and in some cases might replace too much and actually cause more problems than it solves. For example, say you install Office XP, which triggers System Restore to create a restore point, and the software suite works great. Later in the day, you download and install an updated video driver, and because the driver is signed, the installation doesn't trigger System Restore to create a restore point. Now your system hangs on occasion, and you believe that the video driver is the culprit. In this case, you should use the Device Driver Rollback utility because it will address the device-driver problem only and not change anything else on your system. System Restore would roll your computer back to a preOffice XP state, and you would have to reinstall the entire software suite after you resolved the driver problem. Creating a Restore Point Windows XP automatically creates restore points when you would typically need them most. However, occasions arise when you might want to create restore points manually*for example, if you're installing an application that you're not sure will be stable on Windows XP, if you're unsure whether an application is System Restore restorept.api-compliant, or if you're making system changes that could affect the system's stability. For example, I wanted to install Crystal Decisions' Crystal Reports Professional 7, but because that version is several years old, I wasn't sure how well it would run on Windows XP. I decided to create a restore point before installing the software. I clicked Start, All Programs, Accessories, System Tools, System Restore. A Welcome screen appeared, and System Restore asked whether I wanted to restore or create a restore point. I chose Create a restore point and clicked Next. I named my restore point Before Crystal Reports, as Figure 1 shows, and clicked Create.
Windows OS Internal Training
Figure 1: Name restore points so that you can easily identify them later. After the utility collected all the information it needed, it displayed the Restore Point Created screen, which Figure 2 shows. I closed the utility to end the process.
Figure 2: Restoring a System Having created a restore point, I could install Crystal Reports on my Windows XP machine with the confidence of knowing that I could restore my system if
Windows OS Internal Training
anything went wrong. During the installation, several error messages reported that the system couldn't find a particular DLL. The installation finished, and Crystal Reports didn't start. I was immediately glad that I'd created the restore point. Before performing a restore, I used the Crystal Reports uninstallation program to try to delete the application's program files and registry entries, but the procedure overlooked one registry entry. Instead of deleting the registry entry manually, which could destabilize the system, I decided to use System Restore to restore the registry safely. I started the System Restore utility. At the Welcome screen, I chose Restore my computer to an earlier time, then clicked Next. To prompt me to select a restore point, the utility presented the various options in a calendar format, which Figure 3 shows. The calendar format lets you click through dates and see the existing restore points. Restore points that System Restore creates appear as System Checkpoint.
Figure 3: I clicked July 23 and saw the Before Crystal Reports restore point that I had created earlier. I selected that restore point and clicked Next, then confirmed the restore point selection and clicked Next again. System Restore closed all programs and proceeded with the restoration. The computer then rebooted. I logged back on, and the Restoration Complete screen appeared to let me know the restore was finished and had succeeded, as Figure 4 shows.
Windows OS Internal Training
Figure 4: I then checked the hard disk and the registry and found no sign of Crystal Reports. In addition, the files I created between installing and restoring my system remained on my system. My data files were safe, and the system was stable. If your system no longer boots to the OS, start the computer and press the F8 key as Windows begins to run. When the Windows Advanced Options menu appears, choose Last Known Good Configuration and press Enter. If the damage isn't too bad, a boot menu will appear, and you can select Microsoft Windows XP, then press Enter. Windows XP will restore the computer to the most recent restore point. If a restoration fails to resolve a problem, System Restore lets you try to select another restore point or undo the restoration. So, if you chose the wrong restore point earlier, you get a chance to correct your mistake. Remember, performing a restore is one of the events that triggers the system to create a restore point. Now you know why. Troubleshooting I've found System Restore to be stable and reliable. However, as with most programs, you might occasionally experience problems with System Restore. Should you need to disable it, you can do so (for details, see the sidebar "Disabling System Restore"). But first, try troubleshooting:
Read any error messages and address any issues that the messages identify.
Windows OS Internal Training
Check your hard disks for free space. You must have at least 200MB of free space on each disk on which you've enabled System Restore. You can use the Disk Cleanup utility to reclaim space. If necessary, you can also use this utility to delete all but the most recent restore point. Confirm that the System Restore service is running. Try to run the utility in Safe mode. Check the System log for any errors that relate to sr or srservice.
If these steps don't help, run srdiag.exe to troubleshoot further. Srdiag creates a .cab file, which it places in the \%windir%\system32\restore folder by default. You can double-click the file or right-click it and choose Extract. You can then examine the 14 extracted files to troubleshoot your problem. System Restore's scope, ease of use, and reliability are impressive. It's a useful utility that power users, technical support staff, and administrators should familiarize themselves with. System Restore has the potential to significantly reduce administrator work and user downtime.
