Академический Документы
Профессиональный Документы
Культура Документы
Pasang Surut
Загружено:
Ryan PahrunАвторское право
Доступные форматы
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документАвторское право:
Доступные форматы
Pasang Surut
Загружено:
Ryan PahrunАвторское право:
Доступные форматы
Authentication Methods: From
Digital Signatures to Hashes
Lecture Motivation
We have looked at confidentiality services, and also examined
the information theoretic framework for security.
Confidentiality between Alice and Bob only guarantees that Eve
cannot read the message, it does not address:
Is Alice really talking to Bob?
Is Bob really talking to Alice?
In this lecture, we will look at the following problems:
Entity Authentication: Proof of the identity of an individual
Message Authentication: (Data origin authentication) Proof that
the source of information really is what it claims to be
Message Signing: Binding information to a particular entity
Data Integrity: Ensuring that information has not been altered by
unknown entities
Lecture Outline
Discrete Logarithms and ElGamal
Primitive elements and some more number theory (quickly)
DLOG
ElGamal, another Public Key Algorithm
Digital Signatures:
The basic idea
RSA Signatures and ElGamal Signatures
Inefficiencies: Hashing and Signing
Hash Functions:
Definitions and terminology
CHP Hash
SHA-1
Message Authentication Codes
Note: Some attacks will be discussed. More attacks and cryptanalysis will come later in the semester
Primitive Roots
Consider the following powers of 3 (mod 7):
31 3, 32 2, 33 6, 34 4, 35 5, 36 1 (mod 7)
Note that we obtain all non-zero numbers mod 7.
When this happens, we call 3 a primitive root (or generator) mod 7.
Is a number always a primitive root? No.
If p is prime there are (p-1) primitive roots mod p.
How to find them? Good homework problem
Proposition: Let g be a primitive root for the prime p
1.
If n is an integer, then gn=1 (mod p) if and only if and only if n=0 (mod p1) .
2.
If j and k are integers, then gj=gk (mod p) if and only if j=k (mod p-1).
Proof: We sketch (1) on the board.
Discrete Logarithms
Let p be a prime, and and nonzero integers (mod p) with
x (mod p)
The problem of finding x is called the discrete logarithm
problem, and is written:
x L
Often will be a primitive root mod p.
The discrete log behaves like the normal log in many ways:
L 1 2 L 1 L 2
Generally, finding the discrete log is a hard problem.
f(x) = x (mod p) is an example of a one-way function.
ElGamal Public Key Cryptosystem
One way functions are often used to construct public key
cryptosystems. We saw one in RSA, we now show an example
using the DLOG problem.
Alice wants to send m to Bob. Bob chooses a large prime p and a
primitive root . We assume 0 < m < p. Bob also chooses a
secret integer a and computes =a (mod p).
Bobs Public key is: (p, , )
Alice does:
1.
Chooses a secret random integer k and computes r=k (mod p)
2.
Computes t=km (mod p).
3.
Sends (r,t) to Bob.
Bob decrypts by:
tr a m (mod p)
ElGamal Public Key Cryptosystem, pg. 2
Important issues
a must be kept secret, else Eve can decrypt
Eve sees (r,t): t is the product of two random numbers and is
hence random. Knowing r does not really help as Eve would
need to be able to solve DLOG in order to get k.
Very important: A different random k must be used for each
message!
If we have m1 and m2, and use the same k, then the
ciphertexts will be (r,t1) and (r,t2)
If Eve ever finds m1 then she has m2 also!!!
t1 / m1 k t 2 / m 2 m 2 t 2 m1 / t1 mod p
Overview of Digital Signatures
Suppose you have an electronic document (e.g. a Word file).
How do you sign the document to prove to someone that it
belongs to you?
You cant use a scanned signature at the end this is easy to
forge and use elsewhere.
Conventional signing cant work in the digital world.
We require a digital signature to satisfy:
1.
Digital signatures cant be separated from the message and
attached to another message.
2.
Signature needs to be verified by others.
An Application for Digital Signatures
Suppose we have two countries, A and B, that have agreed not
to test any nuclear bombs (which produce seismic waves when
detonated). How can A monitor B by using seismic sensors?
1.
The sensors need to be in country B, but A needs to access
them. There is a conflict here.
2.
Country B wants to make sure that the message sent by the
seismic sensor does not contain other data (espionage).
3.
Country A, however, wants to make sure that the data has not
been altered by country B. (Assumption: the sensor itself is
tamper proof).
How can we solve this problem?
Treaty Verification Example
RSA provides a solution:
1.
