Академический Документы
Профессиональный Документы
Культура Документы
Final PPT 2nd Review
Загружено:
saran0 оценок0% нашли этот документ полезным (0 голосов)
70 просмотров18 страницThis document describes a project that aims to enhance network security using three-level security. It proposes using a magic rectangle with three-prime RSA encryption to map plaintext characters to numerals, encrypt them, then decrypt and map back to recover the plaintext. This adds randomness compared to typical RSA. The system generates a magic rectangle based on column sums, then uses it with 3-prime RSA encryption/decryption in a more secure way than single-layer RSA.
Исходное описание:
project
Оригинальное название
Final Ppt 2nd Review
Авторское право
© © All Rights Reserved
Доступные форматы
PPTX, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документThis document describes a project that aims to enhance network security using three-level security. It proposes using a magic rectangle with three-prime RSA encryption to map plaintext characters to numerals, encrypt them, then decrypt and map back to recover the plaintext. This adds randomness compared to typical RSA. The system generates a magic rectangle based on column sums, then uses it with 3-prime RSA encryption/decryption in a more secure way than single-layer RSA.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PPTX, PDF, TXT или читайте онлайн в Scribd
0 оценок0% нашли этот документ полезным (0 голосов)
70 просмотров18 страницFinal PPT 2nd Review
Загружено:
saranThis document describes a project that aims to enhance network security using three-level security. It proposes using a magic rectangle with three-prime RSA encryption to map plaintext characters to numerals, encrypt them, then decrypt and map back to recover the plaintext. This adds randomness compared to typical RSA. The system generates a magic rectangle based on column sums, then uses it with 3-prime RSA encryption/decryption in a more secure way than single-layer RSA.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PPTX, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 18
VEL TECH MULTI TECH Dr.
RANGARAJAN
Dr. SAKUNTHALA ENGINEERING COLLEGE
DEPARTMENT OF INFORMATION
TECHNOLOGY
ENHANCED NETWORK SECURITY USING THREE LEVEL SECURITY
TEAM MEMBERS : PROJECT GUIDE :
1. V. ARAVINDAN – VM 10019 Dr. M.RAJESH KHANNA, M.TECH.,
Ph.D
2. G. SURIYA PRAKASH – VM 10009 ASST. PROFESSOR ,
IT - DEPT.
3. B. INDRAJITH – VM 10014
ABSTRACT
In today’s world, security is required to transmit confidential
information over the network and also demanded in wide range of
applications. Cryptographic algorithms play an important role in
providing the data security against malicious attacks.
Rivest-Shamir-Adleman (RSA) algorithm is used however, several
attacks are introduced to break the security of these algorithms due
to certain constraints.
In order to overcome the above said issue, “ENHANCED NETWORK
SECURITY USING THREE LEVEL SECURITY” is proposed to provide
more secured crypt analysis technique by enhancing the
randomness in the encryption process.
The main objective of the project is to allow data transmission
between users using three level security with the help of advance
mechanism termed as “MRG” and provides a secured and
authorized network which secures their large amount of data
among themselves.
LITERATURE SURVEY
TITLE : A Research on Enhancing Public Key Cryptography
AUTHOR : Alaa Hussein Al-Hamami and Ibrahem abdallah aldariseh,
(2013)“Enhanced Method of RSA cryptosystem Algorithm”,Kuala
Lampur,IEEE2013
YEAR : 2013
Description: This work prohibits any intruders from obtaining the plain
text in a readable form. The security aspect is enhanced as there is no
repetition of values in Magic rectangle. There are several parameters used
to increase the time complexity for the construction of magic rectangle
such as seed value, column sum, Minstart and Maxstart values. Even if the
intruders found the initial values of MR, it is very difficult to trace the
row/column. It plays a vital role in increasing the randomness and security
of the algorithm. And the use of RSA have the issue that the prime
numbers used should be more than 100. So have taken N-prime RSA so
that more than two prime numbers will be used and that can make the
prediction of prime numbers some what easier.
And the other thing is that two same character in plain text do not have
same cipher text. One of the issues in the proposed work is additional
time needed for the construction of Magic rectangle initially.