Event Viewer With Event Viewer, users can monitor events recorded in the Application, Security, and System logs: Understanding Event Viewer Using the event logs in Event Viewer, you can gather information about hardware, software, and system problems. You can also monitor Windows XP security events. A computer running any version of Windows XP records events in three kinds of logs:
Windows OS Internal Training
Application log The application log contains events logged by applications or programs. For example, a database program might record a file error in the application log. Program developers decide which events to monitor. Security log The security log records events such as valid and invalid logon attempts, as well as events related to resource use such as creating, opening, or deleting files or other objects. An administrator can specify what events are recorded in the security log. For example, if you have enabled logon auditing, attempts to log on to the system are recorded in the security log. System log The system log contains events logged by Windows XP system components. For example, the failure of a driver or other system component to load during startup is recorded in the system log. The event types logged by system components are predetermined by Windows XP. A computer running Windows configured as a domain controller records events in two additional logs: Directory service log The directory service log contains events logged by the Windows directory service. For example, connection problems between the server and the global catalog are recorded in the directory service log. File Replication service log The File Replication service log contains events logged by the Windows File Replication service. For example, file replication failures and events that occur while domain controllers are being updated with information about sysvol changes are recorded in the file replication log. A computer running Windows configured as a Domain Name System (DNS) server records events in an additional log: DNS server log The DNS server log contains events logged by the Windows DNS service. Events associated with resolving DNS names to Internet Protocol (IP) addresses are recorded in this log. Event Viewer displays these types of events:
Windows OS Internal Training
Error A significant problem, such as loss of data or loss of functionality. For example, if a service fails to load during startup, an Error event will be logged. Warning An event that is not necessarily significant, but may indicate a possible future problem. For example, when disk space is low, a Warning event will be logged. Information An event that describes the successful operation of an application, driver, or service. For example, when a network driver loads successfully, an Information event will be logged. Success Audit An audited security access attempt that succeeds. For example, a user's successful attempt to log on to the system will be logged as a Success Audit event. Failure Audit An audited security access attempt that fails. For example, if a user tries to access a network drive and fails, the attempt will be logged as a Failure Audit event. The Event Log service starts automatically when you start Windows. All users can view application and system logs. Only administrators can gain access to security logs. By default, security logging is turned off. You can use Group Policy to enable security logging. The administrator can also set auditing policies in the registry that cause the system to halt when the security log is full.
Windows OS Internal Training
Disk Management You use Disk Management snap-in in Windows XP to perform disk-related tasks, such as creating partitions and volumes, formatting them, and assigning drive letters. On computers running Windows XP or Windows 2003 Server, you can also use Disk Management to perform advanced tasks, such as creating and repairing fault tolerant volumes. Disk Management overview The Disk Management snap-in is a system utility for managing hard disks and the volumes, or partitions, that they contain. With Disk Management, you can initialize disks, create volumes, format volumes with the FAT, FAT32, or NTFS file systems, and create fault-tolerant disk systems. Disk Management enables you to perform most disk-related tasks without shutting down the system or interrupting users; most configuration changes take effect immediately. Disk Management, which replaces the Disk Administrator utility used in Windows NT 4.0, offers many features including:
Simplified tasks and intuitive user interface. Disk Management is easy to use. Menus that are accessible from the right mouse button display the tasks you can perform on the selected object, and wizards guide you through creating partitions or volumes and initializing or converting disks. Basic and dynamic disk storage. Basic disks contain basic volumes, such as primary partitions, extended partitions, and logical drives. Use basic disks on portable computers or when you plan to install multiple operating systems in different partitions on the same disk.
Windows OS Internal Training
Dynamic disks contain dynamic volumes that offer features not available in basic disks, such as the ability to create fault-tolerant volumes. You can extend or mirror dynamic volumes and add new dynamic disks without restarting the computer.
Local and remote disk management. By using Disk Management, you can manage any remote computer running Windows 2000 or Windows XP on which you are a member of the Administrators group. Mounted drives. You can use Disk Management to connect, or mount, a local drive at any empty folder on a local NTFS-formatted volume. Mounted drives make data more accessible and give you the flexibility to manage data storage based on your work environment and system usage. Mounted drives are not subject to the 26-drive limit imposed by drive letters, so you can use mounted drives to access more than 26 drives on your computer. Logical Disk Manager Service. The Logical Disk Manager Service uses disk groups to maintain information about the current state of disks in your computer. Support for MBR and GPT disks. Disk Management offers support for master boot record (MBR) disks in x86-based computers and support for MBR and GUID partition table (GPT) disks in Itanium-based computers. Manage disks at the command line. Use the command-line tool DiskPart to perform disk-related tasks at the command line as an alternative to using Disk Management. With DiskPart, you can create scripts to automate tasks, such as creating volumes or converting disks to dynamic.