Country A makes an RSA public/private key. (n,e) are given to
B but (p,q,d) are kept private in the tamper-proof sensor.
2.
Sensor collects data x and uses d to encrypt: y=xd (mod n), and
sends x and y to country B.
3.
Country B takes x and y and calculates z=ye (mod n).
4.
If z=x, then B can be sure that the encrypted message
corresponds to x. B then forwards (x,y) to A.
5.
Country A checks that ye (mod n)=x. If so, then A is sure that x
has not been modified, and A can trust x as being authentic.
In this example, it is hard for B to forge (x,y) and hence if (x,y)
verifies A can be sure that data came unaltered from the sensor.
RSA Signatures
The treaty example is an example of RSA signatures. We now
formalize it with Alice and Bob.
Alice publishes (n,eA) and keeps private (p,q,dA)
Alice signs m by calculating y=mdA (mod n). The pair (m,y) is
the signed document.
Bob can check that Alice signed m by:
1.
Downloading Alices (n,eA) from a trusted third party.
Guaranteeing that he gets the right (n,eA) is another problem
(well talk about this in a later lecture).
2.
Calculate z=yeA (mod n). If z=m then Bob (or anyone else) can
be guaranteed that Alice signed m.
RSA Signatures, pg. 2
Suppose Eve wants to attach Alices signature to another message m 1. She
cannot simply use (m1, y) since
e
m1 mod n
Therefore, she needs y1 with y1eA=m1 (mod n).
m1 looks like a ciphertext and y1 like a plaintext. In order for Eve to make a
fake y1 she needs to be able to decrypt m1 to get y1!!! She cant due to hardness
of RSA.
Existential Forgery: Eve could choose y1 first and then calculate an m1 using
(n,eA) via m1=y1eA (mod n). Now (m1, y1) will look like a valid message and
signature that Alice created since m1=y1eA (mod n).
Problem with existential forgery: Eve has made an m1 that has a signature, but
m1 might be gibberish!
Usefulness of existential forgery depends on whether there is an underlying
language structure.
Blind RSA Signatures
Sometimes we might want Alice to sign a document without knowing its
contents (e.g. privacy concerns: purchaser does not want Bank to know what is
being purchased, but wants Bank to authorize purchase).
We can accomplish this with RSA signatures (Bob wants Alice to sign a
document m):
1.
Alice generates an RSA public and private key pair.
2.
Bob generates a random k mod n with gcd (k,n)=1.
3.
Bob computes t=keAm (mod n), and sends t to Alice.
4.
Alice signs t as following the normal RSA signature procedure by calculating
s=tdA (mod n). Alice sends Bob s.
5.
Bob computes k-1s (mod n). This is the signed message mdA (mod n).
Verification:
k s mod n k t
1
1 d A
eA
Does Alice learn anything about m from t?
dA
k 1k e A d A m d A m d A mod n
ElGamal Signatures
We may modify the ElGamal public key procedure to become a
signature scheme.
Alice wants to sign m. Alice chooses a large prime p and a
primitive root . Alice also chooses a secret integer a and
computes =a (mod p).
Alices Public key is: (p, , ). Security of the signature depends
on the fact a is private.
Alice does:
1.
Chooses a secret random integer k with gcd(k,p-1)=1, and
computes r=k (mod p)
2.
Computes s=k-1(m-ar) (mod p).
3.
The signed message is the triple (m,r,s).
ElGamal Signatures, pg. 2
Bob can verify by:
1.
Downloading Alices public key (p, , ).
2.
Computes v1=rrs (mod p) and v2=m (mod n)
3.
The signature is valid if and only if v 1=v2 (mod p)
Verification: We have
sk m ar mod p 1 m sk ar mod p 1
Therefore
m
sk ar
a r
k s
v2
r r s v1 mod p
This scheme is believed to be secure, as long as DLOG is hard to
solve.
Dont: Choose a p with (p-1) the product of small primes and
dont reuse k.
Wastefulness of plain signatures
In signature schemes with appendix, where we attach the
signature to the end of the document, we increase the
communication overhead.
If we have a long message m=[m1,m2,,mN], then our signed
document is {[m1,m2,,mN],[sigA(m1),,sigA(mN)]}.
This doubles the overhead!
We dont want to do this when communication resources are
precious (which is always!).
Solution: We need to shrink the message into a smaller
representation and sign that.