LITERATURE SURVEY (cont.,)
TITLE : Add-on Security Level based on hybrid encryption algorithm
based on RSA algorithm and diffie hellman algorithm
AUTHOR : Shilpi Gupta and Jaya Sharma
YEAR : 2015
Description: They proposed an algorithm by combining the two most
popular algorithm RSA algorithm and diffie hellman algorithm in order to
achieve higher security. RSA algorithm can be used for both public key
encryption and digital signature. Diffie hellman algorithm is used to
exchange the secret key between two parties and is also used for
providing more secure cipher text. RSA keys were taken as input to diffie
hellman algorithm. A GUI developed using java applet provides options to
the input user message and to upload file. Thus it provides the better
efficiency in terms of time complexity. A limitation of this paper is that the
key size of this algorithm is large
EXISTING SYSTEM
• Maintaining a database for this problem also has lots of
problem with it.
• Two large prime numbers are used
• RSA Cryptosystem is used to generate keys
• Plaintext is encrypted with respect to ASCII values
• Cipher text is decrypted by RSA
• Repeated characters will have repeated ciphers
DRAWBACKS --
• Time taken to factorize n is less.
• It relies upon factoring problem only ,i.e single layer
security.
• Prime numbers should be carefully chosen such that they
are not relatively close and small.
PROPOSED SYSTEM
• The methodology of the proposed security model is
described in the following steps. Construct different
singly even magic rectangle of order 32x48 and used
in lieu of ASCII table with 128 values. The Magic
rectangle contains totally 1536 values. It has been
divided into 12 quadrants, each consists of 128
characters.
• Each character of the plain text is converted into
numerals based on its position in magic rectangle in
different quadrants. The numerals are then
encrypted and decrypted using RSA algorithm.
DESIGN MODULES
MODULE DESCRIPTION
Generation of MRGA
• The column sum(32*48) , min start and max start is
obtained to compute MR .
Mapping
• Input ASCII value are mapped with numerals in
quadrants.
Encryption
• The mapped numeral is sent to 3-prime RSA to obtain cipher.
Decryption
• The cipher is decrypted to get numerals.
Searching
• The numerals are mapped with MR appropriately with
respect to quadrants to get plaintext.
3 – PRIME RSA DESCRIPTION
• Choose three distinct prime numbers p, q and s.
• Find n such that n = p*q*s. n will be used as the modulus for
both the public and private keys.
• Find the Phi of n, ¥(n) = (p-1)(q-1)(s-1).
• Choose an e such that 1 < e < ¥ (n), and such that e and ¥ (n)
share no divisors other than 1 (e and ¥ (n) are relatively
prime). e is kept as the public key exponent.
• Determine d (using modular arithmetic) which satisfies the
congruence relation .d=e ^- 1 (mod ¥ (n)).
ILLUSTRATION
• Inputs for MRGA
– Column_sum, min_start, max_start.
MRGA DESCRIPTION
• Read the column sum for 32*48
• Obtain column sum for 4*6 from given 32*48 column sum.
• Column sum(4*6)=column sum(32*48) /16
• Row sum(4*6)=(column sum(4*6)/2)+column sum(4*6)
• Form a concrete structure for 4*6 magic rectangle generation
• Pivot=row sum(4*6)-column sum(4*6);
• Supply min start and max start for 64 units of 4*6 such that
sum of both gives pivot
• Combine 4 4*6 to form a 8*12
• Combine 4 8*12 to form a 16*24
• Combine 4 16*24 to form a 32*48
FORMATION OF MAGIC RECTANGLE
FROM SQUARE
• The magic square concept forms the basis for magic
Rectangle.(order n*n)
• The sums of all the elements in every row, column are equal.
• 7 0 5 12
2 4 6 12
3 8 1 12
12 12 12 36
• The generation of magic rectangle is based on perfect
rectangle principle.