Best practices
Back up data Deleting or creating partitions or volumes destroys any existing data. Be sure to back up the disk contents beforehand. As with any major change to disk contents, you should back up the entire contents of the hard disk before working with partitions or volumes, even if you do not plan to make any changes to one or more of your partitions or volumes. Format volumes using the NTFS file system Many features, such as file and folder permissions, encryption, large volume support, and sparse file management, all found in Windows 2000 and Windows XP, require this file format. Use dynamic disks Several Disk Management tasks can be performed only with dynamic disks, including the ability to create fault-tolerant disks. Using dynamic disks, you can create and delete simple, spanned, striped, mirrored, and RAID-5 volumes. Dynamic disks do not contain partitions or logical
Windows OS Internal Training
drives, nor can they be directly accessed by computers running MSDOS, Windows 95, Windows 98, Windows Millennium Edition, Windows NT, or Windows XP Home Edition, so you cannot start these operating systems on dynamic disks. However, shared folders on dynamic disks are available across a network to computers running all of these operating systems.
Registry Overview Registry Editor is an advanced tool for viewing and changing settings in your system registry, which contains information about how your computer runs. Windows stores its configuration information in a database (the registry) that is organized in a tree format. Although Registry Editor enables you to inspect and modify the registry, normally you do not need to do so, and making incorrect changes can break your system. An advanced user who is prepared to both edit and restore the registry can safely use Registry Editor for such tasks as eliminating duplicate entries or deleting entries for programs that have been uninstalled or deleted.
Windows OS Internal Training
Registry Editor overview Registry Editor is an advanced tool for viewing and changing settings in your system registry, which contains information about how your computer runs. Windows stores its configuration information in a database (the registry) that is organized in a tree format. Although Registry Editor enables you to inspect and modify the registry, normally you do not need to do so, and making incorrect changes can break your system. An advanced user who is prepared to both edit and restore the registry can safely use Registry Editor for such tasks as eliminating duplicate entries or deleting entries for programs that have been uninstalled or deleted. Folders represent keys in the registry and are shown in the navigation area on the left side of the Registry Editor window. In the topic area on the right, the entries in a key are displayed. When you double-click a entry, it opens an editing dialog box. You should not edit your registry unless it is absolutely necessary. If there is an error in your registry, your computer may not function properly. If this happens, you can restore the registry to the same version you were using when you last successfully started your computer. For instructions, see Related Topics. Registry Editor Keys The navigation area of the Registry Editor displays folders, each of which represents a predefined key on the local computer. When accessing the registry of a remote computer, only two predefined keys, HKEY_USERS and HKEY_LOCAL_MACHINE, appear. Folder/predefined key Description Contains the root of the configuration information for the user who is currently logged on. The user's folders, screen colors, and Control Panel settings are stored here. This information is referred to as a user's profile. Contains the root of all user profiles on the computer. HKEY_CURRENT_USER is a sub key of HKEY_USERS. Contains configuration information particular to the computer (for any user). Is a sub key of HKEY_LOCAL_MACHINE\Software. The information stored here ensures that the correct program opens when you open a file by
HKEY_CURRENT_USER
HKEY_USERS
HKEY_LOCAL_MACHINE HKEY_CLASSES_ROOT
Windows OS Internal Training
using Windows Explorer. HKEY_CURRENT_CONFIG Contains information about the hardware profile used by the local computer at system startup.
The following table lists the data types currently defined and used by the system. Data type Description Raw binary data. Most hardware component information is stored as binary data and is displayed in Registry Editor in hexadecimal format. Data represented by a number that is 4 bytes long. Many parameters for device drivers and services are this type and are displayed in Registry Editor in binary, hexadecimal, or decimal format. A variable-length data string. This data type includes variables that are resolved when a program or service uses the data. A multiple string. Values that contain lists or multiple values in a form that people can read are usually this type. Entries are separated by spaces, commas, or other marks. A fixed-length text string.
REG_BINARY
REG_DWORD
REG_EXPAND_SZ
REG_MULTI_SZ
REG_SZ
A series of nested arrays designed to REG_FULL_RESOURCE_DESCRIPTOR store a resource list for a hardware component or driver.
Caution
Windows OS Internal Training
Incorrectly editing the registry may severely damage your system. Before making changes to the registry, you should back up any valued data on your computer.
Notes
To open Registry Editor, click Start, click Run, type regedit, and then click OK. To safely use Registry Editor for such tasks as eliminating duplicate entries or deleting entries for programs that have been uninstalled or deleted, you should be prepared to both edit and restore the registry.
Best practices In Windows, system configuration information is centrally located in the registry. While this simplifies the administration of a computer or network, one incorrect edit to the registry can disable the operating system. The following list provides some best practices for using the registry and Registry Editor safely:
Before making changes to the registry, make a backup copy.
You can back up the registry by using a program such as Backup. After you make changes to the registry, create an Automated System Recovery (ASR) disk. For troubleshooting purposes, keep a list of the changes you make to the registry. For more information, see System State data. Do not replace the Windows registry with the registry of another version of the Windows or Windows NT operating systems. Use tools and programs other than Registry Editor to edit the registry.
Incorrectly editing the registry may severely damage your system. You should use tools and programs that provide safer methods for editing the registry.
Never leave Registry Editor running unattended.