Enter: Hash functions
Hash Functions
Straight-forward application of digital signatures can be
expensive when the message is large
In general, many security protocols benefit from using a
digested or compressed representative of a message
We typically need additional cryptographic properties in order for
the compression operation to be useful
This compression function is a hash function:
h(m)
Domain
Range
Hash Functions, pg. 2
Formally, a cryptographic hash function h takes an input
message of arbitrary length and produces a message digest of
fixed length, and satisfies:
1.
Given a message m, h(m) is quick to calculate
2.
One-Way (preimage resistance): Given a digest y, it is
computationally infeasible to find an m with h(m)=y.
3.
Strongly Collision Free: It is computationally infeasible to
find messages m1 and m2 with h(m1)=h(m2).
Can we ever have h(m1)=h(m2)? Yes. Why?
We will look at a couple examples.
Chaum, vanHeijst, Pfitzman Hash
We may use the DLOG problem to construct a hash function
Choose a prime p such that q=(p-1)/2 is also prime. (Theres an
algorithm for doing this, but thats not our goal today). Choose
two primitive roots and .
The hash function h(m) will take integers (mod q2) to integers
(mod p). Hence, producing half the bits.
Write m=x0+x1q with 0 x 0 , x1
. q 1
Define the hash by:
h m x 0 x1 mod p
CHP Hash is strongly collision-free
Proposition: If we know m m with h (m) h (m) , then
we can solve the discrete logarithm a L .
Proof: Will be given on the board after we cover all of the slides.
SHA-1
In order to get fast hash functions, we need to operate at the bitlevel. SHA-1 is one such algorithm.
Many of the popular hash functions (e.g. MD5, SHA-1) use an
iterative design:
Start with a message m of arbitrary length and break it into
n-bit blocks, m=[m1,m2,,ml]. The last block is padded to
fill out a full block size.
Message blocks are processed via a sequence of rounds using
a compression function h which combines current block and
the result of the previous round
X j h X j1 , m j
X0 is an initial value, and Xl is the message digest.
SHA-1, pg. 2
In SHA-1, we pad according to the rule:
Start with a message m of arbitrary length and break it into
n-bit blocks.
The last block is padded with a 1 followed by enough 0 bits
to make the new message 64 bits short of a multiple of 512
bits in length.
Into the 64 unfilled bits of the last block, we append the 64bit representation of the length T of the message.
Overall, we have L T / 512 1 blocks of 512 bits.
The appended message becomes m=[m1,m2,,mL].
SHA-1, pg. 3 (Basic Operations)
We will need the following bit operations:
SHA-1, pg. 4 (Basic Algorithm)
SHA-1, pg. 5 (Inside the Alg.)
Initial 160-bit register
X0=[H0,H1,H2,H3,H4]
SHA-1, pg. 6 (Subregister Operations)
The operations done by
ft(b,C,D) depend on the round
number t
The word Wt depends on the
round number t
The constant Kt depends on
the round number t
Message Authentication Codes
A message authentication code (MAC) is a function that is used
to prevent alteration of messages:
MACs use a shared key K between Alice and Bob
Alice will send not only the message m, but also MACK(m).
Bob checks whether the attached MAC matches what he calculates
Eve cannot alter the message because she does not have K.
The MAC takes two inputs: the key K and an arbitrary size m.
Ideally, a MAC should be a random mapping from all possible
inputs to n-bits of output.
The uncertainty (and security) of the MAC is directly associated
with the size of the key K
Remember: to Eve, the message is known, so its the key that
contains the security
CBC-MAC
CBC-MAC is a method for turning a block cipher into a MAC:
Idea: encrypt m using CBC mode and throw away all but last
block of ciphertext.
For messages P1, P2, , Pk, the MAC is calculated by
H 0 IV
H i E K Pi H i 1
MAC H k
Do not use the same key for encryption (confidentiality) and
authentication!
CBC-MAC, pg. 2
Be careful when using CBC-MAC. Heres a possible protocol
failure:
Observe: Fix K. If MAC(a)=MAC(b), then MAC(a||c)
=MAC(b||c), where c is a single block length in size.
MAC(a || c) E K c MAC(a ) E K c MAC(b) MAC(b || c)
1. Now, suppose attacker collects many MAC values and finds a
collision. This gives a and b for which MAC(a)=MAC(b).
2.
If attacker can get the sender to authenticate (a||c) (How is
another matter) then the attacker can replace the message
being sent to the receiver with (b||c).
Comment: Its not an easy attack to do, but it is a possible
weakness!
CBC-MAC, pg. 3
Practical Implementation Details:
1.
Generally, if your message is m, do not just calculate MAC(m),
rather you should make an intermediate message s=(l||m),
where l is the length of m in a fixed-length format.
2.
Pad s to be a multiple of block size
3.