side lengths ratio=1:1.618
• In magic rectangle to increase randomness columns and rows
have different sum
SOLUTIONS
SOLUTIONS (Cont.,)
SOLUTIONS (Cont.,)
SOLUTIONS (Cont.,)
REFERENCES
• Dr.D.I.George Amalarethinam , J.Sai Geetha (2014) ,
“Enhancing Security level for Public Key
Cryptosystem using MRGA”, World Congress On
Computing and Communication Technologies,IEEE,
vol 4 ,no 5 ,pp.98 – 102
• Hardik Gandhi,Vinit gupta,Rajput,(2015) , “A
Research on Enhancing Public Key Cryptography by
The Use of MRGA with RSA and N-Prime RSA”,
International Journal for Innovative Research in
Science & Technology, vol 1 , no 12 , pp.91 - 98
Вам также может понравиться
- (IJCST-V2I1P3) :K.Devika, M.JawaharДокумент6 страниц(IJCST-V2I1P3) :K.Devika, M.JawaharIJETA - EighthSenseGroupОценок пока нет
- A Review On Implementation of RSA Cryptosystem Using Ancient Indian Vedic MathematicsДокумент3 страницыA Review On Implementation of RSA Cryptosystem Using Ancient Indian Vedic MathematicsEditor IJRITCCОценок пока нет
- Final Report RSAДокумент27 страницFinal Report RSAMounesh Panchal67% (3)
- CryptograpyДокумент4 страницыCryptograpyEng Marwa ElsherifОценок пока нет
- Using Cryptography Algorithms To Secure Cloud Computing Data and ServicesДокумент4 страницыUsing Cryptography Algorithms To Secure Cloud Computing Data and ServicesRareş T. BogdanОценок пока нет
- Modified Rsa Encryption Algorithm Using Four Keys IJERTCONV3IS07021Документ5 страницModified Rsa Encryption Algorithm Using Four Keys IJERTCONV3IS07021Jeff HambreОценок пока нет
- 2012 - High Speed Implementation of RSA Algorithm With Modified Keys ExchangeДокумент4 страницы2012 - High Speed Implementation of RSA Algorithm With Modified Keys ExchangePeraKojotОценок пока нет
- New Encryption AlgorithmДокумент5 страницNew Encryption AlgorithmcheintОценок пока нет
- Comparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingДокумент5 страницComparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingAsaba BrianОценок пока нет
- 4 A Study of Encryption AlgorithmsДокумент9 страниц4 A Study of Encryption AlgorithmsVivekОценок пока нет
- Assignment No.8: 8.1 TitleДокумент6 страницAssignment No.8: 8.1 TitleSagar KhodeОценок пока нет
- Improvised Asymmetric Key Encryption Algorithm Using MATLABДокумент6 страницImprovised Asymmetric Key Encryption Algorithm Using MATLABIOSRjournalОценок пока нет
- A New Symmetric Cryptosystem Using RandoДокумент7 страницA New Symmetric Cryptosystem Using RandoNget ThearithОценок пока нет
- Big Data Security Issues Based On Quantum Cryptography: Prakruti Chaudhari, Prof. Riya GohilДокумент5 страницBig Data Security Issues Based On Quantum Cryptography: Prakruti Chaudhari, Prof. Riya GohilSakshi SinghОценок пока нет
- Advanced Cryptanalytic Algorithm For Data SecurityДокумент4 страницыAdvanced Cryptanalytic Algorithm For Data SecurityInternational Journal of Application or Innovation in Engineering & ManagementОценок пока нет
- Improved Cryptography by Applying Transposition On Modified Playfair Algorithm Followed by SteganographyДокумент5 страницImproved Cryptography by Applying Transposition On Modified Playfair Algorithm Followed by SteganographyInternational Journal of Innovative Science and Research TechnologyОценок пока нет
- Chaotic Rivest-Shamir-Adlerman Algorithm With Data Encryption Standard SchedulingДокумент9 страницChaotic Rivest-Shamir-Adlerman Algorithm With Data Encryption Standard SchedulingCut EncutОценок пока нет
- Cryptographic Accelerator in Reconfigurable HardwareДокумент8 страницCryptographic Accelerator in Reconfigurable HardwareDaniel Andrés CrespoОценок пока нет
- Cryptography and Network Security: Third Edition by William StallingsДокумент58 страницCryptography and Network Security: Third Edition by William StallingsabyОценок пока нет