Control Panel overview Control Panel is full of specialized tools that are used to change the way Windows looks and behaves.
Windows OS Internal Training
Some of these tools help you adjust settings that make your computer more fun to use. For example, use Mouse to replace standard mouse pointers with animated icons that move on your screen, or use Sounds and Audio Devices to replace standard system sounds with sounds you choose. Other tools help you set up Windows so that your computer is easier to use. For example, if you are left-handed, you can use Mouse to switch the mouse buttons so that the button on the right performs the primary functions of selecting and dragging. To open Control Panel, click Start and then click Control Panel. If your computer is set up in Classic view using the more familiar Start menu, click Start, point to Settings, and then click Control Panel. When you first open Control Panel, you will see some of the most commonly used Control Panel items organized by category. To find out more information about an item in Control Panel while in Category view, hold your mouse pointer over the icon or category name and read the text that appears. To open one of these items, click its icon or category name. Some of these items will open to a list of tasks you can perform, as well as a selection of individual Control Panel items. For example, when you click Appearance and Themes, you will see a list of tasks such as Choose a screen saver along with individual Control Panel items. If you open Control Panel and do not see the item you want, click Switch to Classic View. To open an item, double-click its icon. To find out more about an item in Control Panel while in Classic Control Panel view, hold your mouse pointer over the icon and read the text that appears. Each tool in Control Panel is represented by a .cpl file in the Windows\System32 folder. The .cpl files in the Windows\System32 folder are loaded automatically when you start Control Panel. NOTE: Occasionally, Windows uses entries in the [MMCPL] section of the Control.ini file to load Control Panel files. The following table lists the most common .cpl files, including all the .cpl files that are included with Windows: File name Purpose Access.cpl Appwiz.cpl Desk.cpl Hdwwiz.cpl Inetcpl.cpl Accessibility properties Add/Remove Programs properties Display properties Add Hardware properties Internet properties
Windows OS Internal Training
Intl.cpl Irprops.cpl Regional Settings properties Infrared Port properties (located in C:\Windows\Driver cache\I386\Driver.cab until you install an infrared device) Joystick properties Mouse properties Multimedia properties Network Connections properties User Accounts properties Gateway Services for NetWare properties
Joy.cpl Main.cpl Mmsys.cpl Ncpa.cpl Nusrmgr.cpl Nwc.cpl
Odbccp32.cp Open Database Connectivity (ODBC) Data Source Administrator l properties Powercfg.cpl Power Options properties Sapi.cpl Speech Properties (located in C:\Program files\Common files\Microsoft Shared\Speech) System properties
Sysdm.cpl
Telephon.cpl Phone and Modem Options properties Timedate.cpl Time and Date properties Third-party software and hardware manufacturers add Control Panel icons to provide an interface for you to use when you configure settings for their products. An icon is displayed in Control Panel after the program's Setup tool places the .cpl file in the Windows\System32. To create a shortcut to a Control Panel tool, either drag an icon from Control Panel to the desktop or another location or manually create a shortcut, and then specify the path to the .cpl file.
Internal / External commands To find information about a command, on the A-Z button menu at the top of this page, click the letter that the command starts with, and then click the command name.
Windows OS Internal Training
In addition to the tools installed with Windows XP, there are over 40 support tools included on the Windows XP CD. You can use these tools to diagnose and resolve computer problems. For more information about these support tools, see Windows Support Tools For information about installing support tools, see Install Windows Support Tools For more information about changes to the functionality of MS-DOS commands, new command-line tools, command shell functionality, configuring the command prompt, and automating commmand-line tasks, see Command-line reference Some command-line tools require the user to have administrator-level privileges on source and/or target computers. Command-line tools must be run at the prompt of the Cmd.exe command interpreter. To open Command Prompt, click Start, click Run, type cmd, and then click OK. To view help at the command-line, at the command prompt, type the following: Example : CommandName /? Arp, Assoc, At, Atmadm, Attrib Bootcfg, Break Cacls, Call, Change, Chcp, Chdir, Chkdsk, Chkntfs, Cipher, Cls, Cmd, Cmstp, Color, Comp, Compact, Convert, Copy, Cprofile, CScript Date,Defrag,Del,Dir,Diskcomp,Diskcopy,DiskPart,Doskey,Driverquery Echo,Endlocal,Eventcreate,Eventquery,Eventtriggers,Evntcmd,Exit,Expand Fc,Filter,Find,Findstr,Finger,Flattemp,Format,Fsutil,Ftp,Ftype Getmac,Goto,Gpresult,Gpupdate,Graftabl Help,Helpctr,Hostname If,Ipconfig,Ipseccmd,Ipxroute,Irftp Label,Lodctr,Logman,Lpq,Lpr Macfile,Mkdir(md),Mmc,Mode,More,Mountvol,Move,Msiexec,Msinfo32 Nbtstat,Netsh,Netstat,Nslookup,Ntbackup,Ntcmdprompt,Ntsd Openfiles
Windows OS Internal Training
Pagefileconfig,Path,Pathping,Pause,Pbadmin,Pentnt,Perfmon,Ping,Popd,Pri nt,Prncnfg, Prndrvr, Prnjobs,Prnmngr,Prnport,Prnqctl,Prompt,Pushd, Query Rasdial,Rcp,Recover,Reg,Regsvr32,Relog,Rem,Rename,Replace,Rexec,Rm dir,Route, Rsh,Rsm,Runas Sc,Schtasks,Secedit,Set,Setlocal,Shift,Shutdown,Sort,Start,Subst,System info,sfc Taskkill,Tasklist,Tcmsetup,Telnet,Tftp,Time,Title,Tracerpt,Tracert,Tree,Typ e, Typeperf Unlodctr Ver,Verify,Vol,Vssadmin W32tm,Winnt,Winnt32,WMIC Xcopy In detail:
o o
o o