Apply CBC-MAC to the padded string s
4.
Output the last ciphertext block. Do not output any
intermediate block values!
CBC-MAC can reuse same code as confidentiality (encryption)
functions
CBC-MAC is generally tough to use correctly, though.
HMAC
We may also use hash functions to build MACs.
We cannot simply use MACK(m)=h(K||m) or h(m||K):
Having the key at the front allows for length extension
attacks
Having the key at the end allows for key-recovery attacks
Designers of HMAC considered these issues
HMAC computes
MAC K m h K a || h K b || m
Where a and b are constants that are specified.
HMAC has been around for a while and has been cryptanalyzed.
Its the preferred MAC to use.
Using MACs
We must be careful using MACs.
If Alice sends Bob [m||MACK(m)] and Eve records this, she may
send it again at a later time (the replay attack!)
Generally, you want to authenticate not just the message, but the
context. That is, you want to authenticate m and additional data
d (such as message number, source, destination, protocol
identifier, sizes for different fields, etc.)
Why all these possibilities? If you tie the message to the specific
context, then it is harder for an adversary to manipulate context
fields to forge.
Make certain, though, that you have clear rules on how to split
concatenations (d||m) back into d and m.
Problems with Hashes
We must be careful when using hash functions, they are subject to some
attacks
Length Extension Attack: Consider a block-based hash like SHA-1, with
input blocks m=(m1, m2, , mk), and hash h(m).
A new message m =(m1, m2, , mk, mk+1), will have hash h(m)=h(h(m),mk+1),
where h is the compression sub-function.
In systems, such as authentication applications, where we calculate h(X||m), Eve
can append extra text to m and also update the hash.
Partial Message Collision Attack: Suppose we are able to find m and m
such that h(m)=h(m). If a system uses h(m||X) as an authentication
parameter, then due to the iterative nature h(m||X)=h(m||X).
An adversary can replace m with m during authentication.
In general hashing practice, we really use f(m)= h(h(m)||m) or f(m)=h(h(m))
as the hash.
Вам также может понравиться
- Slope Deflection: Ro Ro Se Isikan V, H & Q 0 DanДокумент12 страницSlope Deflection: Ro Ro Se Isikan V, H & Q 0 DanRyan PahrunОценок пока нет
- 10SSLДокумент18 страниц10SSLRyan PahrunОценок пока нет
- FerfedДокумент3 страницыFerfedRyan PahrunОценок пока нет
- Indah Dwi NingrumДокумент1 страницаIndah Dwi NingrumRyan PahrunОценок пока нет
- Ahmad YaniДокумент2 страницыAhmad YaniRyan PahrunОценок пока нет
- Anstruk Transformasi'Документ12 страницAnstruk Transformasi'Ryan PahrunОценок пока нет
- Contoh Soal Stiffness StrussДокумент37 страницContoh Soal Stiffness StrussRyan PahrunОценок пока нет
- Triaxial UU & CDДокумент12 страницTriaxial UU & CDRyan PahrunОценок пока нет
- Ryan Matriks Anstruk IIДокумент12 страницRyan Matriks Anstruk IIRyan PahrunОценок пока нет
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeОт EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeРейтинг: 4 из 5 звезд4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)От EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Рейтинг: 4 из 5 звезд4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryОт EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryРейтинг: 3.5 из 5 звезд3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceОт EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceРейтинг: 4 из 5 звезд4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingОт EverandThe Little Book of Hygge: Danish Secrets to Happy LivingРейтинг: 3.5 из 5 звезд3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItОт EverandNever Split the Difference: Negotiating As If Your Life Depended On ItРейтинг: 4.5 из 5 звезд4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureОт EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureРейтинг: 4.5 из 5 звезд4.5/5 (474)
- The Emperor of All Maladies: A Biography of CancerОт EverandThe Emperor of All Maladies: A Biography of CancerРейтинг: 4.5 из 5 звезд4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnОт EverandTeam of Rivals: The Political Genius of Abraham LincolnРейтинг: 4.5 из 5 звезд4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaОт EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaРейтинг: 4.5 из 5 звезд4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersОт EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersРейтинг: 4.5 из 5 звезд4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyОт EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyРейтинг: 3.5 из 5 звезд3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreОт EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreРейтинг: 4 из 5 звезд4/5 (1090)