- Building Information Security Using New Expanded RSA CryptosystemДокумент4 страницыBuilding Information Security Using New Expanded RSA Cryptosystemabdulg abdulОценок пока нет
- High Speed Implementation of RSA Algorithm With Modified Keys ExchangeДокумент5 страницHigh Speed Implementation of RSA Algorithm With Modified Keys ExchangeYoniОценок пока нет
- Encryption and Decryption Using AES in The Field of Network Communication Based On ConfidentialityДокумент3 страницыEncryption and Decryption Using AES in The Field of Network Communication Based On ConfidentialityUjjwal KumarОценок пока нет
- Xtea AnalysisДокумент4 страницыXtea Analysismiki_dudaulОценок пока нет
- Enhanced Rsa Cryptosystem Based On Three Prime Numbers: Vivek Choudhary and Mr. N. PraveenДокумент5 страницEnhanced Rsa Cryptosystem Based On Three Prime Numbers: Vivek Choudhary and Mr. N. PraveenHarshil ShahОценок пока нет
- Ijdte 01 02 2016 P5Документ8 страницIjdte 01 02 2016 P5xtofsetОценок пока нет
- Ijert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsДокумент4 страницыIjert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsNandha KumarОценок пока нет
- Feasibility Presentation PPT Format (1) (Read-Only)Документ17 страницFeasibility Presentation PPT Format (1) (Read-Only)Sudeepti D NandaОценок пока нет
- Secrets of Number Theoretic Tools in Network Security Algorithms of Public-Key CryptosystemsДокумент25 страницSecrets of Number Theoretic Tools in Network Security Algorithms of Public-Key CryptosystemsVijay AnandОценок пока нет
- Implementation and Comparison of Hybrid Encryption Model For Secure Network Using AES and ElgamalДокумент5 страницImplementation and Comparison of Hybrid Encryption Model For Secure Network Using AES and ElgamalDr. Priyanka MathurОценок пока нет
- File Storage On Cloud Using CryptographyДокумент6 страницFile Storage On Cloud Using CryptographyIJRASETPublicationsОценок пока нет
- Jecet: Journal of Electronics and Communication Engineering & Technology (JECET)Документ13 страницJecet: Journal of Electronics and Communication Engineering & Technology (JECET)IAEME PublicationОценок пока нет
- Bello M ConfДокумент11 страницBello M ConfSýstëmàtíçBéllóОценок пока нет
- RSA 32-Bit Implementation TechniqueДокумент6 страницRSA 32-Bit Implementation TechniqueMaya BoutebОценок пока нет
- Report Writing FormatДокумент8 страницReport Writing FormatAmir KhanОценок пока нет
- A Single Chip Design and IMPLEMENTATION OF AES - 128/192/256 Encryption AlgorithmsДокумент8 страницA Single Chip Design and IMPLEMENTATION OF AES - 128/192/256 Encryption AlgorithmsMahiii MaddipatlaОценок пока нет
- Enhancing RSA Algorithm Using Mersenne Primes WithДокумент6 страницEnhancing RSA Algorithm Using Mersenne Primes WithAxel LucianoОценок пока нет
- Paper 2 - : February 2021Документ22 страницыPaper 2 - : February 2021zubair nawazОценок пока нет
- Cryptosystem An Implementation of RSA Using VerilogДокумент8 страницCryptosystem An Implementation of RSA Using VerilogInternational Journal of Computer Networks and Communications SecurityОценок пока нет
- SUB157380Документ4 страницыSUB157380김동주Оценок пока нет
- Das 2016 Ijca 909789Документ4 страницыDas 2016 Ijca 909789Vishal FundingОценок пока нет
- Asymmetric Key, Data Encryption Standard (DES), NTH - Degree Truncated Polynomial Ring Unit (NTRU), Rivest - Shamir - Adleman (RSA), Symmetric KeyДокумент5 страницAsymmetric Key, Data Encryption Standard (DES), NTH - Degree Truncated Polynomial Ring Unit (NTRU), Rivest - Shamir - Adleman (RSA), Symmetric KeyKruti ShahОценок пока нет
- Comparative Study and Performance Analysis of Encryption in RSA, ECC and Goldwasser-Micali CryptosystemsДокумент8 страницComparative Study and Performance Analysis of Encryption in RSA, ECC and Goldwasser-Micali CryptosystemsInternational Journal of Application or Innovation in Engineering & ManagementОценок пока нет