at (windows XP/2000) Scheduling utility. bootcfg (XP only) This utility allows you to set up your boot options, such as your default OS and other loading options. cacls (XP, 2000, & NT4.0) Changes the ACLs (security Settings) of files and folders. Very similar to chmod in Linux. comp (XP & 2000) This utility is very similar to diff in Linux. Use the /? switch to get examples of command usage. contig (works with NT4.0 and newer) A great defrag utility for NTFS partitions. control (XP only) - unpublished! Allows you to launch control panel applets from the command line. control userpasswords2, for example will launch a helpful local user admin utility. defrag (XP only - NT4.0 and Win2k use contig) Yes, XP comes with a command line disk defrag utility. If you are running Win2k or NT4.0 there is still hope. Contig is a free defrag program that I describe on the defrag page. diskpart (XP only) Use this command to manage your disk partitions. This is the text version for the GUI Disk Manager.
Windows OS Internal Training
o
o o o
o o
o o
driverquery (XP only) Produces a list of drivers, their properties, and their versions. Great for computer documentation. eudcedit (XP only) - unpublished! Private Character editor. Yes with this program built into Windows XP you can create your own font! findstr Find String - similar to Linux's Grep. fsutil (XP only) - unpublished! This is a utility with a lot of capability. Come back soon for great examples. getmac (XP & 2000) This command gets the Media Access Control (MAC) address of your network cards. gpresult (XP & 2000) This generates a summary of the user settings and computer group policy settings. gpupdate (XP only) Use this utility to manually apply computer and user policy from your windows 2000 (or newer) domain. ipconfig (XP, 2000 & NT4.0) This handy tool displays IP settings of the current computer and much more. MMC (XP, 2000 & NT4.0) - Microsoft Management Console This is the master tool for Windows, it is the main interface in which all other tools use starting primarily in Windows 2000 and newer systems. more Utility used to display text output one screen at a time. Ex. more c:\windows\win.ini msconfig (XP only) The ultimate tool to change the services and utilities that start when your Windows machine boots up. You can also copy the executable from XP and use it in Win2k. msinfo32 (XP &smp; 2000) An awesome diagnostic tool. With it you can get a list of running processes, including the residing path of the executable (great for manually removing malware) and get detailed information about hardware and system diagnostics. narrator (XP only) Turns on the system narrator (can also be found in accessibility options in control panel). Will will allow your computer to dictate text to you. netsh (XP & 2000) A network configuration tool console. At the 'netsh>' prompt, use the '?' to list the available commands and type "exit" to get back to a command prompt. netstat (XP) A local network port tool - try netstat -ano. nslookup (all) A DNS name resolution tool.
Windows OS Internal Training
o
o o
openfiles (XP Only) Allows an administrator to display or disconnect open files in XP professional. Type "openfiles /?" for a list of possible parameters. Pathping (XP & 2000) A cross between the ping and traceroute utilities. Who needs Neotrace when you can use this? Type "pathping <ip address>" and watch it go. recover (XP & 2000) This command can recover readable information from a damaged disk and is very easy to use. reg (XP & 2000) A console registry tool, great for scripting Registry edits. sc (XP & 2000) A command line utility called the Service Controller. A power tool to make service changes via a logon/logoff or startup/shutdown script. schtasks (XP only) A newer version of the AT command. This allows an administrator to schedule and manage scheduled tasks on a local and remote machines. secedit (XP & 2000) Use this utility to manually apply computer and user policy from your windows 2000 (or newer) domain. Example to update the machine policy: secedit /refreshpolicy machine_policy /enforce To view help on this, just type secedit. NOTE: In Windows XP SP1 and news, this command is superceded by: gpupdate /force sfc (XP & 2000) The system file checker scans important system files and replaces the ones you (or your applications) hacked beyond repair with the real, official Microsoft versions. shutdown (XP & 2000) With this tool, You can shut down or restart your own computer, or an administrator can shut down or restart a remote computer. sigverif (XP only) Microsoft has created driver signatures. A signed driver is Microsoft tested and approved. With the sigverif tool you can have all driver files analyzed to verify that they are digitally signed. Just type 'sigverif' at the command prompt. systeminfo (XP only) Basic system configuration information, such as the system type, the processor type, time zone, virtual memory settings, system uptime, and much more. This program is great for creating an inventory of computers on your network. sysedit (XP/2000) System Configuration File Editor. An old tool that was very handy for the Windows 9X days. msconfig is what you want to use now. tasklist (XP pro only) Tasklist is the command console equivalent to the task manager in windows. It is a must have when fighting scumware and viruses. Try the command:
Windows OS Internal Training
o
tasklist /svc to view the memory resources your services take up. taskkill (XP only) Taskkill contains the rest of the task manager functionality. It allows you to kill those unneeded or locked up applications. tree (XP & 2000) An amazing experience everyone should try! This command will provide a 'family tree' style display of the drive/folder you specify. WMIC (XP & 2000) Windows Management Instrumentation Command tool. This allows you to pull an amazing amount of low-level system information from a command line scripting interface.