- The Unwinding: An Inner History of the New AmericaОт EverandThe Unwinding: An Inner History of the New AmericaРейтинг: 4 из 5 звезд4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)От EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Рейтинг: 4.5 из 5 звезд4.5/5 (121)
- 0.2 Engineering Information Security PrinciplesДокумент24 страницы0.2 Engineering Information Security Principlestomy maulidiОценок пока нет
- Questions - Computer Crime - U4Документ2 страницыQuestions - Computer Crime - U4api-298865320Оценок пока нет
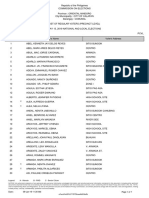
- Comunal DecДокумент70 страницComunal DecAngelika CalingasanОценок пока нет
- Acceptable Encryption PolicyДокумент3 страницыAcceptable Encryption PolicyBoris JohnsonОценок пока нет
- Index: S.No - Program Date RemarksДокумент24 страницыIndex: S.No - Program Date RemarksAyush BhatОценок пока нет
- CehДокумент3 страницыCehapi-3834671Оценок пока нет
- (Bluebee Uet - Com) 1472960712dethiso1 k53khmtДокумент3 страницы(Bluebee Uet - Com) 1472960712dethiso1 k53khmtZhu Ghe LiangОценок пока нет
- The Three Types of Addresses Used On The Internet IsДокумент3 страницыThe Three Types of Addresses Used On The Internet IsFa IzОценок пока нет
- An Introduction To Hacking and Cyber SecurityДокумент19 страницAn Introduction To Hacking and Cyber SecurityArjav JainОценок пока нет
- RHONDA AVE S. VIVARES and SPS. MARGARITA and DAVID SUZARA vs. ST. THERESA'S COLLEGE, MYLENE RHEZA T. ESCUDERO, and JOHN DOESДокумент2 страницыRHONDA AVE S. VIVARES and SPS. MARGARITA and DAVID SUZARA vs. ST. THERESA'S COLLEGE, MYLENE RHEZA T. ESCUDERO, and JOHN DOESJebellePuracanОценок пока нет
- Checklist Web Application SecurityДокумент2 страницыChecklist Web Application SecurityZoltán BalázsОценок пока нет
- Classical Encryption TechniquesДокумент39 страницClassical Encryption TechniquesAbhishek UpadhyayОценок пока нет
- Online Secure File Transfer SystemДокумент5 страницOnline Secure File Transfer Systemprem_shah_1991Оценок пока нет
- Reserve Bank of India: High Level Committee For Preparation of The Information Technology Vision Document 2011-2017Документ40 страницReserve Bank of India: High Level Committee For Preparation of The Information Technology Vision Document 2011-2017harindramehtaОценок пока нет
- Cyber Defence Intelligence - (CDI)Документ12 страницCyber Defence Intelligence - (CDI)FloydCarrasquilloОценок пока нет
- WINSEM2017-18 CSE4003 ETH SJT501 VL2017185003777 Reference Material I Digital Signature TechniquesДокумент23 страницыWINSEM2017-18 CSE4003 ETH SJT501 VL2017185003777 Reference Material I Digital Signature Techniquesanon_687421514Оценок пока нет
- Ads Intallers - Online Application Form 2022Документ13 страницAds Intallers - Online Application Form 2022Jaja ReynaldoОценок пока нет
- Operation Blockbuster ReportДокумент58 страницOperation Blockbuster ReportDell Cameron100% (2)
- Dell Networking N Series Payment Card Industry PCI Best PracticesДокумент24 страницыDell Networking N Series Payment Card Industry PCI Best PracticesRenato Lehmkuhl ScheidtОценок пока нет
- ch11 AISДокумент43 страницыch11 AISGraxa ViОценок пока нет
- Information Security MaintenanceДокумент14 страницInformation Security MaintenanceHamza AliОценок пока нет
- 17) Digital SignatureДокумент12 страниц17) Digital SignatureTelika RamuОценок пока нет
- PDFДокумент2 страницыPDFAbhimanyu SinhalОценок пока нет
- Ransom Cloud enДокумент33 страницыRansom Cloud enJoelcio Ribeiro GomesОценок пока нет
- CEHДокумент14 страницCEHVijay VishwakarmaОценок пока нет
- Syllabus THPv1Документ10 страницSyllabus THPv1alexОценок пока нет
- Encryption LessonДокумент2 страницыEncryption LessonKelly LougheedОценок пока нет
- Chapter 8 - CryptographyДокумент105 страницChapter 8 - CryptographydokkalliОценок пока нет
- Cyber UaeДокумент28 страницCyber UaeShaik Inayath0% (1)
- 3.security Issues in E-Procurement (PKI)Документ50 страниц3.security Issues in E-Procurement (PKI)Rohit BediОценок пока нет