- Effectual Data Integrity Checking Technique Based On Number TheoryДокумент5 страницEffectual Data Integrity Checking Technique Based On Number TheoryiirОценок пока нет
- 24-03-2022-1648118520-6-.-1. Engg - A New Varying Cipher For Symmetric Key CryptosystemsДокумент10 страниц24-03-2022-1648118520-6-.-1. Engg - A New Varying Cipher For Symmetric Key CryptosystemsImpact JournalsОценок пока нет
- Combination of The "Data Encryption Standard" Algorithm (DES) and The "Public-Key Encryption" Algorithm (RSA) On The Key - Generation StageДокумент3 страницыCombination of The "Data Encryption Standard" Algorithm (DES) and The "Public-Key Encryption" Algorithm (RSA) On The Key - Generation StageInternational Journal of Application or Innovation in Engineering & ManagementОценок пока нет
- 3.0 Public KeyДокумент26 страниц3.0 Public KeyshaliniОценок пока нет
- 3.1 Public Key CryptographyДокумент20 страниц3.1 Public Key CryptographyTHIRU MURUGAN R 2k20BCA339Оценок пока нет
- Presentation On: Speeding Up Secure Web Transactions Using "Elliptical Curve Cryptography"Документ16 страницPresentation On: Speeding Up Secure Web Transactions Using "Elliptical Curve Cryptography"BrijnandanSingh ChauhanОценок пока нет
- Cryptography and Network Security: by William StallingsДокумент26 страницCryptography and Network Security: by William StallingsPriyanka Singh SengarОценок пока нет
- Numeric To Numeric Encryption of Databases Using 3kDES AlgorithmДокумент5 страницNumeric To Numeric Encryption of Databases Using 3kDES AlgorithmSwathi VasudevanОценок пока нет
- Chapter 9 - Public Key Cryptography and RSAДокумент26 страницChapter 9 - Public Key Cryptography and RSAswarna_793238588Оценок пока нет
- Embedment of Montgomery Algorithm On Elliptic Curve Cryptography Over RSA Public Key CryptographyДокумент7 страницEmbedment of Montgomery Algorithm On Elliptic Curve Cryptography Over RSA Public Key Cryptographywingwingxd61Оценок пока нет
- DM Project ReportДокумент19 страницDM Project ReportShivang Ahuja100% (1)
- Comparative Study of Symmetric Encryption Techniques For Mobile Data Caching in WMNДокумент6 страницComparative Study of Symmetric Encryption Techniques For Mobile Data Caching in WMNtheijesОценок пока нет
- Private-Key CryptographyДокумент30 страницPrivate-Key CryptographySrikar DuddukuriОценок пока нет
- Comparison of Symmetric and Asymmetric Cryptography With Existing Vulnerabilities and CountermeasuresДокумент4 страницыComparison of Symmetric and Asymmetric Cryptography With Existing Vulnerabilities and CountermeasuresLaine VenâncioОценок пока нет
- A Comparative Study of Symmetric Key Encryption Algorithms: Amit Jain, Divya BhatnagarДокумент6 страницA Comparative Study of Symmetric Key Encryption Algorithms: Amit Jain, Divya BhatnagarrebwarpcОценок пока нет
- Improved Trial Division Algorithm by Lagrange's Interpolation FunctionДокумент5 страницImproved Trial Division Algorithm by Lagrange's Interpolation FunctionEditor IJRITCCОценок пока нет
- 9.public Key Cryptography and RSAДокумент33 страницы9.public Key Cryptography and RSAemmanuelauko4Оценок пока нет
- 15 The End 2oДокумент71 страница15 The End 2osaranОценок пока нет
- Final Report by BinuДокумент77 страницFinal Report by BinusaranОценок пока нет
- First Level ReportДокумент38 страницFirst Level ReportsaranОценок пока нет
- Final Report Batch 15Документ78 страницFinal Report Batch 15saranОценок пока нет
- Experimental Study On Characteristics of Bitumen With RubberДокумент37 страницExperimental Study On Characteristics of Bitumen With RubbersaranОценок пока нет
- JXCX OMT0006 AДокумент87 страницJXCX OMT0006 AEva SuárezОценок пока нет
- Honeycomb Dzone Refcard 364 Full Stack ObservabiliДокумент8 страницHoneycomb Dzone Refcard 364 Full Stack ObservabiliFernandoОценок пока нет
- IBM Partner Ecosystem Sales FoundationДокумент12 страницIBM Partner Ecosystem Sales FoundationTim0% (1)