Run Commands Program Accessibility Controls Accessibility Wizard Add Hardware Wizard Add/Remove Programs Administrative Tools Adobe Acrobat ( if installed ) Adobe Distiller ( if installed ) Adobe ImageReady ( if installed ) Adobe Photoshop ( if installed ) Automatic Updates Basic Media Player Bluetooth Transfer Wizard Calculator Ccleaner ( if installed ) C: Drive Certificate Manager Character Map Check Disk Utility Clipboard Viewer Command Prompt Command Prompt Component Services Computer Management Compare Files Run Command access.cpl accwiz hdwwiz.cpl appwiz.cpl control admintools acrobat acrodist imageready photoshop wuaucpl.cpl mplay32 fsquirt calc ccleaner c: cdrtmgr.msc charmap chkdsk clipbrd cmd command dcomcnfg compmgmt.msc comp
Windows OS Internal Training
Control Panel Create a shared folder Wizard Date and Time Properties DDE Shares Device Manager Direct X Control Panel ( if installed ) Direct X Troubleshooter Disk Cleanup Utility Disk Defragment Disk Partition Manager Display Properties Display Properties Display Properties (w/Appearance Tab Preselected ) Dr. Watson System Troubleshooting Utility Driver Verifier Utility Ethereal ( if installed ) Event Viewer Files and Settings Transfer Tool File Signature Verification Tool Findfast Firefox Folders Properties Fonts Fonts Folder Free Cell Card Game Game Controllers Group Policy Editor ( xp pro ) Hearts Card Game Help and Support Hyperterminal Hotline Client Iexpress Wizard Indexing Service Internet Connection Wizard Internet Properties Internet Setup Wizard IP Configuration (Display Connection Configuration) IP Configuration (Display DNS Cache Contents) IP Configuration (Delete DNS Cache Contents) control shrpubw timedate.cpl ddeshare devmgmt.msc directx.cpl dxdiag cleanmgr dfrg.msc diskmgmt.msc control desktop desk.cpl control color drwtsn32 verifier ethereal eventvwr.msc migwiz sigverif findfast.cpl firefox control folders fonts fonts freecell joy.cpl gpedit.msc mshearts helpctr hypertrm hotlineclient iexpress ciadv.msc icwonn1 inetcpl.cpl inetwiz ipconfig /all ipconfig /displaydns ipconfig /flushdns
Windows OS Internal Training
IP Configuration (Release All Connections) IP Configuration (Renew All Connections) IP Configuration (Refreshes DHCP & ReRegisters DNS) IP Configuration (Display DHCP Class ID) IP Configuration (Modifies DHCP Class ID) Java Control Panel ( if installed ) Java Control Panel ( if installed ) Keyboard Properties Local Security Settings Local Users and Groups Logs You Out of Windows Malicious Software Removal Tool Microsoft Access ( if installed ) Microsoft Chat Microsoft Excel ( if installed ) Microsoft Diskpart Microsoft Frontpage ( if installed ) Microsoft Movie Maker Microsoft Management Console Microsoft Narrator Microsoft Paint Microsoft Powerpoint Microsoft Word ( if installed ) Microsoft Syncronization Tool Minesweeper Game Mouse Properties Mouse Properties MS-Dos Editor MS-Dos FTP Nero ( if installed ) Netmeeting Network Connections Network Connections Network Setup Wizard Notepad Nview Desktop Manager ( if installed ) Object Packager ODBC Data Source Administrator ODBC Data Source Administrator ipconfig /release ipconfig /renew ipconfig /registerdns ipconfig /showclassid ipconfig /setclassid jpicpl32.cpl javaws control keyboard secpol.msc lusrmgr.msc logoff mrt access.cpl winchat excel diskpart frontpg moviemk mmc narrator mspaint powerpnt winword mobsync winmine control mouse main.cpl edit ftp nero conf control netconnections ncpa.cpl netsetup.cpl notepad nvtuicpl.cpl packager odbccp32 odbccp32.cpl
Windows OS Internal Training
On Screen Keyboard Opens AC3 Filter ( if installed ) Outlook Express Paint Password Properties Performance Monitor Performance Monitor Phone and Modem Options Phone Dialer Pinball Game Power Configuration Printers and Faxes Printers Folder Private Characters Editor Quicktime ( if installed ) Quicktime Player ( if installed ) Real Player ( if installed ) Regional Settings Registry Editor Registry Editor Remote Access Phonebook Remote Desktop Removable Storage Removable Storage Operator Requests Resultant Set of Policy ( xp pro ) Scanners and Cameras Scheduled Tasks Security Center Services Shared Folders Sharing Session Shuts Down Windows Sounds Recorder Sounds and Audio Spider Solitare Card Game SQL Client Configuration System Configuration Editor System Configuration Utility System File Checker Utility ( Scan Immediately ) System File Checker Utility ( Scan Once At Next osk ac3filter.cpl msimn pbrush password.cpl perfmon.msc perfmon telephon.cpl dialer pinball powercfg.cpl control printers printers eudcedit quicktime.cpl quicktimeplayer realplay intl.cpl regedit regedit32 rasphone mstsc ntmsmgr.msc ntmsoprq.msc rsop.msc sticpl.cpl control schedtasks wscui.cpl services.msc fsmgmt.msc rtcshare shutdown sndrec32 mmsys.cpl spider clicongf sysedit msconfig sfc /scannow sfc /scanonce
Windows OS Internal Training
Boot ) System File Checker Utility ( Scan On Every Boot ) System File Checker Utility ( Return to Default Settings) System File Checker Utility ( Purge File Cache ) System File Checker Utility ( Set Cache Size to Size x ) System Information System Properties Task Manager TCP Tester Telnet Client Tweak UI ( if installed ) User Account Management Utility Manager Volume Serial Number for C: Volume Control Windows Address Book Windows Address Book Import Utility Windows Backup Utility ( if installed ) Windows Explorer Windows Firewall Windows Installer Details Windows Magnifier Windows Management Infrastructure Windows Media Player Windows Messenger Windows Picture Import Wizard (Need camera connected) Windows System Security Tool Windows Script host settings Widnows Update Launches Windows Version ( shows your windows version ) Windows XP Tour Wizard Wordpad Zoom Utility sfc /scanboot sfc /revert sfc /purgecache sfc /cachesize=x msinfo32 sysdm.cpl taskmgr tcptest telnet tweakui nusrmgr.cpl utilman label sndvol32 wab wabmig ntbackup explorer firewall.cpl msiexec magnify wmimgmt.msc wmplayer msnsgs wiaacmgr syskey wscript wupdmgr winver tourstart write igfxzoom
Вам также может понравиться
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- Form C LatestДокумент1 страницаForm C LatestChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- KXTDE Programming Manual 100 200 600Документ948 страницKXTDE Programming Manual 100 200 600Markos AguilarОценок пока нет
- KXTDE Programming Manual 100 200 600Документ948 страницKXTDE Programming Manual 100 200 600Markos AguilarОценок пока нет
- General Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesДокумент1 страницаGeneral Election To Vidhan Sabha Trends & Result 2019: Constituencywise-All CandidatesChandraSekharОценок пока нет
- OSPF LSA TypesДокумент8 страницOSPF LSA TypesChandraSekharОценок пока нет
- Windows 2012 DCДокумент14 страницWindows 2012 DCChandraSekharОценок пока нет
- Consumer Mobiles Pub Lenovo Z P Series HMM v1.0Документ121 страницаConsumer Mobiles Pub Lenovo Z P Series HMM v1.0Pradeep Singh Kshatriya0% (1)
- Riddles in HinduismДокумент447 страницRiddles in HinduismProf.M.M.Ninan100% (26)
- Operating System ControlДокумент17 страницOperating System ControlChandraSekharОценок пока нет
- Mcse NotesДокумент90 страницMcse NotesAbhishek kapoor85% (13)
- Excel 2013 Windows QRG8 Keyboard Shortcut KeysДокумент5 страницExcel 2013 Windows QRG8 Keyboard Shortcut KeysMilovanОценок пока нет
- Material For MCSEДокумент117 страницMaterial For MCSEChandraSekharОценок пока нет
- HSRPДокумент18 страницHSRPChandraSekharОценок пока нет
- VPNДокумент36 страницVPNPinal ShahОценок пока нет
- Routing ProtocolsДокумент6 страницRouting ProtocolsChandraSekharОценок пока нет
- CVДокумент12 страницCVvinod000Оценок пока нет
- EIGRPДокумент7 страницEIGRPChandraSekharОценок пока нет
- BGP Confederation Explained: IBGP TutorialДокумент7 страницBGP Confederation Explained: IBGP TutorialChandraSekharОценок пока нет
- Ethical HackingДокумент26 страницEthical HackingChandraSekharОценок пока нет