- Iteration Split With Firefly AlgorithmДокумент7 страницIteration Split With Firefly AlgorithmPriyanka SharmaОценок пока нет
- Curriculum Vitae MD Asik Ali: Degree / Certificate Qualification Institute Board/ University Year DGPA/Aggre Gate %Документ4 страницыCurriculum Vitae MD Asik Ali: Degree / Certificate Qualification Institute Board/ University Year DGPA/Aggre Gate %dambakuОценок пока нет
- Short Term Preparation FSC 1 PTB Salman Sherazi PDFДокумент53 страницыShort Term Preparation FSC 1 PTB Salman Sherazi PDFMuhammad AliОценок пока нет
- Electronic System: 5, 7 Information Technology: 1, 3, 6Документ16 страницElectronic System: 5, 7 Information Technology: 1, 3, 6makessseuОценок пока нет
- Sap Simple Finance Interview QuestionsДокумент3 страницыSap Simple Finance Interview QuestionsMOORTHYОценок пока нет
- Product Presentation - Vehicle Access Automation SolutionsДокумент18 страницProduct Presentation - Vehicle Access Automation SolutionsRefaat BenbayaОценок пока нет
- BCMT Module 5 - Monitoring and Evaluating Tech4ED CentersДокумент30 страницBCMT Module 5 - Monitoring and Evaluating Tech4ED CentersCabaluay NHS0% (1)
- DEM Extraction From OR2A Stereo and ERDAS LPSДокумент12 страницDEM Extraction From OR2A Stereo and ERDAS LPSSanto CheboskyОценок пока нет
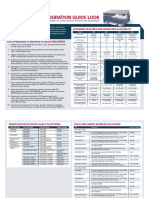
- Datasheet 4Документ2 страницыDatasheet 4Ivan ElisioОценок пока нет
- Getting Started With Wko5: Trainingpeaks University - Instructor: Tim CusickДокумент61 страницаGetting Started With Wko5: Trainingpeaks University - Instructor: Tim CusickDiego RiosОценок пока нет
- Ad3301 Data Exploration and VisualizationДокумент24 страницыAd3301 Data Exploration and VisualizationKowsalya GОценок пока нет
- ProductDataSheet-IgnitionCloudEdition SinglePagesДокумент6 страницProductDataSheet-IgnitionCloudEdition SinglePages2oeufsfraisaukiloОценок пока нет
- Sem 620Документ22 страницыSem 620Soumya PanjaОценок пока нет
- The Engineering Design Revolution - CAD History - 10 BentleyДокумент27 страницThe Engineering Design Revolution - CAD History - 10 Bentleyphamduyproject100% (1)
- TRДокумент21 страницаTRtrang03x1bОценок пока нет
- Online Loan Application and Verification 2016Документ34 страницыOnline Loan Application and Verification 2016ashutosh nandaniОценок пока нет
- Temperature and Humidity Transmitter SHT20 Sensor Modbus RS485Документ8 страницTemperature and Humidity Transmitter SHT20 Sensor Modbus RS485thang doanОценок пока нет
- Peoplesoft Price List 070612Документ11 страницPeoplesoft Price List 070612ravi pОценок пока нет
- 13.A Real Time Crime Records Management System For National Security AgenciesДокумент13 страниц13.A Real Time Crime Records Management System For National Security AgenciesAfshan Yasmeen 490-FBAS/BSIT4/F20Оценок пока нет
- Chapter One: Introduction To Marketing ResearchДокумент35 страницChapter One: Introduction To Marketing ResearchEmjae ColmenaresОценок пока нет
- Academica Pro 3.0 - Documentation - WPZOOMДокумент14 страницAcademica Pro 3.0 - Documentation - WPZOOMBenedek RakovicsОценок пока нет
- Introduction To Support Vector MachinesДокумент23 страницыIntroduction To Support Vector Machinesvarshitha sureshОценок пока нет
- Rack Stack ChecklistДокумент2 страницыRack Stack ChecklistJuller Efren Zabarburu MasОценок пока нет
- Assessment of Interpolation Methods For Solving The Real Life ProblemДокумент6 страницAssessment of Interpolation Methods For Solving The Real Life ProblemGaurav BasniwalОценок пока нет
- FIFO Depth Calculation ?Документ1 страницаFIFO Depth Calculation ?AbhОценок пока нет
- Licensing Microsoft Office Software PDFДокумент9 страницLicensing Microsoft Office Software PDFinfo for businessОценок пока нет
- CSC 2304 01 - Syllabus - Computer ArchitectureДокумент4 страницыCSC 2304 01 - Syllabus - Computer ArchitectureAmine NaitlhoОценок пока нет