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5784)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (890)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (399)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (119)
- How To Install Java JDKДокумент5 страницHow To Install Java JDKJimi DbonoОценок пока нет
- Install Kali ARM On A Raspberry PiДокумент3 страницыInstall Kali ARM On A Raspberry PigejibОценок пока нет
- 11.4.1.5 Lab Work in The Windows Command ShellДокумент3 страницы11.4.1.5 Lab Work in The Windows Command ShellLEE JUN WEIОценок пока нет
- MOC Firmware UpdateДокумент2 страницыMOC Firmware UpdateWeihan KhorОценок пока нет
- Jails: Lightweight, Operating-System-level VirtualizationДокумент14 страницJails: Lightweight, Operating-System-level VirtualizationSupriya SharmaОценок пока нет
- Installing TeXLive packages on Magisk-v13.1Документ22 страницыInstalling TeXLive packages on Magisk-v13.1Dustin BogartОценок пока нет
- Operating SystemДокумент2 страницыOperating SystemShabdik ChakrabortyОценок пока нет
- RHCSA Syllabus Day WiseДокумент4 страницыRHCSA Syllabus Day WiseAbdul KuddusОценок пока нет
- Archiving Material Master - Some Simple StepsДокумент22 страницыArchiving Material Master - Some Simple StepsFah Mun KwanОценок пока нет
- Buffer Cache Algorithms: Session No:5 Operating System Design @KL University, 2020Документ21 страницаBuffer Cache Algorithms: Session No:5 Operating System Design @KL University, 2020Sai susheel gupta sanagapalliОценок пока нет
- 10 Most Popular Linux Distributions ComparedДокумент10 страниц10 Most Popular Linux Distributions ComparedKristian ShytiОценок пока нет
- The Heap Size in WeblogicДокумент6 страницThe Heap Size in Weblogicvij_raajeev5534Оценок пока нет
- Advanced RDBMS Chapter 10 ConceptsДокумент7 страницAdvanced RDBMS Chapter 10 ConceptsGhanshyam SharmaОценок пока нет
- Archive Log ListДокумент10 страницArchive Log ListNarayan JayaramОценок пока нет
- SetPoint ReportДокумент64 страницыSetPoint ReportMaciell32Оценок пока нет
- Zend Guard Release Notes v6 0Документ3 страницыZend Guard Release Notes v6 0Marcos Vinícius GuardaОценок пока нет
- DberrДокумент28 страницDberrsergioОценок пока нет
- Linux-Practicals OdtДокумент3 страницыLinux-Practicals Odtsrinivas godavarthyОценок пока нет
- Install and Set Up OpenMediaVault 6 on a Raspberry Pi for NFS Sharing in Under 40 StepsДокумент9 страницInstall and Set Up OpenMediaVault 6 on a Raspberry Pi for NFS Sharing in Under 40 StepsSubrat Kumarr PandaОценок пока нет
- Vmcore-Dmesg 1Документ64 страницыVmcore-Dmesg 1LTI MaintenanceОценок пока нет
- How To Install MongoDB On Ubuntu 18.04 - DigitalOceanДокумент1 страницаHow To Install MongoDB On Ubuntu 18.04 - DigitalOceanYusto Malik OmondiОценок пока нет
- Micro Digital SMXFFS & SMXFD Flash File SystemsДокумент8 страницMicro Digital SMXFFS & SMXFD Flash File Systemsapi-3802214Оценок пока нет
- Debian 5 (Lenny) Step by Step InstallationsДокумент16 страницDebian 5 (Lenny) Step by Step InstallationsmadefundayОценок пока нет
- SAP Setup GuideДокумент49 страницSAP Setup GuidealaОценок пока нет
- Guide To Linux+ (2 Edition) ISBN 0-619-21621-2 End of Chapter Solutions Chapter 4 SolutionsДокумент8 страницGuide To Linux+ (2 Edition) ISBN 0-619-21621-2 End of Chapter Solutions Chapter 4 SolutionsNorhasimaSulaimanОценок пока нет
- Time Sharing: Operating SystemДокумент8 страницTime Sharing: Operating SystemJillian NoreenОценок пока нет
- Virtual Memory Behavior in Red Hat Linux Advanced ...Документ10 страницVirtual Memory Behavior in Red Hat Linux Advanced ...pavankalluriОценок пока нет
- Lab Assignment 1: Mapreduce / Hadoop: NotesДокумент2 страницыLab Assignment 1: Mapreduce / Hadoop: NotesKarthick JothivelОценок пока нет
- RHEV - What, Why and How-To PDFДокумент25 страницRHEV - What, Why and How-To PDFRakesh SinghОценок пока нет
- ArLCD EzLCD Startup Guide v2p3Документ25 страницArLCD EzLCD Startup Guide v2p3jomka4Оценок пока нет